| File name: | tor.exe |
| Full analysis: | https://app.any.run/tasks/8f334ac9-5857-44c4-a230-08f5334adbc3 |
| Verdict: | Malicious activity |
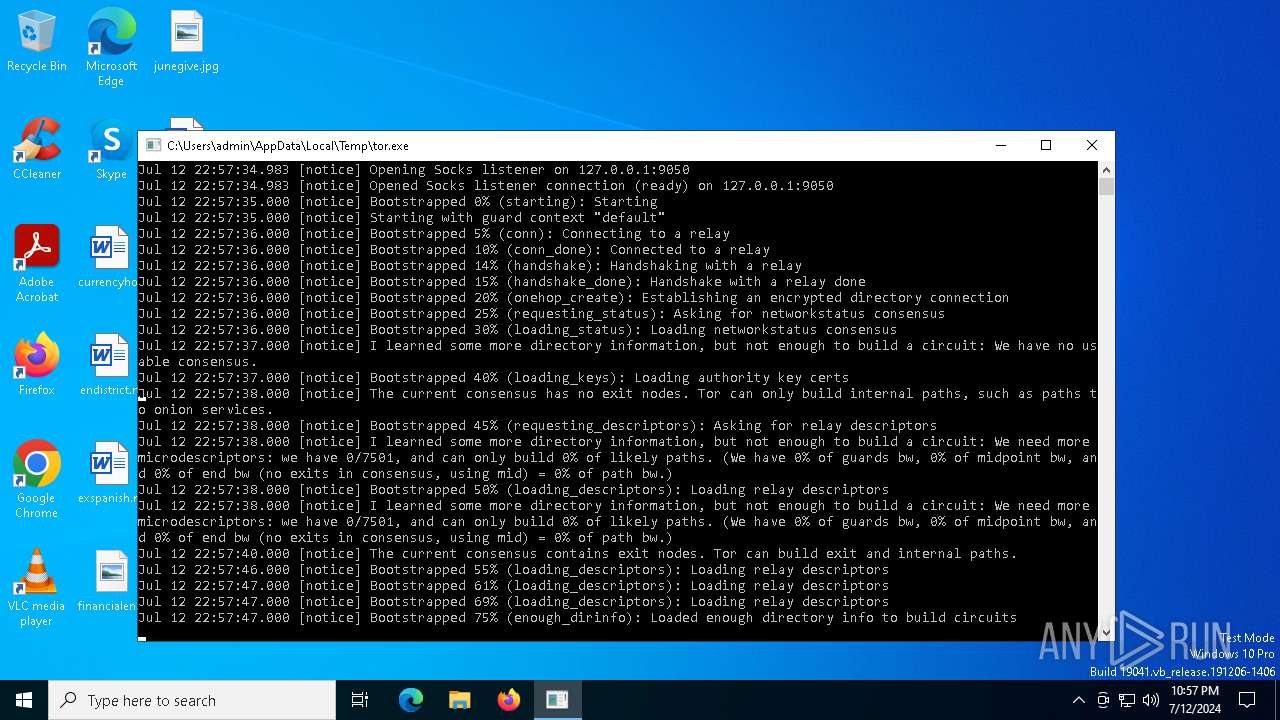
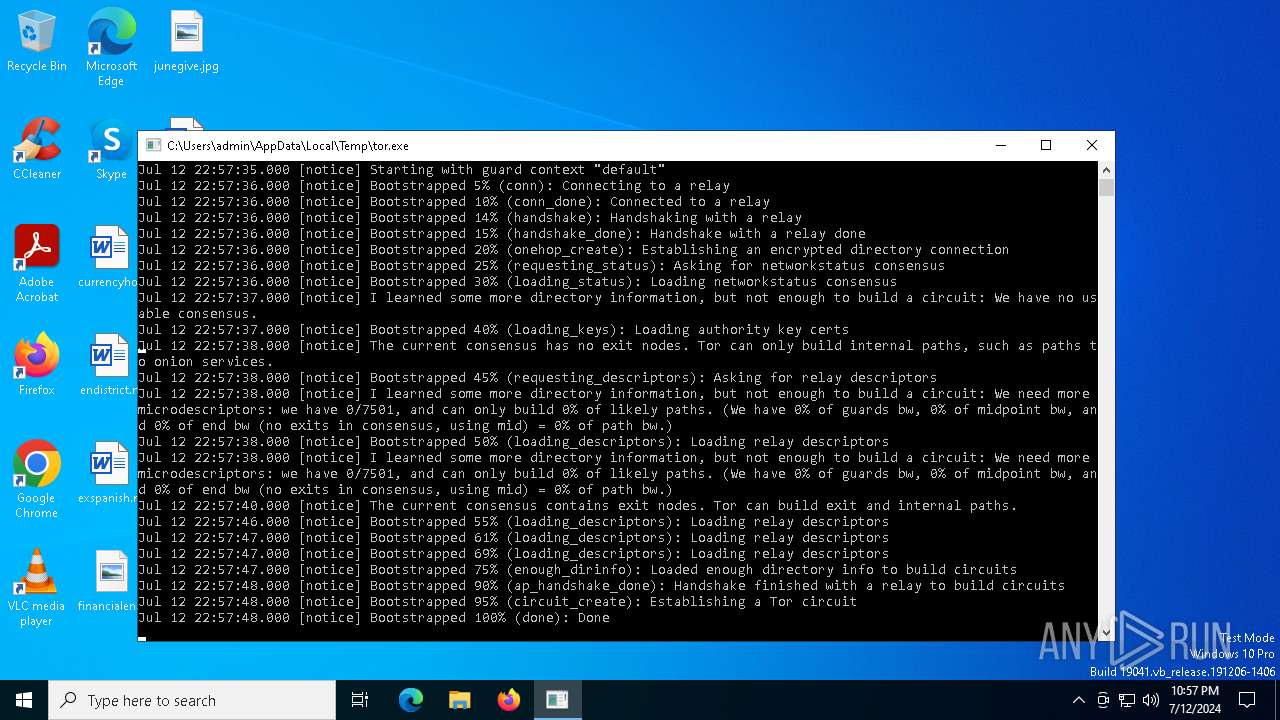
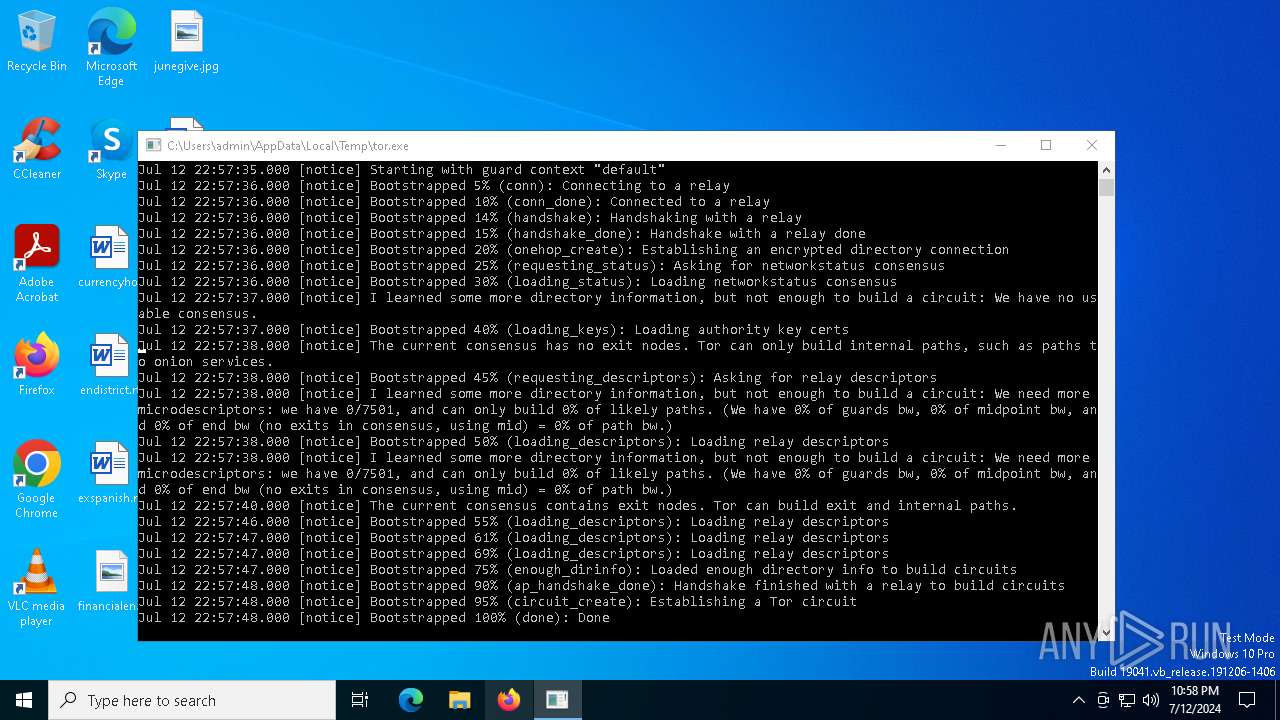
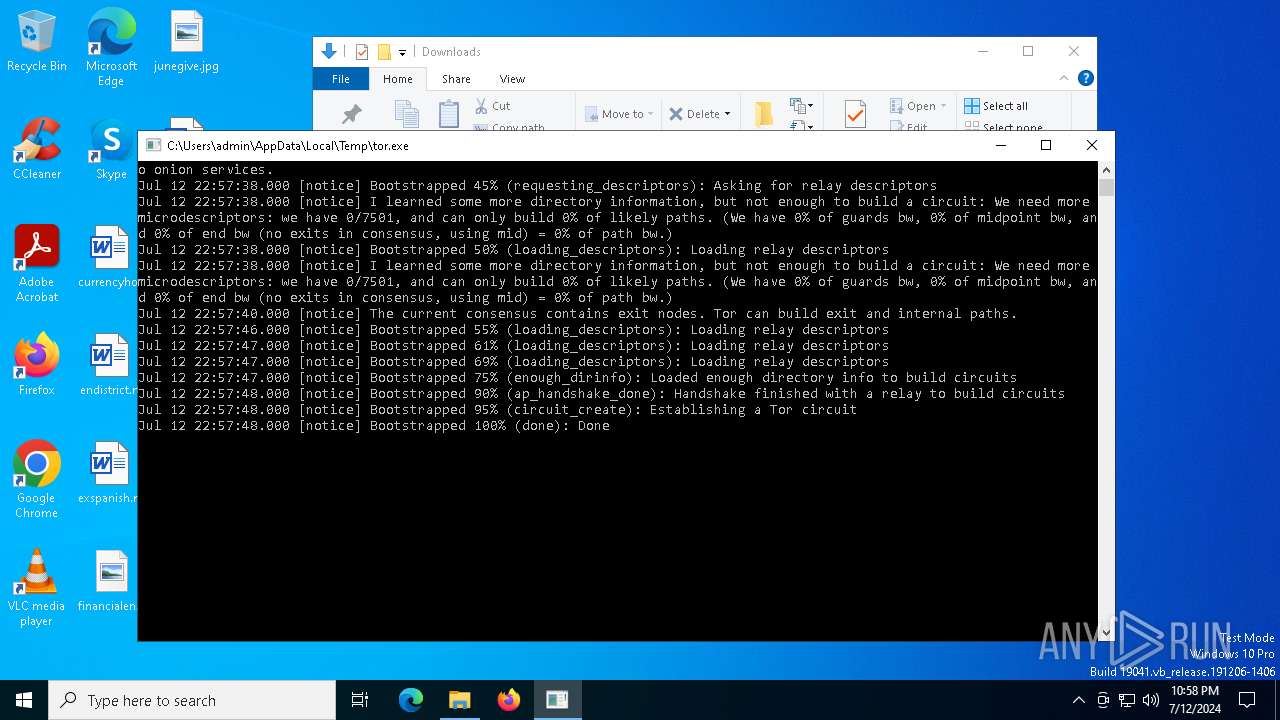
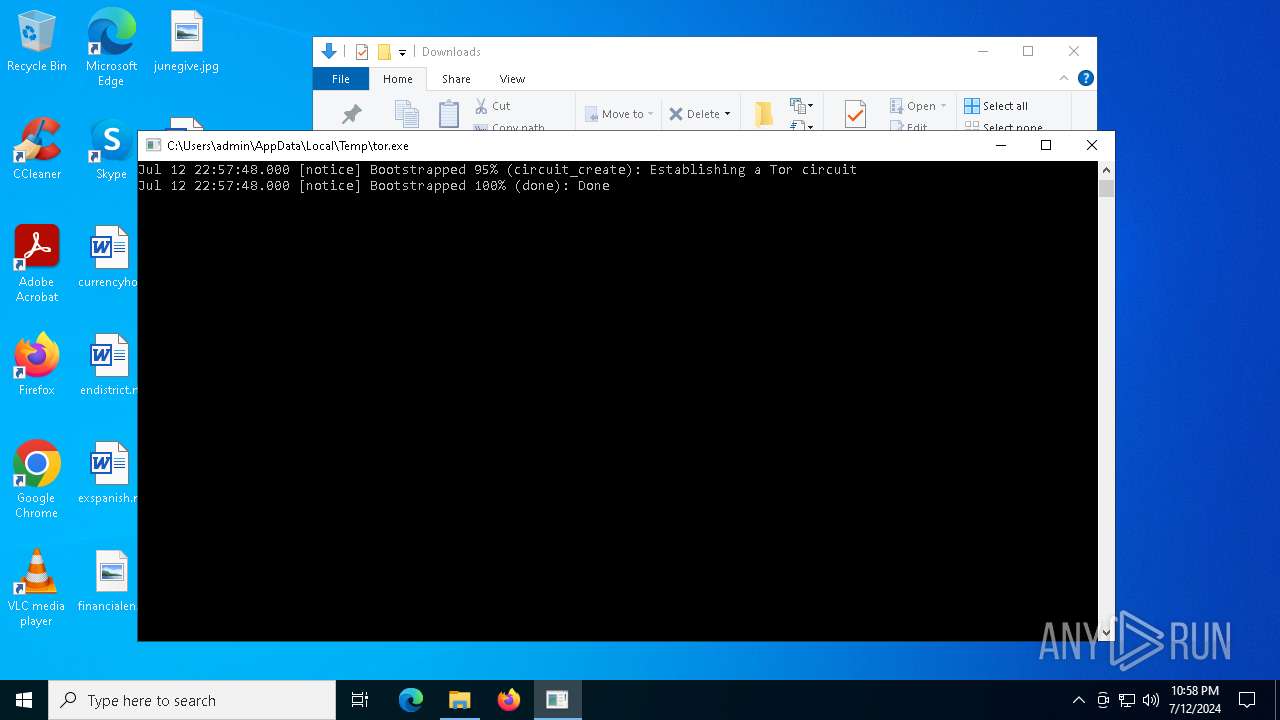
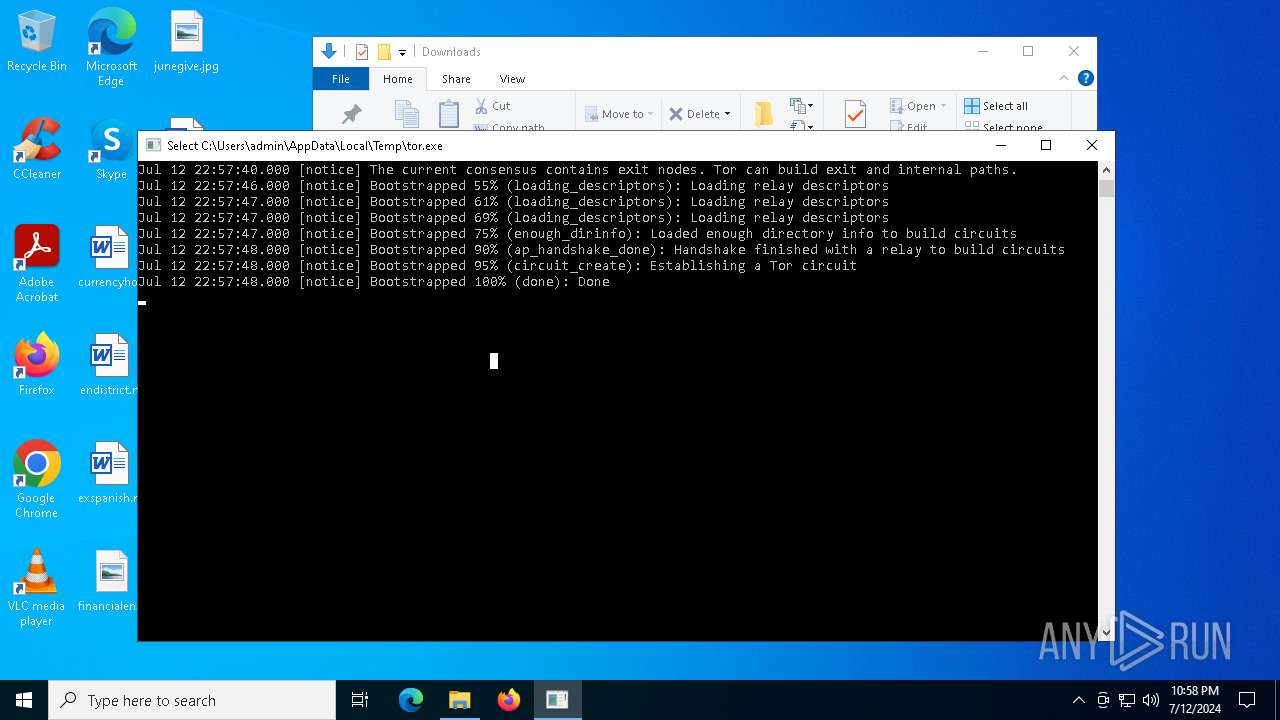
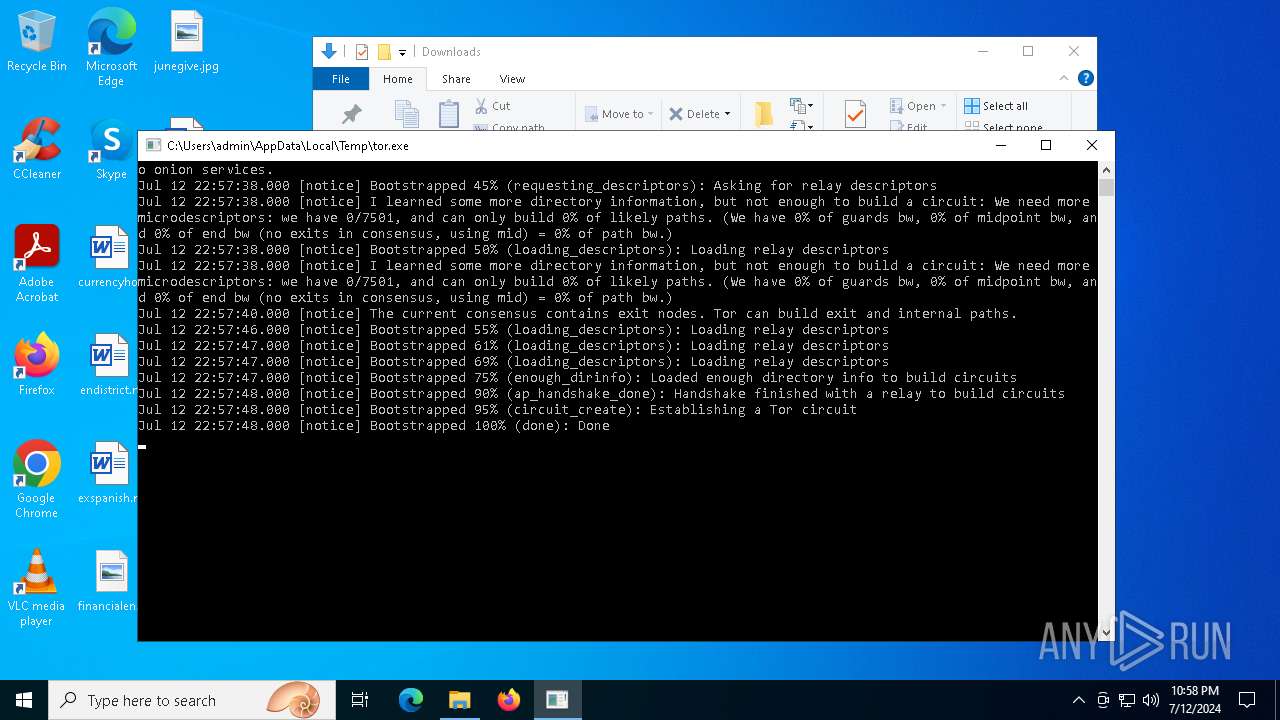
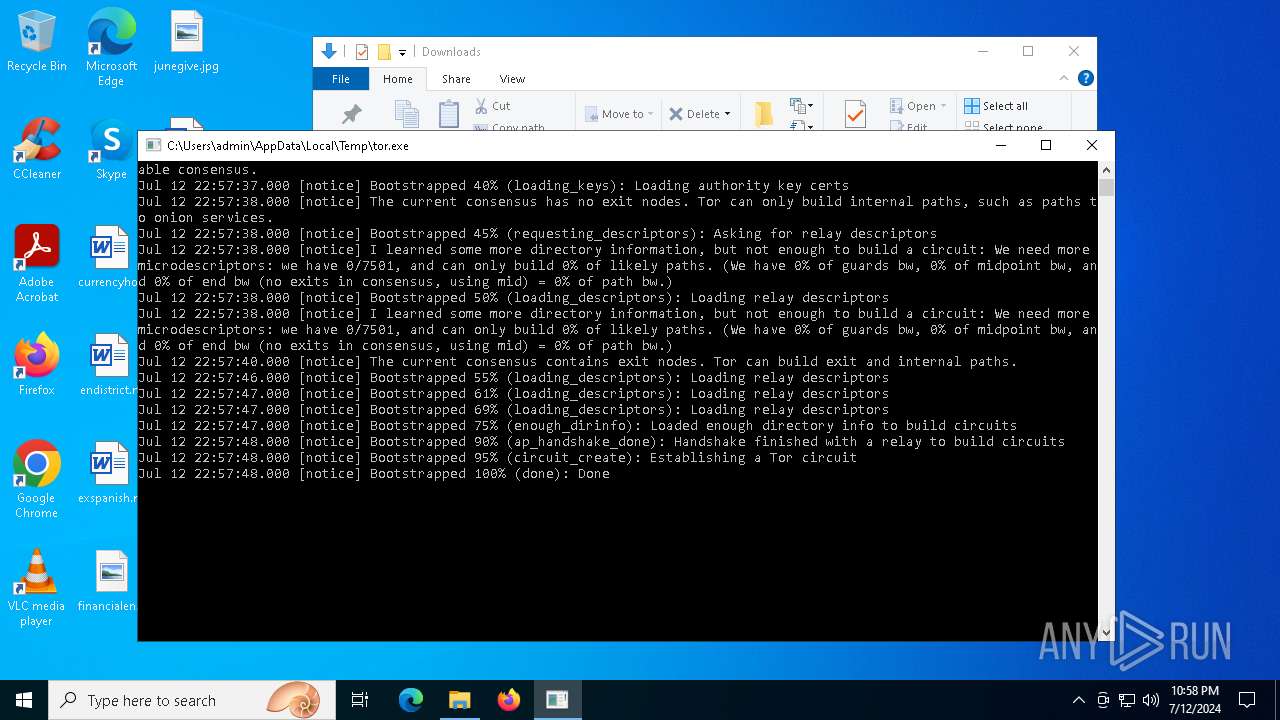
| Analysis date: | July 12, 2024, 22:57:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | A46913AB31875CF8152C96BD25027B4D |
| SHA1: | 99E9C857A9BCCA65E727773B40595478C38E7A75 |
| SHA256: | 66FD723D0DD219807C6D7DCC331E25C8D05ADCCF4A66312928FBE1D0E45670ED |
| SSDEEP: | 98304:TOPU8DPCBmhqrL+qO9vZRdA7qGRplv9L1Z3dYrUeBkBx8eL1IPPGwiylCMXZx9Nj:aw1IPVXVNS |
MALICIOUS
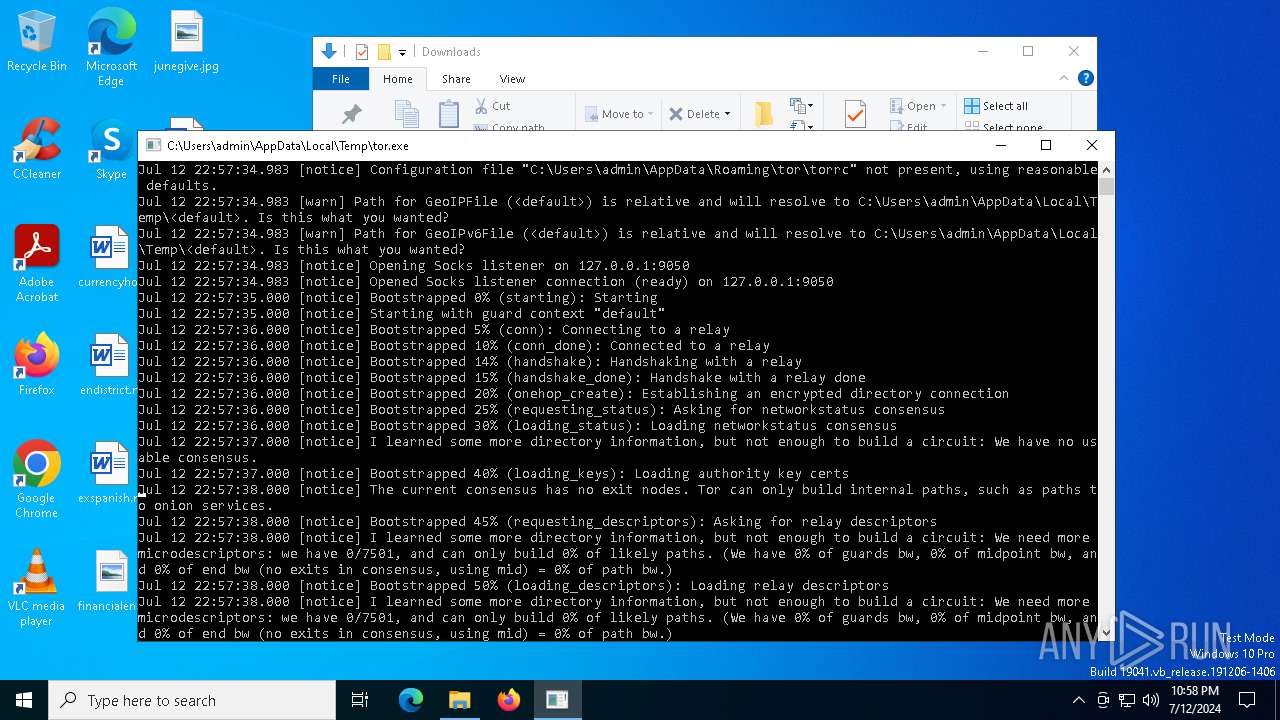
Drops the executable file immediately after the start
- tor.exe (PID: 752)
SUSPICIOUS
Connects to unusual port
- tor.exe (PID: 752)
INFO
Reads the computer name
- tor.exe (PID: 752)
Creates files or folders in the user directory
- tor.exe (PID: 752)
Checks supported languages
- tor.exe (PID: 752)
Reads the machine GUID from the registry
- tor.exe (PID: 752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 7133184 |
| InitializedDataSize: | 1848832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1350 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
136
Monitored processes
3
Malicious processes
0
Suspicious processes
1
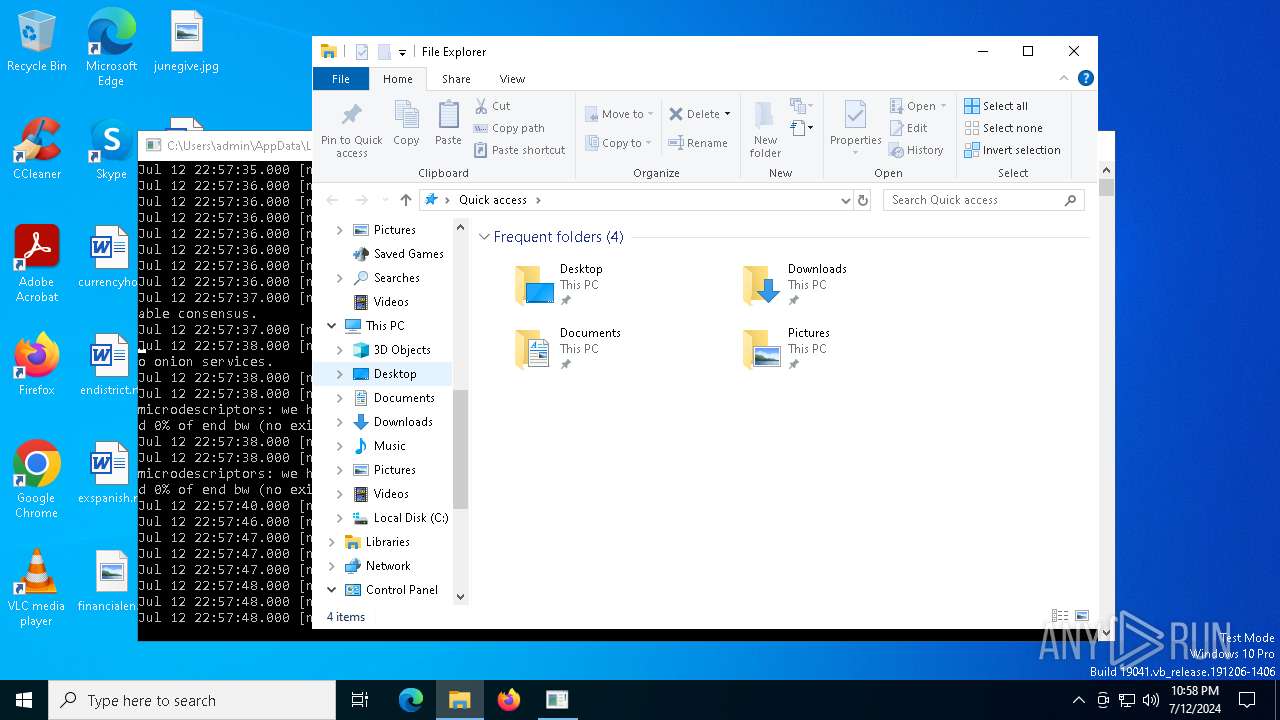
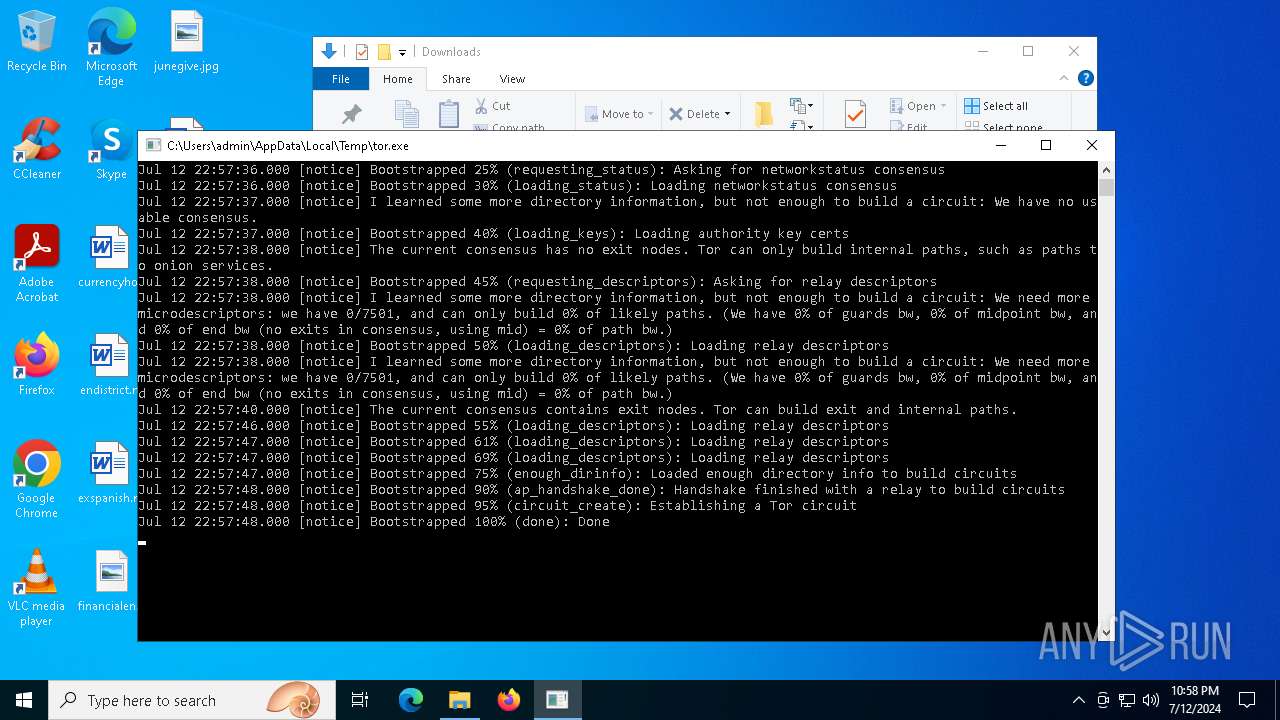
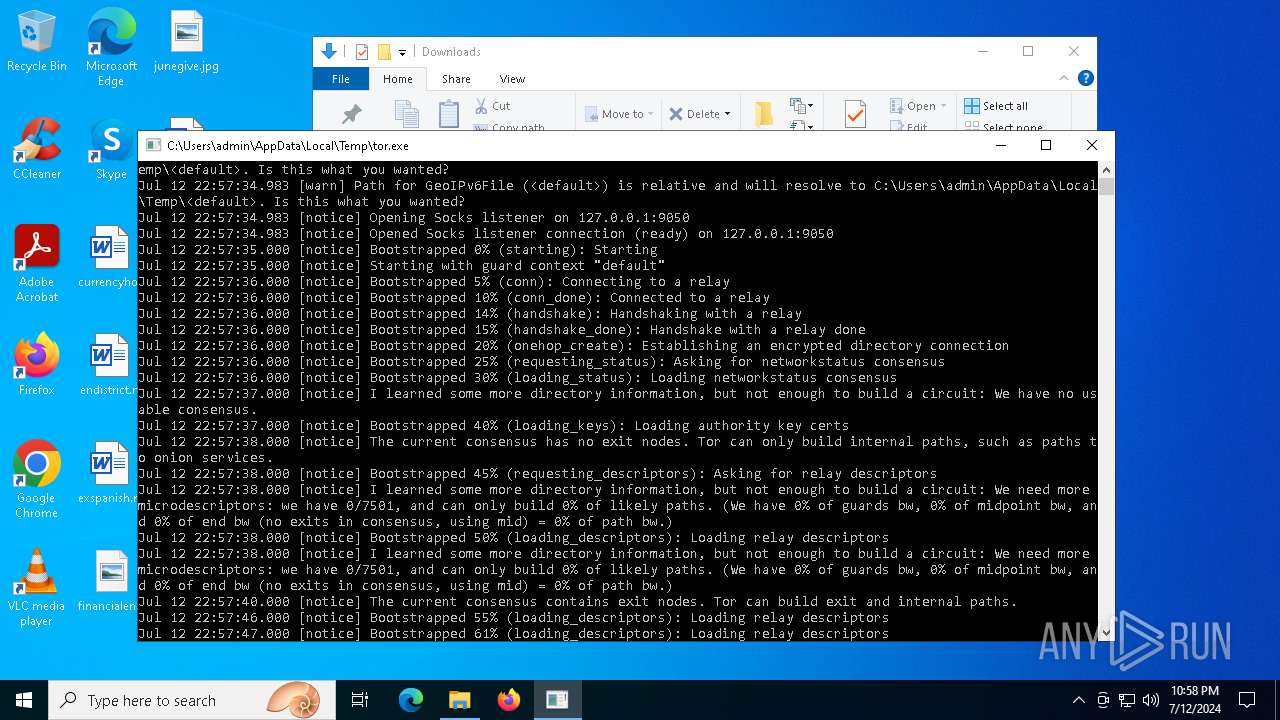
Behavior graph
Click at the process to see the details
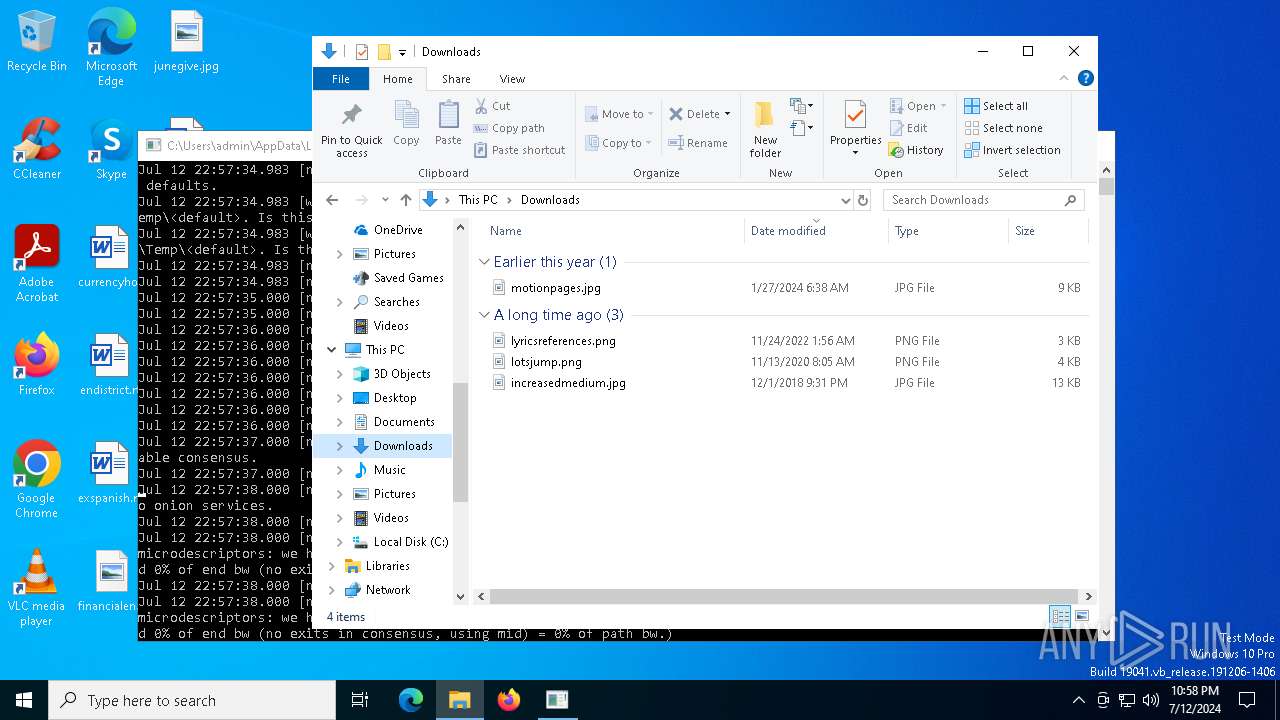
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
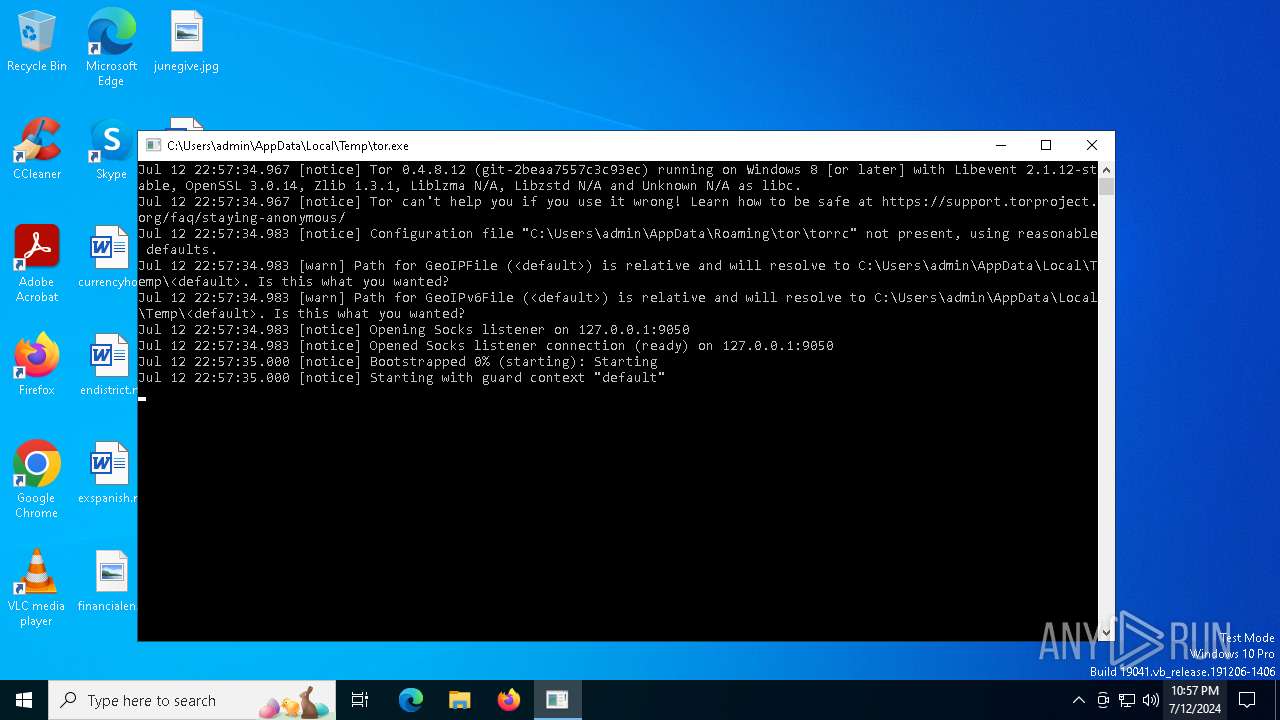
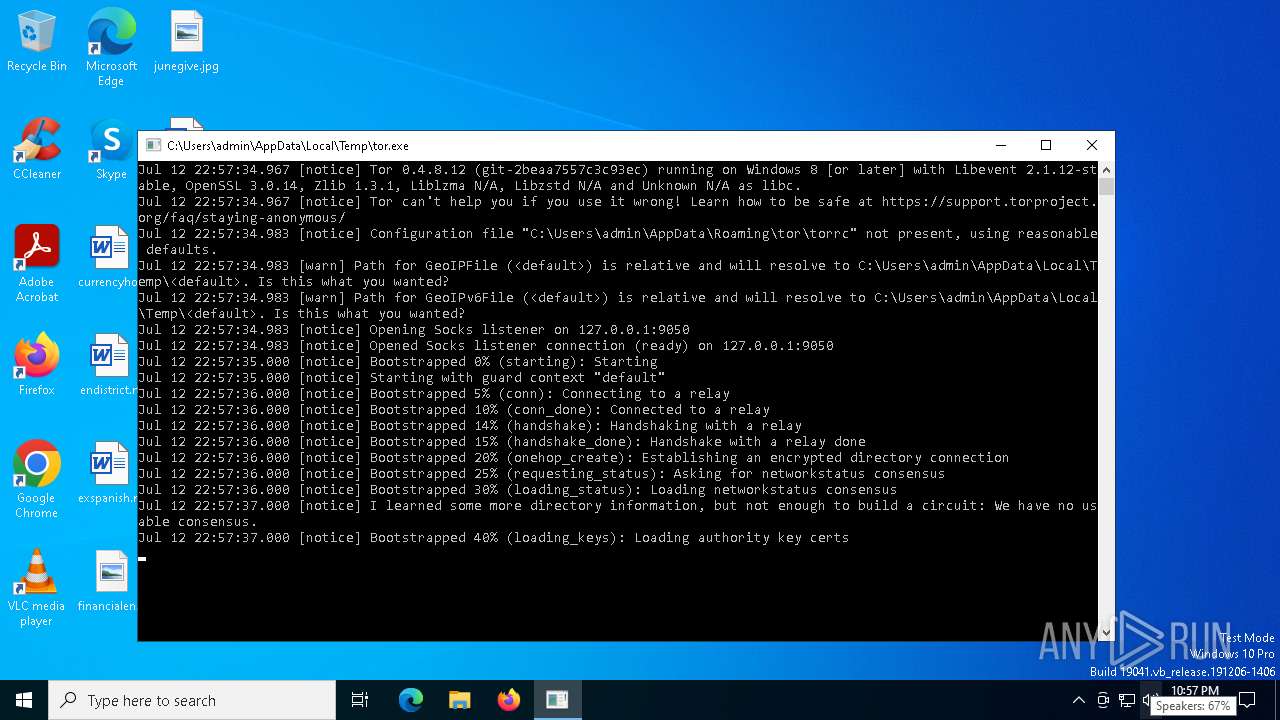
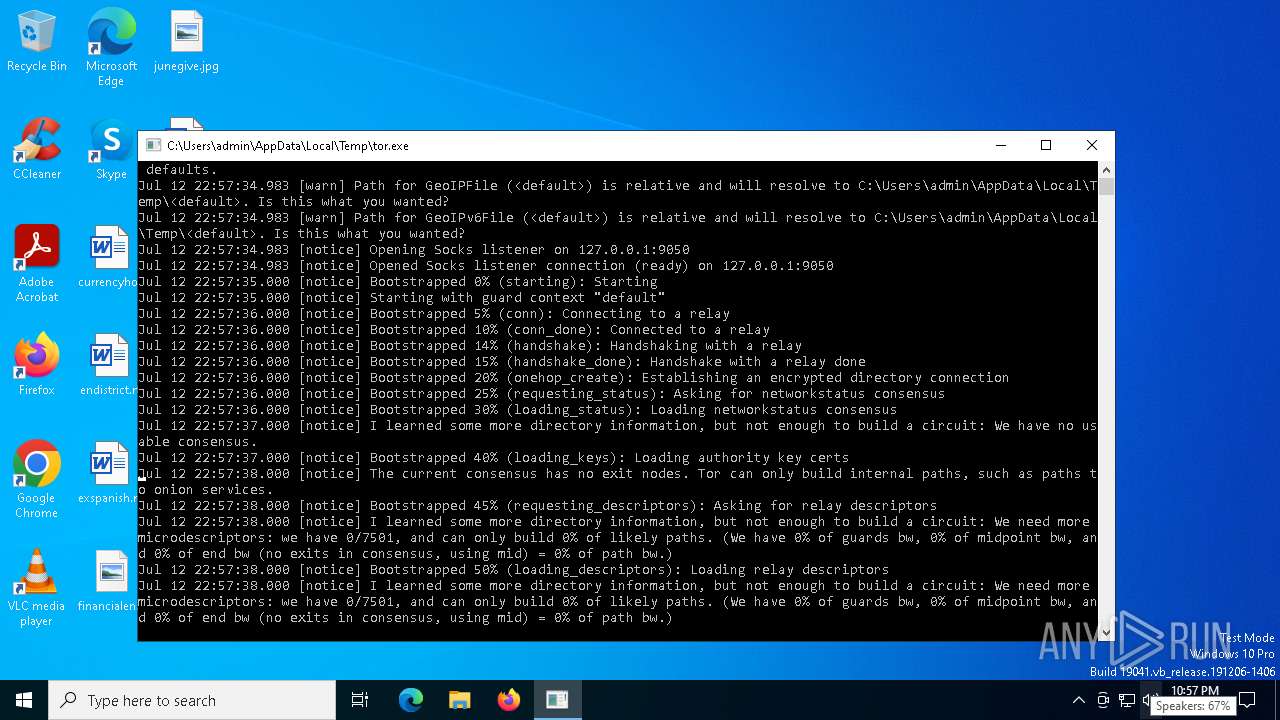
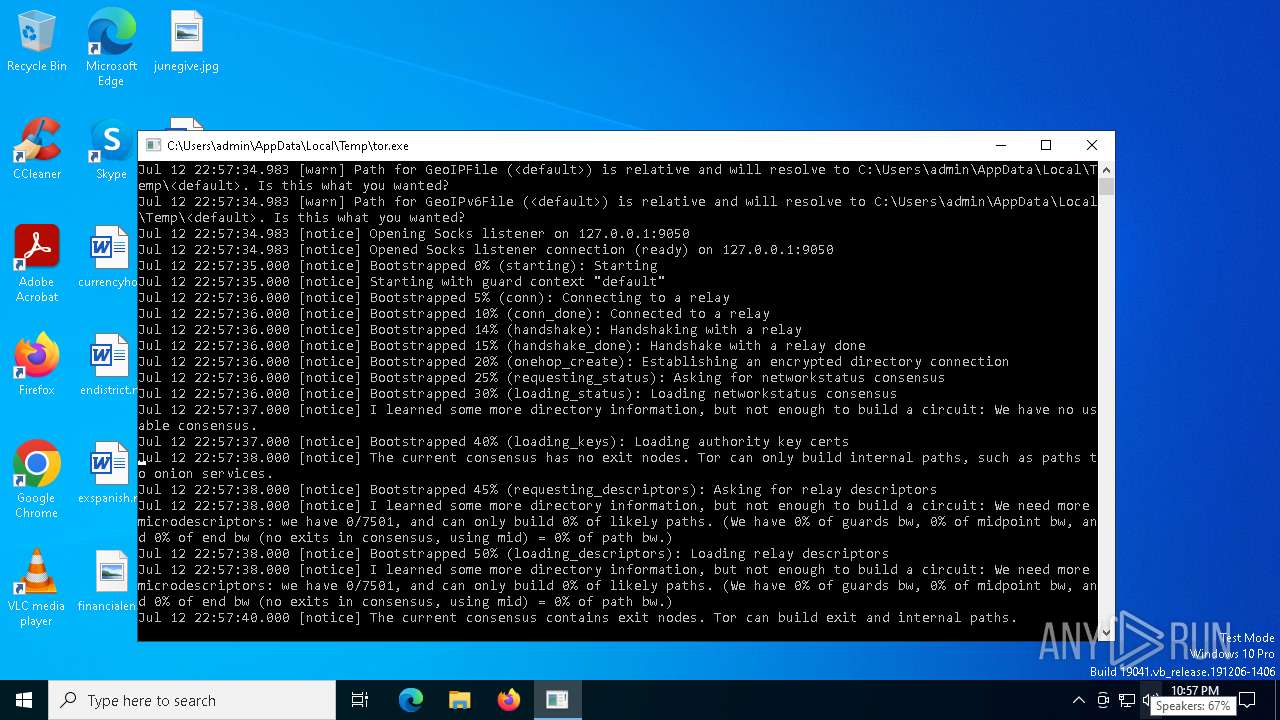
| 752 | "C:\Users\admin\AppData\Local\Temp\tor.exe" | C:\Users\admin\AppData\Local\Temp\tor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7036 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
816
Read events
816
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
15
Unknown types
0
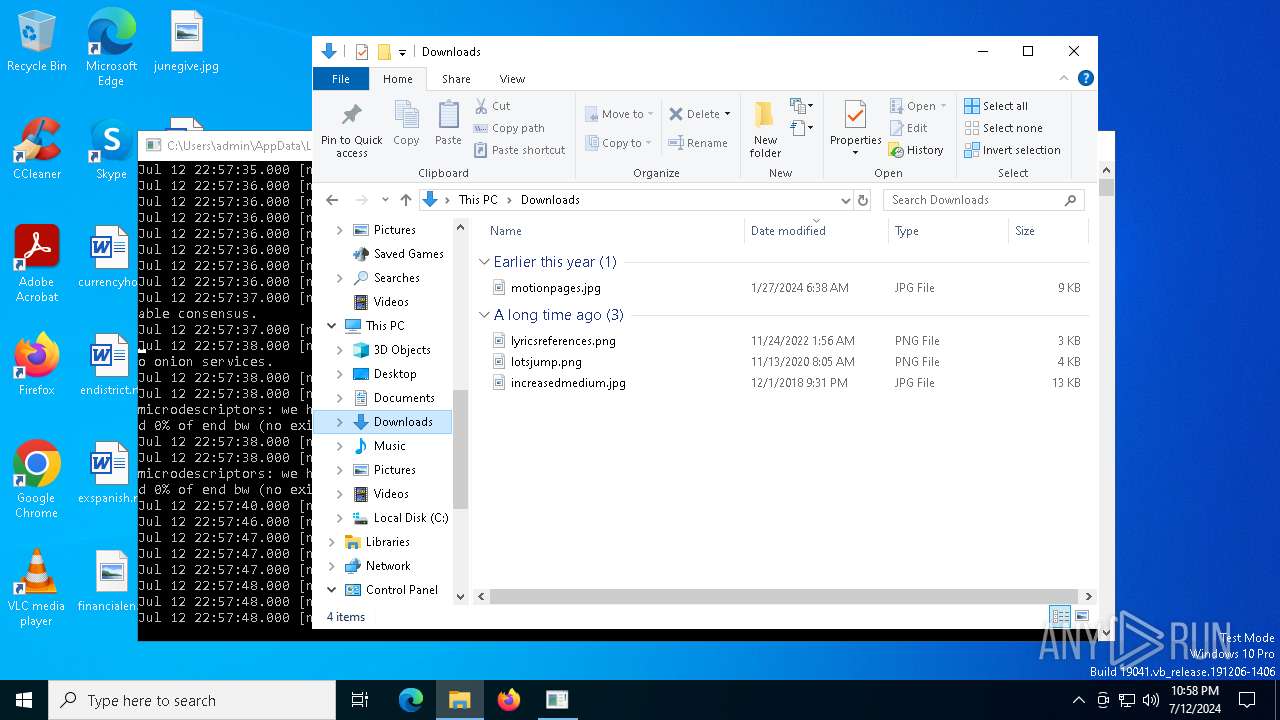
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\state | text | |
MD5:B1567A768F93F9A5584D679670D376B5 | SHA256:6E5E3B714A91D191B3D9FB2BDE50BCDBF299C5826EFAE8422FC13E70E62C7131 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-certs.tmp | text | |
MD5:37B17FB88A80C535490D67908734AD1E | SHA256:E0E3B4871FF572EF65F48B6DC85233C7B568809CC255E5FD6276BA627A8C6F85 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdesc-consensus.tmp | text | |
MD5:B378D97C8C5775420651A392A1452504 | SHA256:7D194F538D3180AB89047563BC03C9968E0BA3A965D7DA1FFC50B251B84E27E0 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-certs | text | |
MD5:37B17FB88A80C535490D67908734AD1E | SHA256:E0E3B4871FF572EF65F48B6DC85233C7B568809CC255E5FD6276BA627A8C6F85 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdescs.new | text | |
MD5:9D199BA304C86AA6FCF2523B24A0AE66 | SHA256:F11CAEF077D3E7A2F9697C331ADC54B40364A92B4B7220A9F95EF3938A6564A6 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdesc-consensus | text | |
MD5:B378D97C8C5775420651A392A1452504 | SHA256:7D194F538D3180AB89047563BC03C9968E0BA3A965D7DA1FFC50B251B84E27E0 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\unverified-microdesc-consensus.tmp | text | |
MD5:B378D97C8C5775420651A392A1452504 | SHA256:7D194F538D3180AB89047563BC03C9968E0BA3A965D7DA1FFC50B251B84E27E0 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\unverified-microdesc-consensus | text | |
MD5:B378D97C8C5775420651A392A1452504 | SHA256:7D194F538D3180AB89047563BC03C9968E0BA3A965D7DA1FFC50B251B84E27E0 | |||
| 752 | tor.exe | C:\Users\admin\AppData\Roaming\tor\state.tmp | text | |
MD5:B1567A768F93F9A5584D679670D376B5 | SHA256:6E5E3B714A91D191B3D9FB2BDE50BCDBF299C5826EFAE8422FC13E70E62C7131 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
85
DNS requests
24
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4448 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4448 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2916 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6720 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6720 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5284 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1968 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1376 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4448 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4448 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4656 | SearchApp.exe | 104.126.37.177:443 | www.bing.com | Akamai International B.V. | DE | unknown |
752 | tor.exe | 107.189.31.232:9000 | — | PONYNET | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
752 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 7 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 7 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 246 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 689 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 382 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 246 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 7 |
752 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 7 |