| File name: | Windows-KB890830-x64-V5.129.exe |
| Full analysis: | https://app.any.run/tasks/83c96288-bce4-4da4-bdd5-1e07150addfb |
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2024, 01:01:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | BE658348A40C5099ED06B9A2745393C1 |
| SHA1: | 5E096DF396E49E67CE5B11054D3162BDE364254F |
| SHA256: | 66BA9991A5D8CA3B27BEED650A98A90FF39D8294EC2ED5EBE7A2E9093E721AA9 |
| SSDEEP: | 24576:Q07XB/MVARoWc5RWrNtPpUMM/NyQVtkXnR6SgkO1q:Q07RkVARoWc5RWrNtPpUMM/NyQVGXngw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
Reads the date of Windows installation
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
Executing commands from a ".bat" file
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
Executable content was dropped or overwritten
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
- cmd.exe (PID: 6256)
- amibhhuu.sef.exe (PID: 6692)
Process drops legitimate windows executable
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
Starts CMD.EXE for commands execution
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
- amibhhuu.sef.exe (PID: 6692)
The executable file from the user directory is run by the CMD process
- mbr.exe (PID: 5616)
- amibhhuu.sef.exe (PID: 6692)
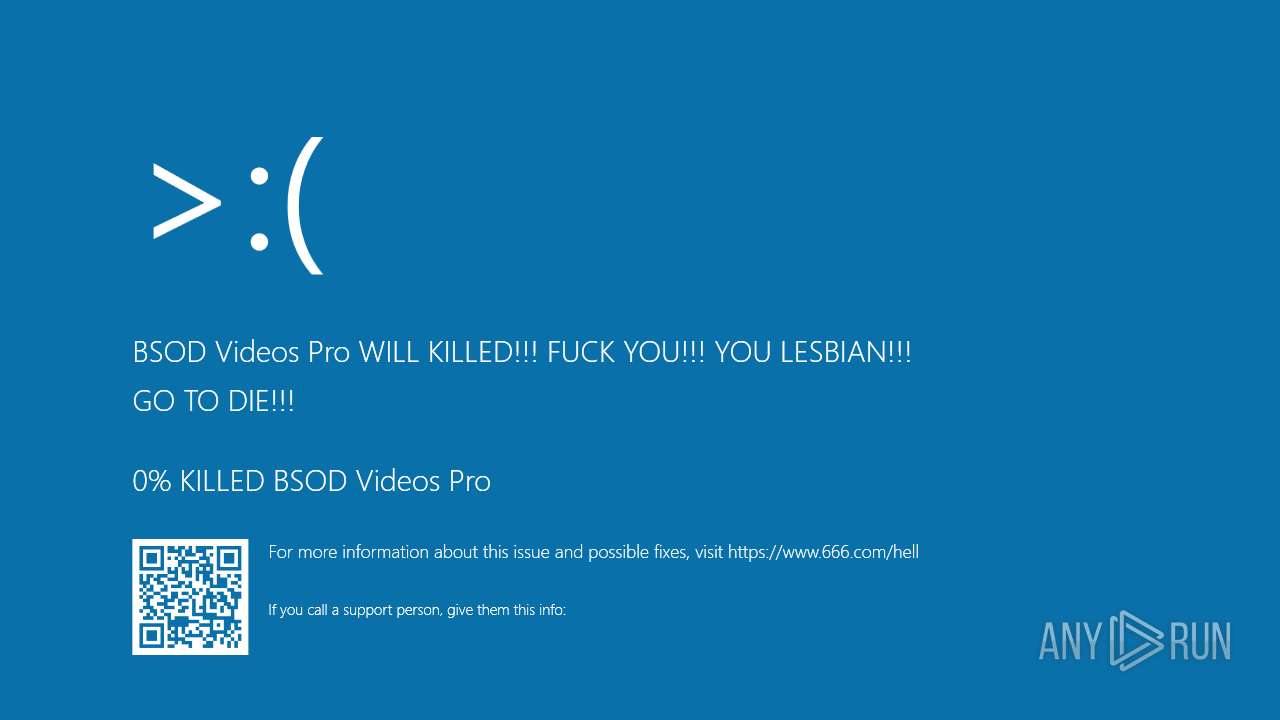
- BluescreenSimulator.exe (PID: 5912)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6256)
Starts a Microsoft application from unusual location
- amibhhuu.sef.exe (PID: 6692)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6256)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6256)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 6256)
INFO
Checks supported languages
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
- mbr.exe (PID: 5616)
- amibhhuu.sef.exe (PID: 6692)
Reads the computer name
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
Process checks computer location settings
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
The process uses the downloaded file
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
Create files in a temporary directory
- Windows-KB890830-x64-V5.129.exe (PID: 6600)
- amibhhuu.sef.exe (PID: 6692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:07:30 08:52:21+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 90624 |
| InitializedDataSize: | 545280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.129.24100.1001 |
| ProductVersionNumber: | 5.129.24100.1001 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 5.129.24100.1001 |
| ProductVersion: | 5.129.24100.1001 |
| ProductName: | Malicious Software Removal Tool |
| OriginalFileName: | mrtsrtub.exe |
| FileDescription: | Microsoft Windows Malicious Software Removal Tool (KB890830) |
| LegalCopyright: | @Microsoft Corporation. All rights reserved. |
Total processes
179
Monitored processes
49
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | timeout 10 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 824 | reg add "HKCR\exefile\shell\open\command" /ve /t REG_SZ /d rundll32.exe /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | reg add "hkcu\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v NoSMMyPictures /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | rundll32 user32, SwapMouseButton | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | reg add "hkcu\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v NoDrives /t REG_DWORD /d 67108863 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\Temp\Windows-KB890830-x64-V5.129.exe" | C:\Users\admin\AppData\Local\Temp\Windows-KB890830-x64-V5.129.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3276 | reg add "hkcu\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v NoClose /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3604 | reg add "hklm\Software\Microsoft\Windows\CurrentVersion\run" /v SwapNT /t REG_SZ /d rundll32 user32, SwapMouseButton /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3824 | reg add "HKCU\Software\Policies\Microsoft\Internet Explorer\Restrictions" /v "NoNavButtons" /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 679
Read events
2 635
Write events
44
Delete events
0
Modification events
| (PID) Process: | (6044) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | disabletaskmgr |
Value: 1 | |||
| (PID) Process: | (6692) amibhhuu.sef.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (6260) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (6260) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | write | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (6260) SearchApp.exe | Key: | \REGISTRY\A\{a1cf41e4-e45d-26dc-58c4-7e6168ff206c}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_USEREMAIL |
Value: 0000BB9D07E4D428DB01 | |||
| (PID) Process: | (6260) SearchApp.exe | Key: | \REGISTRY\A\{a1cf41e4-e45d-26dc-58c4-7e6168ff206c}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPETEXT |
Value: 0000701408E4D428DB01 | |||
| (PID) Process: | (6260) SearchApp.exe | Key: | \REGISTRY\A\{a1cf41e4-e45d-26dc-58c4-7e6168ff206c}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 0000701408E4D428DB01 | |||
| (PID) Process: | (6260) SearchApp.exe | Key: | \REGISTRY\A\{a1cf41e4-e45d-26dc-58c4-7e6168ff206c}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 4E006F006E0065000000701408E4D428DB01 | |||
| (PID) Process: | (7128) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | ForceActiveDesktopOn |
Value: 0 | |||
| (PID) Process: | (7128) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoActiveDesktop |
Value: 1 | |||
Executable files
5
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5616 | mbr.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 6600 | Windows-KB890830-x64-V5.129.exe | C:\Users\admin\AppData\Local\Temp\1.reg | text | |
MD5:F976E9E0FABC4ED83D70F5841D82E2C9 | SHA256:4A9C129CF86CA4D0558CA606DDDDC8FA121E1CD88B4D032096E66C566C8CA6D2 | |||
| 6600 | Windows-KB890830-x64-V5.129.exe | C:\Users\admin\AppData\Local\Temp\h.exe | executable | |
MD5:5BF2570C3FFAB02DA3CE5F2E42A852E8 | SHA256:453867B795FE8360B1BAB43A818CD58F98384987C9FFDBEBD1DD64418960CAF8 | |||
| 6692 | amibhhuu.sef.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BluescreenSimulator.exe | executable | |
MD5:E021AD0649B6E06642965239A0F1DFFB | SHA256:A872AB63FD3E70627D7BF28A74045A5FCA407D79A950AC1FDBCECD6B7672469F | |||
| 6600 | Windows-KB890830-x64-V5.129.exe | C:\Users\admin\AppData\Local\Temp\amibhhuu.sef.exe | executable | |
MD5:6475963506E27331BED6B37FB360D69E | SHA256:F7DFA08C8DF028737057779A1545CC705D5B228CDFE5F929C22502804D4B6C1D | |||
| 6256 | cmd.exe | C:\Windows\winnit32.exe | executable | |
MD5:5BF2570C3FFAB02DA3CE5F2E42A852E8 | SHA256:453867B795FE8360B1BAB43A818CD58F98384987C9FFDBEBD1DD64418960CAF8 | |||
| 6600 | Windows-KB890830-x64-V5.129.exe | C:\Users\admin\AppData\Local\Temp\B5BC.tmp\B5BD.tmp\B5BE.bat | text | |
MD5:8A00D153AE87C972291F784F402B77BD | SHA256:0D927334FF338C6E3B7C271DDA846E2CD50BC428AD1D9109DEA66DCCAD84D544 | |||
| 6600 | Windows-KB890830-x64-V5.129.exe | C:\Users\admin\AppData\Local\Temp\mbr.exe | executable | |
MD5:09A02FF6A69E7ED4E7A6FA77593C101E | SHA256:13919BD650176D8A67255B2676432BC099E29CEDF2779F63E42A734D4C971FC7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
38
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4700 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5048 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5016 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5016 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2776 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2776 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
780 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |