| File name: | WhatsappWeb.msi |
| Full analysis: | https://app.any.run/tasks/4b2c76ff-b1ee-4ecf-8914-01261305198f |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2024, 18:02:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: PDQConnectAgent, Author: PDQ.com, Keywords: Installer, Comments: This installer database contains the logic and data required to install PDQConnectAgent., Template: x64;1033, Revision Number: {85C6D84F-37EC-4D4B-94DE-DB23DEF61F1F}, Create Time/Date: Wed Nov 6 23:53:40 2024, Last Saved Time/Date: Wed Nov 6 23:53:40 2024, Number of Pages: 200, Number of Words: 2, Name of Creating Application: WiX Toolset (5.0.0.0), Security: 2 |
| MD5: | 82F3F74379C6DBDBCA3A64C5717C2FAA |
| SHA1: | BA5562E233C1F83D6929DB8DD03860A99BF58FA4 |
| SHA256: | 6696D790EE119B0DE93919050A642D3DCA502A2AE1864700B6B06FA2B955EC9D |
| SSDEEP: | 98304:g3Q8NTtWfTSdT8sMAxt9QdQ80K6/ySxzgvb41t70DaPe/0sVHhD2xGKxkFA8g//E:BLb6K |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6872)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 6740)
- powershell.exe (PID: 6996)
- powershell.exe (PID: 6904)
- powershell.exe (PID: 1488)
- powershell.exe (PID: 6840)
- powershell.exe (PID: 5380)
- powershell.exe (PID: 7060)
- powershell.exe (PID: 6440)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5208)
- powershell.exe (PID: 6972)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 7572)
- powershell.exe (PID: 7612)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 7548)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 7712)
- powershell.exe (PID: 7592)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 5308)
Changes powershell execution policy (Bypass)
- pdq-connect-agent.exe (PID: 7076)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 5528)
- pdq-connect-agent.exe (PID: 7076)
- pdq-connect-updater.exe (PID: 6760)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 6800)
- msiexec.exe (PID: 6600)
- msiexec.exe (PID: 6508)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6644)
- rundll32.exe (PID: 6840)
- rundll32.exe (PID: 6704)
- rundll32.exe (PID: 6992)
- rundll32.exe (PID: 6532)
- pdq-connect-agent.exe (PID: 7076)
- rundll32.exe (PID: 6940)
- rundll32.exe (PID: 6680)
- csc.exe (PID: 8784)
- csc.exe (PID: 7308)
- powershell.exe (PID: 7572)
- powershell.exe (PID: 7060)
Starts SC.EXE for service management
- rundll32.exe (PID: 6992)
PDQConnect is probably used for system patching and software deployment
- sc.exe (PID: 7024)
The process hide an interactive prompt from the user
- pdq-connect-agent.exe (PID: 7076)
Starts POWERSHELL.EXE for commands execution
- pdq-connect-agent.exe (PID: 7076)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7184)
- powershell.exe (PID: 648)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 8608)
- powershell.exe (PID: 2536)
- powershell.exe (PID: 4140)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 8932)
- powershell.exe (PID: 8868)
- powershell.exe (PID: 6016)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 9132)
- powershell.exe (PID: 8344)
- powershell.exe (PID: 8748)
- powershell.exe (PID: 7840)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 4576)
The process hides Powershell's copyright startup banner
- pdq-connect-agent.exe (PID: 7076)
- powershell.exe (PID: 7184)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 648)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 8608)
- powershell.exe (PID: 2536)
- powershell.exe (PID: 4140)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 8868)
- powershell.exe (PID: 6016)
- powershell.exe (PID: 8932)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 9132)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 8344)
- powershell.exe (PID: 8748)
- powershell.exe (PID: 7840)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 4576)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 8236)
The process bypasses the loading of PowerShell profile settings
- pdq-connect-agent.exe (PID: 7076)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 648)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 7184)
- powershell.exe (PID: 8608)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 4140)
- powershell.exe (PID: 2536)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 4576)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 8932)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 8868)
- powershell.exe (PID: 6016)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 9132)
- powershell.exe (PID: 8344)
- powershell.exe (PID: 8748)
- powershell.exe (PID: 7840)
- powershell.exe (PID: 7444)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8784)
- csc.exe (PID: 7308)
Application launched itself
- powershell.exe (PID: 7184)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 648)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 8608)
- powershell.exe (PID: 2536)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4140)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 4576)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 8932)
- powershell.exe (PID: 8868)
- powershell.exe (PID: 6016)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 9132)
- powershell.exe (PID: 8344)
- powershell.exe (PID: 8748)
- powershell.exe (PID: 7840)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 6516)
Process drops legitimate windows executable
- powershell.exe (PID: 7060)
- powershell.exe (PID: 7572)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 7304)
- DismHost.exe (PID: 6520)
INFO
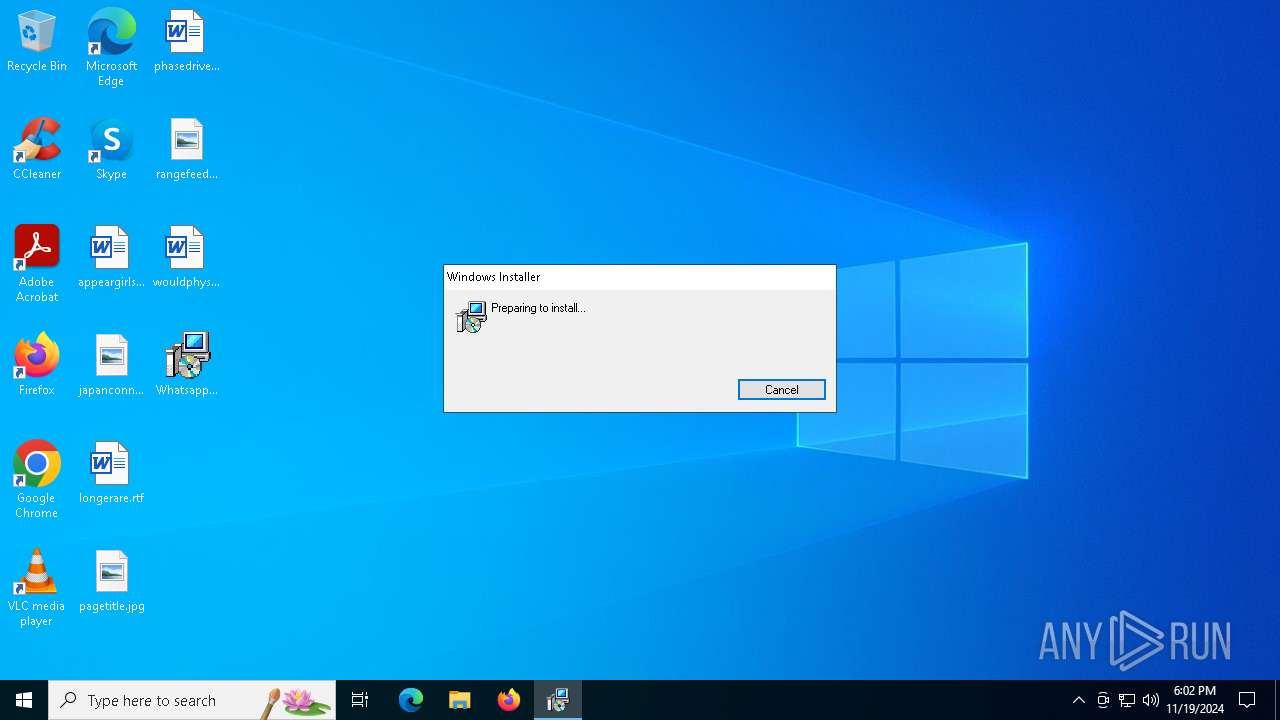
An automatically generated document
- msiexec.exe (PID: 488)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 488)
Reads the software policy settings
- msiexec.exe (PID: 488)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5316)
Creates files or folders in the user directory
- msiexec.exe (PID: 488)
Application launched itself
- msiexec.exe (PID: 5316)
Manages system restore points
- SrTasks.exe (PID: 6452)
Application based on Rust
- pdq-connect-agent.exe (PID: 7076)
- pdq-connect-updater.exe (PID: 6760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
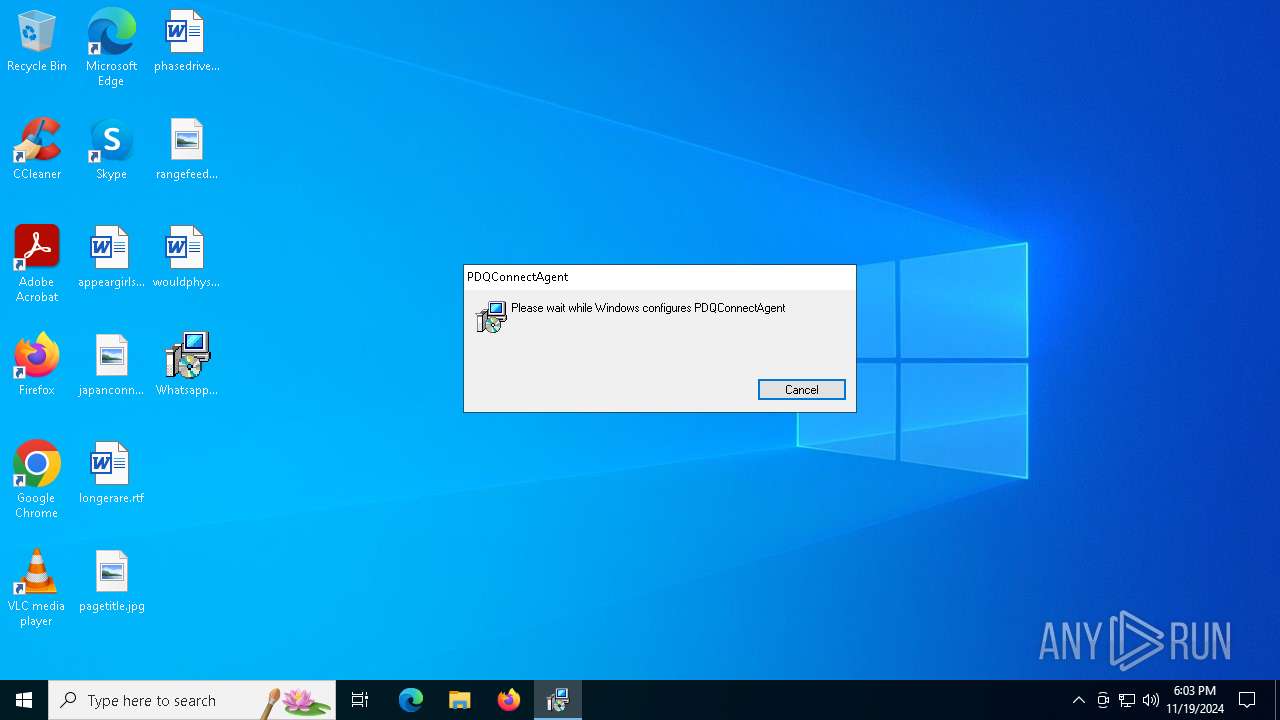
| Subject: | PDQConnectAgent |
| Author: | PDQ.com |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install PDQConnectAgent. |
| Template: | x64;1033 |
| RevisionNumber: | {85C6D84F-37EC-4D4B-94DE-DB23DEF61F1F} |
| CreateDate: | 2024:11:06 23:53:40 |
| ModifyDate: | 2024:11:06 23:53:40 |
| Pages: | 200 |
| Words: | 2 |
| Software: | WiX Toolset (5.0.0.0) |
| Security: | Read-only recommended |
Total processes
302
Monitored processes
171
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\WhatsappWeb.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 520 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Version 5.1 -s -NoLogo -NoProfile | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 648 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Version 5.1 -s -NoLogo -NoProfile | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 904 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\WINDOWS\TEMP\RES9EB7.tmp" "c:\Windows\Temp\uoz3gixg\CSC6B591C828ABB4A39B5E15C1520F96017.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 | |||||||||||||||
| 1140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1488 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1596 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1708 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
4 619
Read events
4 585
Write events
25
Delete events
9
Modification events
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000334C2A45AD3ADB01C41400000C0B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000334C2A45AD3ADB01C41400000C0B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000031836345AD3ADB01C41400000C0B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000031836345AD3ADB01C41400000C0B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000079E76545AD3ADB01C41400000C0B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000008A4A6845AD3ADB01C41400000C0B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000A35ED845AD3ADB01C41400000C0B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000026C2DA45AD3ADB01C4140000BC150000E8030000010000000000000000000000B1D18873897FB640B096A79A746DE48900000000000000000000000000000000 | |||
| (PID) Process: | (5528) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003F40E445AD3ADB019815000074090000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
141
Suspicious files
50
Text files
194
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5316 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5316 | msiexec.exe | C:\Windows\Installer\ed30b.msi | — | |
MD5:— | SHA256:— | |||
| 488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_8DBAD5A433D1F9275321E076E8B744D4 | der | |
MD5:057D0AF1F3BB46423B56E4C1C75393BF | SHA256:6691143F23DD0B020F1B0A1551F5AD14CB0D8D8BB610E1CADA0175992E9BB9CC | |||
| 488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:4302AC33571A665623F83CAA83E9D7B7 | SHA256:85D864FDF43320E3535AD37F3D946A3BD648DF66622CBBCB079B976ABFA7FF41 | |||
| 5316 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{7388d1b1-7f89-40b6-b096-a79a746de489}_OnDiskSnapshotProp | binary | |
MD5:601DCAE35736A11000E9887DB4B33D2F | SHA256:B2AFB8304AAC9BC495C2202CDF4E6C20821BCE6ADB767D8475A571CD91CA34DB | |||
| 6644 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCAA97201CFB9488C1BDB40DFA604F1FDCB\WixSharp.dll | executable | |
MD5:EBED2675D27B9383EE8E58BDEDDD5DA4 | SHA256:CAA9DA1C55E33446EAEB783957E990847369423C7DD652F07A5C93BF1D786A66 | |||
| 488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D9CB7DFFEEA63BAB482BD2705E7E24AB_D64C5BFAB2C28B4652E4AC7169A0D3DB | der | |
MD5:29FEAA220E7DC2D386FEDEBEFF4CB068 | SHA256:EECB268820B5BE9D0CDA58BDDAA3185561C42A48FF000500C72C86D0CAA31EBB | |||
| 488 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D9CB7DFFEEA63BAB482BD2705E7E24AB_D64C5BFAB2C28B4652E4AC7169A0D3DB | binary | |
MD5:D88A39473961DEE009B8A900988970E8 | SHA256:44A67667306FCD8E20560CCC0589186DE069BE32A47F66648EF2ECB2AB0E4242 | |||
| 6704 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCA043547043142D2CA141999110D4542C3\WixSharp.dll | executable | |
MD5:EBED2675D27B9383EE8E58BDEDDD5DA4 | SHA256:CAA9DA1C55E33446EAEB783957E990847369423C7DD652F07A5C93BF1D786A66 | |||
| 5316 | msiexec.exe | C:\Windows\Installer\MSIDC65.tmp | executable | |
MD5:E8DC682F2C486075C6ABA658971A62CC | SHA256:7AACD4C18710E9BC4FF2034895A0A0C8F80F21809FB177D520E93F7688216E6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
44
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEA5NZ%2FZDFskqO3oXzEaXao8%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhtVltVOu8OqBzmsd%2B%2FeFfks3xTQQUvGsiZZ2MaObmHgXx2HIl1LjgSMACEAvcoEuhCK%2FAlHGPdKmo6gs%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 184.24.77.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4932 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5996 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
488 | msiexec.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.178:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
app.pdq.com |
| whitelisted |
pdqinstallers.e9d69694c3d8f7465fd531512c22bd0f.r2.cloudflarestorage.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |