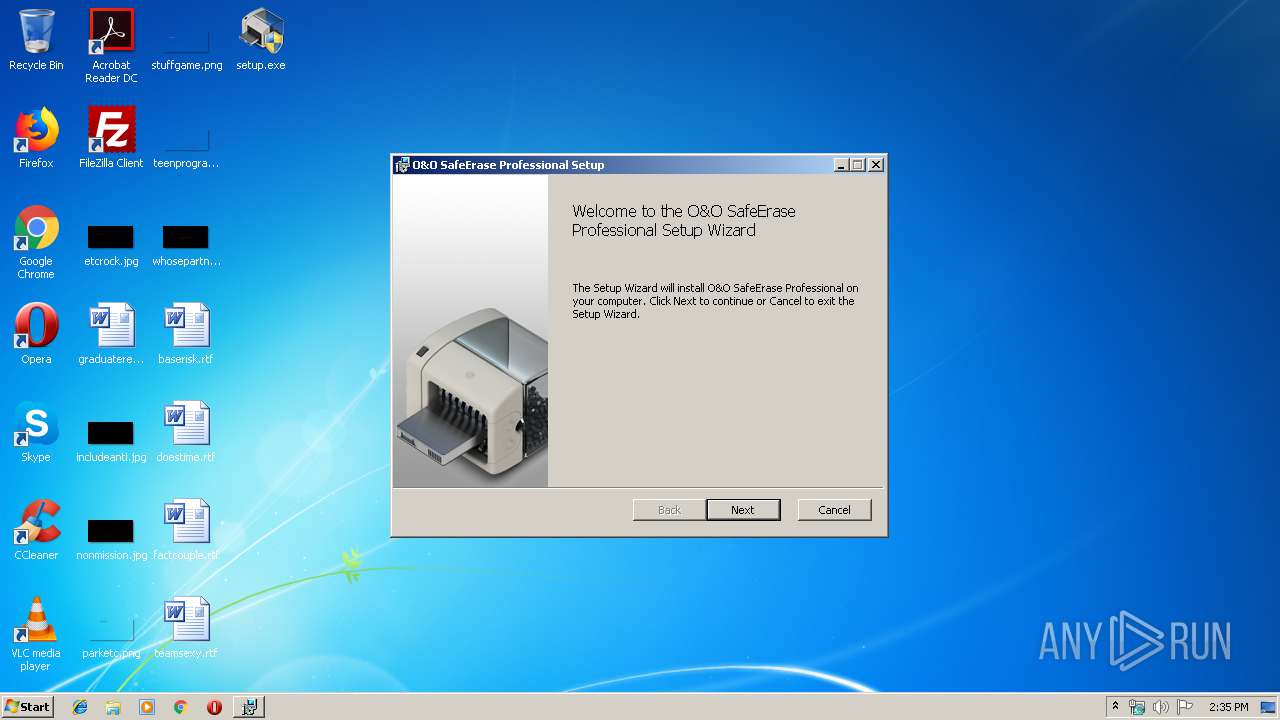
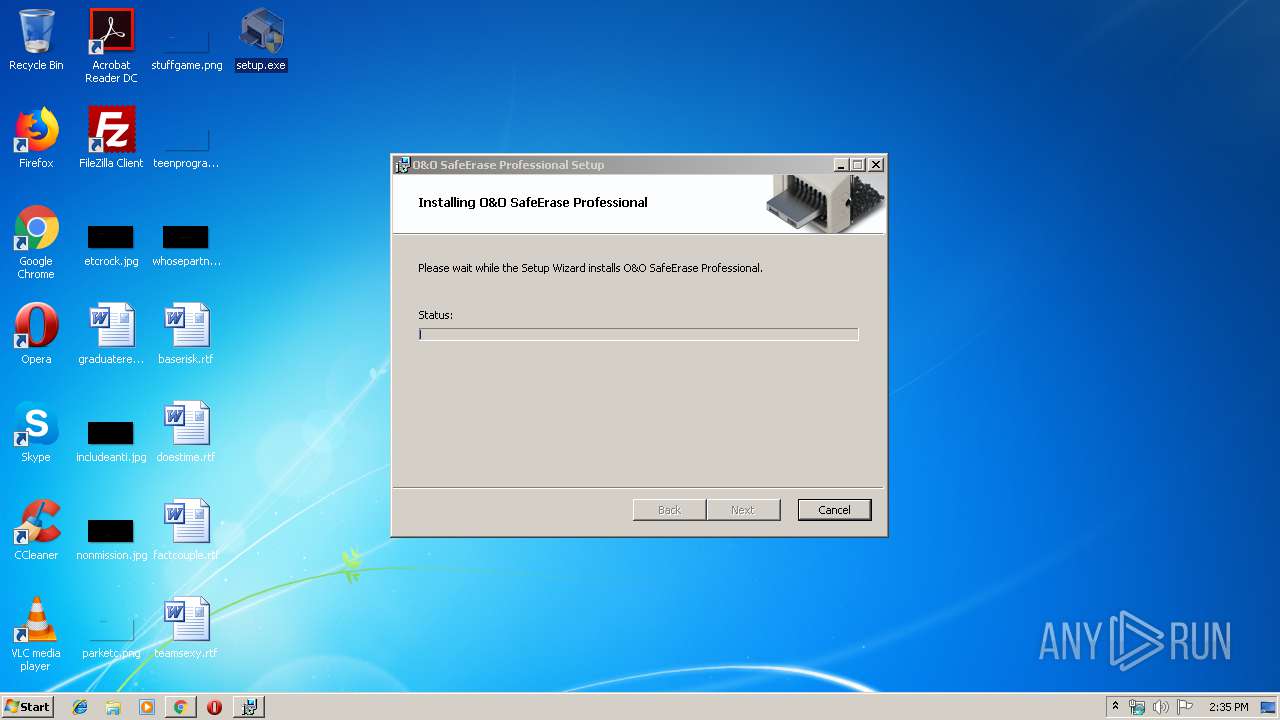
| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/98c45a41-3ae2-4d49-8a56-922841d5739c |
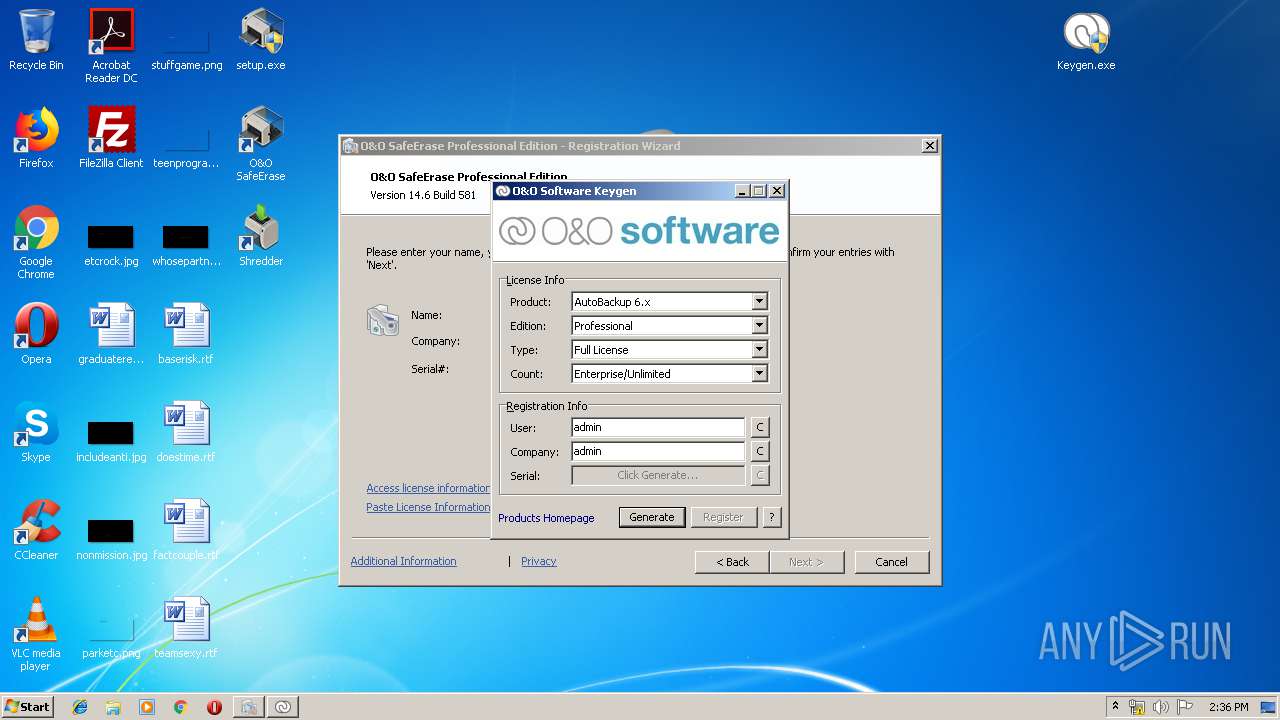
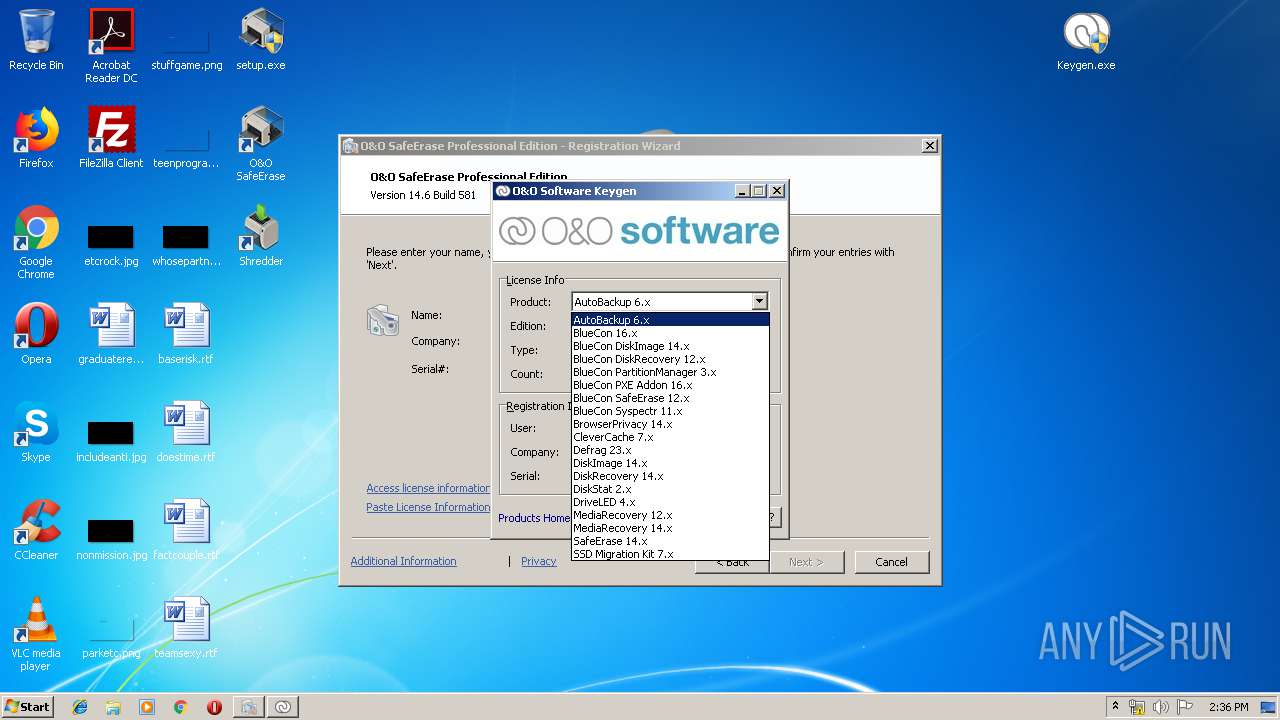
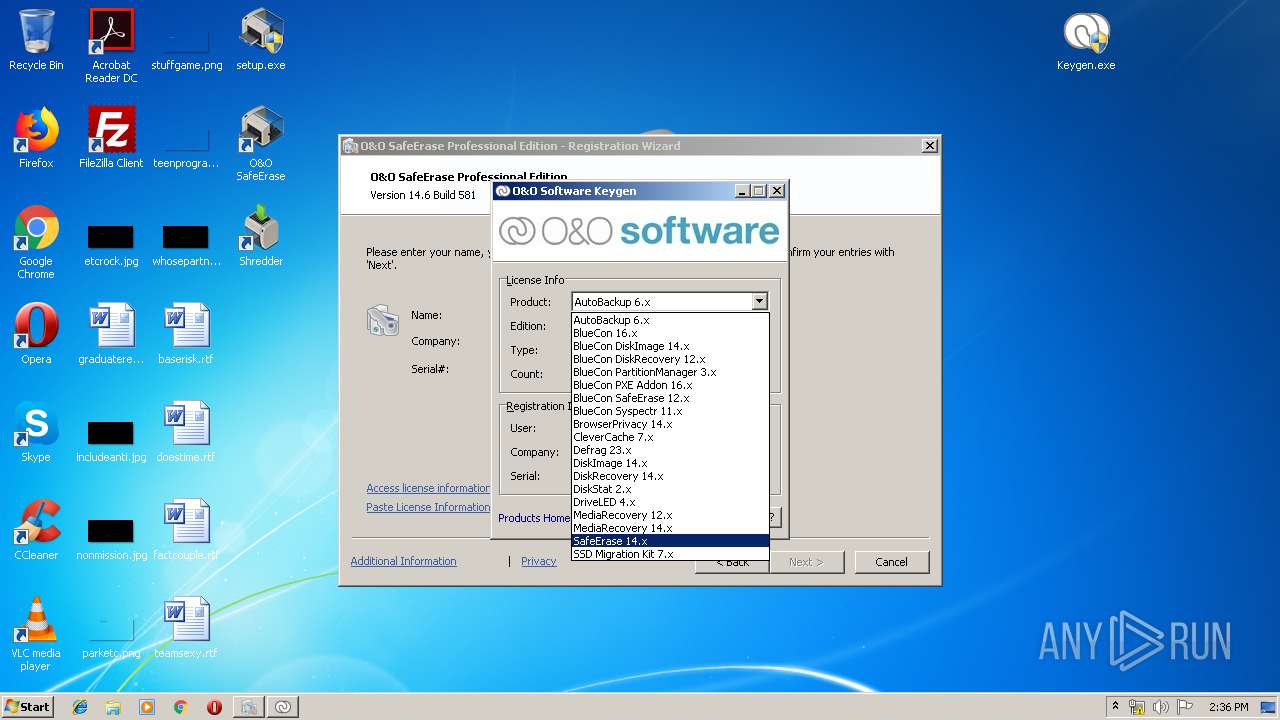
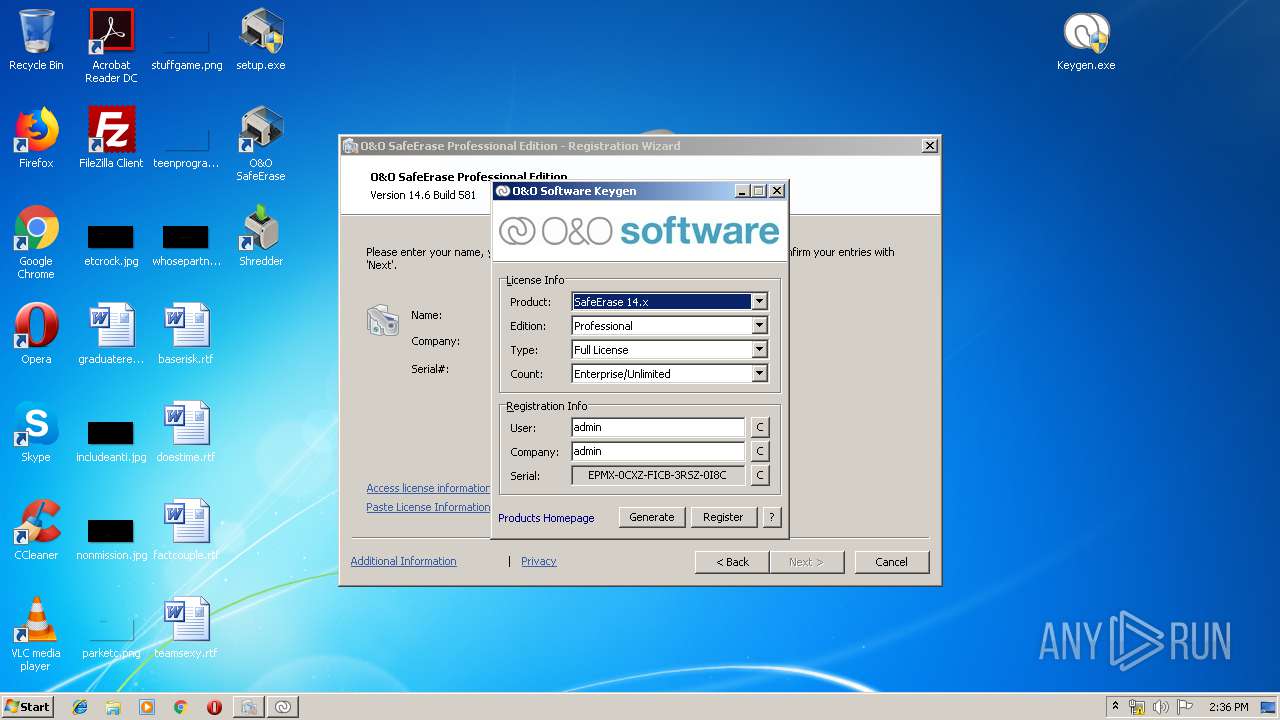
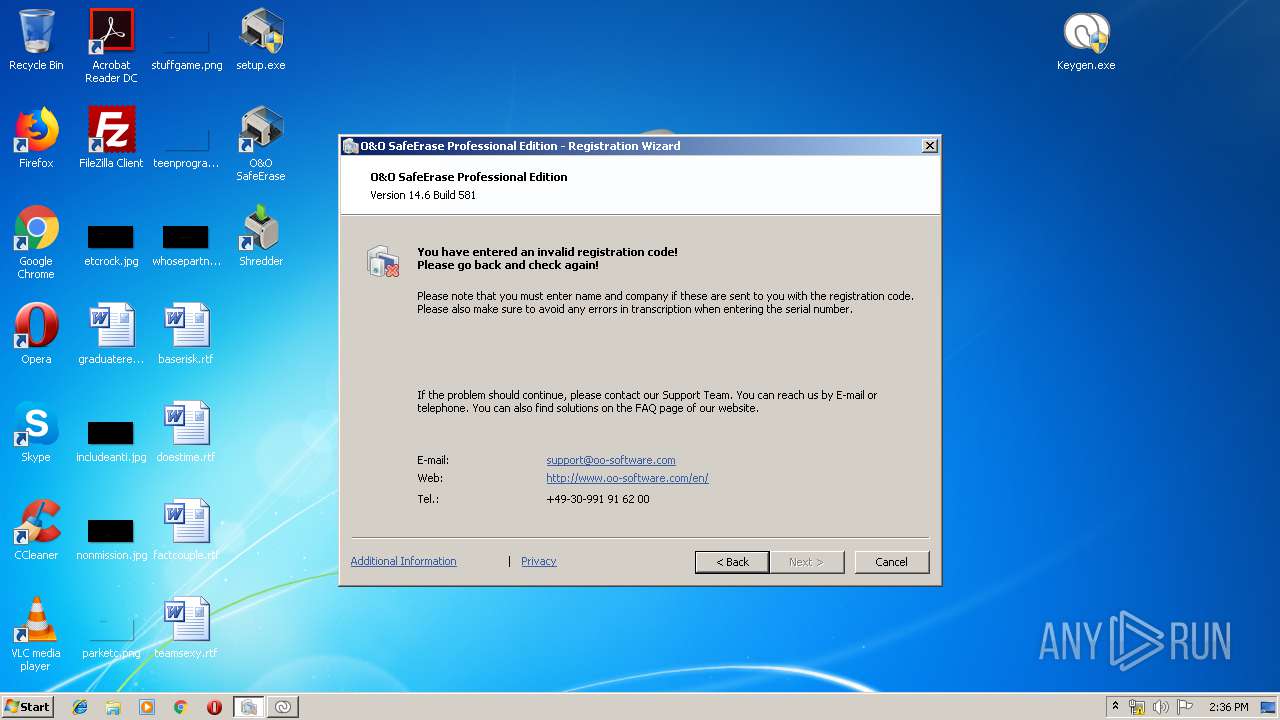
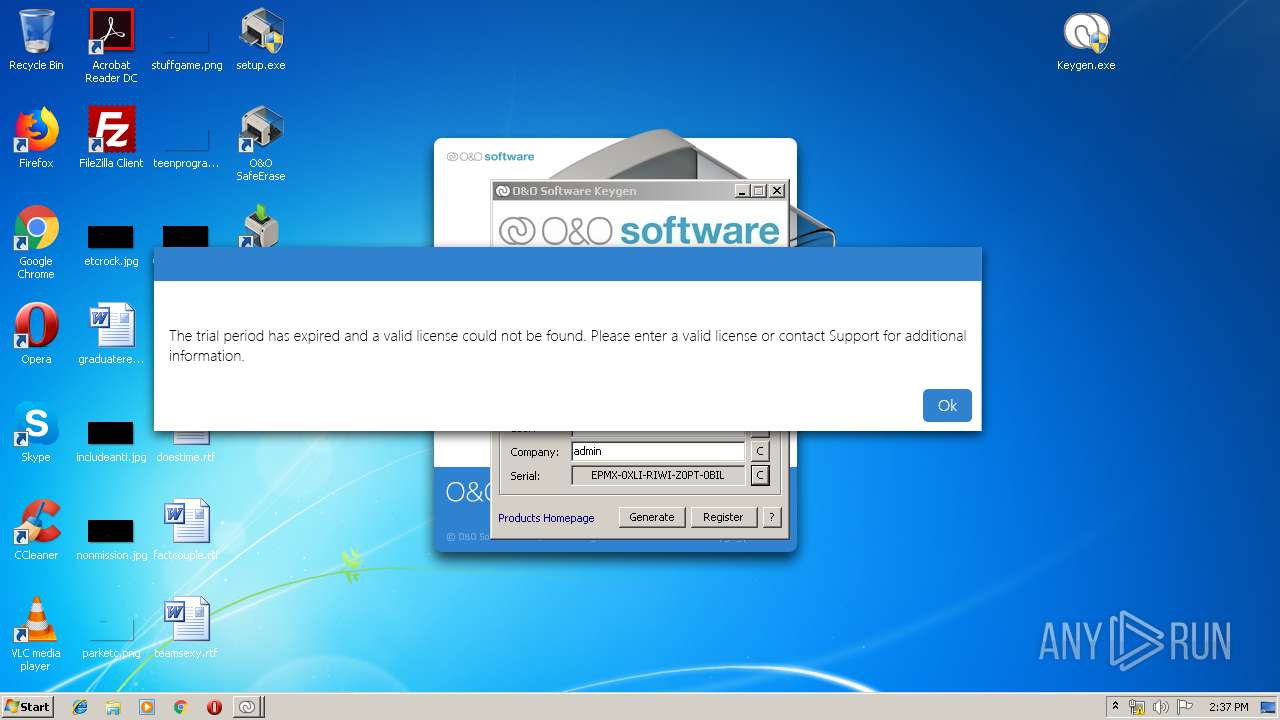
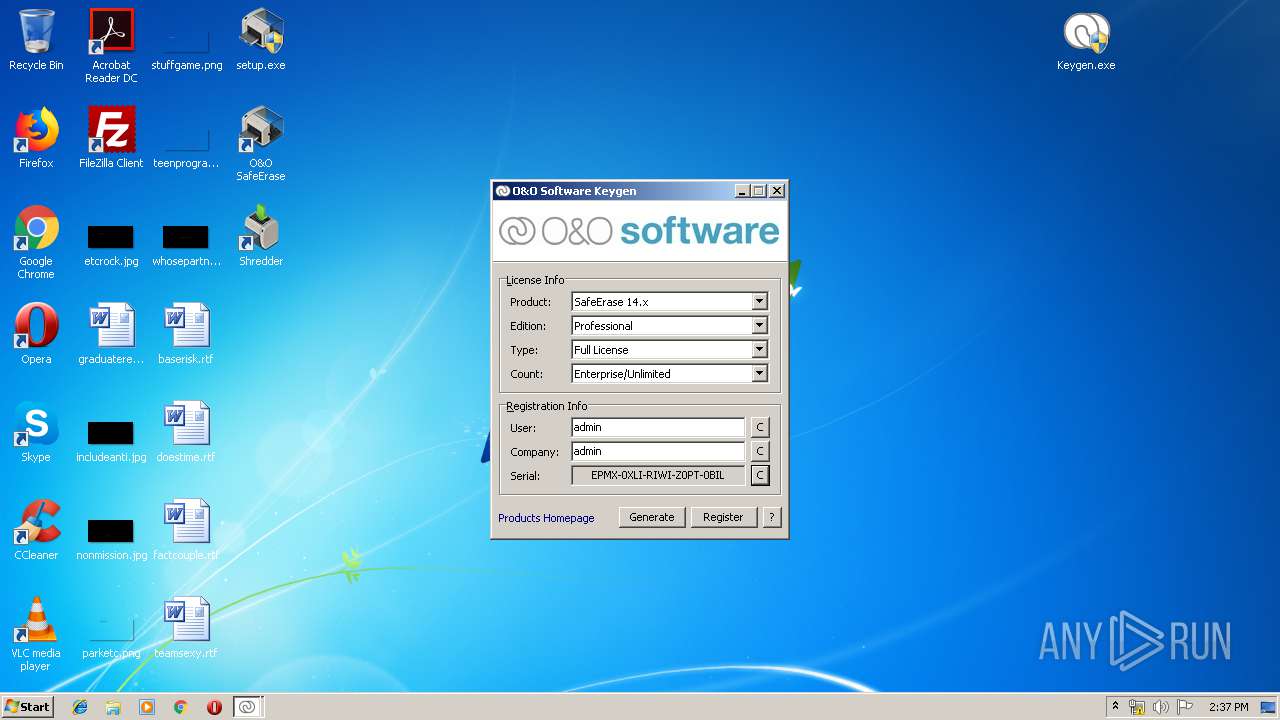
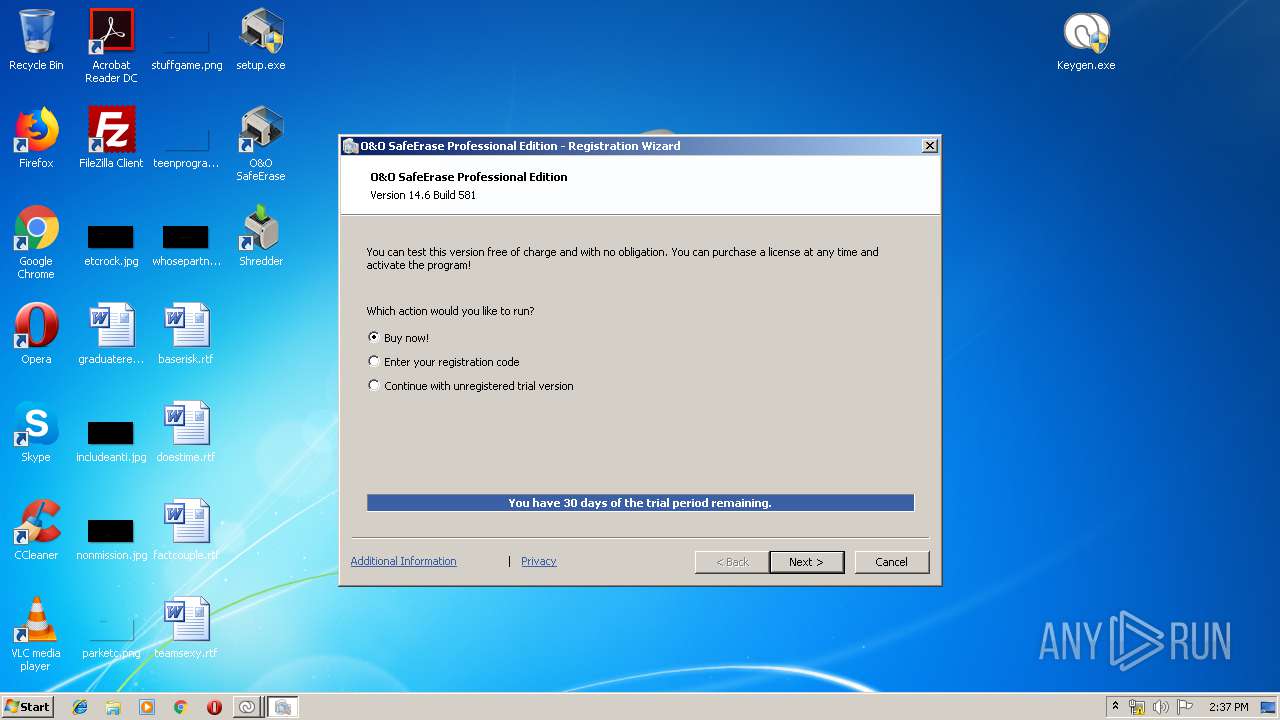
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 14:34:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1D5217C3A98B25D1E67EDE33BA5981E5 |
| SHA1: | 6ED6869A791E2C24B6C3E29FE14B8005FA601444 |
| SHA256: | 66E886133DFEC1626BF44E02BDB75980B143084DA87F3E321B9A280D351D0FF2 |
| SSDEEP: | 393216:r506cOXTIhkZwfqPBQYWgDF0b8TlLDipUQwNkJ27XA8Te+FKjP9WxnppEw5oOgoM:Nb9MeZqYWgDJTdFQPJ2MKzFKL9WpDEwm |
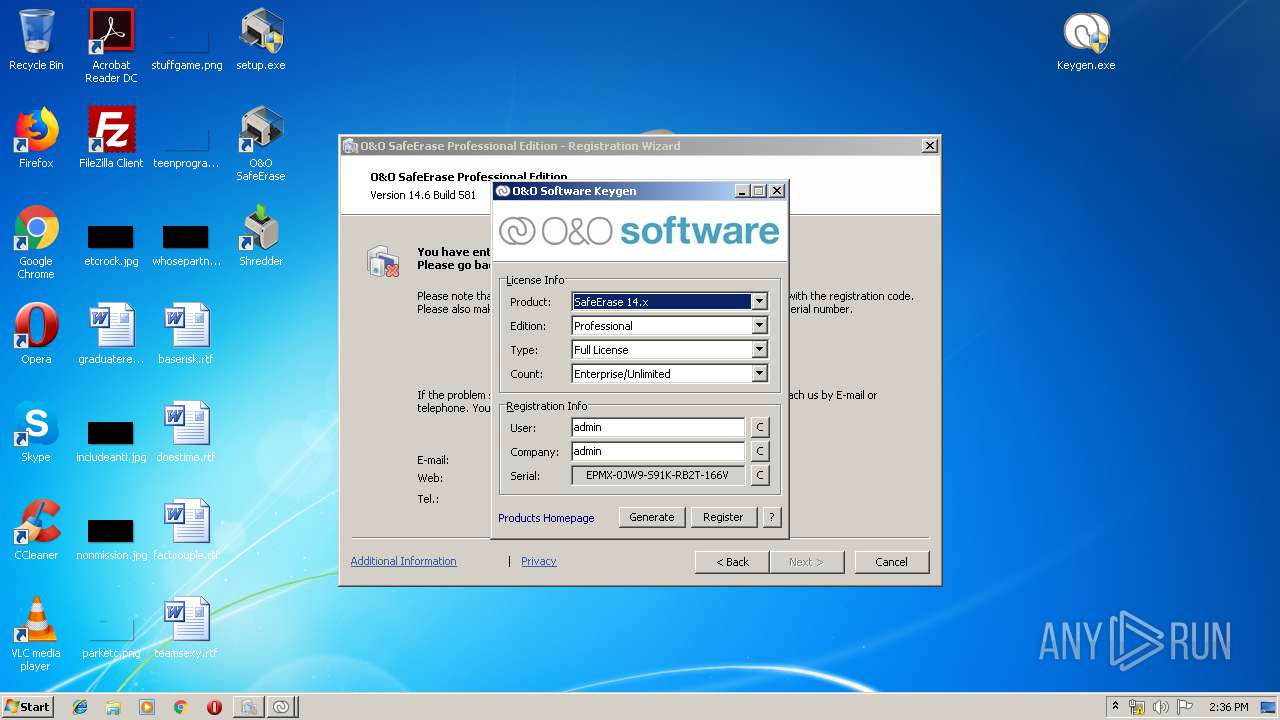
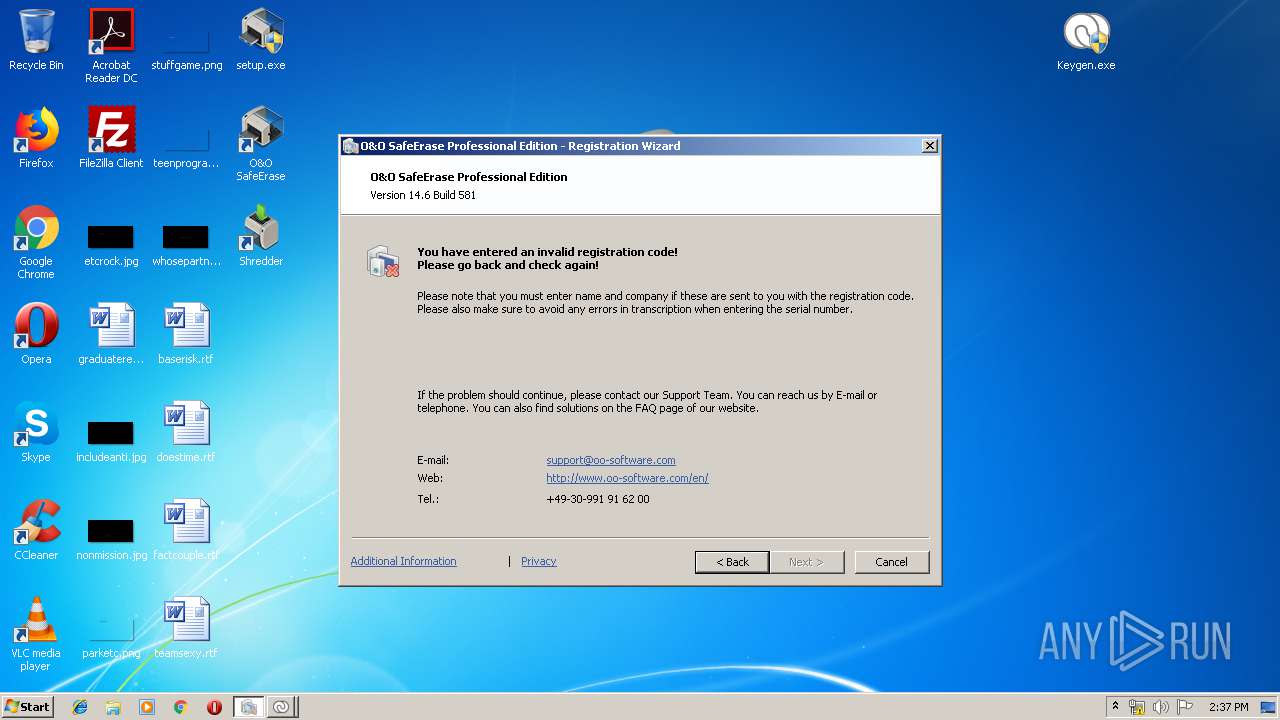
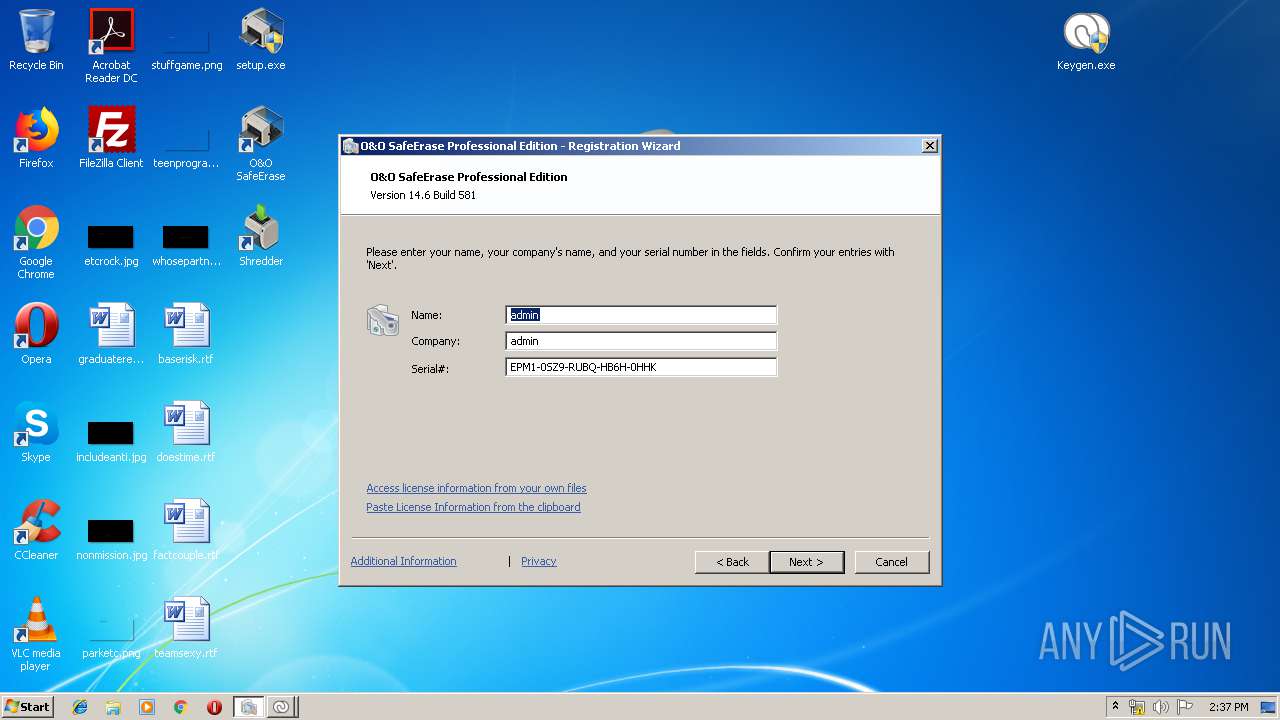
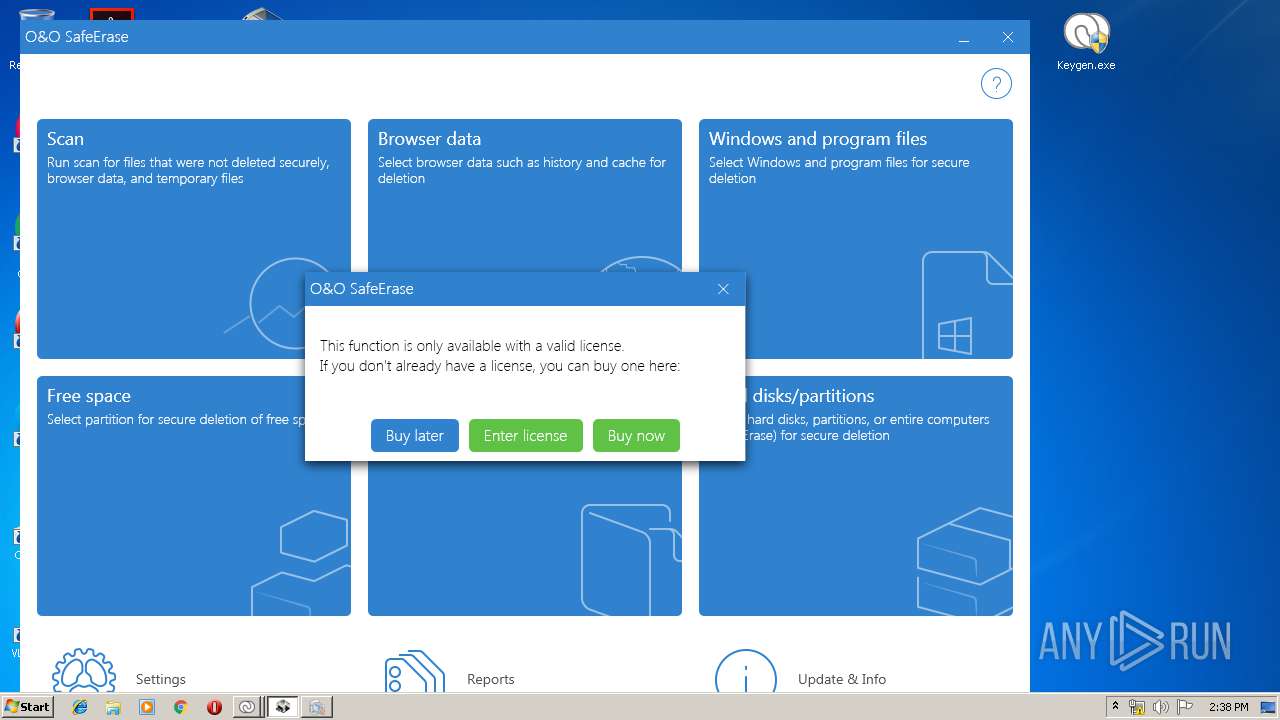
MALICIOUS
Loads dropped or rewritten executable
- SafeEraseAgent.exe (PID: 2724)
- OOSE.EXE (PID: 2252)
- OOSE.EXE (PID: 3656)
- OOSEA.exe (PID: 2624)
- OOSEA.exe (PID: 3848)
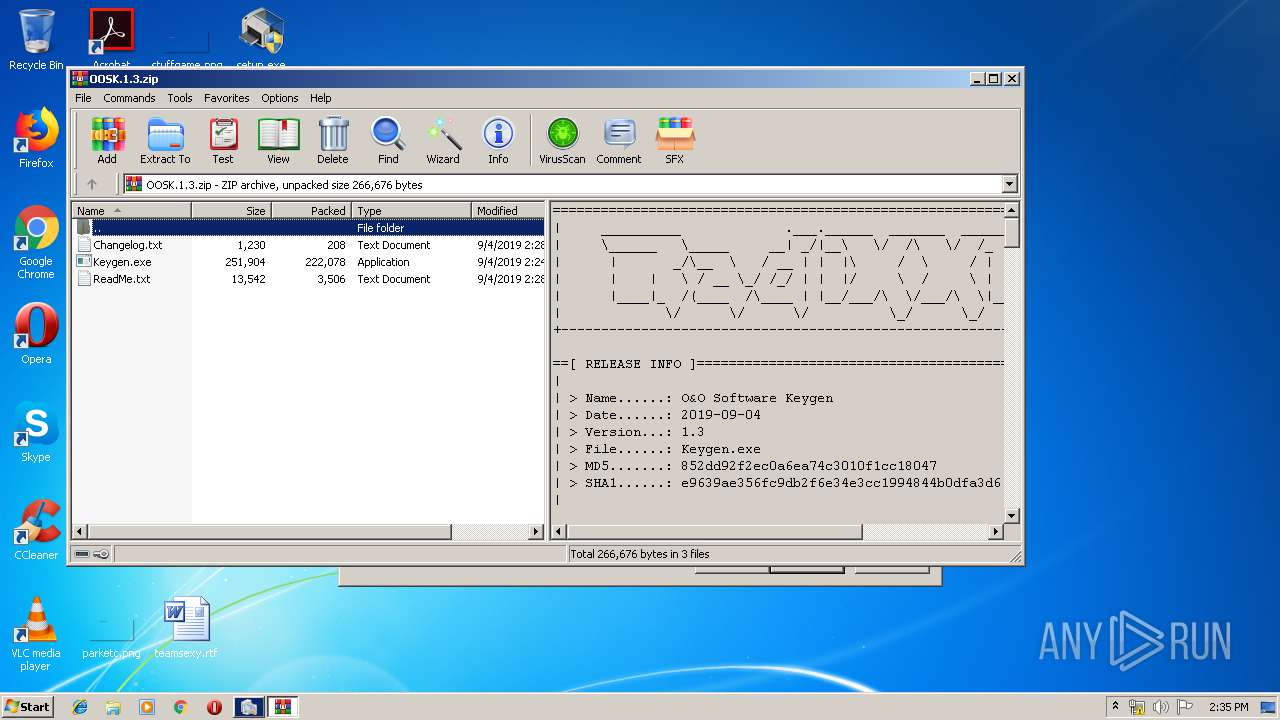
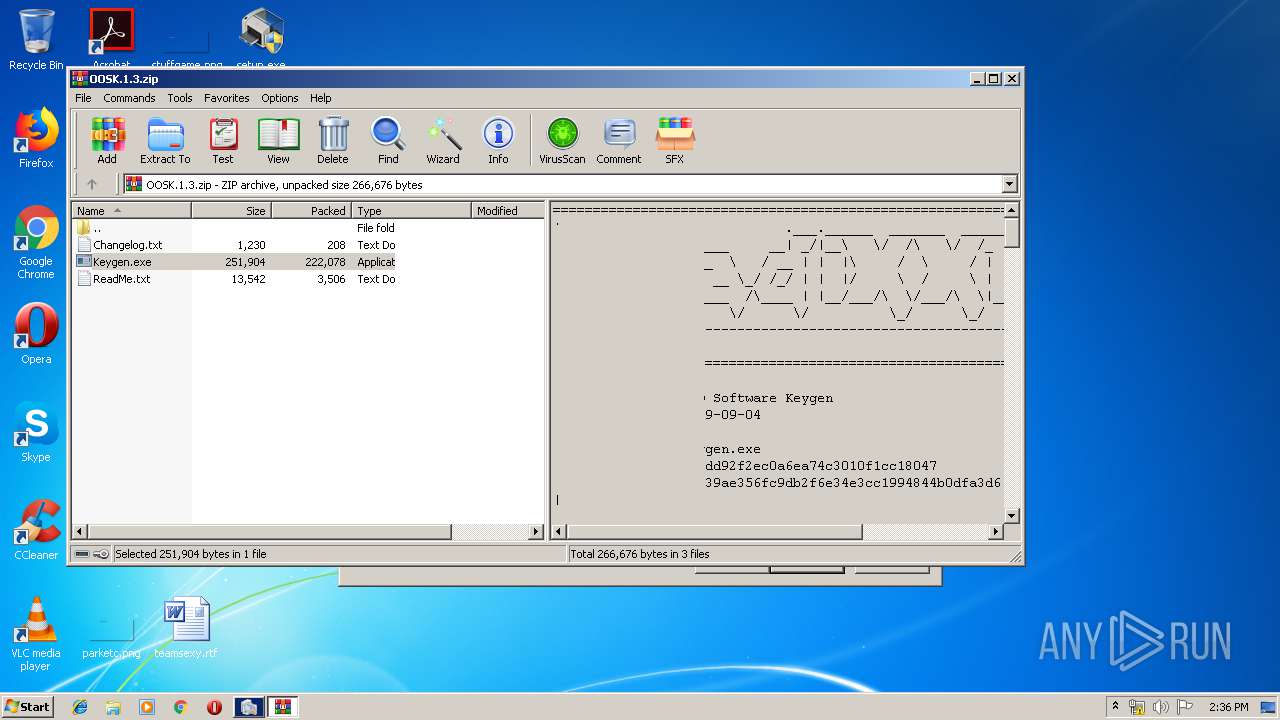
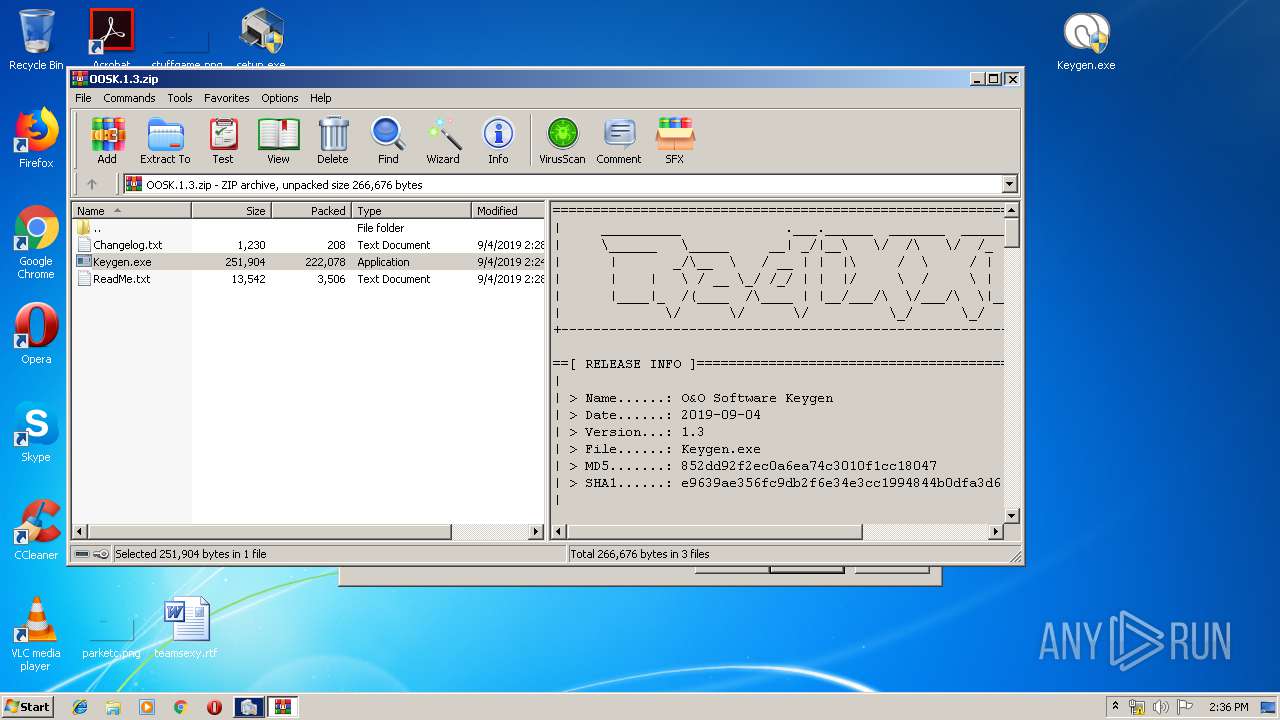
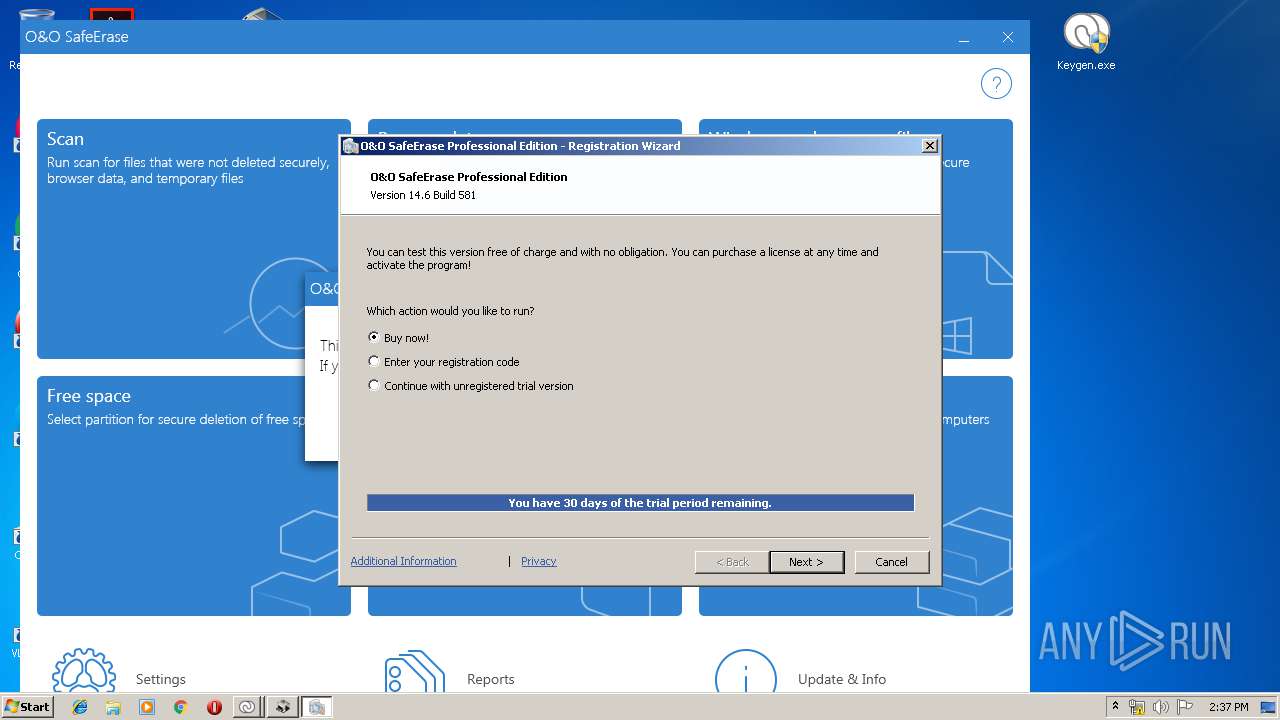
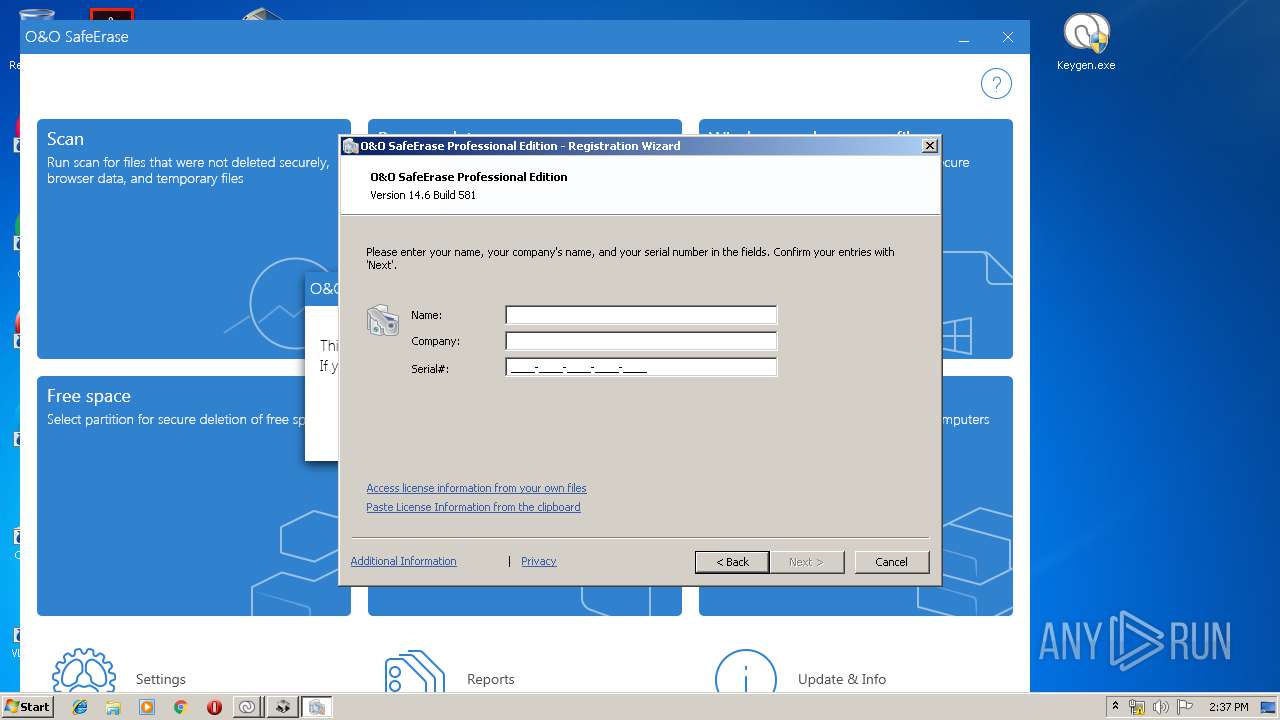
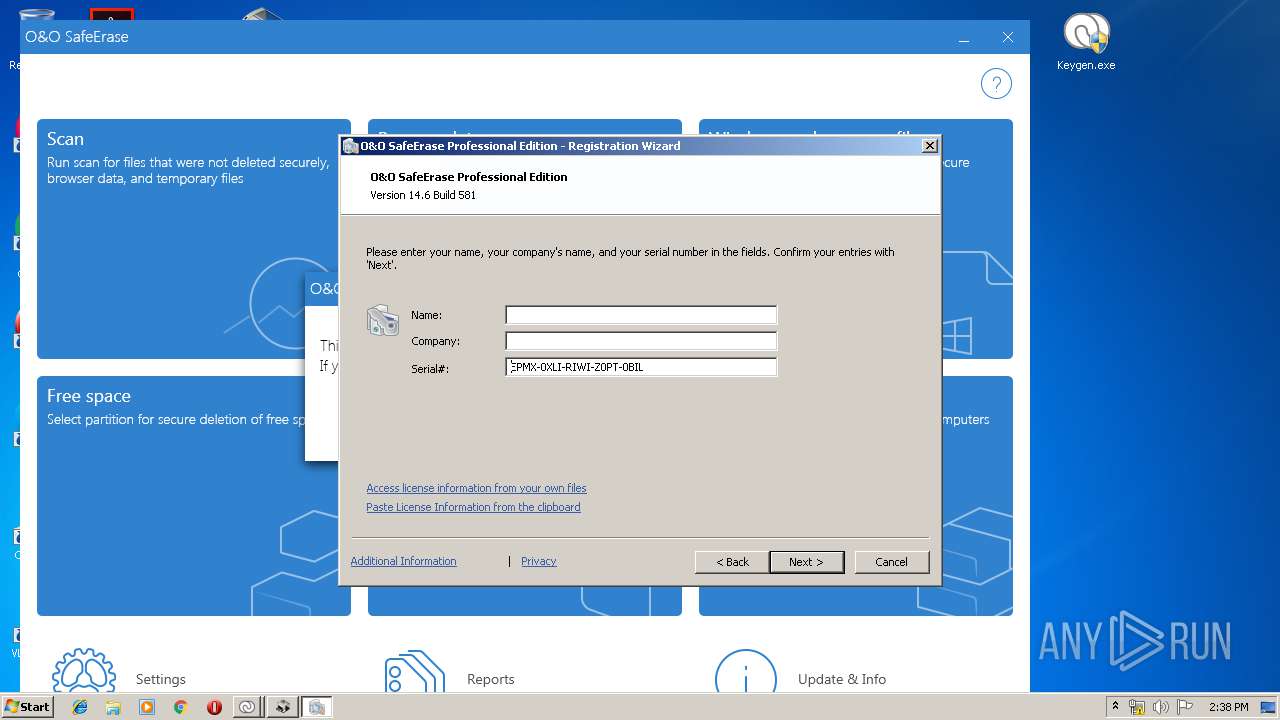
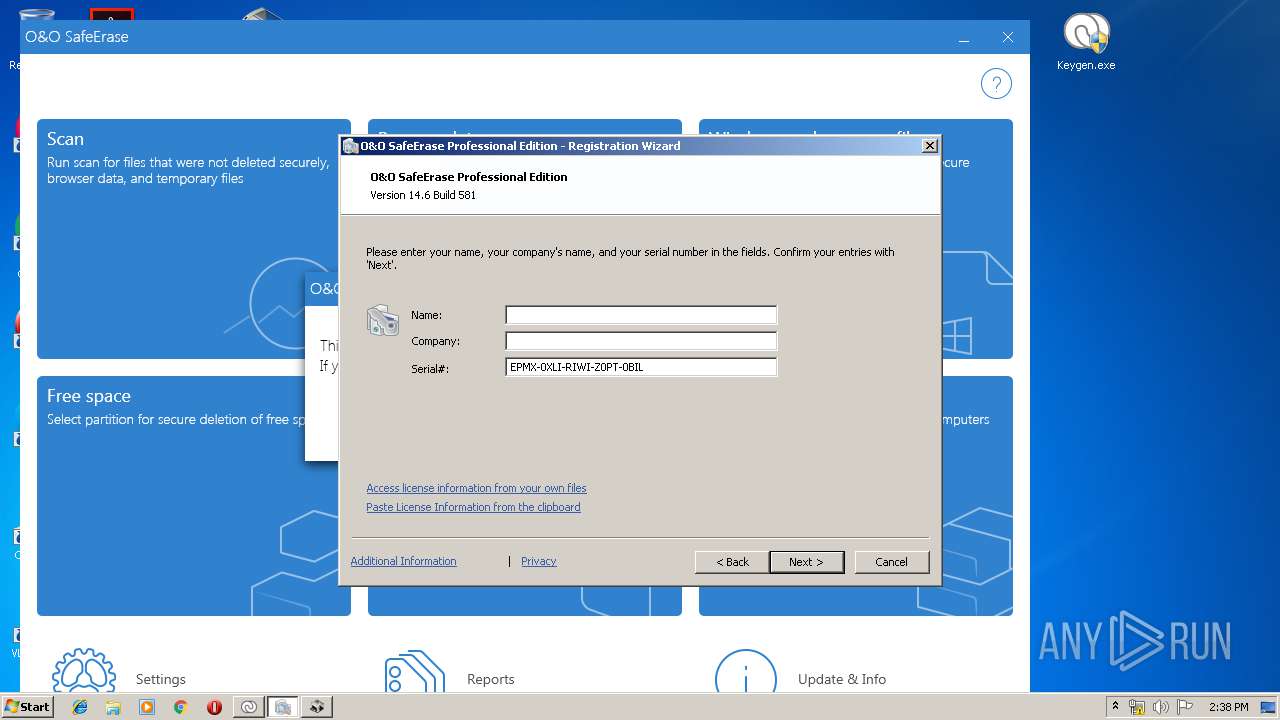
Application was dropped or rewritten from another process
- SafeEraseAgent.exe (PID: 2724)
- OOSE.EXE (PID: 2252)
- OOLiveUpdate.exe (PID: 2752)
- OOLiveUpdateWorker.exe (PID: 392)
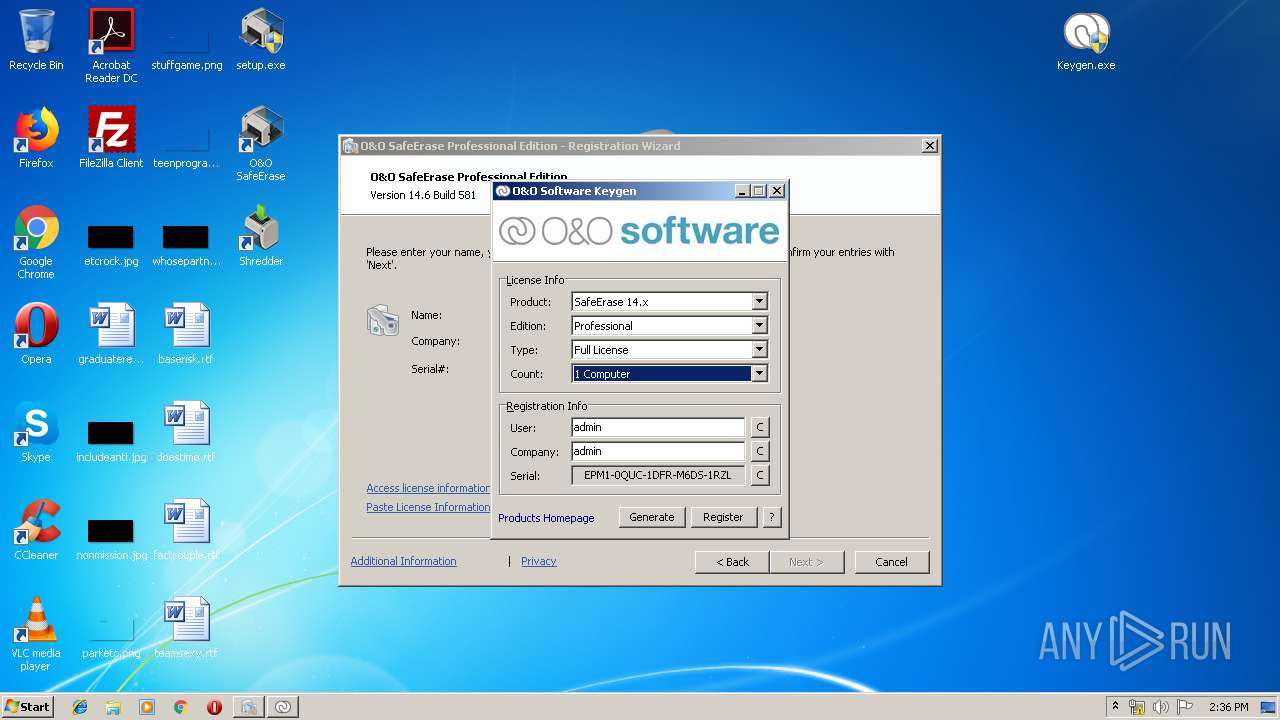
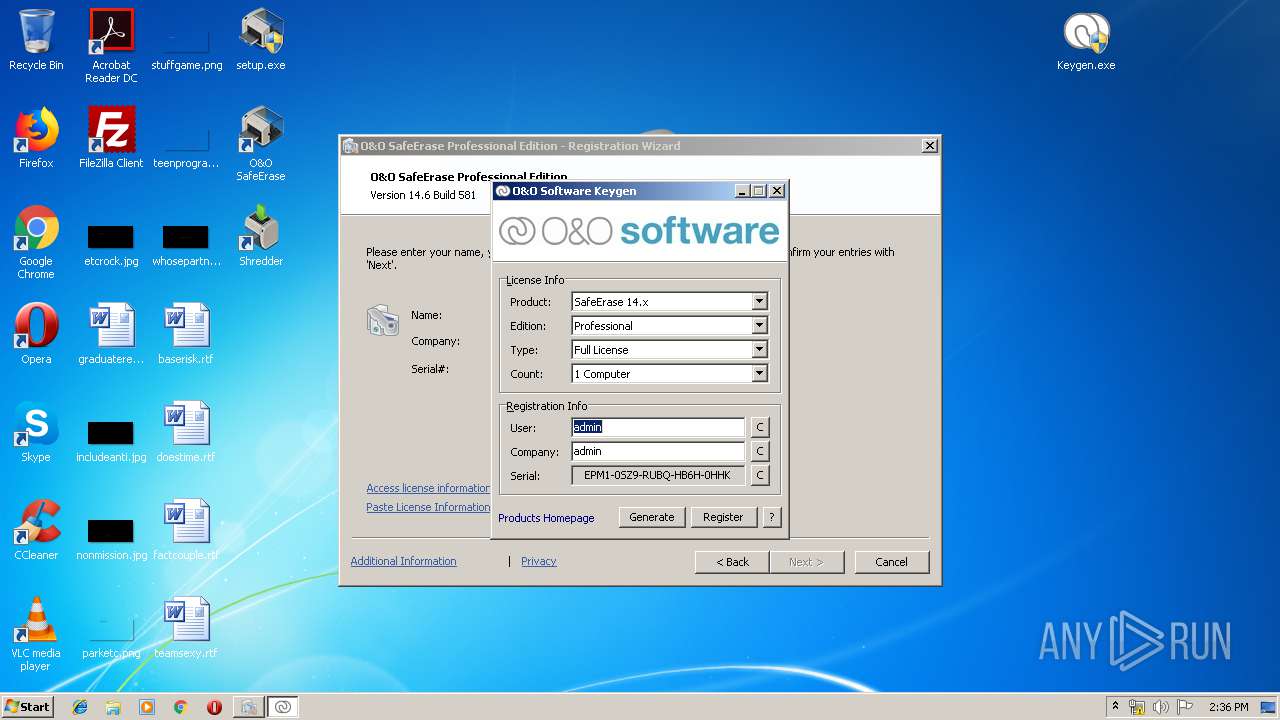
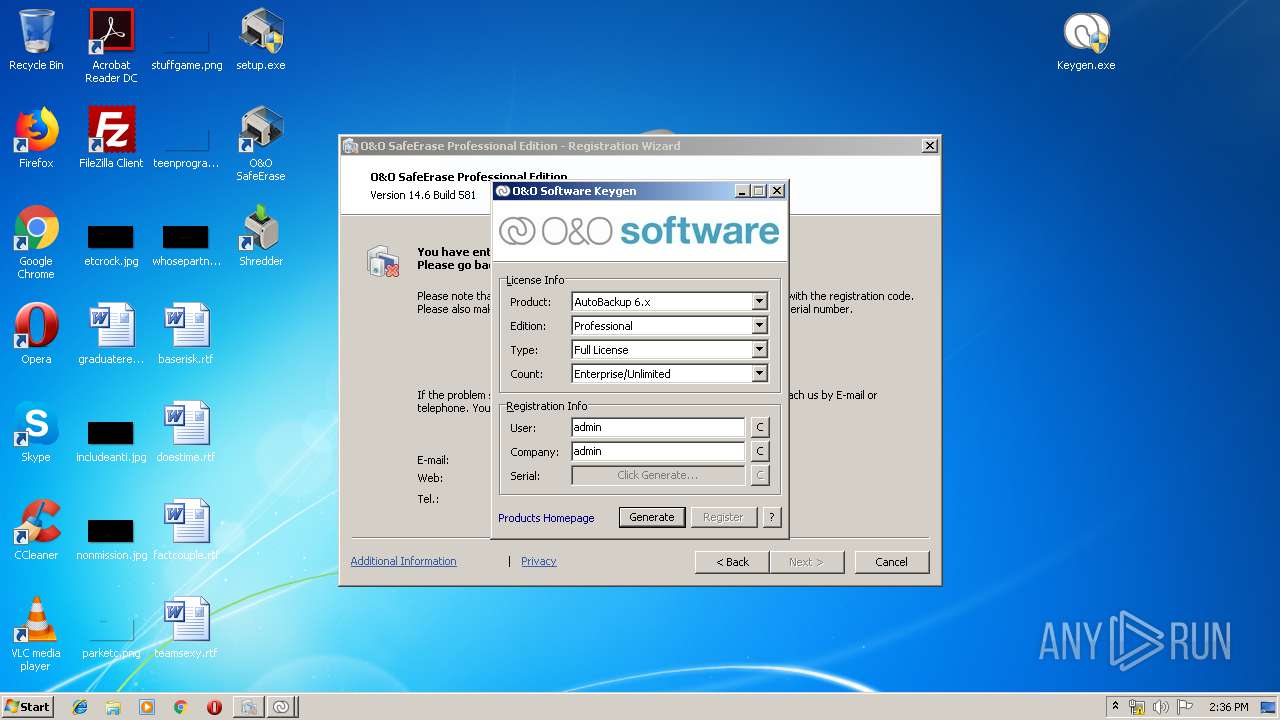
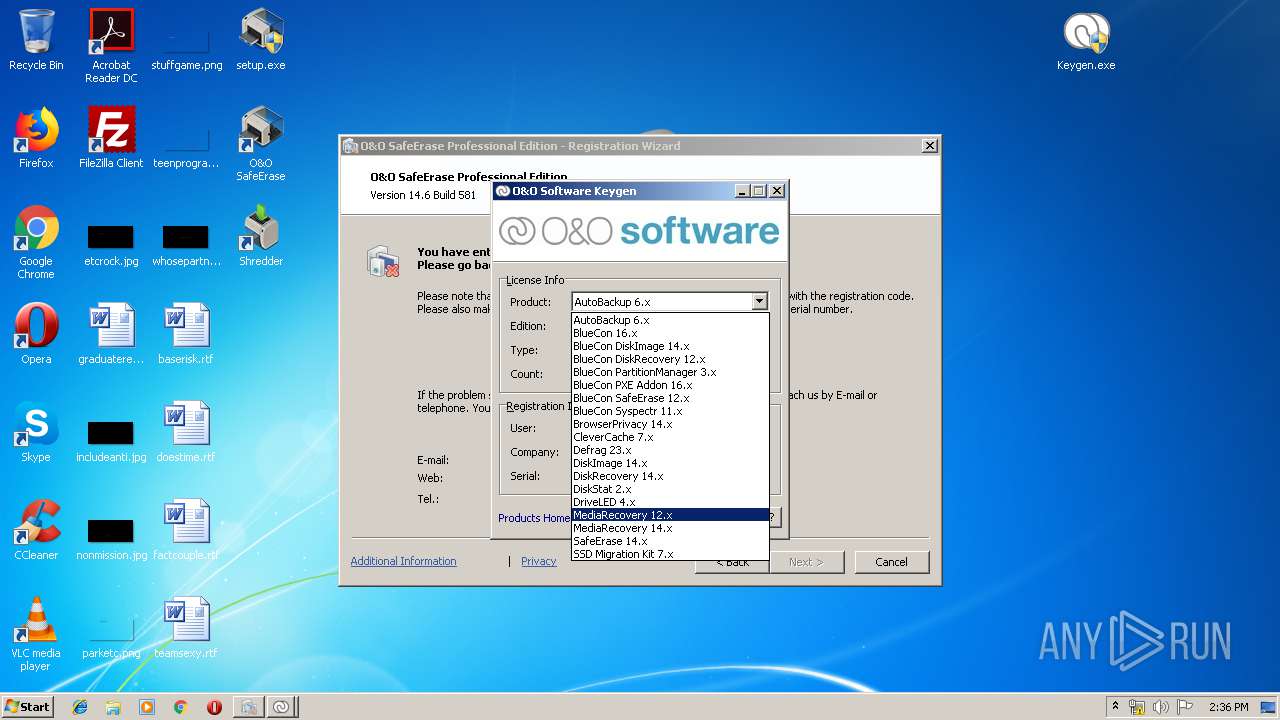
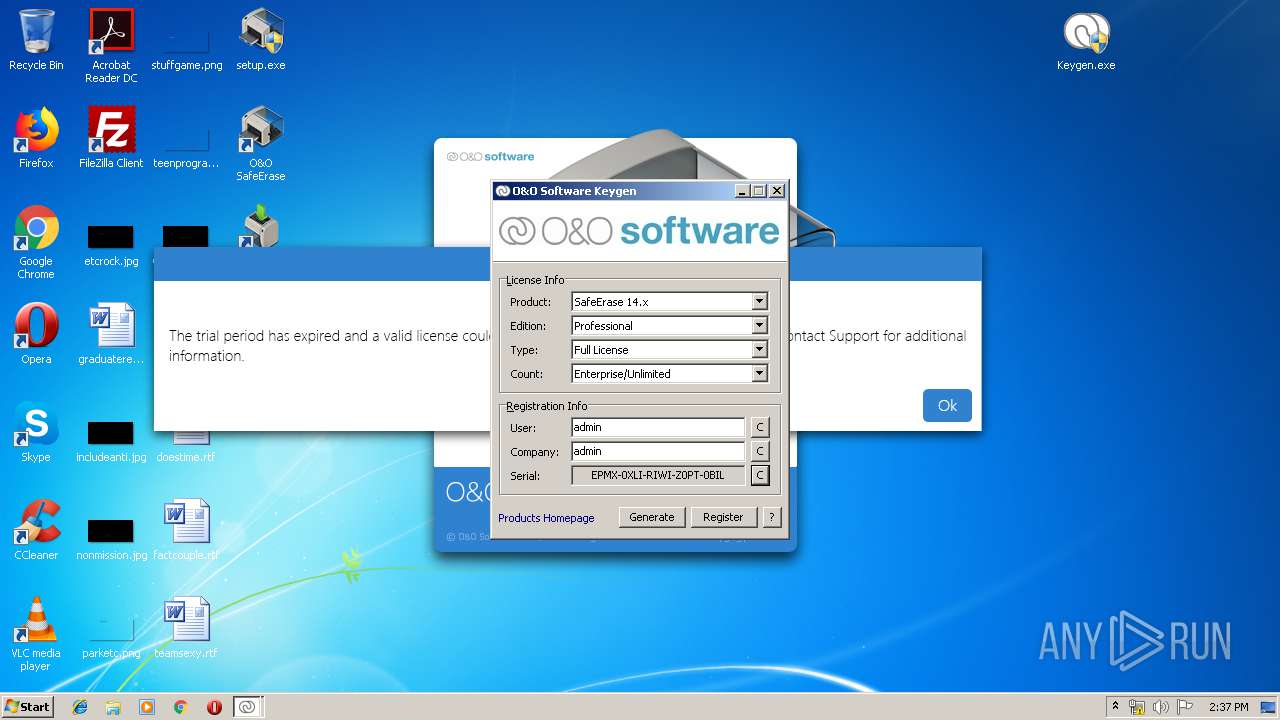
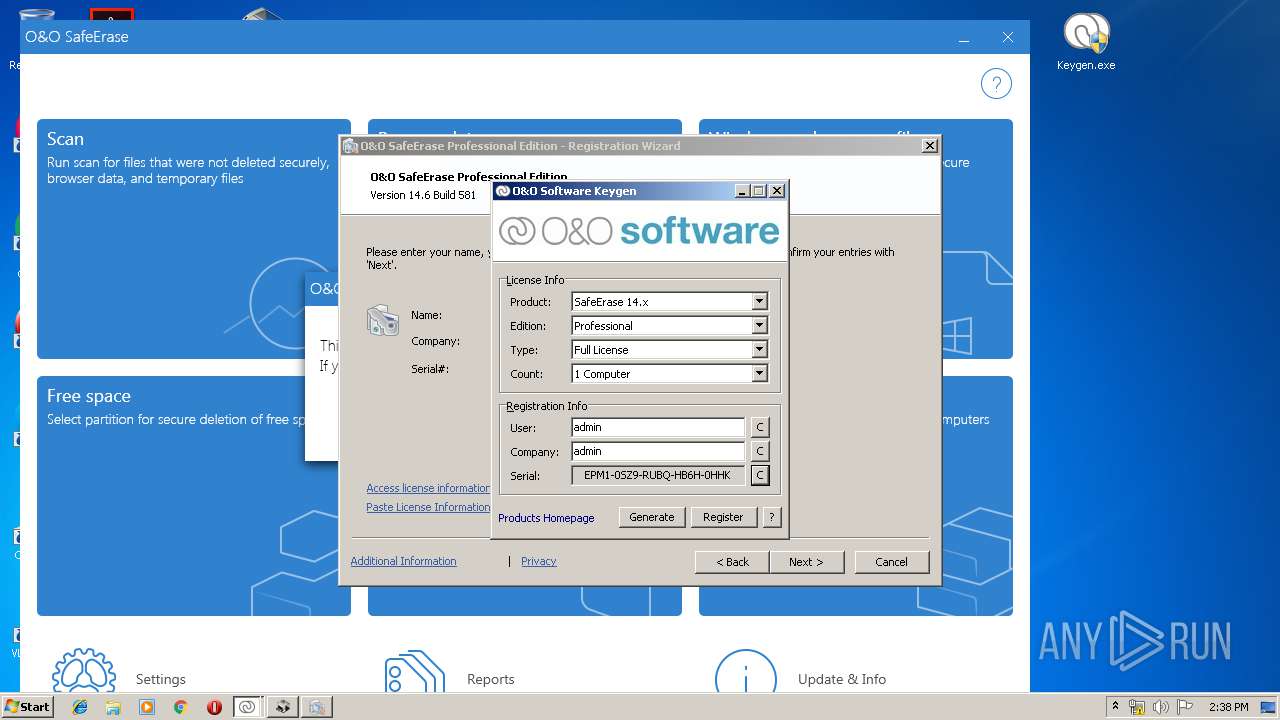
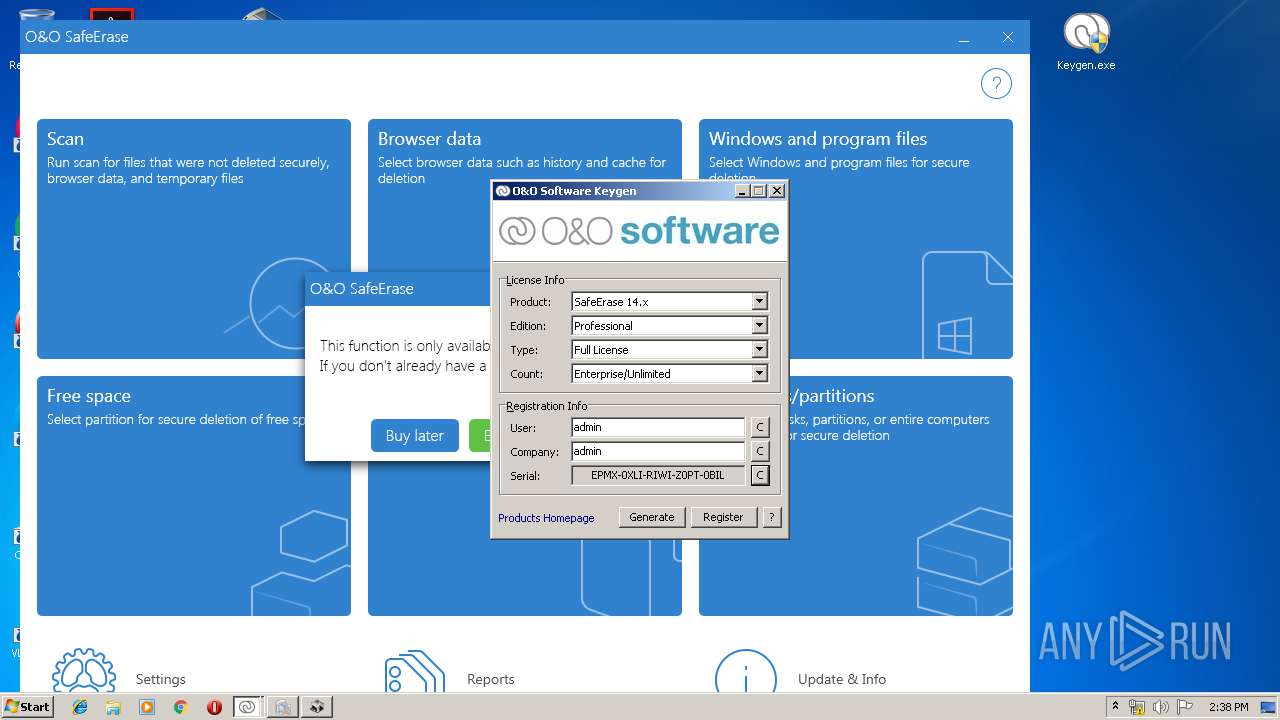
- Keygen.exe (PID: 2248)
- Keygen.exe (PID: 2736)
- Keygen.exe (PID: 3820)
- Keygen.exe (PID: 2136)
- OOSE.EXE (PID: 3656)
- OOLiveUpdate.exe (PID: 1780)
- OOSEA.exe (PID: 3184)
- OOSEA.exe (PID: 2624)
- OOSEA.exe (PID: 2448)
- OOSEA.exe (PID: 3848)
Changes settings of System certificates
- OOLiveUpdate.exe (PID: 2752)
SUSPICIOUS
Creates files in the program directory
- setup.exe (PID: 1712)
Executed as Windows Service
- vssvc.exe (PID: 2572)
- SafeEraseAgent.exe (PID: 2724)
- vds.exe (PID: 460)
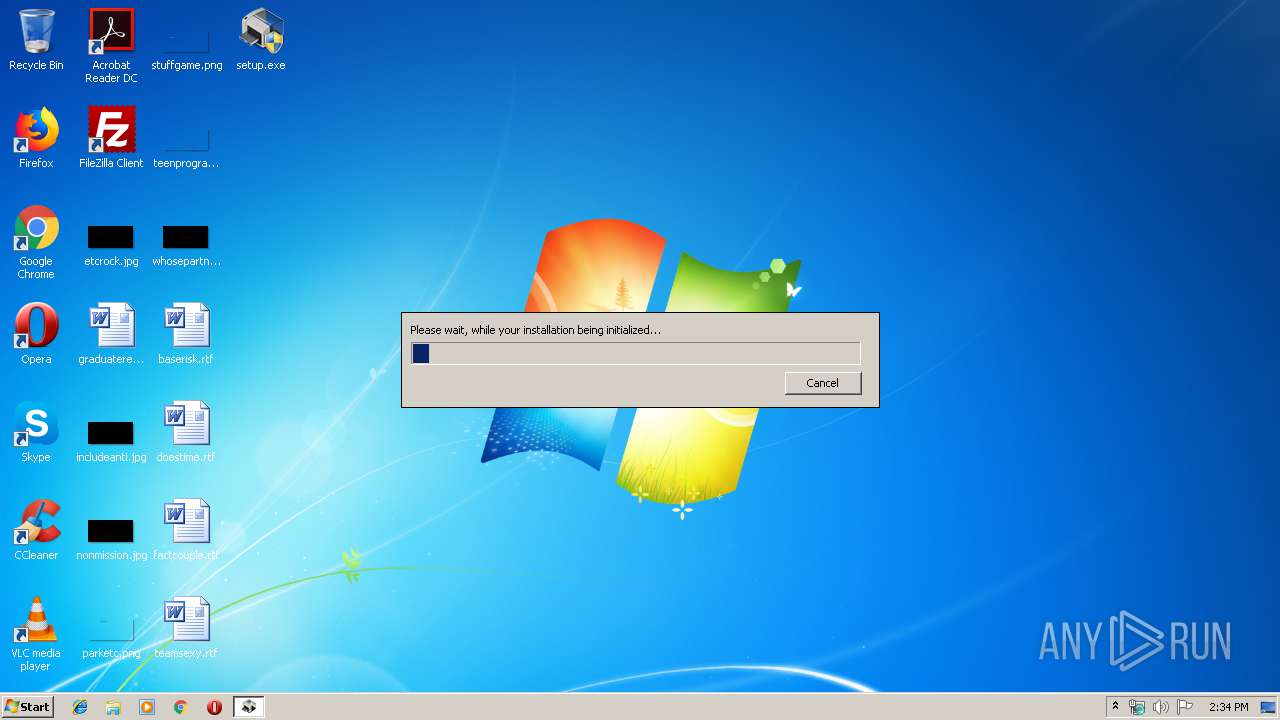
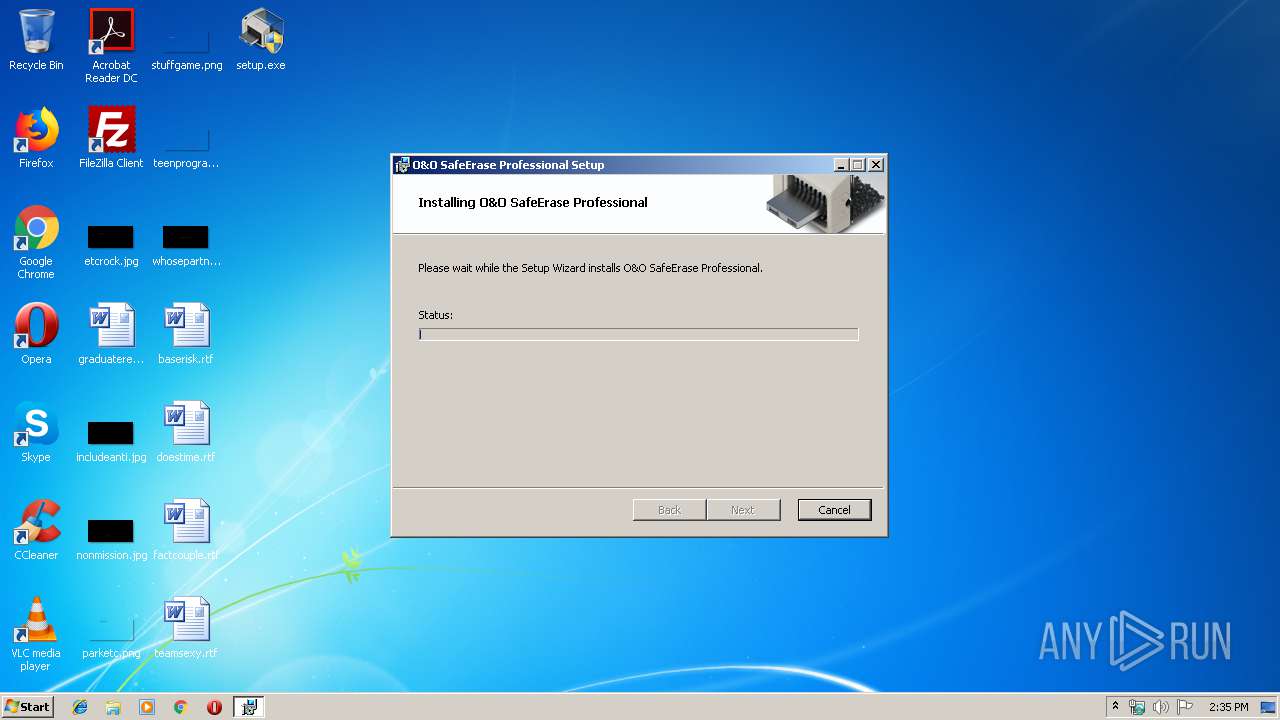
Starts Microsoft Installer
- setup.exe (PID: 1712)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2408)
- OOLiveUpdate.exe (PID: 2752)
Creates COM task schedule object
- msiexec.exe (PID: 2408)
Executed via COM
- vdsldr.exe (PID: 2392)
Low-level read access rights to disk partition
- vds.exe (PID: 460)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2932)
Reads Internet Cache Settings
- OOSE.EXE (PID: 2252)
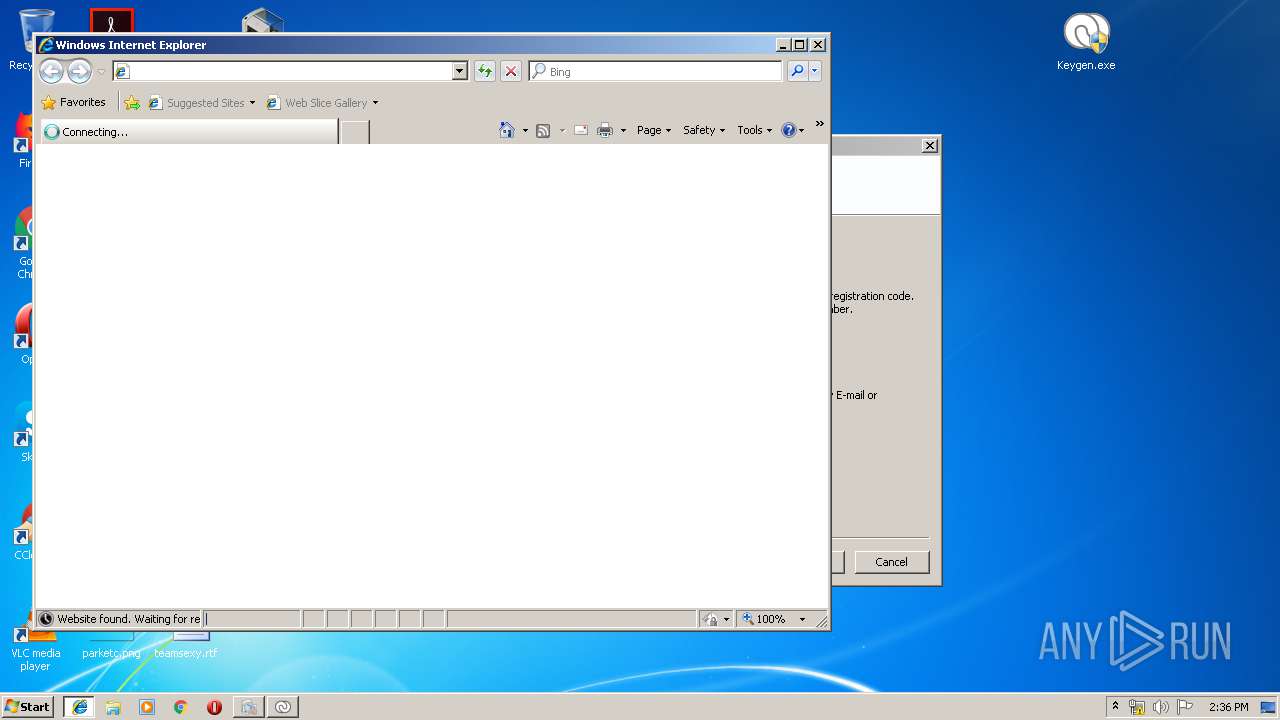
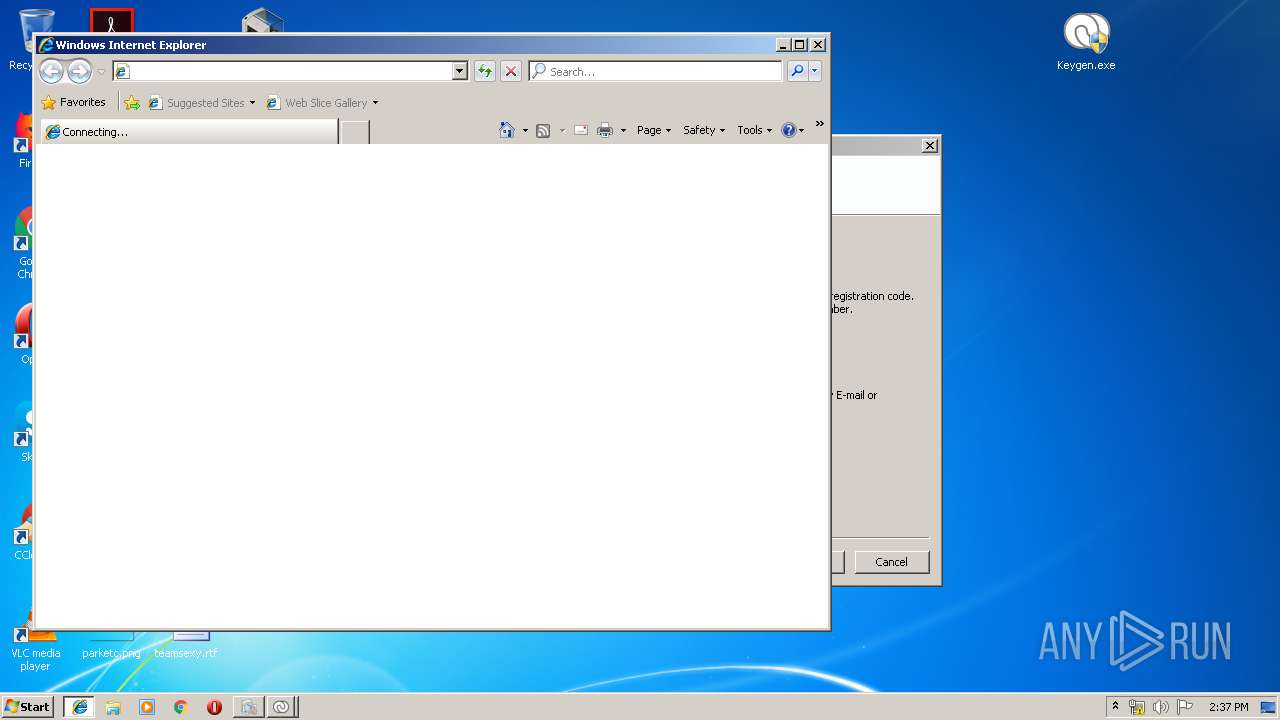
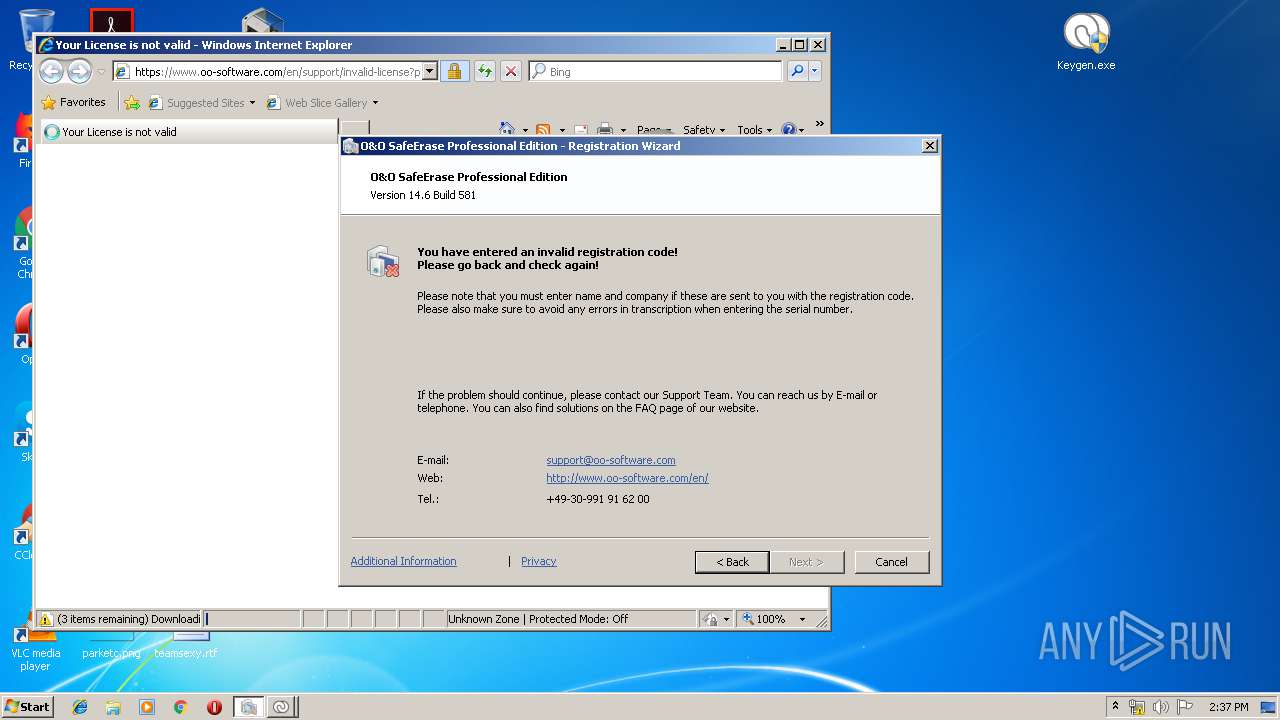
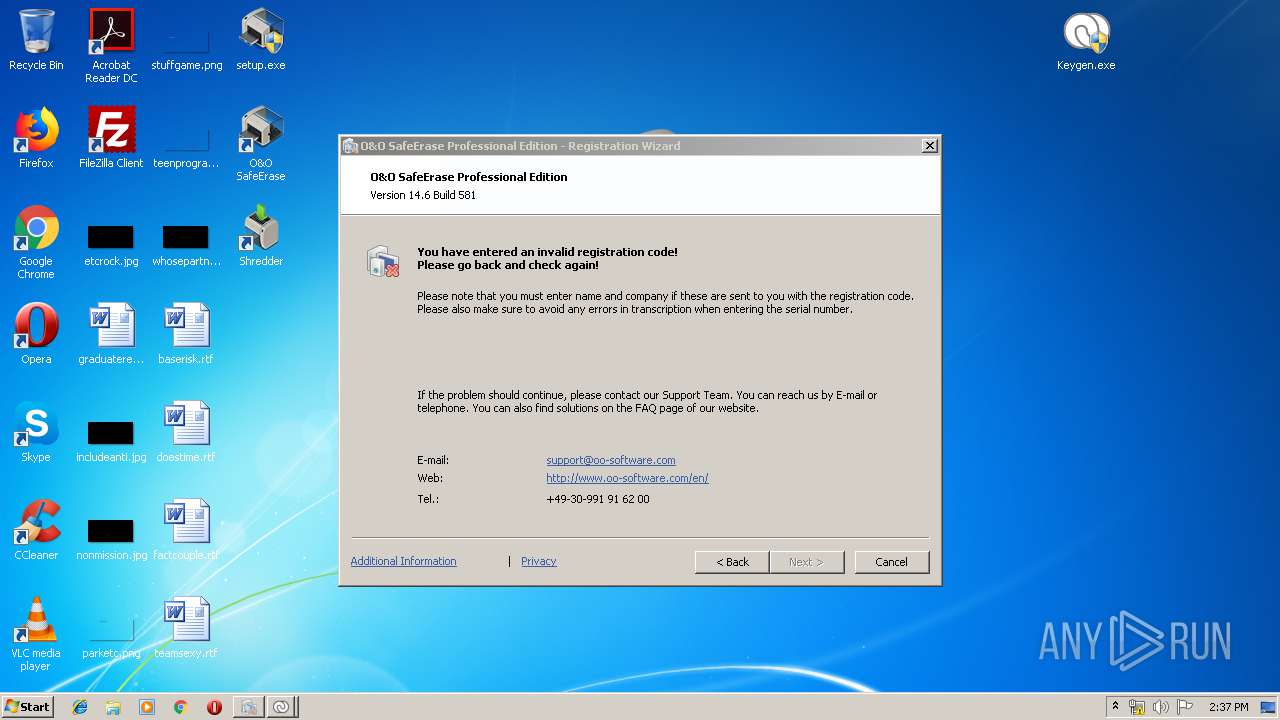
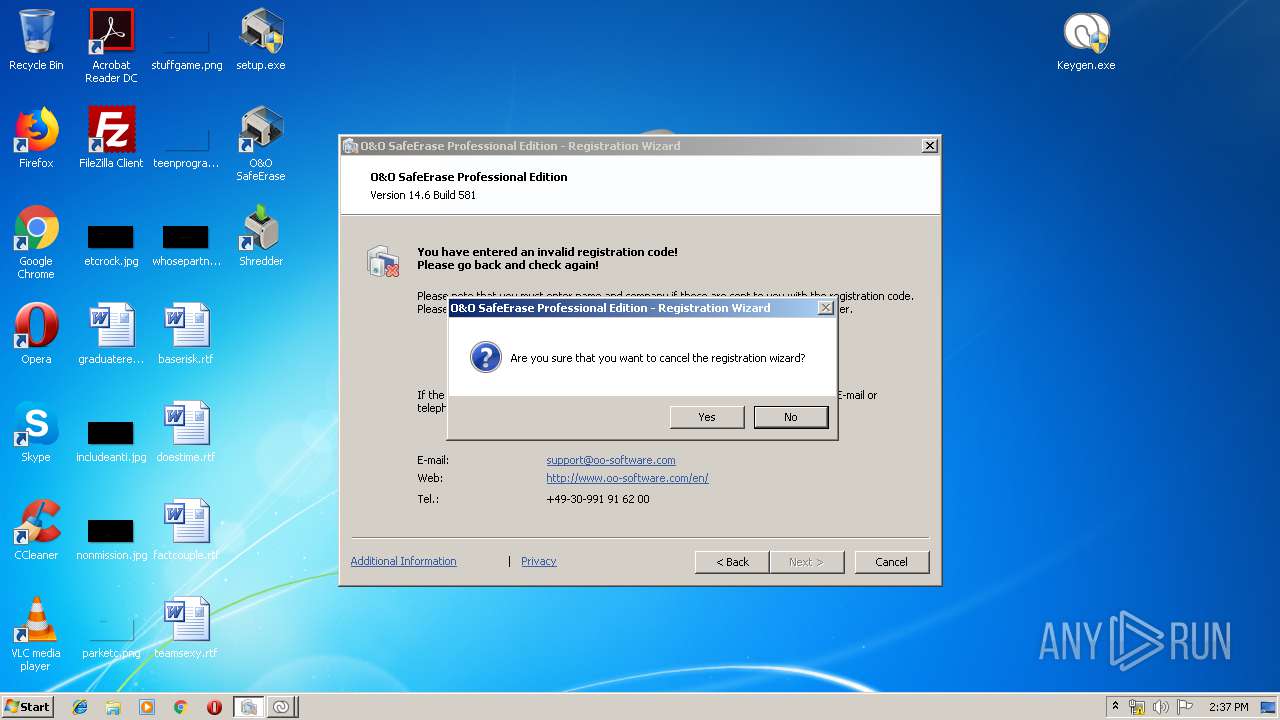
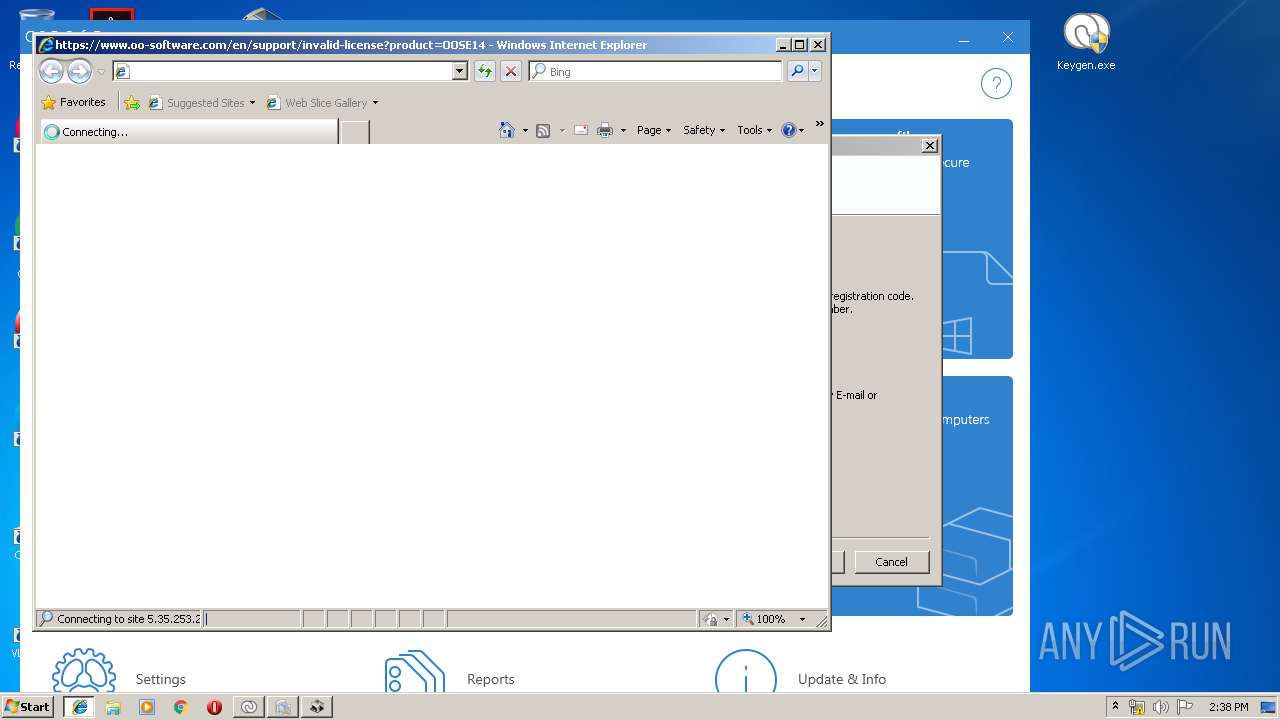
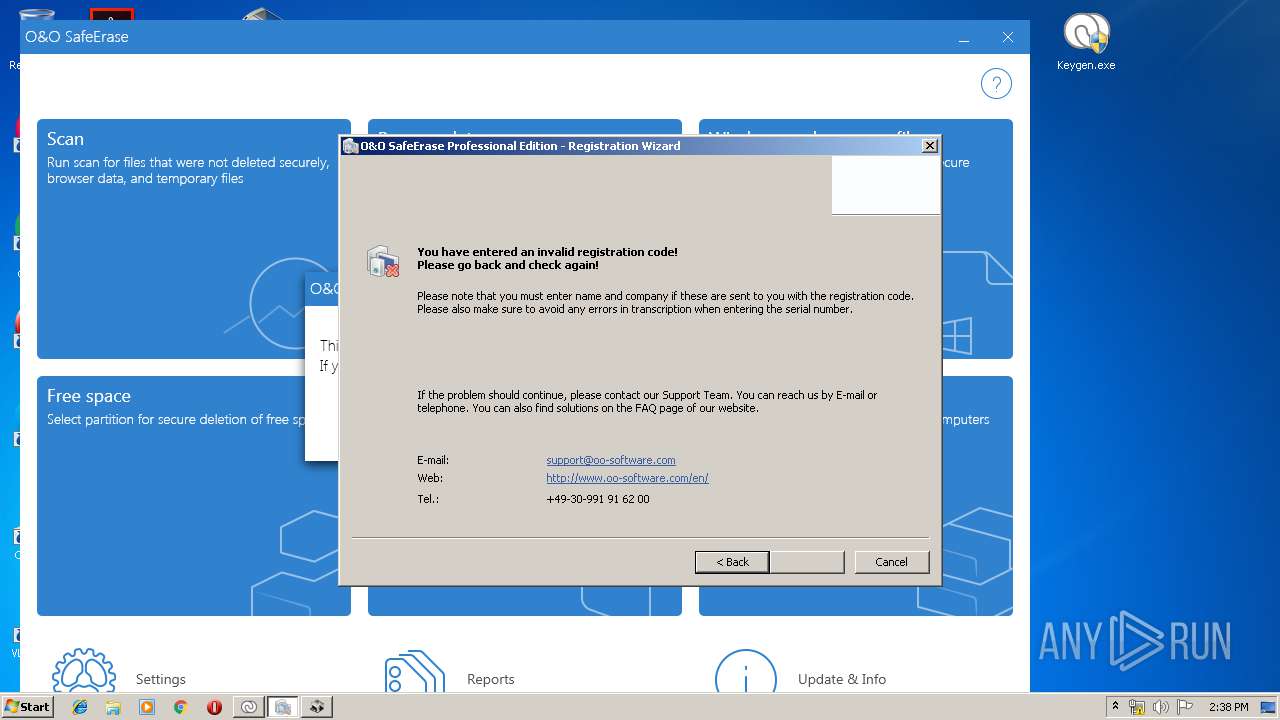
Starts Internet Explorer
- OOSE.EXE (PID: 2252)
- OOSEA.exe (PID: 3848)
Reads Windows owner or organization settings
- SafeEraseAgent.exe (PID: 2724)
Reads the Windows organization settings
- SafeEraseAgent.exe (PID: 2724)
Searches for installed software
- OOSE.EXE (PID: 3656)
- OOSE.EXE (PID: 2252)
INFO
Searches for installed software
- msiexec.exe (PID: 2408)
Reads the hosts file
- chrome.exe (PID: 2932)
- chrome.exe (PID: 592)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2572)
Manual execution by user
- chrome.exe (PID: 2932)
- Keygen.exe (PID: 2248)
- Keygen.exe (PID: 2736)
- Keygen.exe (PID: 2136)
- Keygen.exe (PID: 3820)
- OOSE.EXE (PID: 3656)
Application launched itself
- msiexec.exe (PID: 2408)
- chrome.exe (PID: 2932)
- iexplore.exe (PID: 3716)
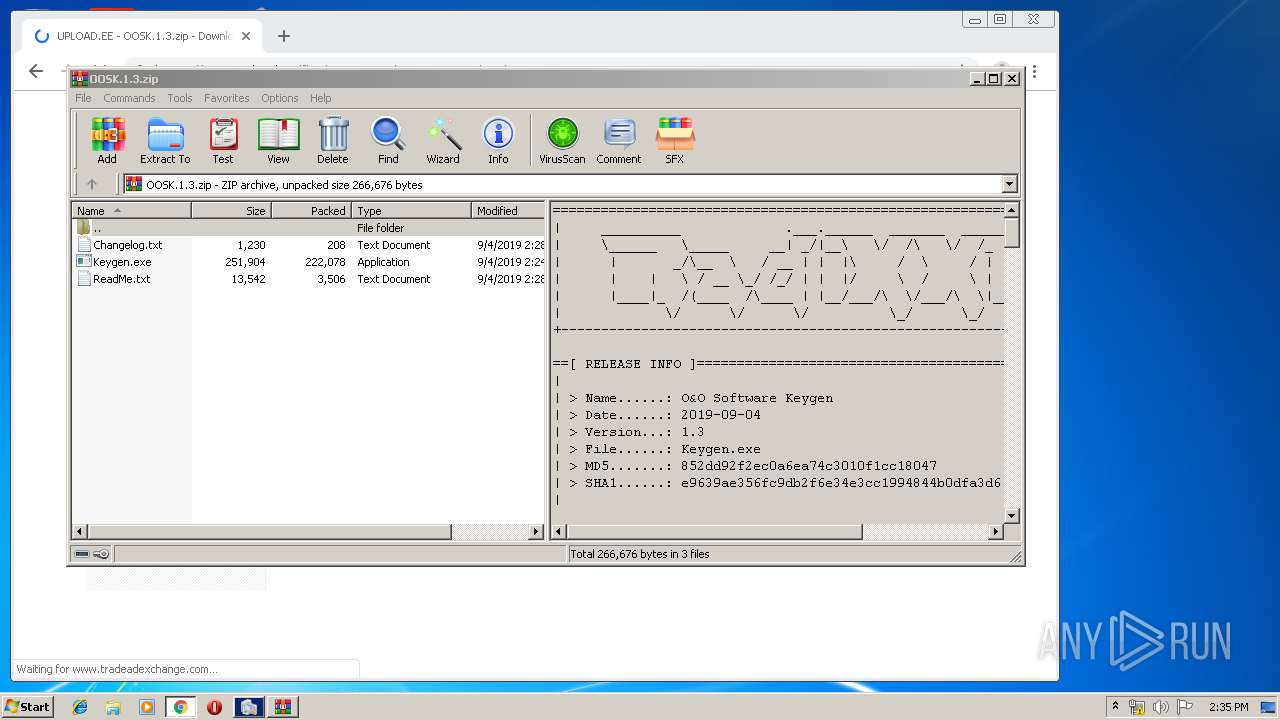
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2408)
Creates a software uninstall entry
- msiexec.exe (PID: 2408)
Changes settings of System certificates
- chrome.exe (PID: 592)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1812)
- MsiExec.exe (PID: 1344)
- MsiExec.exe (PID: 2352)
Reads Internet Cache Settings
- chrome.exe (PID: 2932)
- iexplore.exe (PID: 1504)
- iexplore.exe (PID: 1016)
Creates files in the user directory
- chrome.exe (PID: 2932)
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 1504)
- iexplore.exe (PID: 1016)
Creates files in the program directory
- msiexec.exe (PID: 2408)
Changes internet zones settings
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 1024)
Reads internet explorer settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 1016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:10:11 18:48:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 206336 |
| InitializedDataSize: | 429568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a7e3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
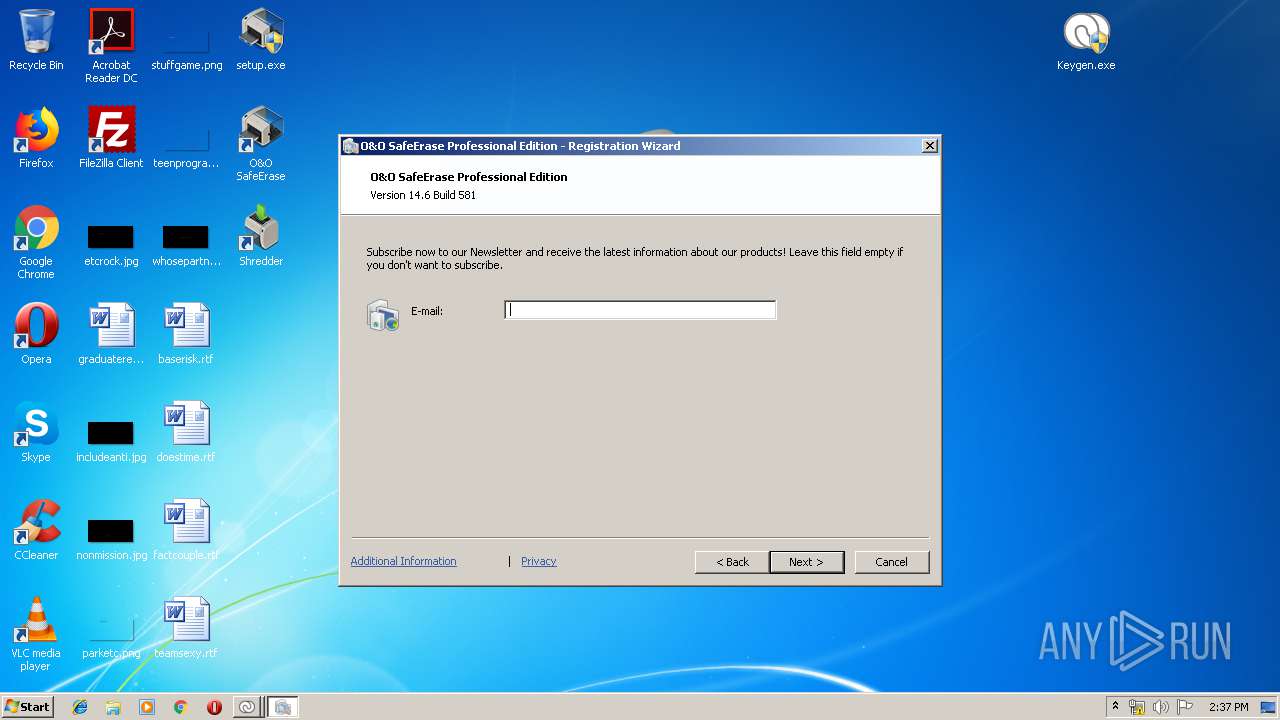
| FileVersionNumber: | 14.6.581.0 |
| ProductVersionNumber: | 14.6.581.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| CompanyName: | - |
| Comments: | A:1000$L:1033$O:MsiLanguage |
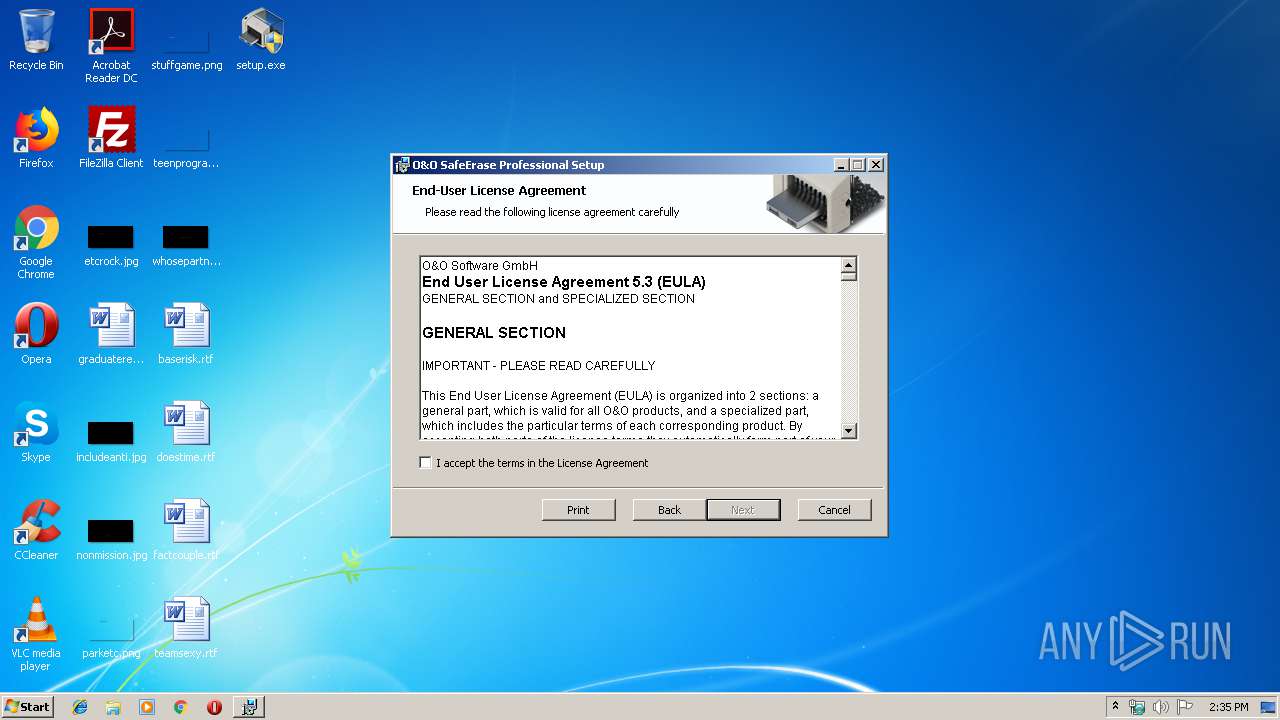
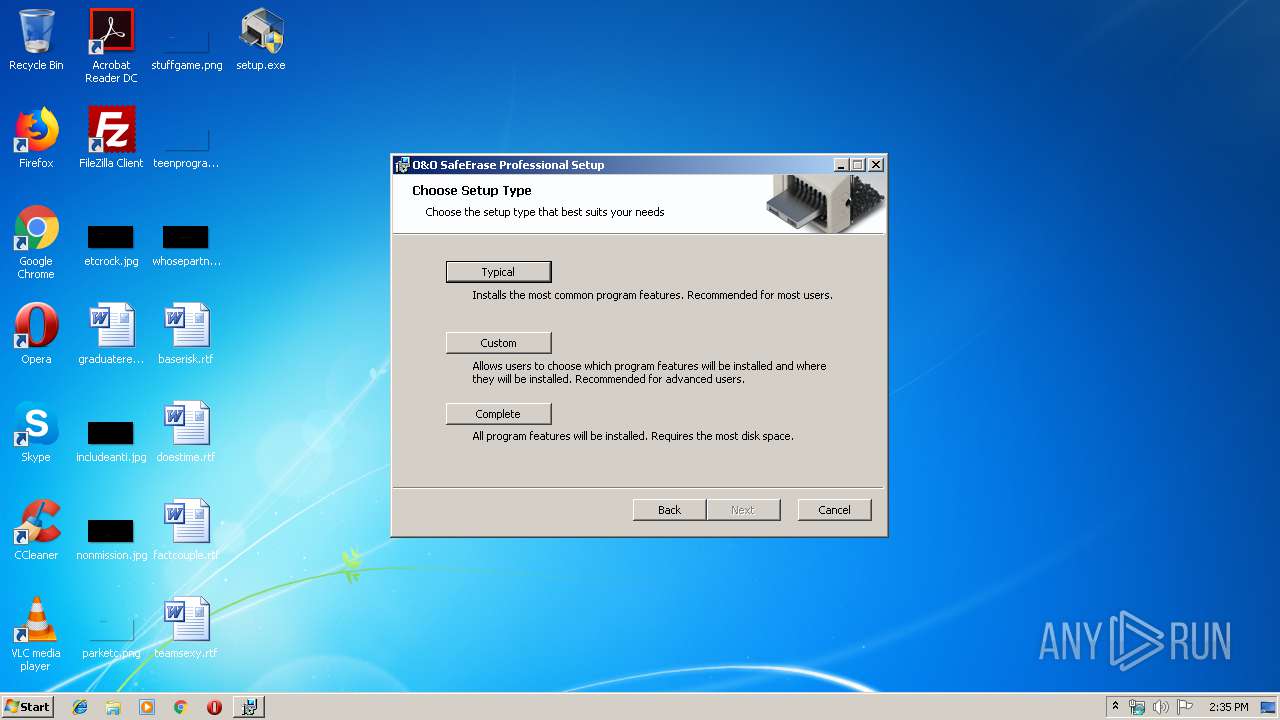
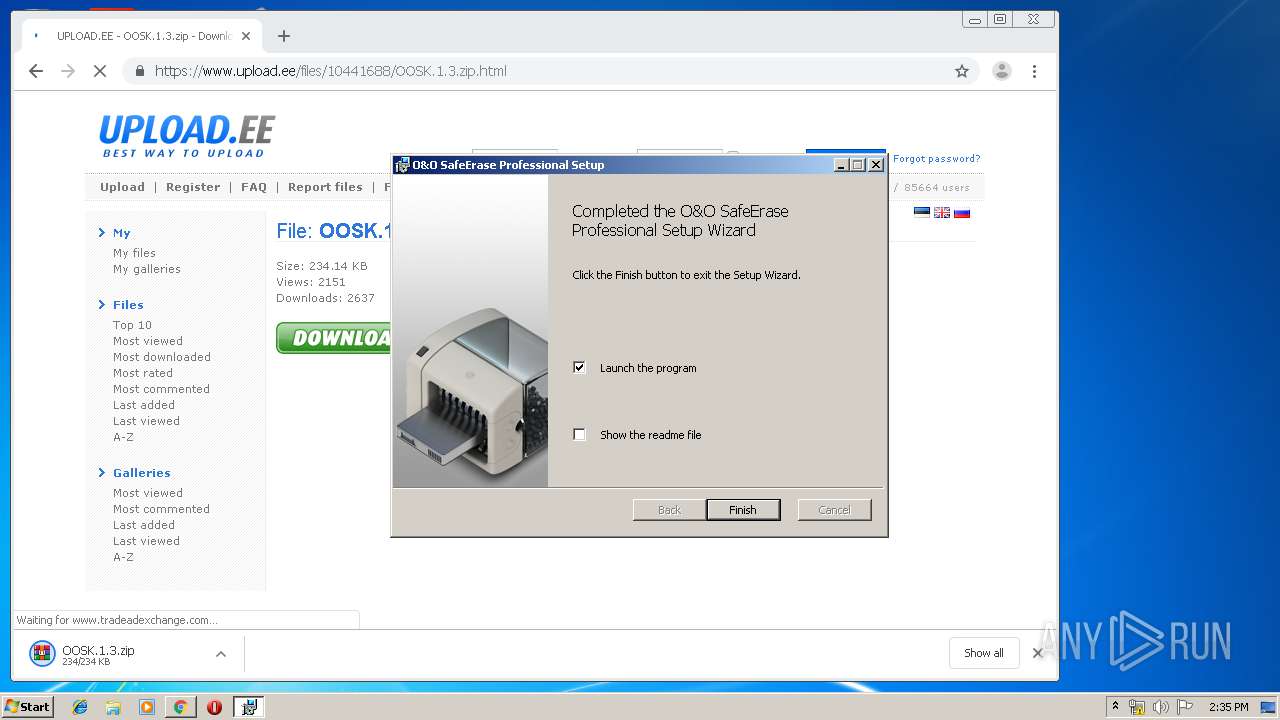
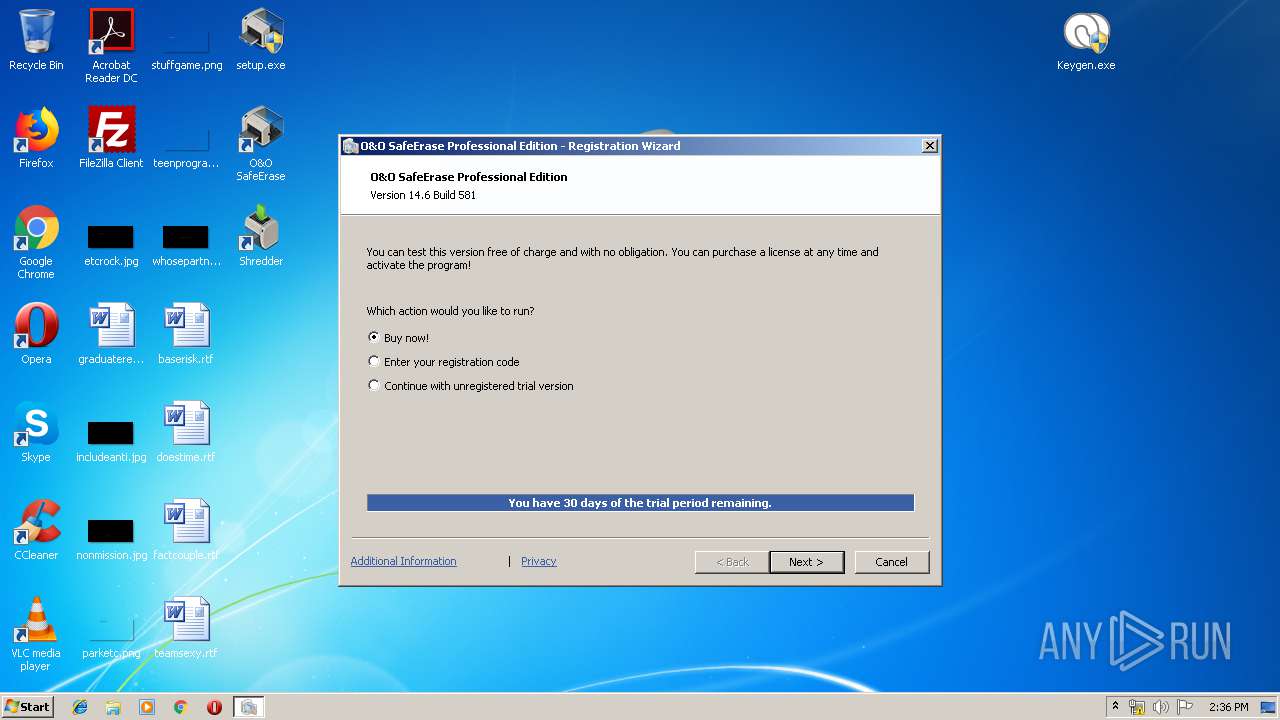
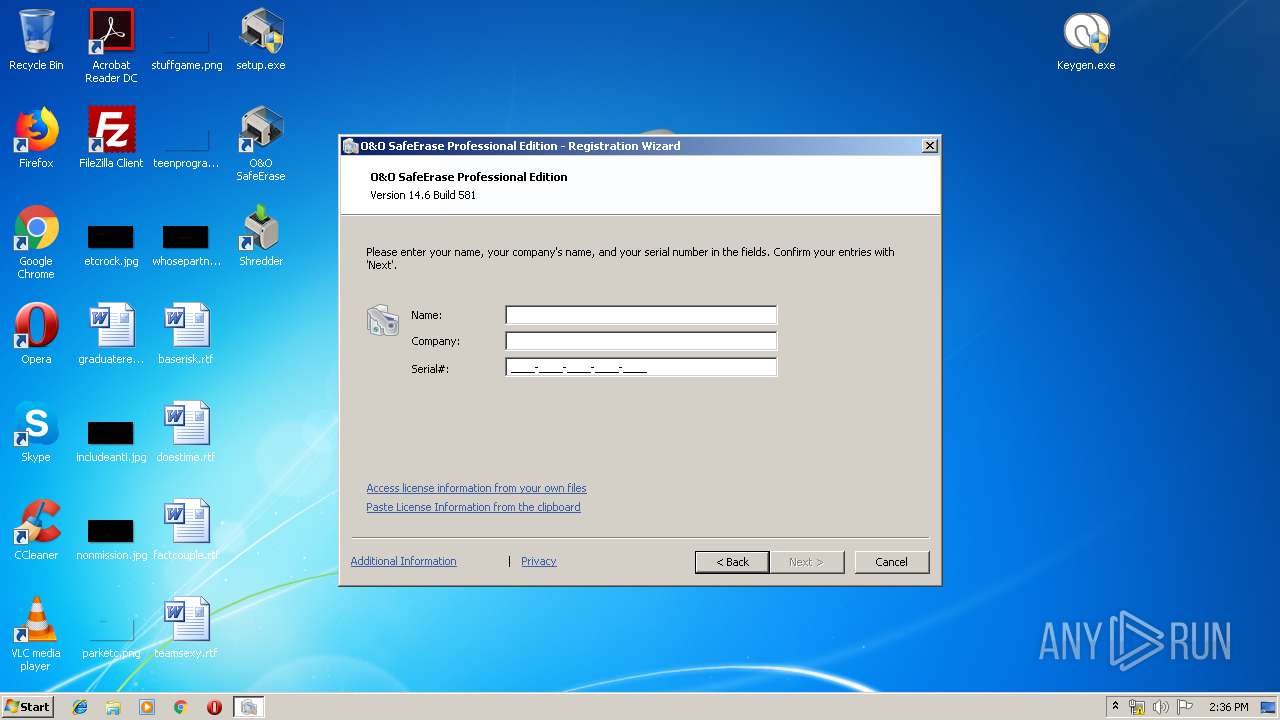
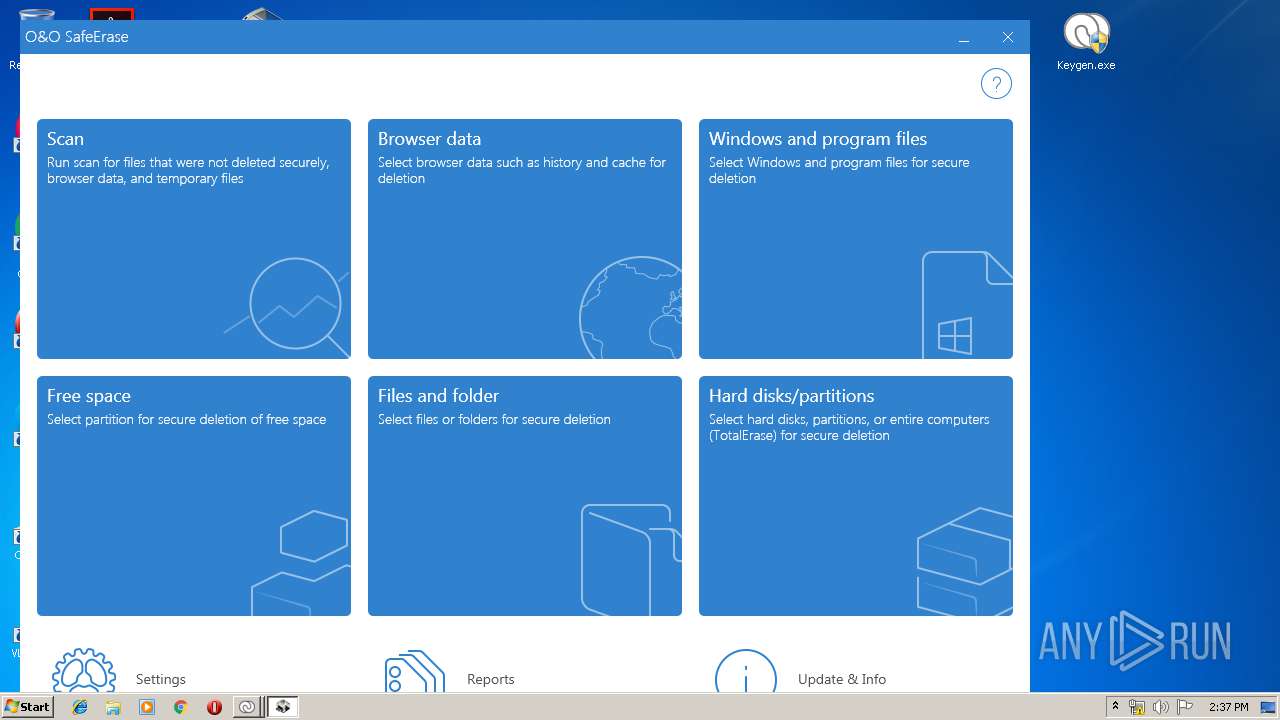
| FileDescription: | O&O SafeErase Professional Setup |
| FileVersion: | 14.6.581 |
| InternalName: | Stub.exe |
| LegalCopyright: | O&O Software GmbH |
| OriginalFileName: | Stub.exe |
| ProductName: | O&O SafeErase Professional |
| ProductVersion: | 14.6.581 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Oct-2017 16:48:18 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | O&O Software GmbH |
| Comments: | A:1000$L:1031 |
| FileDescription: | - |
| FileVersion: | 6.0.242 |
| InternalName: | Stub.exe |
| LegalCopyright: | Copyright (C) 2012 |
| OriginalFilename: | Stub.exe |
| ProductName: | O&O SafeErase Professional |
| ProductVersion: | 6.0.242 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Oct-2017 16:48:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003256C | 0x00032600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62254 |
.rdata | 0x00034000 | 0x000095FE | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7308 |
.data | 0x0003E000 | 0x00003C04 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.63209 |
.rsrc | 0x00042000 | 0x0005ABF0 | 0x0005AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52354 |
.reloc | 0x0009D000 | 0x000031A8 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.22348 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01229 | 633 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.83856 | 2216 | Latin 1 / Western European | German - Germany | RT_ICON |
3 | 4.43591 | 3752 | Latin 1 / Western European | German - Germany | RT_ICON |
4 | 3.54222 | 74792 | Latin 1 / Western European | German - Germany | RT_ICON |
5 | 6.012 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
6 | 5.99374 | 4264 | Latin 1 / Western European | German - Germany | RT_ICON |
7 | 5.89124 | 9640 | Latin 1 / Western European | German - Germany | RT_ICON |
8 | 5.77014 | 270376 | Latin 1 / Western European | German - Germany | RT_ICON |
101 | 3.32982 | 740 | Latin 1 / Western European | German - Germany | RT_DIALOG |
103 | 2.69824 | 118 | Latin 1 / Western European | German - Germany | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINTRUST.dll |
msi.dll (delay-loaded) |
Total processes
120
Monitored processes
62
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12749065824748108706,2422758447888039723,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6087547709413693346 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d52a9d0,0x6d52a9e0,0x6d52a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Temp\OO Software\OO LiveUpdate\OO SafeErase Professional 14\OOLiveUpdateWorker.exe" UpdateCheckSilent -ProgramName "O&O SafeErase Professional" -DisplayName "O&O SafeErase Professional" -ProgramVersion 14.6.581 -InstallDate 20191108 -InstalledLocation "C:\Program Files\OO Software\SafeErase\\" -Language 1033 -AffiliateId "1000" -UpdateIntervalInHours 72 -WindowRec "367 184" -WindowCaption "O&O LiveUpdate" | C:\Users\admin\AppData\Local\Temp\OO Software\OO LiveUpdate\OO SafeErase Professional 14\OOLiveUpdateWorker.exe | OOLiveUpdate.exe | ||||||||||||
User: admin Company: O&O Software GmbH Integrity Level: HIGH Description: O&O LiveUpdate Exit code: 0 Version: 10.0.0.0 Modules
| |||||||||||||||
| 460 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12749065824748108706,2422758447888039723,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12942641690909174629 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12749065824748108706,2422758447888039723,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7491238615684410005 --mojo-platform-channel-handle=3352 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12749065824748108706,2422758447888039723,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16483576774116216312 --mojo-platform-channel-handle=4432 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12749065824748108706,2422758447888039723,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16818338241859600660 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1024 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | OOSE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12 956
Read events
12 184
Write events
756
Delete events
16
Modification events
| (PID) Process: | (1712) setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3036) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000D85E66B84196D5016809000008070000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000D85E66B84196D5016809000008070000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 33 | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000BE47B0B84196D5016809000008070000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000018AAB2B84196D5016809000094070000E8030000010000000000000000000000346117FAF1024F4796B8D084DF239B840000000000000000 | |||
| (PID) Process: | (2572) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E8BCC5B84196D5010C0A0000480D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2572) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E8BCC5B84196D5010C0A0000840D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2572) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E8BCC5B84196D5010C0A000014080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
68
Suspicious files
57
Text files
409
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1712 | setup.exe | C:\Users\admin\AppData\Local\Temp\OO Software\OO SetupStub\OOSTUB15732236991712\setup.dat | — | |
MD5:— | SHA256:— | |||
| 1712 | setup.exe | C:\Users\admin\AppData\Local\Temp\OO Software\OO SetupStub\OOSTUB15732236991712\setup.MSI | — | |
MD5:— | SHA256:— | |||
| 1712 | setup.exe | C:\ProgramData\OO Software\Installations\31DF14AB20762CA648AEAA44C9687DCD19AA3993.msi | — | |
MD5:— | SHA256:— | |||
| 3036 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIDDC8.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cbba67ed-3db2-46d9-b1f5-46db2790bce2.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
63
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | iexplore.exe | GET | 307 | 5.35.253.237:80 | http://go.oo-software.com/91313 | DE | — | — | whitelisted |
2876 | iexplore.exe | GET | 307 | 5.35.253.237:80 | http://go.oo-software.com/91313 | DE | — | — | whitelisted |
1016 | iexplore.exe | GET | 307 | 5.35.253.237:80 | http://go.oo-software.com/91313 | DE | — | — | whitelisted |
592 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
2752 | OOLiveUpdate.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
592 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
592 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigzrney&ms=nvh&mt=1573223609&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
592 | chrome.exe | GET | 200 | 74.125.4.169:80 | http://r4---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1573223609&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
392 | OOLiveUpdateWorker.exe | GET | 404 | 46.16.74.95:80 | http://update10.oo-software.com/LiveUpdate//Banner/Banner_OO_SafeErase_Professional_14.bmp | DE | html | 688 b | unknown |
3716 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
592 | chrome.exe | 172.217.16.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
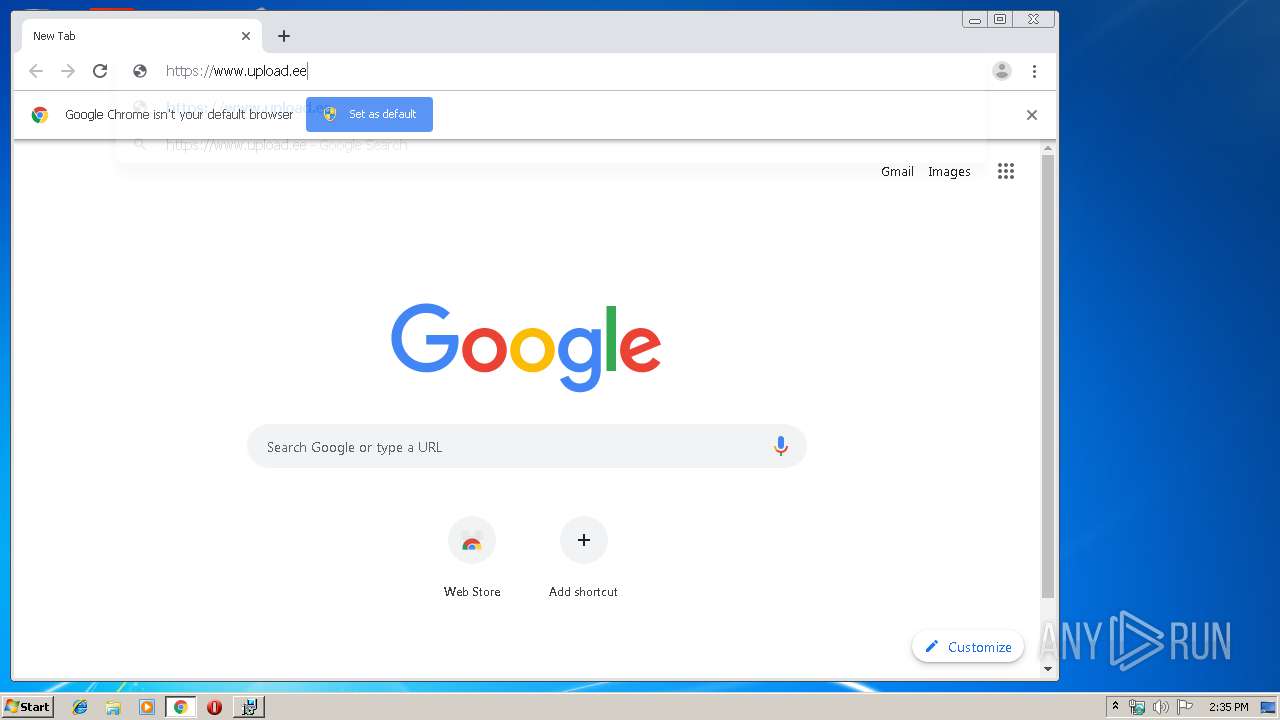
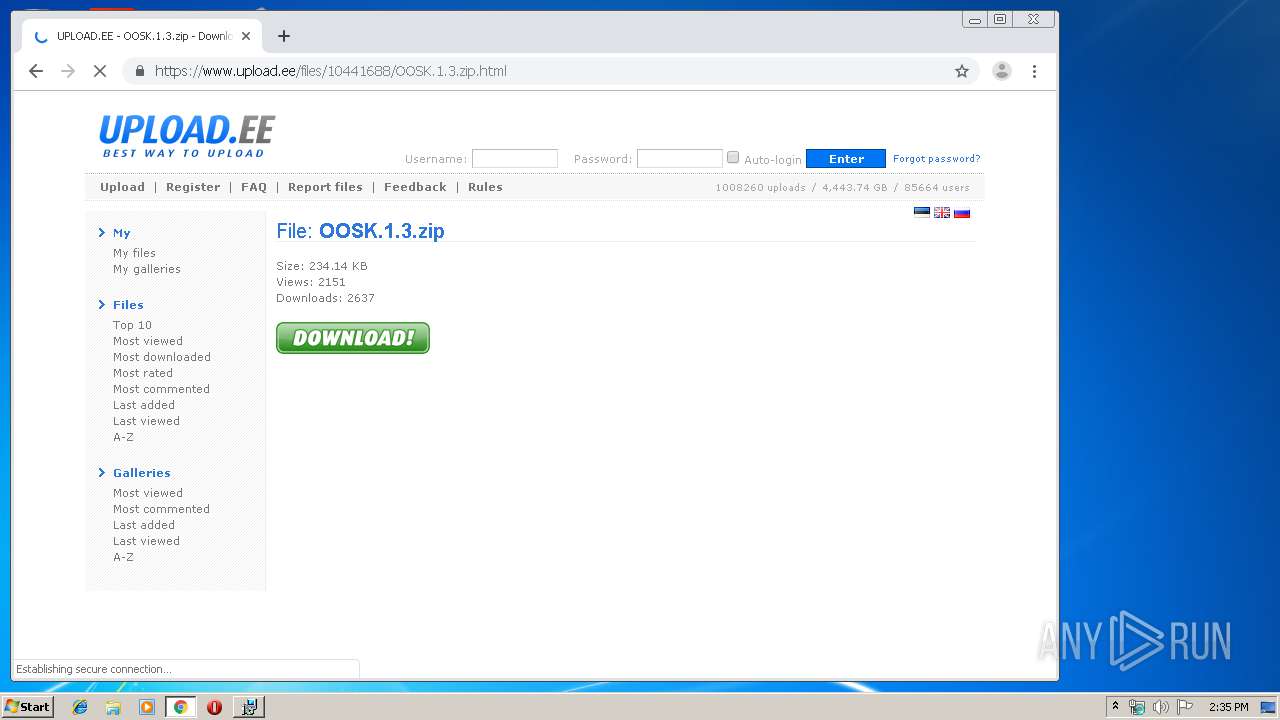
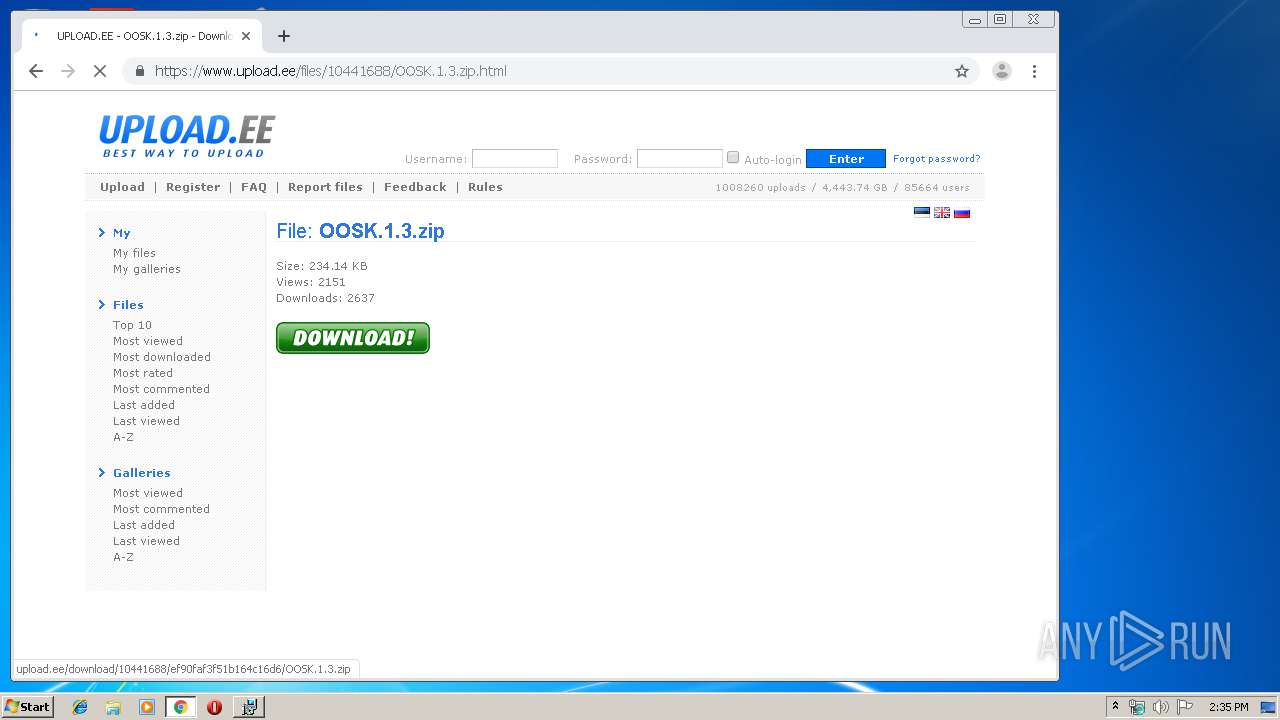
592 | chrome.exe | 37.187.167.53:443 | www.upload.ee | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SafeEraseAgent.exe | invalid image engine parameter
|