| URL: | apidevst.com |
| Full analysis: | https://app.any.run/tasks/3c61c797-66d9-478a-b41f-ebd70c7b7397 |
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2024, 09:58:58 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 9439BB4C8807F332003BFA4F19D72E26 |
| SHA1: | 4388FF12D3078C3FDC943041D4E55B696A74A92E |
| SHA256: | 667996EF3DB3620E41C215EBDFC472569FC2D8FD5E4B1DBE468228BC85156140 |
| SSDEEP: | 3:8M2Tzn:8M2Tzn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
298
Monitored processes
79
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 9264 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome apidevst\.com " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 9265 | sudo -iu user google-chrome apidevst.com | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 9266 | /usr/bin/google-chrome apidevst.com | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 9267 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9268 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9269 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9270 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9271 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9272 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9273 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9266 | chrome | /9266/fd/63 | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-663B4CEB-2432.pma | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /.com.google.Chrome.EA4EUk | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /.com.google.Chrome.V8CLs0 | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /home/user/.config/google-chrome/Default/Session Storage/LOG | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/LOG | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /home/user/.config/google-chrome/WidevineCdm/.com.google.Chrome.7lTXAc | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /.com.google.Chrome.csJEFR | — | |
MD5:— | SHA256:— | |||
| 9266 | chrome | /.com.google.Chrome.e7VCzr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
16
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.188.55:443 | — | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.58:443 | — | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 31.184.253.65:80 | apidevst.com | OOO Network of data-centers Selectel | RU | unknown |
— | — | 31.184.253.65:443 | apidevst.com | OOO Network of data-centers Selectel | RU | unknown |
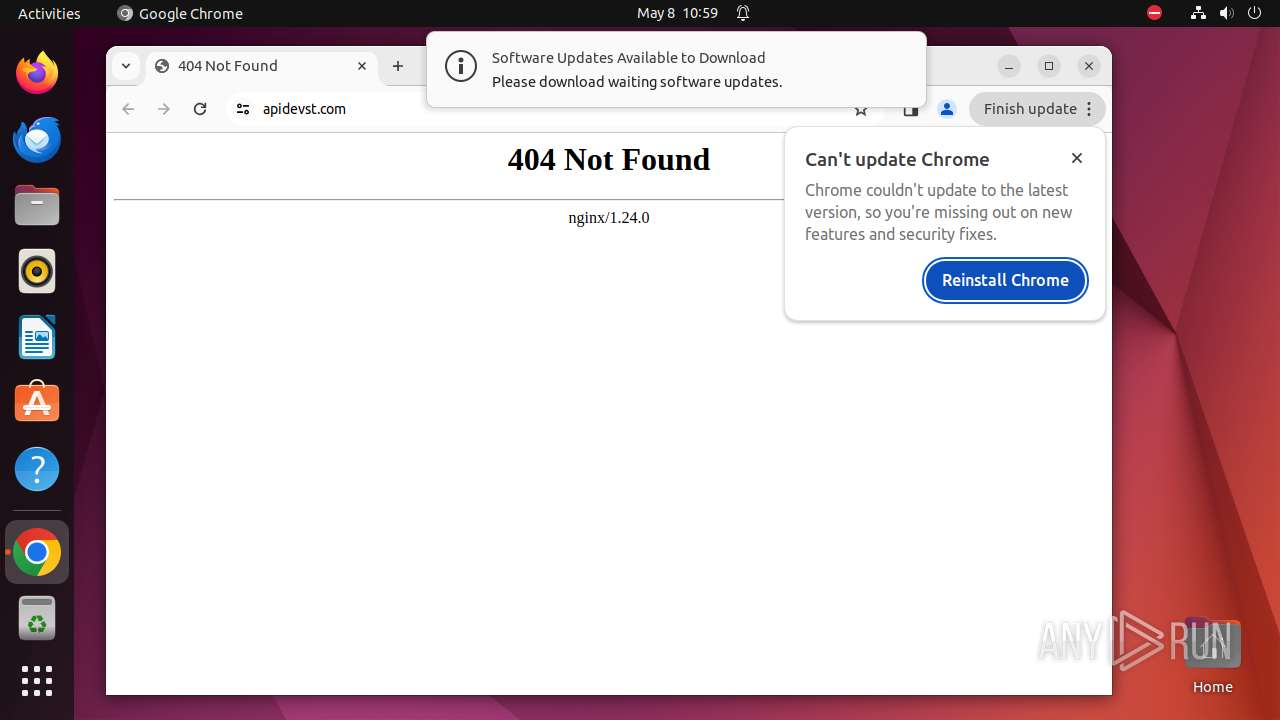
— | — | 172.217.18.99:443 | update.googleapis.com | GOOGLE | US | unknown |
— | — | 216.58.206.68:443 | www.google.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
apidevst.com |
| unknown |
139.100.168.192.in-addr.arpa |
| unknown |
update.googleapis.com |
| unknown |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
connectivity-check.ubuntu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (apidevst .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (apidevst .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in TLS SNI (apidevst .com) |