| File name: | PowerISO7-x64.exe |
| Full analysis: | https://app.any.run/tasks/00b33034-7f7c-4e2e-82d1-1929068c1cd9 |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2019, 16:37:10 |
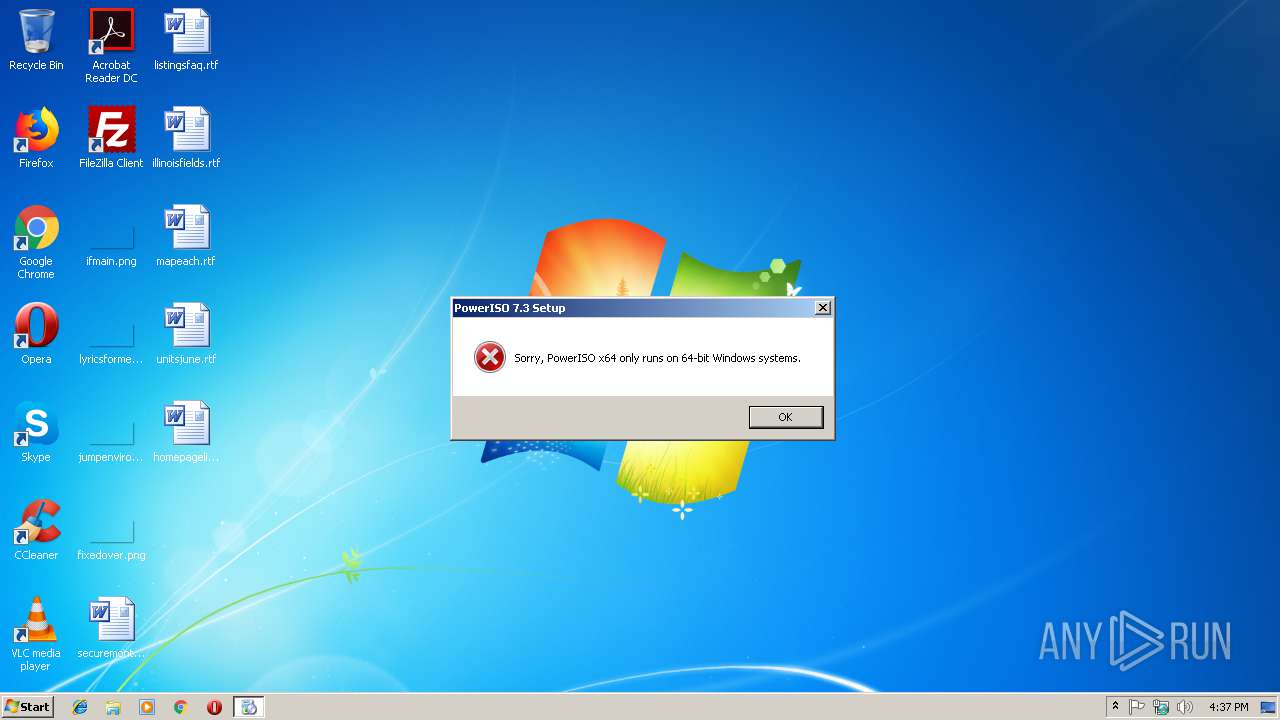
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E90648E4DB19B308949F2BA2685DF546 |
| SHA1: | 8F703F92D1643CA23FED8684AABCF98B372623C9 |
| SHA256: | 66B505BA23E857D0166EE18A2B0090097EE171CC5C10EFB52B6E9B3B0CFCAEE9 |
| SSDEEP: | 98304:2axKYYQQRG7HGygwXZpIu6FsfxjnHBUXOkhZpBgRkuUA4:2OKvLo7F3XH4sJjnhYfqkuk |
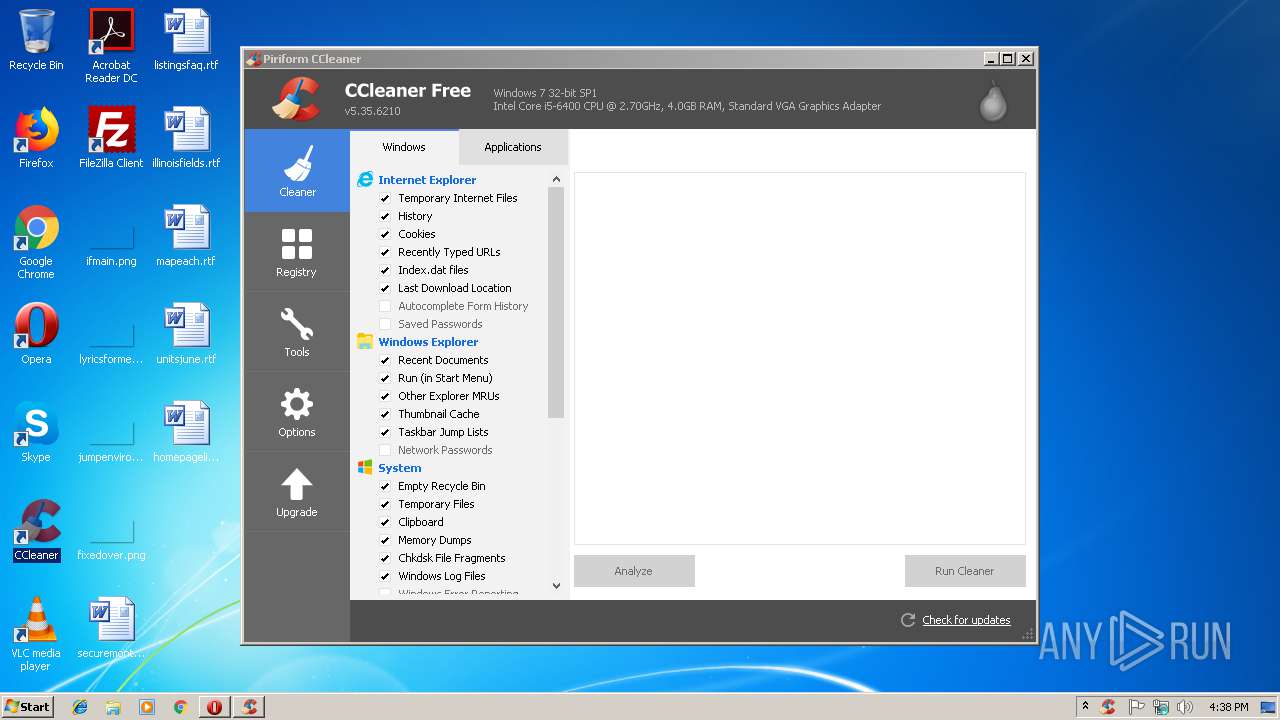
MALICIOUS
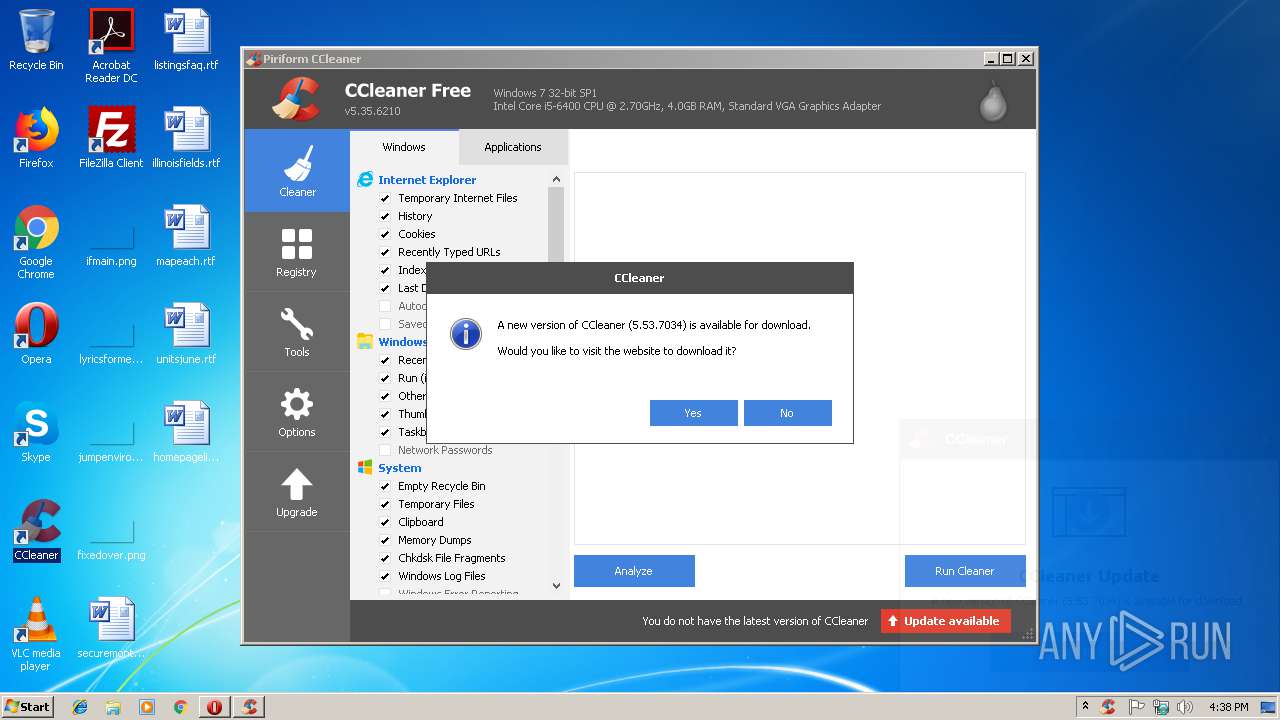
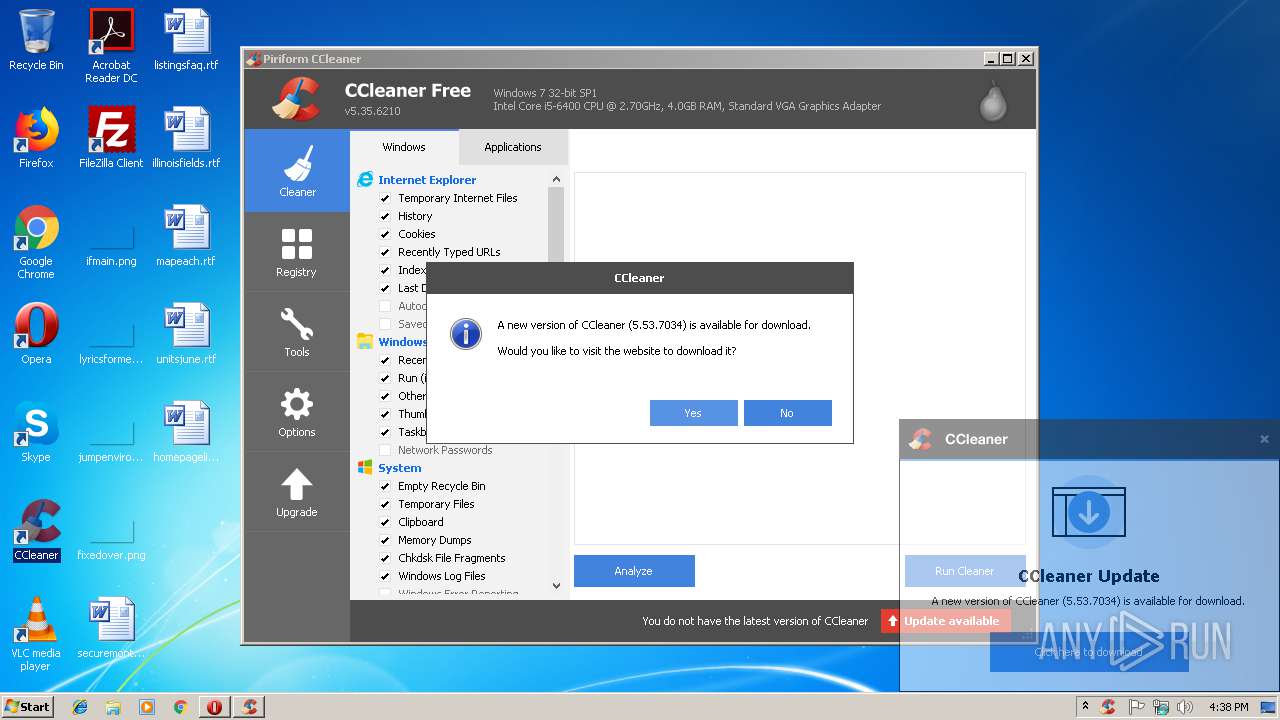
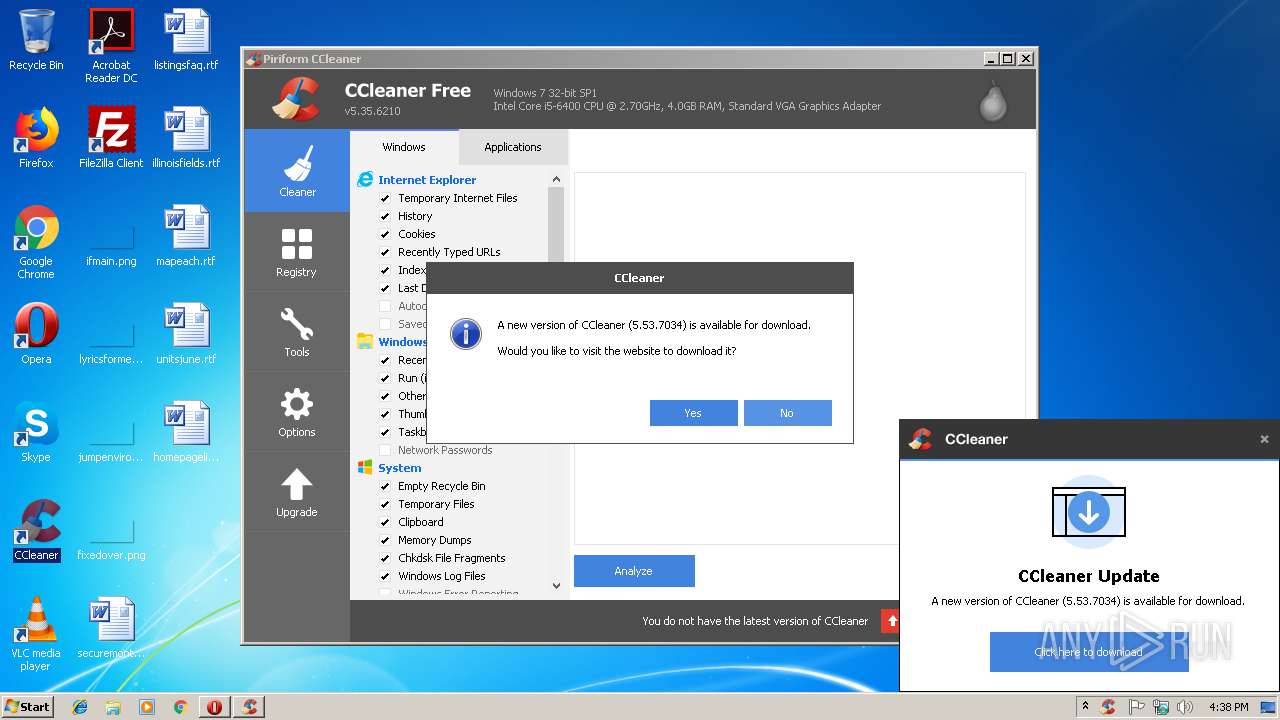
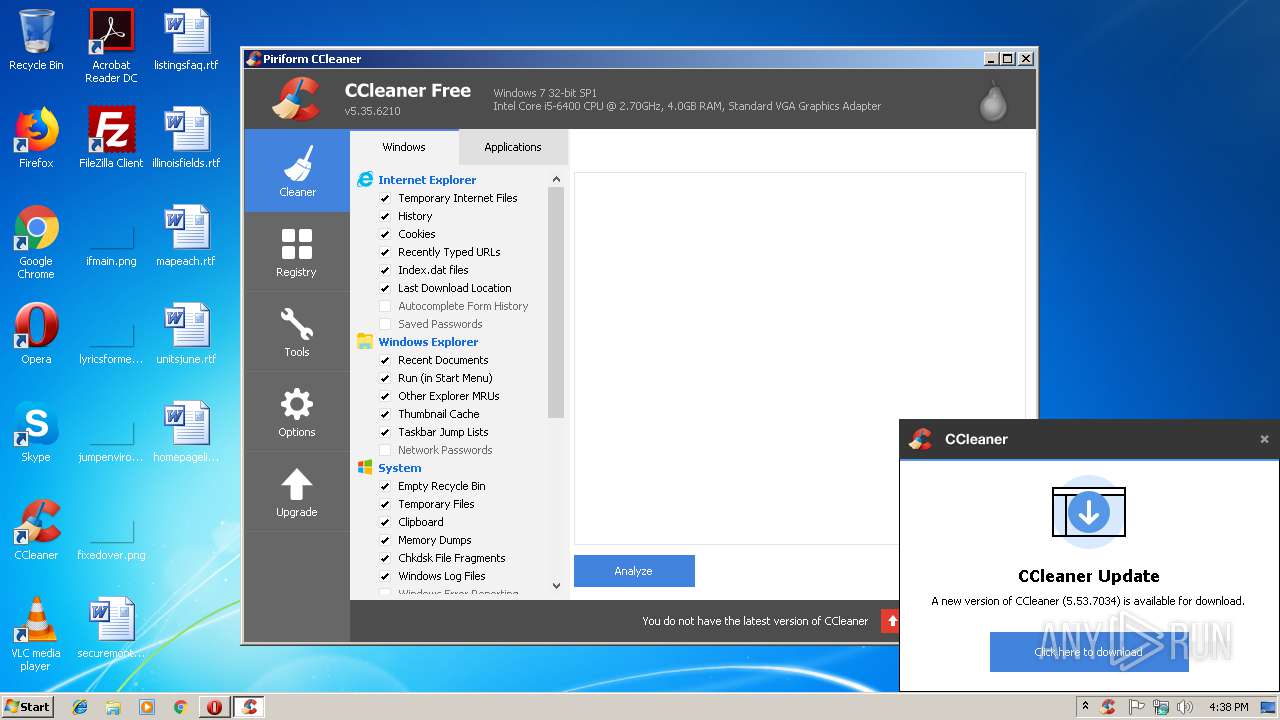
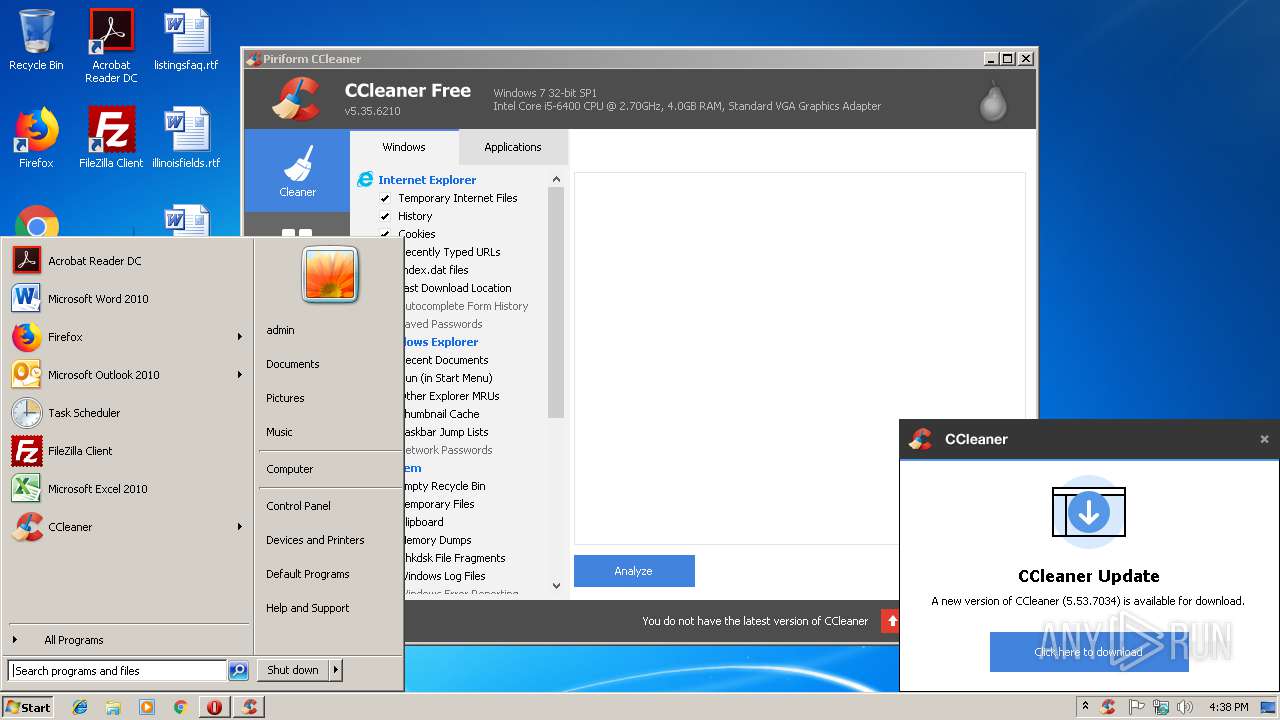
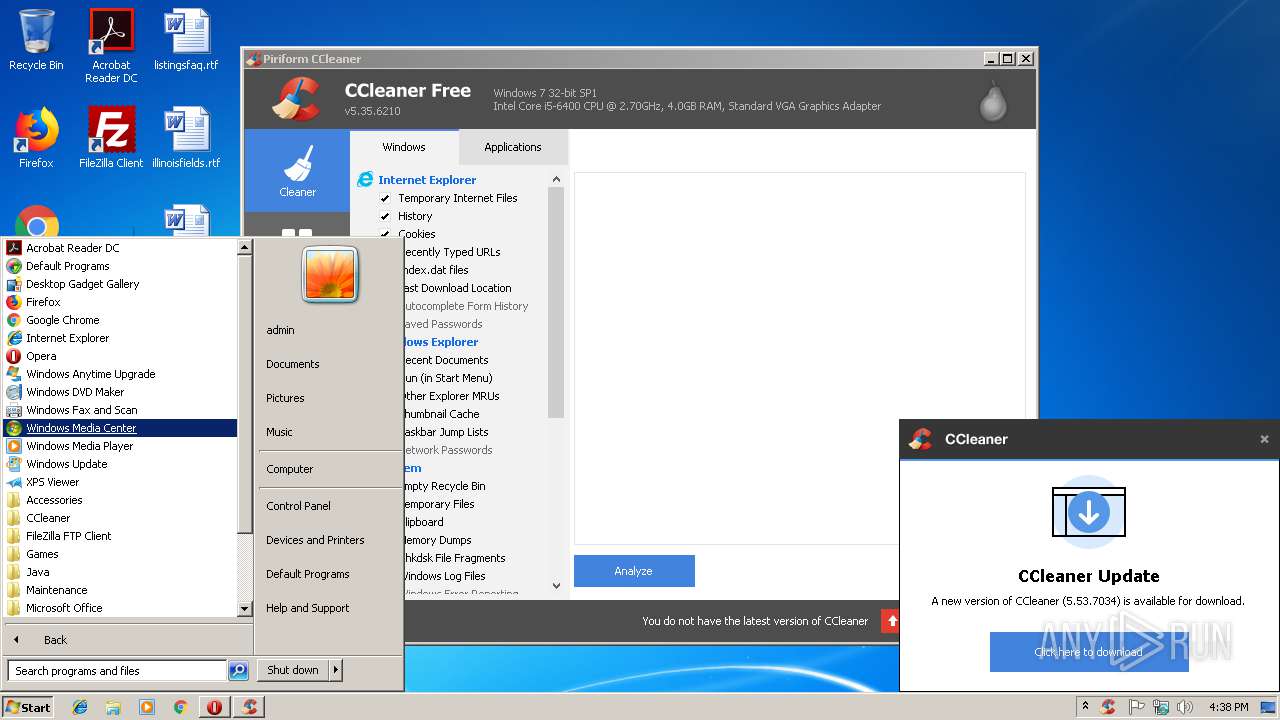
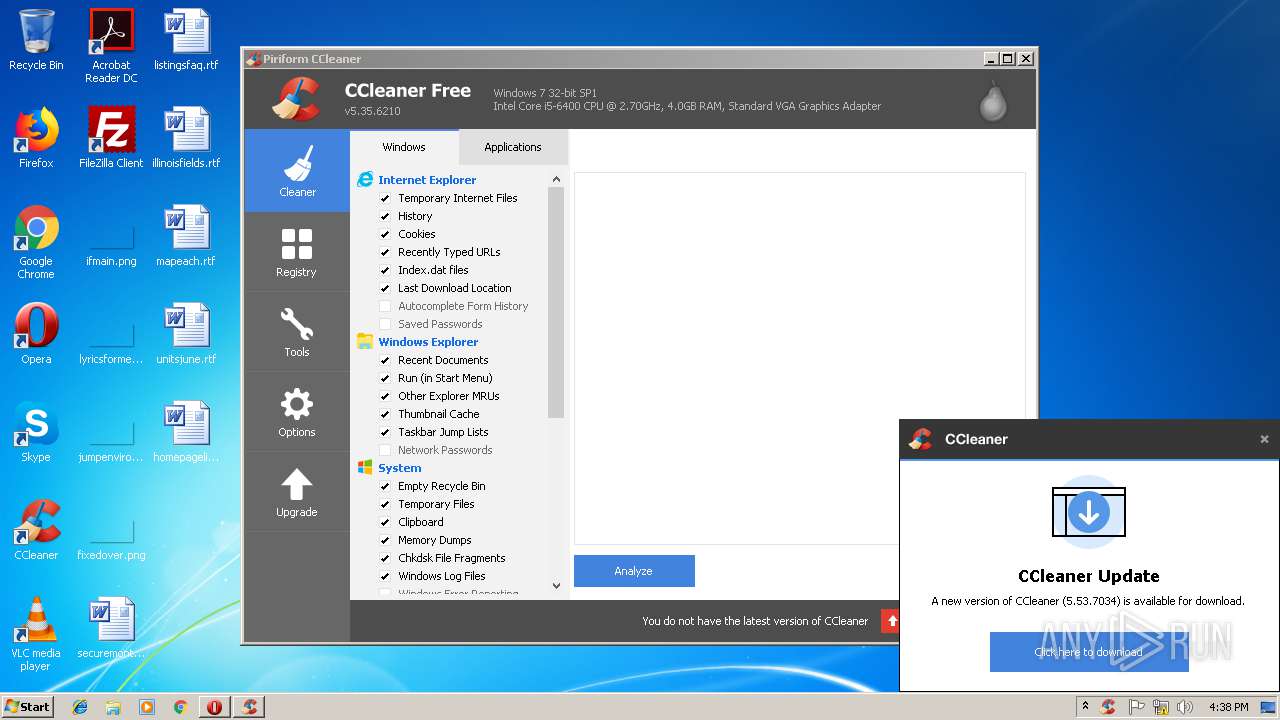
Actions looks like stealing of personal data
- CCleaner.exe (PID: 1248)
- CCleaner.exe (PID: 2720)
Loads dropped or rewritten executable
- PowerISO7-x64.exe (PID: 2580)
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2720)
- CCleaner.exe (PID: 4016)
Changes the autorun value in the registry
- CCleaner.exe (PID: 2720)
SUSPICIOUS
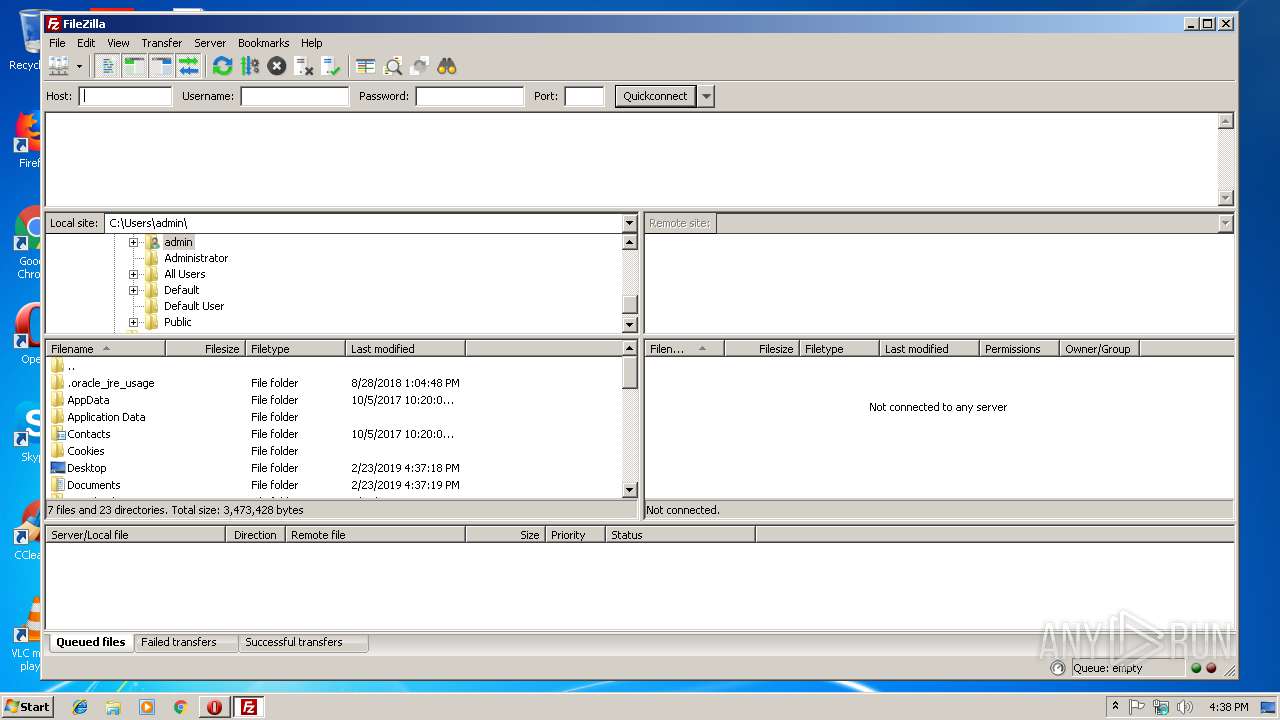
Creates files in the user directory
- filezilla.exe (PID: 2316)
- CCleaner.exe (PID: 1248)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 1248)
Reads internet explorer settings
- CCleaner.exe (PID: 1248)
- CCleaner.exe (PID: 2720)
Executable content was dropped or overwritten
- PowerISO7-x64.exe (PID: 2580)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 1248)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 1248)
INFO
Creates files in the user directory
- opera.exe (PID: 3592)
Reads settings of System Certificates
- CCleaner.exe (PID: 1248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.3.0.0 |
| ProductVersionNumber: | 7.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | Power Software Ltd |
| FileDescription: | PowerISO Setup |
| FileVersion: | 7.3.0.0 |
| LegalCopyright: | Copyright(c) 2004-2018 |
| ProductName: | PowerISO Setup |
| ProductVersion: | 7.3.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| CompanyName: | Power Software Ltd |
| FileDescription: | PowerISO Setup |
| FileVersion: | 7.3.0.0 |
| LegalCopyright: | Copyright(c) 2004-2018 |
| ProductName: | PowerISO Setup |
| ProductVersion: | 7.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x00135000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001A8000 | 0x00008F88 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38405 |
.reloc | 0x001B1000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.14318 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61929 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 6.6097 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.72198 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.68002 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.4516 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 6.08044 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.88101 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 4.13606 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
42
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | explorer.exe | |||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3, 36, 0, 0 Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\PowerISO7-x64.exe" | C:\Users\admin\AppData\Local\Temp\PowerISO7-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Power Software Ltd Integrity Level: HIGH Description: PowerISO Setup Exit code: 2 Version: 7.3.0.0 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 3592 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3784 | "C:\Users\admin\AppData\Local\Temp\PowerISO7-x64.exe" | C:\Users\admin\AppData\Local\Temp\PowerISO7-x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Power Software Ltd Integrity Level: MEDIUM Description: PowerISO Setup Exit code: 3221226540 Version: 7.3.0.0 Modules
| |||||||||||||||
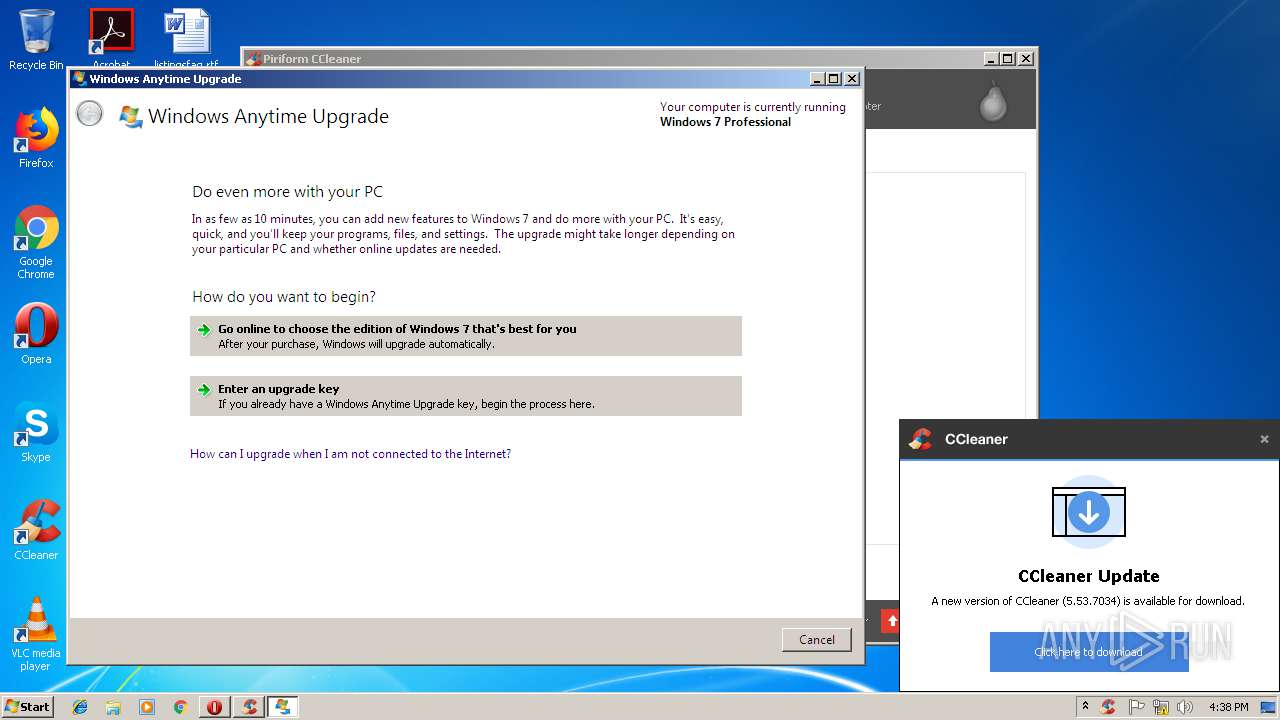
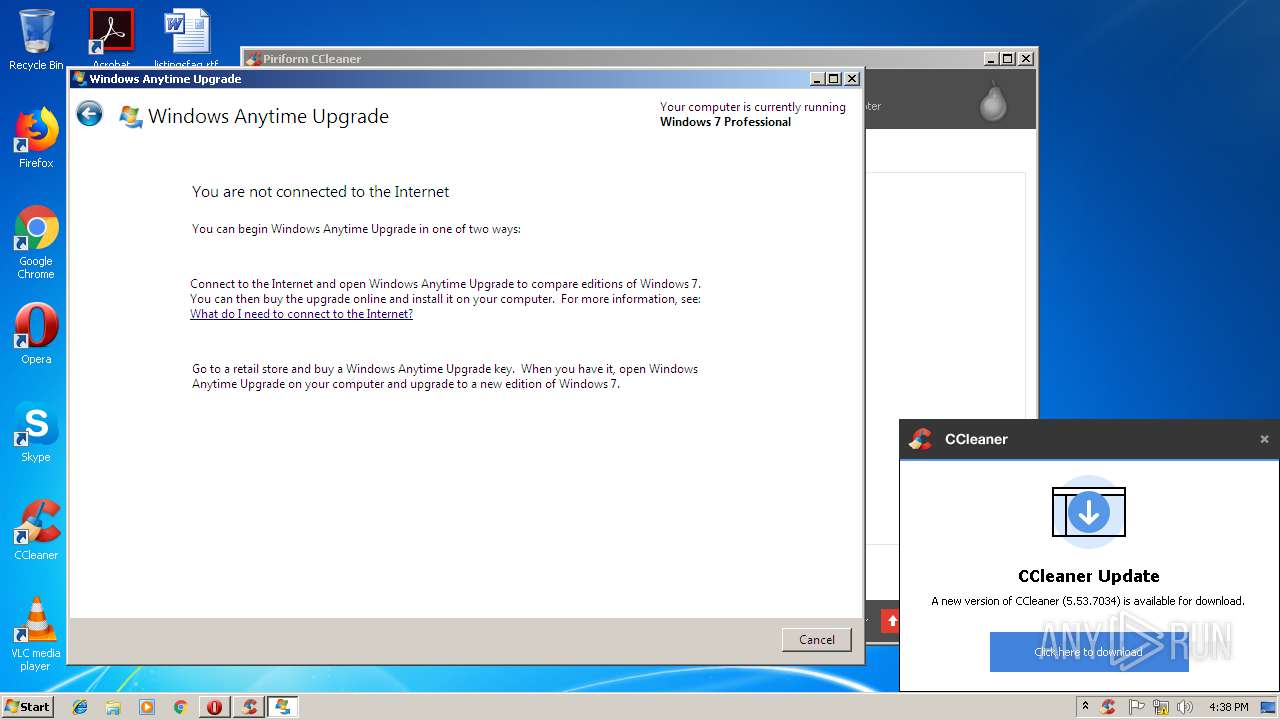
| 3944 | "C:\Windows\system32\WindowsAnytimeUpgradeUI.exe" | C:\Windows\system32\WindowsAnytimeUpgradeUI.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Anytime Upgrade User Interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
Total events
1 475
Read events
1 220
Write events
254
Delete events
1
Modification events
| (PID) Process: | (3592) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3592) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | WipeFreeSpaceDrives |
Value: C:\ | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | CookiesToSave |
Value: *.piriform.com|facebook.com|google.com | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | RunICS |
Value: 0 | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | delete value | Name: | AutoICS |
Value: 1 | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1248) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | NewVersion |
Value: | |||
Executable files
1
Suspicious files
23
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | PowerISO7-x64.exe | C:\Users\admin\AppData\Local\Temp\nsaEF63.tmp | — | |
MD5:— | SHA256:— | |||
| 3592 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4EA9.tmp | — | |
MD5:— | SHA256:— | |||
| 3592 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4F37.tmp | — | |
MD5:— | SHA256:— | |||
| 3592 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr0000V.tmp | — | |
MD5:— | SHA256:— | |||
| 3592 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JYFQHH16VI8H20D6Y4BB.temp | — | |
MD5:— | SHA256:— | |||
| 2316 | filezilla.exe | C:\Users\admin\AppData\Roaming\FileZilla\layout.xml~ | — | |
MD5:— | SHA256:— | |||
| 2316 | filezilla.exe | C:\Users\admin\AppData\Roaming\FileZilla\filezilla.xml~ | — | |
MD5:— | SHA256:— | |||
| 3592 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr849F.tmp | — | |
MD5:— | SHA256:— | |||
| 1248 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1248 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3592 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
1248 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
3592 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3592 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3592 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
3592 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1248 | CCleaner.exe | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
1248 | CCleaner.exe | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
1248 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |