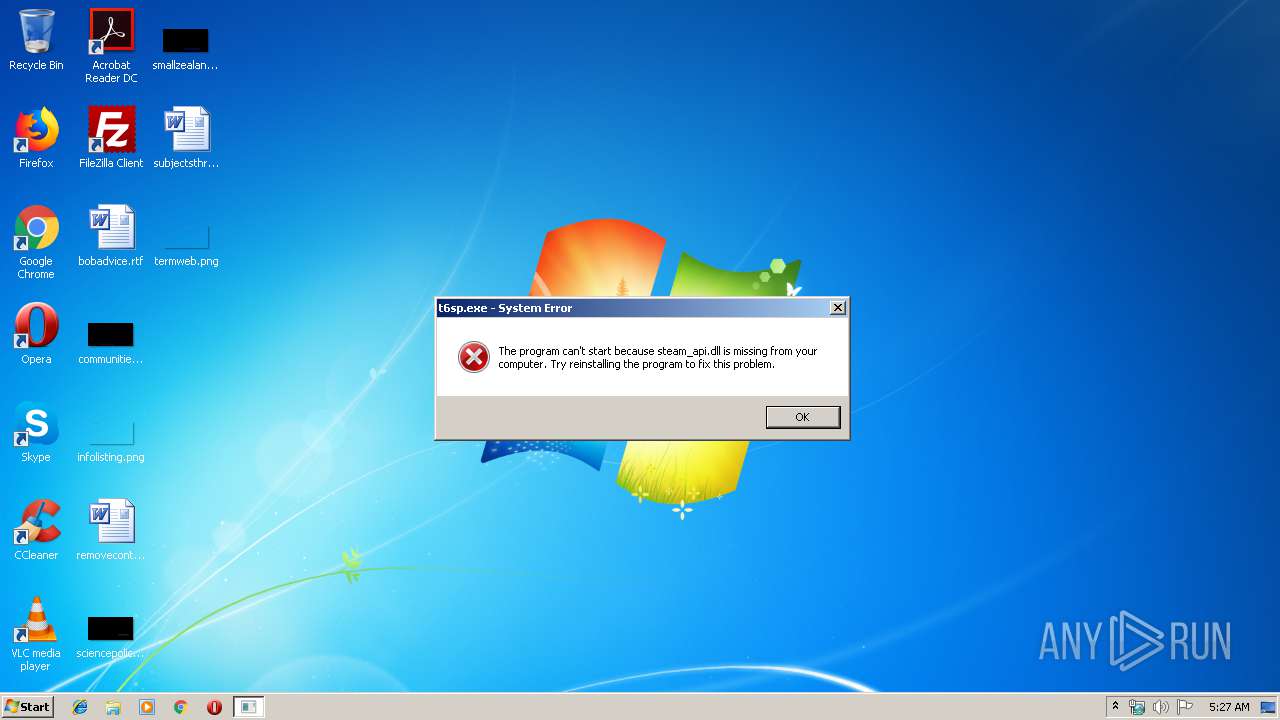
| File name: | t6sp.exe |
| Full analysis: | https://app.any.run/tasks/53cbf684-755e-45de-848c-f093a3050847 |
| Verdict: | No threats detected |
| Analysis date: | December 05, 2019, 05:27:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D78D20A01A28A44FDD2D58CAC5299EF8 |
| SHA1: | 0A8073B80374977E217B6A28D99EFDBE32C37E6B |
| SHA256: | 669867D16088AF695A3A4A28AE71CDB461D8ED627CC84F017A51E8908CC77B29 |
| SSDEEP: | 98304:9Krkl8Aq0W44Umfnqt1rv2gEcCqMKM0jPERAYqK7wPcWVaZ6wSc:oOUc1ru1cCqMV0XYqeL9Sc |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:12 03:17:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 6524416 |
| InitializedDataSize: | 4993536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x56b75c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 6.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Activision Publishing Inc. |
| FileDescription: | Call of Duty(R): Black Ops II |
| FileVersion: | 1 |
| LegalCopyright: | (C) 2012 Activision Publishing Inc. |
| OriginalFileName: | t6sp.exe |
| ProductName: | Call of Duty(R): Black Ops II |
| ProductVersion: | 6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Dec-2012 02:17:41 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Activision Publishing Inc. |
| FileDescription: | Call of Duty(R): Black Ops II |
| FileVersion: | 1.0 |
| LegalCopyright: | (C) 2012 Activision Publishing Inc. |
| OriginalFilename: | t6sp.exe |
| ProductName: | Call of Duty(R): Black Ops II |
| ProductVersion: | 6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000140 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 12-Dec-2012 02:17:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x006304B0 | 0x00630600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71738 |
.conceal4\x1f | 0x00632000 | 0x00001F34 | 0x00002000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.92036 |
.interpr,f | 0x00634000 | 0x0000662C | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.33081 |
.rdata | 0x0063B000 | 0x0018BC1F | 0x0018BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.8852 |
.data | 0x007C7000 | 0x035BDBE4 | 0x002F4A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.556427 |
.tls | 0x03D85000 | 0x00001A5D | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.00369694 |
.version\x04 | 0x03D87000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0815394 |
.rodata | 0x03D88000 | 0x00000BD0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.16695 |
.rsrc | 0x03D89000 | 0x0003FEA8 | 0x00040000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.15154 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41192 | 748 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 2.07431 | 7336 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.31542 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.13498 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.97399 | 4268 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 3.5161 | 4268 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 4.7784 | 4268 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 4.29719 | 4268 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 4.30742 | 4268 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 3.97399 | 4268 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
DSOUND.dll |
GDI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WS2_32.dll |
WSOCK32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
NvOptimusEnablement | 1 | 0x00ABA7B4 |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||
|---|---|---|---|---|---|---|---|---|---|
| 3140 | "C:\Users\admin\AppData\Local\Temp\t6sp.exe" | C:\Users\admin\AppData\Local\Temp\t6sp.exe | — | explorer.exe | |||||
User: admin Company: Activision Publishing Inc. Integrity Level: MEDIUM Description: Call of Duty(R): Black Ops II Exit code: 3221225781 Version: 1.0 Modules
| |||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report