| File name: | twZOCRpuzo.bin |
| Full analysis: | https://app.any.run/tasks/6a1d1b3d-a5e1-4e3a-9b0a-faa86b30bfb2 |
| Verdict: | Malicious activity |
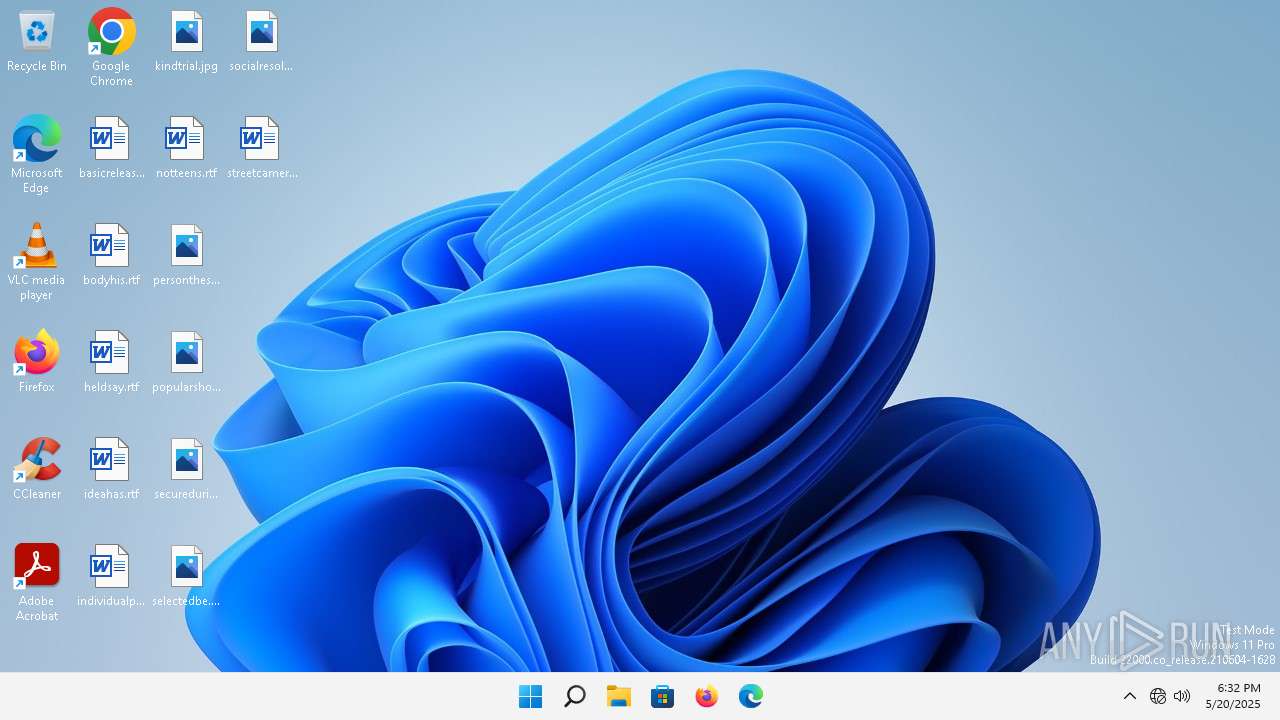
| Analysis date: | May 20, 2025, 18:32:48 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 5 sections |
| MD5: | F5610C801CF023BED27BF63A96735EFC |
| SHA1: | 532004076A678BA81F8411774898A6FC7C533701 |
| SHA256: | 66AAC2857EEE73B1F5F715214BB50A03C0DC052D4BB3E64D6B0B492F2C85F374 |
| SSDEEP: | 49152:f8z8QktQpa/5f7PGUsW7p+uU2LsjlrobspRic6WNlVV/bMvI9k37jwz+ULRKscn2:0ly/JT7pZU2IBrZpRiclnV5UI9qP4FCR |
MALICIOUS
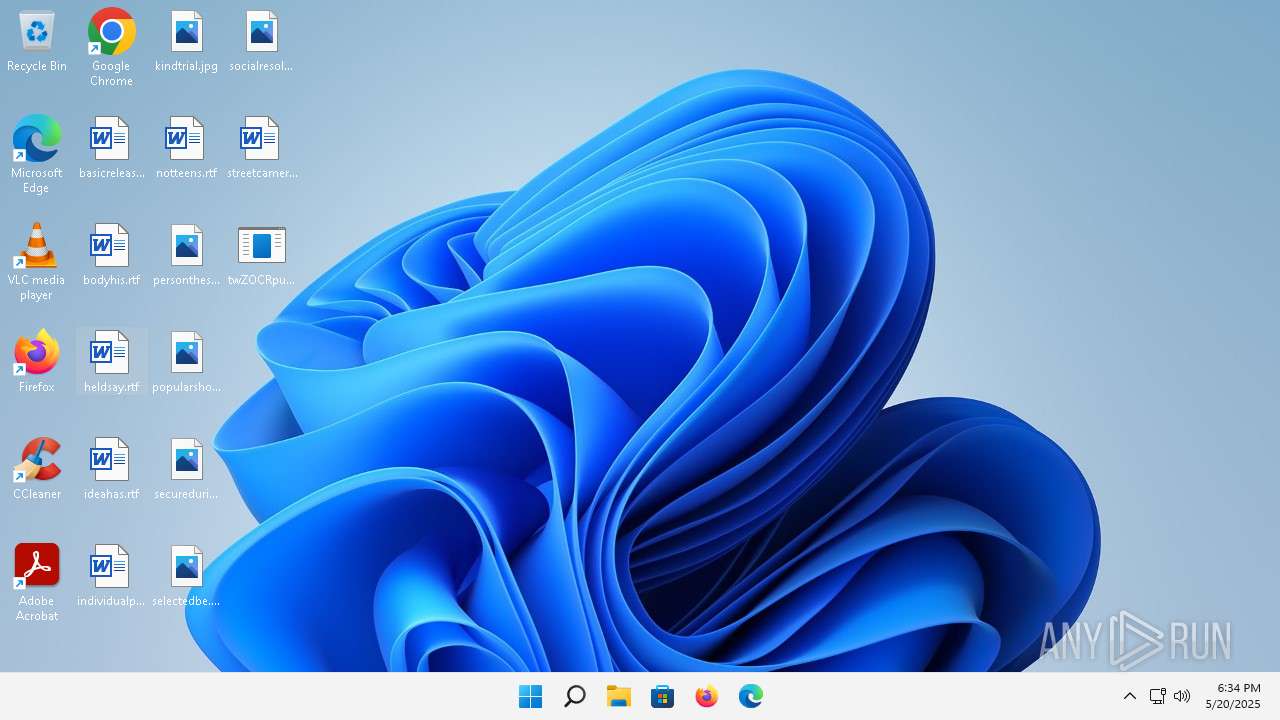
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 3768)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- twZOCRpuzo.bin.exe (PID: 1228)
- twZOCRpuzo.bin.exe (PID: 4348)
Reads the Internet Settings
- powershell.exe (PID: 1152)
- powershell.exe (PID: 1216)
- twZOCRpuzo.bin.exe (PID: 1228)
- powershell.exe (PID: 1084)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 5752)
Checks for external IP
- twZOCRpuzo.bin.exe (PID: 1228)
- svchost.exe (PID: 1664)
- twZOCRpuzo.bin.exe (PID: 4348)
- svchost.exe (PID: 1708)
Connects to unusual port
- twZOCRpuzo.bin.exe (PID: 1228)
- twZOCRpuzo.bin.exe (PID: 4348)
The process executes via Task Scheduler
- twZOCRpuzo.bin.exe (PID: 2448)
- twZOCRpuzo.bin.exe (PID: 4348)
INFO
Reads the computer name
- twZOCRpuzo.bin.exe (PID: 1784)
- twZOCRpuzo.bin.exe (PID: 1228)
Checks supported languages
- twZOCRpuzo.bin.exe (PID: 1228)
- twZOCRpuzo.bin.exe (PID: 1784)
- twZOCRpuzo.bin.exe (PID: 2448)
Reads the machine GUID from the registry
- twZOCRpuzo.bin.exe (PID: 1228)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1152)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 1084)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 5752)
Checks current location (POWERSHELL)
- powershell.exe (PID: 1152)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 1084)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 5752)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1152)
- powershell.exe (PID: 1216)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 1084)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 5752)
Application based on Rust
- twZOCRpuzo.bin.exe (PID: 1228)
Create files in a temporary directory
