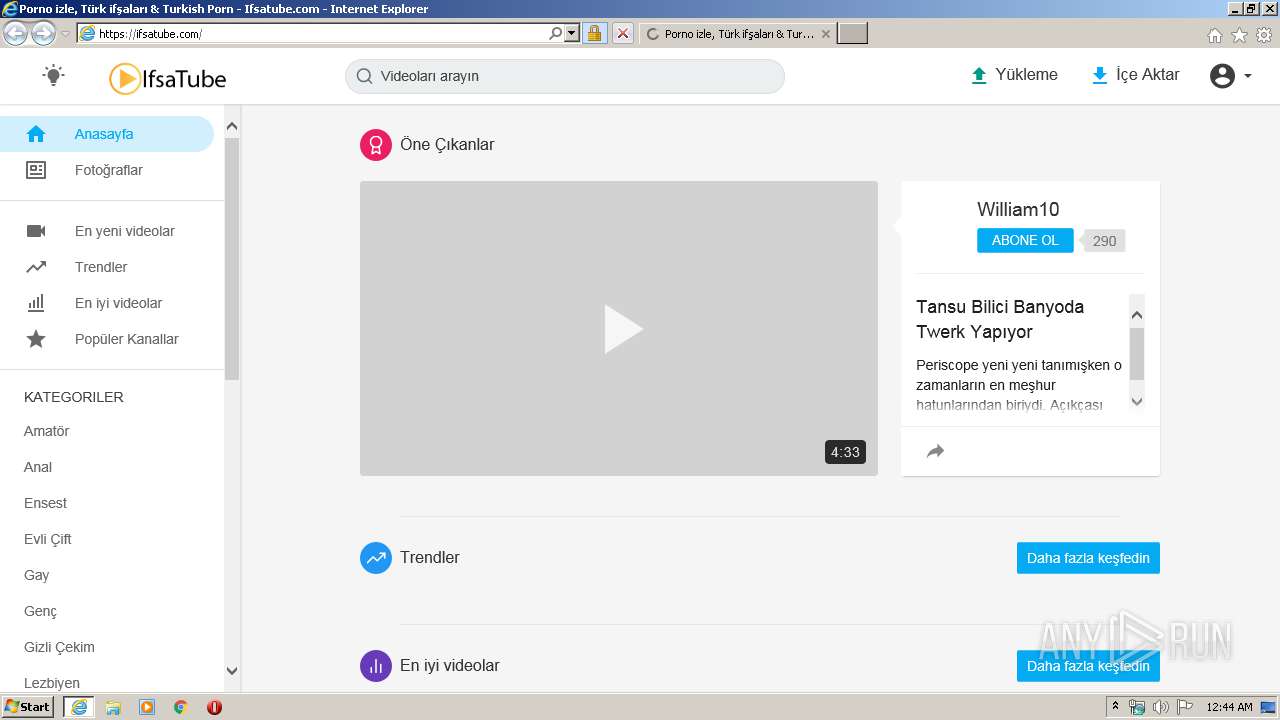
| URL: | https://ifsatube.com/ |
| Full analysis: | https://app.any.run/tasks/a7b3bfd9-7780-4694-a2ae-82fcced35abe |
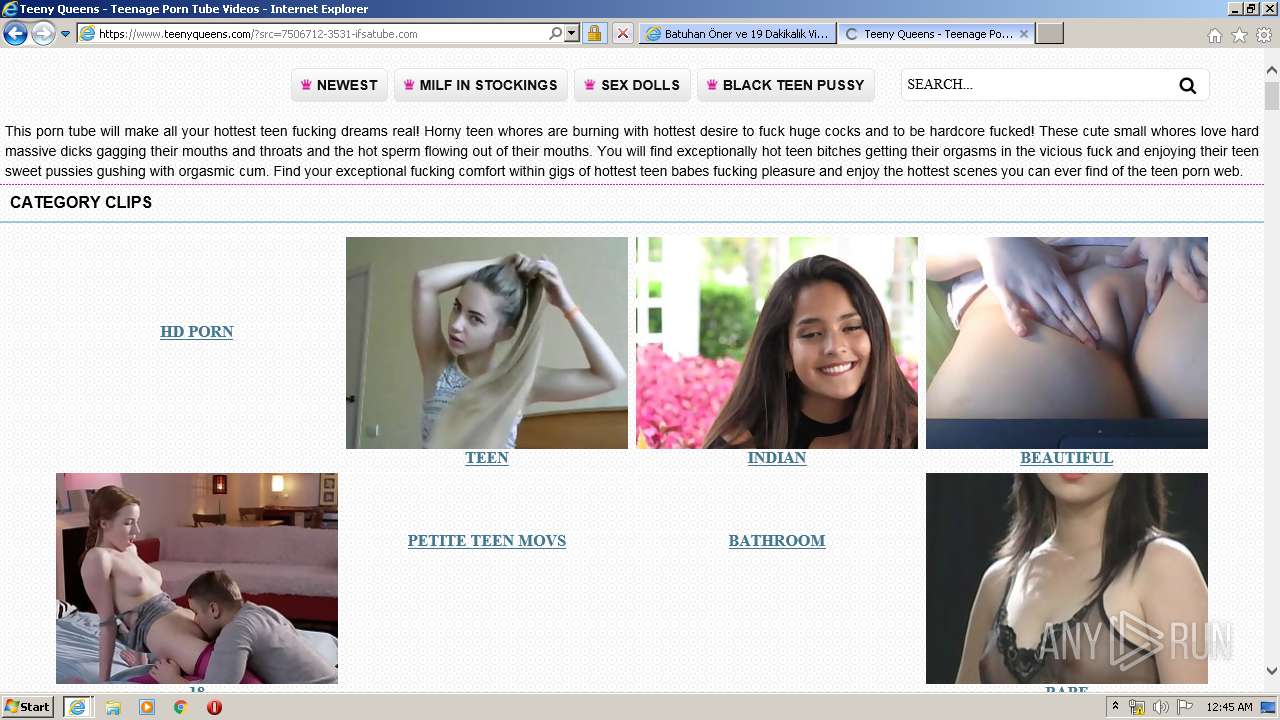
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 23:44:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 69418D13F46D41A991E288D72EE8DA5D |
| SHA1: | 5F0DD4814FB1B2E5D97F6544E796510A2A4A5AD6 |
| SHA256: | 66E71855A88D3D56367170E3BD944AE79EEDCAB82EA979F0EE2B91DA82A6C219 |
| SSDEEP: | 3:N8T4QBKn:2x8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2720)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1248)
Reads Internet Cache Settings
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 3452)
Reads internet explorer settings
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 3452)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2720)
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 3452)
Application launched itself
- iexplore.exe (PID: 1248)
Reads settings of System Certificates
- iexplore.exe (PID: 3452)
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 1248)
Changes settings of System certificates
- iexplore.exe (PID: 1248)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Program Files\Internet Explorer\iexplore.exe" https://ifsatube.com/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1248 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2720 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1248 CREDAT:595215 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 895
Read events
1 546
Write events
3 632
Delete events
1 717
Modification events
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 839838174 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30814556 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1248) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
191
Text files
457
Unknown types
98
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8A2D.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8A2E.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VZC0S2YA.txt | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NGK2LIYY.txt | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:EECA7D7931E81161CC2B08494D6E9812 | SHA256:A9A830E7E5D7B8D15B418D22CDA4EA3975C2DE2B83FFEC712438F6608F2E8562 | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C1B3CC7FF1466C71640A202F8258105B_D9BA2FE4F5BA0CF50D457802CD948C4B | der | |
MD5:68C2CCABEF4632B18C840F4B50E065BE | SHA256:29D6723D6B44DC423CA4A8392432F7D0314663C6EE4F0AA89E1ED778A998CC3F | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C1B3CC7FF1466C71640A202F8258105B_D9BA2FE4F5BA0CF50D457802CD948C4B | binary | |
MD5:BA74B0DFFF058854B85B3F7F32222E3B | SHA256:08C2452EA04BA36EAE46ECA2E10D36DFD4C330376B62F8818AB958F11DF3F515 | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:DB0FEC3AA35B2F66AF15F2EF2DA844B2 | SHA256:CFB308141FB90D994F7E670F318B79016FBC673DCBF70AC476E5C9BAAAC66F2F | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VW8R3KPN.txt | text | |
MD5:BF20283BAEC2C5FF22A0E488A6076EC4 | SHA256:DCAB082CB7BB8C430C35B87935AF04F26C7C95C5631A8C26425E5B866F41CF94 | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\8RFTWVE4.htm | html | |
MD5:F8D8A286BD507D09E857D9539872CD5E | SHA256:3FE4F64E3525133ED128E366F45DD90DD378A3BFDCB0F60858E8005A3363327A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
114
TCP/UDP connections
215
DNS requests
76
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2160 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2160 | iexplore.exe | GET | 304 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2160 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2160 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | iexplore.exe | 104.27.173.40:443 | — | Cloudflare Inc | US | unknown |
2160 | iexplore.exe | 205.185.216.42:443 | a.exosrv.com | Highwinds Network Group, Inc. | US | whitelisted |
2160 | iexplore.exe | 209.197.3.15:443 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 209.197.3.15:443 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2160 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2160 | iexplore.exe | 185.199.111.153:443 | gitcdn.github.io | GitHub, Inc. | NL | shared |
2160 | iexplore.exe | 104.16.87.20:443 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
— | — | 185.199.111.153:443 | gitcdn.github.io | GitHub, Inc. | NL | shared |
2160 | iexplore.exe | 151.101.14.167:443 | player.twitch.tv | Fastly | US | suspicious |
2160 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ifsatube.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
halleyperson.pro |
| suspicious |
api.clickaine.com |
| suspicious |
a.exosrv.com |
| suspicious |
netdna.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
gitcdn.github.io |
| shared |
cdn.jsdelivr.net |
| whitelisted |
player.twitch.tv |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3452 | iexplore.exe | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |