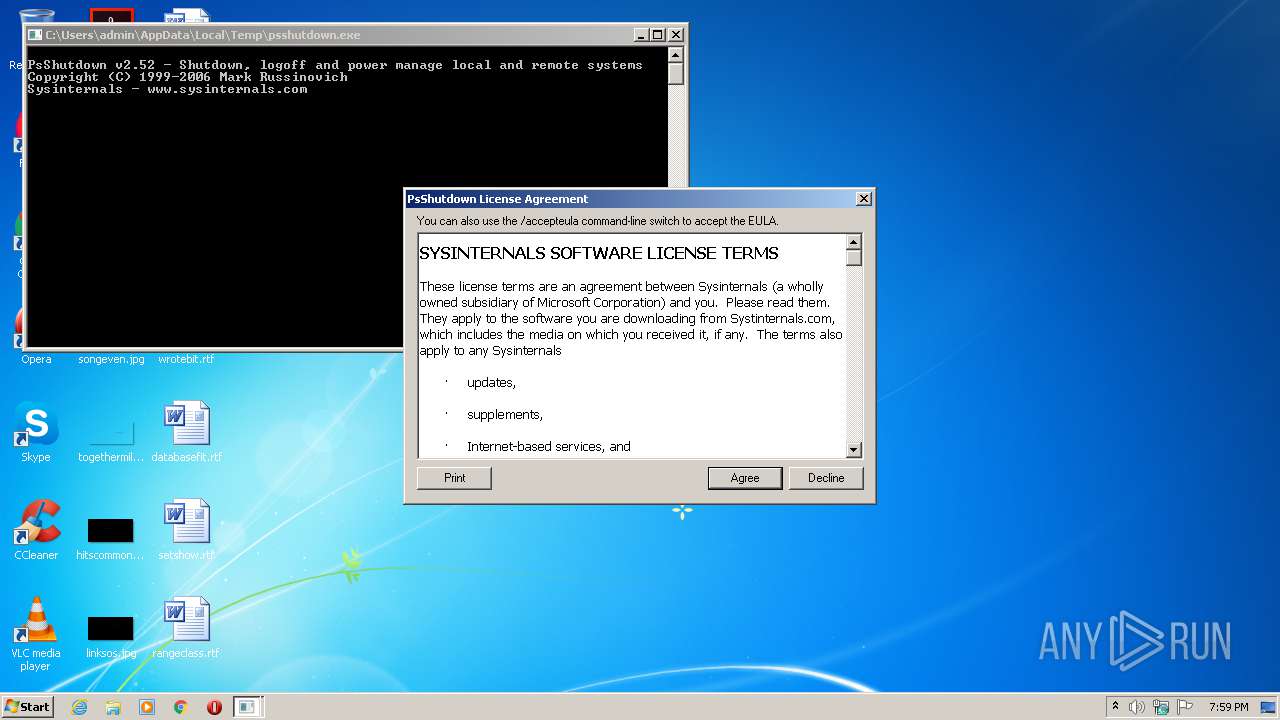
| File name: | psshutdown.exe |
| Full analysis: | https://app.any.run/tasks/15b27318-2be1-4f0d-8c5c-68fef36053c6 |
| Verdict: | No threats detected |
| Analysis date: | August 23, 2020, 18:58:56 |
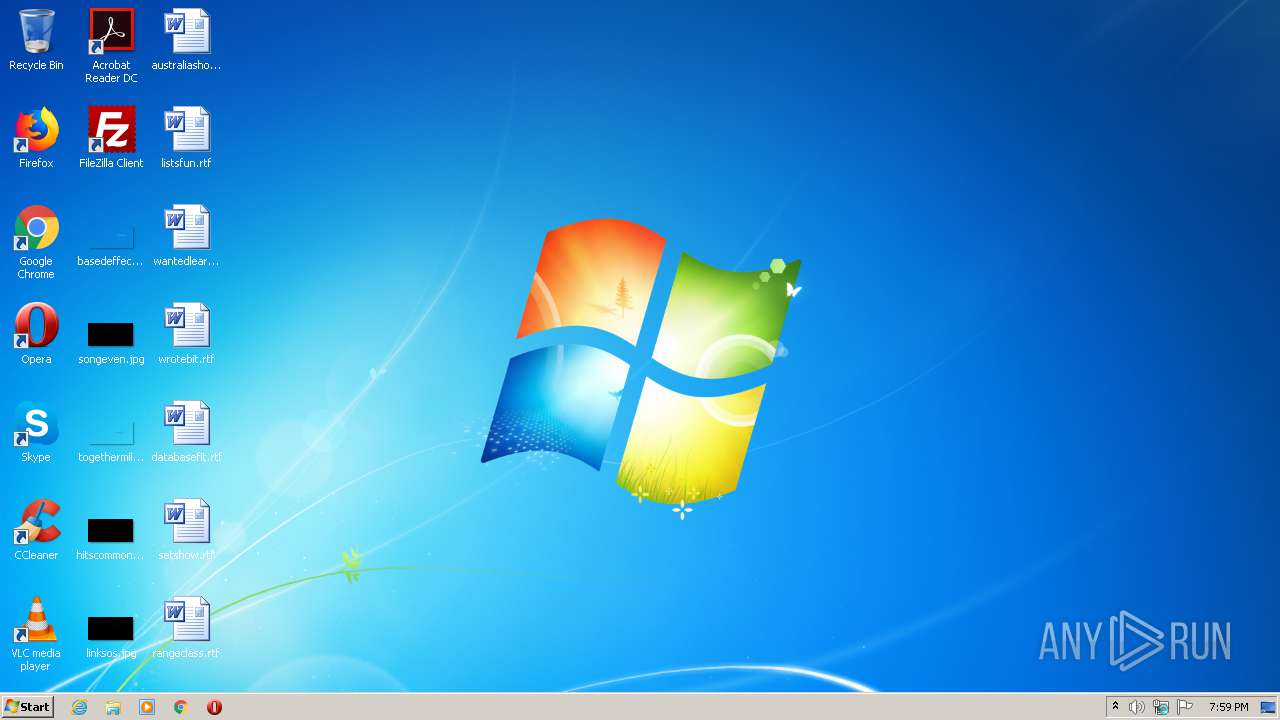
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 6AA0305AF2C055AC6C94B5D24F6CEC35 |
| SHA1: | 1F0A68FA8ABE3ABBEDB2D52B24FD805AEB90F2F1 |
| SHA256: | 66885C2B1773A6D02C3937E67B94B786FC64AF17A7E8BAD050BE5149092A0117 |
| SSDEEP: | 3072:c1j29ITWXL5vjJngtJVcKkPzhwrbttgqWtjW/TxOZ2:ga9IT8hwJkPzhwrHFiW7+2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
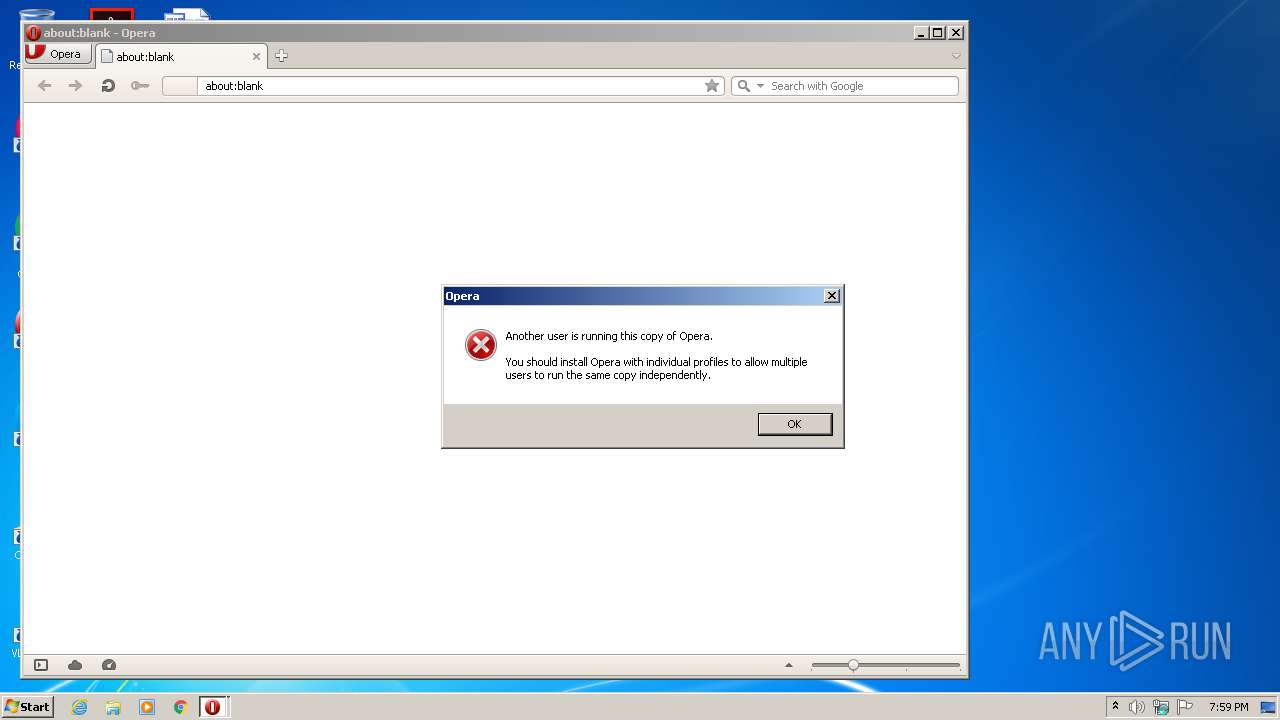
Manual execution by user
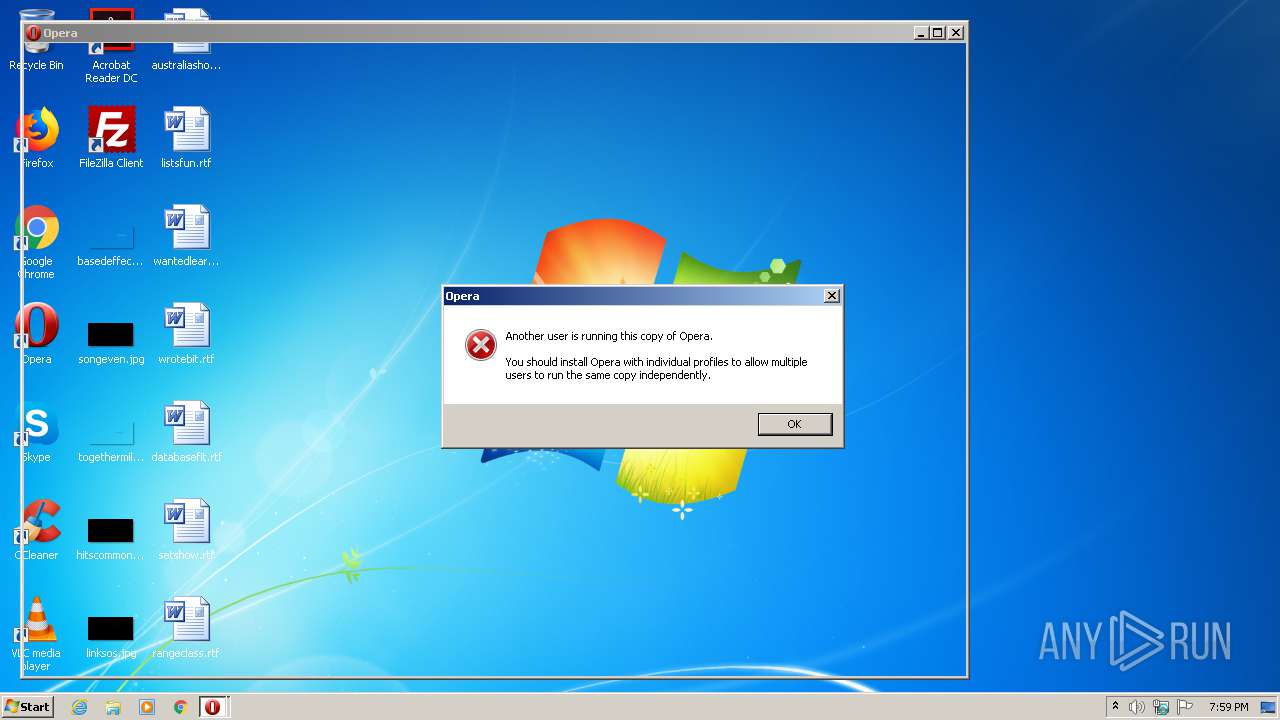
- opera.exe (PID: 3528)
- opera.exe (PID: 2696)
Creates files in the user directory
- opera.exe (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:12:05 01:35:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 69632 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x677f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.52.0.0 |
| ProductVersionNumber: | 2.52.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Sysinternals - www.sysinternals.com |
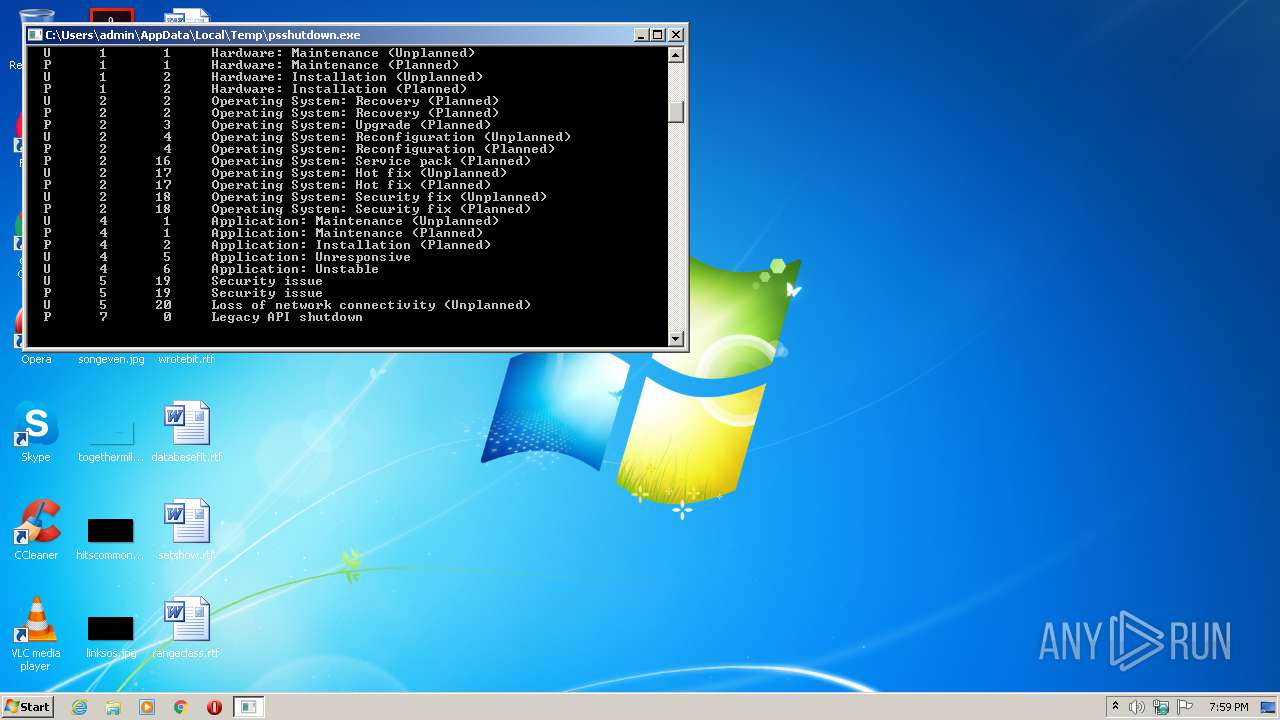
| FileDescription: | Shutdown, logoff and power manage local and remote systems |
| FileVersion: | 2.52 |
| InternalName: | PsShutdown |
| LegalCopyright: | Copyright (C) 1999-2006 Mark Russinovich |
| LegalTrademarks: | - |
| OriginalFileName: | psshutdown.exe |
| PrivateBuild: | - |
| ProductName: | Sysinternals PsShutdown |
| ProductVersion: | 2.52 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 05-Dec-2006 00:35:30 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Shutdown, logoff and power manage local and remote systems |
| FileVersion: | 2.52 |
| InternalName: | PsShutdown |
| LegalCopyright: | Copyright (C) 1999-2006 Mark Russinovich |
| LegalTrademarks: | - |
| OriginalFilename: | psshutdown.exe |
| PrivateBuild: | - |
| ProductName: | Sysinternals PsShutdown |
| ProductVersion: | 2.52 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Dec-2006 00:35:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010198 | 0x00011000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44035 |
.rdata | 0x00012000 | 0x00006708 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00636 |
.data | 0x00019000 | 0x00003864 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42348 |
.rsrc | 0x0001D000 | 0x00015BB4 | 0x00016000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05489 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
PSSHUTDOWNSVC | 6.06536 | 87616 | Latin 1 / Western European | English - United States | BINRES |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
NETAPI32.dll |
USER32.dll |
VERSION.dll |
WS2_32.dll |
comdlg32.dll |
Total processes
43
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2288 | "C:\Users\admin\AppData\Local\Temp\psshutdown.exe" | C:\Users\admin\AppData\Local\Temp\psshutdown.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Shutdown, logoff and power manage local and remote systems Exit code: 4294967295 Version: 2.52 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | — | explorer.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3528 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
323
Read events
209
Write events
114
Delete events
0
Modification events
| (PID) Process: | (2288) psshutdown.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\PsShutdown |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (3528) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3528) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3528) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @"%windir%\System32\ie4uinit.exe",-732 |
Value: Finds and displays information and Web sites on the Internet. | |||
Executable files
0
Suspicious files
34
Text files
9
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr23E.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr26E.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y1T7WJX1ZYLBUE81PUWK.temp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\H03HG0QR5FZPBCTFF27F.temp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr2950.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2960.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2961.tmp | — | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3528 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3528 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3528 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3528 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |