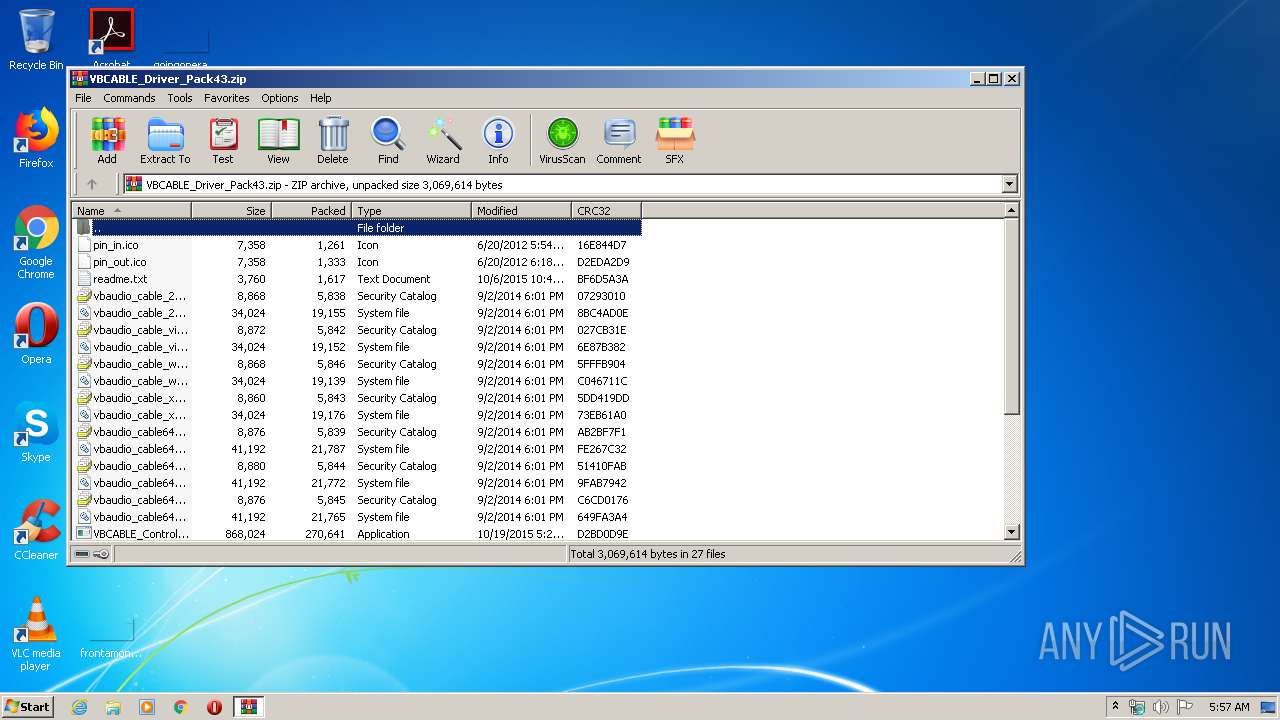
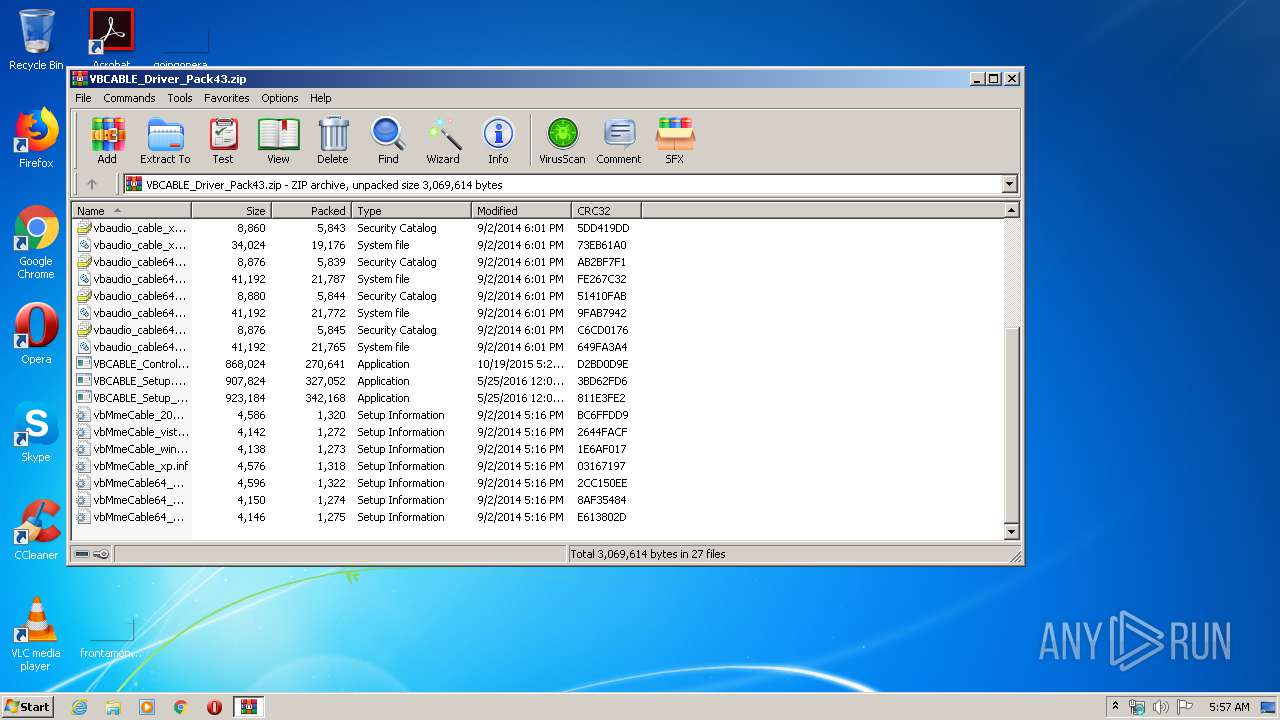
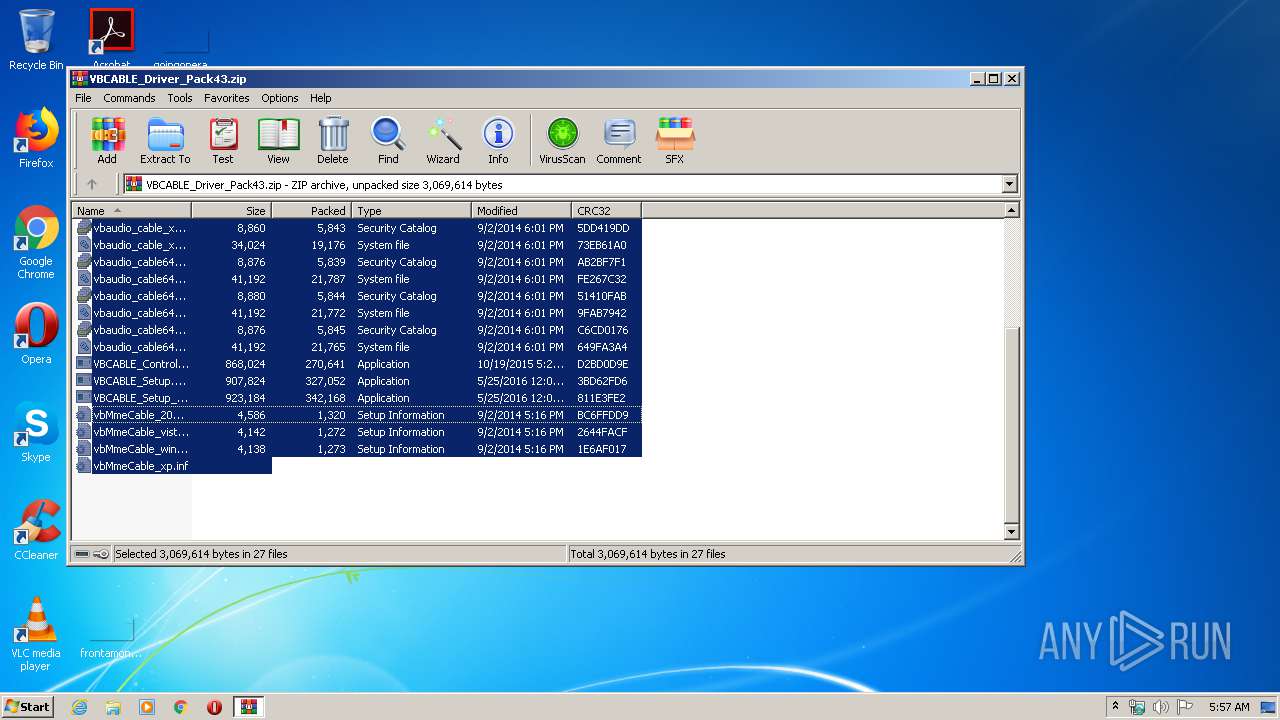
| File name: | VBCABLE_Driver_Pack43.zip |
| Full analysis: | https://app.any.run/tasks/a243b998-c318-4606-9c79-e144c379f819 |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2020, 04:57:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3E2F6DDF5A06C66DC4DAED708F8BB2A6 |
| SHA1: | 0FC70FD364B76B3DBDF6C9780369A834ED9EFD3E |
| SHA256: | 66FD0A4D9F4896FF41632B7E3D53892C085C4561F53E8AE8D0F0BC10EEDD1CDD |
| SSDEEP: | 24576:dqtBKwfPZ5JLfG/Dtl27gdahBUV1G7h4si2KRayG81atW8:dsKwZ5ZfG/Bo72aQVeh4siZaA4tW8 |
MALICIOUS
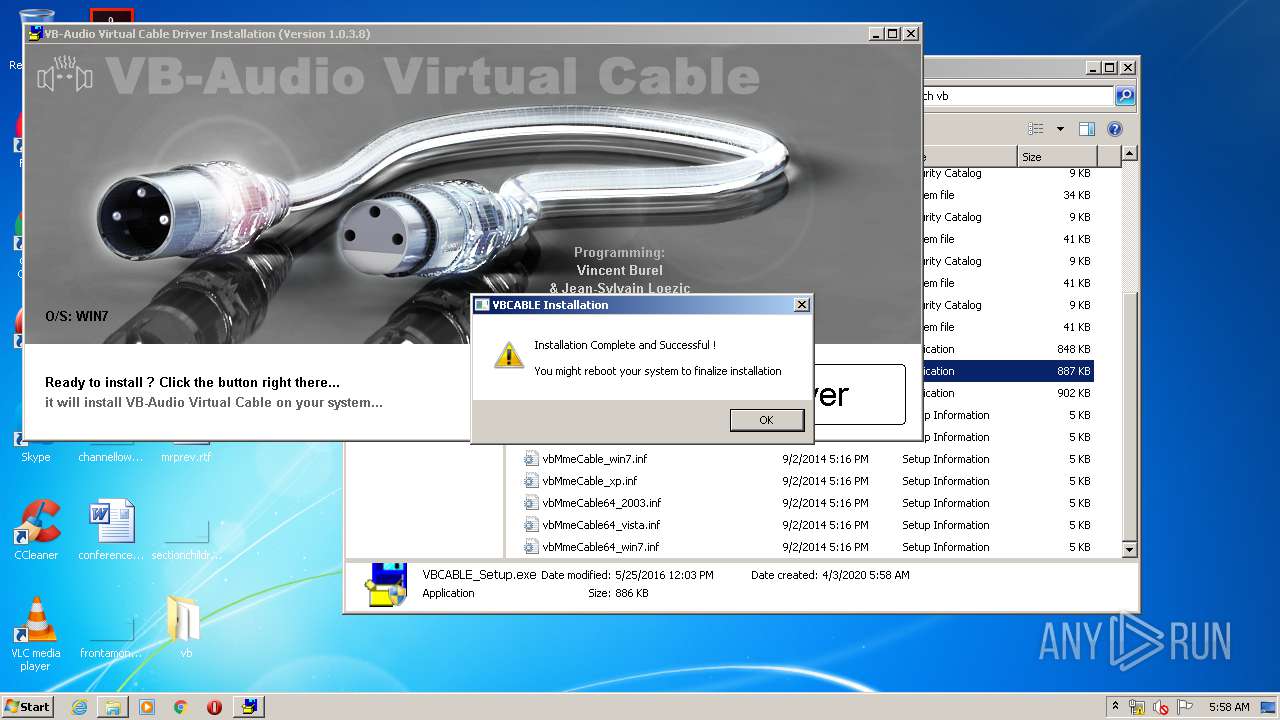
Application was dropped or rewritten from another process
- VBCABLE_Setup.exe (PID: 1028)
- VBCABLE_Setup.exe (PID: 3968)
- VBCABLE_ControlPanel.exe (PID: 3544)
- VBCABLE_ControlPanel.exe (PID: 1268)
Changes settings of System certificates
- VBCABLE_Setup.exe (PID: 3968)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3312)
- VBCABLE_Setup.exe (PID: 3968)
- DrvInst.exe (PID: 3608)
- DrvInst.exe (PID: 2520)
Removes files from Windows directory
- DrvInst.exe (PID: 3608)
- DrvInst.exe (PID: 2520)
Executed as Windows Service
- vssvc.exe (PID: 2892)
Executed via COM
- DrvInst.exe (PID: 2520)
- DrvInst.exe (PID: 3608)
Creates files in the Windows directory
- DrvInst.exe (PID: 3608)
- DrvInst.exe (PID: 2520)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3608)
Creates files in the driver directory
- DrvInst.exe (PID: 3608)
- DrvInst.exe (PID: 2520)
Creates files in the program directory
- VBCABLE_Setup.exe (PID: 3968)
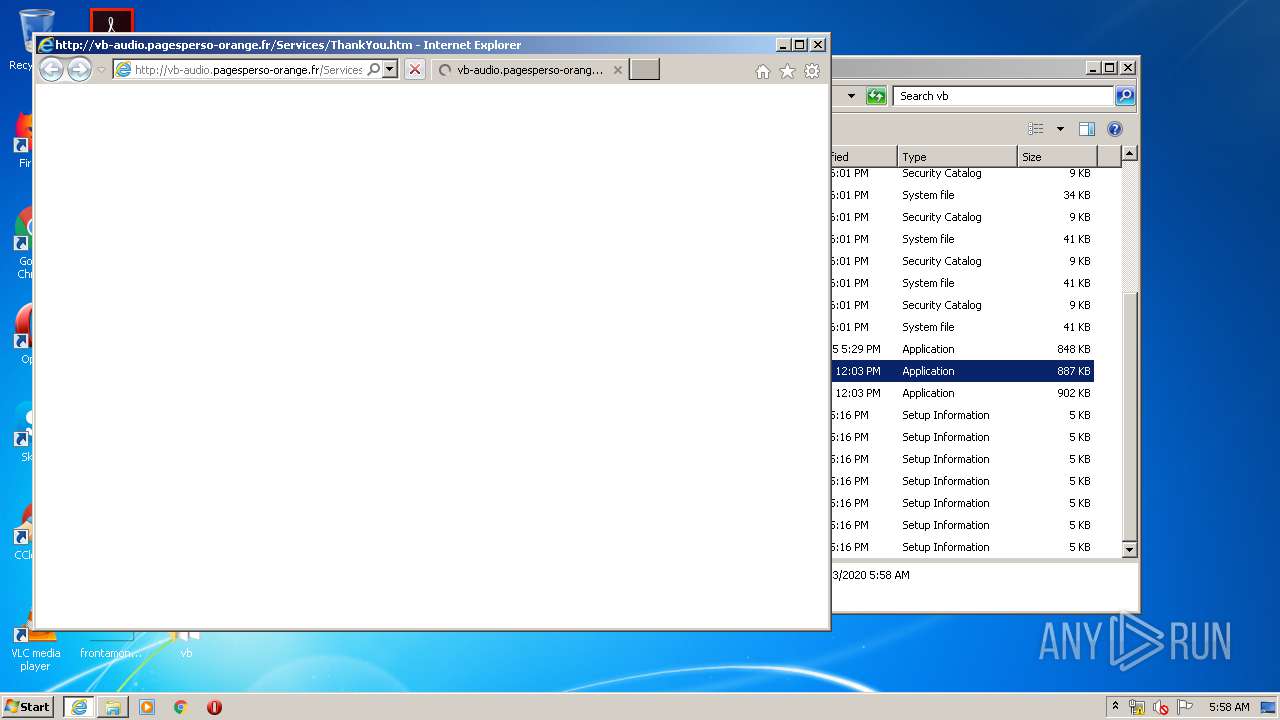
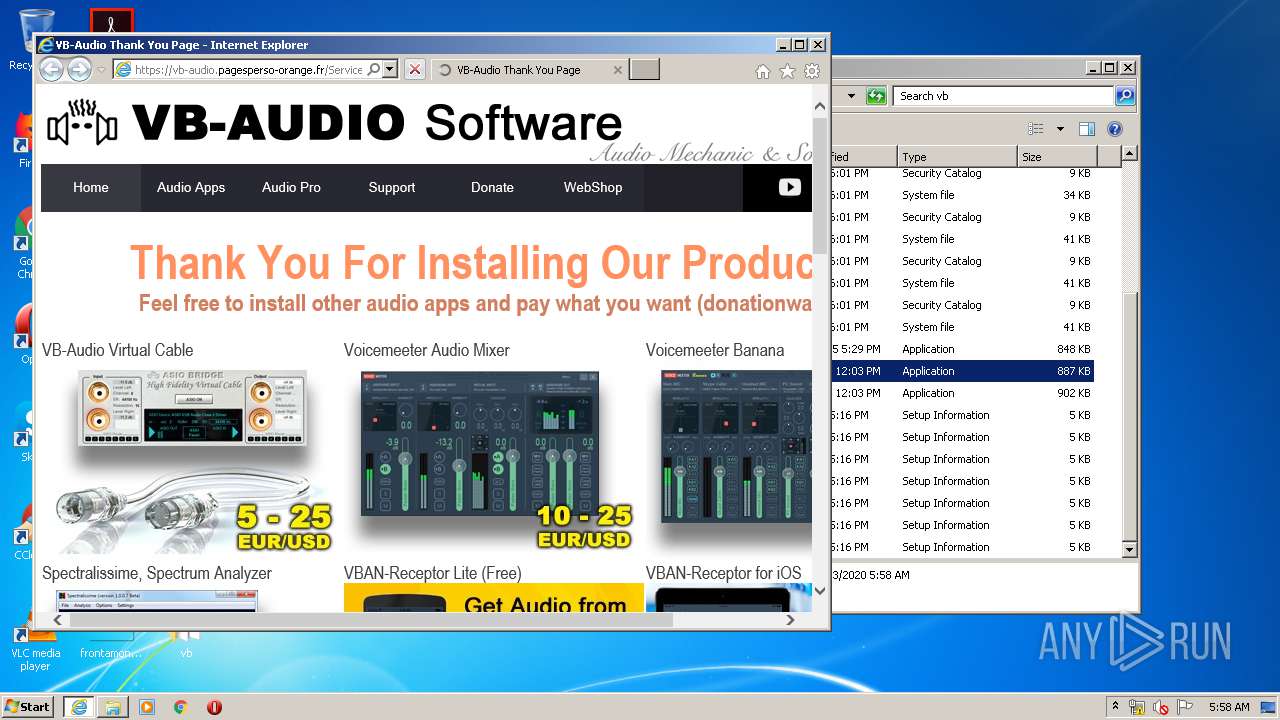
Starts Internet Explorer
- VBCABLE_Setup.exe (PID: 3968)
Creates a software uninstall entry
- VBCABLE_Setup.exe (PID: 3968)
Application launched itself
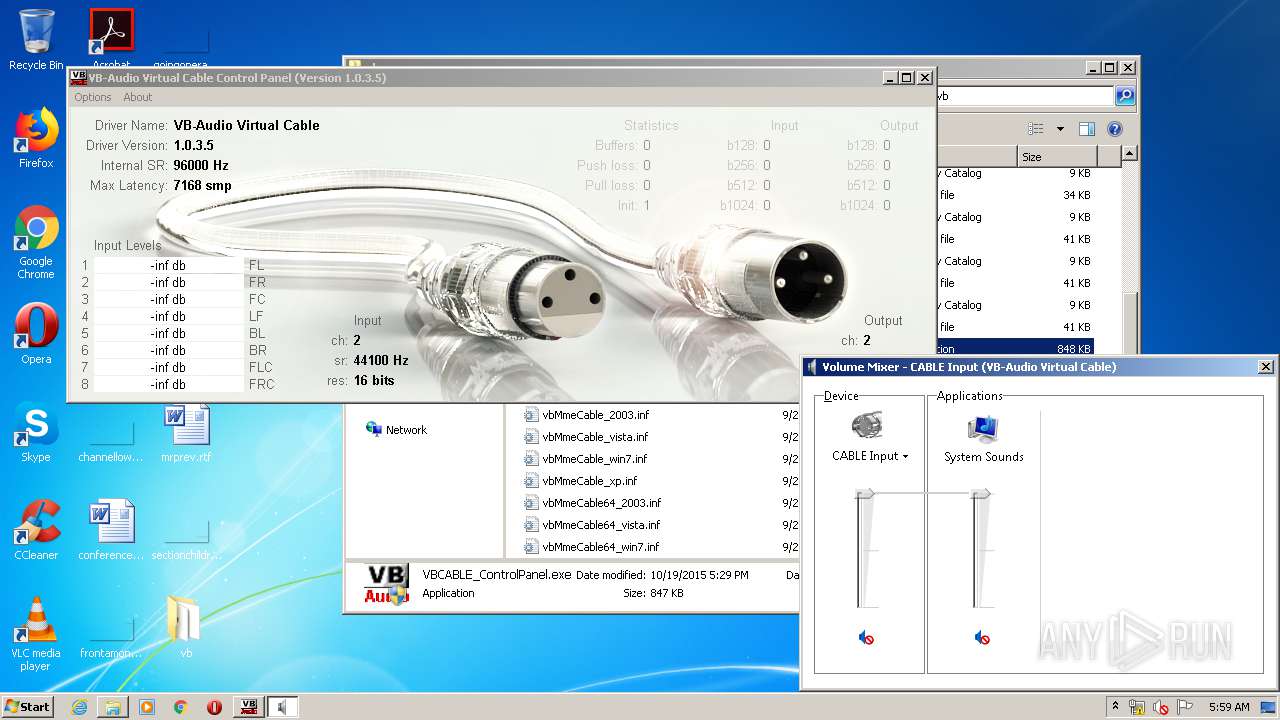
- SndVol.exe (PID: 4032)
Adds / modifies Windows certificates
- VBCABLE_Setup.exe (PID: 3968)
INFO
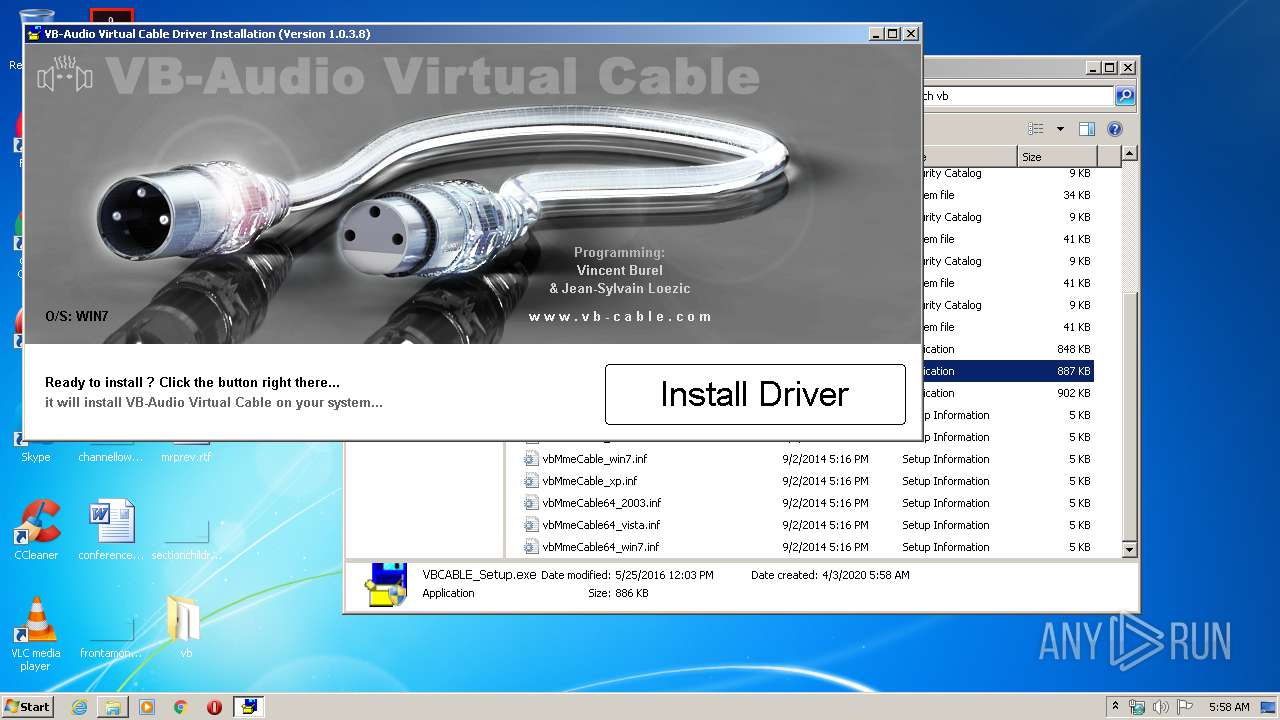
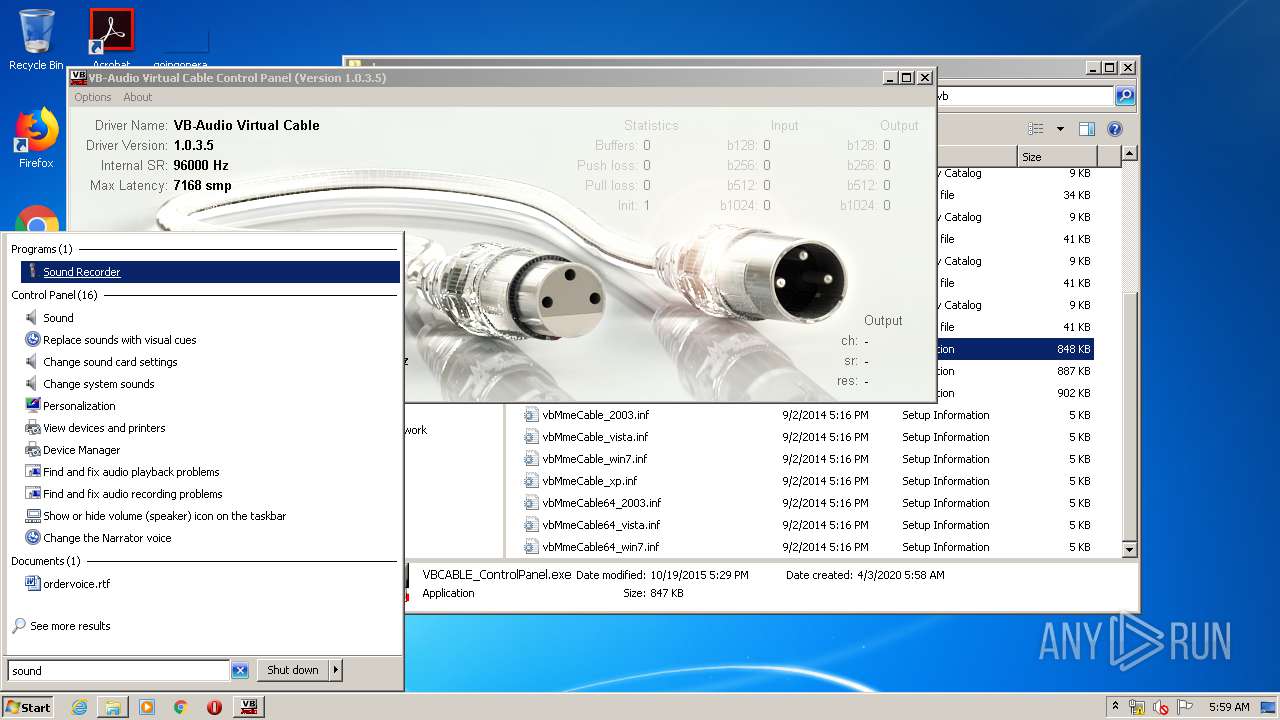
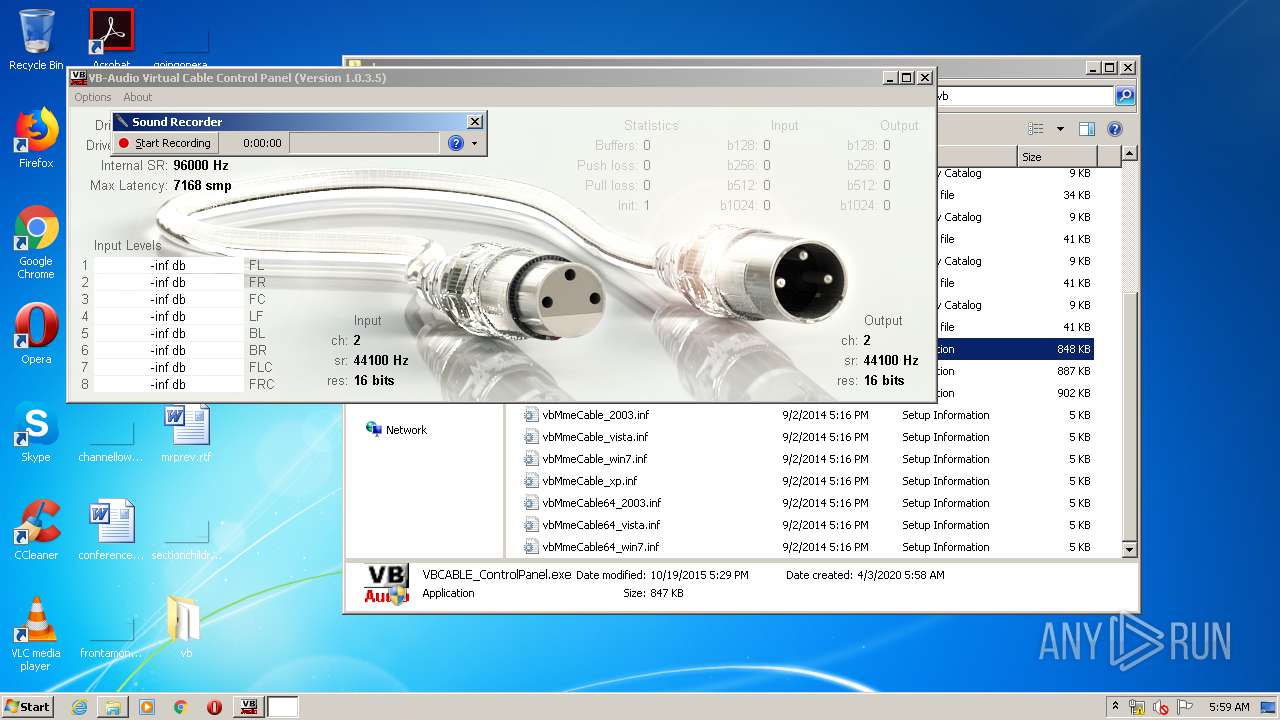
Manual execution by user
- VBCABLE_Setup.exe (PID: 3968)
- VBCABLE_Setup.exe (PID: 1028)
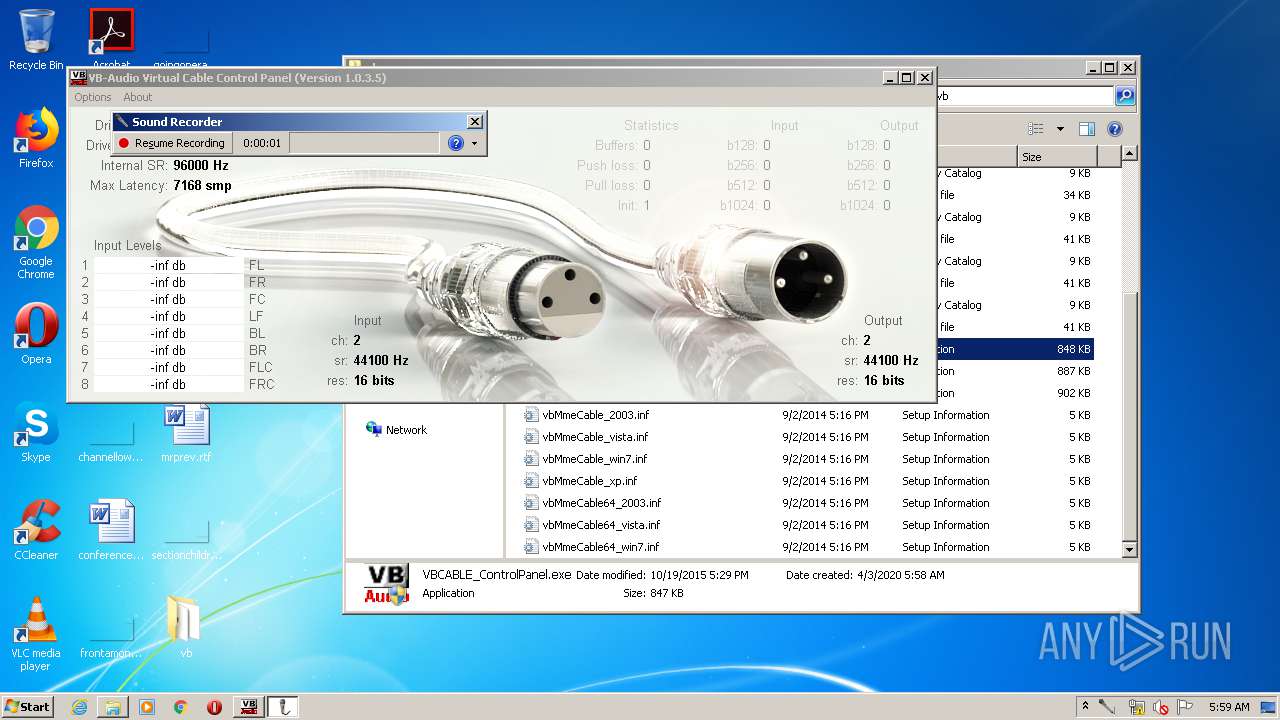
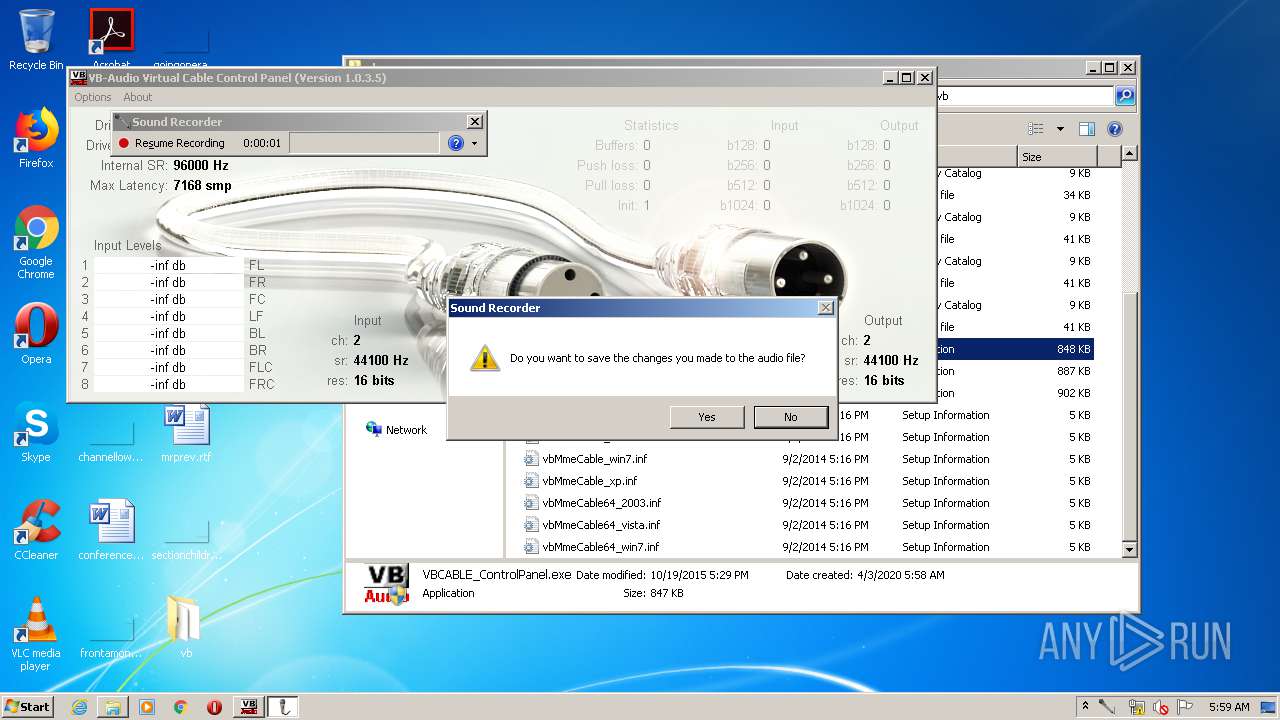
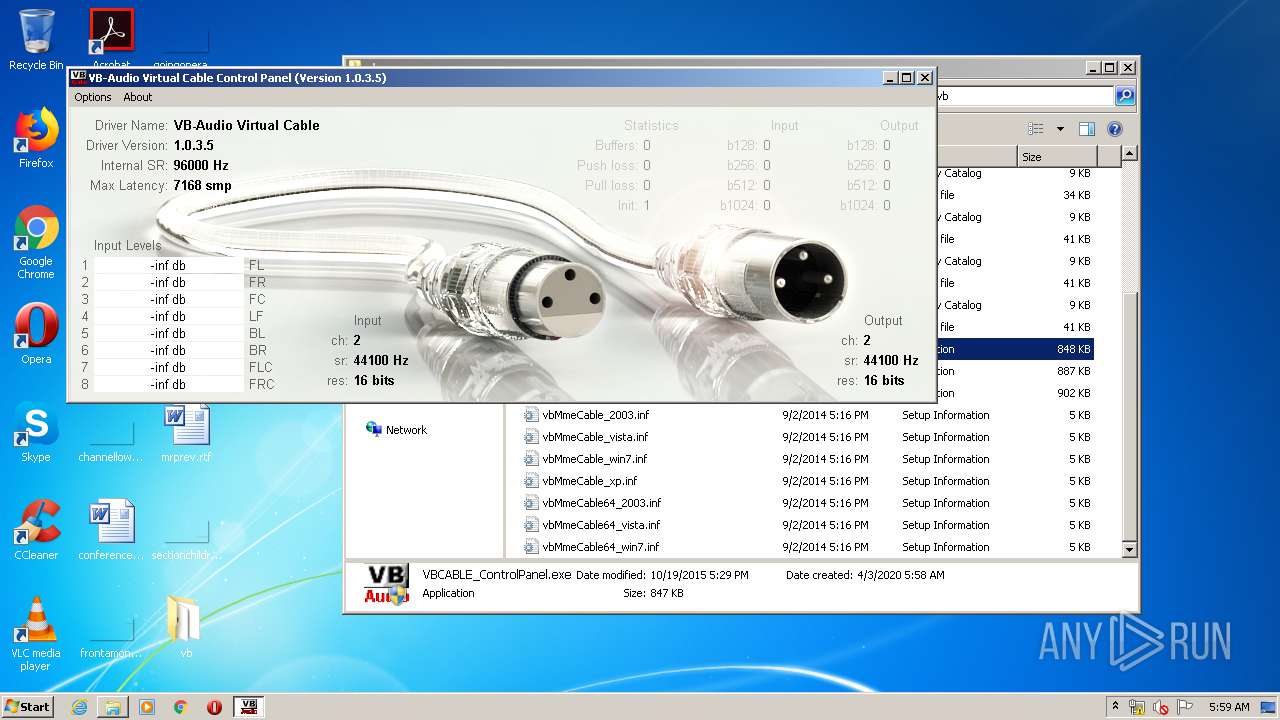
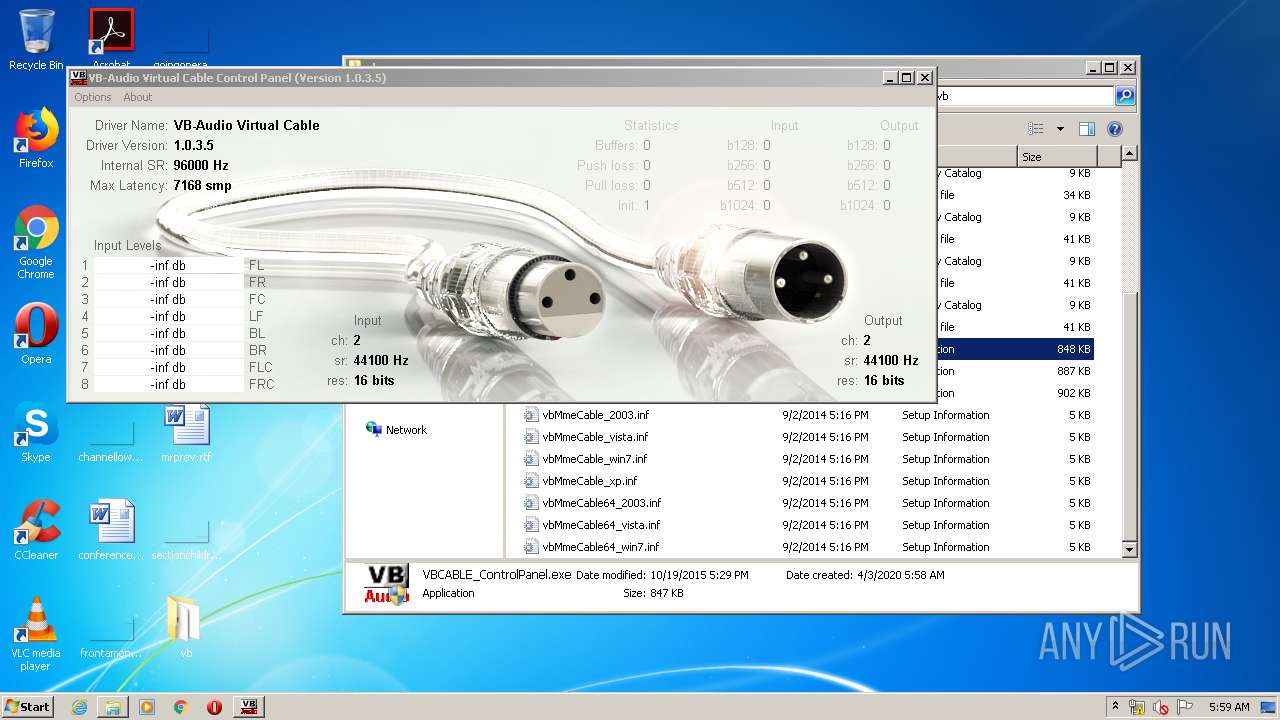
- VBCABLE_ControlPanel.exe (PID: 1268)
- VBCABLE_ControlPanel.exe (PID: 3544)
- SndVol.exe (PID: 4032)
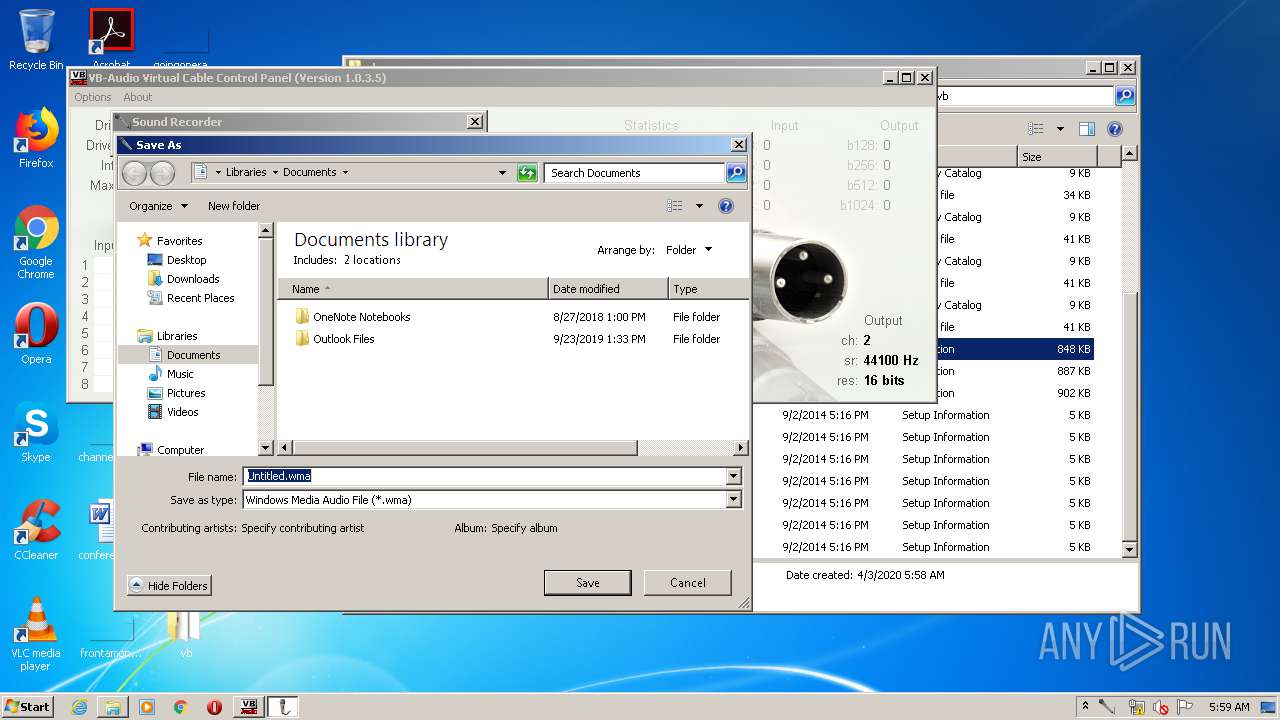
- SoundRecorder.exe (PID: 4040)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3312)
- VBCABLE_Setup.exe (PID: 3968)
Reads settings of System Certificates
- VBCABLE_Setup.exe (PID: 3968)
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 2492)
Searches for installed software
- DrvInst.exe (PID: 3608)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2892)
Reads Internet Cache Settings
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 3456)
Changes internet zones settings
- iexplore.exe (PID: 2492)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 2492)
Changes settings of System certificates
- iexplore.exe (PID: 3456)
- iexplore.exe (PID: 2492)
Creates files in the user directory
- iexplore.exe (PID: 3456)
Reads internet explorer settings
- iexplore.exe (PID: 3456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:09:02 17:16:17 |
| ZipCRC: | 0xe613802d |
| ZipCompressedSize: | 1275 |
| ZipUncompressedSize: | 4146 |
| ZipFileName: | vbMmeCable64_win7.inf |
Total processes
60
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
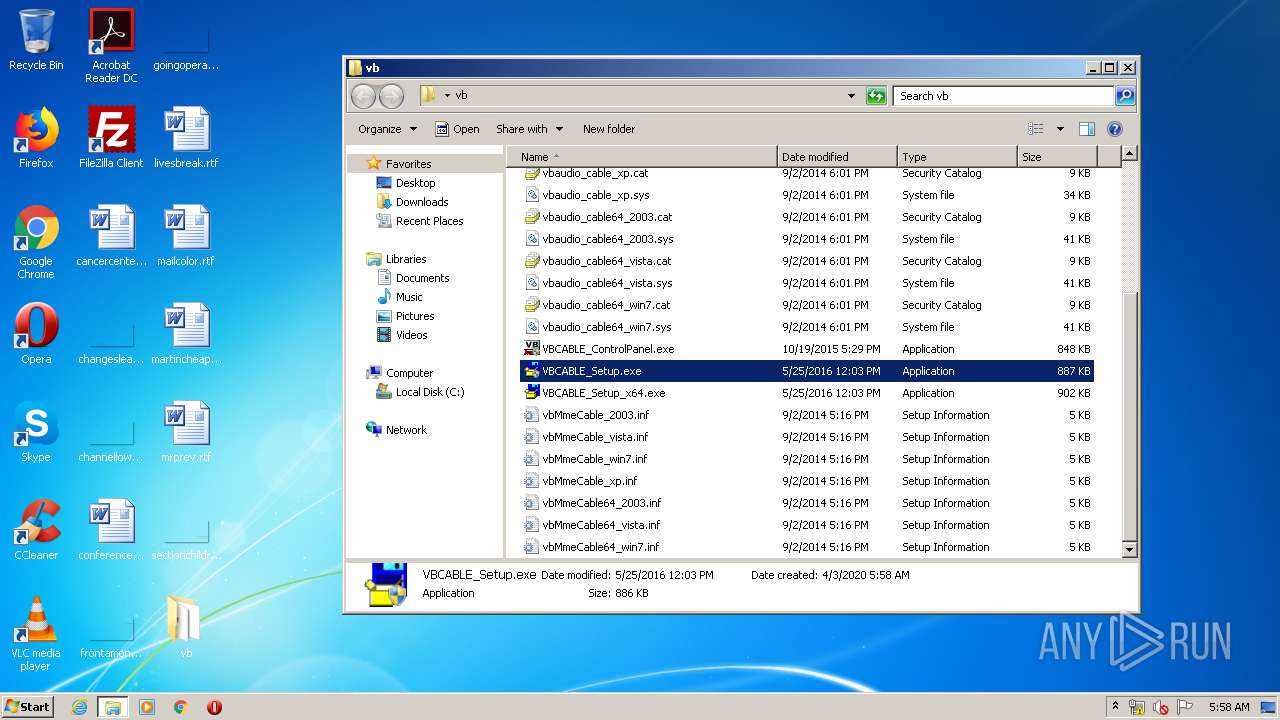
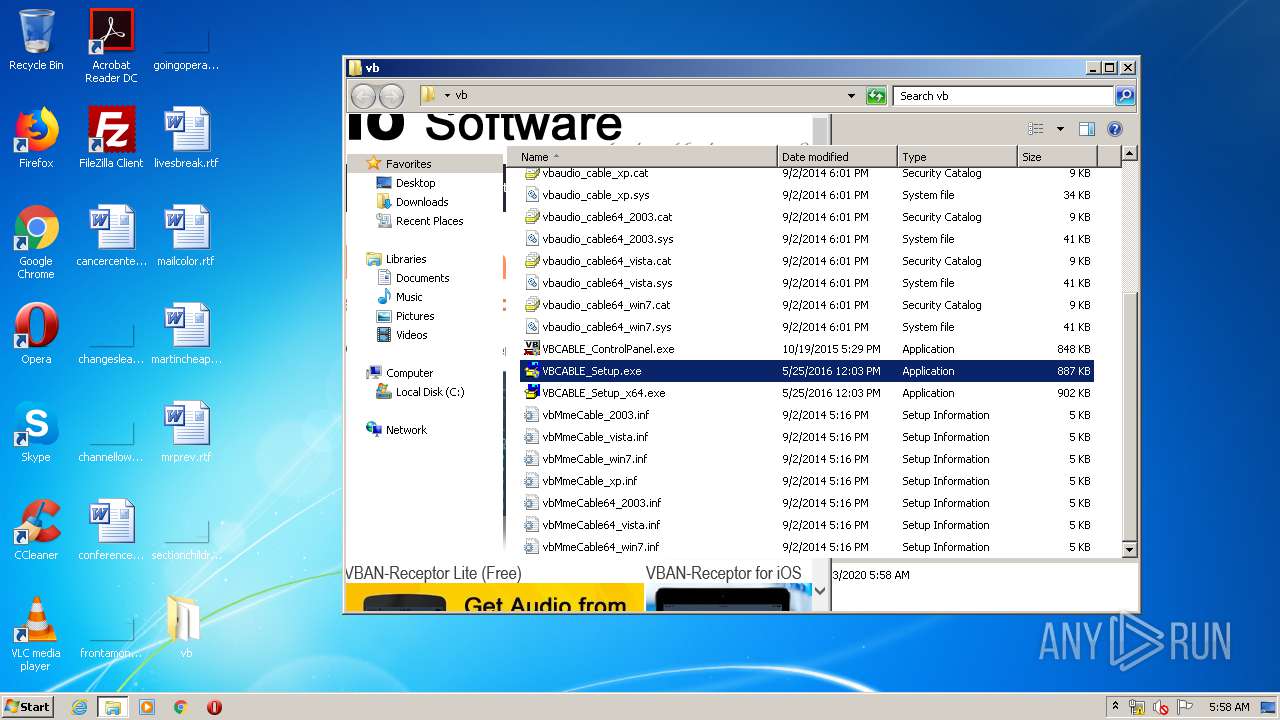
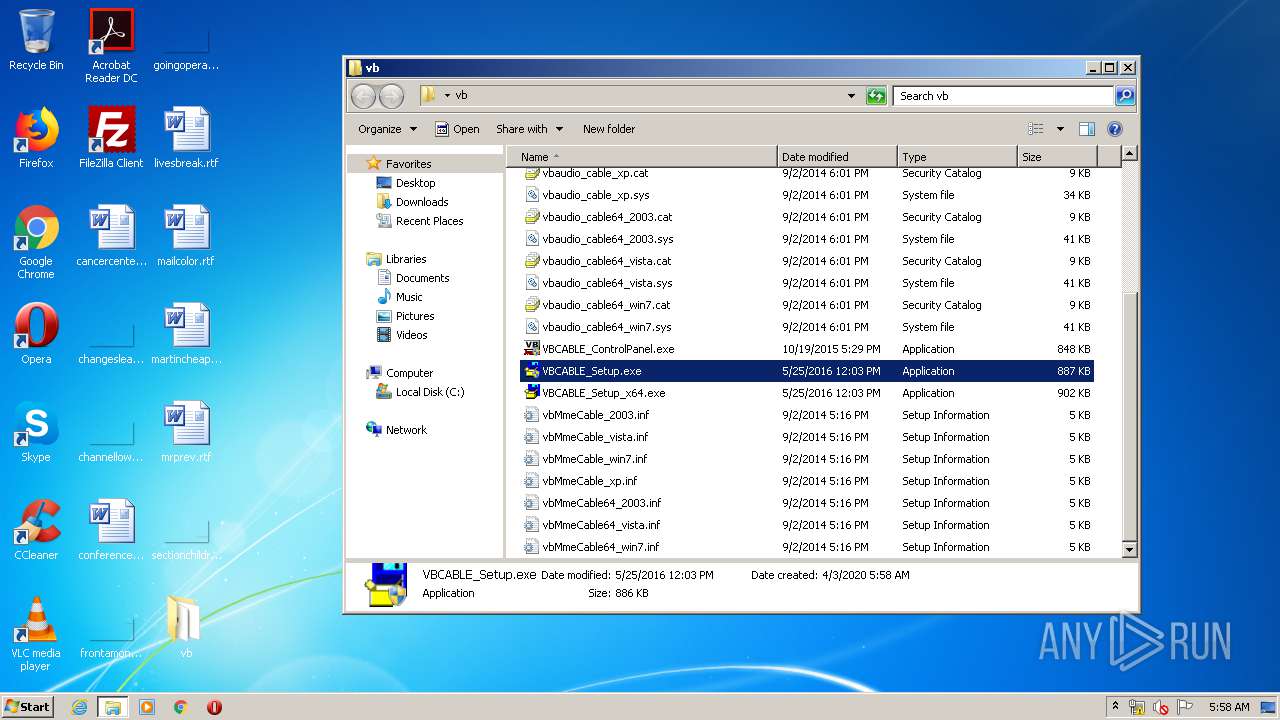
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
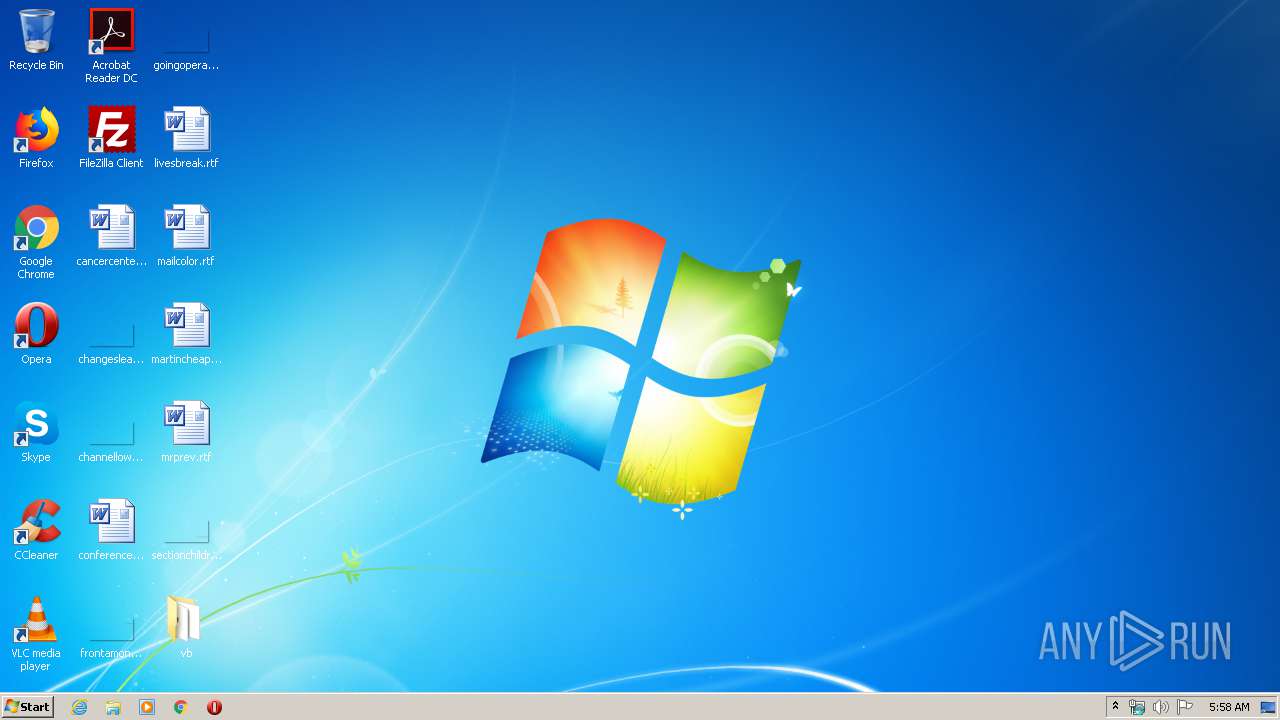
| 1028 | "C:\Users\admin\Desktop\vb\VBCABLE_Setup.exe" | C:\Users\admin\Desktop\vb\VBCABLE_Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: VB-AUDIO Software Integrity Level: MEDIUM Description: VB-AUDIO Virtual Cable Installer Exit code: 3221226540 Version: 1, 0, 3, 8 Modules
| |||||||||||||||
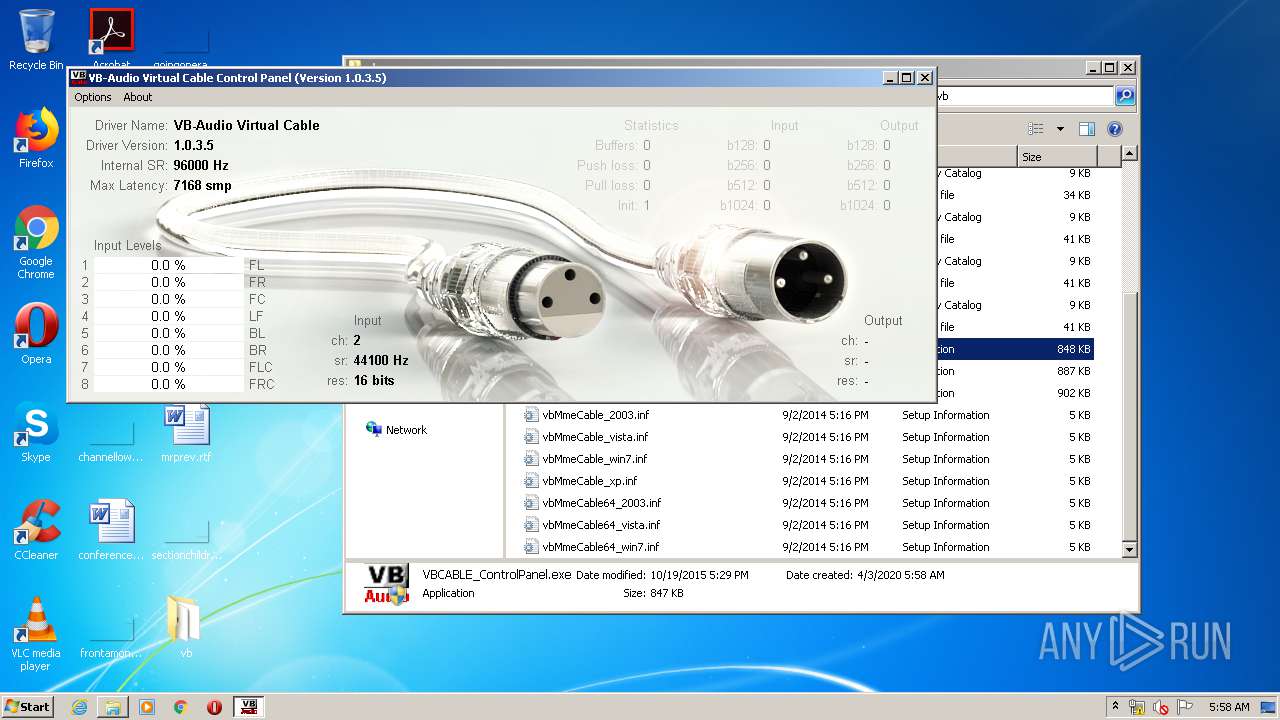
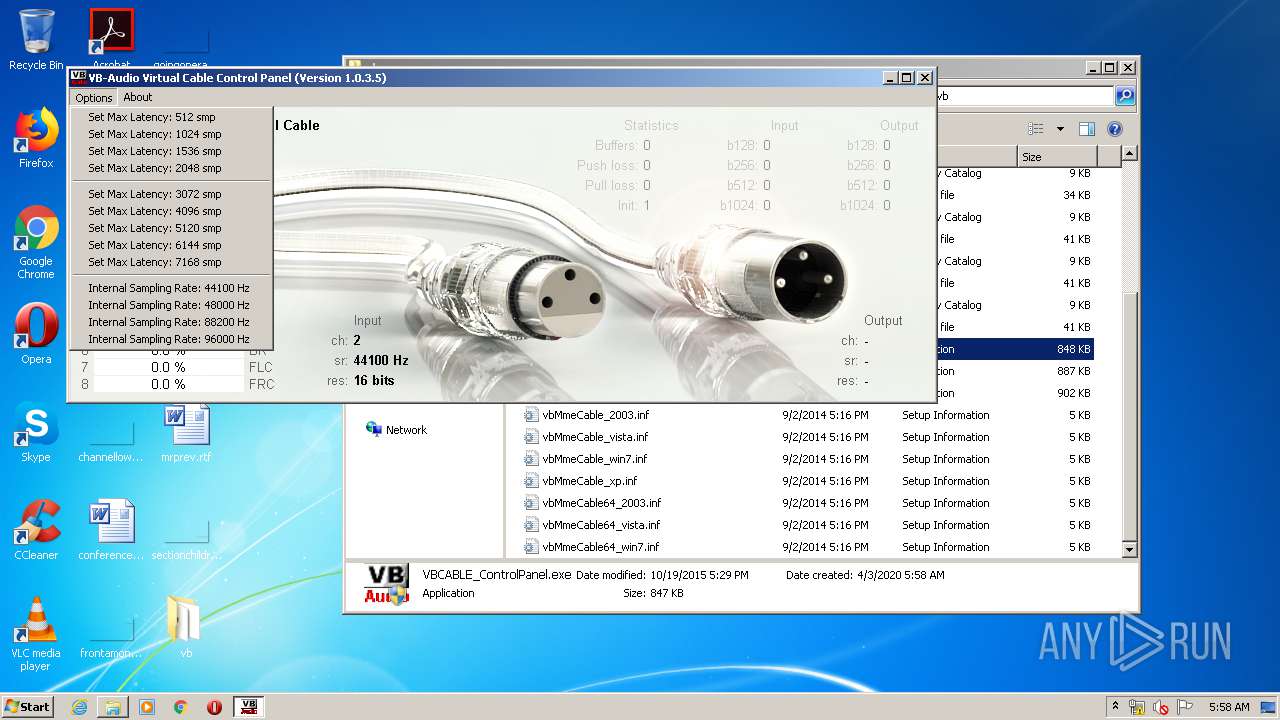
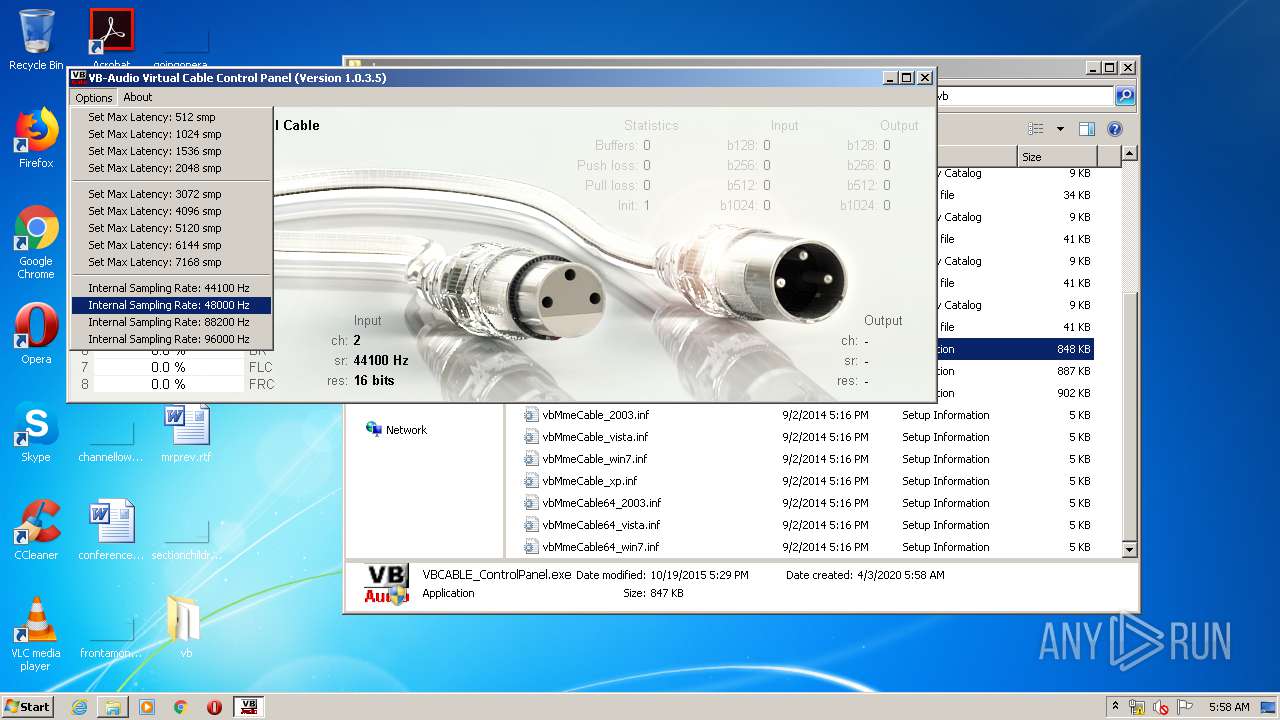
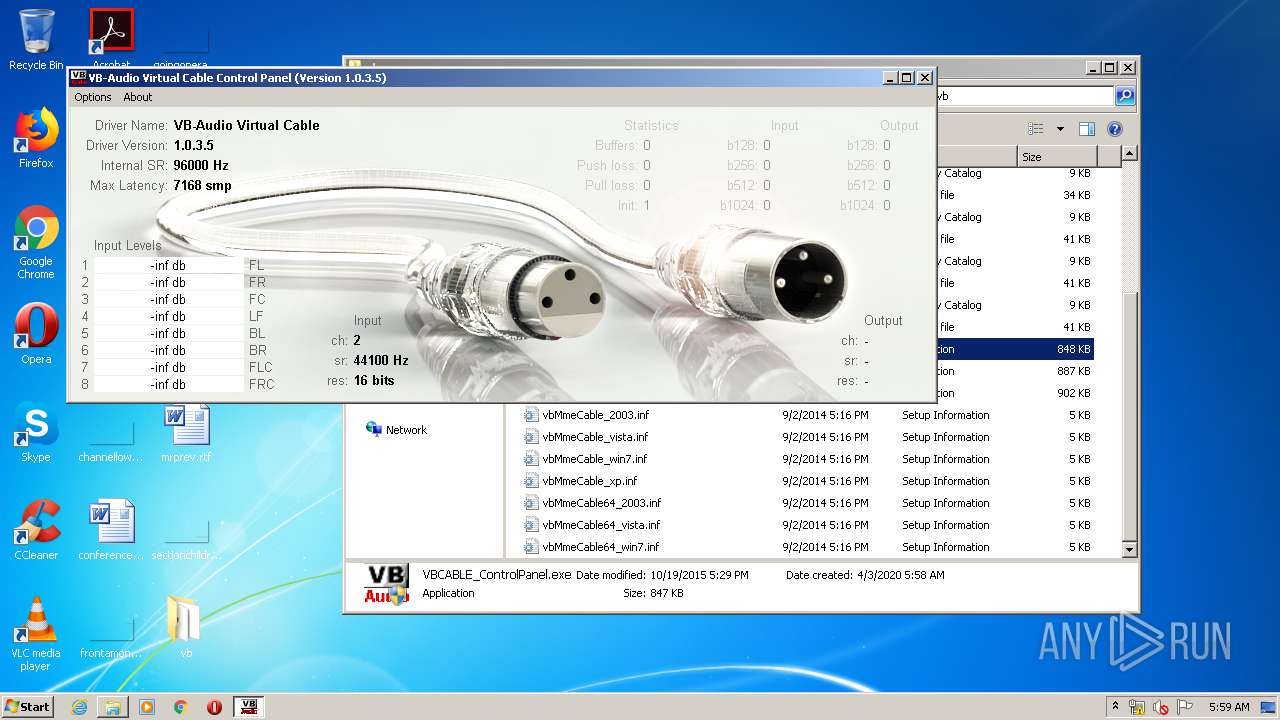
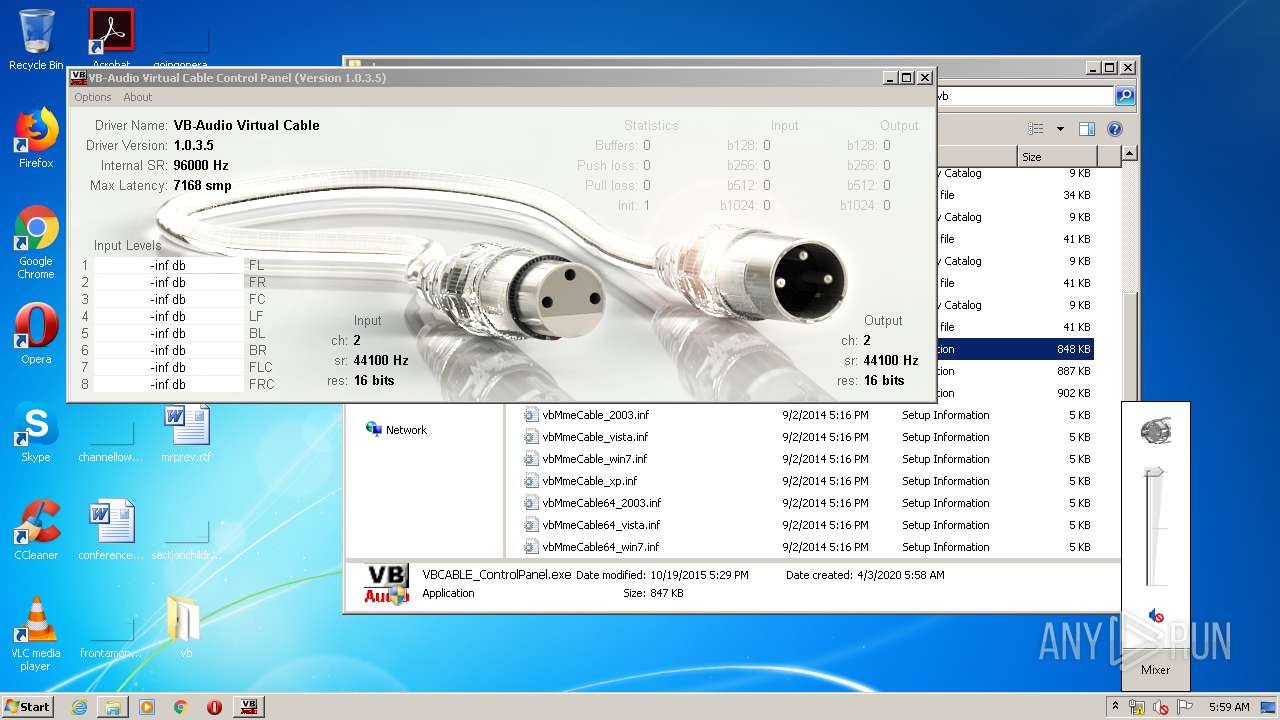
| 1268 | "C:\Users\admin\Desktop\vb\VBCABLE_ControlPanel.exe" | C:\Users\admin\Desktop\vb\VBCABLE_ControlPanel.exe | explorer.exe | ||||||||||||
User: admin Company: VB-AUDIO Software Integrity Level: HIGH Description: VB-AUDIO Virtual Cable Control Panel Exit code: 0 Version: 1, 0, 3, 5 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" http://vb-audio.pagesperso-orange.fr/Services/ThankYou.htm | C:\Program Files\Internet Explorer\iexplore.exe | VBCABLE_Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2520 | DrvInst.exe "2" "211" "ROOT\MEDIA\0000" "C:\Windows\INF\oem4.inf" "vbmmecable_win7.inf:VBCable:VBCableInst:1.0.3.5:vbaudiovacwdm" "612cfd737" "00000554" "000005D0" "00000064" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3228 | SndVol.exe -r 45745284 0 {0.0.0.00000000}.{1a48e0ed-9f2f-4d65-bb8a-742835bdd0ef} | C:\Windows\system32\SndVol.exe | — | SndVol.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
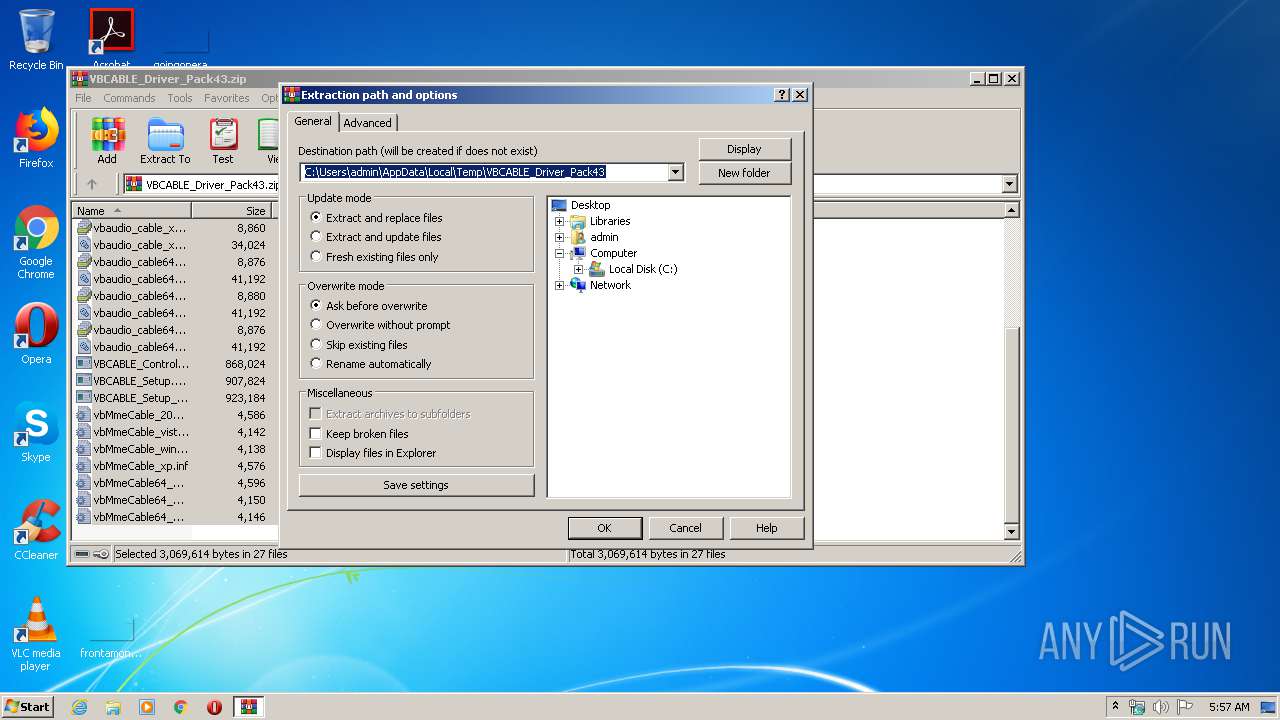
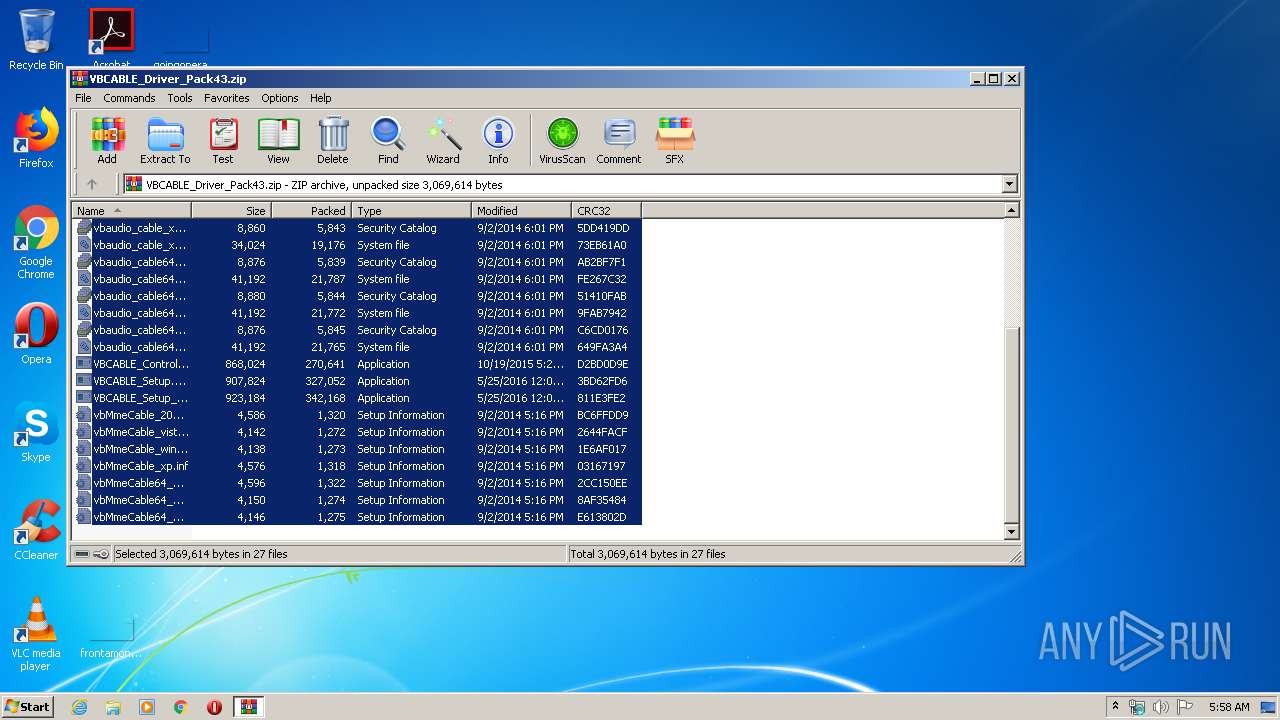
| 3312 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\VBCABLE_Driver_Pack43.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3364 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{152c8a29-4da5-05ef-513a-69058d003811} Global\{4c5ee015-6721-520c-9db8-6f58b9f80454} C:\Windows\System32\DriverStore\Temp\{28139f51-d511-3b0d-3811-374e38e55254}\vbmmecable_win7.inf C:\Windows\System32\DriverStore\Temp\{28139f51-d511-3b0d-3811-374e38e55254}\vbaudio_cable_win7.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2492 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\Desktop\vb\VBCABLE_ControlPanel.exe" | C:\Users\admin\Desktop\vb\VBCABLE_ControlPanel.exe | — | explorer.exe | |||||||||||
User: admin Company: VB-AUDIO Software Integrity Level: MEDIUM Description: VB-AUDIO Virtual Cable Control Panel Exit code: 3221226540 Version: 1, 0, 3, 5 Modules
| |||||||||||||||
Total events
3 605
Read events
1 764
Write events
1 834
Delete events
7
Modification events
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VBCABLE_Driver_Pack43.zip | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @cryptext.dll,-6145 |
Value: Security Catalog | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
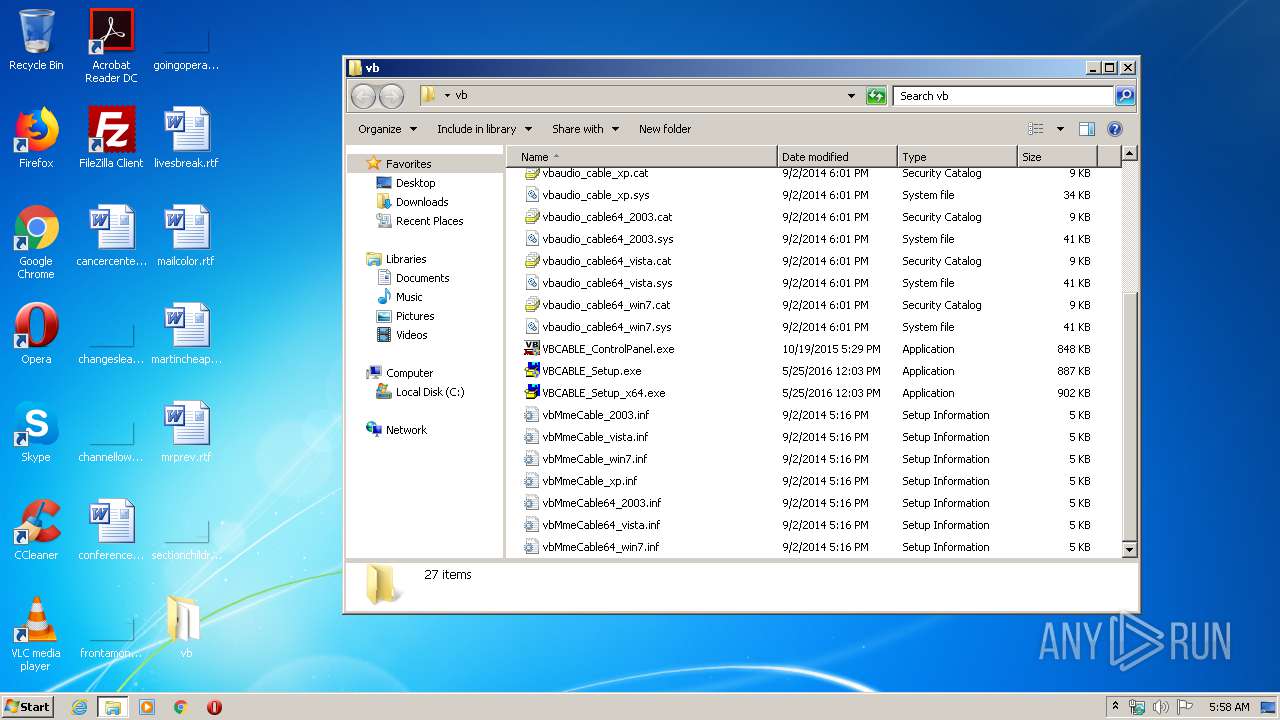
Value: C:\Users\admin\Desktop\vb | |||
Executable files
15
Suspicious files
39
Text files
196
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
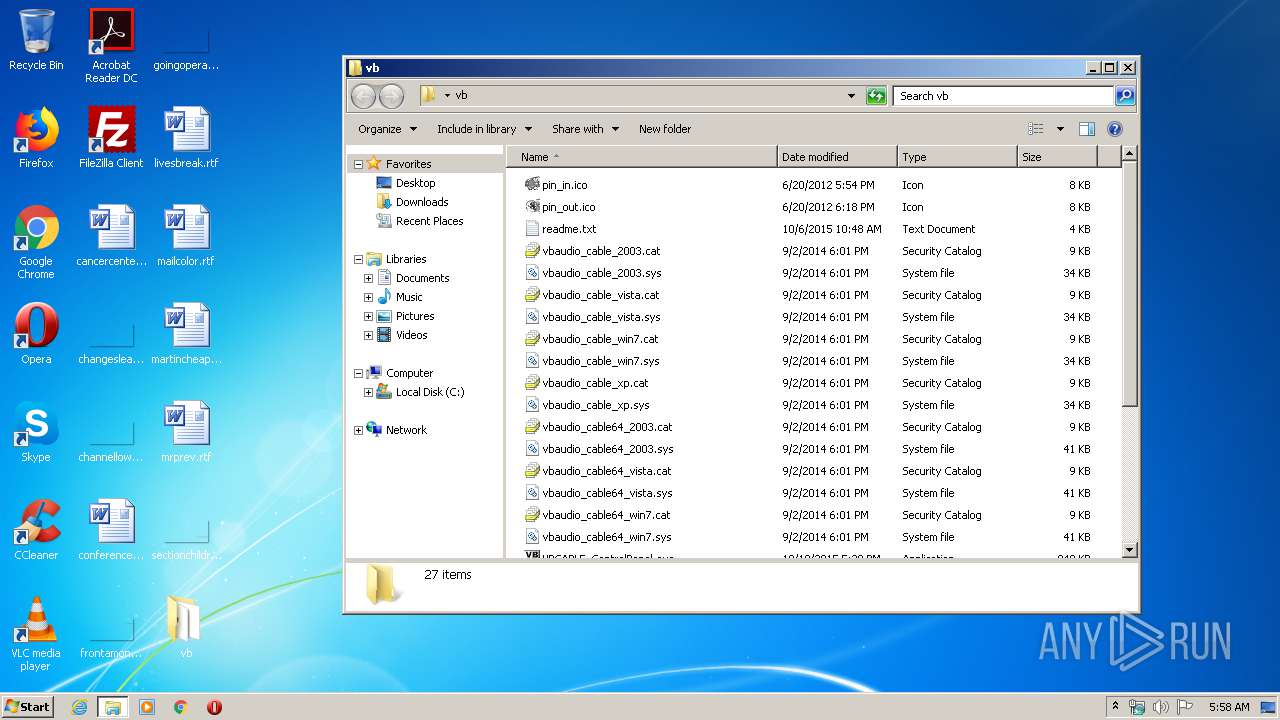
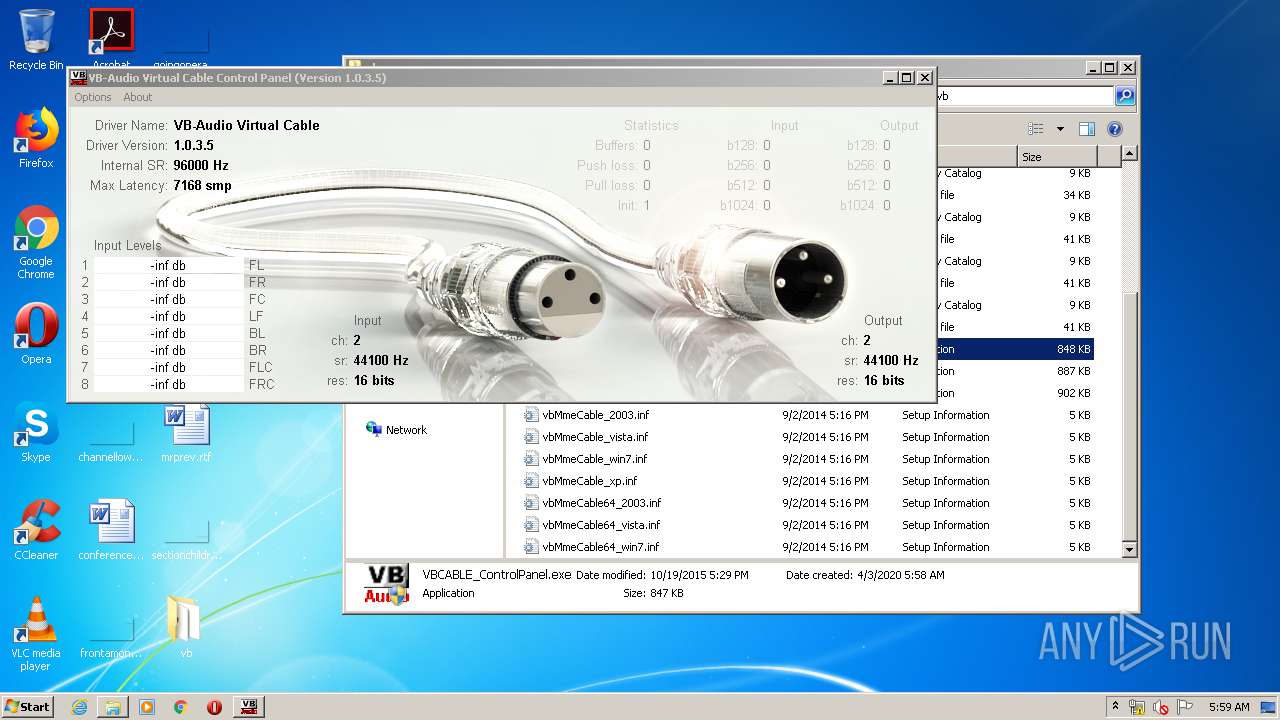
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbMmeCable64_win7.inf | ini | |
MD5:498FAEE2DE63C1C428900920203FDF9B | SHA256:DA35387CCFE813F5C553BB7E0CAF4E67ADBB4429E742C2BD3C2014F80E6EC516 | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable_xp.cat | cat | |
MD5:F548E80F9A5DF41B91B1F6A51C9C362A | SHA256:51434EBBDA13CAF3C7617EF3035126BAACCA3E523FEAF6828B398D52503D70D2 | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\VBCABLE_ControlPanel.exe | executable | |
MD5:BF51F5D7F3CACCBC18D4B75C0B5161AC | SHA256:290CE0F5A52AB17C35DE5782C390EF62D56EE61AC6F64290CB6C96873400718C | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable_vista.cat | cat | |
MD5:40401678D0272A448795432615F8B762 | SHA256:810B30193A400B1559302C23F81EF8AAADF038B3CAF3AFF9BF200B59688A2DEF | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable_win7.sys | executable | |
MD5:F23A66967591AEA2B8840F02B3DA993A | SHA256:D047E3EE66E3EE023E598232EA22AA28DBB39ADEABE818ADFB2A72AB738DF0B9 | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable64_2003.cat | cat | |
MD5:1A938E376ABA87FD3D4285A261146923 | SHA256:70F88E34C857C999367EB5B0303E23F5676B15A79ED4054F374749232BAA0E3A | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable_win7.cat | cat | |
MD5:9CC8F7A387484C49A6F1296586CD1DDB | SHA256:1C38AFACF115818C925BC26FAF216E3563E85BBC4D6D793E5F76F2AA670D08E7 | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\pin_in.ico | image | |
MD5:E442346F22DA9A5BB15DFABA67A360B8 | SHA256:934865449455103C1C5997D8220ACD160C3891F8A870F8E745B743D12681AC42 | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable_vista.sys | executable | |
MD5:6CC2CE471671F7665BA15A177A3CCF10 | SHA256:8B02C26313B75CEB8FB9BD16B6B167CF70D7F3BC977DFC1986C0859F8C72B49F | |||
| 3312 | WinRAR.exe | C:\Users\admin\Desktop\vb\vbaudio_cable64_vista.sys | executable | |
MD5:96B795DE860F111144632A3AAE5422C5 | SHA256:703572FA9E8AA1616E6B2ABD36B91A4718DE77EADC02AE05ED2C8F304D058AFC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
28
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3456 | iexplore.exe | GET | 200 | 72.247.178.27:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
3456 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAyEjWbgb3fYdv3f6E81lXM%3D | US | der | 471 b | whitelisted |
3456 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAfHxhHnkMBjFmx7tQC%2B5yg%3D | US | der | 471 b | whitelisted |
3456 | iexplore.exe | GET | 200 | 72.247.178.41:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
3456 | iexplore.exe | GET | 301 | 193.252.121.241:80 | http://pages.perso.orange.fr/php/compteur.php?url=vb-audio&df=ThankYou&dd=E&frgb=noir&ft=0&tr=Oui&pad=Non&comma=Oui | FR | html | 352 b | unknown |
2492 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjqTAc%2FHIGOD%2BaUx0%3D | US | der | 492 b | whitelisted |
3456 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAL2JkUQasIQbzfM%2F0VVMQI%3D | US | der | 471 b | whitelisted |
2492 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2492 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3456 | iexplore.exe | 193.252.121.242:80 | vb-audio.pagesperso-orange.fr | Orange | FR | suspicious |
3456 | iexplore.exe | 193.252.121.242:443 | vb-audio.pagesperso-orange.fr | Orange | FR | suspicious |
3456 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3456 | iexplore.exe | 51.38.42.138:443 | shop.vb-audio.com | — | GB | unknown |
3456 | iexplore.exe | 193.252.121.241:80 | pages.perso.orange.fr | Orange | FR | unknown |
3456 | iexplore.exe | 193.252.121.241:443 | pages.perso.orange.fr | Orange | FR | unknown |
3456 | iexplore.exe | 72.247.178.41:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
2492 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2492 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1052 | svchost.exe | 216.58.208.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vb-audio.pagesperso-orange.fr |
| suspicious |
ocsp.digicert.com |
| whitelisted |
shop.vb-audio.com |
| unknown |
pages.perso.orange.fr |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
s.gstat.orange.fr |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |