| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/e0fc4e2e-6e0e-4dcb-b19f-9b482c322e56 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2018, 22:18:44 |
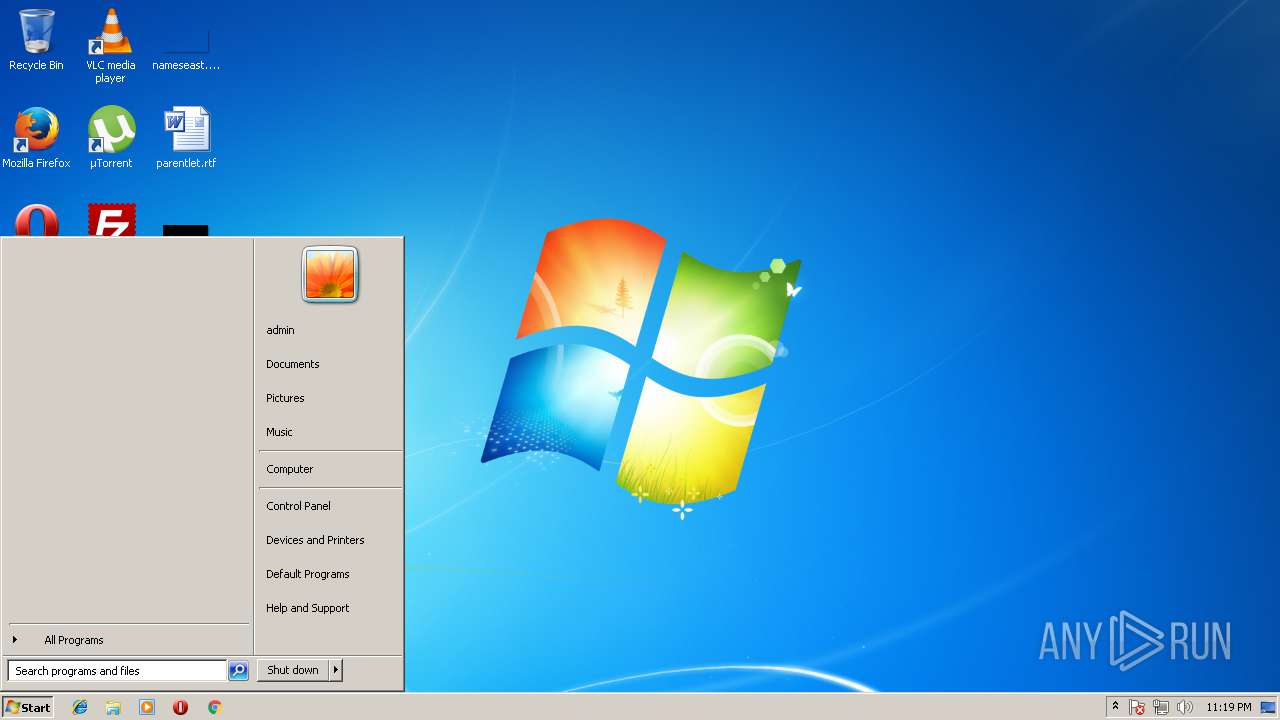
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 1490B6A9000304DA7627B23114480B72 |
| SHA1: | F68D31FE8A30E26531DBD287E07EEC4E89A44E87 |
| SHA256: | 6672C26138F4D85EFC64BA3D3B8952CF7F900380E50F88766443A15AD1D9083F |
| SSDEEP: | 98304:hfz5w7F6ZUSDhQpwpSaFjjM52Pd+WxcSaJW1OhulIDXevzN3vkeBgRLxq8o/0B+y:F9DhhQ+cKpVNrNlODXerN3MHxY0BthX |
MALICIOUS
Application was dropped or rewritten from another process
- crack.exe (PID: 2384)
- crack.exe (PID: 3444)
- patch.exe (PID: 2600)
- patch.exe (PID: 2852)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2272)
- rundll32.exe (PID: 3824)
Loads the Task Scheduler DLL interface
- rundll32.exe (PID: 2272)
- rundll32.exe (PID: 3824)
Application loaded dropped or rewritten executable
- rundll32.exe (PID: 3824)
- rundll32.exe (PID: 2272)
SUSPICIOUS
Starts CMD.EXE for commands execution
- crack.tmp (PID: 3060)
- crack.tmp (PID: 2484)
INFO
Loads rich edit control libraries
- crack.tmp (PID: 2484)
- KMSAuto Net.exe (PID: 1340)
- patch.exe (PID: 2600)
- crack.tmp (PID: 3060)
Dropped object may contain URL's
- crack.exe (PID: 3444)
- crack.exe (PID: 2384)
Application was dropped or rewritten from another process
- crack.tmp (PID: 3060)
- crack.tmp (PID: 2484)
Application loaded dropped or rewritten executable
- crack.tmp (PID: 2484)
- crack.tmp (PID: 3060)
Creates files in the program directory
- crack.tmp (PID: 3060)
- crack.tmp (PID: 2484)
Loads the .NET runtime environment
- patch.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:02:03 20:38:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 169984 |
| InitializedDataSize: | 217600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e64b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Feb-2016 19:38:25 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Feb-2016 19:38:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00029604 | 0x00029800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.7094 |
.rdata | 0x0002B000 | 0x000058A3 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09421 |
.data | 0x00031000 | 0x00021608 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.58964 |
.rsrc | 0x00053000 | 0x0000E13E | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63416 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24978 | 1886 | UNKNOWN | German - Germany | RT_MANIFEST |
2 | 5.29604 | 2216 | UNKNOWN | German - Germany | RT_ICON |
3 | 4.35071 | 1736 | UNKNOWN | German - Germany | RT_ICON |
4 | 3.03007 | 1384 | UNKNOWN | German - Germany | RT_ICON |
5 | 3.79019 | 16936 | UNKNOWN | German - Germany | RT_ICON |
6 | 4.1678 | 9640 | UNKNOWN | German - Germany | RT_ICON |
7 | 3.47493 | 522 | UNKNOWN | German - Germany | RT_STRING |
8 | 3.38062 | 668 | UNKNOWN | German - Germany | RT_STRING |
9 | 3.50179 | 592 | UNKNOWN | German - Germany | RT_STRING |
10 | 3.39224 | 290 | UNKNOWN | German - Germany | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
52
Monitored processes
14
Malicious processes
1
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Users\admin\AppData\Local\Temp\KMSAuto Net.exe" | C:\Users\admin\AppData\Local\Temp\KMSAuto Net.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Local\Temp\KMSAuto Net.exe" | C:\Users\admin\AppData\Local\Temp\KMSAuto Net.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2192 | ping 127.0.0.1 -n 2 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Windows\system32\rundll32.exe" "C:\ProgramData\27784f82383l94738z2\27784f82383l94738z2.dll",ftqflz | C:\Windows\system32\rundll32.exe | — | crack.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\crack.exe" /VERYSILENT /password=123 /subid=landing4 | C:\Users\admin\AppData\Local\Temp\RarSFX1\crack.exe | patch.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup Setup Exit code: 0 Version: 23.0.0.5 Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Temp\is-U27U3.tmp\crack.tmp" /SL5="$1015C,1082646,57856,C:\Users\admin\AppData\Local\Temp\RarSFX0\crack.exe" /VERYSILENT /password=123 /subid=landing5 | C:\Users\admin\AppData\Local\Temp\is-U27U3.tmp\crack.tmp | crack.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\patch.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\patch.exe | KMSAuto Net.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2824 | ping 127.0.0.1 -n 2 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\patch.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\patch.exe | — | patch.exe | |||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMSAuto Net Exit code: 0 Version: 1.4.9 Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\AppData\Local\Temp\is-S6V5V.tmp\crack.tmp" /SL5="$30178,1061314,57856,C:\Users\admin\AppData\Local\Temp\RarSFX1\crack.exe" /VERYSILENT /password=123 /subid=landing4 | C:\Users\admin\AppData\Local\Temp\is-S6V5V.tmp\crack.tmp | crack.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
878
Read events
869
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1340) KMSAuto Net.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1340) KMSAuto Net.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2484) crack.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2600) patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2600) patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
10
Suspicious files
10
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | crack.tmp | C:\ProgramData\776o72c3w8717\is-F24FP.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | crack.tmp | C:\ProgramData\776o72c3w8717\is-JPSSR.tmp | — | |
MD5:— | SHA256:— | |||
| 3060 | crack.tmp | C:\ProgramData\27784f82383l94738z2\is-N8KHO.tmp | — | |
MD5:— | SHA256:— | |||
| 3060 | crack.tmp | C:\ProgramData\27784f82383l94738z2\is-T93QD.tmp | — | |
MD5:— | SHA256:— | |||
| 1340 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crack.exe | executable | |
MD5:— | SHA256:— | |||
| 1340 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\patch.exe | executable | |
MD5:— | SHA256:— | |||
| 2484 | crack.tmp | C:\ProgramData\776o72c3w8717\169.tmp | binary | |
MD5:— | SHA256:— | |||
| 3824 | rundll32.exe | C:\ProgramData\776o72c3w8717\169.tmp | binary | |
MD5:— | SHA256:— | |||
| 2484 | crack.tmp | C:\ProgramData\776o72c3w8717\776o72c3w8717.dll | executable | |
MD5:— | SHA256:— | |||
| 2600 | patch.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\crack.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 111.90.145.100:80 | http://cdn2dload.com/aff/?a=track&id=1&subid=landing5 | MY | — | — | unknown |
— | — | GET | 200 | 111.90.145.100:80 | http://cdn2dload.com/aff/?a=track&id=1&subid=landing4 | MY | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 111.90.145.100:80 | cdn2dload.com | Shinjiru Technology Sdn Bhd | MY | unknown |
— | — | 111.90.145.100:51568 | cdn2dload.com | Shinjiru Technology Sdn Bhd | MY | unknown |
— | — | 103.52.117.70:9822 | — | Colocation Australia Pty Ltd | AU | unknown |
— | — | 221.133.9.29:40360 | — | Saigon Postel Corporation | VN | unknown |
— | — | 93.78.253.165:8594 | — | Volia | UA | unknown |
— | — | 24.216.216.71:11582 | — | Charter Communications | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn2dload.com |
| unknown |
webf.linkpc.net |
| malicious |