| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/c2282b20-dd16-455b-932b-6ed7a1893645 |
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2024, 11:18:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FBA93D8D029E85E0CDE3759B7903CEE2 |
| SHA1: | 525B1AA549188F4565C75AB69E51F927204CA384 |
| SHA256: | 66F62408DFCE7C4A5718D2759F1D35721CA22077398850277D16E1FCA87FE764 |
| SSDEEP: | 196608:adAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3m:OaWedh+Idx75QYub//73lc6u7bLMYxDm |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 2520)
- INSTALLER.exe (PID: 2816)
SUSPICIOUS
Executing commands from a ".bat" file
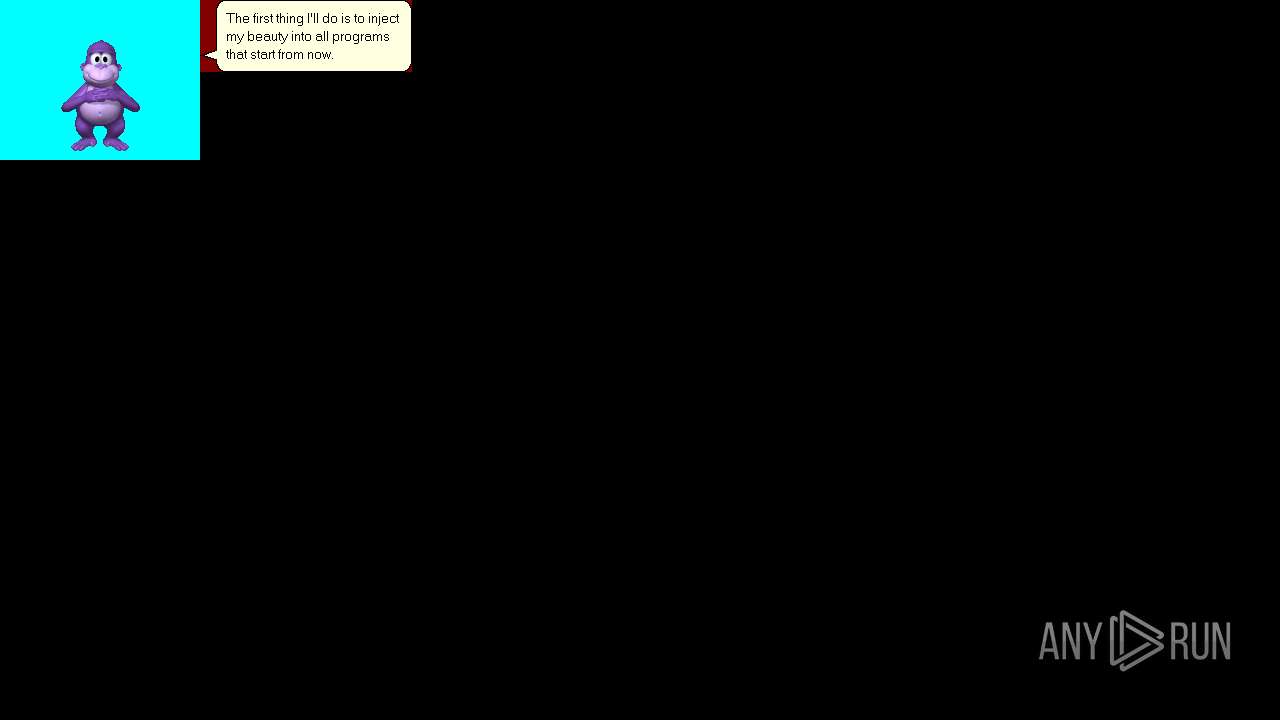
- Bonzify.exe (PID: 7004)
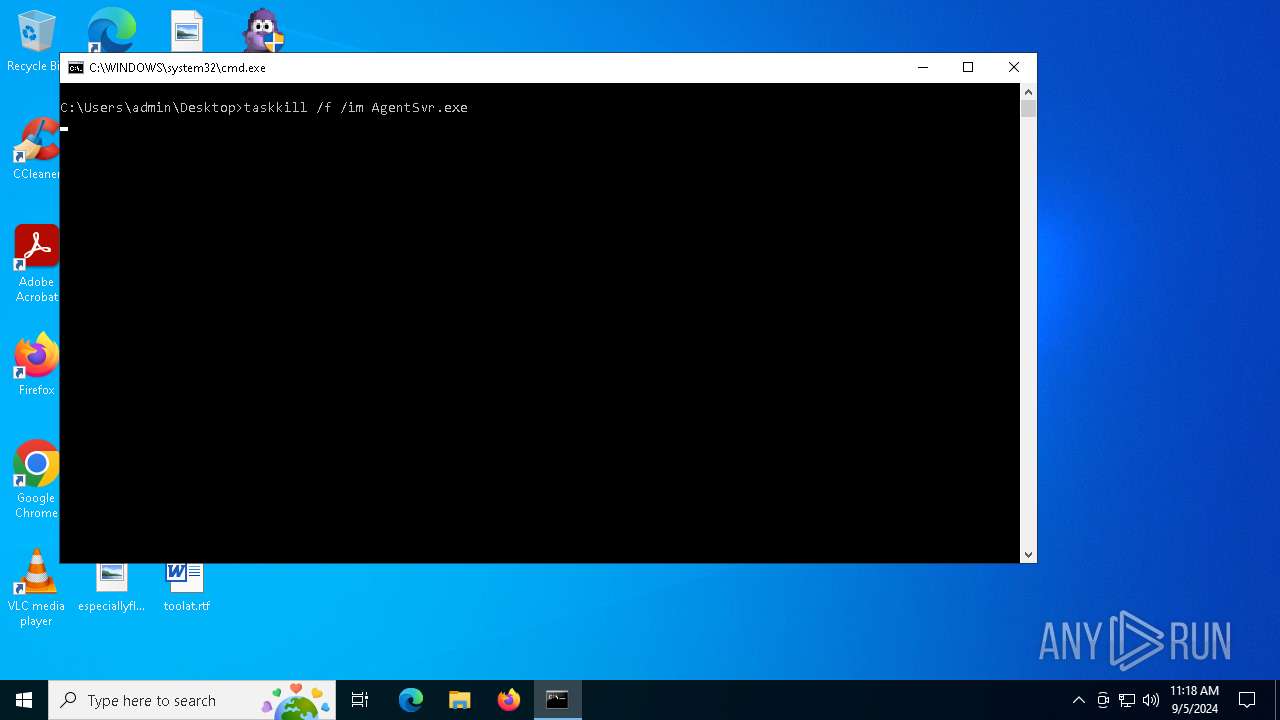
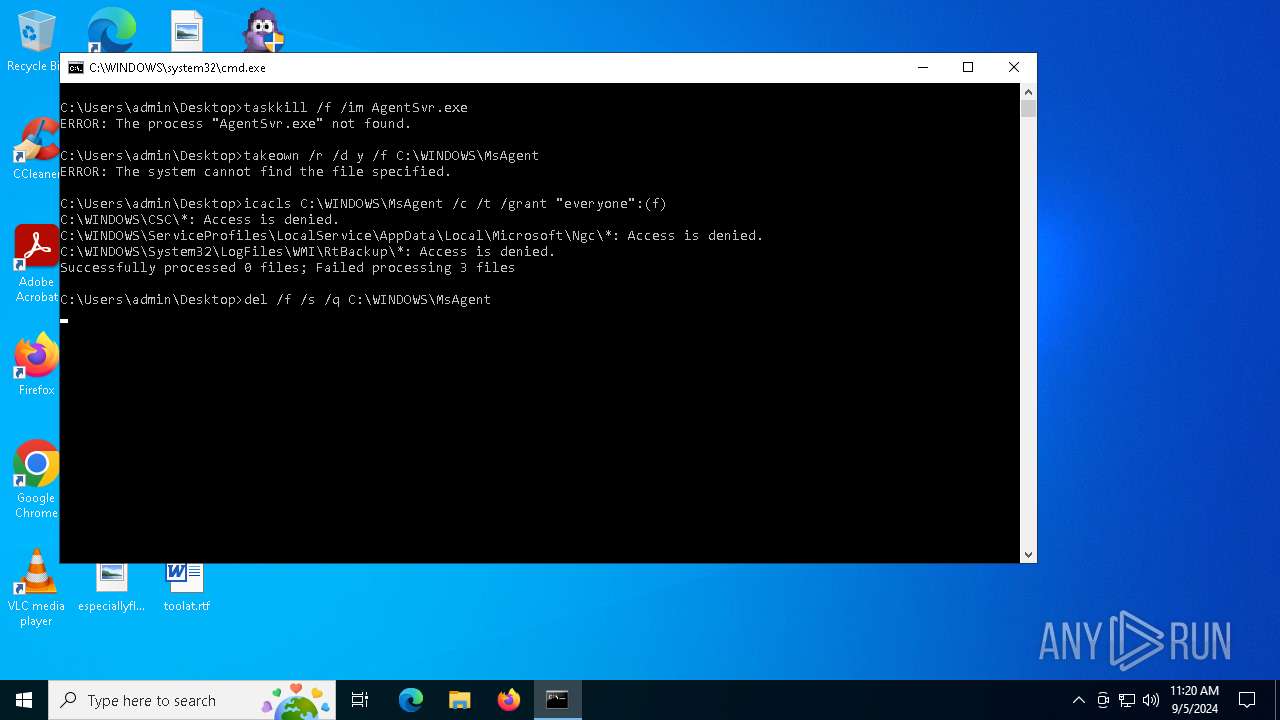
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6752)
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 7004)
Process drops legitimate windows executable
- Bonzify.exe (PID: 7004)
- INSTALLER.exe (PID: 2816)
- INSTALLER.exe (PID: 2520)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6752)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 6752)
Starts a Microsoft application from unusual location
- INSTALLER.exe (PID: 2816)
- INSTALLER.exe (PID: 2520)
Executable content was dropped or overwritten
- INSTALLER.exe (PID: 2816)
- INSTALLER.exe (PID: 2520)
- Bonzify.exe (PID: 7004)
INFO
Checks supported languages
- Bonzify.exe (PID: 7004)
Create files in a temporary directory
- Bonzify.exe (PID: 7004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:13 11:42:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4096 |
| InitializedDataSize: | 6696960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
158
Monitored processes
26
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | regsvr32 /s "C:\WINDOWS\msagent\AgentCtl.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2520 | INSTALLER.exe /q | C:\Users\admin\AppData\Local\Temp\INSTALLER.exe | Bonzify.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 | |||||||||||||||
| 2520 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2572 | regsvr32 /s C:\WINDOWS\lhsp\tv\tvenuax.dll | C:\Windows\SysWOW64\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2684 | "C:\WINDOWS\msagent\AgentSvr.exe" /regserver | C:\Windows\msagent\AgentSvr.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 | |||||||||||||||
| 2816 | INSTALLER.exe /q | C:\Users\admin\AppData\Local\Temp\INSTALLER.exe | Bonzify.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 | |||||||||||||||
| 3180 | regsvr32 /s "C:\WINDOWS\msagent\mslwvtts.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4056 | regsvr32 /s "C:\WINDOWS\msagent\AgentMPx.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 4084 | regsvr32 /s "C:\WINDOWS\msagent\AgentDP2.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
163
Read events
163
Write events
0
Delete events
0
Modification events
Executable files
55
Suspicious files
33
Text files
64
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7004 | Bonzify.exe | C:\Windows\executables.bin | binary | |
MD5:1F3566FC3700775016BE546F9BEBD9E9 | SHA256:829DECB1EE9CC6861774CA87440DB2AD43CEAAE39A2468E29A4A04AA9A5BE794 | |||
| 7004 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\TakeOwn.bat | text | |
MD5:F80E36CD406022944558D8A099DB0FA7 | SHA256:7B41E5A6C2DD92F60C38CB4FE09DCBE378C3E99443F7BAF079ECE3608497BDC7 | |||
| 7004 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\KillAgent.bat | text | |
MD5:EA7DF060B402326B4305241F21F39736 | SHA256:E4EDC2CB6317AB19EE1A6327993E9332AF35CFBEBAFF2AC7C3F71D43CFCBE793 | |||
| 7004 | Bonzify.exe | C:\Users\admin\AppData\Local\Temp\INSTALLER.exe | executable | |
MD5:66996A076065EBDCDAC85FF9637CEAE0 | SHA256:16CA09AD70561F413376AD72550AE5664C89C6A76C85C872FFE2CB1E7F49E2AA | |||
| 2816 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTDP2.DLL | executable | |
MD5:A334BBF5F5A19B3BDB5B7F1703363981 | SHA256:C33BEABA130F8B740DDDB9980FE9012F9322AC6E94F36A6AA6086851C51B98DE | |||
| 2816 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTPSH.DLL | executable | |
MD5:B4AC608EBF5A8FDEFA2D635E83B7C0E8 | SHA256:8414DFE399813B7426C235BA1E625BD2B5635C8140DA0D0CFC947F6565FE415F | |||
| 2816 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGENTSVR.EXE | executable | |
MD5:5C91BF20FE3594B81052D131DB798575 | SHA256:E8CE546196B6878A8C34DA863A6C8A7E34AF18FB9B509D4D36763734EFA2D175 | |||
| 2816 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ADVPACK.DLL | executable | |
MD5:81E5C8596A7E4E98117F5C5143293020 | SHA256:7D126ED85DF9705EC4F38BD52A73B621CF64DD87A3E8F9429A569F3F82F74004 | |||
| 2816 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGTCTL15.TLB | executable | |
MD5:F1656B80EAAE5E5201DCBFBCD3523691 | SHA256:3F8ADC1E332DD5C252BBCF92BF6079B38A74D360D94979169206DB34E6A24CD2 | |||
| 2816 | INSTALLER.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AGTINST.INF | binary | |
MD5:B127D9187C6DBB1B948053C7C9A6811F | SHA256:BD1295D19D010D4866C9D6D87877913EEE69E279D4D089E5756BA285F3424E00 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
26
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1356 | svchost.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6404 | RUXIMICS.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 404 | 184.86.251.7:443 | https://r.bing.com/rb/4N/jnc,nj/Btu7tBP0vQIHDIMxag4vCxAtQuY.js?bu=FrYs9ir8AYcriyuNK48rtCu9LIMs_BGfLKUswSz8AfwBpSjmK_oR8RH6K-sr&or=w | unknown | — | — | unknown |
— | — | GET | 200 | 184.86.251.19:443 | https://www.bing.com/fd/ls/l?IG=16800713CD244755B15D5E88DF9D3BC0&Type=Event.ClientInst&DATA=[{%22T%22:%22CI.ClientInst%22,%22FID%22:%22CI%22,%22Name%22:%22max%20errors%20reached%22}] | unknown | — | — | unknown |
— | — | GET | 304 | 184.86.251.24:443 | https://r.bing.com/rb/19/cir3,ortl,cc,nc/oT6Um3bDKq3bSDJ4e0e-YJ5MXCI.css?bu=B74CSK0CiwFdXcoC&or=w | unknown | — | — | unknown |
— | — | POST | 204 | 184.86.251.23:443 | https://www.bing.com/fd/ls/lsp.aspx? | unknown | — | — | unknown |
— | — | POST | 204 | 184.86.251.23:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | unknown |
— | — | GET | 200 | 184.86.251.7:443 | https://r.bing.com/rp/-UAIppANYxiGpRWJy2NDph4qOEw.gz.js | unknown | s | 20.3 Kb | unknown |
— | — | POST | 204 | 184.86.251.16:443 | https://www.bing.com/fd/ls/lsp.aspx? | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6404 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1356 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1356 | svchost.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
6404 | RUXIMICS.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1356 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |