| File name: | edf00ca569ae407d61962f31e19bf409 |
| Full analysis: | https://app.any.run/tasks/bc0419ad-c694-4f21-bd7f-da47dd304666 |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2019, 14:52:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EDF00CA569AE407D61962F31E19BF409 |
| SHA1: | A93F1555B7F4DEEBDB31243501E25A26151B0A97 |
| SHA256: | 669BEF2BD6125AB1F4D3999535ED8323D1F4F5532026C70E2AACA4ECDD4F3058 |
| SSDEEP: | 196608:AdQt3l399JK6qJ4iR7xn75bJB2oXgMMBXmxAT2mQhAV7sdoj:jtV3891RdFJB2ouB2+amui7cQ |
MALICIOUS
Application was dropped or rewritten from another process
- DocBlue.exe (PID: 3504)
- WebSoft.exe (PID: 3508)
Changes the autorun value in the registry
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
Loads dropped or rewritten executable
- WebSoft.exe (PID: 3508)
- DocBlue.exe (PID: 3504)
SUSPICIOUS
Reads Windows owner or organization settings
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
Executable content was dropped or overwritten
- edf00ca569ae407d61962f31e19bf409.exe (PID: 656)
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
Reads the machine GUID from the registry
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
Reads the Windows organization settings
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
INFO
Loads dropped or rewritten executable
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
Application was dropped or rewritten from another process
- edf00ca569ae407d61962f31e19bf409.tmp (PID: 1032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:01:30 15:21:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 188416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
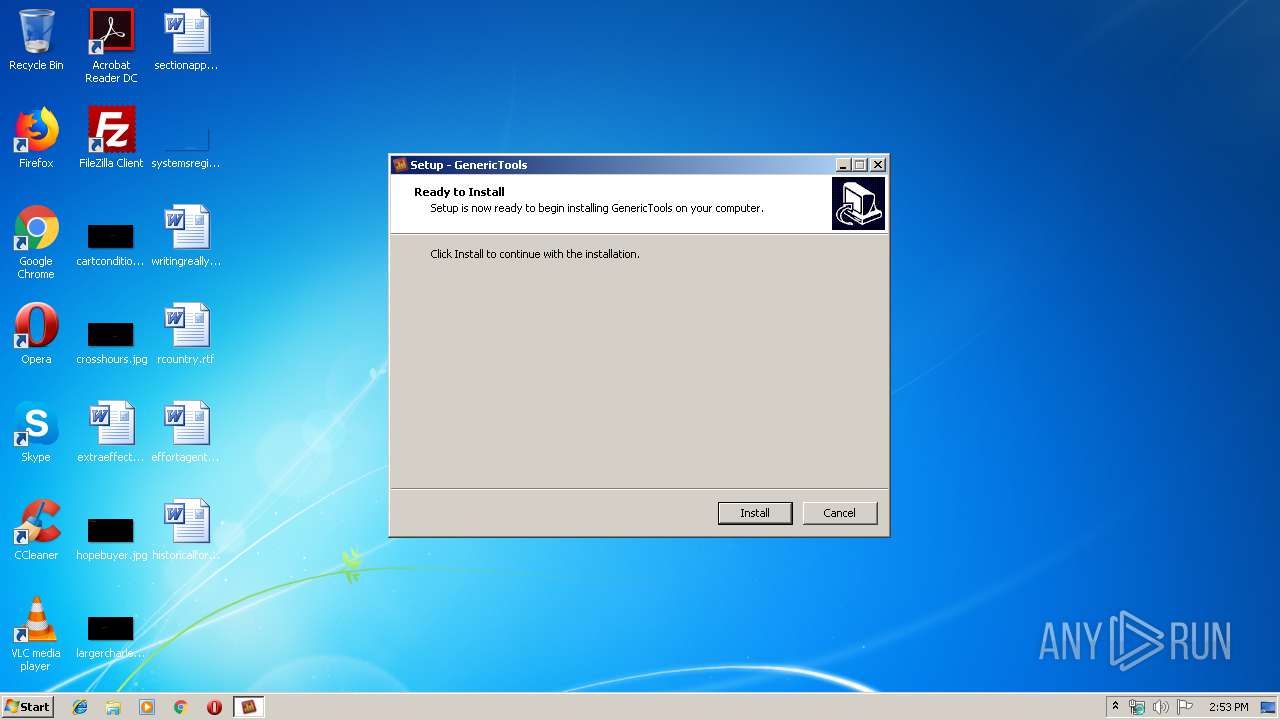
| FileDescription: | GenericTools Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | GenericTools |
| ProductVersion: | 3.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2013 14:21:56 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | GenericTools Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | GenericTools |
| ProductVersion: | 3.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 30-Jan-2013 14:21:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F12C | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39148 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73207 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24631 |
.bss | 0x00013000 | 0x000056B4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0002C1C4 | 0x0002C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44981 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.26483 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.12265 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.82176 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.70242 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.53043 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.18486 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
36
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | "C:\Users\admin\AppData\Local\Temp\edf00ca569ae407d61962f31e19bf409.exe" | C:\Users\admin\AppData\Local\Temp\edf00ca569ae407d61962f31e19bf409.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: GenericTools Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1032 | "C:\Users\admin\AppData\Local\Temp\is-41MHG.tmp\edf00ca569ae407d61962f31e19bf409.tmp" /SL5="$30128,8828999,254464,C:\Users\admin\AppData\Local\Temp\edf00ca569ae407d61962f31e19bf409.exe" | C:\Users\admin\AppData\Local\Temp\is-41MHG.tmp\edf00ca569ae407d61962f31e19bf409.tmp | edf00ca569ae407d61962f31e19bf409.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\GenericTools\DocBlue.exe" | C:\Users\admin\AppData\Local\GenericTools\DocBlue.exe | edf00ca569ae407d61962f31e19bf409.tmp | ||||||||||||
User: admin Company: DocBlue LTD Integrity Level: MEDIUM Description: DocBlue Exit code: 0 Version: 3.2.6.1 Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\GenericTools\WebSoft.exe" | C:\Users\admin\AppData\Local\GenericTools\WebSoft.exe | edf00ca569ae407d61962f31e19bf409.tmp | ||||||||||||
User: admin Company: WebSoft LTD Integrity Level: MEDIUM Description: WebSoft Exit code: 0 Version: 2.3.2.0 Modules
| |||||||||||||||
Total events
86
Read events
70
Write events
16
Delete events
0
Modification events
| (PID) Process: | (1032) edf00ca569ae407d61962f31e19bf409.tmp | Key: | HKEY_CURRENT_USER\Software\GenericTools |
| Operation: | write | Name: | insterra |
Value: 191113 | |||
| (PID) Process: | (1032) edf00ca569ae407d61962f31e19bf409.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | DocBlue |
Value: C:\Users\admin\AppData\Local\GenericTools\DocBlue.exe | |||
| (PID) Process: | (1032) edf00ca569ae407d61962f31e19bf409.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WebSoft |
Value: C:\Users\admin\AppData\Local\GenericTools\WebSoft.exe | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 40804 | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 2012-11-26T12:31:46 | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qico4.dll |
Value: 40804 | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qico4.dll |
Value: 2012-11-26T12:31:58 | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qjpeg4.dll |
Value: 40804 | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qjpeg4.dll |
Value: 2012-11-26T12:31:44 | |||
| (PID) Process: | (3508) WebSoft.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\GenericTools\imageformats |
| Operation: | write | Name: | qmng4.dll |
Value: 40804 | |||
Executable files
21
Suspicious files
0
Text files
1 413
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-5EQC4.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-TPEB4.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-3AG8B.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-ULO5N.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-3EVGO.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-3IB18.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-0UEHV.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-G9PSN.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-GBR6P.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | edf00ca569ae407d61962f31e19bf409.tmp | C:\Users\admin\AppData\Local\GenericTools\is-I0KUA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2 226
TCP/UDP connections
2 184
DNS requests
434
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3504 | DocBlue.exe | GET | 302 | 190.2.151.248:80 | http://b97.cleverjumper.com/q_get.php?uid=8d2f2125e78a03bb54c832deec8f70f21c605cb5 | CW | — | — | unknown |
3504 | DocBlue.exe | GET | 302 | 190.2.151.248:80 | http://b97.cleverjumper.com/q_get.php?uid=8d2f2125e78a03bb54c832deec8f70f21c605cb5 | CW | — | — | unknown |
3504 | DocBlue.exe | GET | 200 | 190.2.151.248:80 | http://b97.cleverjumper.com/k_get_new.php?bot=14 | CW | — | — | unknown |
3504 | DocBlue.exe | GET | 302 | 190.2.151.248:80 | http://b97.cleverjumper.com/q_get.php?uid=8d2f2125e78a03bb54c832deec8f70f21c605cb5 | CW | — | — | unknown |
3508 | WebSoft.exe | GET | 301 | 198.49.23.144:80 | http://camkendell.com/ | US | — | — | malicious |
3504 | DocBlue.exe | GET | 200 | 190.2.151.248:80 | http://b97.cleverjumper.com/k_get_new.php?bot=14 | CW | text | 239 b | unknown |
3508 | WebSoft.exe | GET | 200 | 93.190.141.177:80 | http://server19.openfrost.com/sinder4.php | NL | text | 48 b | suspicious |
1032 | edf00ca569ae407d61962f31e19bf409.tmp | GET | 200 | 93.190.142.79:80 | http://myprintscreen.com/ | NL | html | 16.7 Kb | suspicious |
3504 | DocBlue.exe | POST | 200 | 190.2.151.248:80 | http://b97.cleverjumper.com/k_put_new.php?id=352508-z123-89361933-16-14&uid=8d2f2125e78a03bb54c832deec8f70f21c605cb5 | CW | — | — | unknown |
3508 | WebSoft.exe | GET | 200 | 93.190.141.177:80 | http://server19.openfrost.com/sinder4.php | NL | text | 50 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.190.142.79:80 | myprintscreen.com | WorldStream B.V. | NL | suspicious |
3504 | DocBlue.exe | 190.2.151.248:80 | b97.cleverjumper.com | Scarlet B.V. | CW | unknown |
3504 | DocBlue.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
3508 | WebSoft.exe | 190.2.151.247:80 | b14.cleverjumper.com | Scarlet B.V. | CW | unknown |
3508 | WebSoft.exe | 93.190.141.177:80 | server19.openfrost.com | WorldStream B.V. | NL | suspicious |
3508 | WebSoft.exe | 198.49.23.144:80 | camkendell.com | Squarespace, Inc. | US | malicious |
3508 | WebSoft.exe | 198.49.23.144:443 | camkendell.com | Squarespace, Inc. | US | malicious |
3508 | WebSoft.exe | 190.2.134.126:80 | b17.cleverjumper.com | Scarlet B.V. | CW | unknown |
3508 | WebSoft.exe | 190.2.151.243:80 | b15.cleverjumper.com | Scarlet B.V. | CW | suspicious |
3508 | WebSoft.exe | 190.2.151.204:80 | b23.cleverjumper.com | Scarlet B.V. | CW | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
myprintscreen.com |
| suspicious |
b97.cleverjumper.com |
| unknown |
www.google.com |
| malicious |
b14.cleverjumper.com |
| unknown |
server19.openfrost.com |
| suspicious |
camkendell.com |
| malicious |
b17.cleverjumper.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
assets.squarespace.com |
| whitelisted |
static1.squarespace.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
3508 | WebSoft.exe | Misc activity | SUSPICIOUS [PTsecurity] JS obfuscation (obfuscator.io) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
3508 | WebSoft.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3508 | WebSoft.exe | Misc activity | SUSPICIOUS [PTsecurity] Malicious Redirect (EK seen) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |
Process | Message |
|---|---|
DocBlue.exe | taskUrl: "http://b97.cleverjumper.com/q_get.php"
|
DocBlue.exe | taskUrl: "http://b97.cleverjumper.com/q_get.php"
|
DocBlue.exe | QUrl( "http://b97.cleverjumper.com/q_get.php?uid=8d2f2125e78a03bb54c832deec8f70f21c605cb5" )
|
DocBlue.exe | QUrl( "http://b97.cleverjumper.com/k_get_new.php?bot=14" )
|
DocBlue.exe | "http://b97.cleverjumper.com/q_get.php?uid=8d2f2125e78a03bb54c832deec8f70f21c605cb5 ==> redirect to ==> http://b97.cleverjumper.com/k_get_new.php?bot=14"
|
DocBlue.exe | "Try to get content from: https://www.google.com/search?q=600+x+1024+11%3A42+Kindle%D0%B3%D0%BE%D1%80%D0%B8%D0%B7%D0%BE%D0%BD%D1%82%D0%B0%D0%BB%D1%8C%D0%BD%D0%BE+1024+x+600+&hl=all&gws_rd=cr"
|
DocBlue.exe | Go to: "https://www.google.com/search?q=600+x+1024+11%3A42+Kindle%D0%B3%D0%BE%D1%80%D0%B8%D0%B7%D0%BE%D0%BD%D1%82%D0%B0%D0%BB%D1%8C%D0%BD%D0%BE+1024+x+600+&hl=all&gws_rd=cr"
|
DocBlue.exe | "Get task from server: {"id":"352508-z123-89361933-16-14","url":"https:\/\/www.google.cl\/search?q=tira+de+cola+con+crema+depilatoria+definitiva&hl=es-419&gl=cl&start=0&num=100&gws_rd=cr,ssl","returnurl":"http:\/\/b97.cleverjumper.com\/k_put_new.php","bot":"14"}"
|
WebSoft.exe | "Status code: 302 Status message: Url: http://b14.cleverjumper.com/sinder4.php"
|
WebSoft.exe | "http://b14.cleverjumper.com/sinder4.php
==> redirect to ==>
http://server19.openfrost.com/sinder4.php"
|