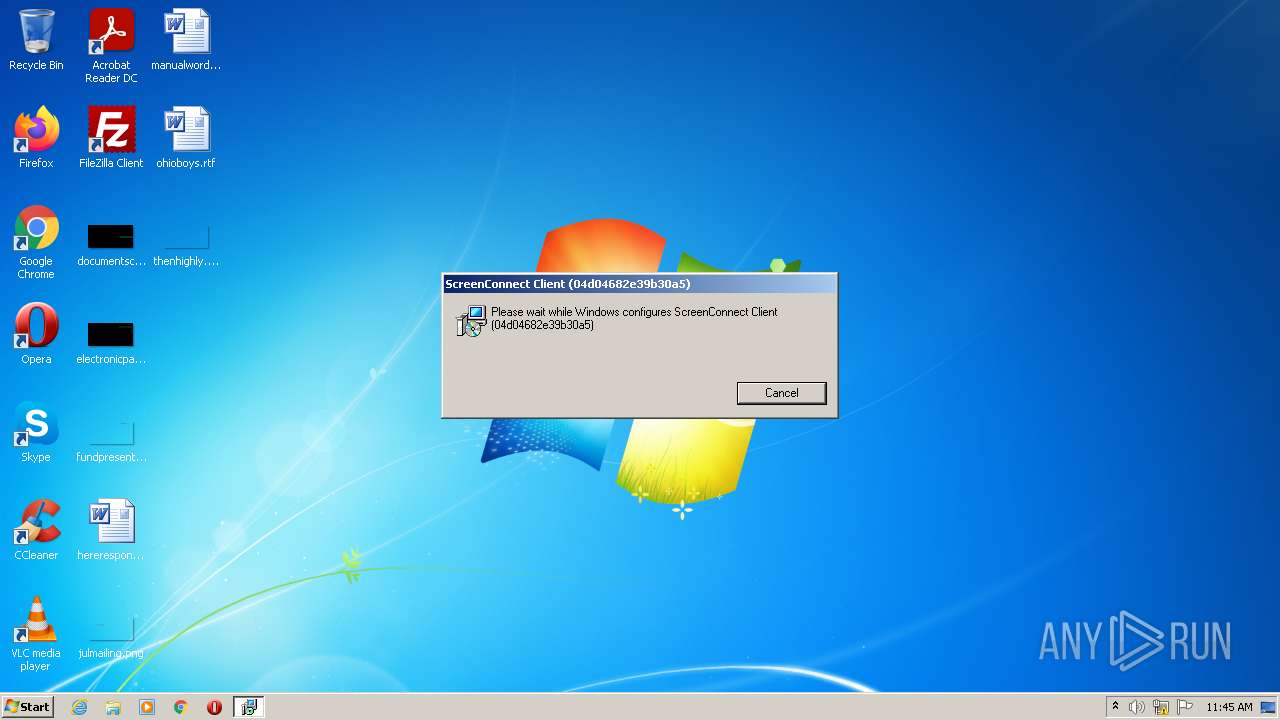
| File name: | ScreenConnect.ClientSetup.exe_ |
| Full analysis: | https://app.any.run/tasks/3732de44-c234-408e-996d-463359bd2bad |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2022, 10:45:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 16EC8EAA97A6C1840D9D6EFE648B021C |
| SHA1: | F72904F570A916C4CC4074FFE056D37355CE2AB1 |
| SHA256: | 66953EF52FE1A9B53F893AA94A7BEB8945343993512F418311583CF12C789631 |
| SSDEEP: | 98304:34p6+6efPDU9pOE702rs1ouR9GPZ5HMuOX:7efPDUrx7PSohjHOX |
MALICIOUS
Drops executable file immediately after starts
- rundll32.exe (PID: 2268)
- msiexec.exe (PID: 3784)
Loads dropped or rewritten executable
- rundll32.exe (PID: 2268)
SUSPICIOUS
Checks supported languages
- ScreenConnect.ClientSetup.exe_.exe (PID: 1380)
- msiexec.exe (PID: 844)
- MsiExec.exe (PID: 3724)
- MsiExec.exe (PID: 3964)
- MsiExec.exe (PID: 2352)
Starts Microsoft Installer
- ScreenConnect.ClientSetup.exe_.exe (PID: 1380)
Reads the computer name
- ScreenConnect.ClientSetup.exe_.exe (PID: 1380)
- msiexec.exe (PID: 844)
- MsiExec.exe (PID: 3724)
- MsiExec.exe (PID: 2352)
- MsiExec.exe (PID: 3964)
Executable content was dropped or overwritten
- ScreenConnect.ClientSetup.exe_.exe (PID: 1380)
- msiexec.exe (PID: 3784)
- msiexec.exe (PID: 844)
- rundll32.exe (PID: 2268)
Reads the Windows organization settings
- msiexec.exe (PID: 3784)
- msiexec.exe (PID: 844)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3784)
- msiexec.exe (PID: 844)
Drops a file that was compiled in debug mode
- rundll32.exe (PID: 2268)
- msiexec.exe (PID: 844)
Drops a file with a compile date too recent
- rundll32.exe (PID: 2268)
- msiexec.exe (PID: 844)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3724)
Executed as Windows Service
- vssvc.exe (PID: 2460)
Reads Environment values
- vssvc.exe (PID: 2460)
Creates a directory in Program Files
- msiexec.exe (PID: 844)
Changes default file association
- msiexec.exe (PID: 844)
INFO
Reads the computer name
- msiexec.exe (PID: 3784)
- rundll32.exe (PID: 2268)
- vssvc.exe (PID: 2460)
Checks supported languages
- msiexec.exe (PID: 3784)
- vssvc.exe (PID: 2460)
- rundll32.exe (PID: 2268)
Application launched itself
- msiexec.exe (PID: 844)
Creates files in the program directory
- msiexec.exe (PID: 844)
Creates a software uninstall entry
- msiexec.exe (PID: 844)
Searches for installed software
- msiexec.exe (PID: 844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (53.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (35.5) |
| .exe | | | Win32 Executable (generic) (5.8) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1499 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4049408 |
| CodeSize: | 48640 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2022:02:04 06:49:14+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Feb-2022 05:49:14 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Feb-2022 05:49:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BCE6 | 0x0000BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62079 |
.rdata | 0x0000D000 | 0x00005D68 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8737 |
.data | 0x00013000 | 0x000011E4 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.25909 |
.rsrc | 0x00015000 | 0x003D5234 | 0x003D5400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.24779 |
.reloc | 0x003EB000 | 0x00000ECC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.31471 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
SCREENCONNECT.CORE, VERSION=22.3.7487.8130, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 6.01763 | 451584 | Latin 1 / Western European | UNKNOWN | FILES |
SCREENCONNECT.WINDOWS, VERSION=22.3.7487.8130, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 6.68637 | 1647616 | Latin 1 / Western European | UNKNOWN | FILES |
SCREENCONNECT.WINDOWSINSTALLER, VERSION=22.3.7487.8130, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 5.76345 | 71168 | Latin 1 / Western European | UNKNOWN | FILES |
_ENTRYPOINT | 7.7021 | 1841360 | Latin 1 / Western European | UNKNOWN | FILES |
_RESOLVER | 3.86896 | 5632 | Latin 1 / Western European | UNKNOWN | FILES |
Imports
KERNEL32.dll |
OLEAUT32.dll |
mscoree.dll |
Total processes
42
Monitored processes
8
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\AppData\Local\Temp\ScreenConnect.ClientSetup.exe_.exe" | C:\Users\admin\AppData\Local\Temp\ScreenConnect.ClientSetup.exe_.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2268 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI9968.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1022406 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2352 | C:\Windows\system32\MsiExec.exe -Embedding DF27C2E9CE578EC57103F3C727D70CDF E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3724 | C:\Windows\system32\MsiExec.exe -Embedding CF2231BB17EE27AF8C8189C4C0D918AD C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3784 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\System32\msiexec.exe | ScreenConnect.ClientSetup.exe_.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | C:\Windows\system32\MsiExec.exe -Embedding 0E6E1720DC5EC10E818538FCB679A83C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 347
Read events
3 094
Write events
241
Delete events
12
Modification events
| (PID) Process: | (1380) ScreenConnect.ClientSetup.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1380) ScreenConnect.ClientSetup.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1380) ScreenConnect.ClientSetup.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1380) ScreenConnect.ClientSetup.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (844) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000A87E02775A4ED8014C03000088080000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (844) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000A87E02775A4ED8014C03000088080000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (844) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (844) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000009C8E53775A4ED8014C03000088080000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (844) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009C8E53775A4ED8014C030000F4070000E803000001000000000000000000000086E4457B77407549836C245AA9F170A50000000000000000 | |||
| (PID) Process: | (2460) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AAB55A775A4ED8019C0900002C090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
17
Suspicious files
9
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1380 | ScreenConnect.ClientSetup.exe_.exe | C:\Users\admin\AppData\Local\Temp\setup.msi | executable | |
MD5:— | SHA256:— | |||
| 844 | msiexec.exe | C:\Windows\Installer\fb1e2.msi | executable | |
MD5:— | SHA256:— | |||
| 844 | msiexec.exe | C:\Windows\Installer\fb1e3.ipi | binary | |
MD5:— | SHA256:— | |||
| 844 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{7b45e486-4077-4975-836c-245aa9f170a5}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 844 | msiexec.exe | C:\Windows\Installer\MSIB53D.tmp | binary | |
MD5:— | SHA256:— | |||
| 2268 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI9968.tmp-\CustomAction.config | xml | |
MD5:EB99EE012EB63C162EEBC1DF3A15990B | SHA256:C5045C2D482F71215877EB668264EE47E1415792457F19A5A55651C3554CC7CD | |||
| 844 | msiexec.exe | C:\Windows\Installer\MSIB53E.tmp | executable | |
MD5:BA84DD4E0C1408828CCC1DE09F585EDA | SHA256:3CFF4AC91288A0FF0C13278E73B282A64E83D089C5A61A45D483194AB336B852 | |||
| 844 | msiexec.exe | C:\Program Files\ScreenConnect Client (04d04682e39b30a5)\ScreenConnect.Windows.dll | executable | |
MD5:EE9A6B55F260FCBCECDDE33BCB320E4F | SHA256:FA9AF5BC6B913C84BD55387B854FA16E676102CDF7DBFE30B53A5EC76B68AF35 | |||
| 2268 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI9968.tmp-\ScreenConnect.Core.dll | executable | |
MD5:99EAB5CD79DC04097F1C22E8ED0D840B | SHA256:6B0ADBA76FEF5B60A1CE5C21EF514D1463F31925F415AABB71CA00DE79EB9D4E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report