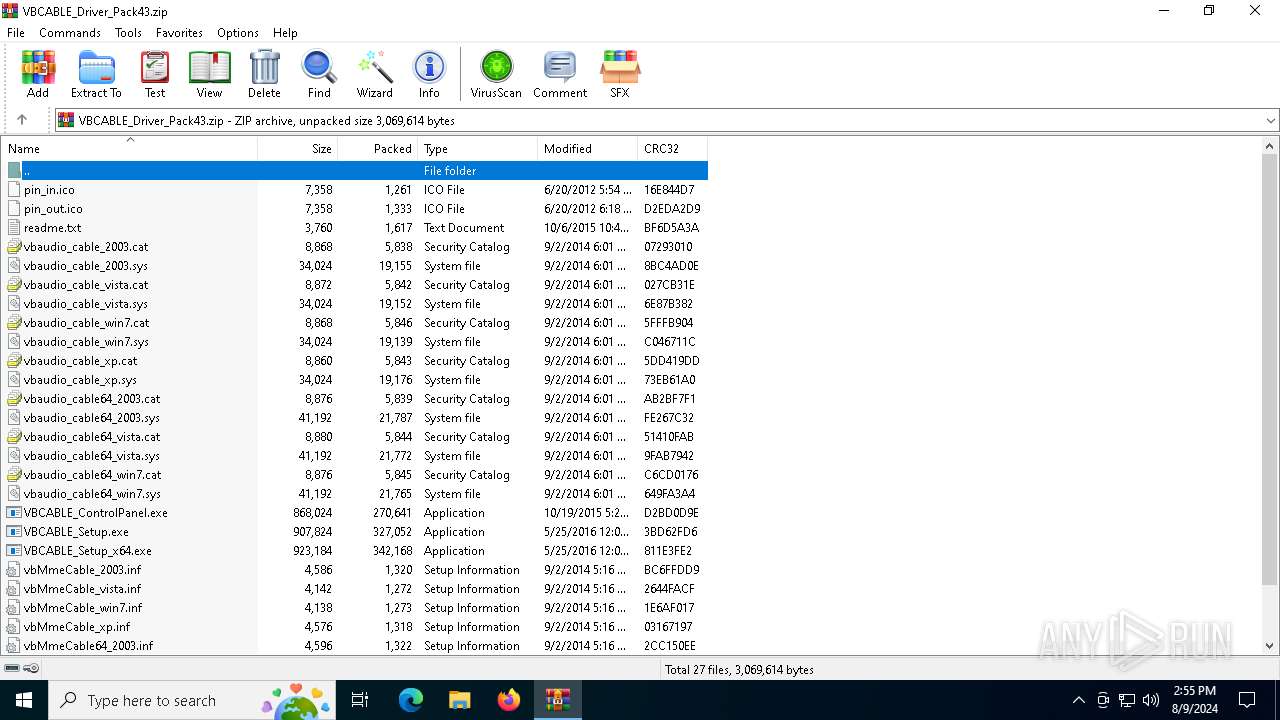
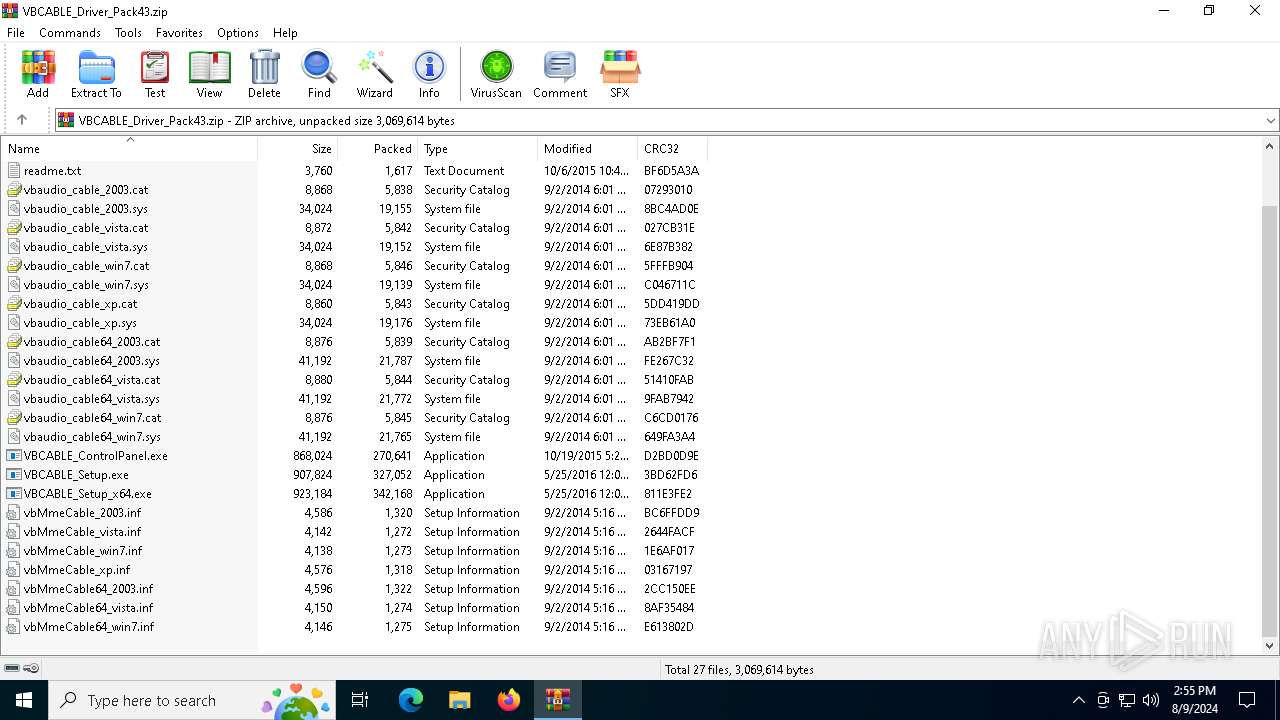
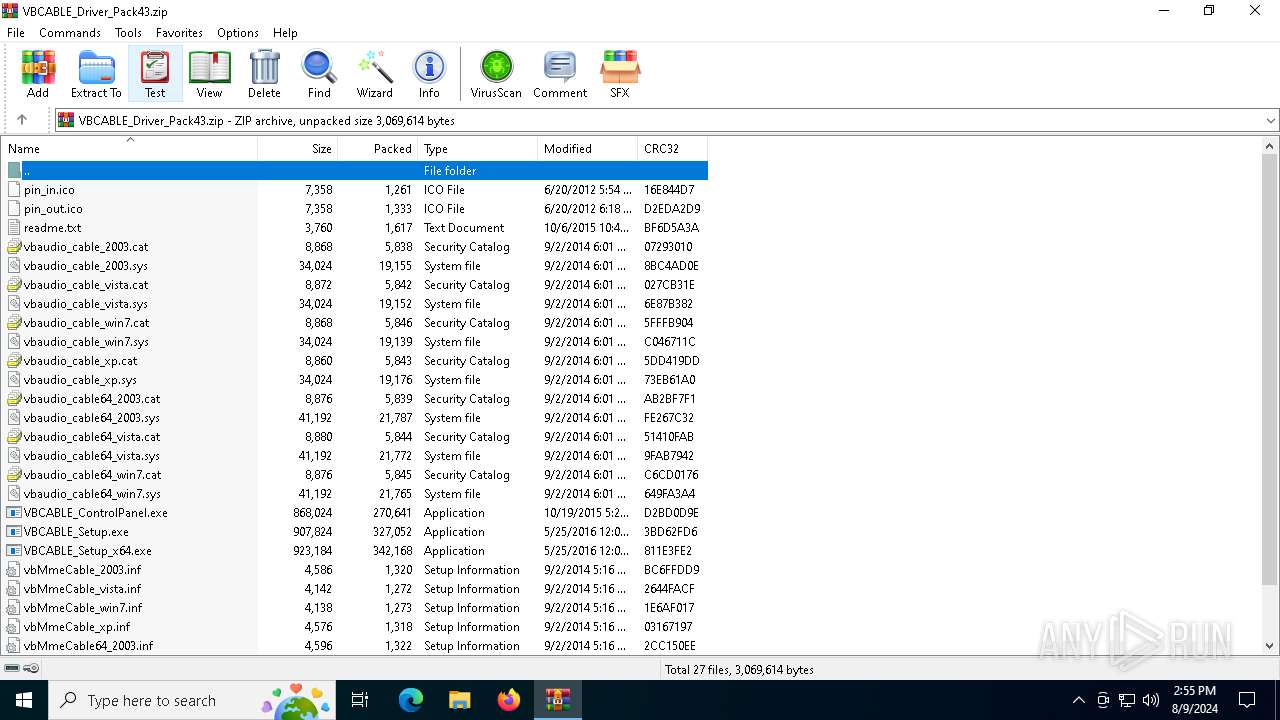
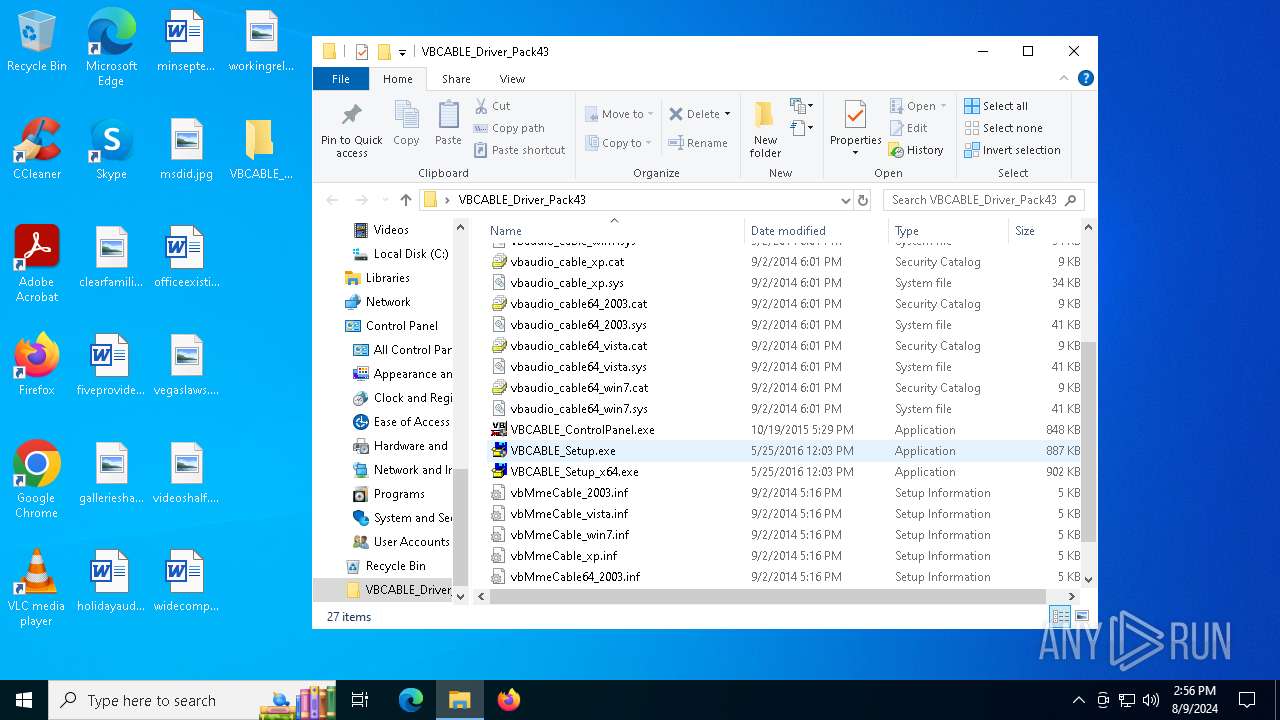
| File name: | VBCABLE_Driver_Pack43.zip |
| Full analysis: | https://app.any.run/tasks/ae0992ea-60cb-44dd-a2a1-f0d8ca8ad531 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2024, 14:55:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3E2F6DDF5A06C66DC4DAED708F8BB2A6 |
| SHA1: | 0FC70FD364B76B3DBDF6C9780369A834ED9EFD3E |
| SHA256: | 66FD0A4D9F4896FF41632B7E3D53892C085C4561F53E8AE8D0F0BC10EEDD1CDD |
| SSDEEP: | 24576:dqtBKwfPZ5JLfG/Dtl27gdahBUV1G7h4si2KRayG81atW8:dsKwZ5ZfG/Bo72aQVeh4siZaA4tW8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6460)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6460)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6460)
Checks supported languages
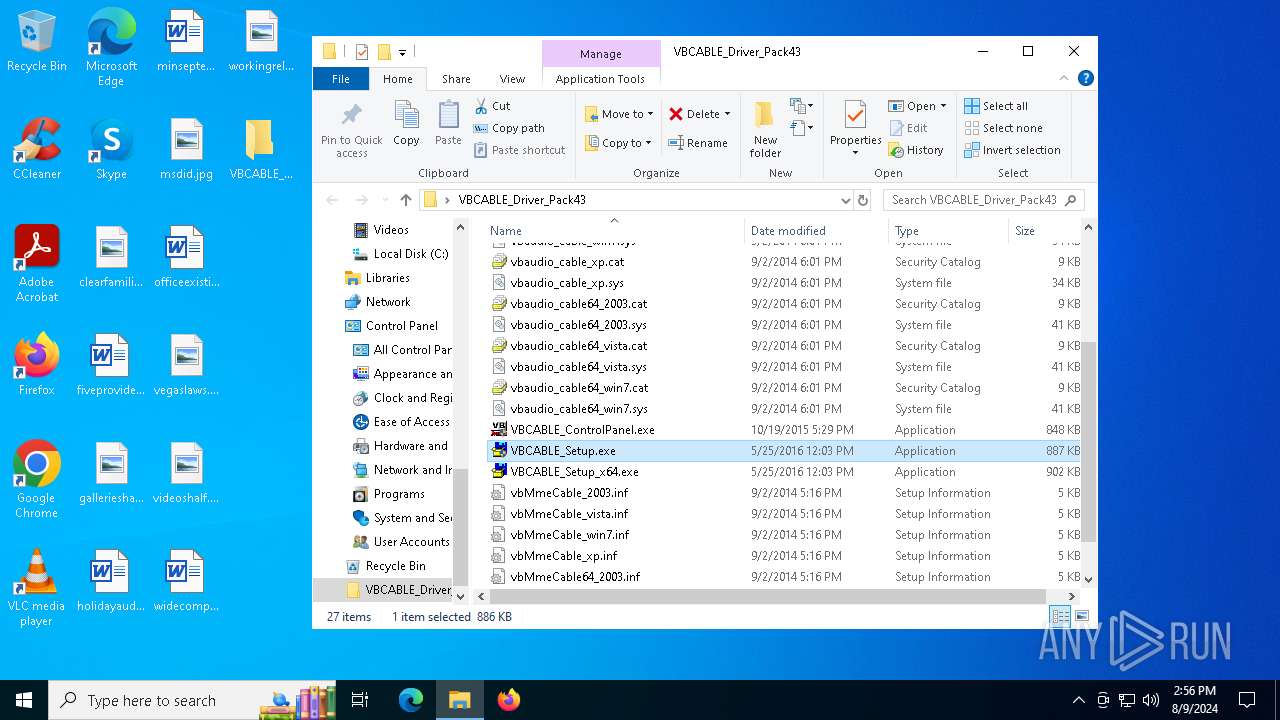
- VBCABLE_Setup.exe (PID: 4924)
Manual execution by a user
- VBCABLE_Setup.exe (PID: 6288)
- VBCABLE_Setup.exe (PID: 4924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:09:02 17:16:34 |
| ZipCRC: | 0xe613802d |
| ZipCompressedSize: | 1275 |
| ZipUncompressedSize: | 4146 |
| ZipFileName: | vbMmeCable64_win7.inf |
Total processes
136
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3372 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
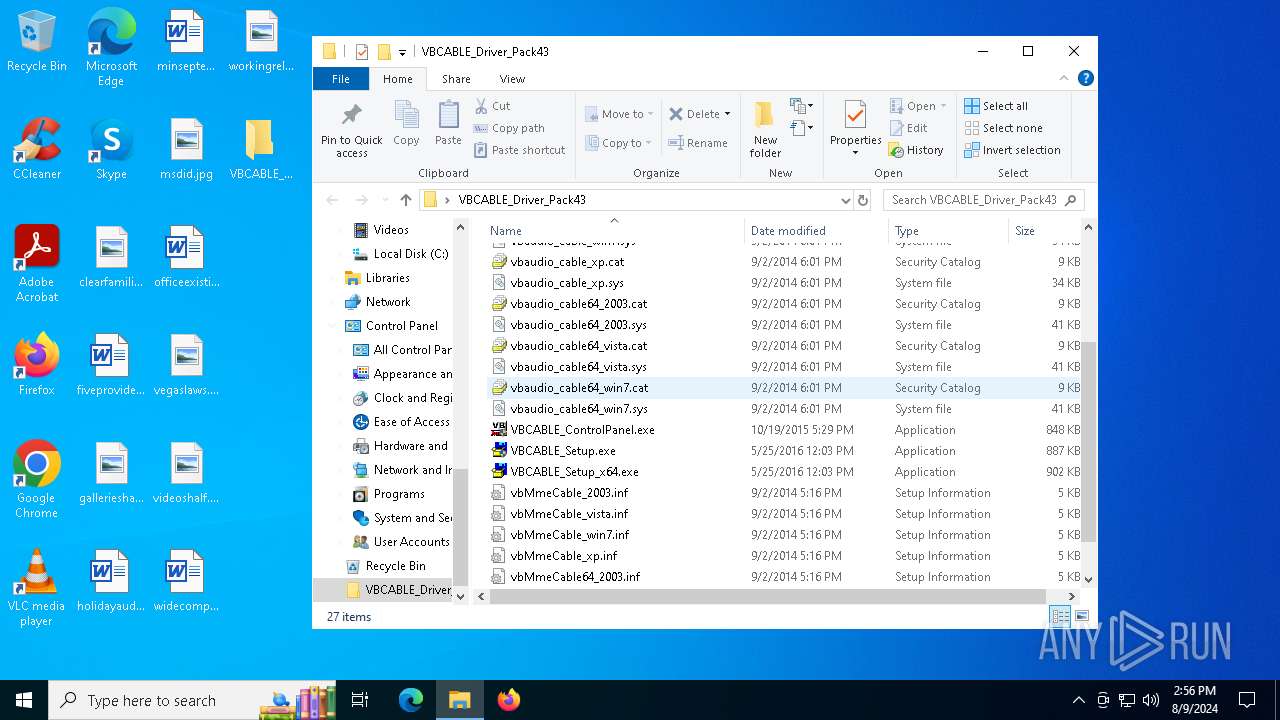
| 4924 | "C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\VBCABLE_Setup.exe" | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\VBCABLE_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: VB-AUDIO Software Integrity Level: HIGH Description: VB-AUDIO Virtual Cable Installer Exit code: 4294967295 Version: 1, 0, 3, 8 Modules
| |||||||||||||||
| 6288 | "C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\VBCABLE_Setup.exe" | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\VBCABLE_Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: VB-AUDIO Software Integrity Level: MEDIUM Description: VB-AUDIO Virtual Cable Installer Exit code: 3221226540 Version: 1, 0, 3, 8 Modules
| |||||||||||||||
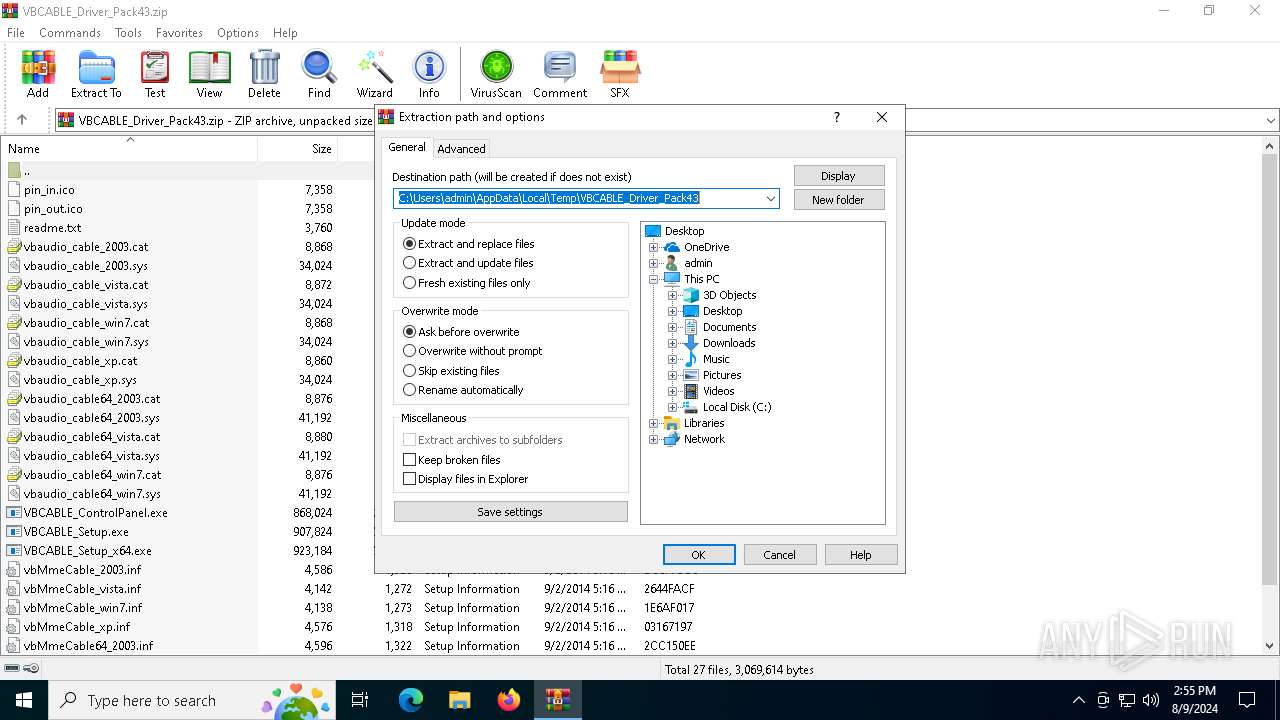
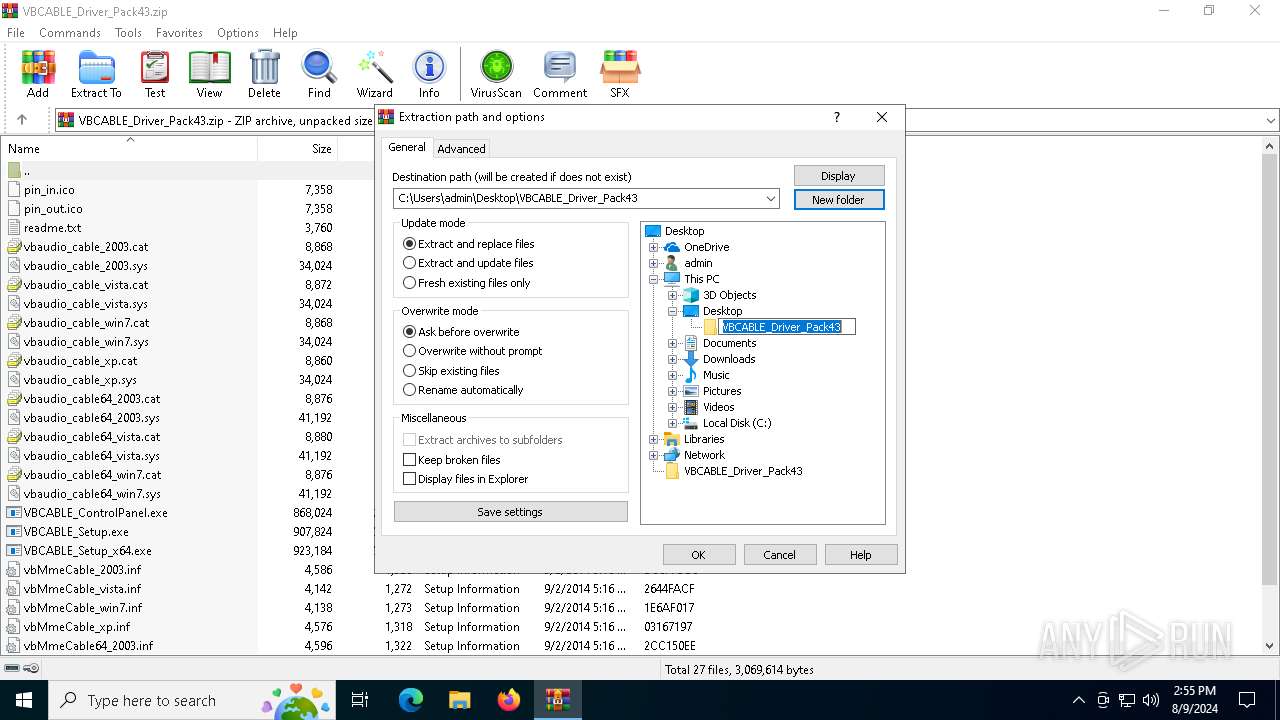
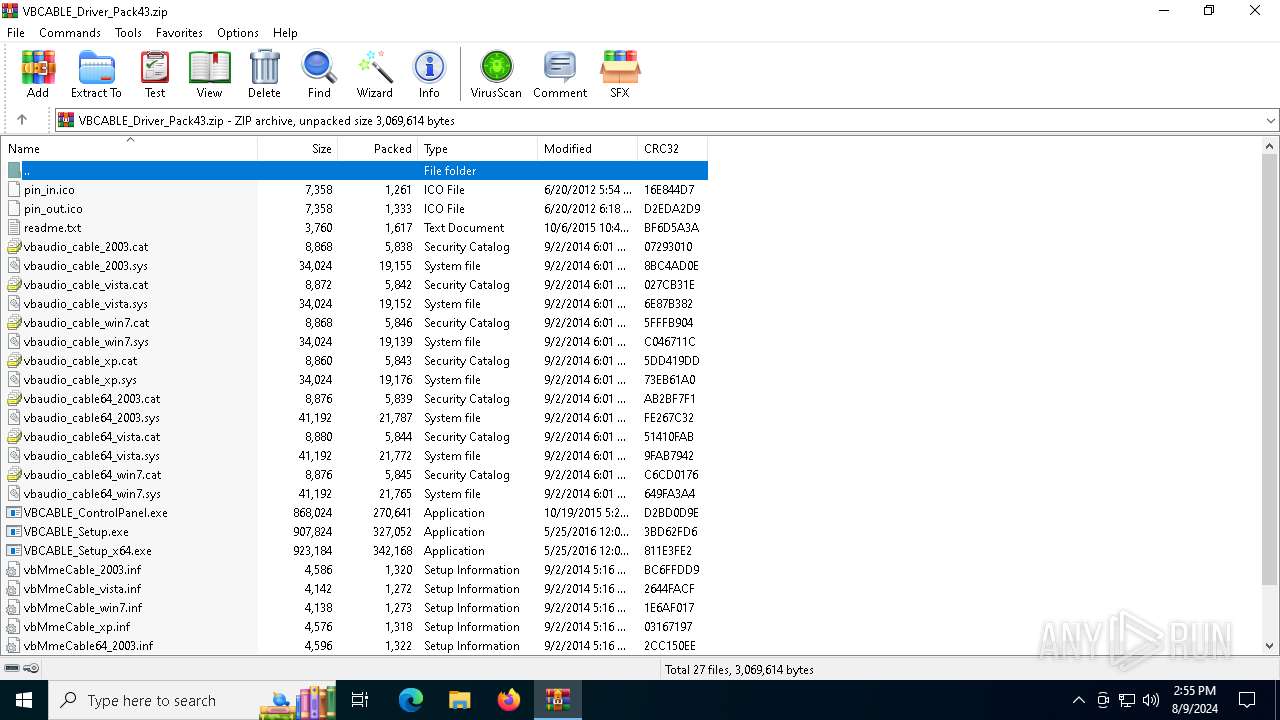
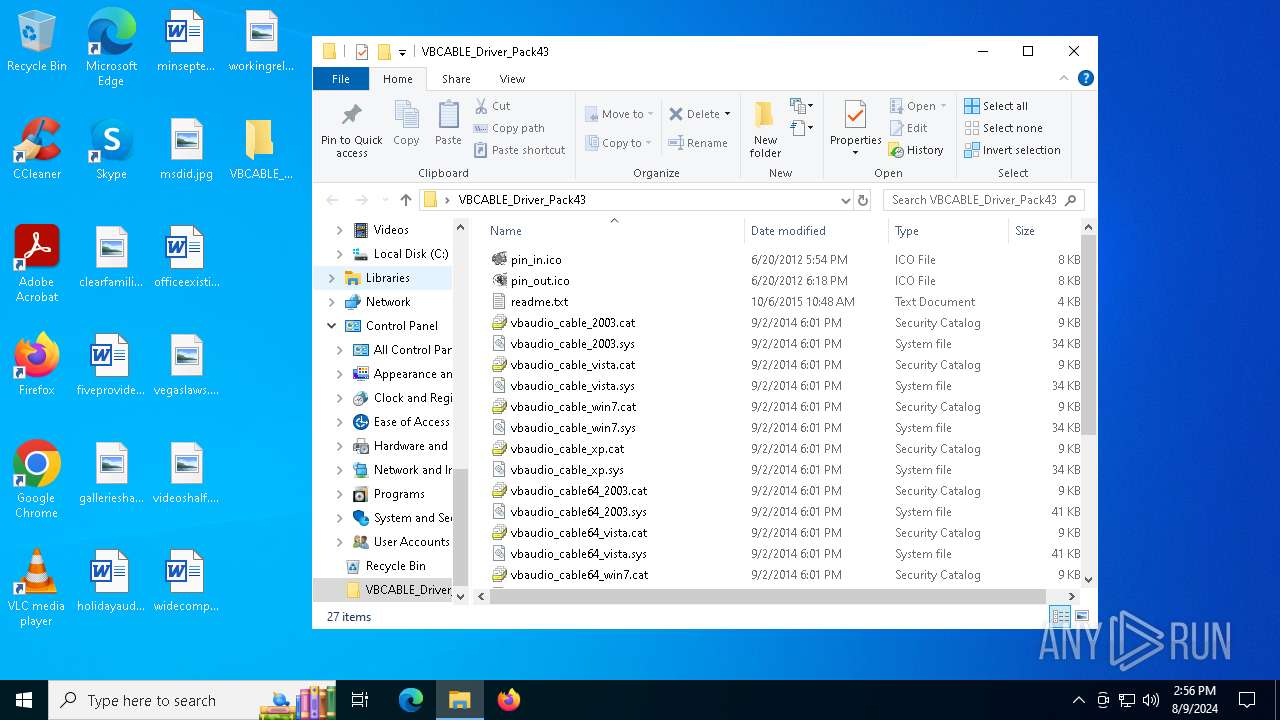
| 6460 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\VBCABLE_Driver_Pack43.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 941
Read events
5 921
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VBCABLE_Driver_Pack43.zip | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\VBCABLE_Driver_Pack43 | |||
| (PID) Process: | (6460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
10
Suspicious files
6
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable_vista.sys | executable | |
MD5:6CC2CE471671F7665BA15A177A3CCF10 | SHA256:8B02C26313B75CEB8FB9BD16B6B167CF70D7F3BC977DFC1986C0859F8C72B49F | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbMmeCable64_win7.inf | ini | |
MD5:498FAEE2DE63C1C428900920203FDF9B | SHA256:DA35387CCFE813F5C553BB7E0CAF4E67ADBB4429E742C2BD3C2014F80E6EC516 | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\pin_out.ico | image | |
MD5:235559DE67569EBC8FDCF5D51D753B57 | SHA256:E8728A811E1F1AF7D2BA31F77E47D449D5BBA091E3E89A0DF325AC7A3E67652C | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable_2003.cat | cat | |
MD5:F3D83B61A6ECCE5DC90687496AABA335 | SHA256:23A10E3BCD6FFE0DE6D3D67830BE4C447724B3299E13E954DD6BD2257CF55DA1 | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable_vista.cat | cat | |
MD5:40401678D0272A448795432615F8B762 | SHA256:810B30193A400B1559302C23F81EF8AAADF038B3CAF3AFF9BF200B59688A2DEF | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable_win7.cat | cat | |
MD5:9CC8F7A387484C49A6F1296586CD1DDB | SHA256:1C38AFACF115818C925BC26FAF216E3563E85BBC4D6D793E5F76F2AA670D08E7 | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable_win7.sys | executable | |
MD5:F23A66967591AEA2B8840F02B3DA993A | SHA256:D047E3EE66E3EE023E598232EA22AA28DBB39ADEABE818ADFB2A72AB738DF0B9 | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable64_2003.cat | cat | |
MD5:1A938E376ABA87FD3D4285A261146923 | SHA256:70F88E34C857C999367EB5B0303E23F5676B15A79ED4054F374749232BAA0E3A | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable64_2003.sys | executable | |
MD5:326FAB289623BCF815C38FCD71330F3B | SHA256:5A726F3F1616F587C9F118BF337FD359DF3F7CB9FC967A14229D59A31F2A9720 | |||
| 6460 | WinRAR.exe | C:\Users\admin\Desktop\VBCABLE_Driver_Pack43\vbaudio_cable_xp.sys | executable | |
MD5:37B9BA59092ADFC1CA318A29D94F9D4E | SHA256:9F9BC80A96CC94C761887749E51D9B4FB7EE6741CE624B8B2F9F85CD2E3FB02E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6764 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1984 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 2.16.110.170:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3376 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |