| File name: | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f |
| Full analysis: | https://app.any.run/tasks/1b8e4f58-20c6-4b87-a231-9c2cbb935fbb |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 19:24:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | DC2A41AE71F851114BBD250858F72760 |
| SHA1: | 46B86A25071076436378318C95D3C9B7C7A779C5 |
| SHA256: | 6678BC6C477241FDA05929D12AA57D80511F56BDE4C16EABA2338B7AE039DD2F |
| SSDEEP: | 49152:ZK9SBi1fdPHdXmy86gsRo3axuS6idyfrnQ2YfxEgpWf4lkl0kp9m65hxE7NyJNfG:USBi1P98I5uS6idaz+5Egpg4VuSklvAT |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6804)
Changes the autorun value in the registry
- pcdxxavbdj.txt (PID: 5880)
SUSPICIOUS
Starts the AutoIt3 executable file
- cmd.exe (PID: 6332)
Starts application with an unusual extension
- cmd.exe (PID: 6332)
Executable content was dropped or overwritten
- 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe (PID: 6516)
- pcdxxavbdj.txt (PID: 5880)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6804)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 6468)
The executable file from the user directory is run by the CMD process
- pcdxxavbdj.txt (PID: 5880)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6804)
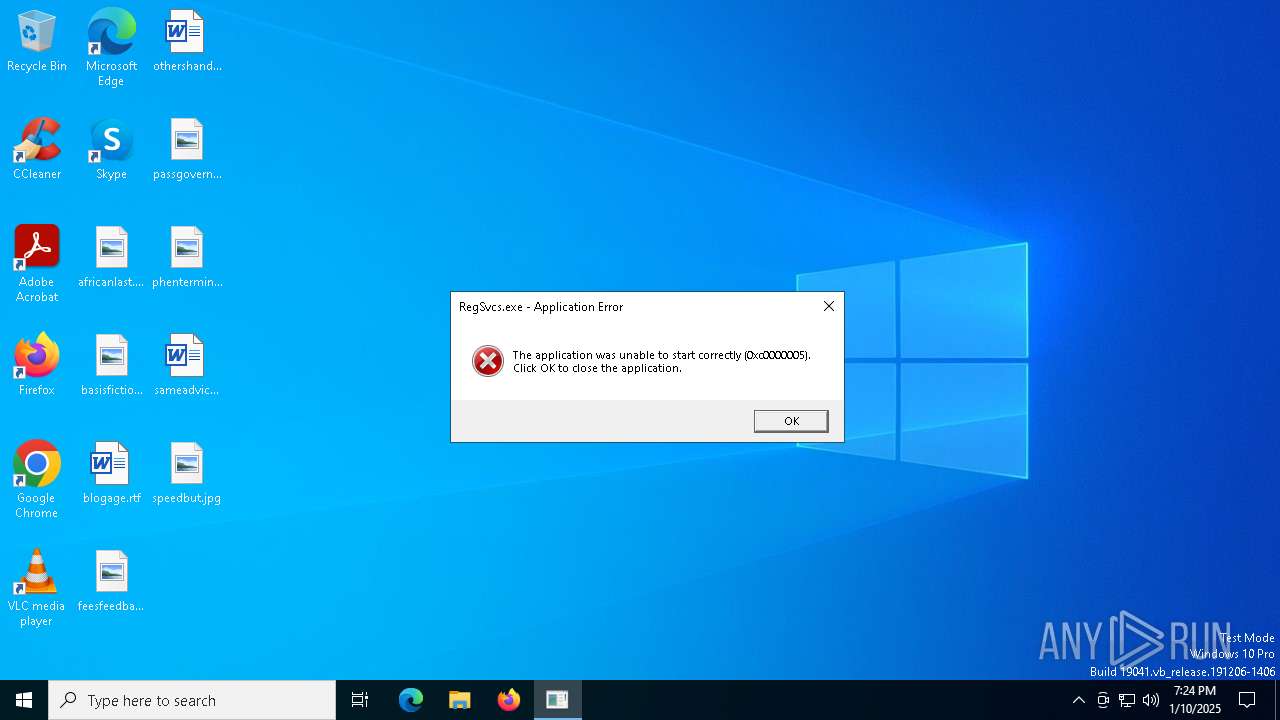
Executes application which crashes
- RegSvcs.exe (PID: 1804)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 5916)
INFO
Reads the computer name
- 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe (PID: 6516)
- pcdxxavbdj.txt (PID: 5880)
Checks supported languages
- 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe (PID: 6516)
- pcdxxavbdj.txt (PID: 5880)
The sample compiled with english language support
- 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe (PID: 6516)
- pcdxxavbdj.txt (PID: 5880)
Reads mouse settings
- pcdxxavbdj.txt (PID: 5880)
Drops encrypted VBS script (Microsoft Script Encoder)
- pcdxxavbdj.txt (PID: 5880)
- 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe (PID: 6516)
Create files in a temporary directory
- pcdxxavbdj.txt (PID: 5880)
The process uses the downloaded file
- wscript.exe (PID: 6804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:12 10:17:03+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 238592 |
| InitializedDataSize: | 150528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x265d0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
144
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | ipconfig /renew | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | pcdxxavbdj.txt | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 3221225477 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4840 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1804 -s 80 | C:\Windows\SysWOW64\WerFault.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4932 | ipconfig /release | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | pcdxxavbdj.txt | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5880 | pcdxxavbdj.txt pwkjcdxt.mp3 | C:\Users\admin\AppData\Local\Temp\RarSFX0\pcdxxavbdj.txt | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 5916 | "C:\Windows\System32\cmd.exe" /c ipconfig /renew | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6332 | "C:\Windows\System32\cmd.exe" /c pcdxxavbdj.txt pwkjcdxt.mp3 | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 132
Read events
2 128
Write events
4
Delete events
0
Modification events
| (PID) Process: | (6516) 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (5880) pcdxxavbdj.txt | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsUpdate |
Value: C:\Users\admin\AppData\Local\Temp\wvkr\PCDXXA~1.EXE C:\Users\admin\AppData\Local\Temp\wvkr\pwkjcdxt.mp3 | |||
Executable files
4
Suspicious files
0
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\pwkjcdxt.mp3 | — | |
MD5:— | SHA256:— | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\evlkwbgow.mp3 | text | |
MD5:2D6418B1F15843F9F9B78CED3736DC43 | SHA256:039BB70B1B489C3115A32734EEE6D2A4C8851C4DE968A319FF206688B31452EF | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\sglbs.pdf | text | |
MD5:213938ED8CED0000AD22092C7F1737AF | SHA256:A0C9FB789C89B3F0E211F9956C5BA9D1CE3FEDC5EC52C5C82EEB0A01A65CB8EF | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\sogqcd.icm | text | |
MD5:58CDAE13A18555582B886807BF997BD5 | SHA256:324DD82D369D8CD70C860A66968D798A98E1A89D2B4383723D5462F4981F454D | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\qwpgwlchj.xl | text | |
MD5:D82B2E3A4A3604E15C75AE6D328B6FA8 | SHA256:3CEA4F255DAB6A13545C165E65B15FCEC2D12A2295DB03D7346CB5224B77BDA1 | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\pcdxxavbdj.txt | executable | |
MD5:0ADB9B817F1DF7807576C2D7068DD931 | SHA256:98E4F904F7DE1644E519D09371B8AFCBBF40FF3BD56D76CE4DF48479A4AB884B | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\mhewb.docx | text | |
MD5:E796A382640B30CF7FCF7ADE79E124AA | SHA256:4503B694B6CF06B4AB6229A2351F1AECCFBD2607613EF5B2594E347F0B427467 | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\kjjxi.bin | text | |
MD5:75CBD97CC613BB2CB2907927714155D5 | SHA256:A692D537CF68353629CC095EE4C98AE8D5CCC04B4F7E70FA2A48952B17560B1A | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\xqlnfmbxbi.das | text | |
MD5:081CD99D971161AD7D3ABECB4C937142 | SHA256:5B12B1C603B885099BB627BA2F036B32EACD5117C7CA8BBB8CFE0BAF4C34CA60 | |||
| 6516 | 6678bc6c477241fda05929d12aa57d80511f56bde4c16eaba2338b7ae039dd2f.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\xfoqwvvfkd.mp2 | text | |
MD5:D0914C6E31B73AD9EB754E22C4987182 | SHA256:E558E701E5EAEF0EFA96D84279E3161D08B0A729BDDB887E0CE7F3269E9911F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4308 | svchost.exe | GET | 200 | 2.16.164.82:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.82:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4308 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4540 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6600 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4540 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2092 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.82:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4308 | svchost.exe | 2.16.164.82:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4308 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1076 | svchost.exe | 2.23.242.9:443 | go.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |