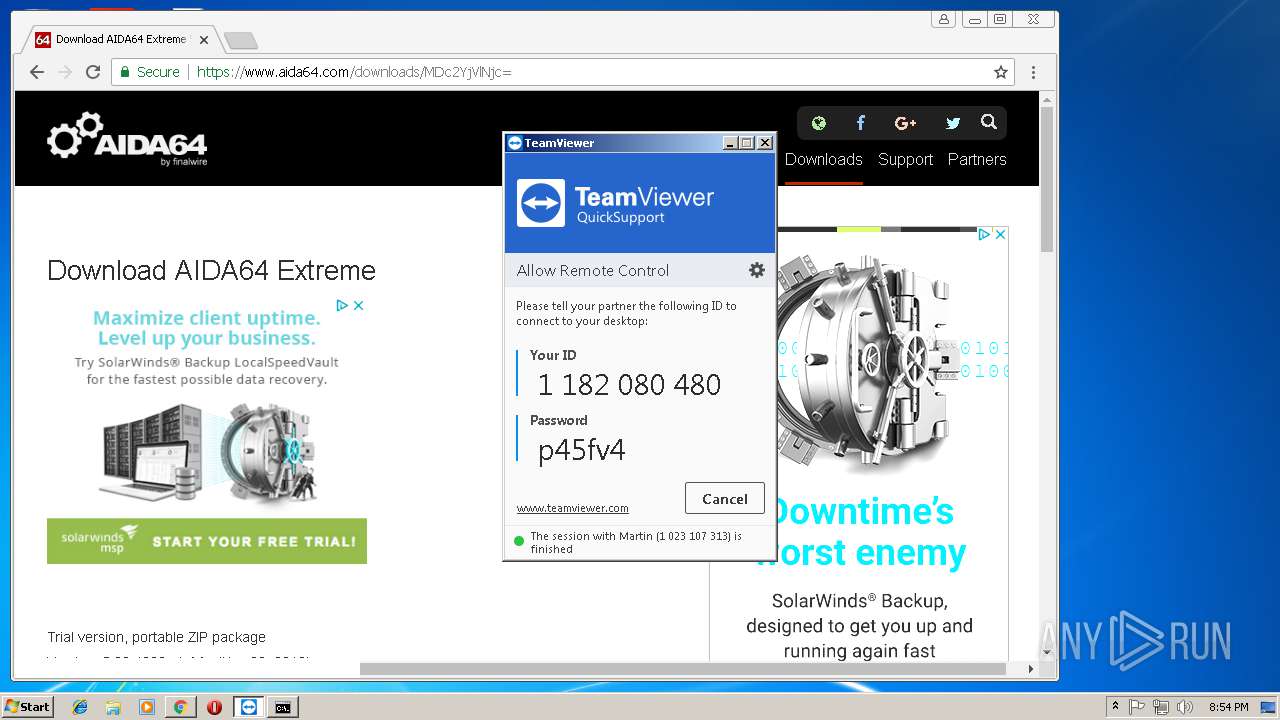
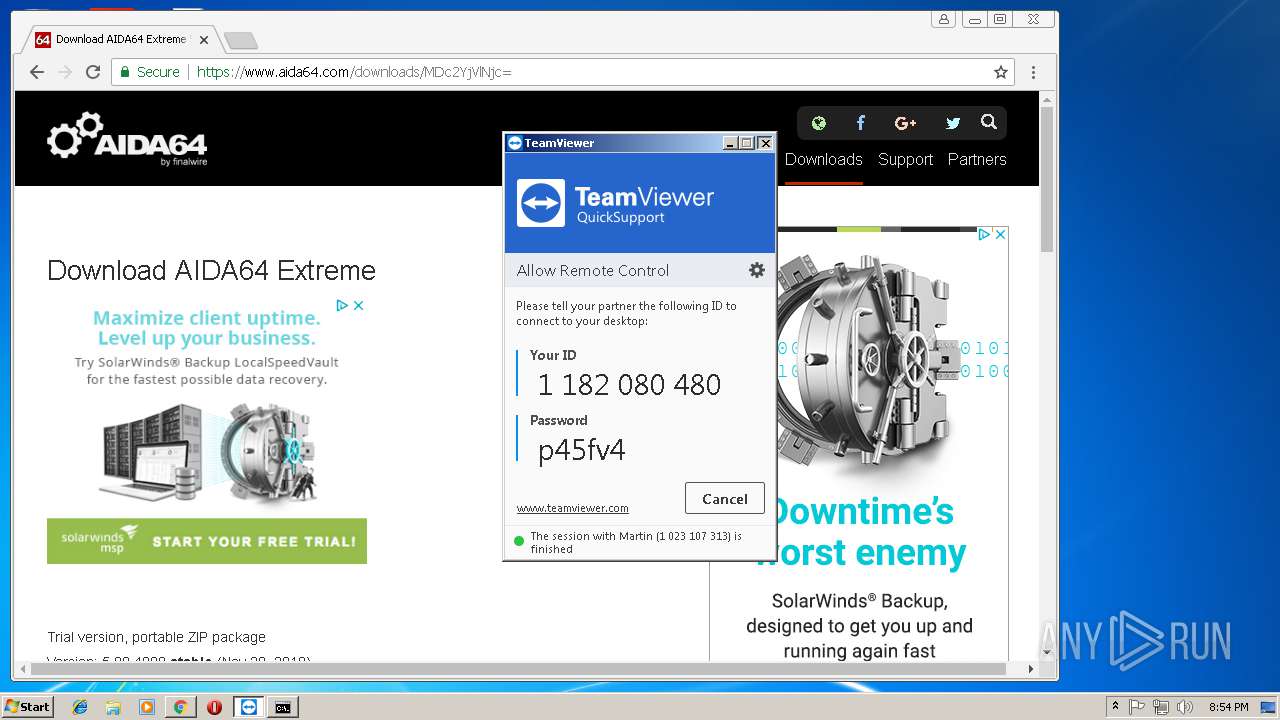
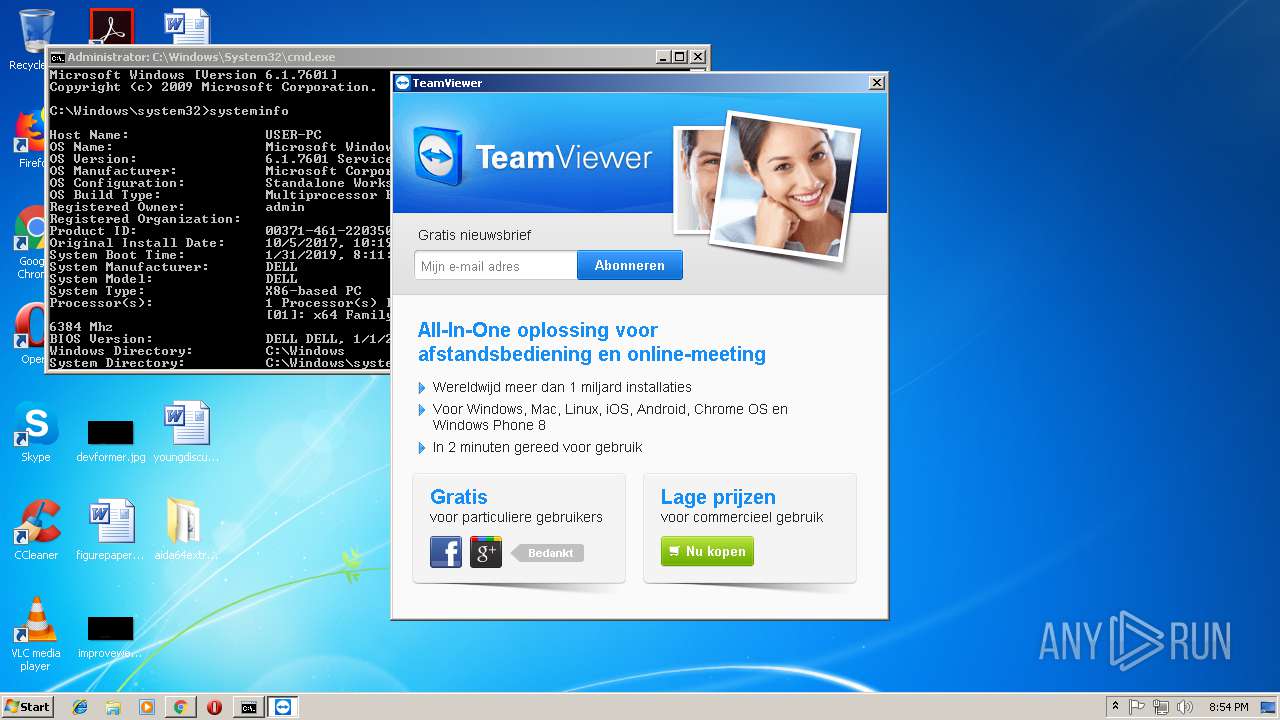
| download: | TeamViewerQS.exe |
| Full analysis: | https://app.any.run/tasks/5ba66389-3fee-4cfc-b458-a73dca631411 |
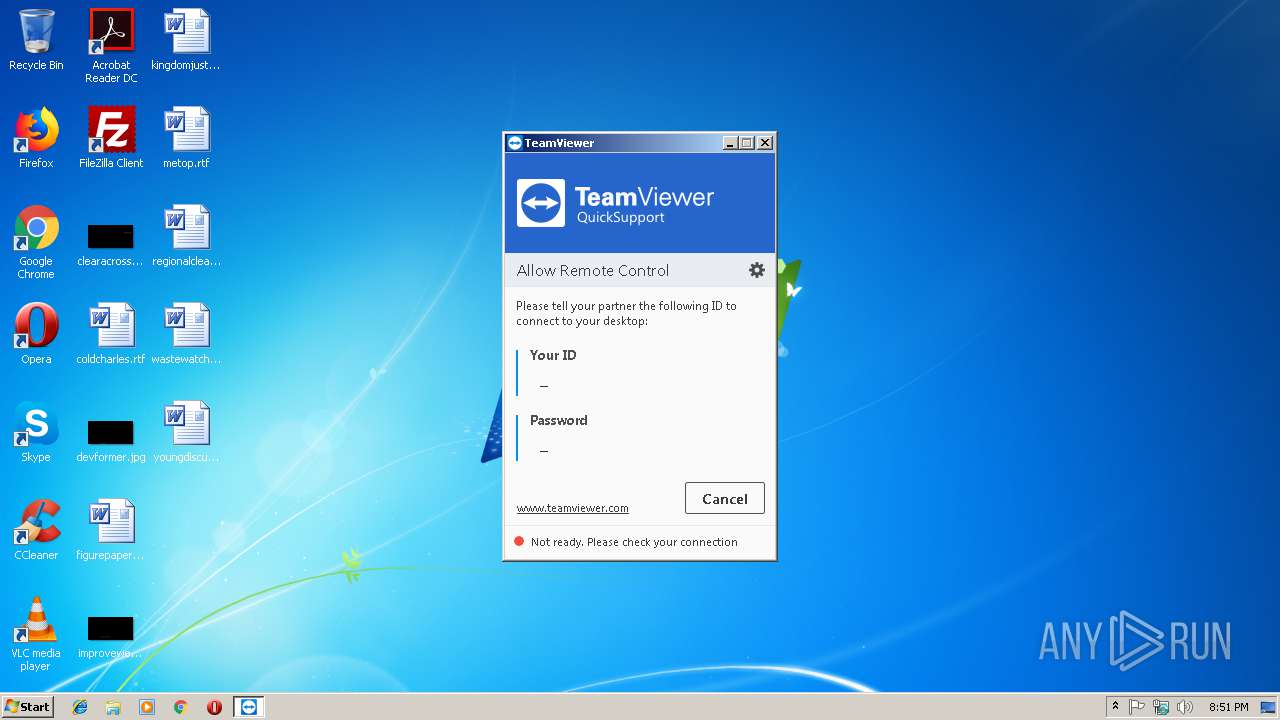
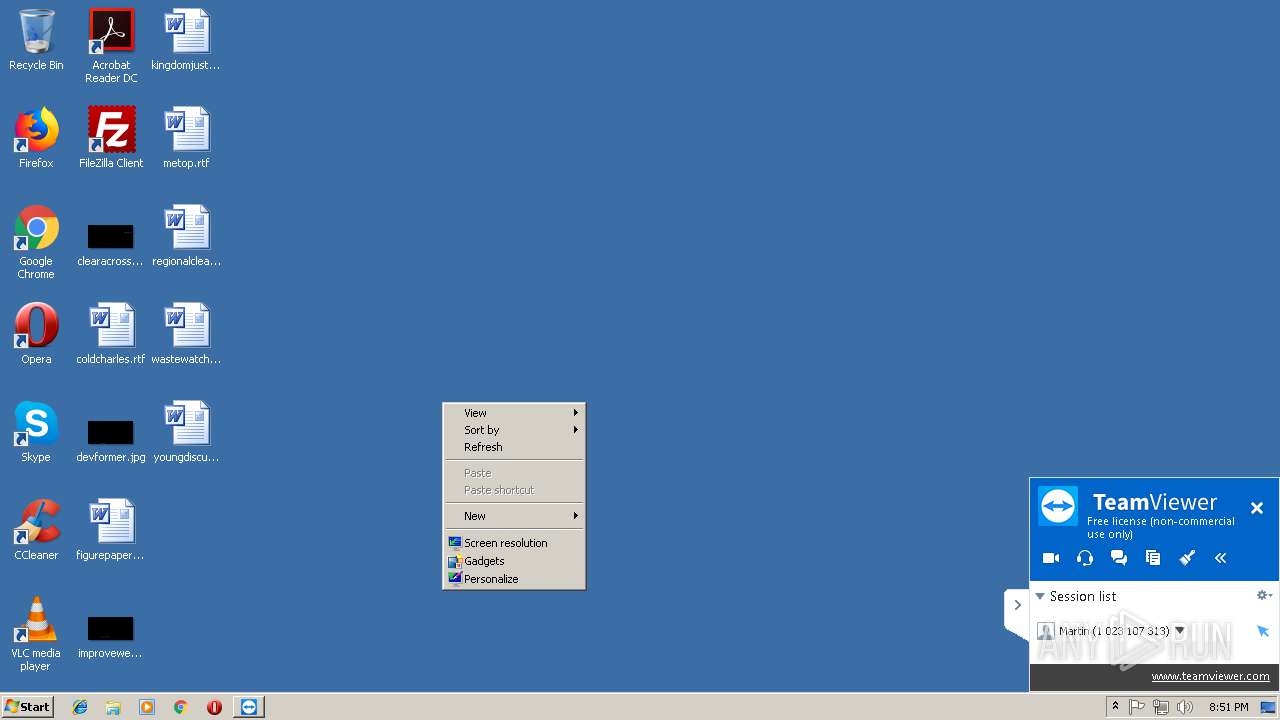
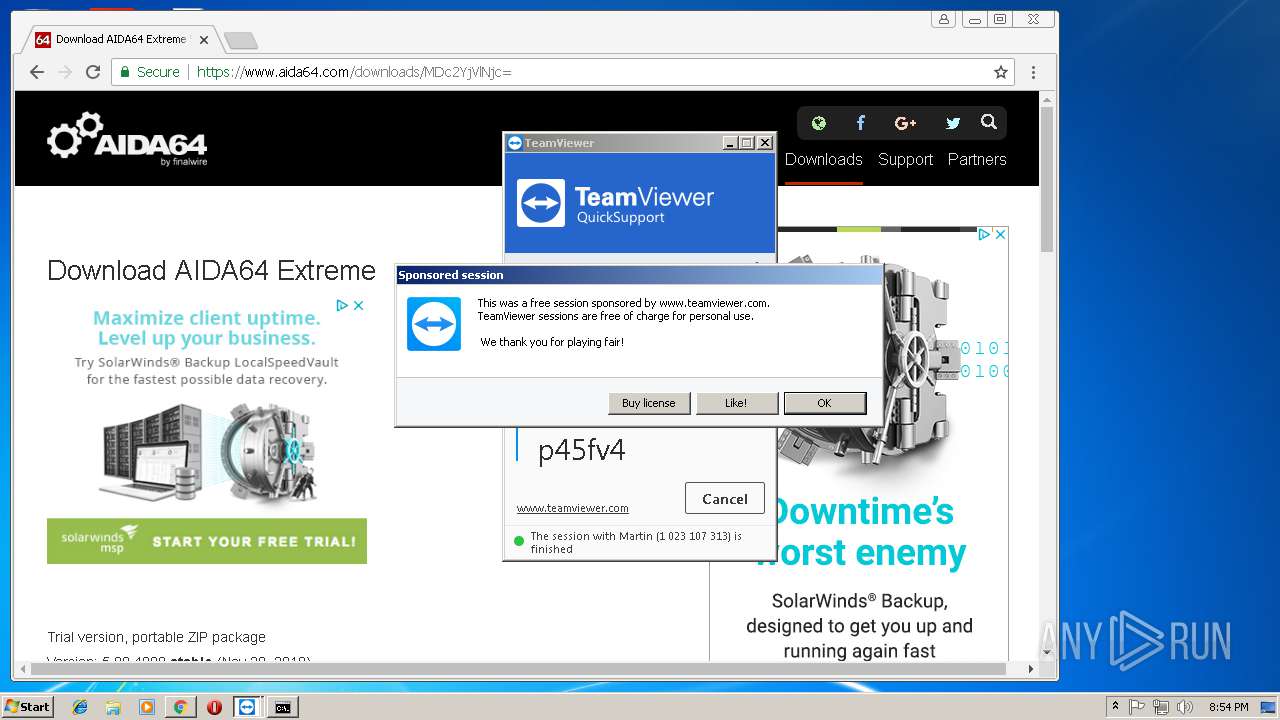
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2019, 20:51:04 |
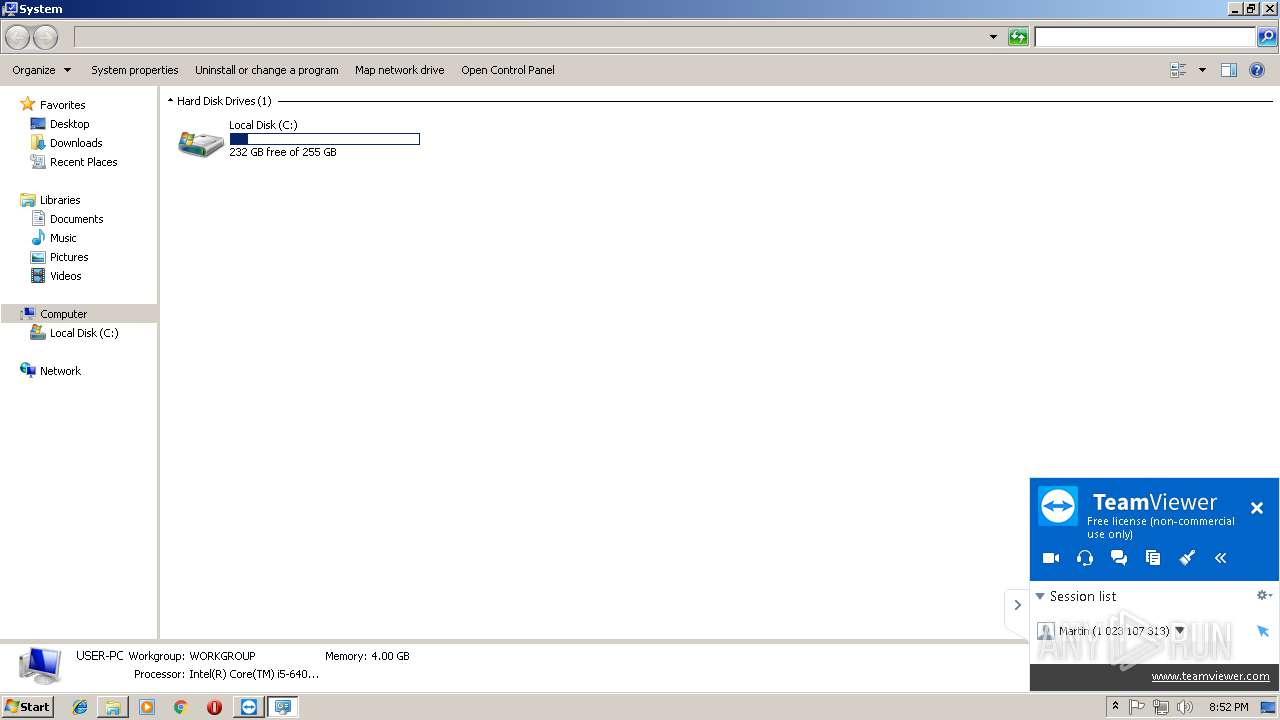
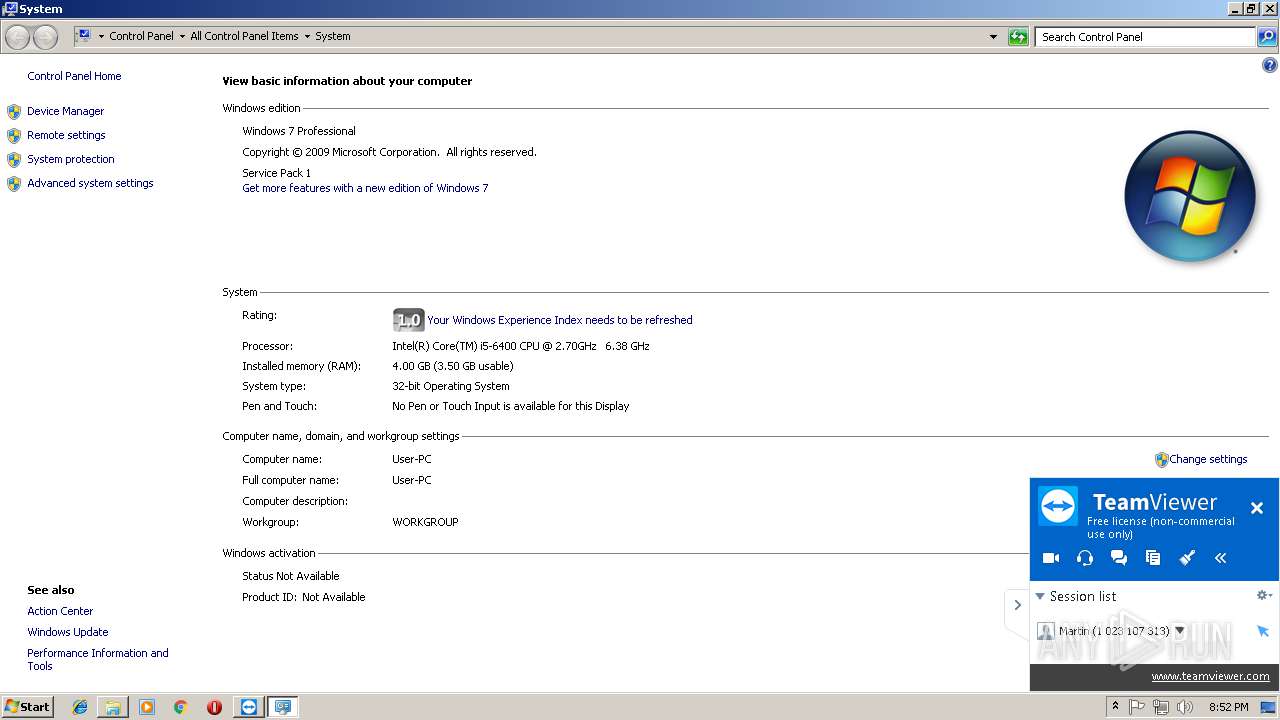
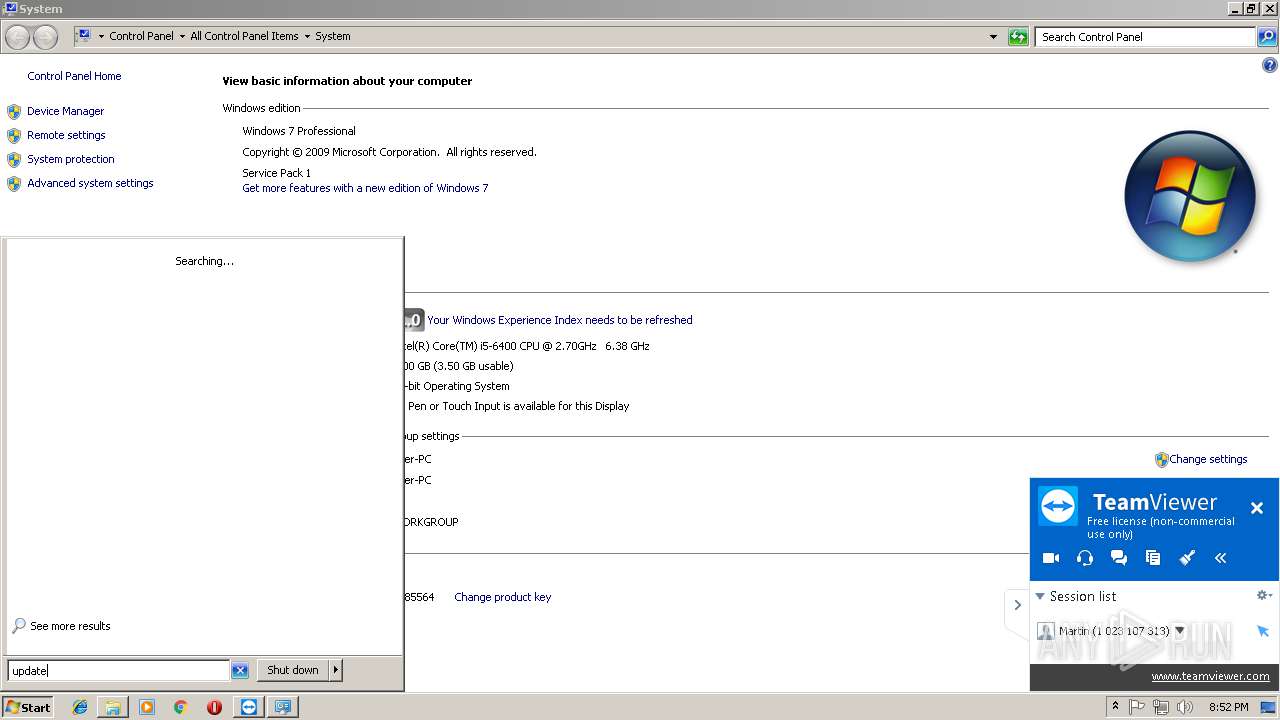
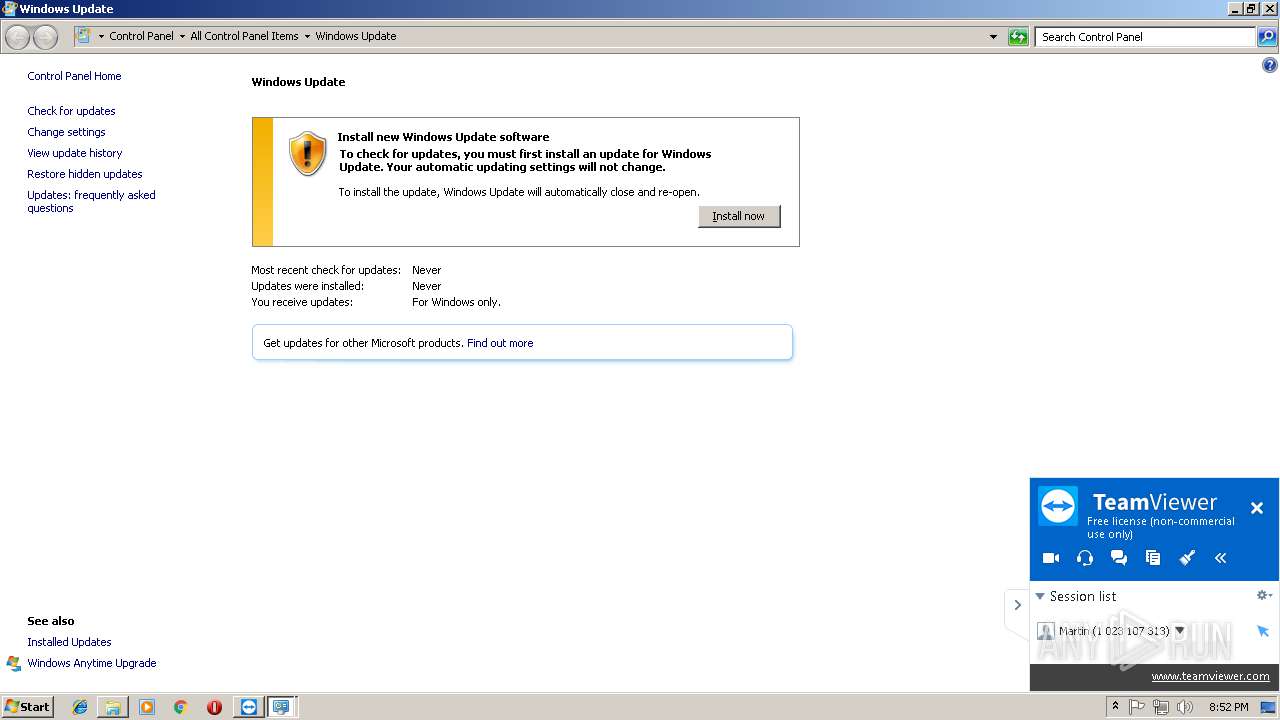
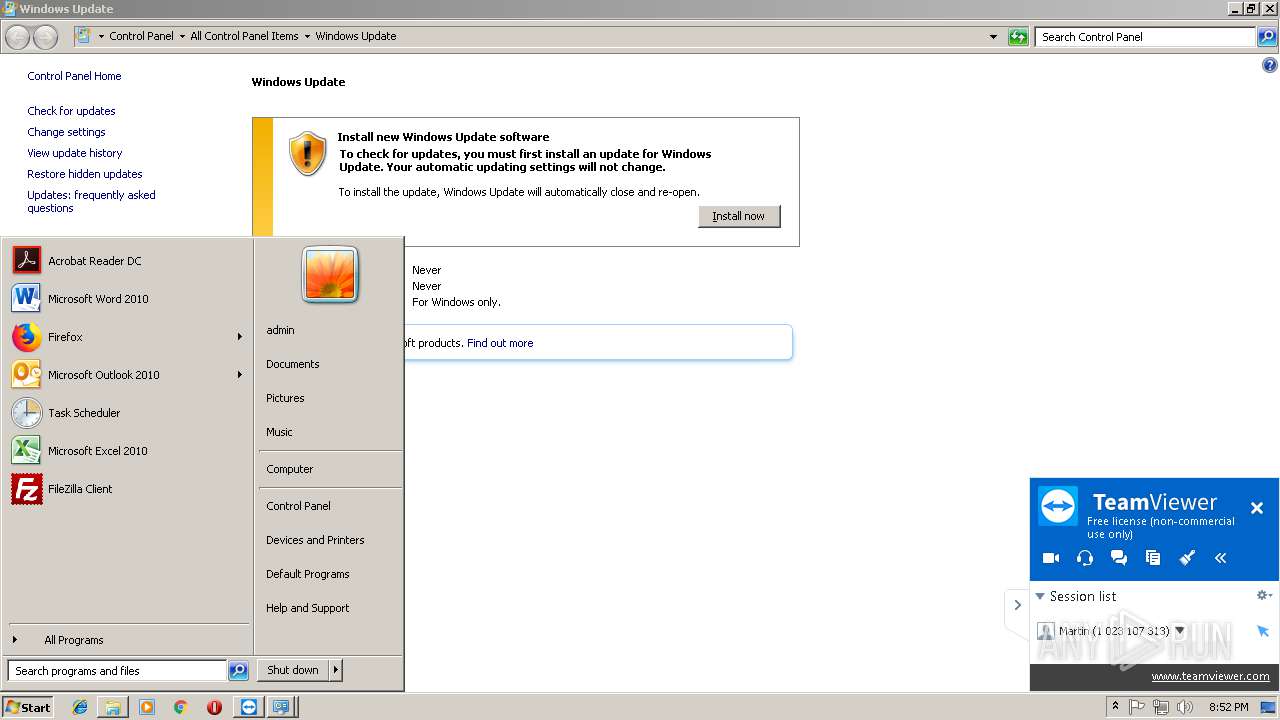
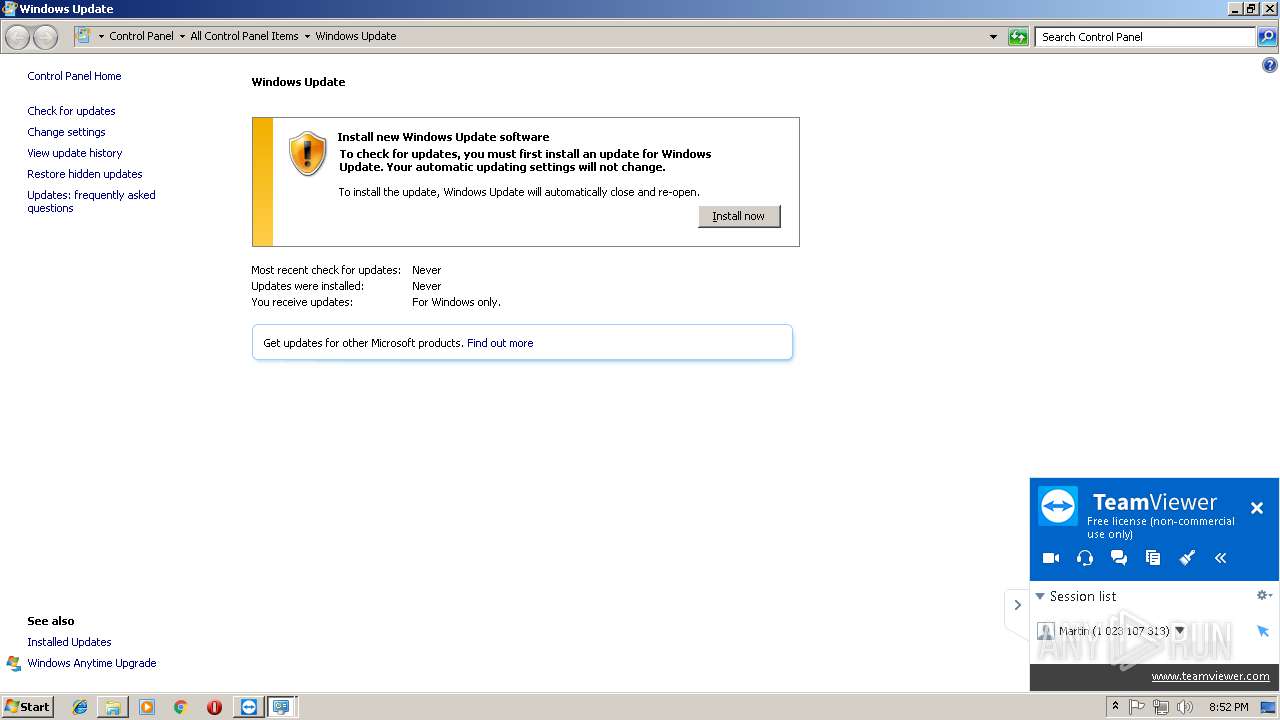
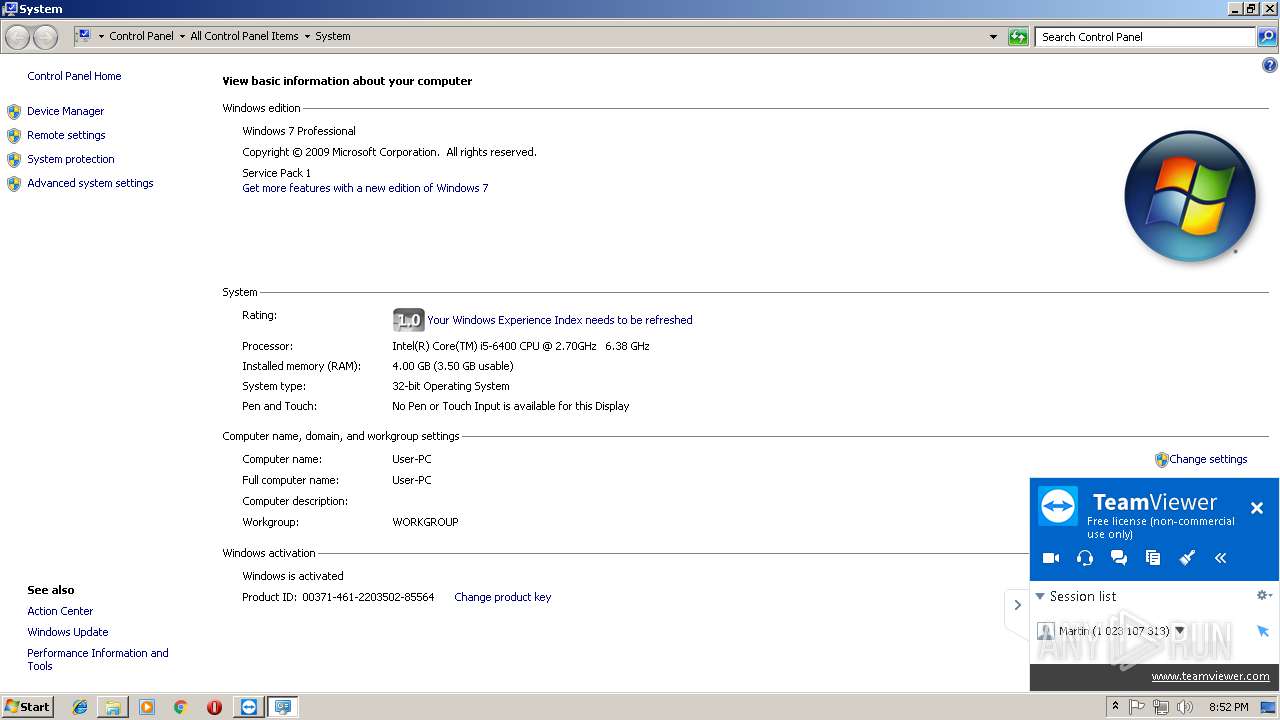
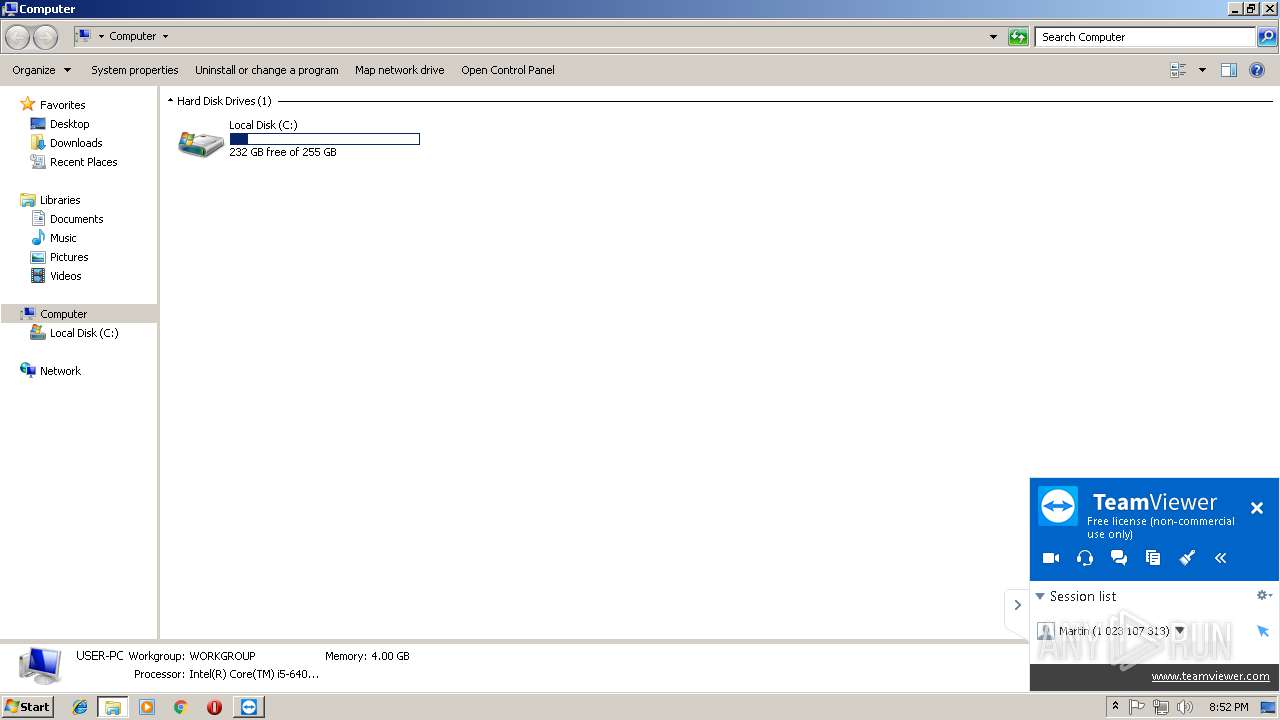
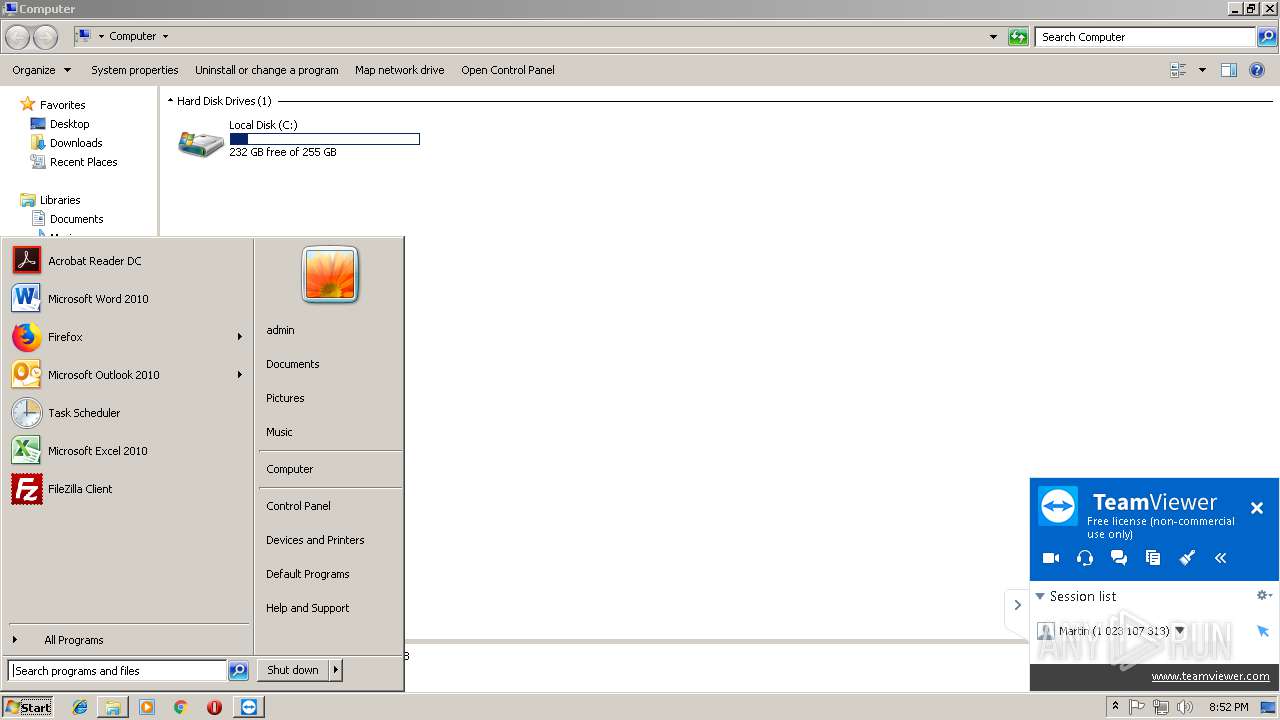
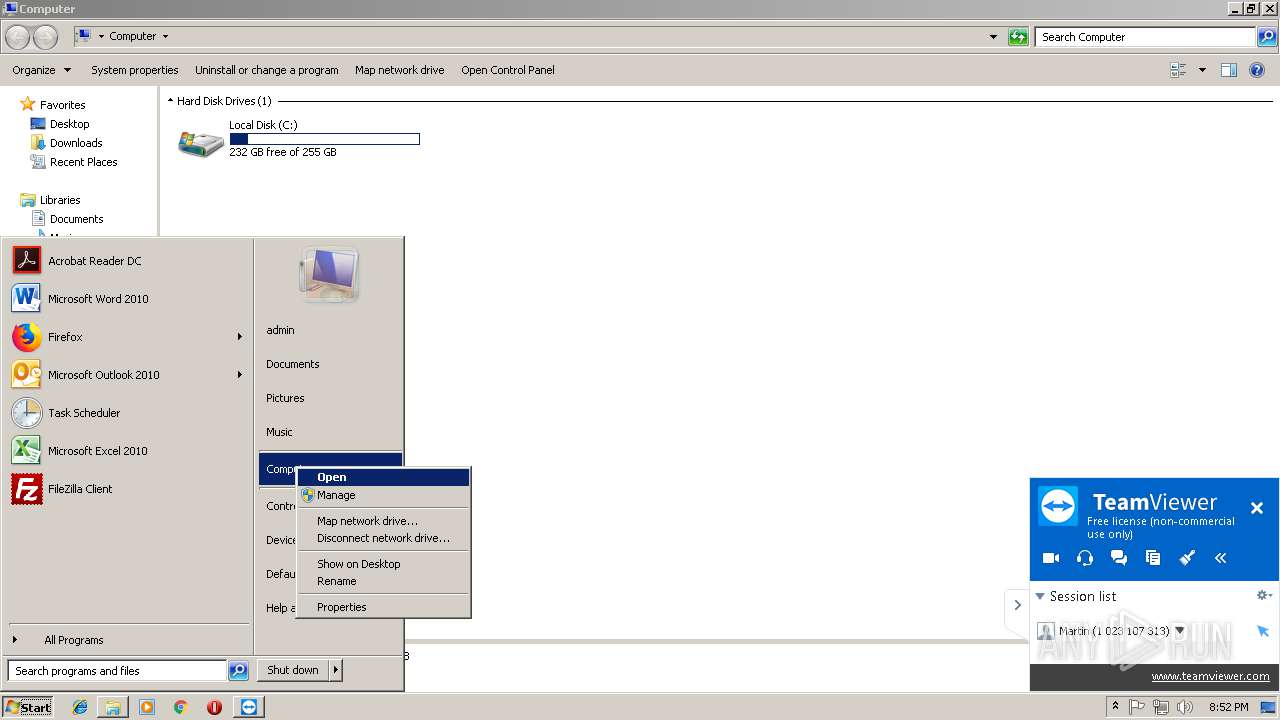
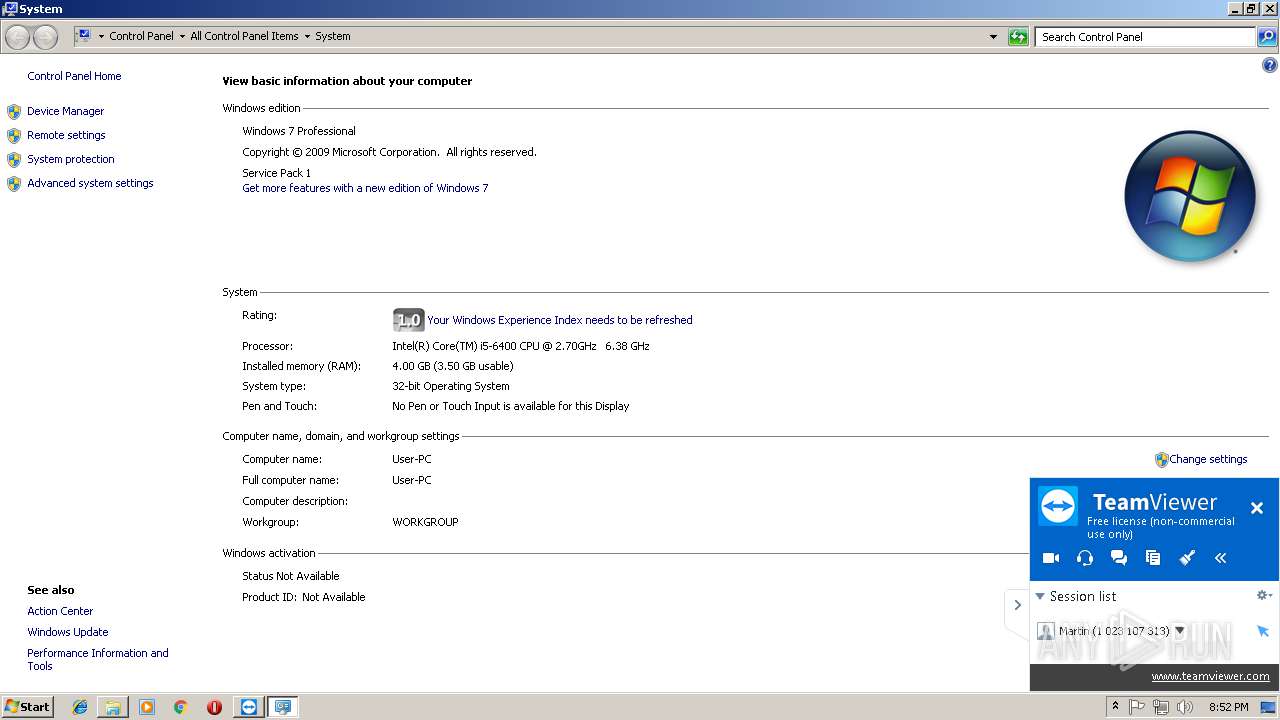
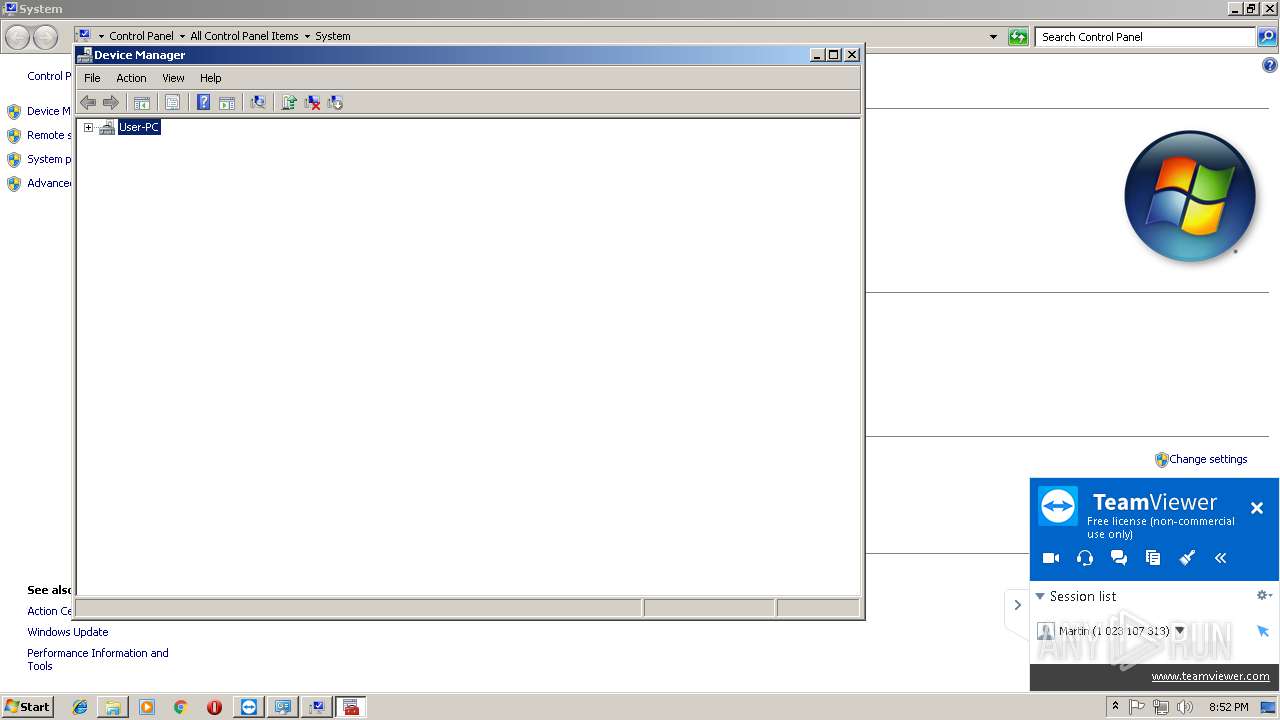
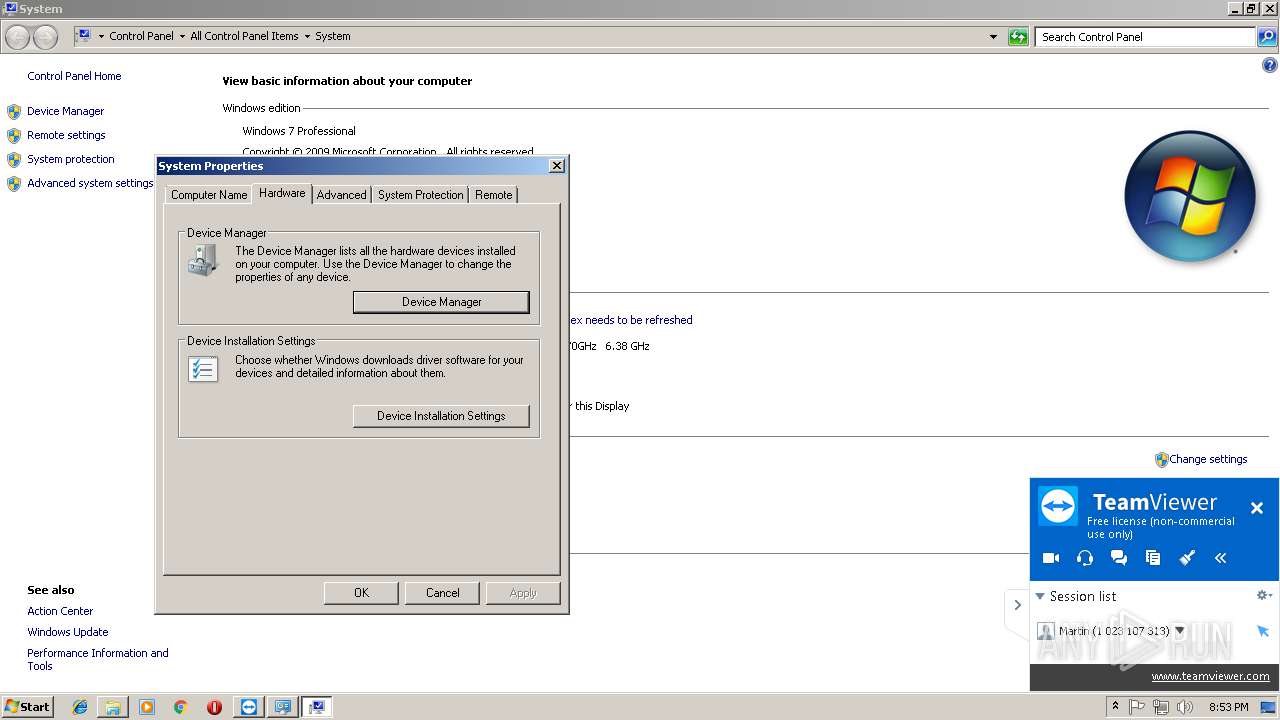
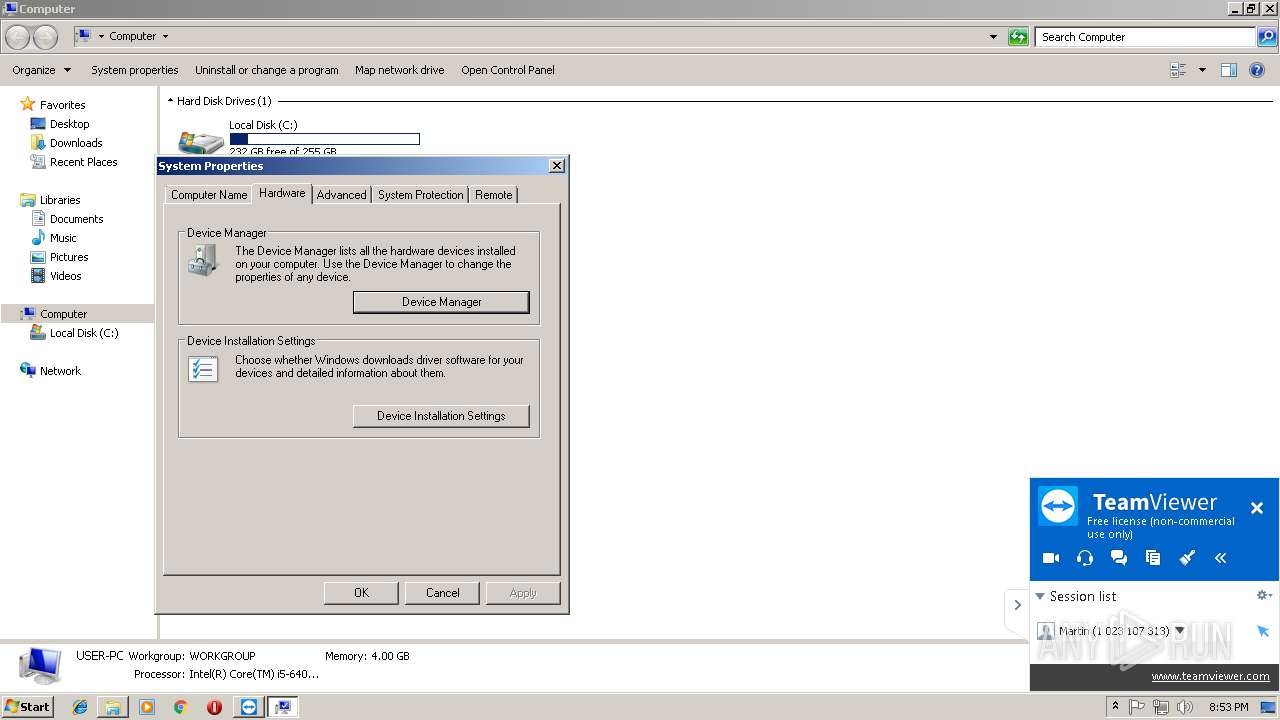
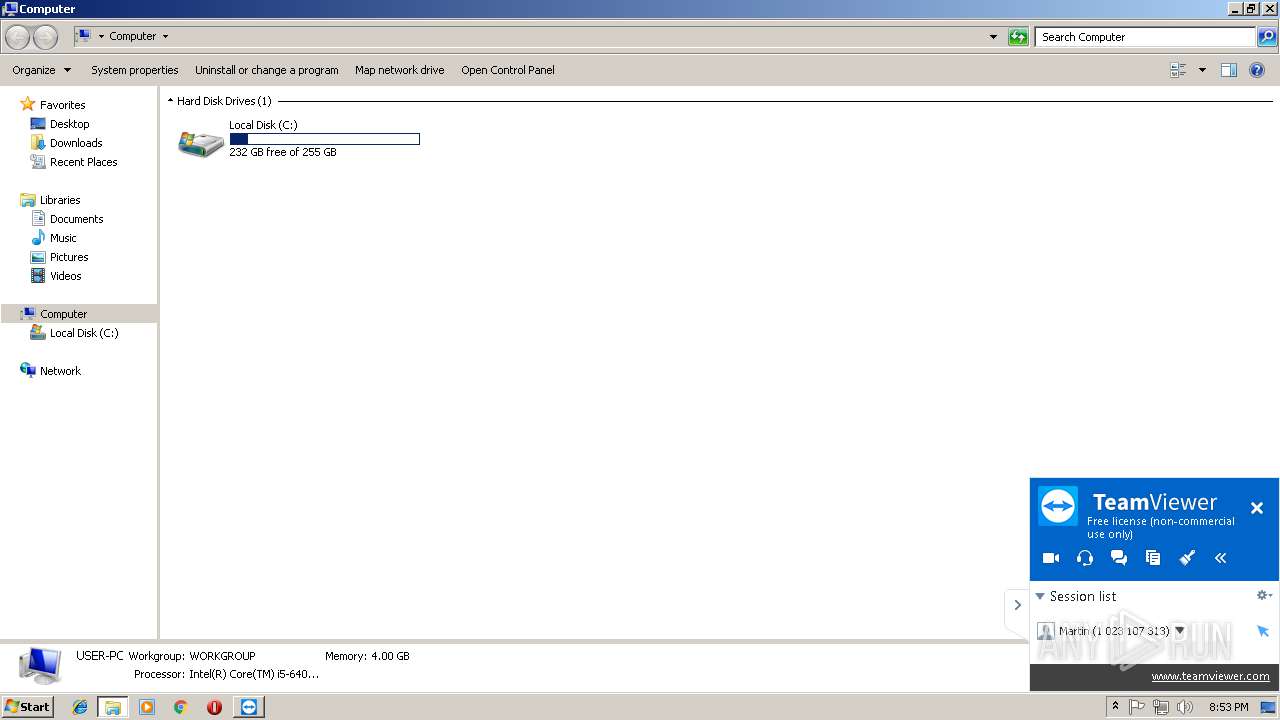
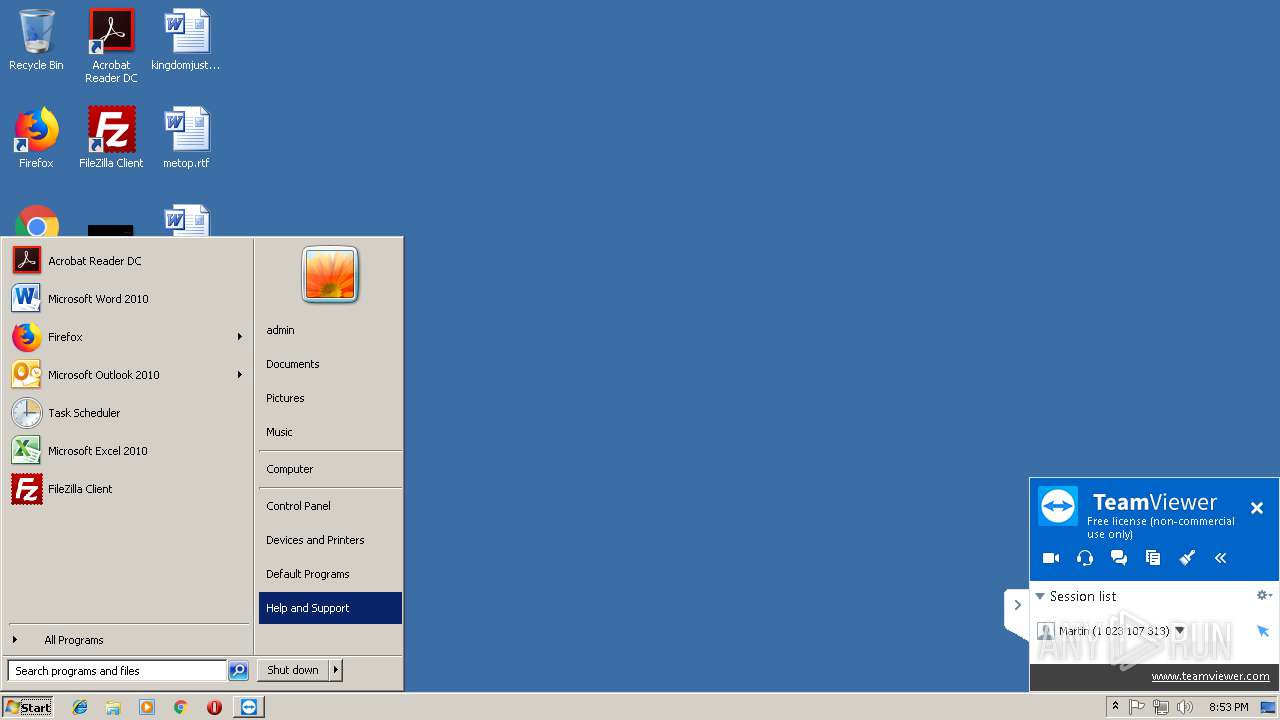
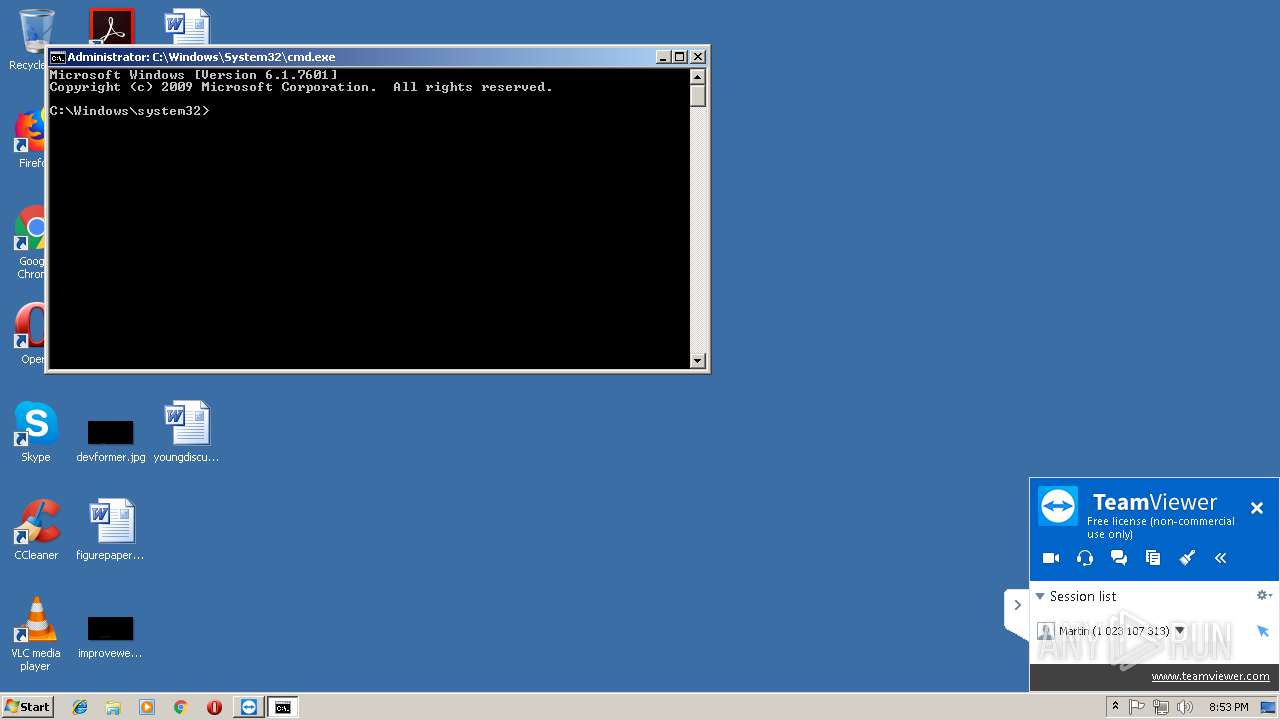
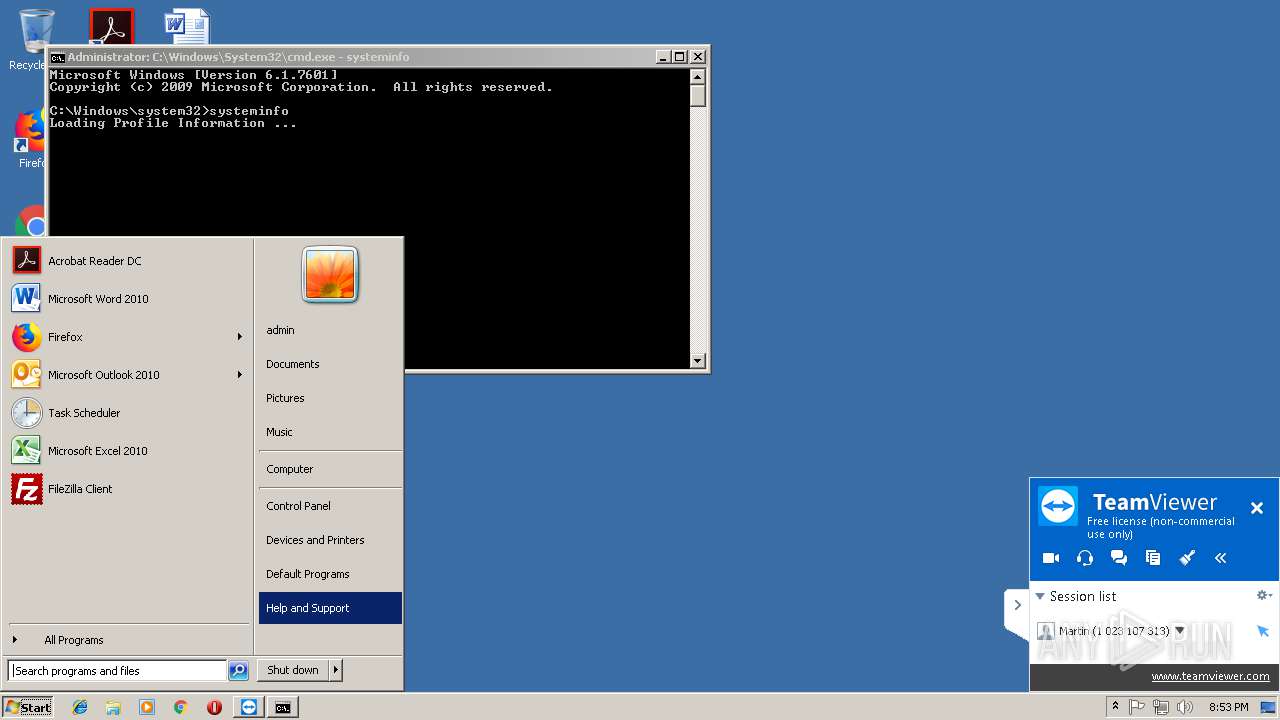
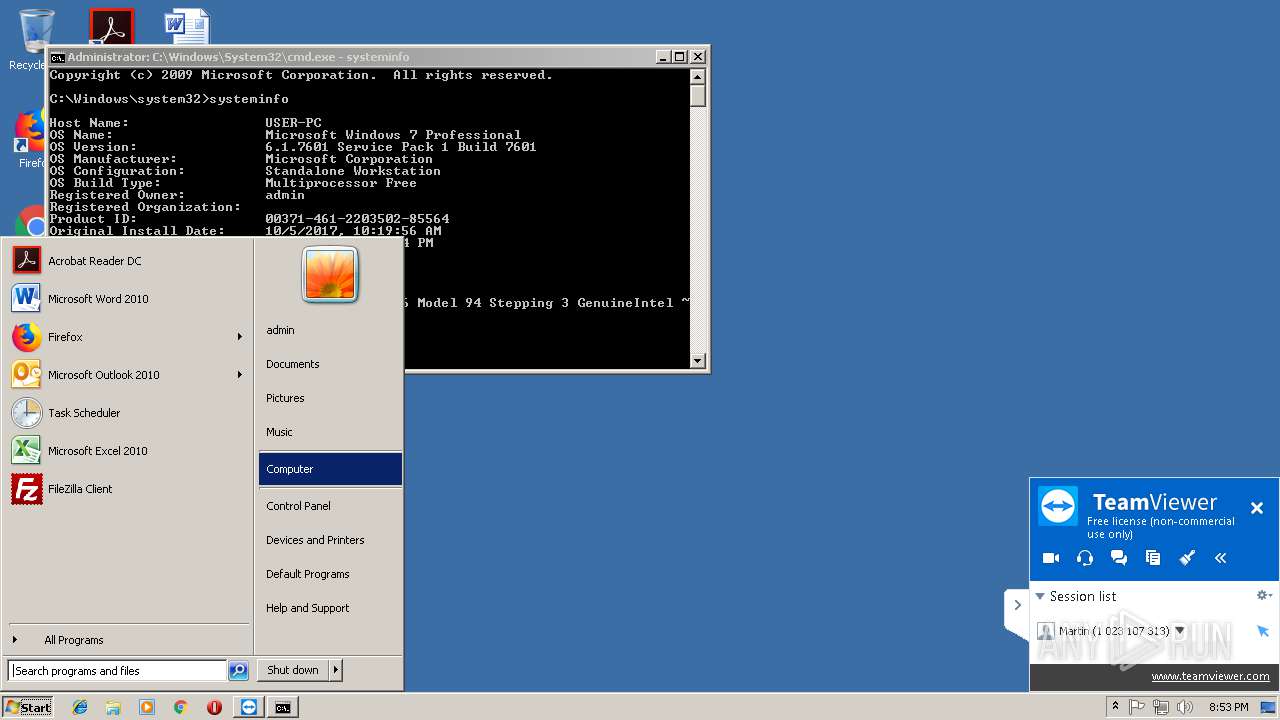
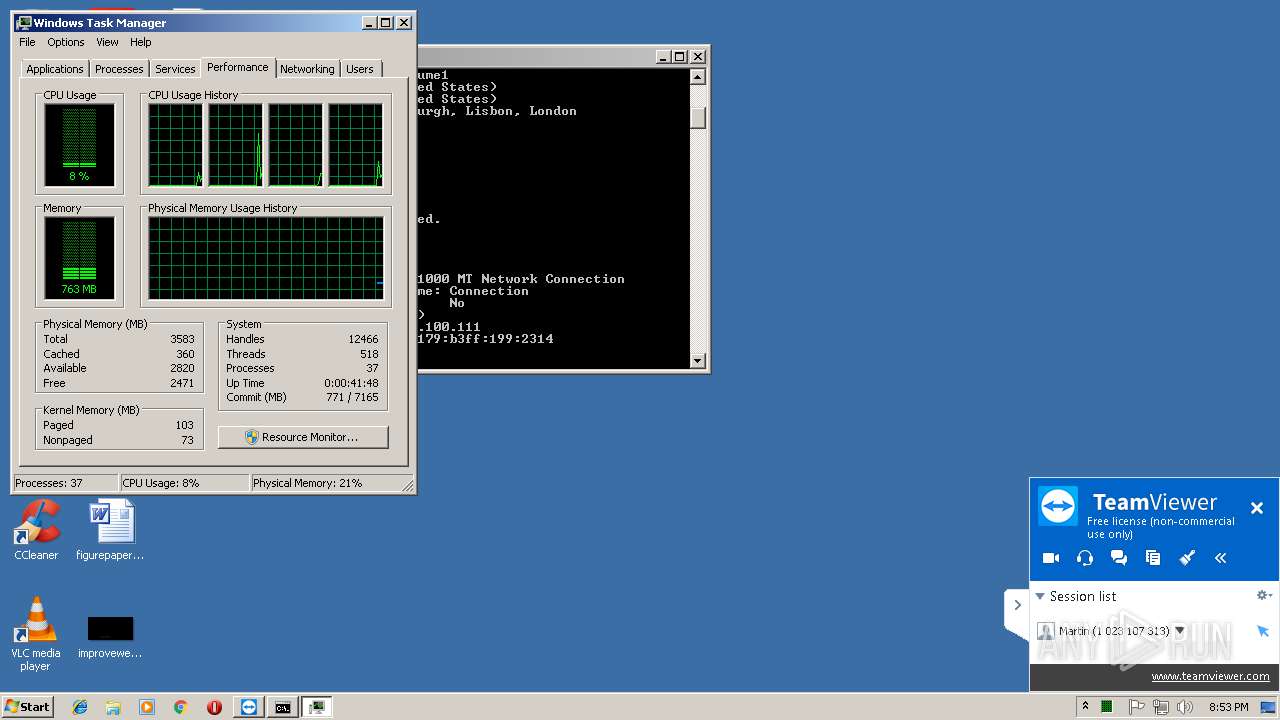
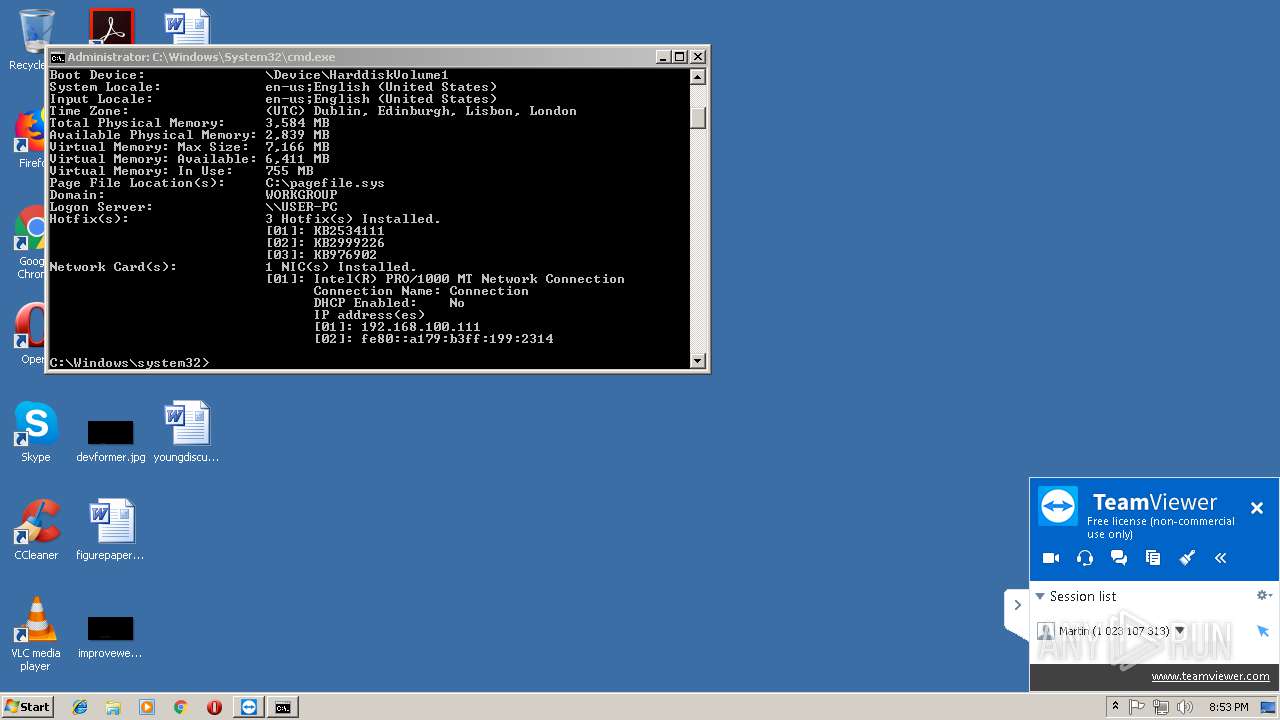
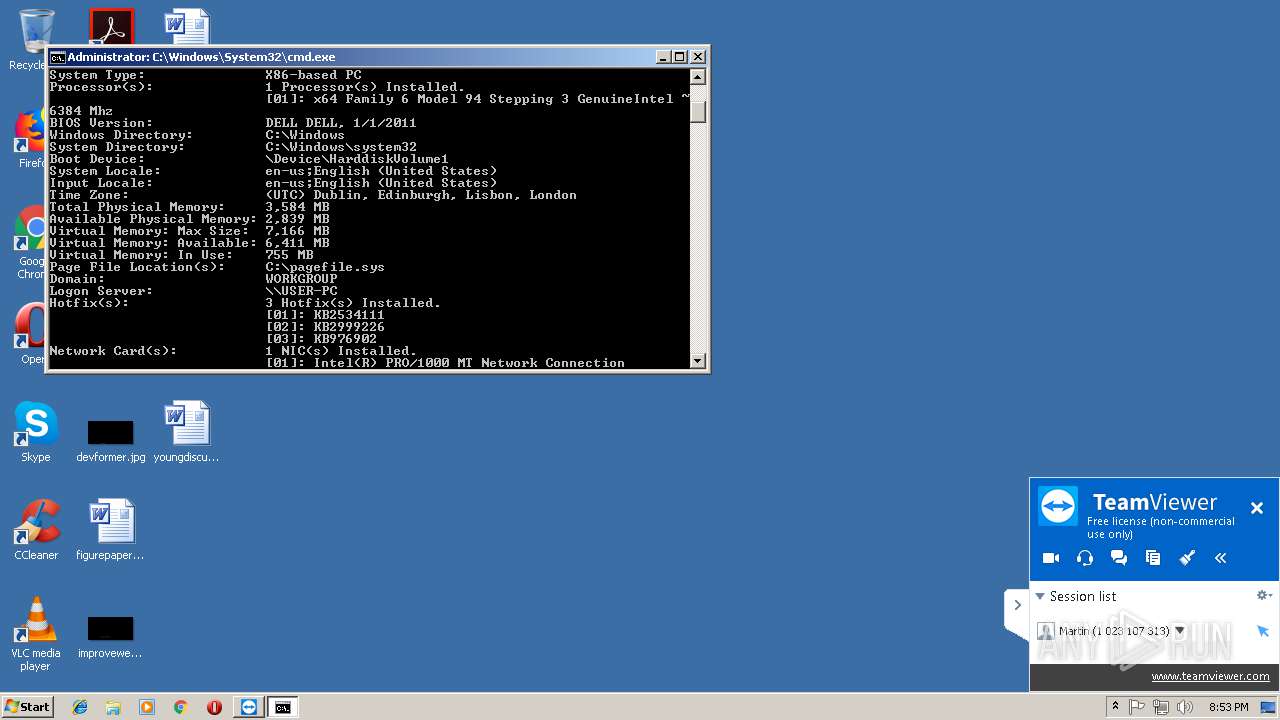
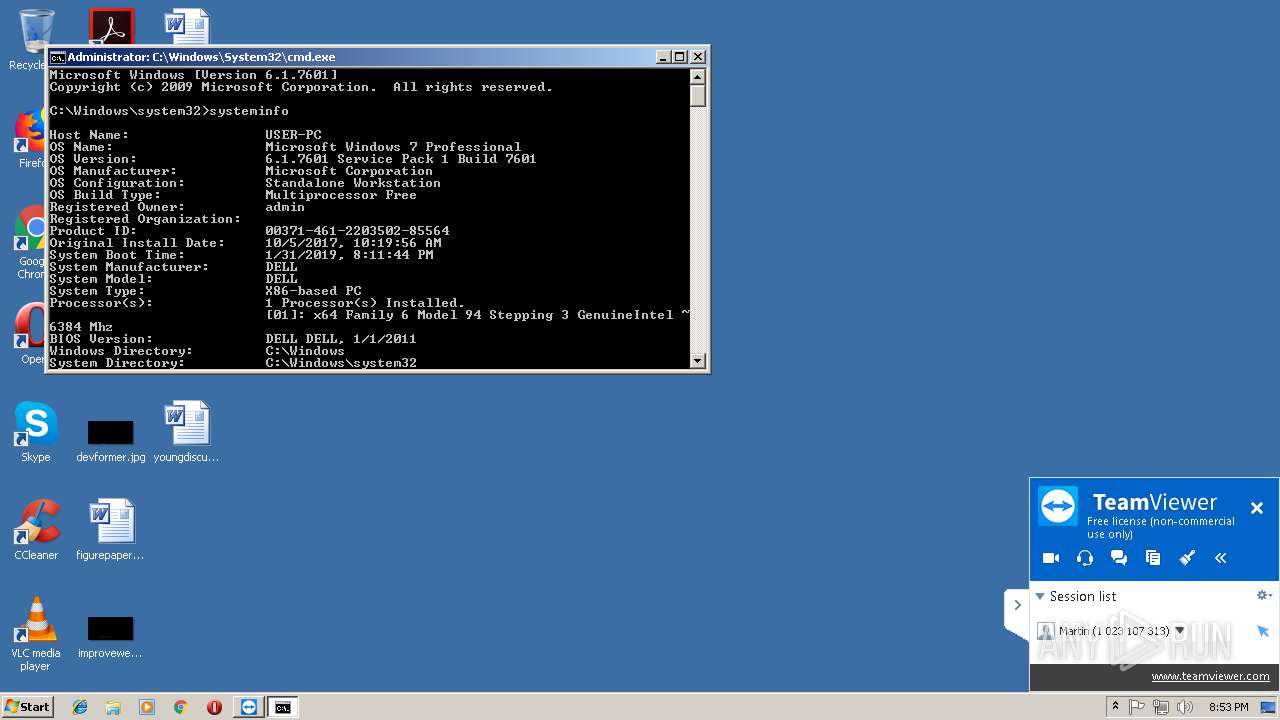
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F336DB82F8CD7CD5C5769EB0C0D848E0 |
| SHA1: | B90F3A0D056A09EC76E9FF0DF55A28C6DFE9BBF2 |
| SHA256: | 66E7A3739F7EECDC9C930777D226C846BE1BA54143B603E1EF1F5E41CCA4C6F6 |
| SSDEEP: | 393216:qYiMcuPGK12C2ADmHqqwcFVrgzOsfnPxZLJEwu3VmZ54Mg0JeK:q5FuPH12i6bXgS2xZKn3U+X0Jb |
MALICIOUS
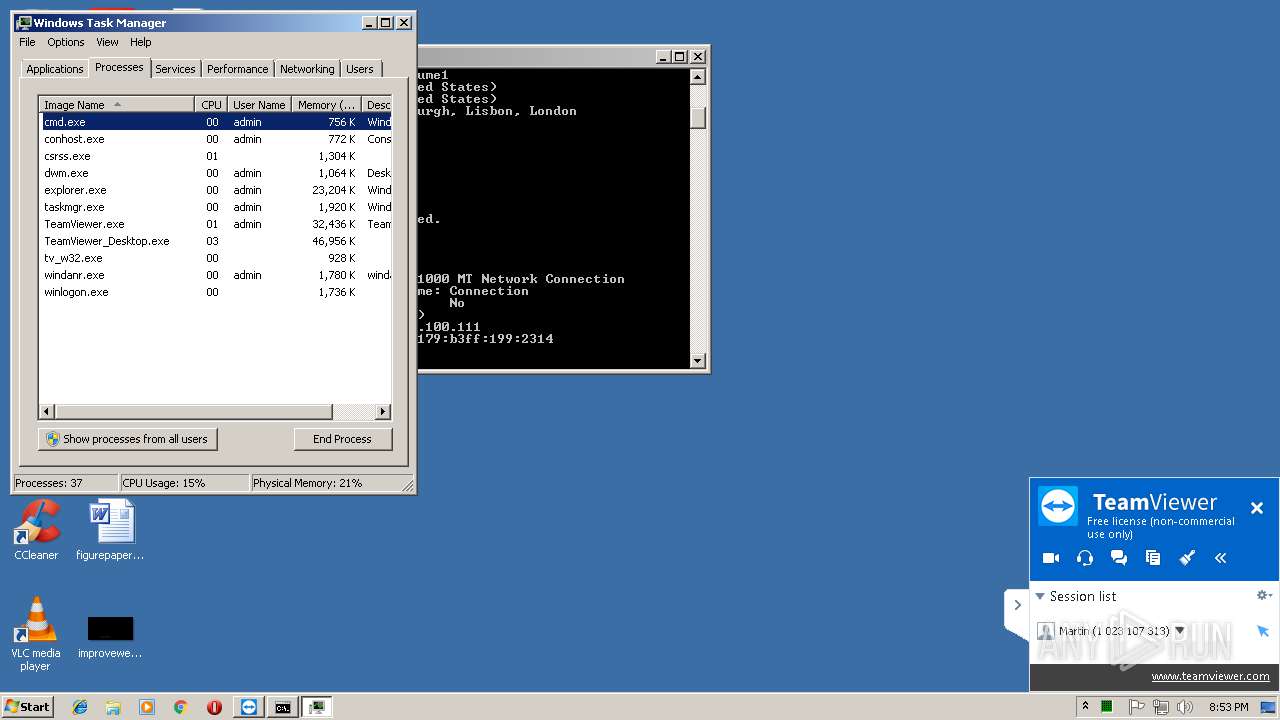
Application was dropped or rewritten from another process
- tv_w32.exe (PID: 3280)
- TeamViewer_Desktop.exe (PID: 3852)
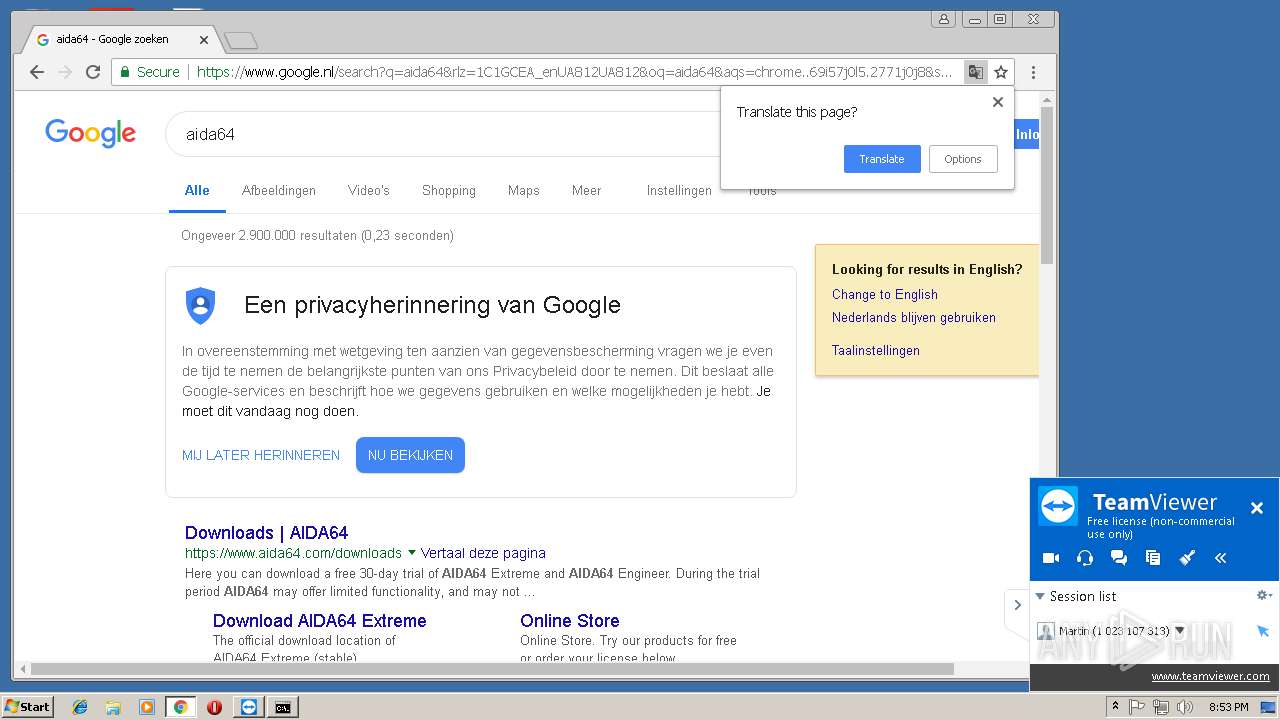
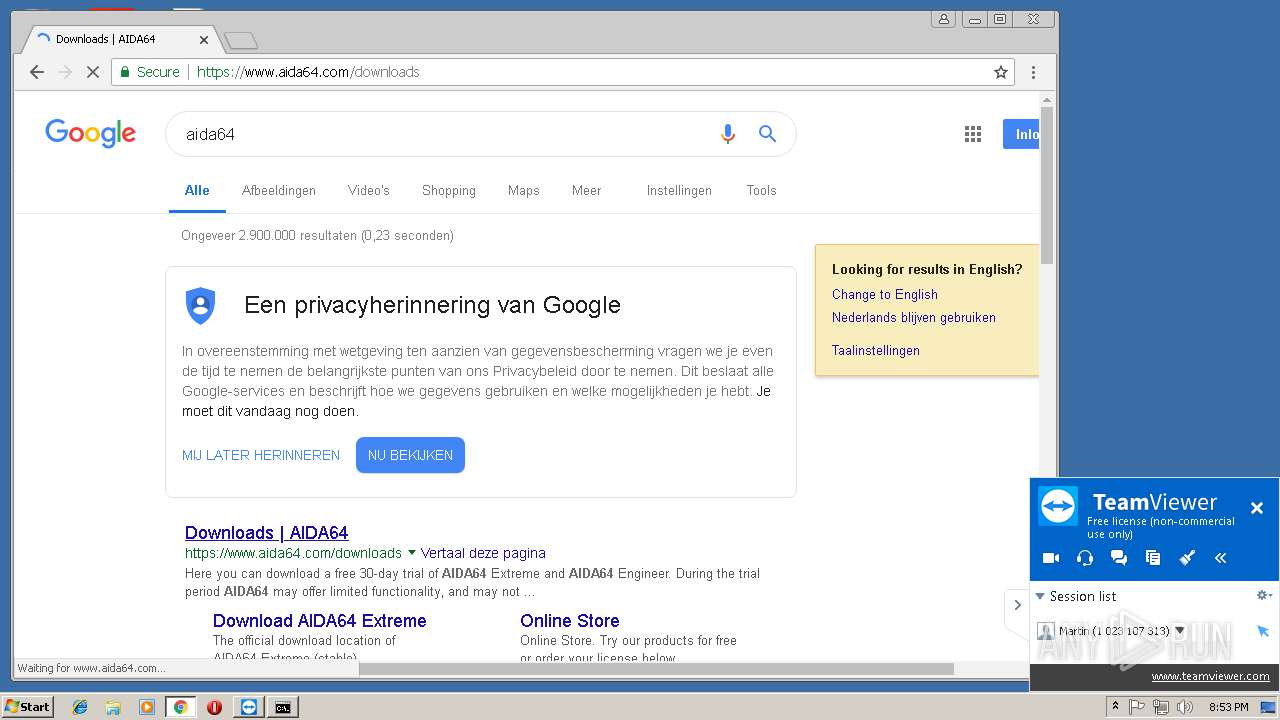
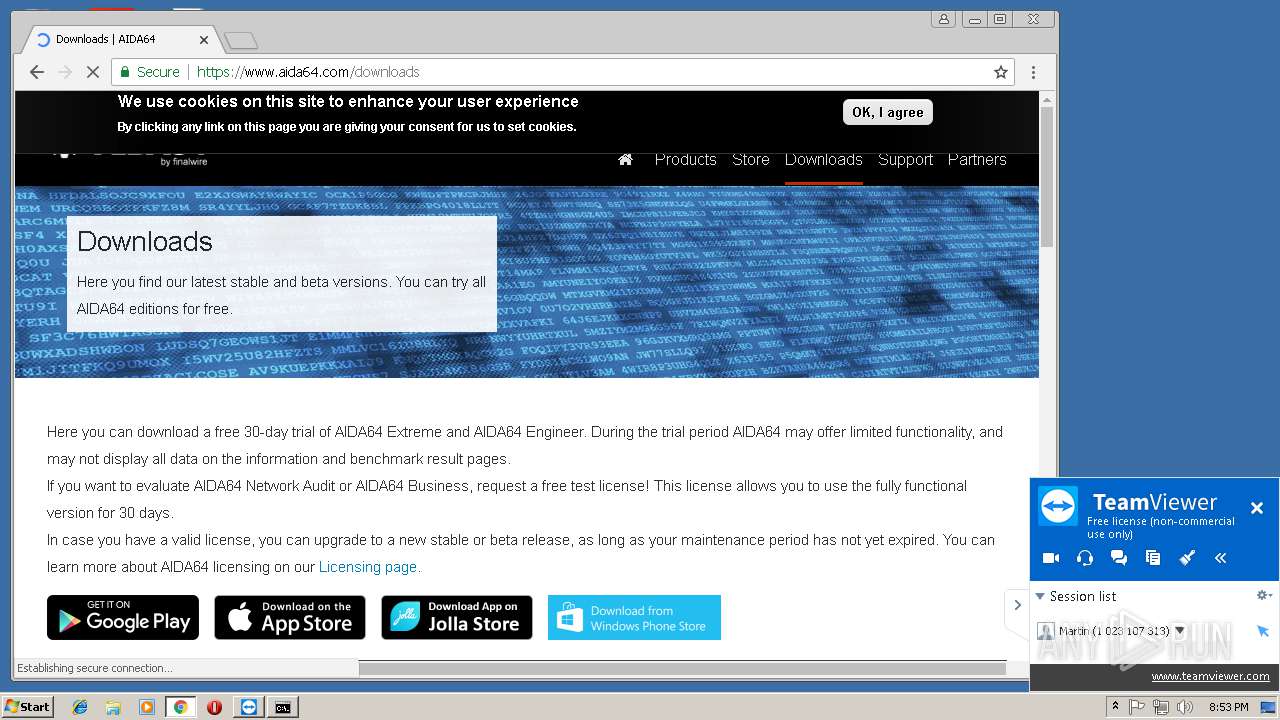
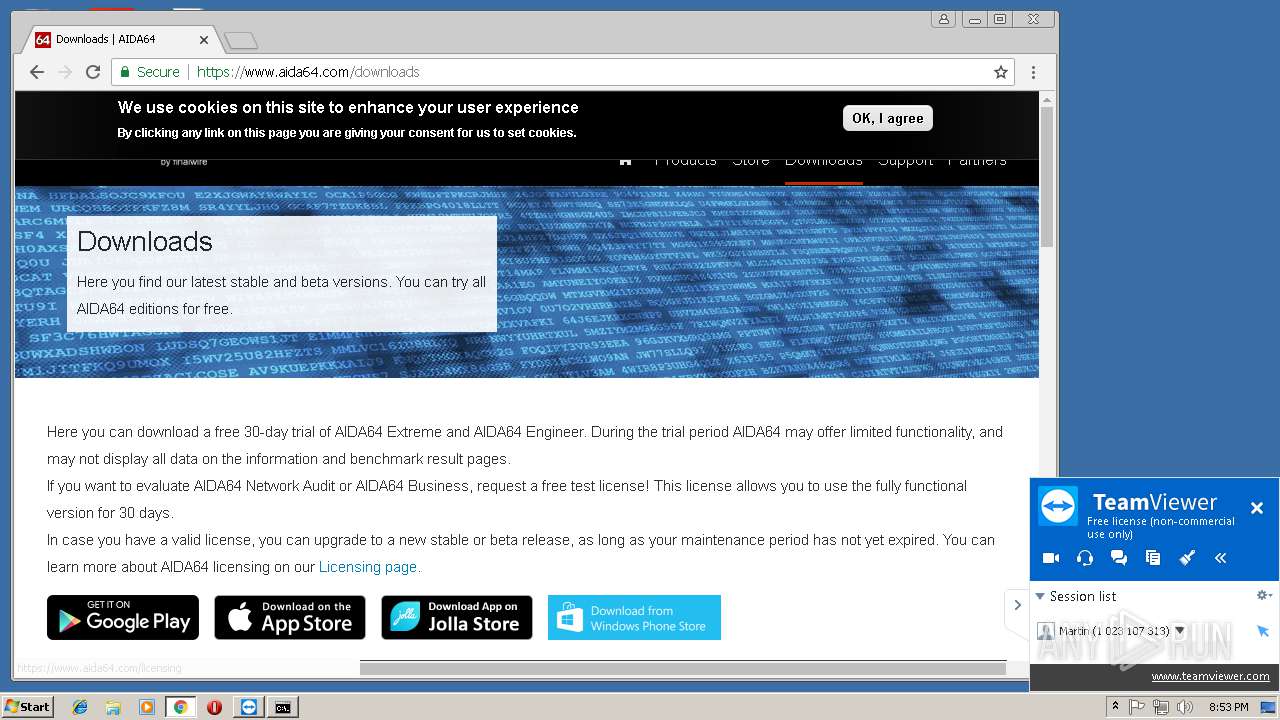
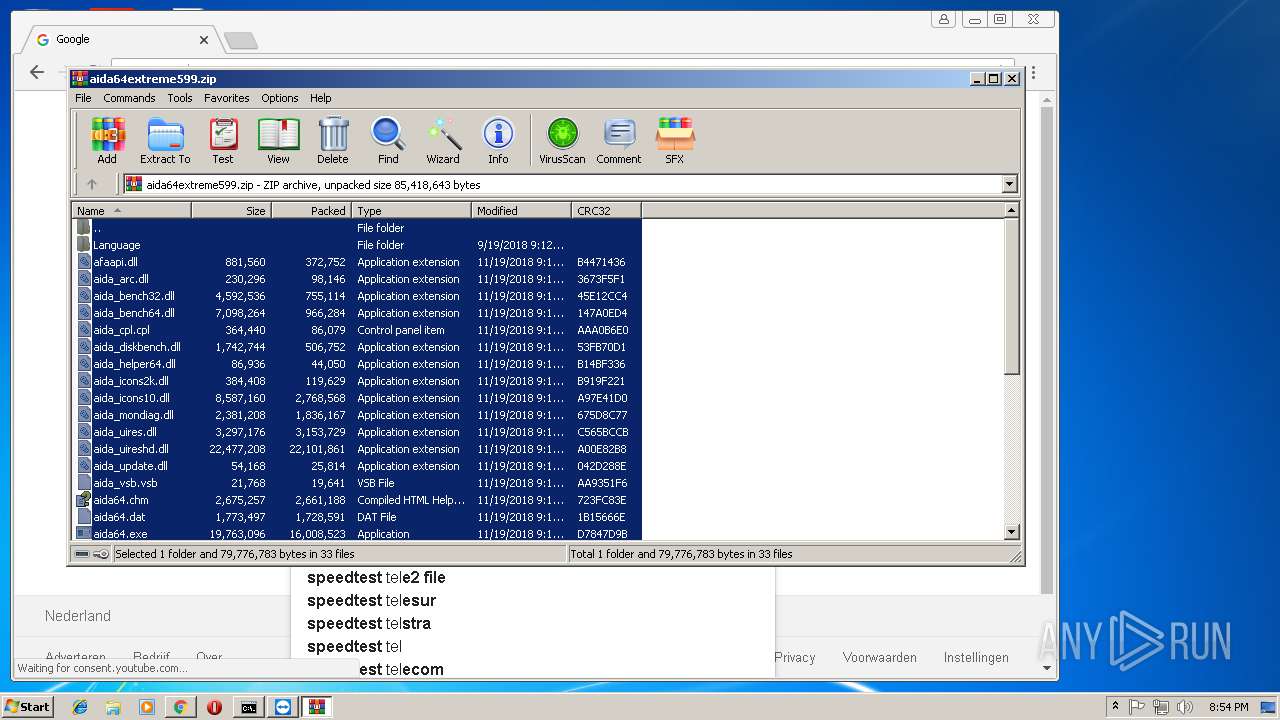
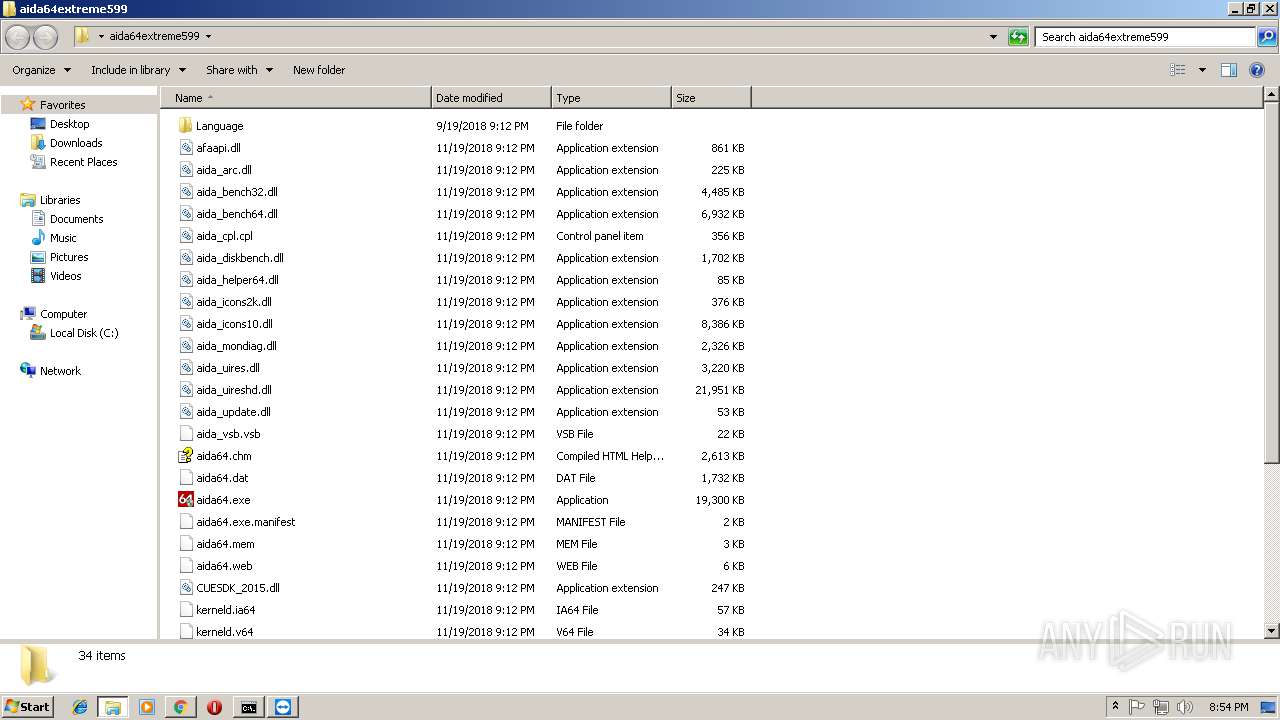
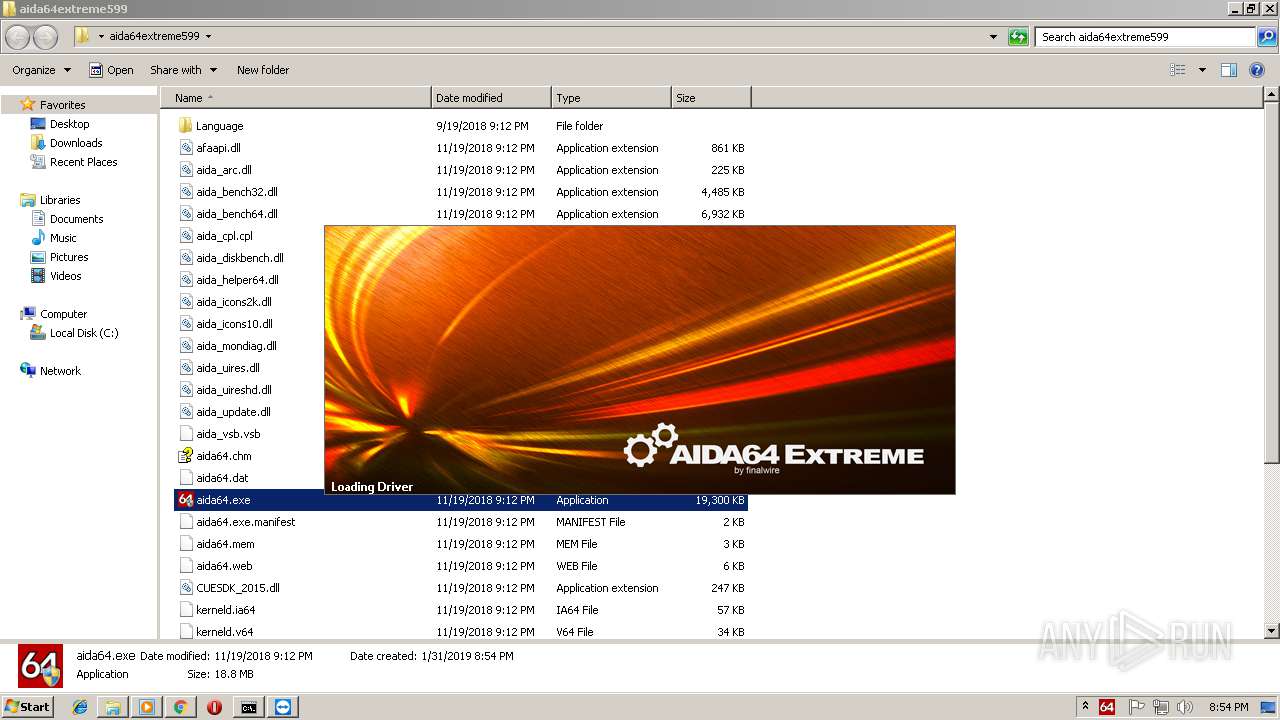
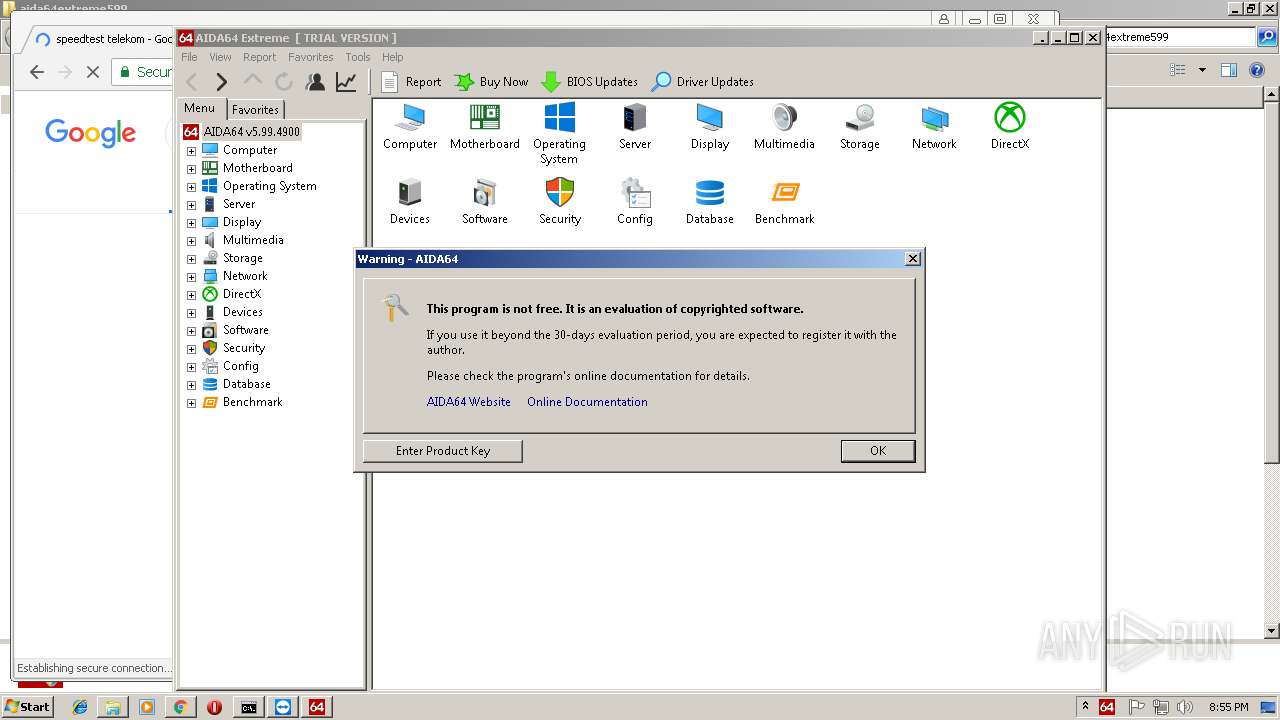
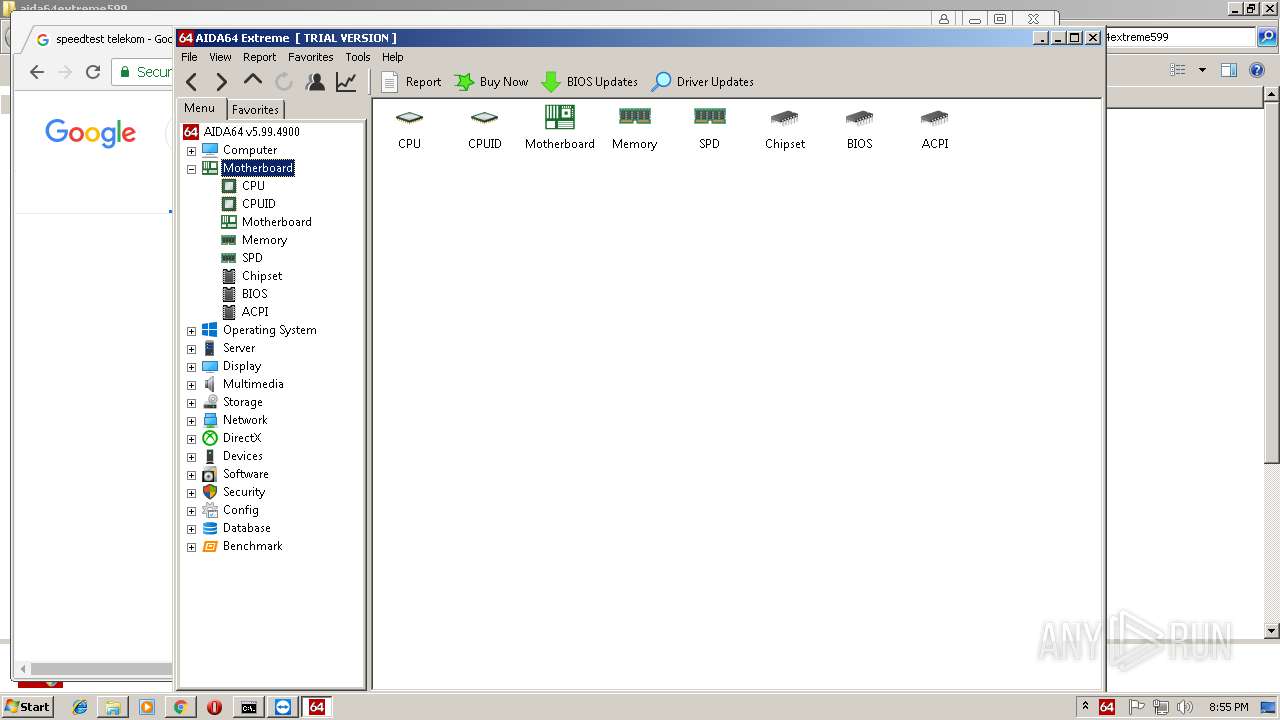
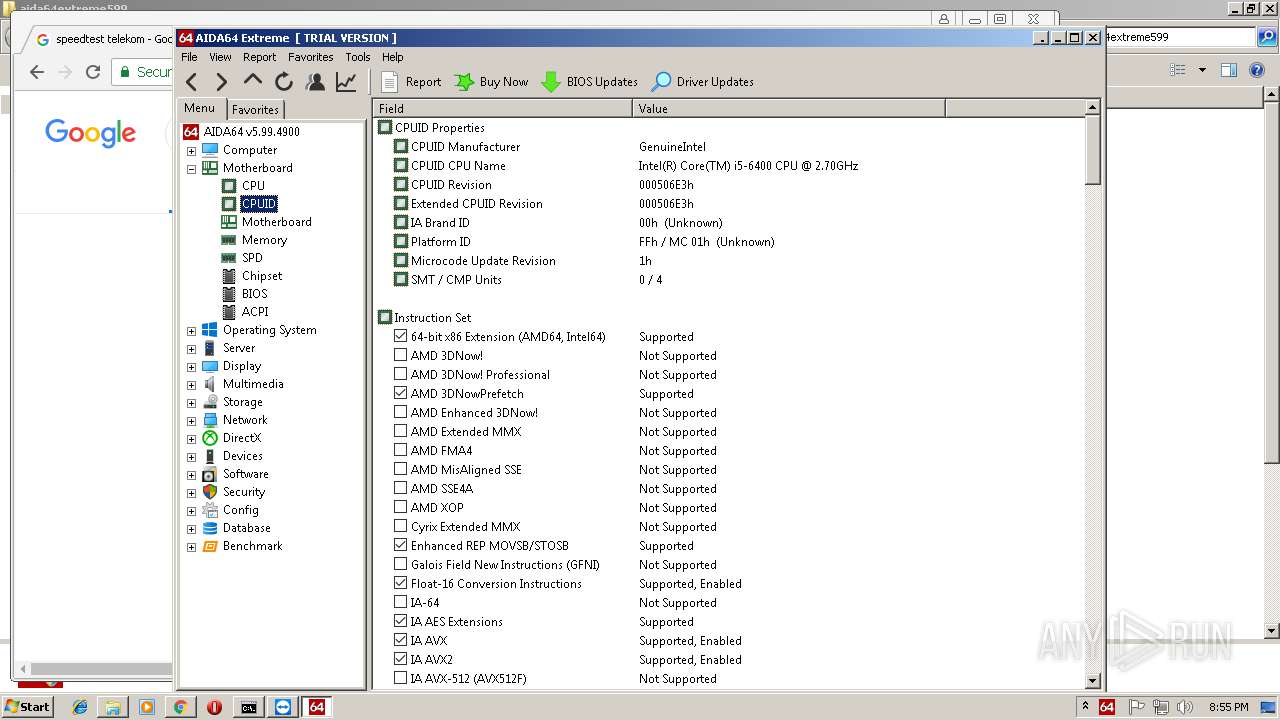
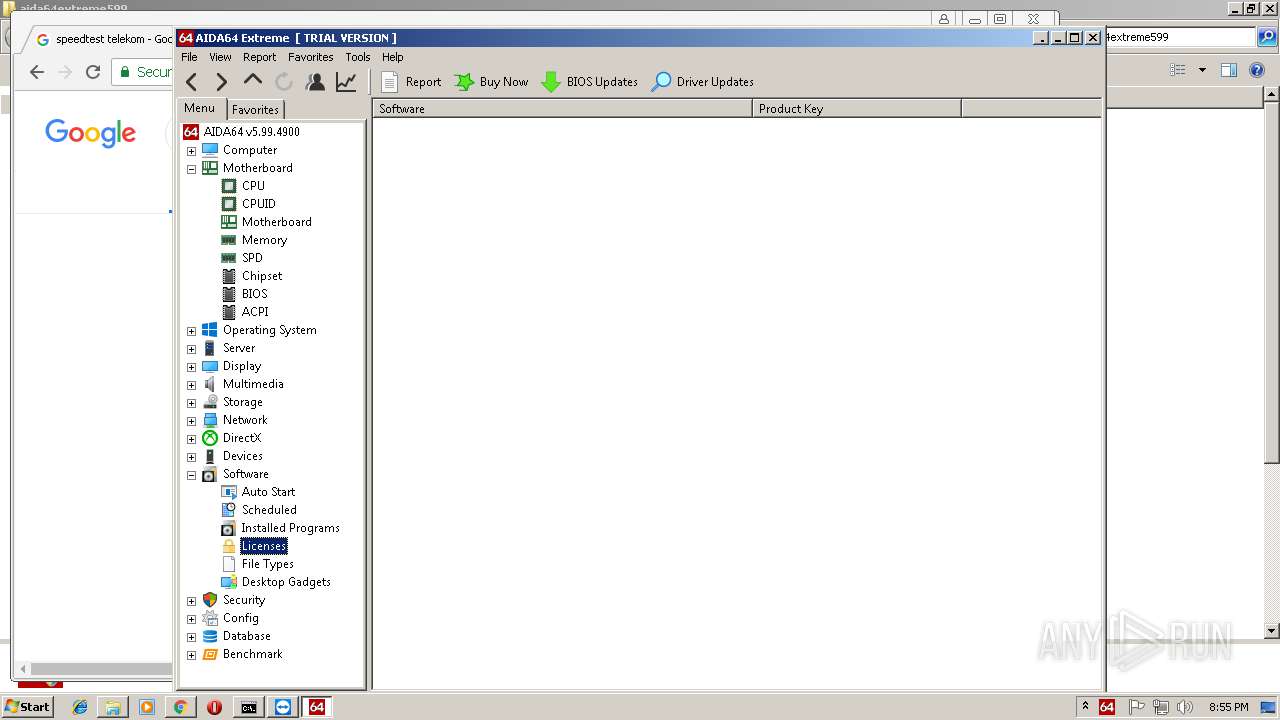
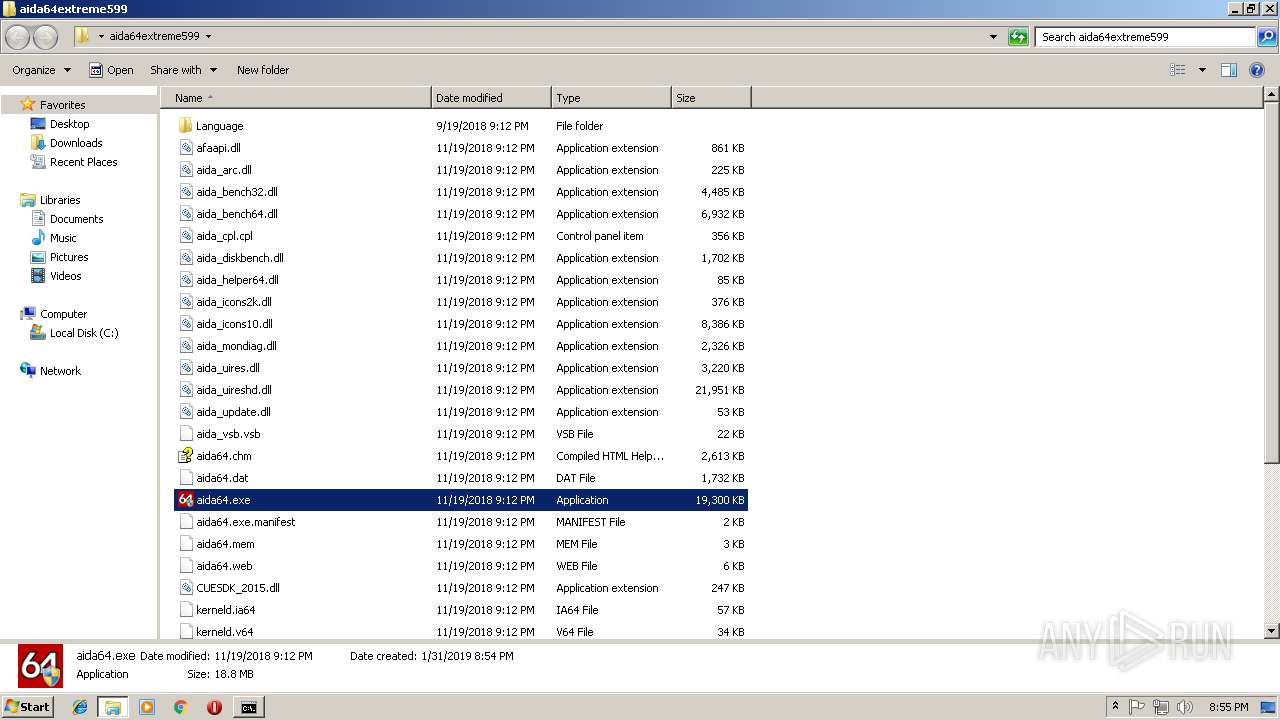
- aida64.exe (PID: 2996)
- aida64.exe (PID: 2120)
Loads dropped or rewritten executable
- TeamViewer.exe (PID: 3864)
- TeamViewer.exe (PID: 2848)
- TeamViewerQS.exe (PID: 480)
- TeamViewer_Desktop.exe (PID: 3852)
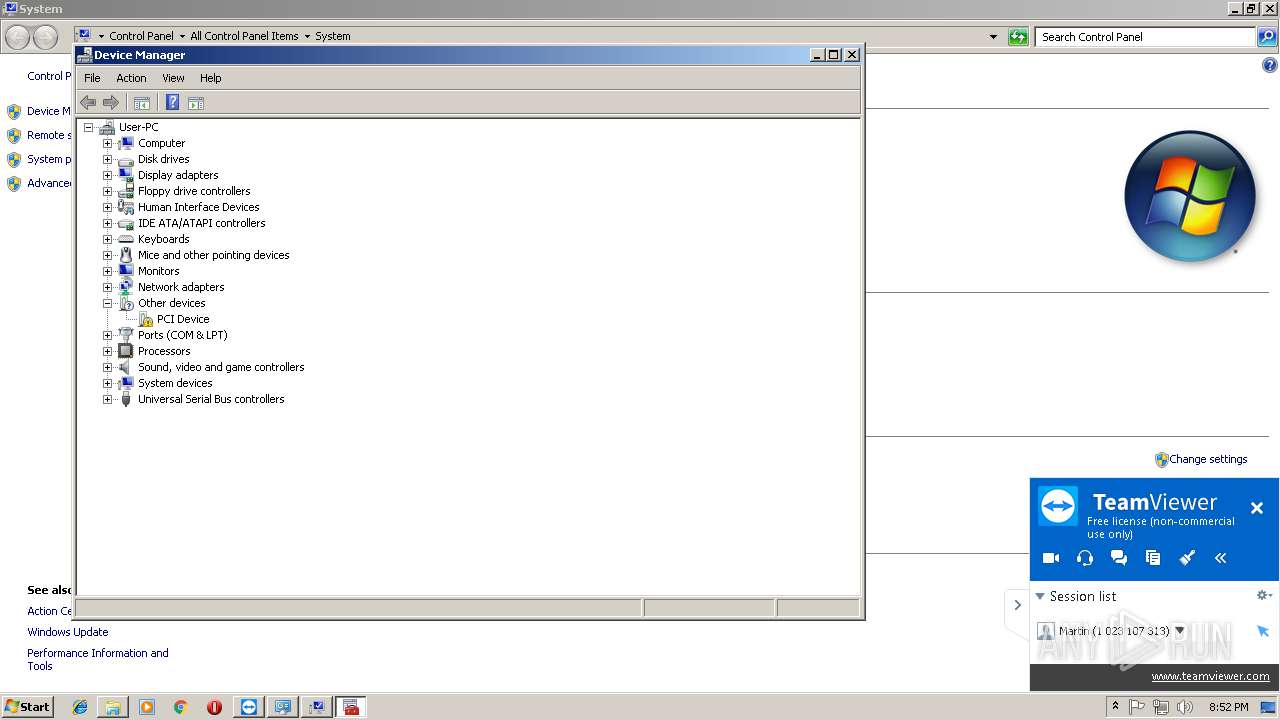
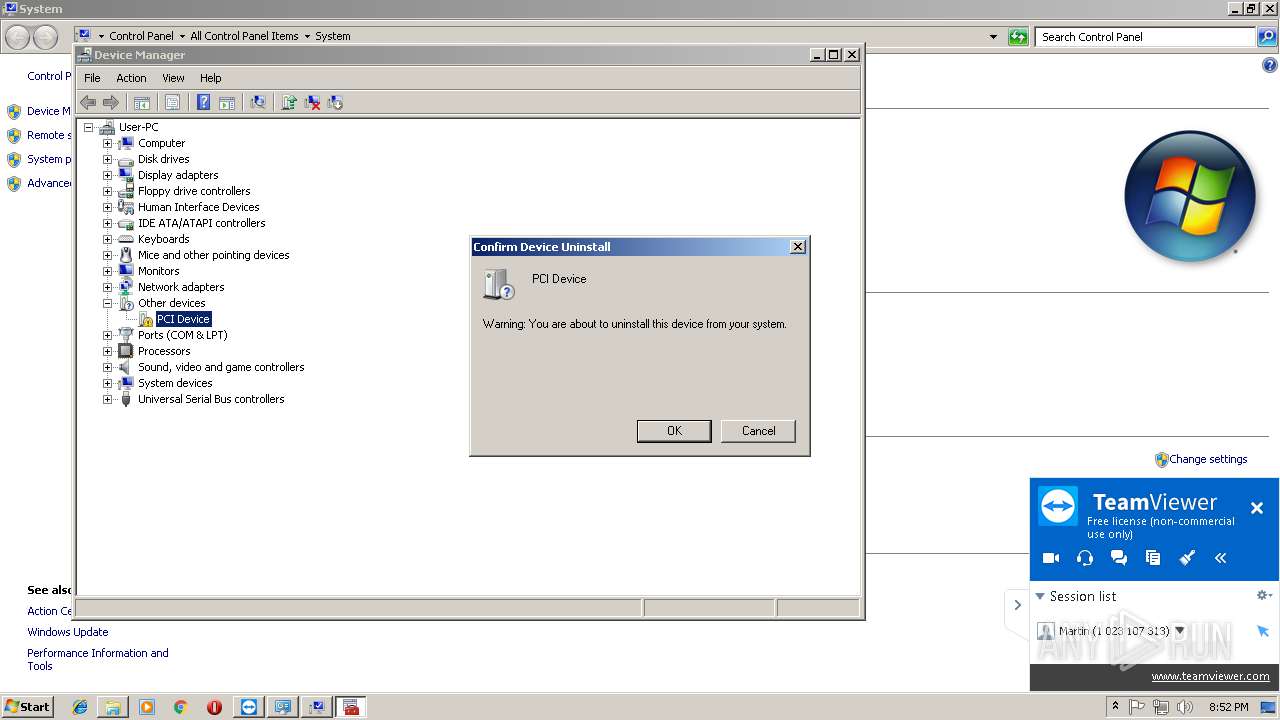
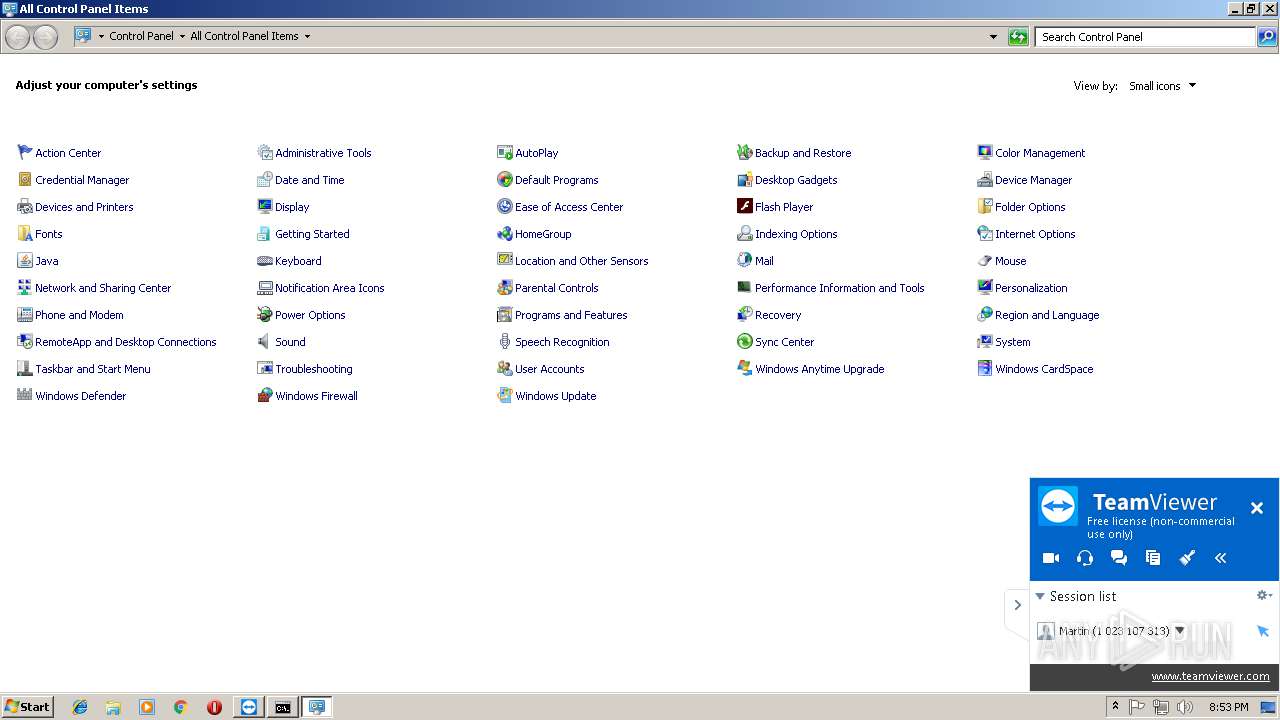
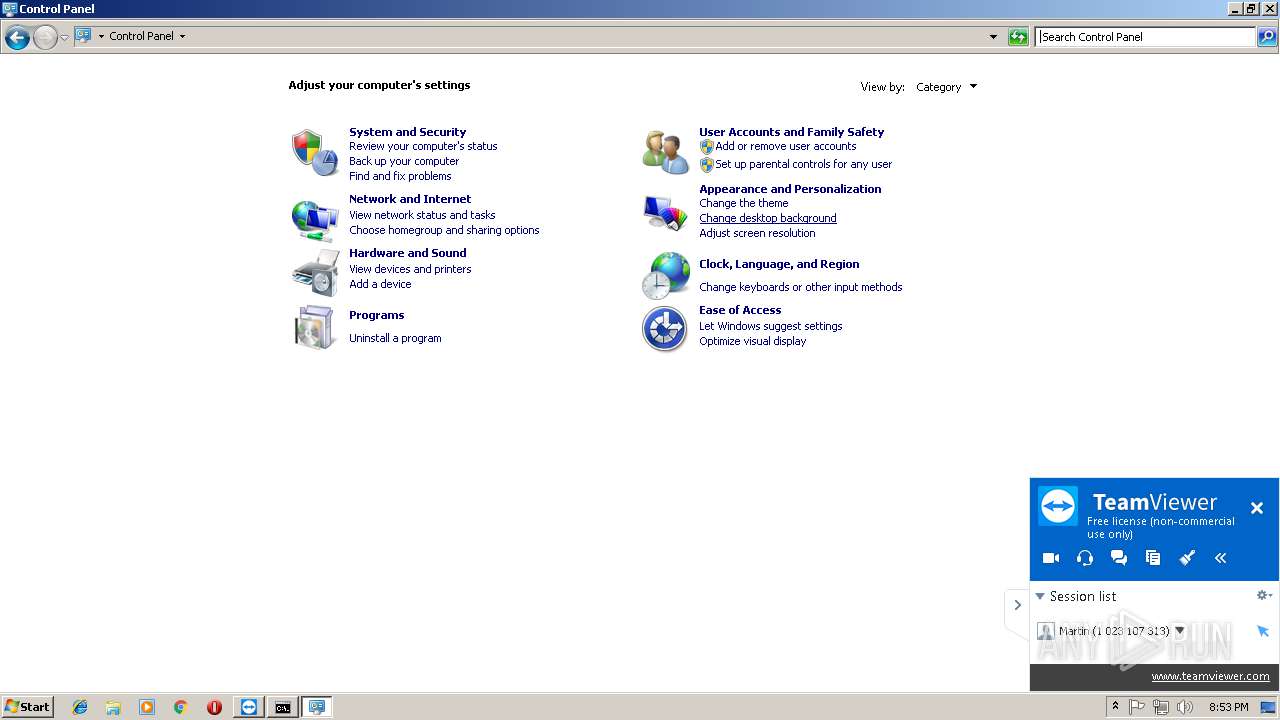
- control.exe (PID: 3040)
- tv_w32.exe (PID: 3280)
- dwm.exe (PID: 1968)
- wuapp.exe (PID: 3932)
- explorer.exe (PID: 2028)
- DllHost.exe (PID: 3940)
- control.exe (PID: 1336)
- consent.exe (PID: 2492)
- DllHost.exe (PID: 1244)
- DllHost.exe (PID: 3820)
- conhost.exe (PID: 2904)
- mmc.exe (PID: 4004)
- consent.exe (PID: 1532)
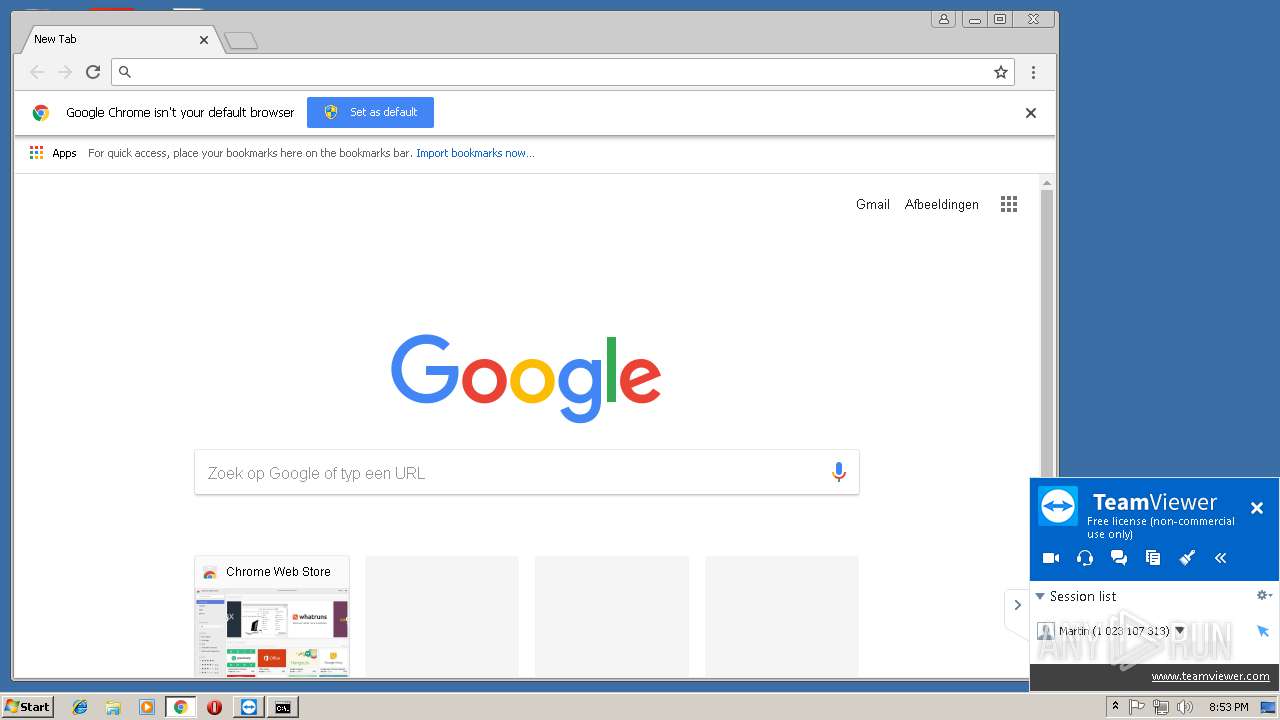
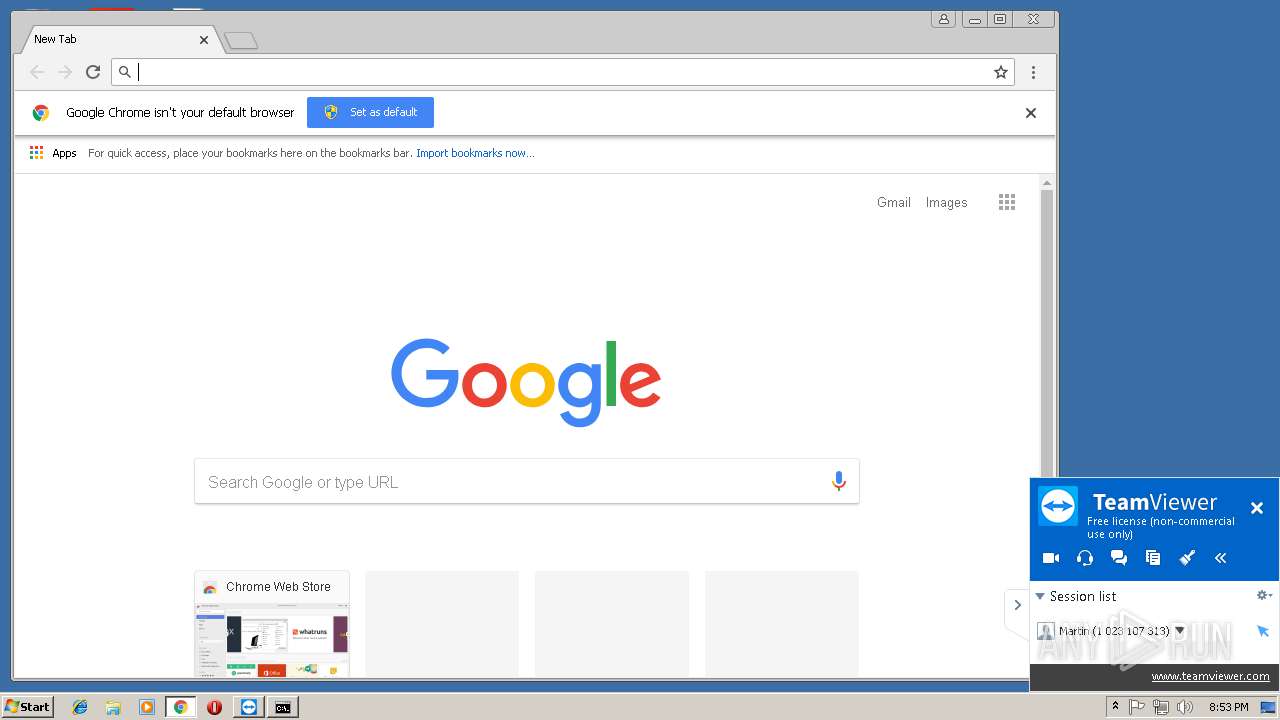
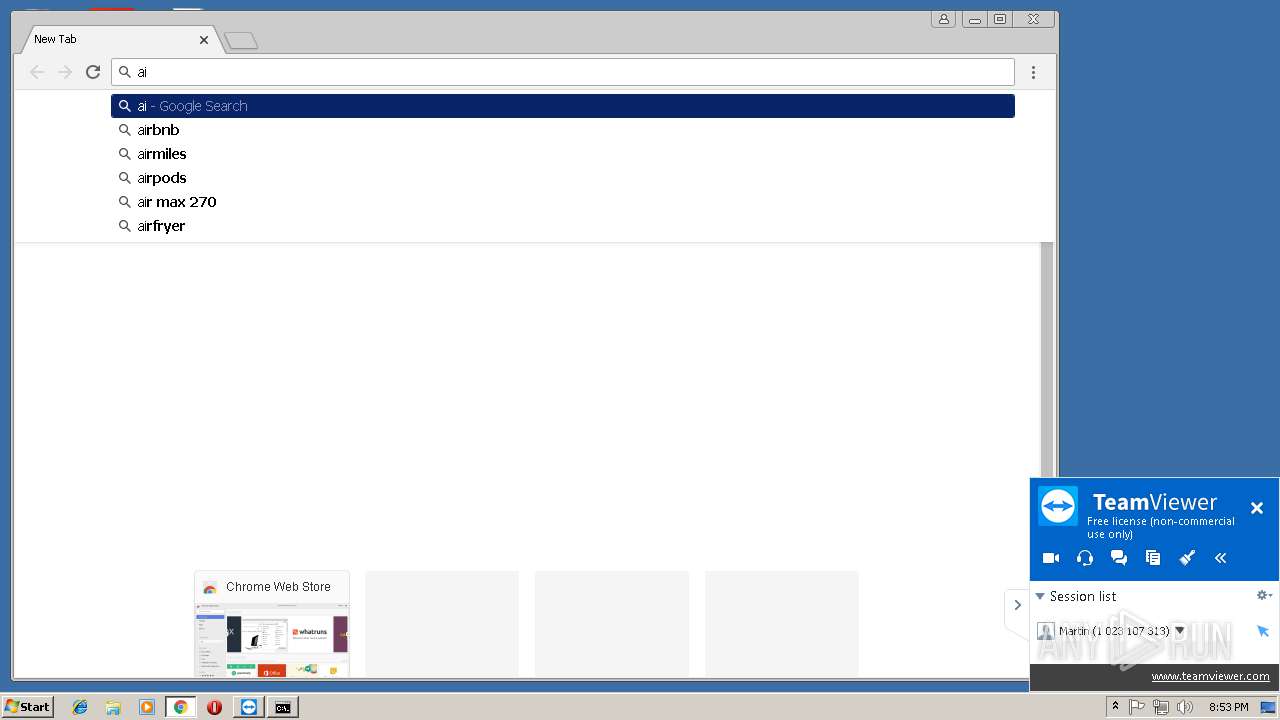
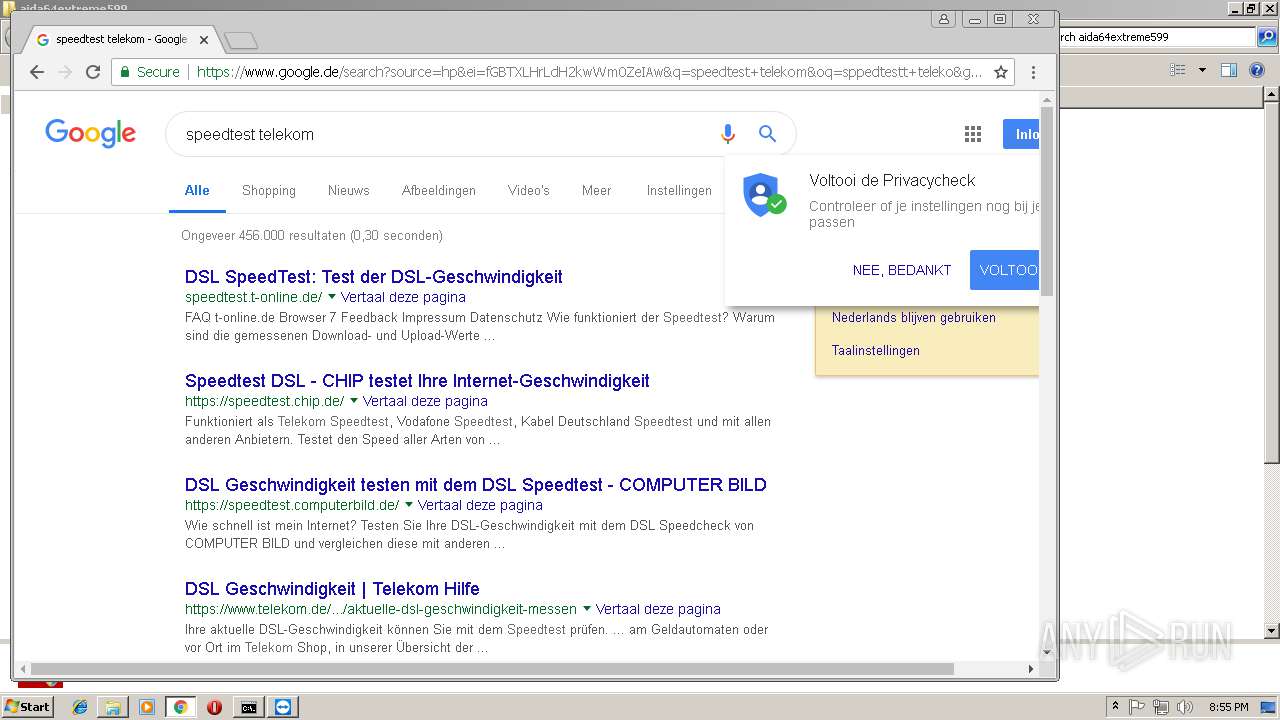
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3776)
- taskmgr.exe (PID: 2832)
- chrome.exe (PID: 4036)
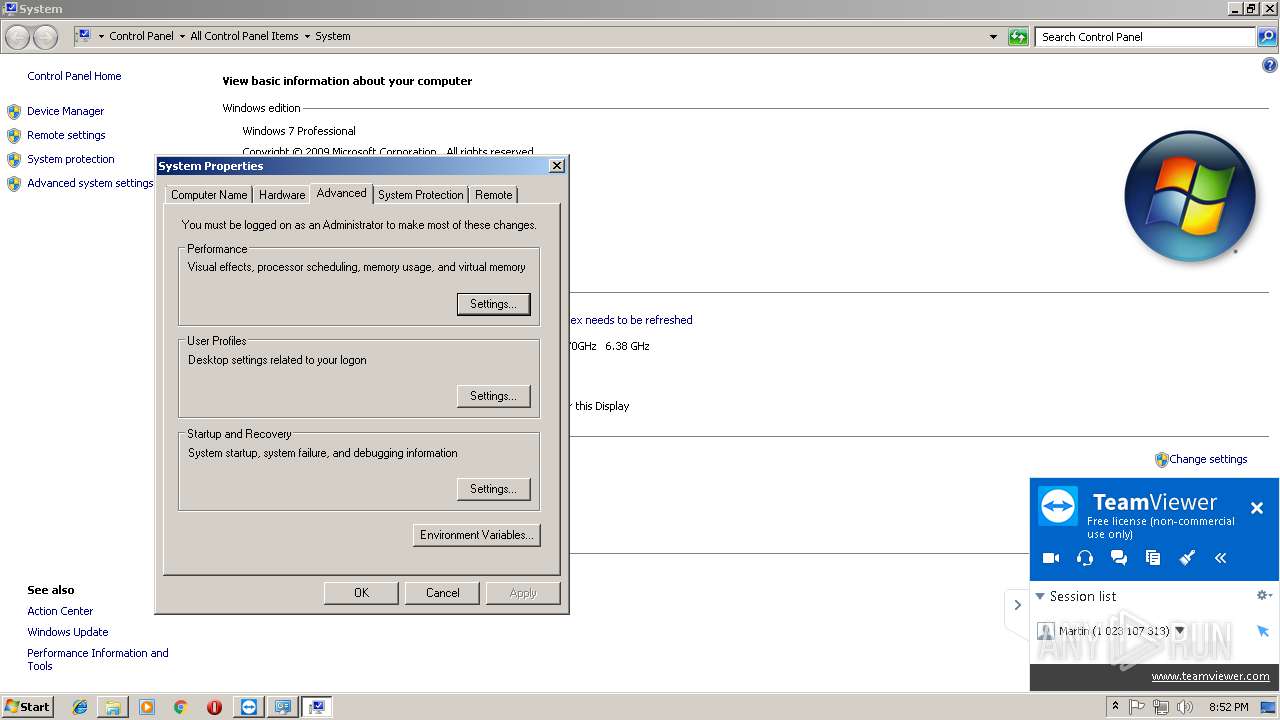
- systempropertiesadvanced.exe (PID: 3536)
- chrome.exe (PID: 2648)
- SearchProtocolHost.exe (PID: 1688)
- aida64.exe (PID: 2996)
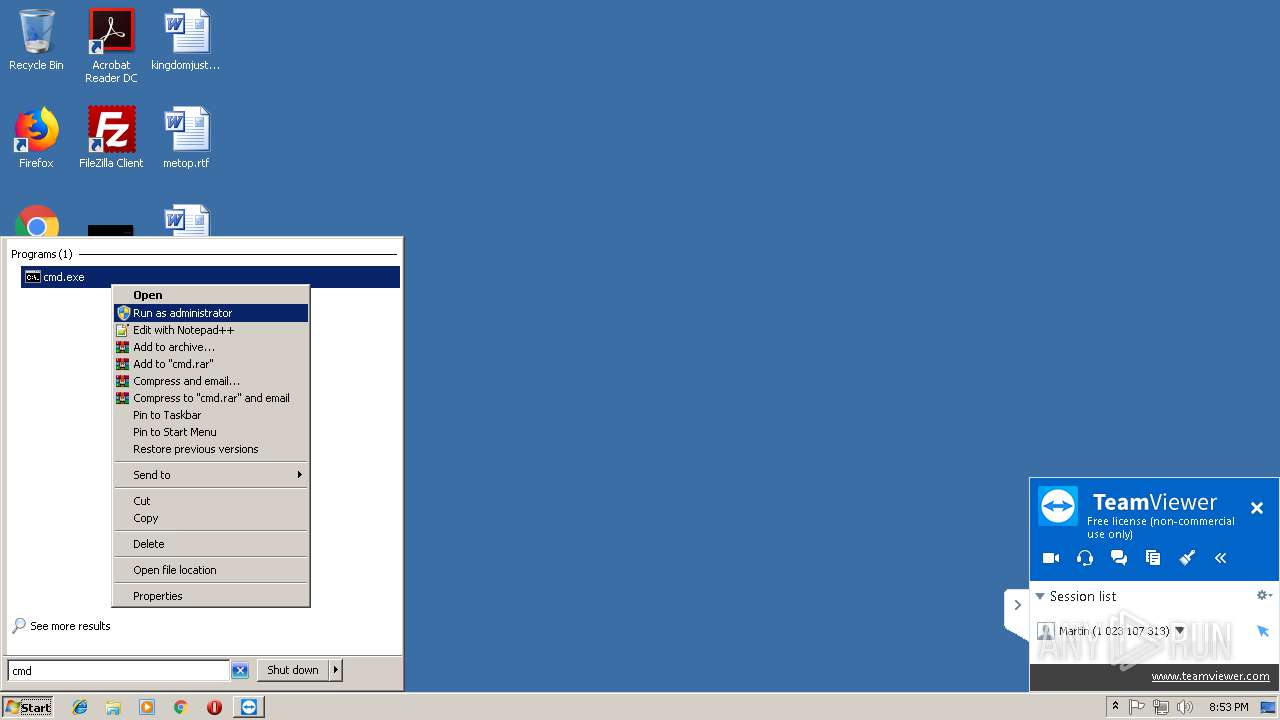
Runs app for hidden code execution
- explorer.exe (PID: 2028)
Changes settings of System certificates
- mshta.exe (PID: 2780)
Loads the Task Scheduler COM API
- aida64.exe (PID: 2996)
SUSPICIOUS
Application launched itself
- TeamViewer.exe (PID: 2848)
Connects to unusual port
- TeamViewer.exe (PID: 3864)
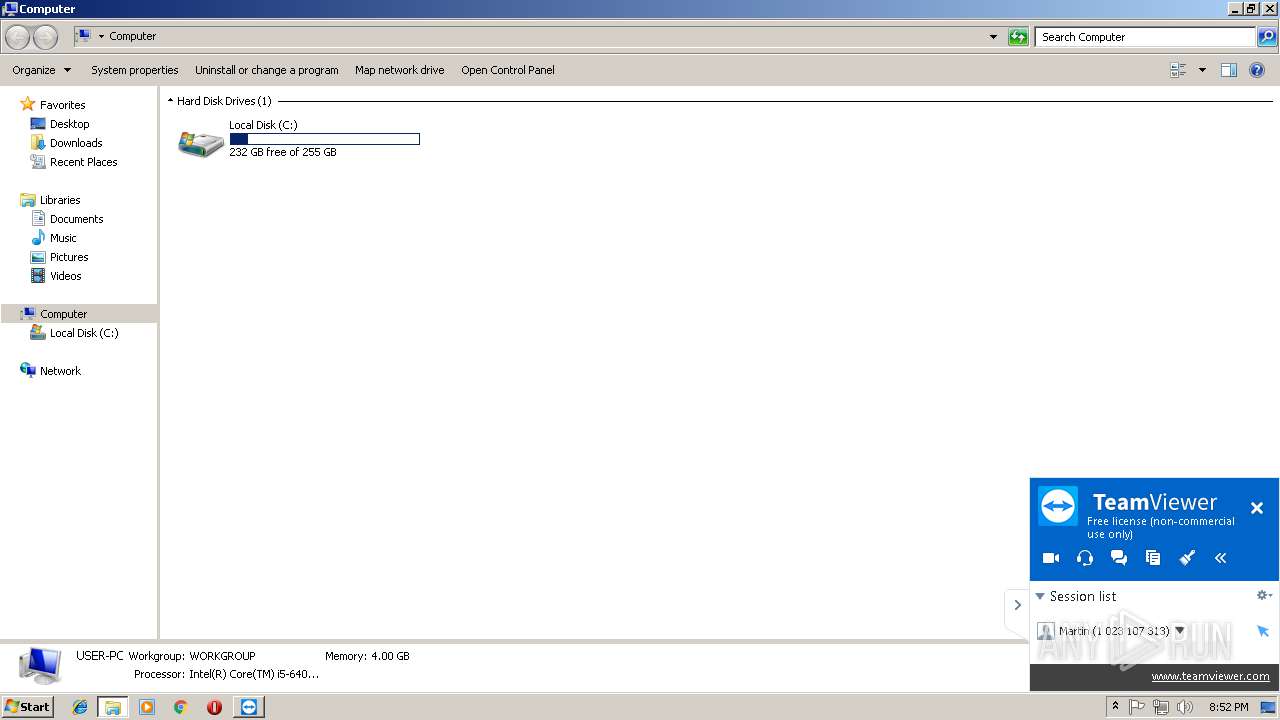
Creates files in the user directory
- TeamViewer.exe (PID: 2848)
- explorer.exe (PID: 2028)
- mshta.exe (PID: 2780)
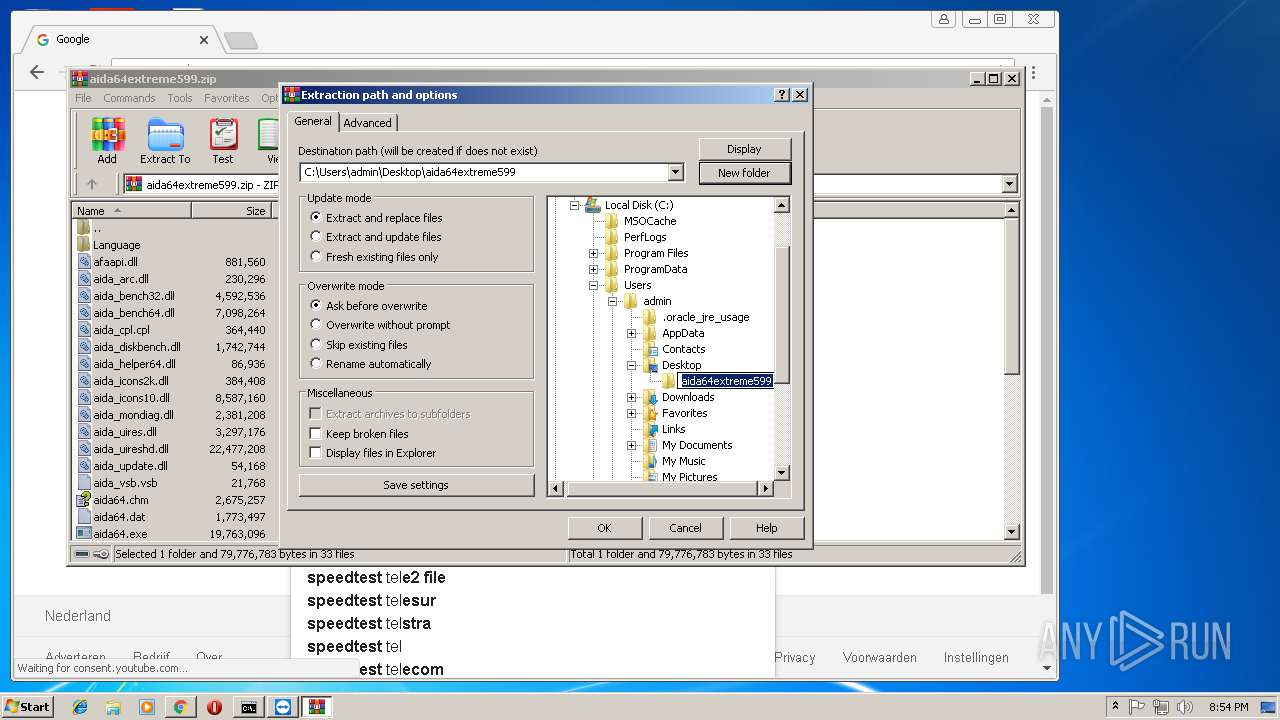
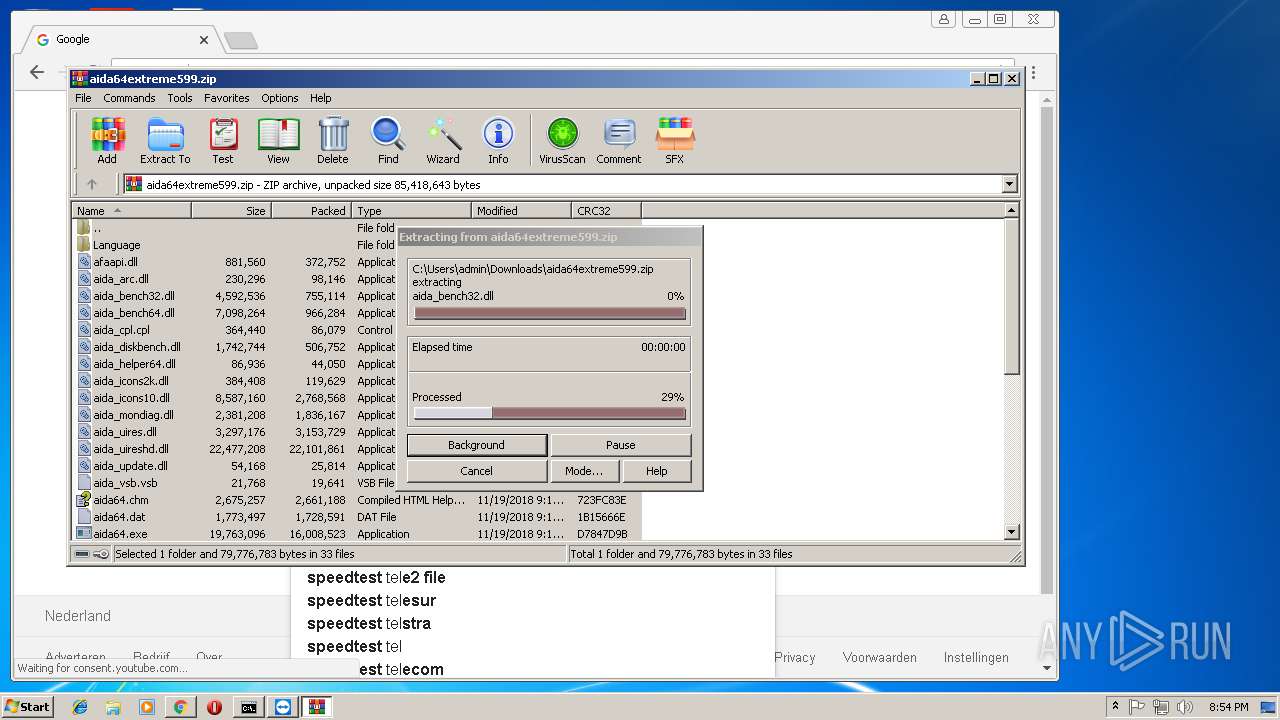
Executable content was dropped or overwritten
- TeamViewerQS.exe (PID: 480)
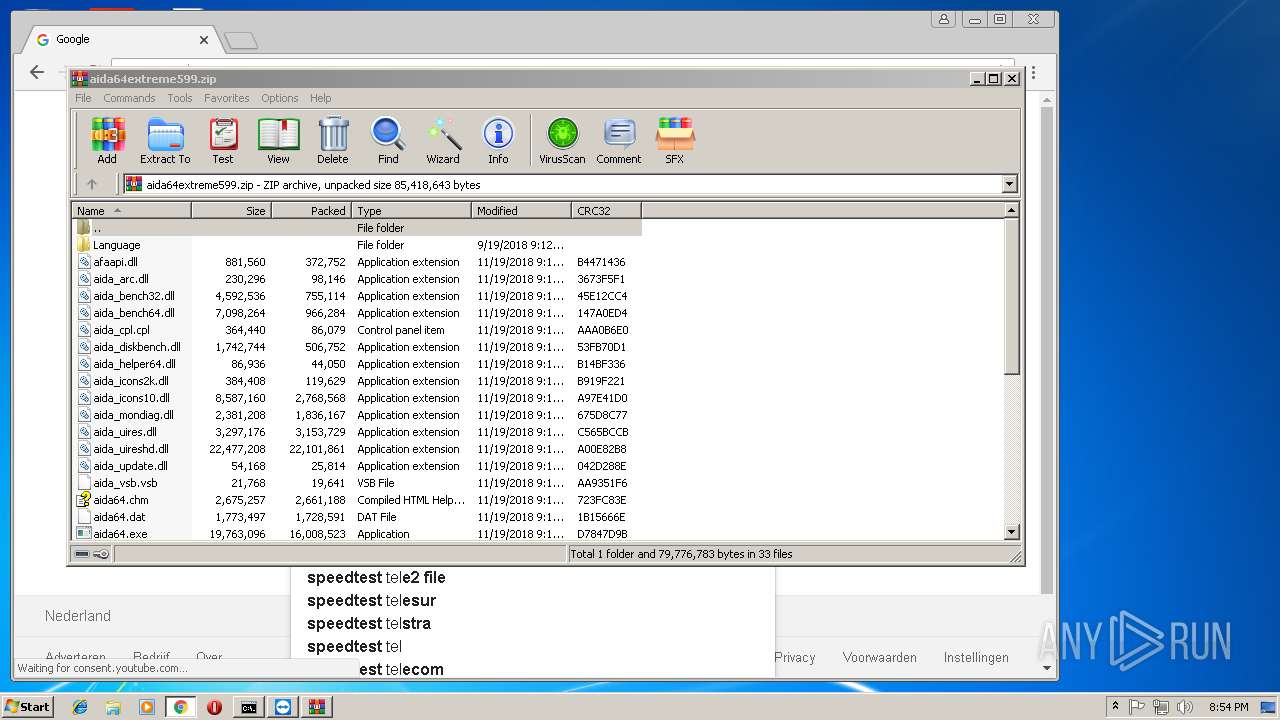
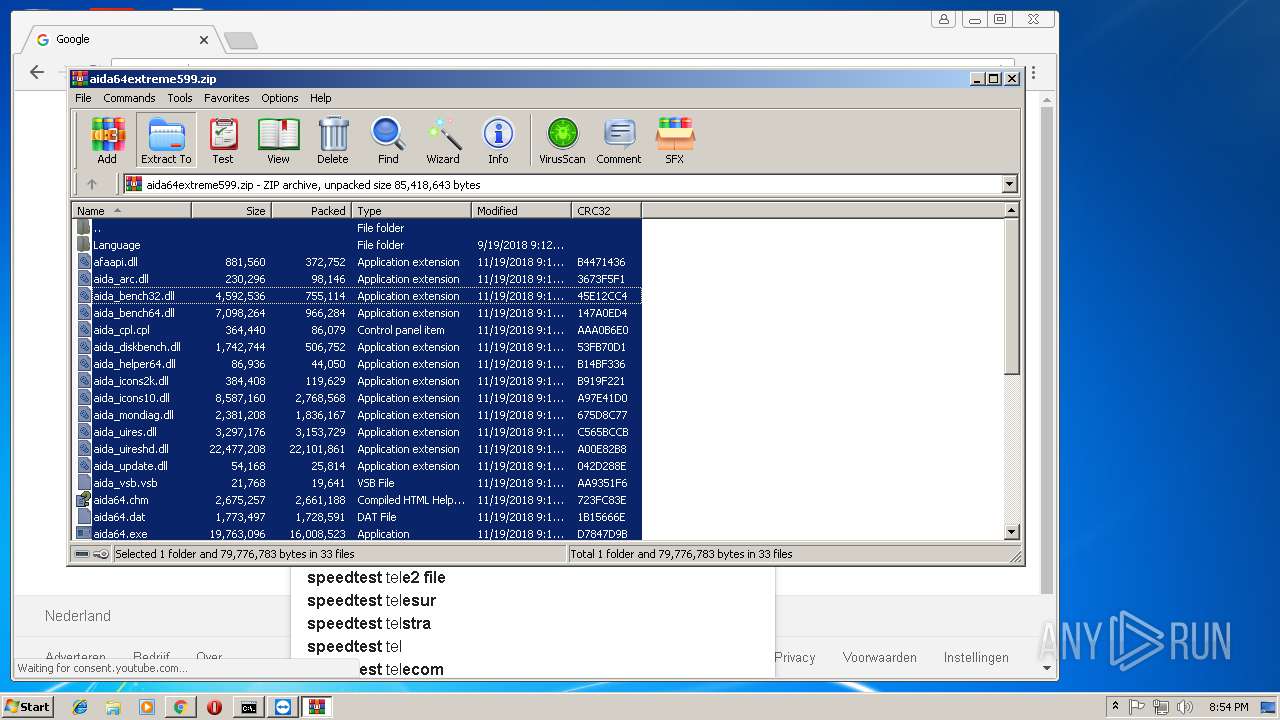
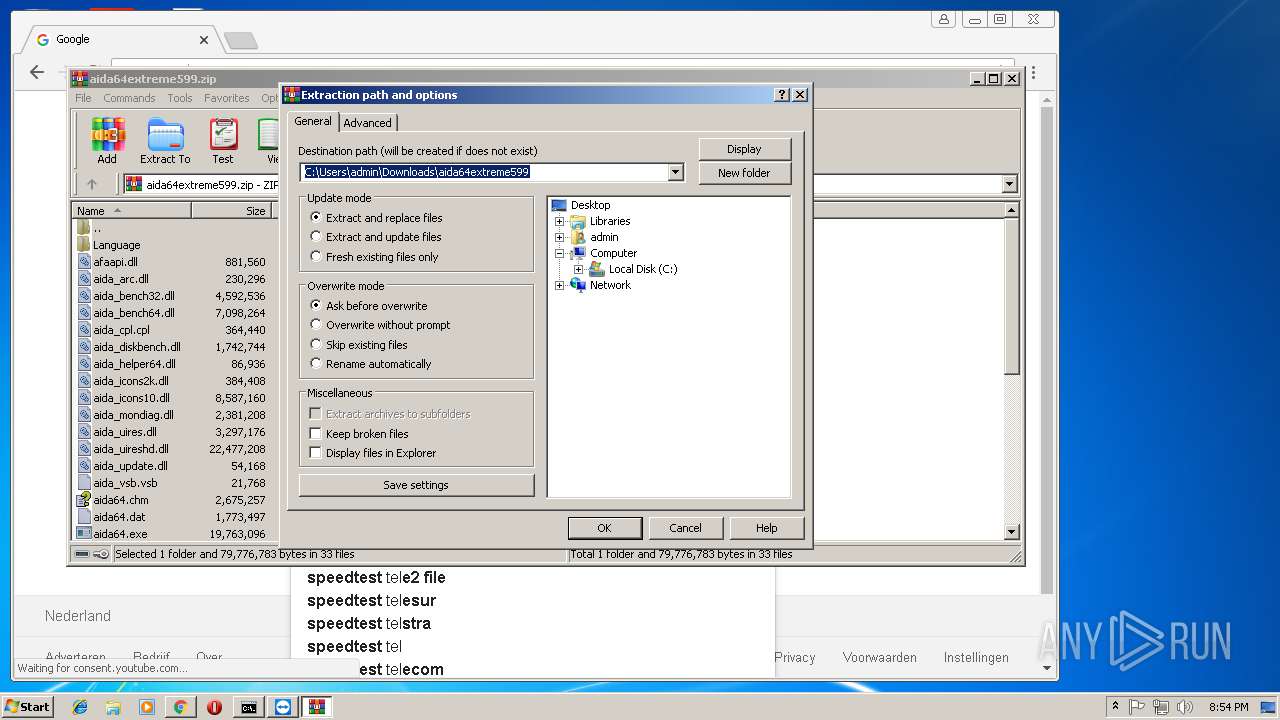
- WinRAR.exe (PID: 3720)
Reads Internet Cache Settings
- explorer.exe (PID: 2028)
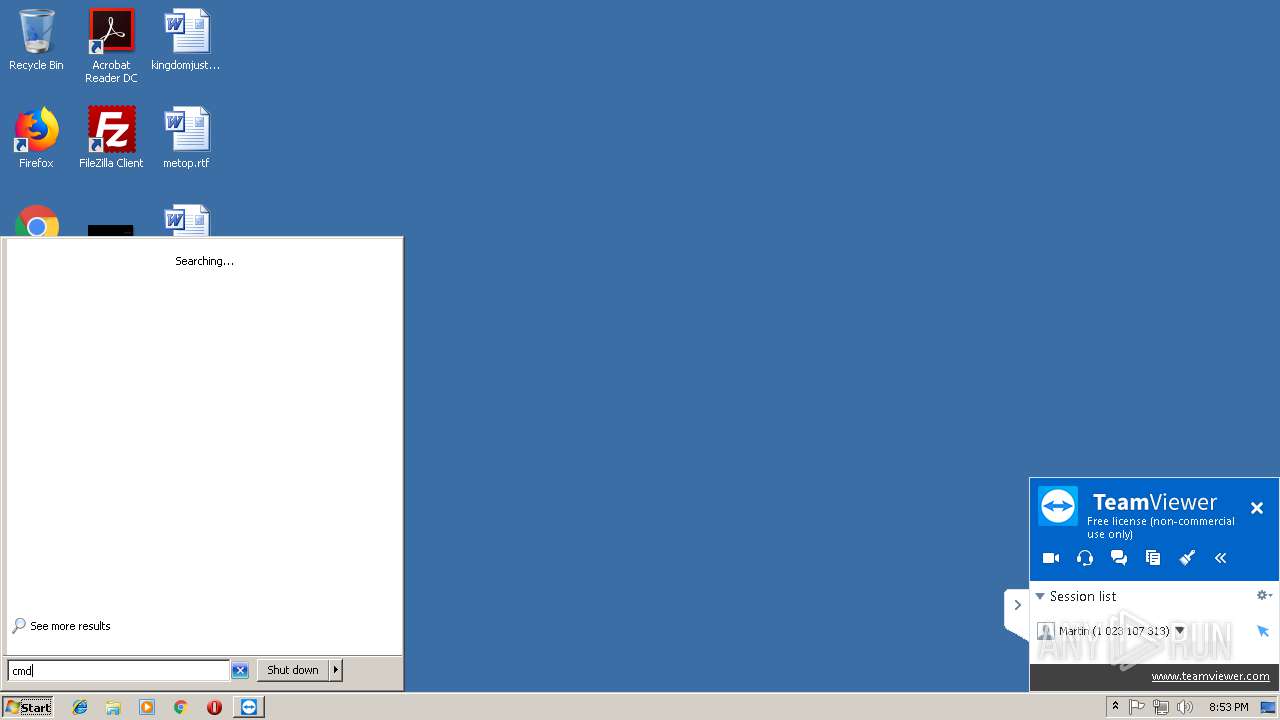
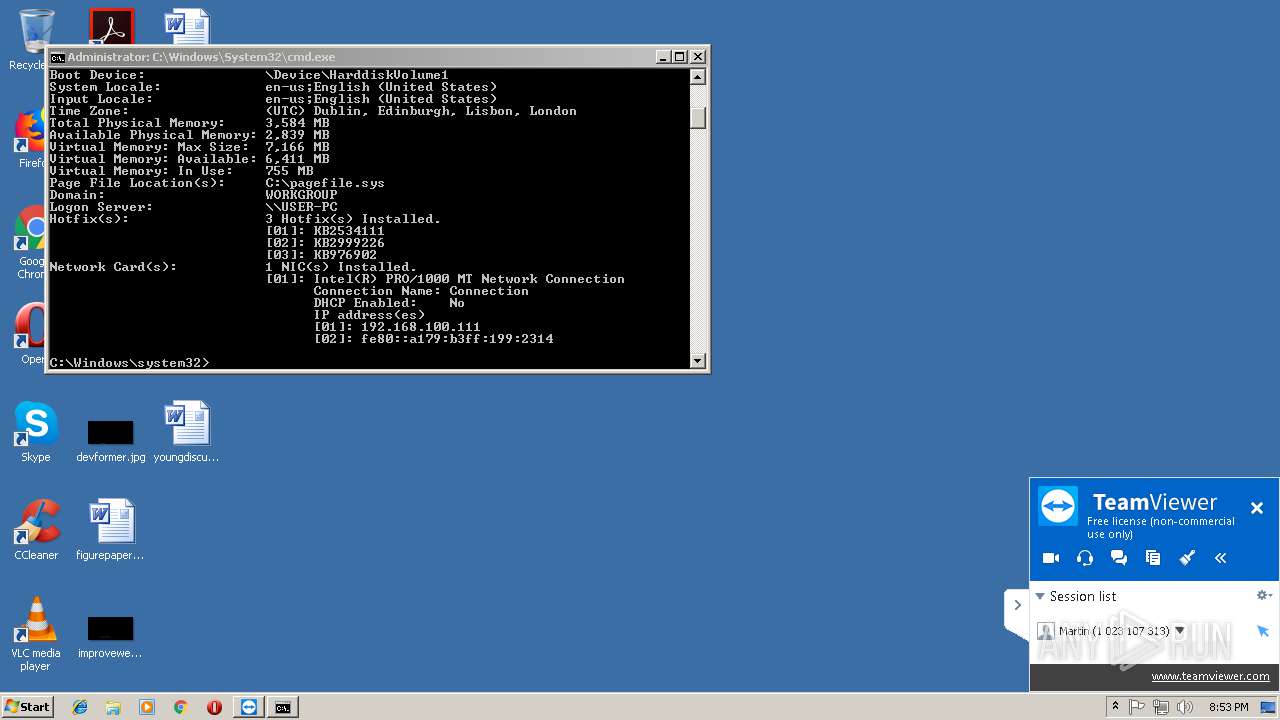
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 2800)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 2028)
Starts MSHTA.EXE for opening HTA or HTMLS files
- TeamViewer.exe (PID: 3864)
Adds / modifies Windows certificates
- mshta.exe (PID: 2780)
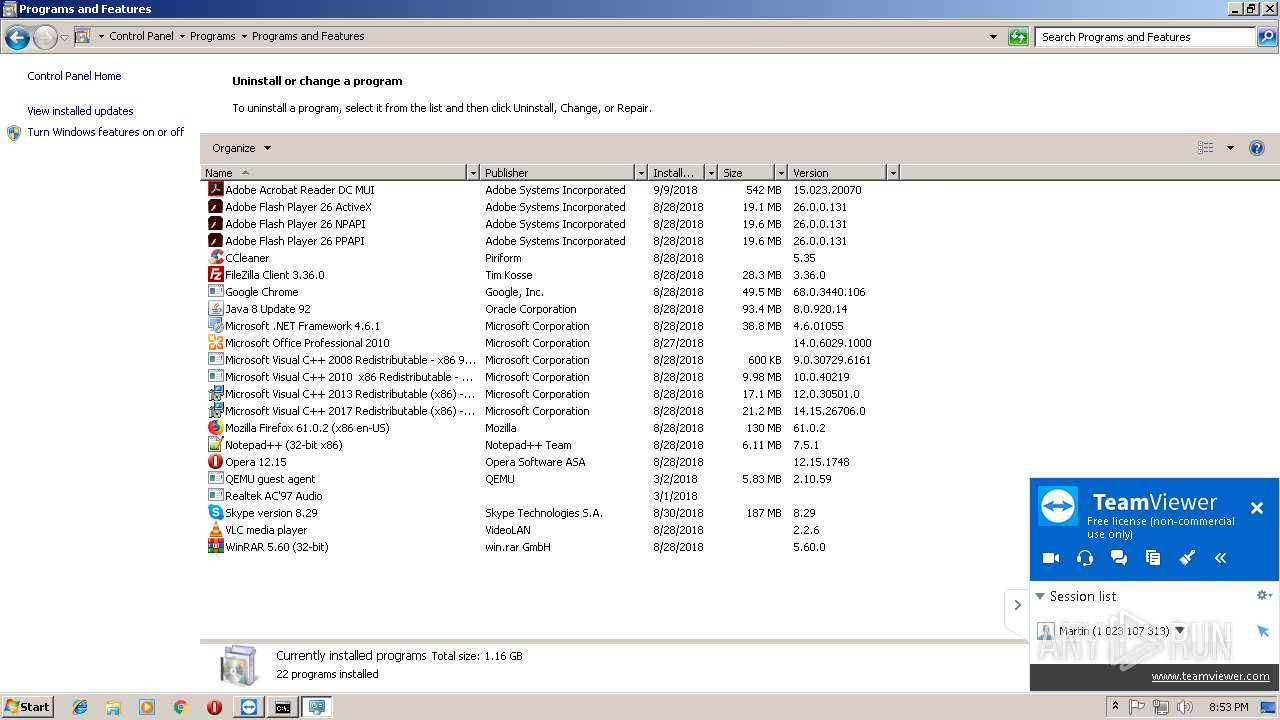
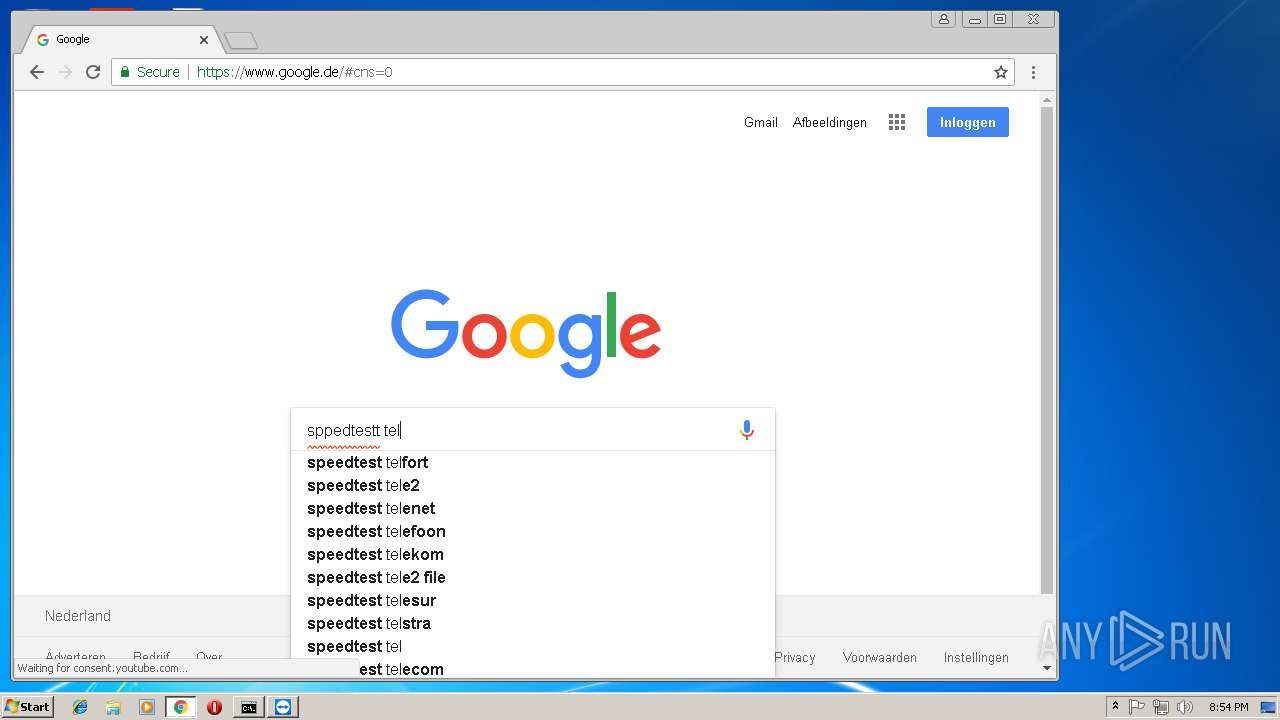
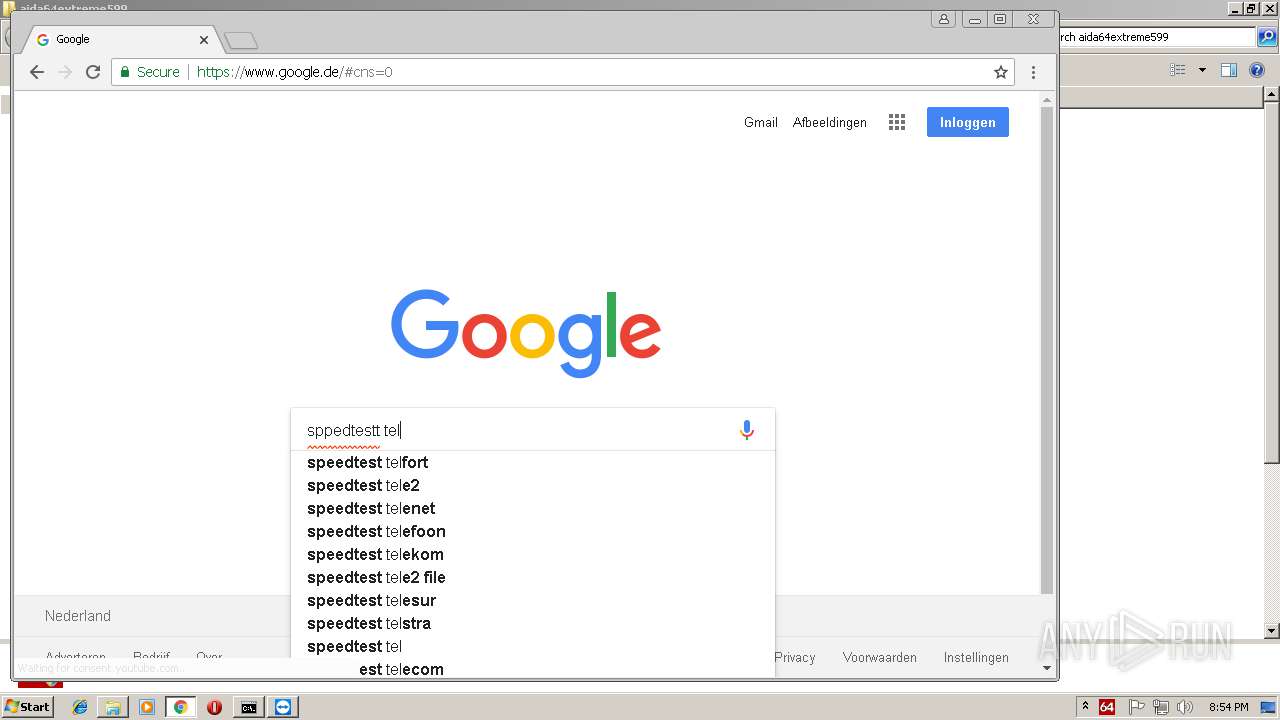
Searches for installed software
- explorer.exe (PID: 2028)
INFO
Application launched itself
- chrome.exe (PID: 4092)
Reads internet explorer settings
- mshta.exe (PID: 2780)
Reads settings of System Certificates
- chrome.exe (PID: 4092)
- mshta.exe (PID: 2780)
Reads Internet Cache Settings
- chrome.exe (PID: 4092)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 22:18:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.1.9025.0 |
| ProductVersionNumber: | 14.1.9025.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | TeamViewer Remote Control Application |
| CompanyName: | TeamViewer |
| LegalCopyright: | TeamViewer |
| ProductName: | TeamViewer QS |
| ProductVersion: | 14.1.9025.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Apr-2016 20:18:56 |
| Detected languages: |
|
| Comments: | TeamViewer Remote Control Application |
| CompanyName: | TeamViewer |
| LegalCopyright: | TeamViewer |
| ProductName: | TeamViewer QS |
| ProductVersion: | 14.1.9025.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Apr-2016 20:18:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45041 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9824 |
.ndata | 0x0002B000 | 0x00019000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00044000 | 0x00047200 | 0x00047200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.81977 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29548 | 1061 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.22479 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.43297 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.39572 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89069 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
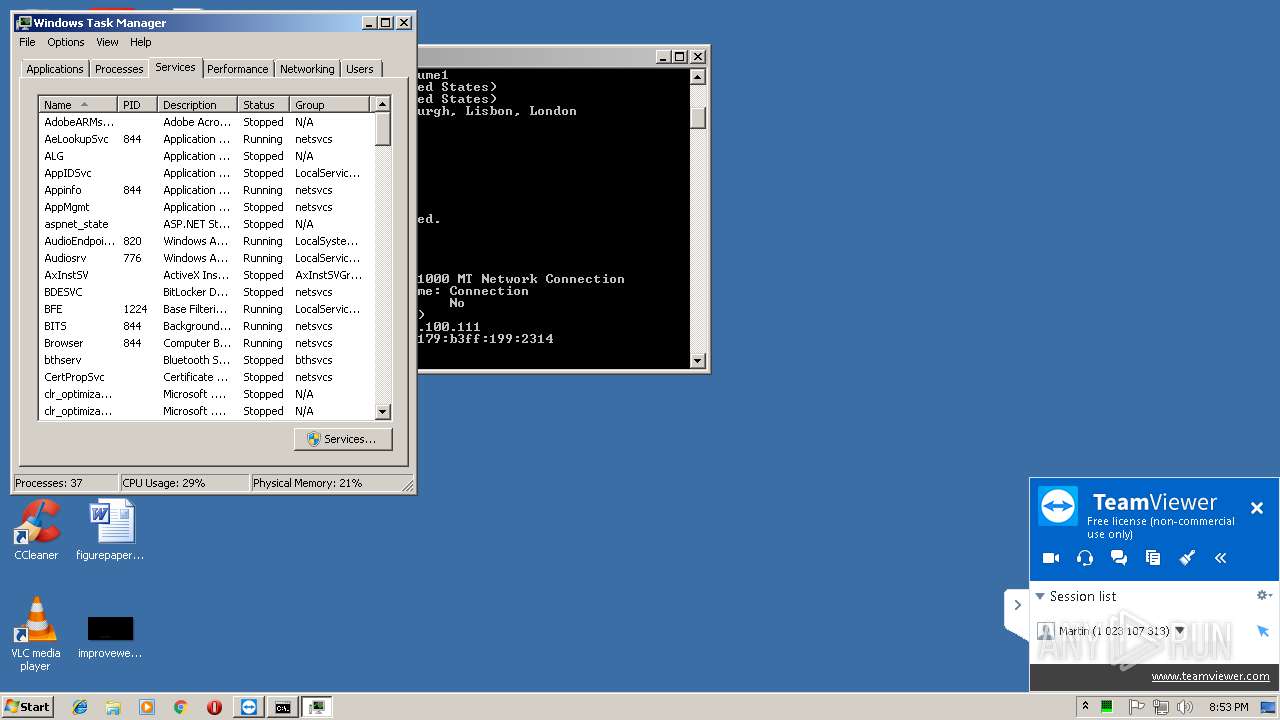
Total processes
88
Monitored processes
44
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9047353032818826034,15039675891040634233,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=257AF92791C9D040616A937E34D71798 --mojo-platform-channel-handle=3860 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 480 | "C:\Users\admin\AppData\Local\Temp\TeamViewerQS.exe" | C:\Users\admin\AppData\Local\Temp\TeamViewerQS.exe | explorer.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 920 | "C:\Windows\System32\ie4uinit.exe" -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | aida64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9047353032818826034,15039675891040634233,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4B57D4B67828759071A9F3CE943DE67B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4B57D4B67828759071A9F3CE943DE67B --renderer-client-id=8 --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1244 | C:\Windows\system32\DllHost.exe /Processid:{E10F6C3A-F1AE-4ADC-AA9D-2FE65525666E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\Windows\System32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | consent.exe 844 240 01E690F8 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe7_ Global\UsGthrCtrlFltPipeMssGthrPipe7 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9047353032818826034,15039675891040634233,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3AEE0BEF4D1E47C7C0A792F2B1159962 --mojo-platform-channel-handle=3120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1968 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 950
Read events
7 358
Write events
1 577
Delete events
15
Modification events
| (PID) Process: | (480) TeamViewerQS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (480) TeamViewerQS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TeamViewer.exe | |||
| (PID) Process: | (2848) TeamViewer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2848) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3864) TeamViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TeamViewer.exe | |||
| (PID) Process: | (3864) TeamViewer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3864) TeamViewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TeamViewer\DefaultSettings |
| Operation: | write | Name: | Autostart_GUI |
Value: 0 | |||
| (PID) Process: | (3864) TeamViewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TeamViewer\Temp |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
73
Suspicious files
113
Text files
208
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\tvqsfiles.7z | — | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe | — | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Service.exe | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_ar.dll | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Note.exe | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_da.dll | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_bg.dll | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_fr.dll | executable | |
MD5:— | SHA256:— | |||
| 480 | TeamViewerQS.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer_Resource_de.dll | executable | |
MD5:— | SHA256:— | |||
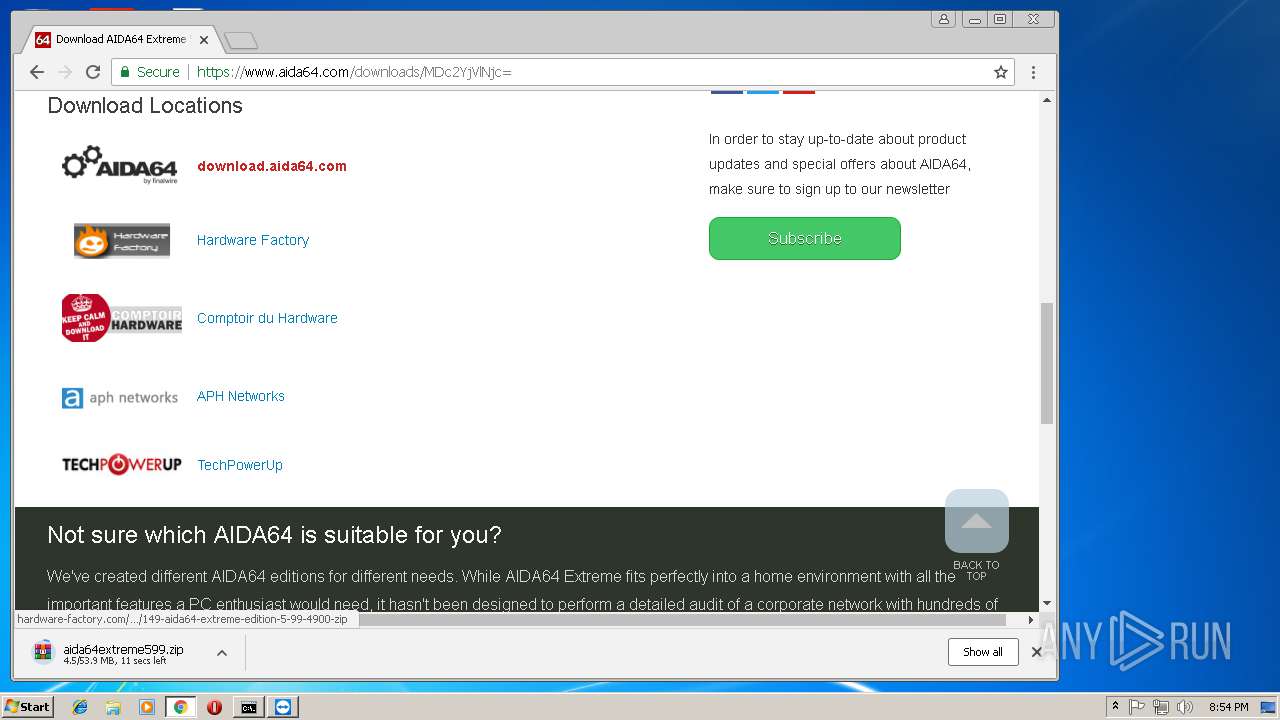
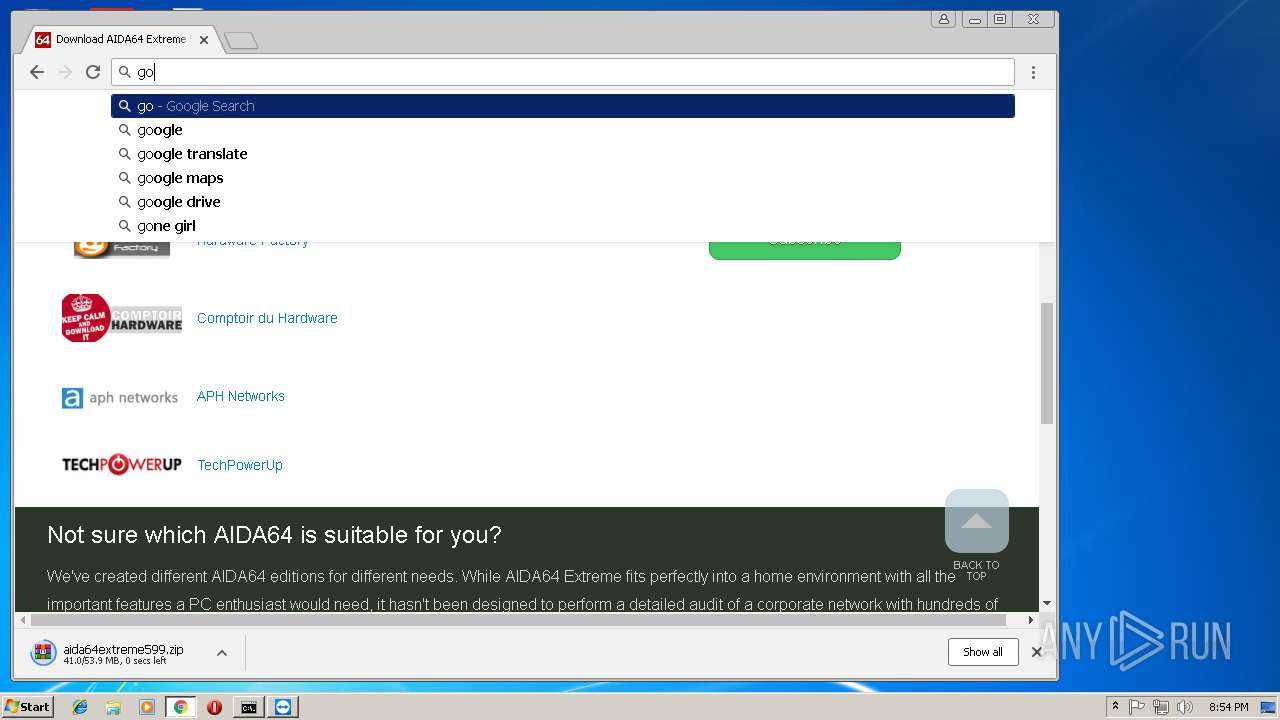
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
124
DNS requests
76
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
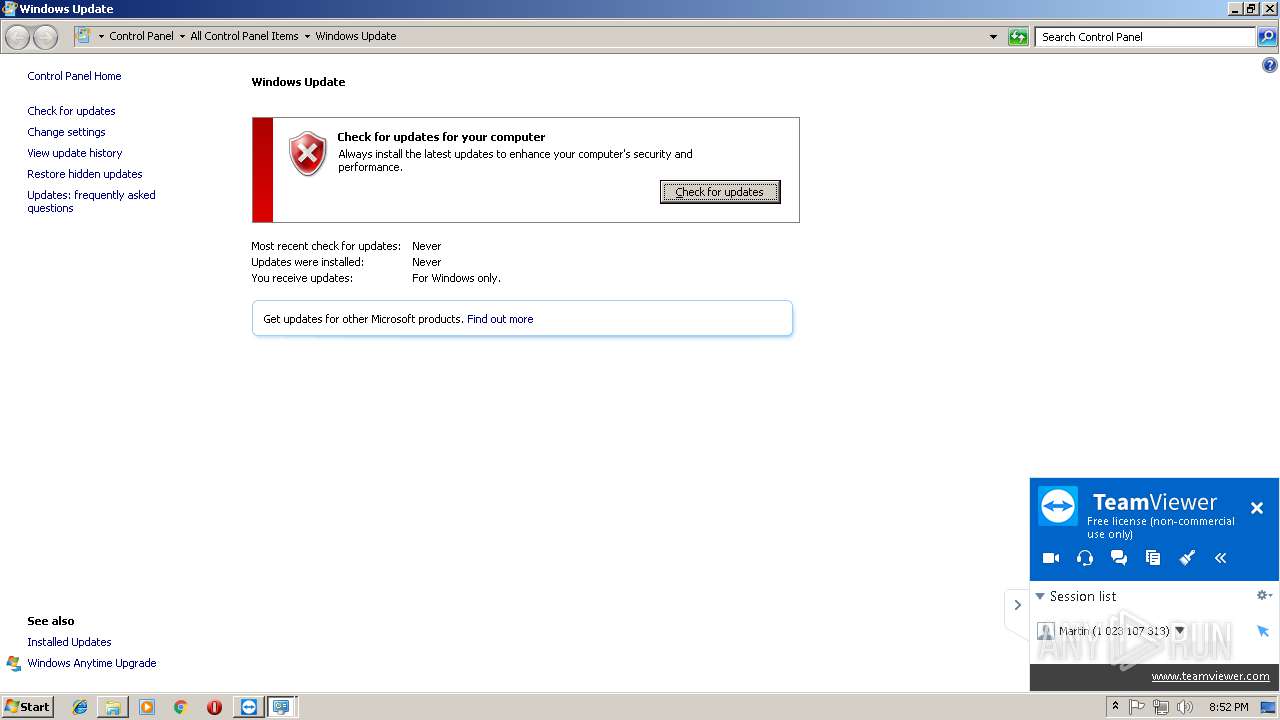
— | — | HEAD | 200 | 93.184.221.240:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?1901312052 | US | — | — | whitelisted |
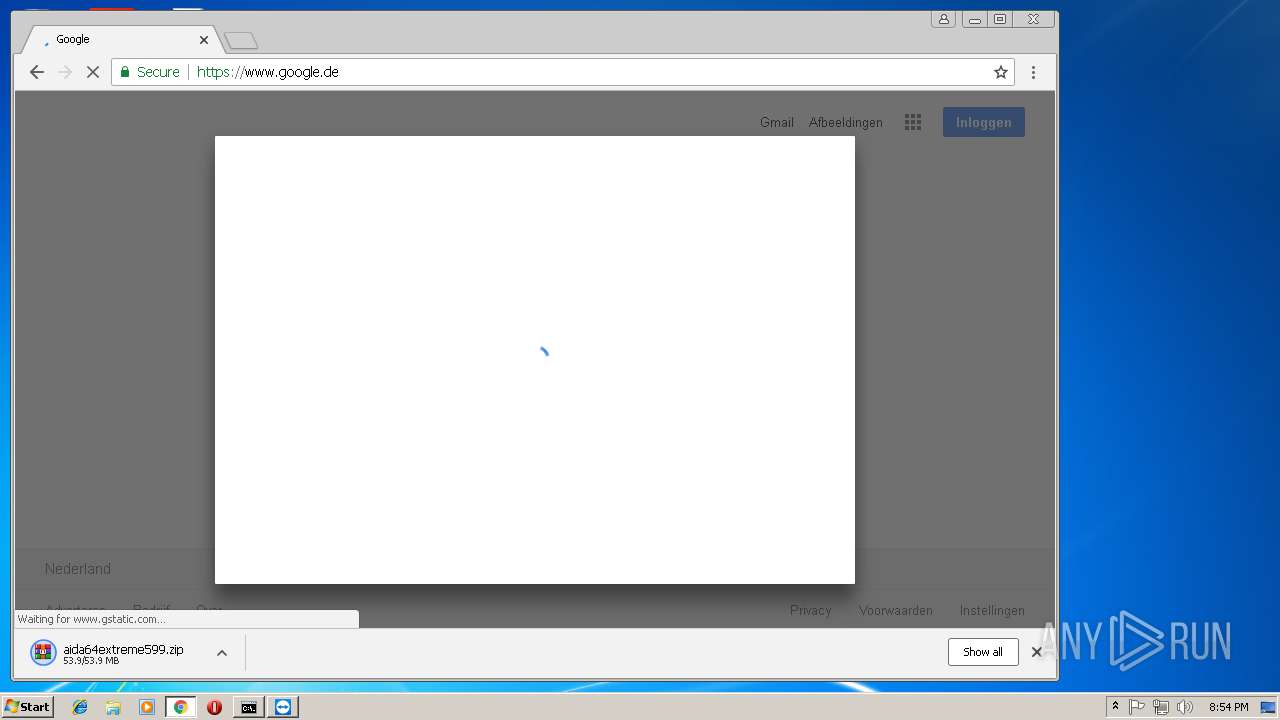
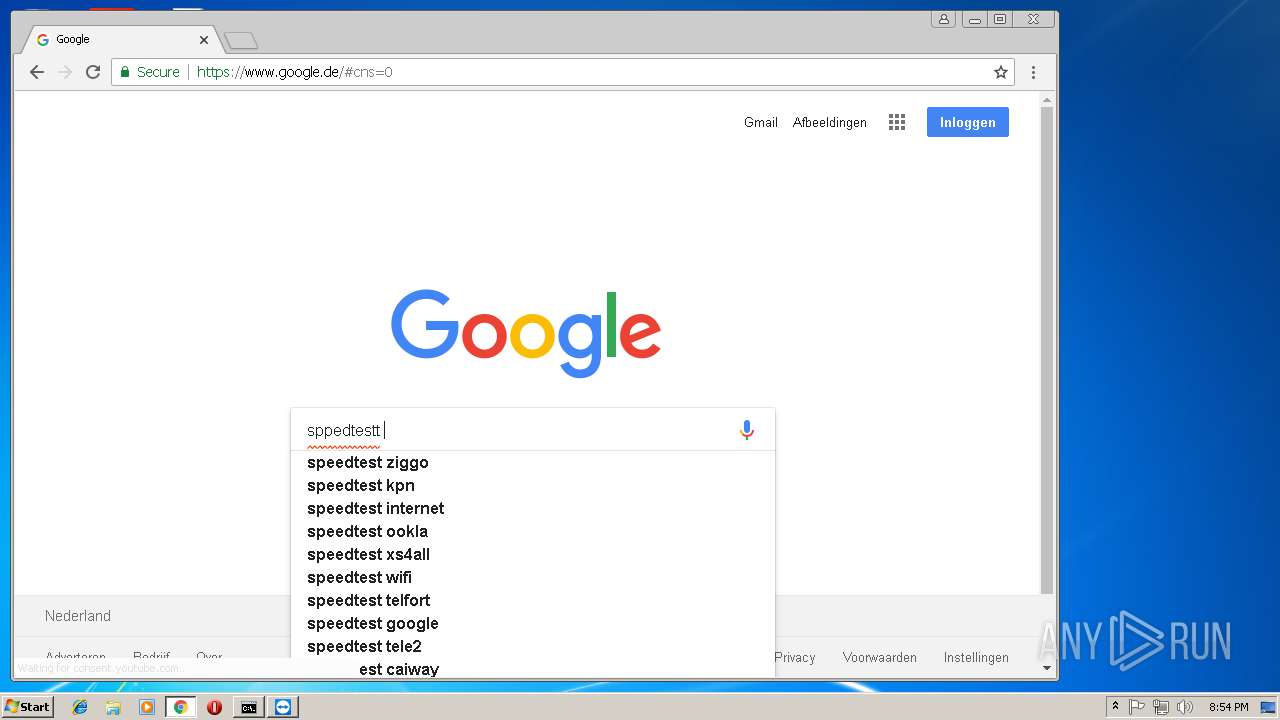
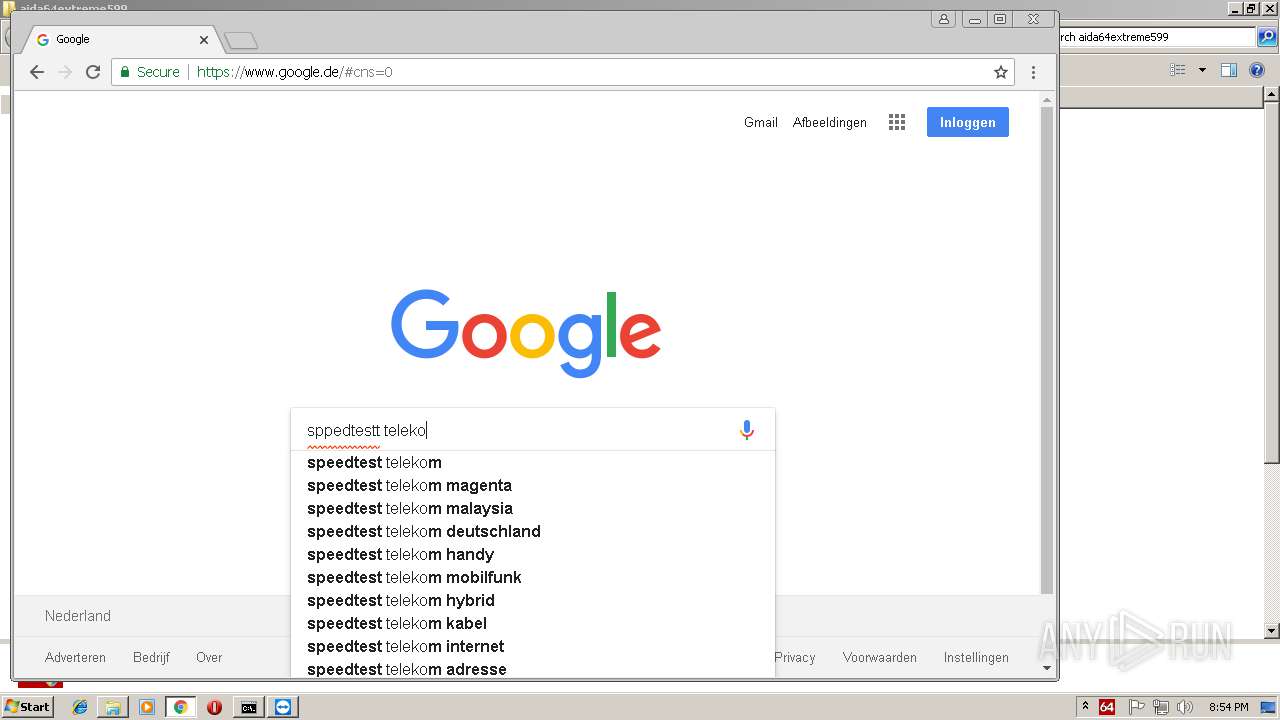
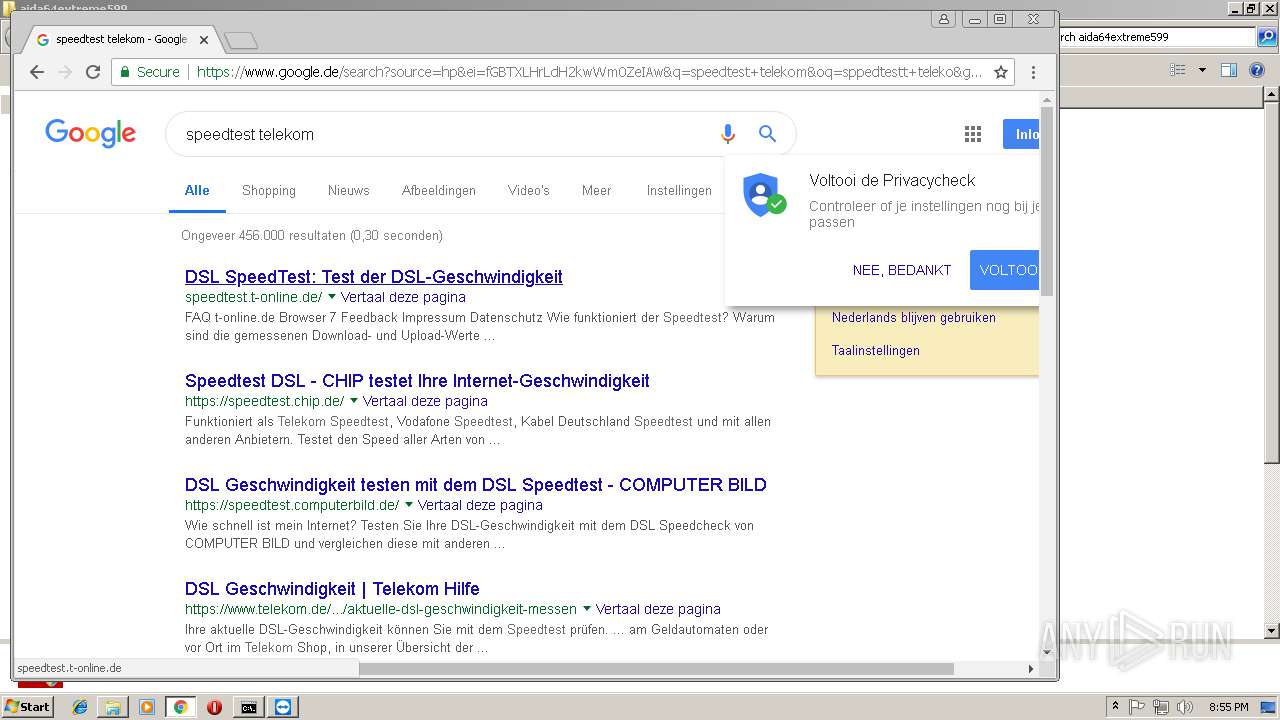
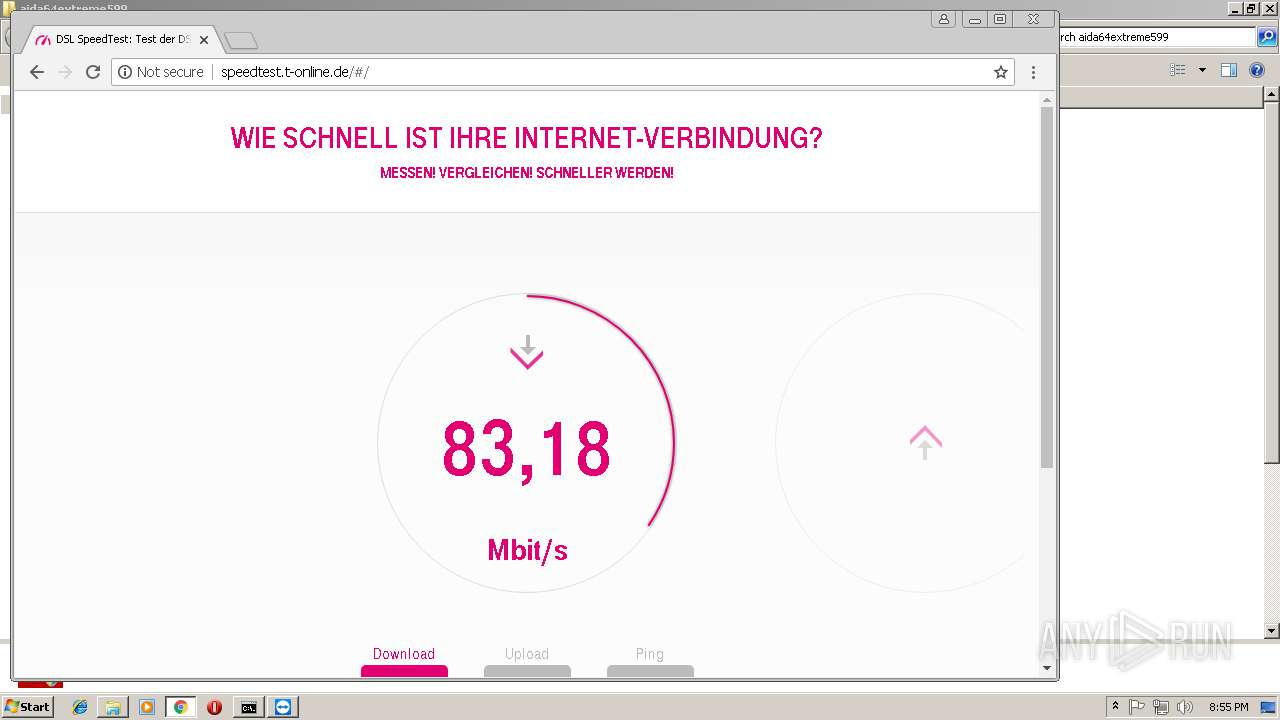
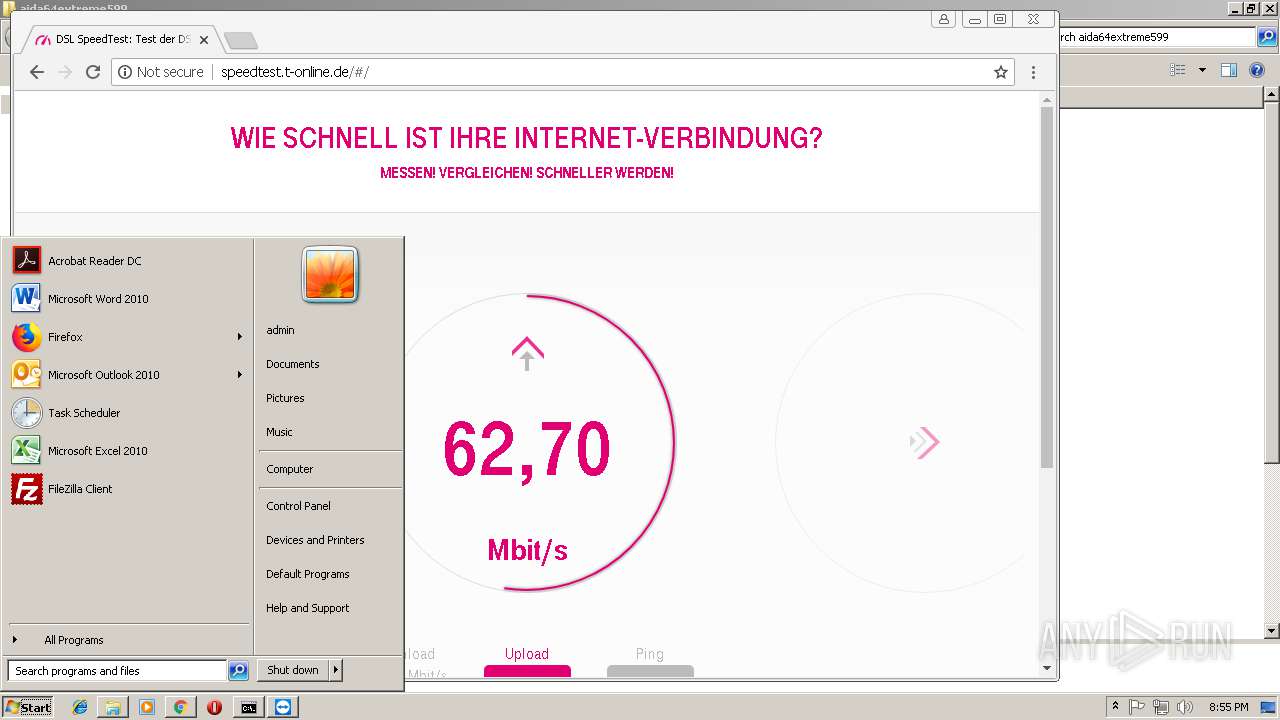
4092 | chrome.exe | GET | 302 | 91.215.103.65:80 | http://de.ioam.de/tx.io?st=toi&cp=speedtest&sv=in&co=kommentar&pt=CP&ps=lin&er=N22&rf=www.google.de&r2=https%3A%2F%2Fwww.google.de%2F&ur=speedtest.t-online.de&xy=1280x720x24&lo=NL%2FUtrecht&cb=0009&i2=0009618a25d85d6fc5c5360ac&ep=1571826889&vr=412&id=1q0p57&i3=nocookie&n1=2&dntt=0<=1548968117719&ev=&cs=i3t3ub&mo=1 | DE | — | — | whitelisted |
4092 | chrome.exe | GET | 200 | 91.215.103.65:80 | http://de.ioam.de/tx.io?st=toi&cp=speedtest&sv=in&co=kommentar&pt=CP&ps=lin&er=N22&rf=www.google.de&r2=https%3A%2F%2Fwww.google.de%2F&ur=speedtest.t-online.de&xy=1280x720x24&lo=NL%2FUtrecht&cb=0009&i2=0009618a25d85d6fc5c5360ac&ep=1571826889&vr=412&id=1q0p57&i3=nocookie&n1=2&dntt=0<=1548968117719&ev=&cs=i3t3ub&mo=1&sr=71 | DE | — | — | whitelisted |
— | — | HEAD | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/wsus3setup.cab?1901312052 | US | — | — | whitelisted |
— | — | GET | 200 | 13.107.4.50:80 | http://ds.download.windowsupdate.com/v11/3/windowsupdate/selfupdate/WSUS3/x86/Win7SP1/wsus3setup.cab?1901312052 | US | compressed | 32.9 Kb | whitelisted |
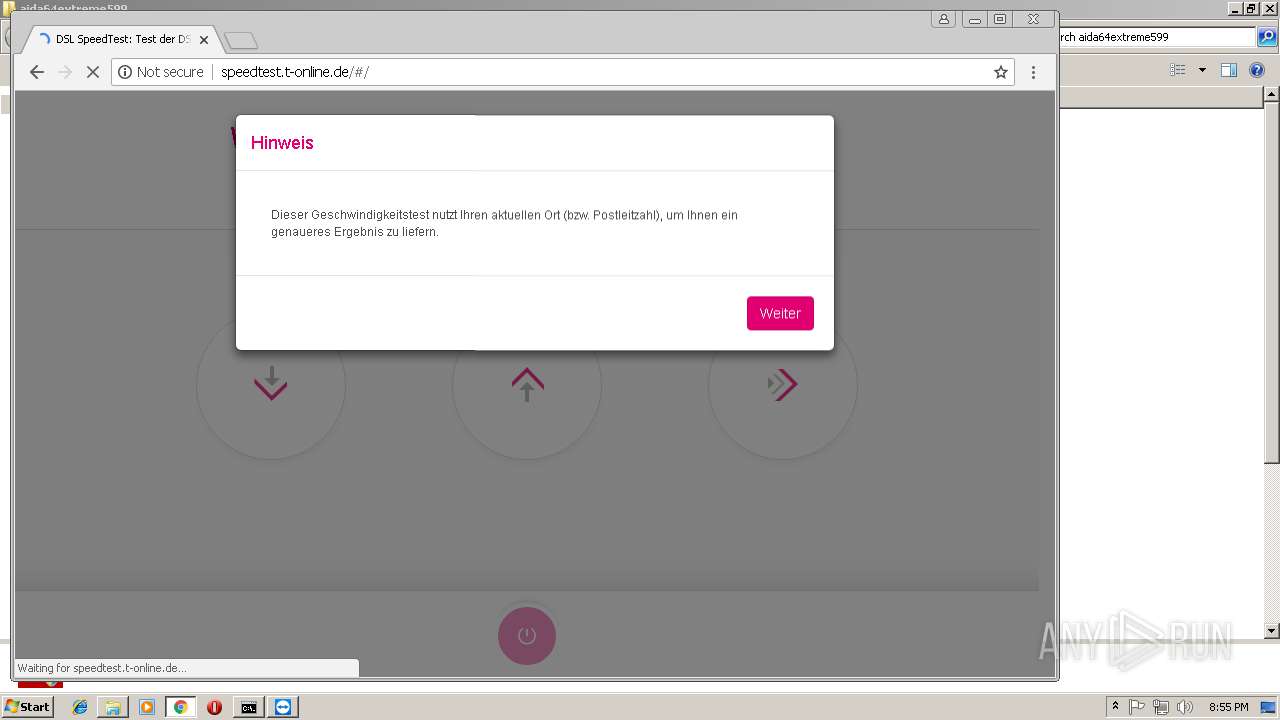
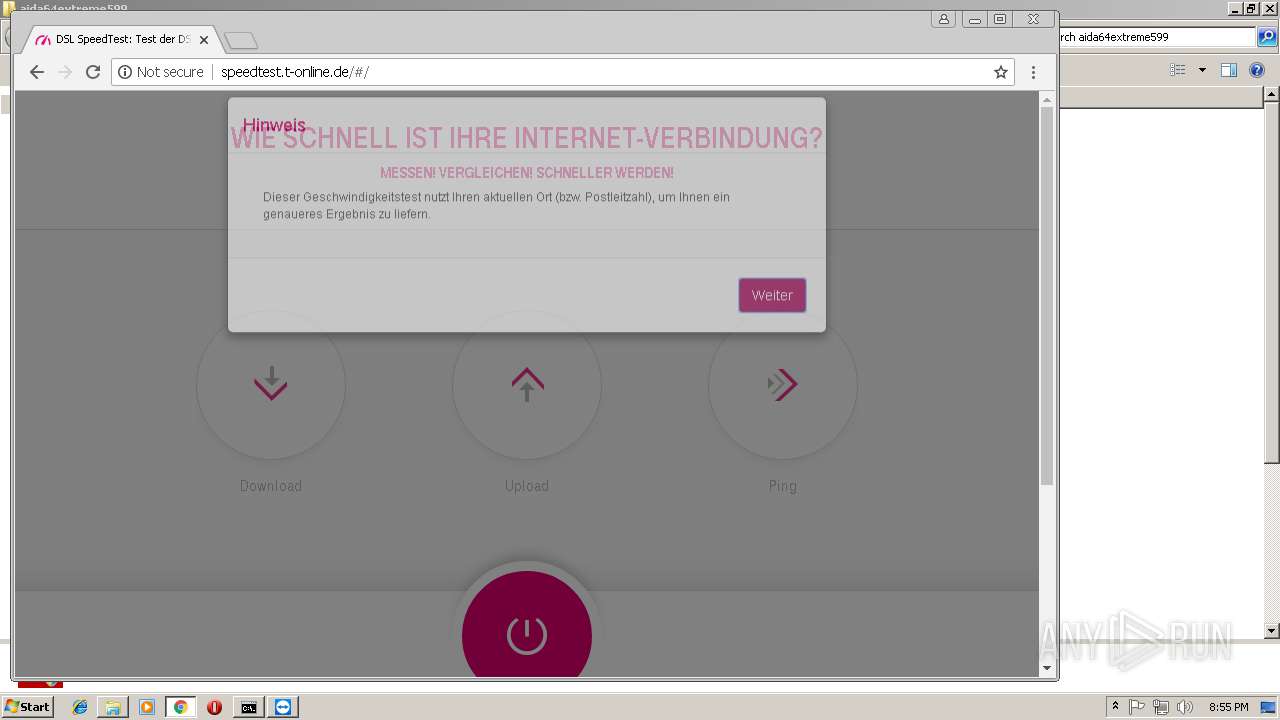
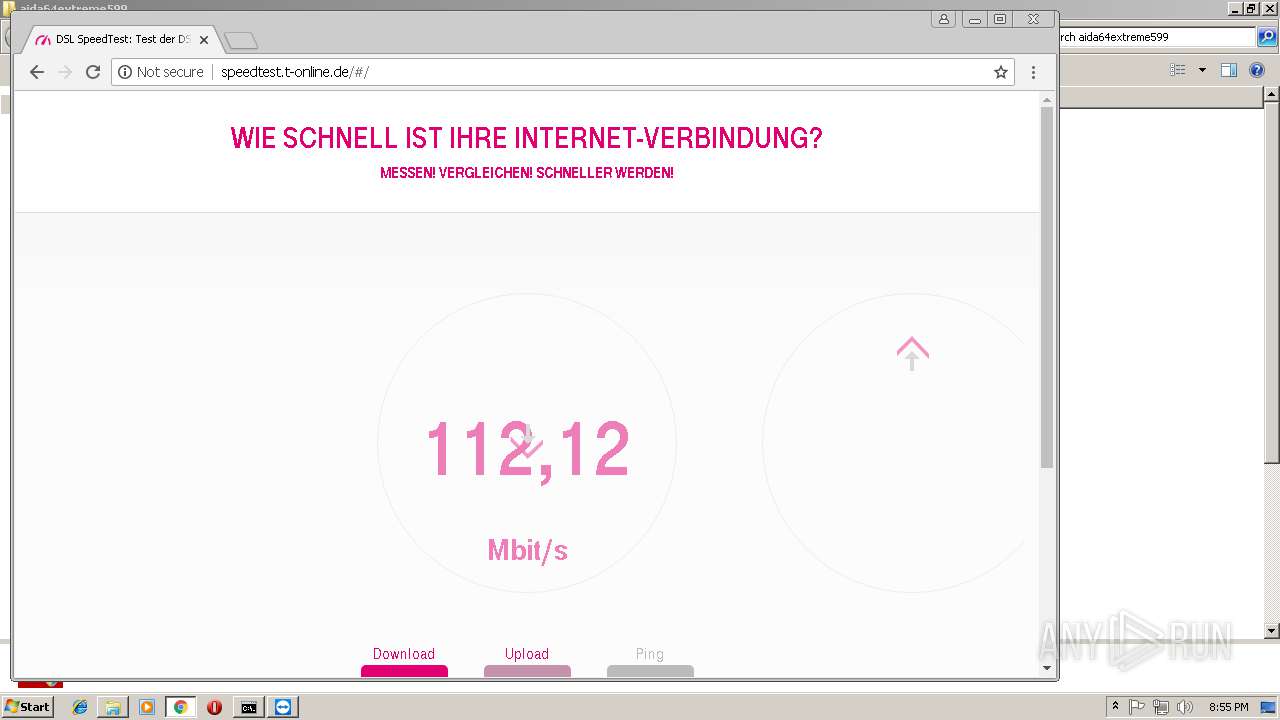
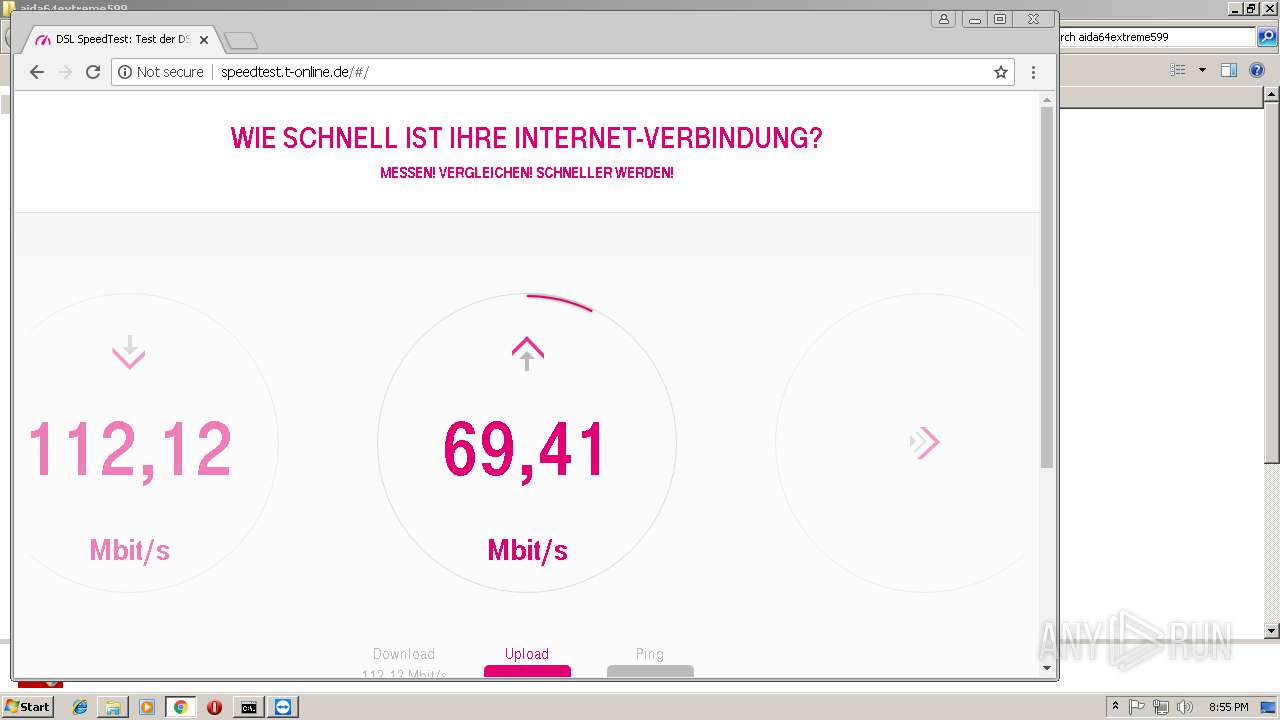
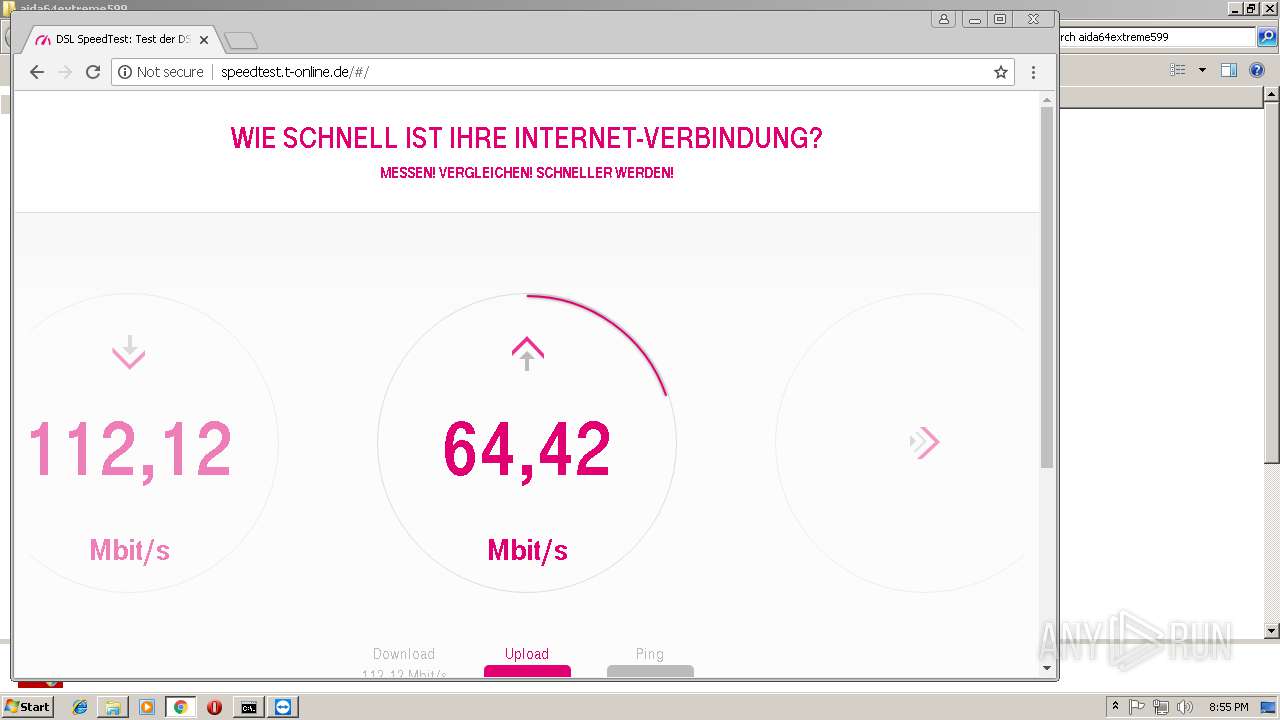
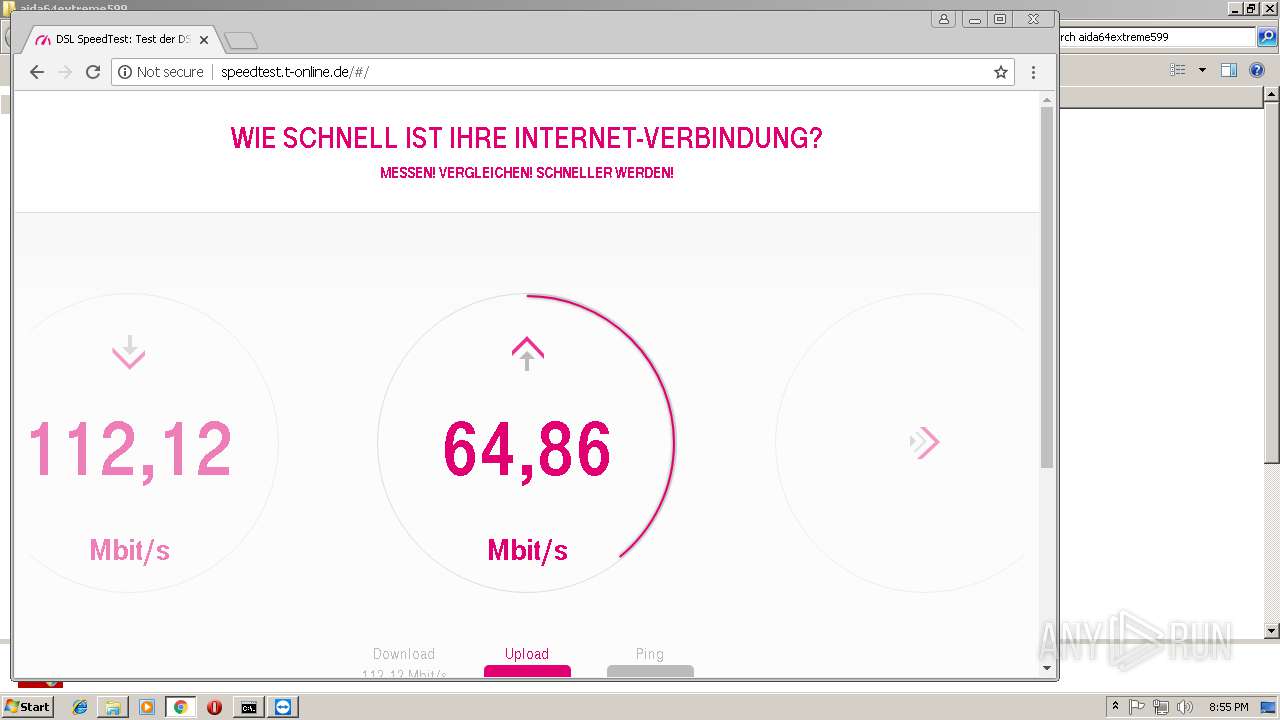
4092 | chrome.exe | GET | 200 | 191.233.93.31:80 | http://speedtest.t-online.de/Scripts/AppJsBundle.min.js | NL | text | 178 Kb | unknown |
4092 | chrome.exe | GET | 200 | 191.233.93.31:80 | http://speedtest.t-online.de/Content/AppCssBundle.min.css | NL | text | 23.7 Kb | unknown |
4092 | chrome.exe | GET | 200 | 191.233.93.31:80 | http://speedtest.t-online.de/ | NL | html | 5.66 Kb | unknown |
4092 | chrome.exe | GET | 200 | 191.233.93.31:80 | http://speedtest.t-online.de/app/AppSpeedtestJsBundle.min.js | NL | text | 11.7 Kb | unknown |
4092 | chrome.exe | GET | 200 | 193.46.63.75:80 | http://irqs.ioam.de/identitystatus?offerIdentifier=toi&siteIdentifier=speedtest&sampleType=in&pixelType=CP&isFadeoutFlash=true&isFadeoutFrame=true&isFadeoutForm=true&positionTop=10&positionLeft=100&zIndex=1100000&c=0.15199299167663116 | DE | text | 25 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3864 | TeamViewer.exe | 213.227.168.145:5938 | DE-FRA-ANX-R014.teamviewer.com | ANEXIA Internetdienstleistungs GmbH | AT | suspicious |
— | — | 213.227.162.126:5938 | udpping.teamviewer.com | ANEXIA Internetdienstleistungs GmbH | FR | suspicious |
— | — | 188.172.246.190:5938 | udpping.teamviewer.com | ANEXIA Internetdienstleistungs GmbH | AT | suspicious |
— | — | 87.165.241.115:49435 | — | Deutsche Telekom AG | DE | unknown |
— | — | 13.64.25.102:443 | www.update.microsoft.com | Microsoft Corporation | US | malicious |
— | — | 93.184.221.240:80 | download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 13.107.4.50:80 | ds.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
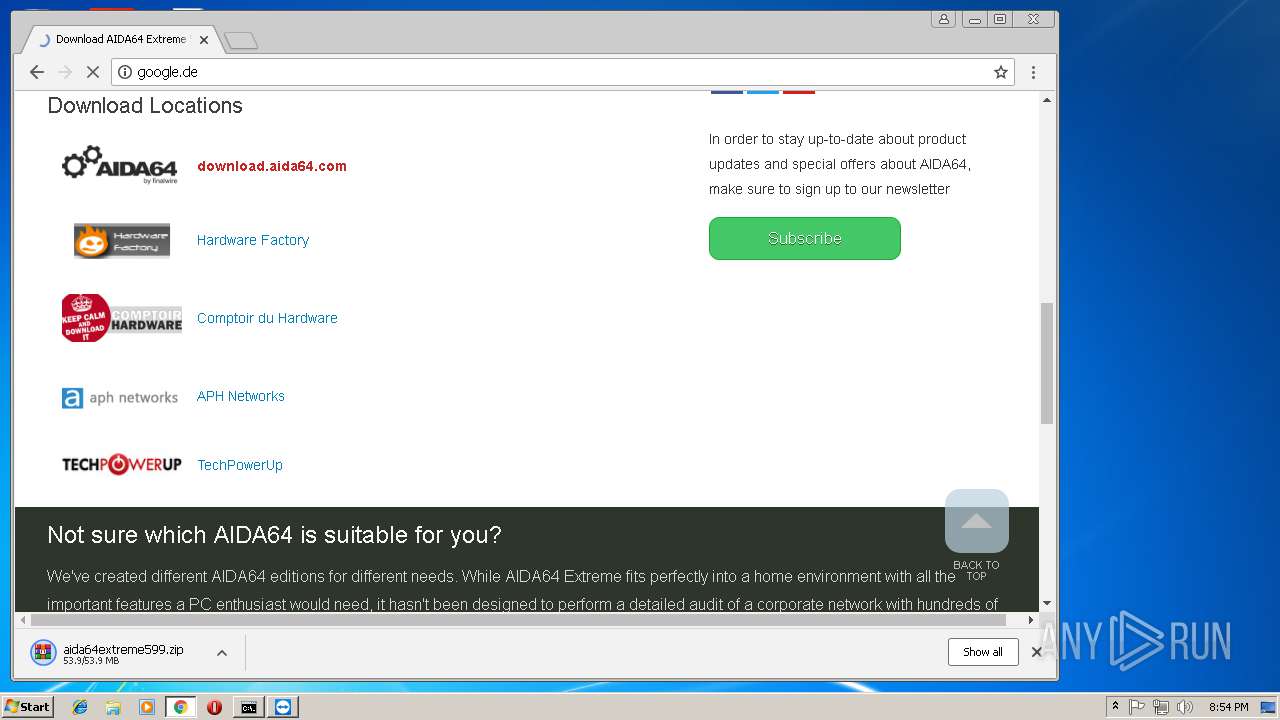
4092 | chrome.exe | 172.217.22.3:443 | www.google.de | Google Inc. | US | whitelisted |
4092 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4092 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
router3.teamviewer.com |
| suspicious |
client.teamviewer.com |
| shared |
DE-FRA-ANX-R014.teamviewer.com |
| suspicious |
udpping.teamviewer.com |
| suspicious |
download.windowsupdate.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |
ds.download.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3864 | TeamViewer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer connection |
3864 | TeamViewer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer negotiation |
3864 | TeamViewer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer connection |
3864 | TeamViewer.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TeamViewer negotiation |