- twZOCRpuzo.bin.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:06 16:19:24+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 85504 |
| InitializedDataSize: | 1595392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13d54 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
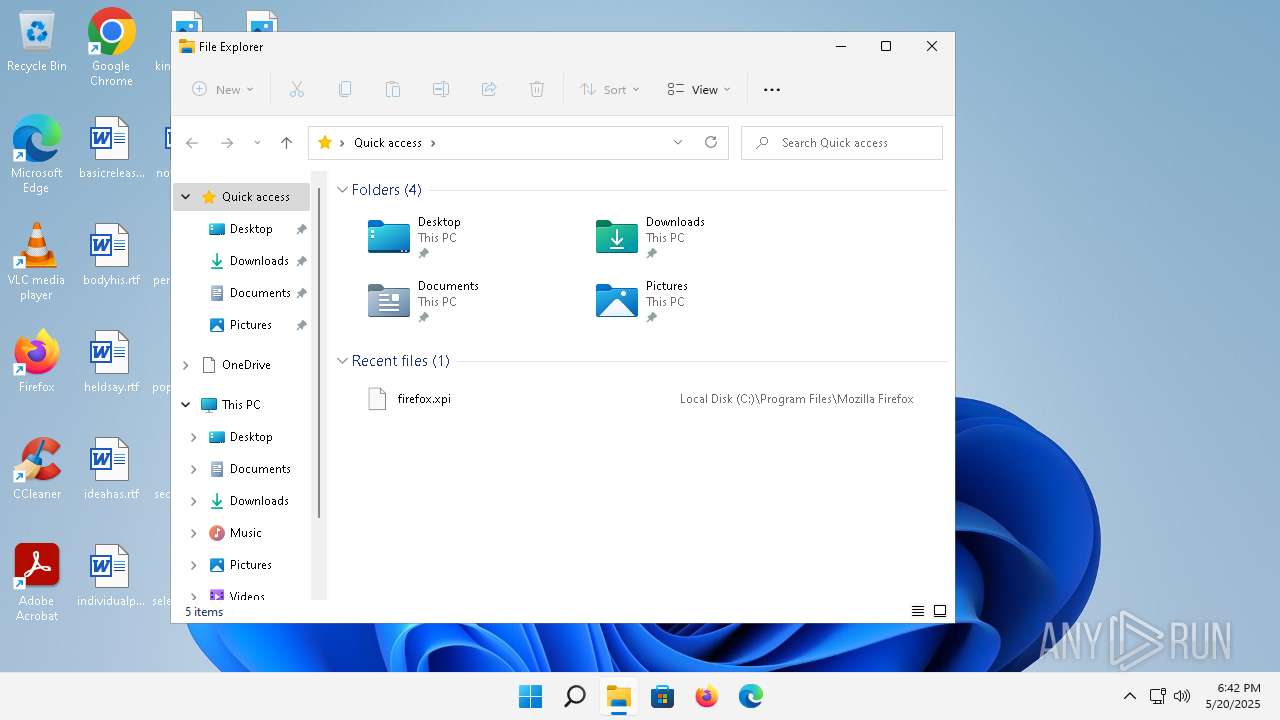
Total processes
243
Monitored processes
24
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | twZOCRpuzo.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | twZOCRpuzo.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | twZOCRpuzo.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\Desktop\twZOCRpuzo.bin.exe" | C:\Users\admin\Desktop\twZOCRpuzo.bin.exe | ComputerDefaults.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 1568 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | twZOCRpuzo.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1708 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | "C:\Users\admin\Desktop\twZOCRpuzo.bin.exe" | C:\Users\admin\Desktop\twZOCRpuzo.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2068 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
46 678
Read events
46 612
Write events
66
Delete events
0
Modification events
| (PID) Process: | (1152) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1152) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1152) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1152) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1084) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1084) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
2
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j5y304it.jqq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1152 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:15DB25D73A54985B8B39DB40BB432C9E | SHA256:025D6F963BC7D42686AEC6AF3ED8B58FA91DFFBDD5B076B910571F1E25CA20A7 | |||
| 1152 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0\UsageLogs\powershell.exe.log | text | |
MD5:656AFFFD15B3E8D265AD341242D33EC6 | SHA256:6F46AED14E028DB08F34C4695E42EBD69762E54AE67BE956B6CC12DD5D841ECE | |||
| 1084 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_d34qc30e.x5b.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fc5aux23.bqd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gqz1ibfj.m0a.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1084 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zr53pegz.zri.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ss01cwps.wb5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_os2a3zea.tfk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3752 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4qfnhh1y.be0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
86
DNS requests
30
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | smartscreen.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fd044436cf96e567 | unknown | — | — | whitelisted |
4348 | twZOCRpuzo.bin.exe | GET | 200 | 208.95.112.1:80 | http://www.ip-api.com/line/?fields=147505 | unknown | — | — | whitelisted |
4184 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
4184 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
4184 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
4184 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
4184 | svchost.exe | POST | 403 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 184.24.77.24:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?01658cdb802755c3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?7ffa61214c1c53e3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1352 | svchost.exe | 184.24.77.24:80 | — | Akamai International B.V. | DE | unknown |
2064 | smartscreen.exe | 172.205.25.163:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | VN | whitelisted |
2064 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3560 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2776 | svchost.exe | 20.189.173.8:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2592 | svchost.exe | 2.16.185.191:443 | fs.microsoft.com | AKAMAI-AS | DE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1228 | twZOCRpuzo.bin.exe | 208.95.112.1:80 | www.ip-api.com | TUT-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
www.ip-api.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1664 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1228 | twZOCRpuzo.bin.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
— | — | Misc activity | ET INFO Microsoft Connection Test |
1708 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
4348 | twZOCRpuzo.bin.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |