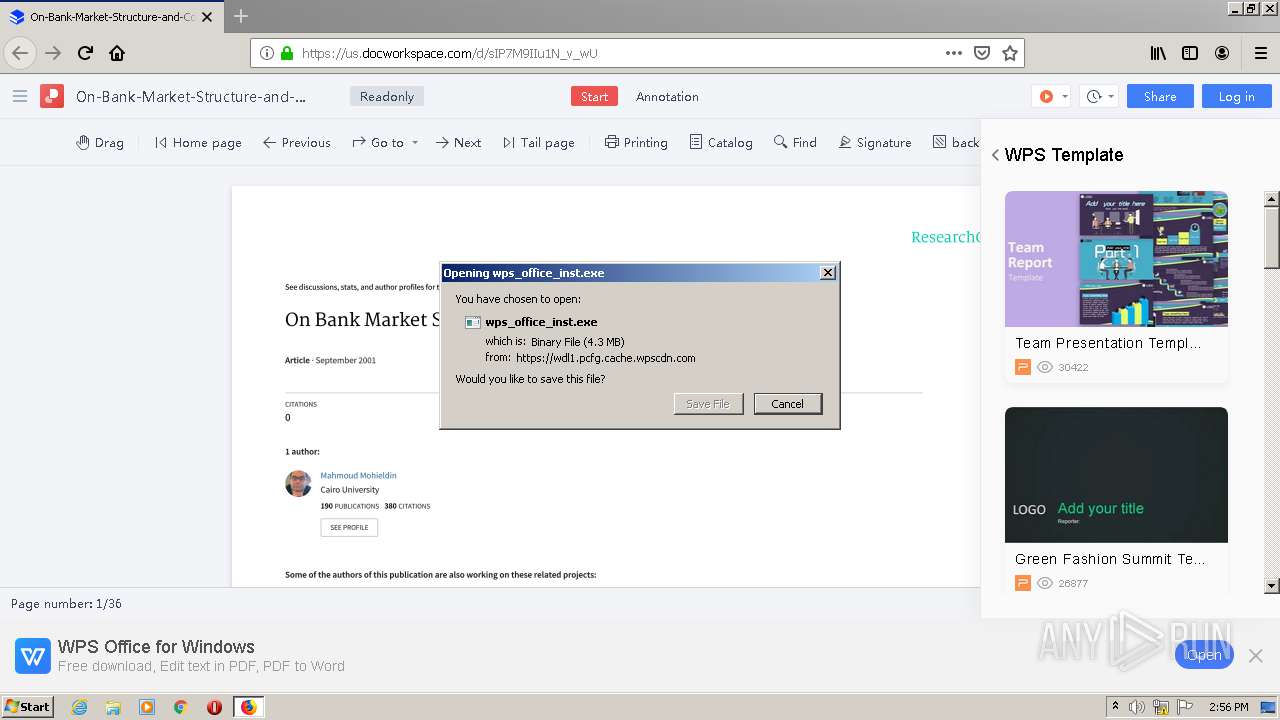
| URL: | https://us.docworkspace.com/d/sIP7M9IIu1N_v_wU |
| Full analysis: | https://app.any.run/tasks/7703e31f-3474-434a-9190-9d861a433206 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2021, 14:54:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C2E39F7469EDE9B90267A139704AD5C1 |
| SHA1: | 10936E59D8A357A90FD0FE4DFFF8EC1D87A96140 |
| SHA256: | 66785500BC752FD68C1F73636F85F83B472CD6254FD808D61F61B4AB3FDEB8D8 |
| SSDEEP: | 3:N8cKeyTaKB15w:2cKe2Bzu |
MALICIOUS
Application was dropped or rewritten from another process
- wps_office_inst.exe (PID: 2848)
- wps_office_inst.exe (PID: 3068)
- wpscloudsvr.exe (PID: 3468)
Changes settings of System certificates
- wps_office_inst.exe (PID: 3068)
Loads dropped or rewritten executable
- setup_urls_default.500.2001.exe (PID: 3164)
- ksomisc.exe (PID: 608)
- ksomisc.exe (PID: 3608)
- ksomisc.exe (PID: 3088)
Drops known malicious document
- setup_urls_default.500.2001.exe (PID: 3164)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 3432)
- setup_urls_default.500.2001.exe (PID: 3164)
Drops a file with a compile date too recent
- firefox.exe (PID: 3432)
- setup_urls_default.500.2001.exe (PID: 3164)
Drops a file that was compiled in debug mode
- firefox.exe (PID: 3432)
- setup_urls_default.500.2001.exe (PID: 3164)
Drops a file with too old compile date
- setup_urls_default.500.2001.exe (PID: 3164)
Application launched itself
- wps_office_inst.exe (PID: 2848)
Creates files in the user directory
- wps_office_inst.exe (PID: 3068)
- setup_urls_default.500.2001.exe (PID: 3164)
- ksomisc.exe (PID: 608)
Adds / modifies Windows certificates
- wps_office_inst.exe (PID: 3068)
Creates files in the program directory
- setup_urls_default.500.2001.exe (PID: 3164)
Low-level read access rights to disk partition
- setup_urls_default.500.2001.exe (PID: 3164)
Creates a software uninstall entry
- setup_urls_default.500.2001.exe (PID: 2948)
Changes default file association
- ksomisc.exe (PID: 3608)
INFO
Application launched itself
- firefox.exe (PID: 1596)
- firefox.exe (PID: 3432)
Reads CPU info
- firefox.exe (PID: 3432)
Creates files in the program directory
- firefox.exe (PID: 3432)
Reads settings of System Certificates
- firefox.exe (PID: 3432)
- wps_office_inst.exe (PID: 2848)
- wps_office_inst.exe (PID: 3068)
- setup_urls_default.500.2001.exe (PID: 3164)
Manual execution by user
- setup_urls_default.500.2001.exe (PID: 2948)
Dropped object may contain Bitcoin addresses
- setup_urls_default.500.2001.exe (PID: 3164)
Creates files in the user directory
- firefox.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
15
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.2.0.9937\office6\ksomisc.exe" -setlng en_US | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.2.0.9937\office6\ksomisc.exe | setup_urls_default.500.2001.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 11,2,0,9937 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://us.docworkspace.com/d/sIP7M9IIu1N_v_wU" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3432.3.910203647\811886648" -childID 1 -isForBrowser -prefsHandle 1728 -prefMapHandle 1740 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3432 "\\.\pipe\gecko-crash-server-pipe.3432" 1340 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3432.0.372324511\756385994" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3432 "\\.\pipe\gecko-crash-server-pipe.3432" 1184 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3432.13.2102580615\1217531168" -childID 2 -isForBrowser -prefsHandle 2900 -prefMapHandle 2904 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3432 "\\.\pipe\gecko-crash-server-pipe.3432" 2916 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3432.20.1930375028\884346923" -childID 3 -isForBrowser -prefsHandle 3684 -prefMapHandle 3688 -prefsLen 7566 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3432 "\\.\pipe\gecko-crash-server-pipe.3432" 3700 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
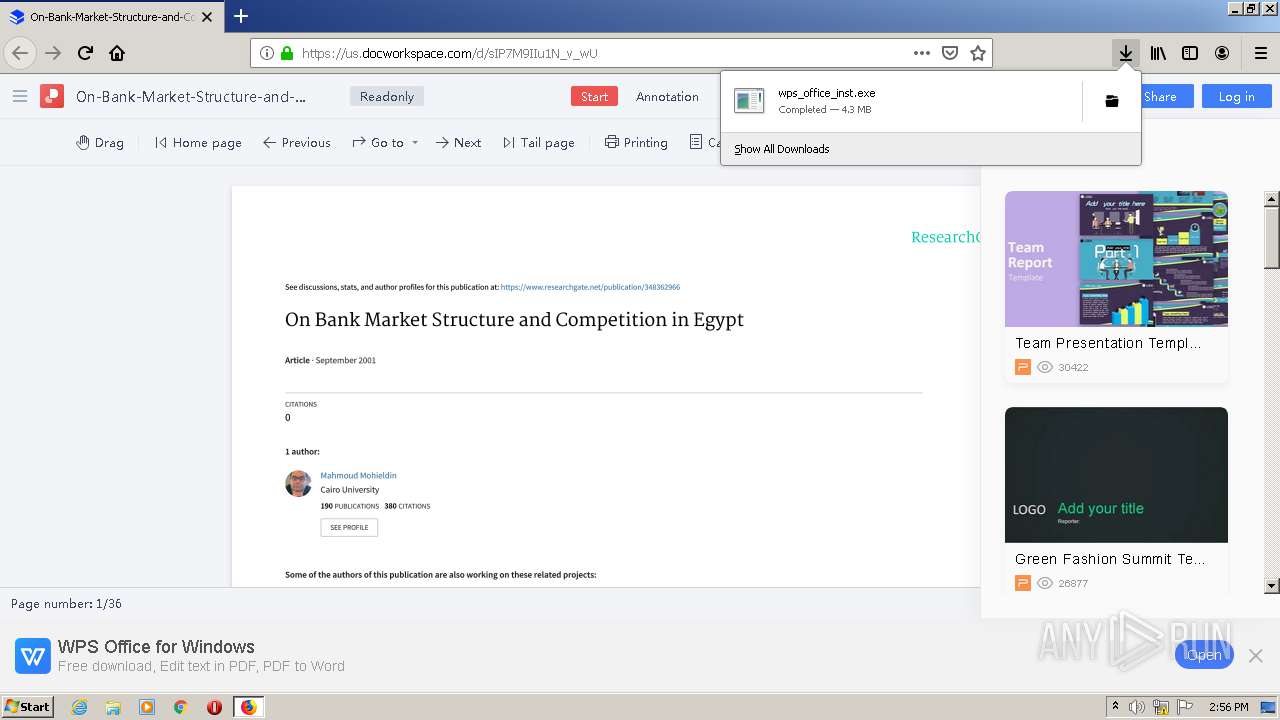
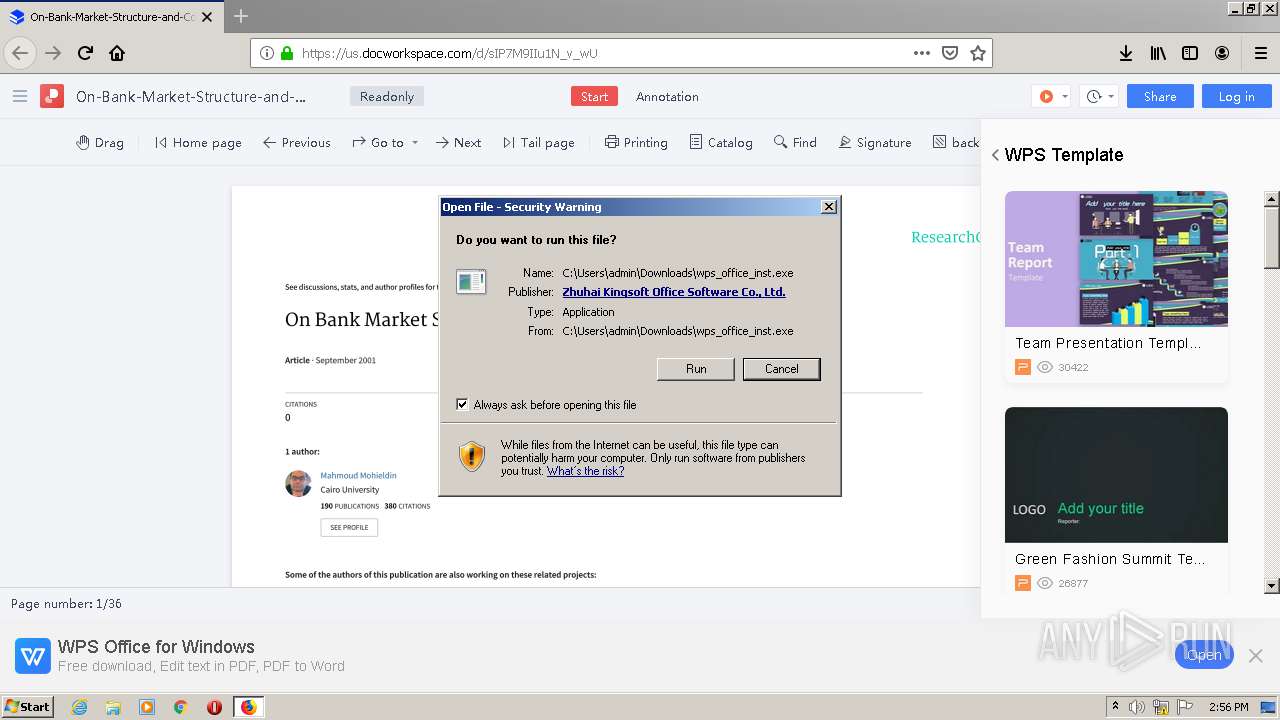
| 2848 | "C:\Users\admin\Downloads\wps_office_inst.exe" | C:\Users\admin\Downloads\wps_office_inst.exe | firefox.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Setup Exit code: 1 Version: 11,2,0,9914 Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\AppData\Roaming\wps_download\28FB25562D28AAA61D9AFA3058FCE874\setup_urls_default.500.2001.exe" -downpower -installCallByOnlineSetup -defaultOpen -defaultOpenPdf -createIcons -curlangofinstalledproduct="en_US" -D="C:\Users\admin\AppData\Local\Kingsoft\WPS Office" -msgwndname=wpssetup_message_163D6B | C:\Users\admin\AppData\Roaming\wps_download\28FB25562D28AAA61D9AFA3058FCE874\setup_urls_default.500.2001.exe | explorer.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Install Application Exit code: 0 Version: 11,2,0,9937 Modules
| |||||||||||||||
| 3068 | "C:\Users\admin\Downloads\wps_office_inst.exe" -upgradepower -fromstartinstall -chkboxModifySystemSettings=checked -chkboxDefaultOpenPdf=checked -chkboxCreateDesktopLink=checked -lang=en_US -installPath="C:\Users\admin\AppData\Local\Kingsoft\WPS Office" | C:\Users\admin\Downloads\wps_office_inst.exe | wps_office_inst.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: HIGH Description: WPS Office Setup Exit code: 0 Version: 11,2,0,9914 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.2.0.9937\office6\ksomisc.exe" -setservers | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.2.0.9937\office6\ksomisc.exe | setup_urls_default.500.2001.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 11,2,0,9937 Modules
| |||||||||||||||
Total events
5 307
Read events
1 364
Write events
3 941
Delete events
2
Modification events
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: D996080201000000 | |||
| (PID) Process: | (1596) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 918A040201000000 | |||
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) wps_office_inst.exe | Key: | HKEY_CURRENT_USER\Software\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | infoGuid |
Value: 83657D53694C402DAC2A1FCCC7529E8C | |||
| (PID) Process: | (2848) wps_office_inst.exe | Key: | HKEY_CURRENT_USER\Software\kingsoft\kwpsonlinesetup |
| Operation: | write | Name: | infoHdid |
Value: 7031ACB87D29089175B554F17076EDFA | |||
Executable files
132
Suspicious files
272
Text files
1 978
Unknown types
375
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3432 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
95
DNS requests
175
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3432 | firefox.exe | POST | 200 | 47.246.43.228:80 | http://ocsp.dcocsp.cn/ | US | der | 471 b | whitelisted |
3432 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
3432 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3432 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3432 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3432 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3432 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3432 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3432 | firefox.exe | POST | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3432 | firefox.exe | POST | 200 | 47.246.43.228:80 | http://ocsp.dcocsp.cn/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3432 | firefox.exe | 44.232.99.182:443 | us.docworkspace.com | University of California, San Diego | US | unknown |
3432 | firefox.exe | 35.167.169.250:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3432 | firefox.exe | 52.37.150.23:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3432 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3432 | firefox.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3432 | firefox.exe | 99.84.144.6:443 | snippets.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
3432 | firefox.exe | 47.246.43.228:80 | ocsp.dcocsp.cn | — | US | malicious |
3432 | firefox.exe | 44.236.112.68:443 | us-weboffice.wps.com | University of California, San Diego | US | unknown |
3432 | firefox.exe | 99.84.144.33:443 | snippets.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
us.docworkspace.com |
| unknown |
alb-kae-docworkspace-1868440764.us-west-2.elb.amazonaws.com |
| unknown |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
Process | Message |
|---|---|
setup_urls_default.500.2001.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_BrandAreaWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_BrandAreaWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_urls_default.500.2001.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|