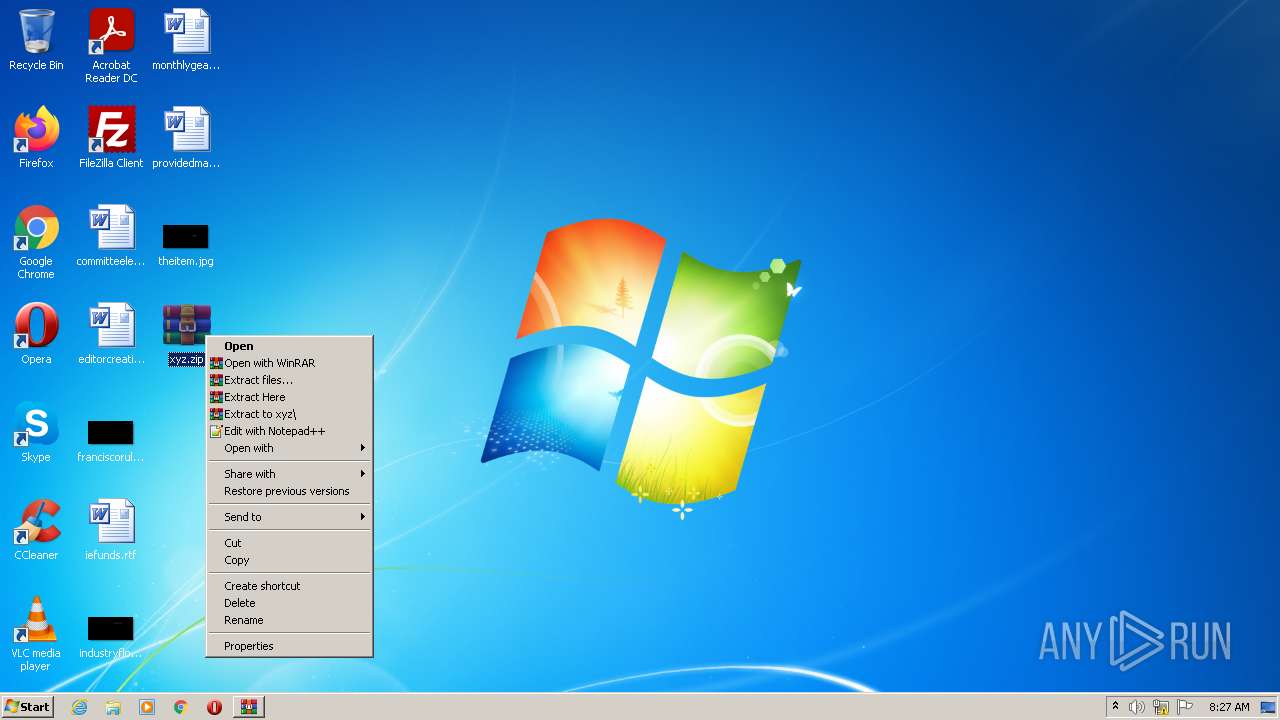
| File name: | xyz.zip |
| Full analysis: | https://app.any.run/tasks/6fd3a7bc-ee19-4477-a87a-695ed350ba5b |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 07:23:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CE956CAE713473A97745EA0D83463F3A |
| SHA1: | 8FAE38F3240F6EE5068F9CBE40112F651C4042B1 |
| SHA256: | 66FC76BB7FC8F2BDADB5112A0AC7396E25D847CDCFB9FF715CB790EA1E0B26EB |
| SSDEEP: | 192:+yohirCchhF23OUw4Vk4EZff/o6pN/EDjyIQ68nXr3e3xc3FGNNKn:+yRrCN5hbEZfXo6z/EDjGvD3Eun |
MALICIOUS
Application was dropped or rewritten from another process
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3204)
SUSPICIOUS
Reads Internet Settings
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
Reads the machine GUID from the registry
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
Executes PowerShell scripts
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3204)
Reads settings of System Certificates
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1716)
Process checks LSA protection
- WinRAR.exe (PID: 1716)
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
- WinRAR.exe (PID: 3204)
Checks supported languages
- WinRAR.exe (PID: 1716)
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
- WinRAR.exe (PID: 3204)
Reads the computer name
- WinRAR.exe (PID: 1716)
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
- WinRAR.exe (PID: 3204)
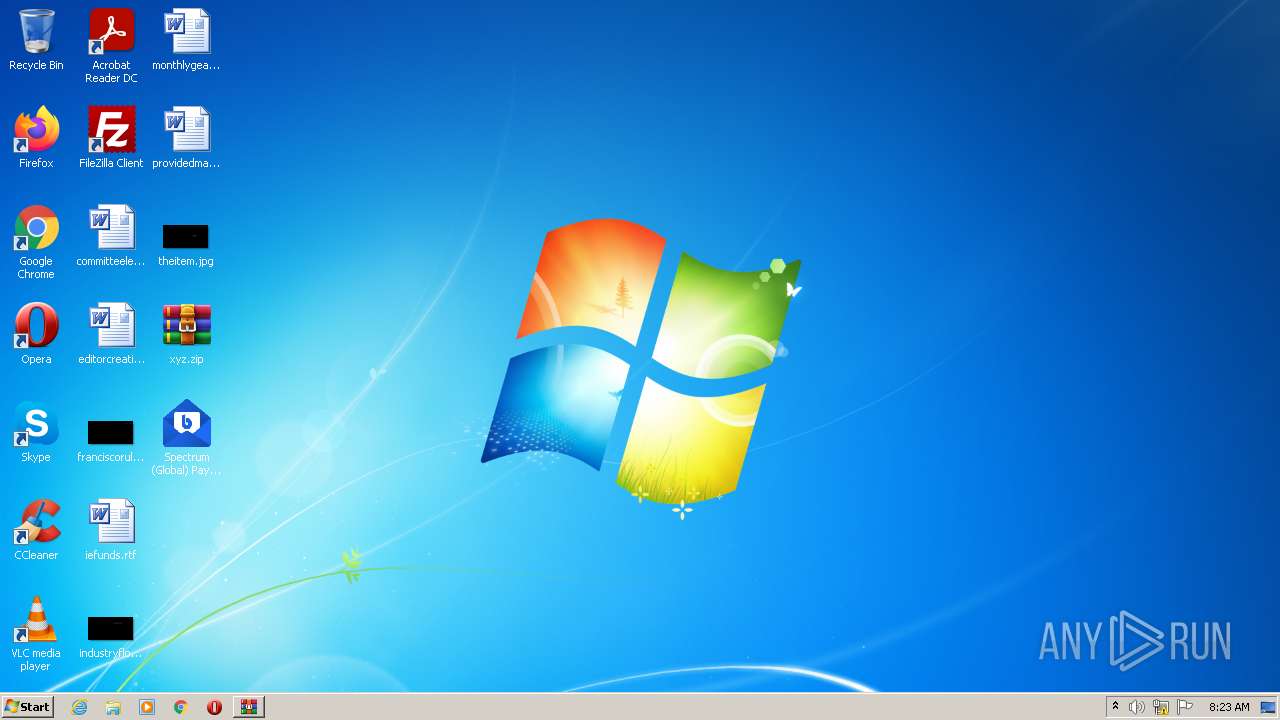
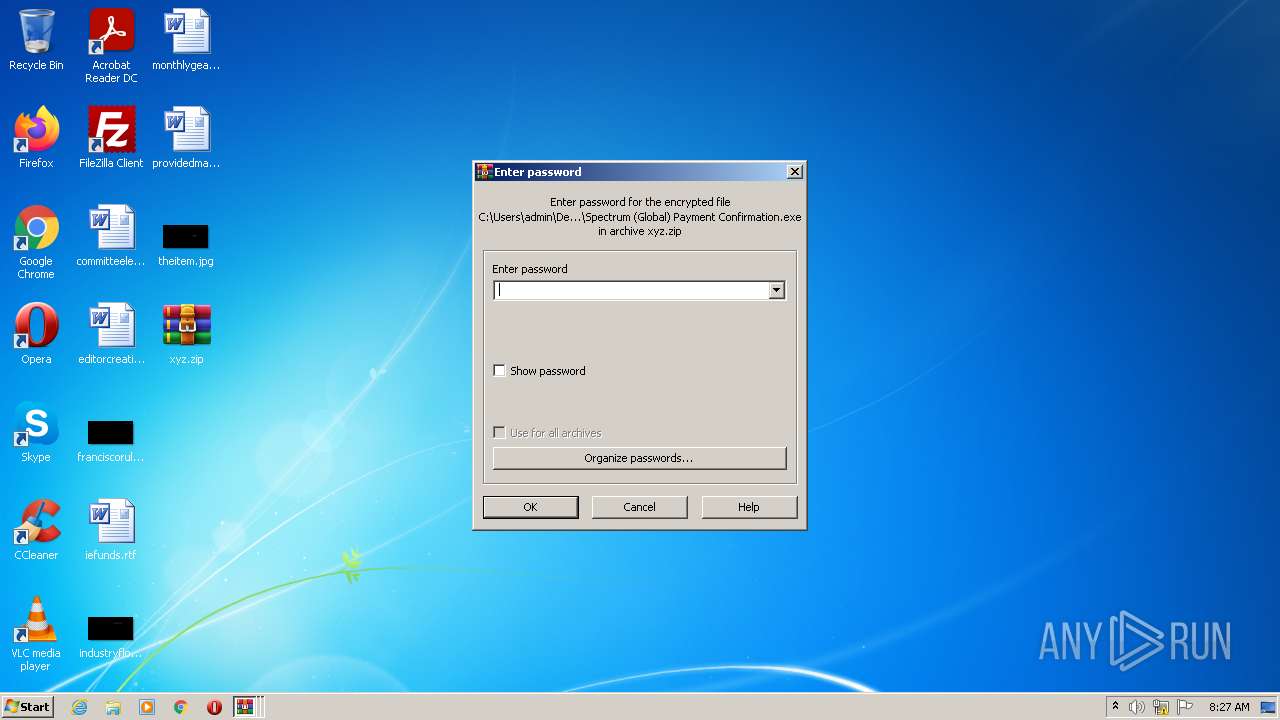
Manual execution by user
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
- WinRAR.exe (PID: 3204)
Reads Environment values
- Spectrum (Global) Payment Confirmation.exe (PID: 2576)
Creates files in the user directory
- WinRAR.exe (PID: 1716)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
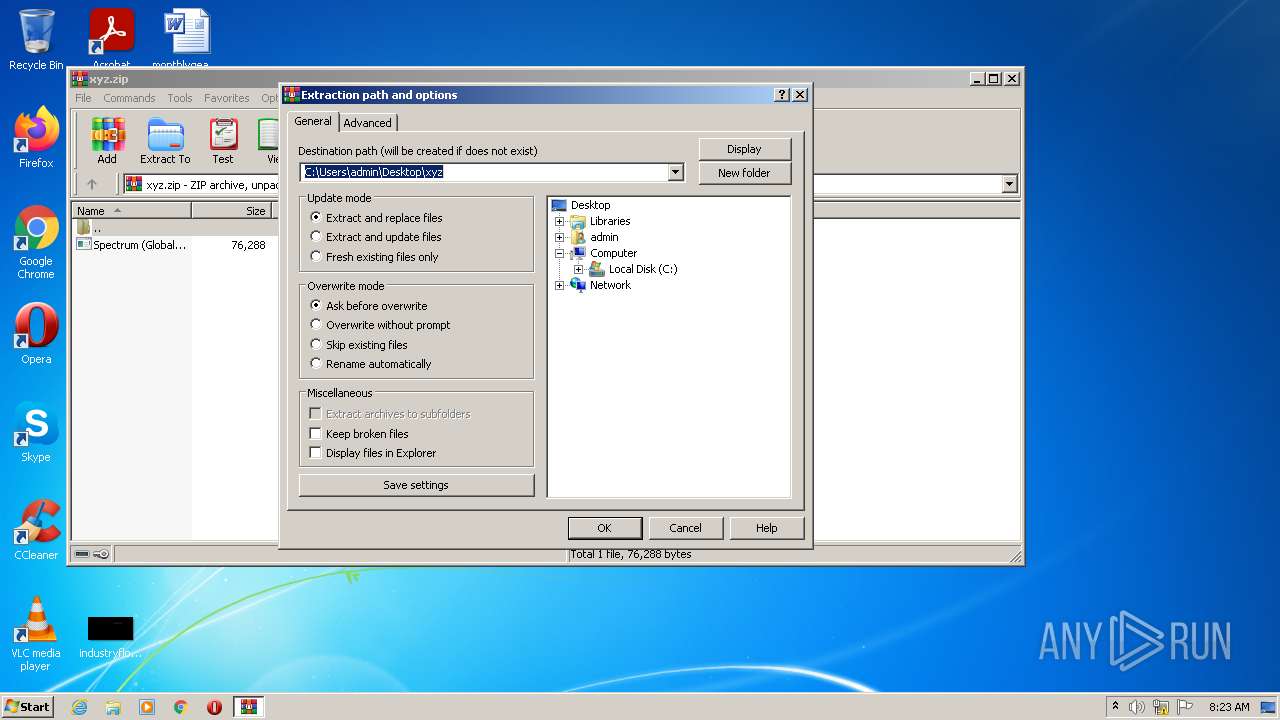
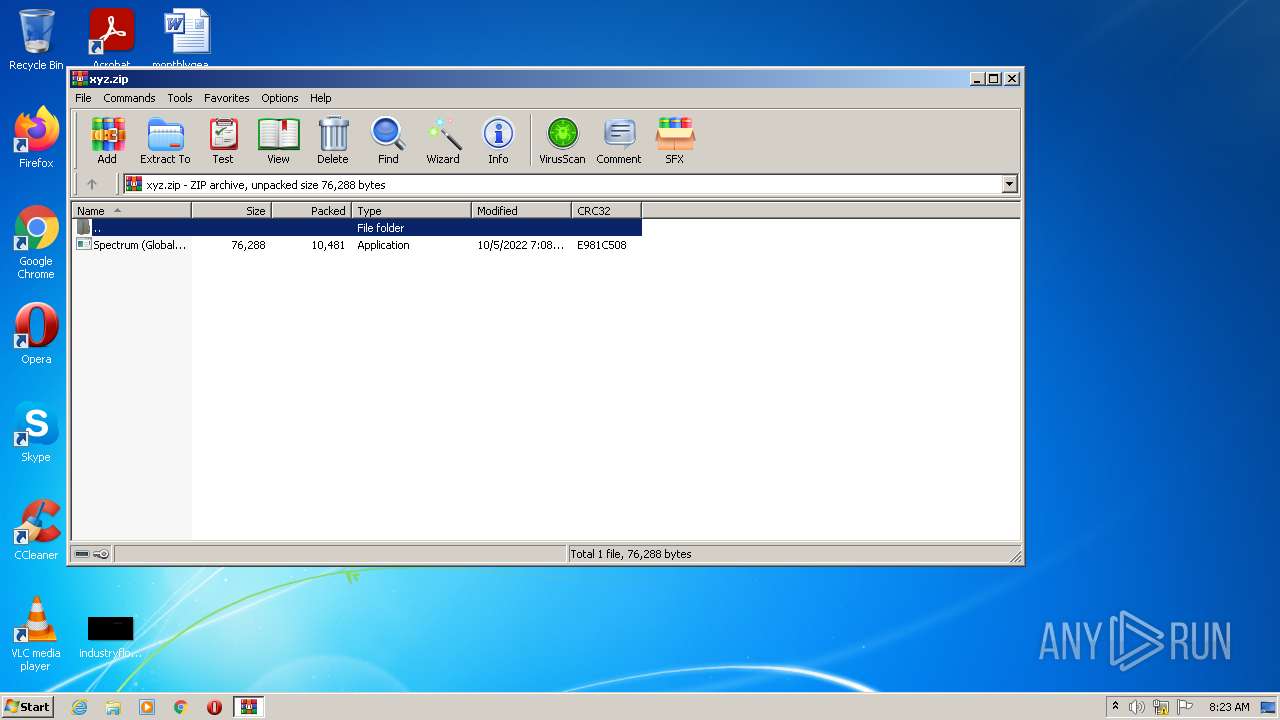
| 1716 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\xyz.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\Desktop\Spectrum (Global) Payment Confirmation.exe" | C:\Users\admin\Desktop\Spectrum (Global) Payment Confirmation.exe | Explorer.EXE | ||||||||||||
User: admin Company: Dialpad Integrity Level: MEDIUM Description: Dialpad for Windows Exit code: 0 Version: 19.10.0.0 Modules
| |||||||||||||||
| 3204 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\xyz.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3456 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc UwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBTAGUAYwBvAG4AZABzACAANQAwAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spectrum (Global) Payment Confirmation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3468 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc UwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBzACAAMQAwADsAIABSAGUAbQBvAHYAZQAtAEkAdABlAG0AIAAtAFAAYQB0AGgAIAAiAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEQAZQBzAGsAdABvAHAAXABTAHAAZQBjAHQAcgB1AG0AIAAoAEcAbABvAGIAYQBsACkAIABQAGEAeQBtAGUAbgB0ACAAQwBvAG4AZgBpAHIAbQBhAHQAaQBvAG4ALgBlAHgAZQAiACAALQBGAG8AcgBjAGUA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Spectrum (Global) Payment Confirmation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
5 286
Read events
5 232
Write events
54
Delete events
0
Modification events
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\xyz.zip | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
5
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
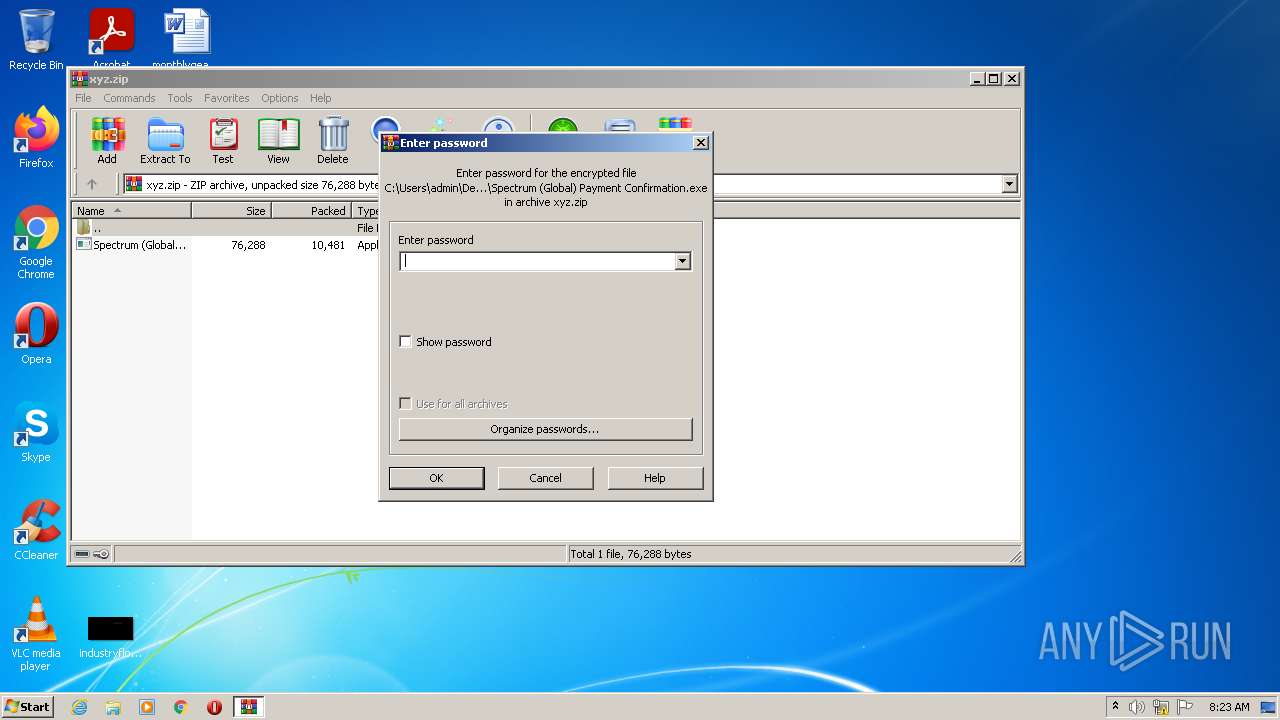
| 1716 | WinRAR.exe | C:\Users\admin\Desktop\Spectrum (Global) Payment Confirmation.exe | executable | |
MD5:— | SHA256:— | |||
| 3204 | WinRAR.exe | C:\Users\admin\Desktop\Spectrum (Global) Payment Confirmation.exe | executable | |
MD5:— | SHA256:— | |||
| 3456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\umigmzij.taw.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5nnz3r1z.mo2.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3456 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\12x3ojw5.ct3.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tifp4i1g.ald.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3456 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:1068BF0B9B98C206F587A7DB05F6DD06 | SHA256:534478EDAFC5087DAA3749624454988B1F7DF923BF1A0A9E28C5F97C3308CFDB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2576 | Spectrum (Global) Payment Confirmation.exe | 198.54.116.205:443 | janiking.xyz | NAMECHEAP-NET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
janiking.xyz |
| unknown |