| File name: | doc.rtf |
| Full analysis: | https://app.any.run/tasks/959785fc-2da2-451a-a26f-c124e3bdc41a |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 13:21:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, ANSI |
| MD5: | 59FFE4835A14C7A1A32B94D2F07769A9 |
| SHA1: | 6159A9D0EAE4640F9A1721098B87A84E14FC3AED |
| SHA256: | 665D8739E265D1AA9AD056A9EB4A3C194F28C41E0B2A065EFFAF6289E14752E8 |
| SSDEEP: | 24576:e1xQwFUYTIHZhxM2vlddNDdLoZGkc2yjGmYsOHhlG+JqIon4GgQf2X05LtjMw9v0:w |
MALICIOUS
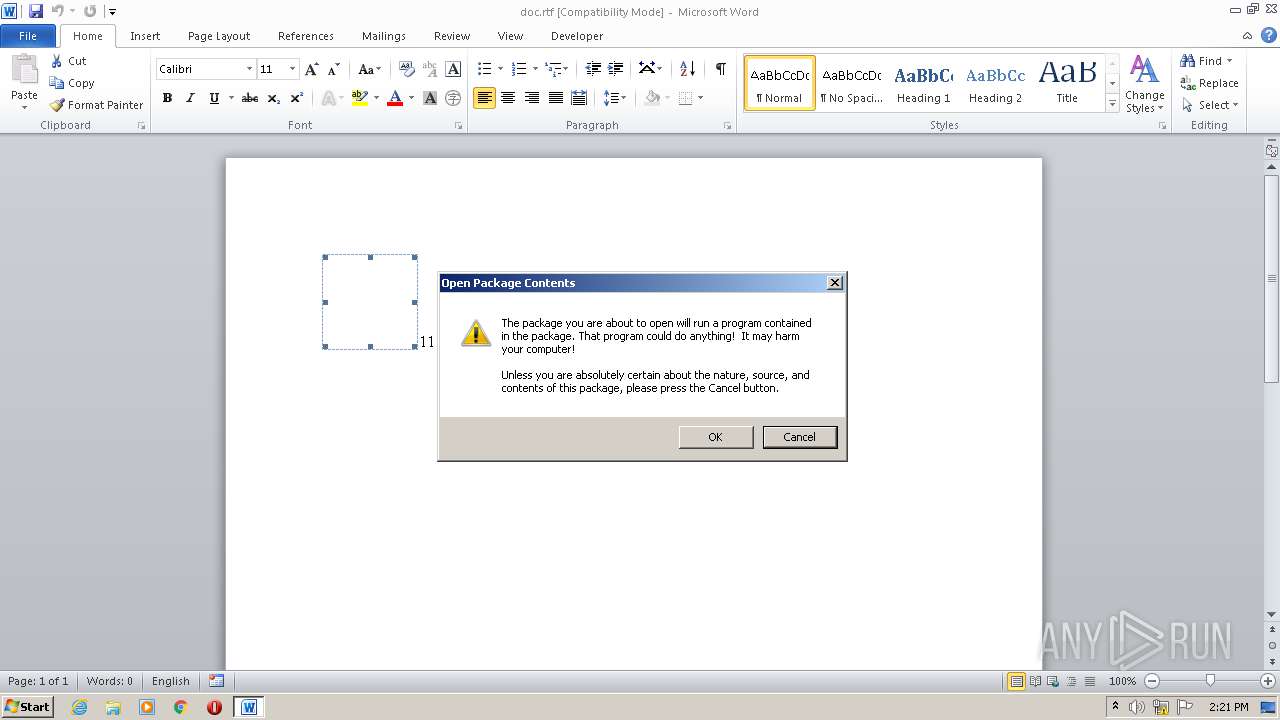
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2208)
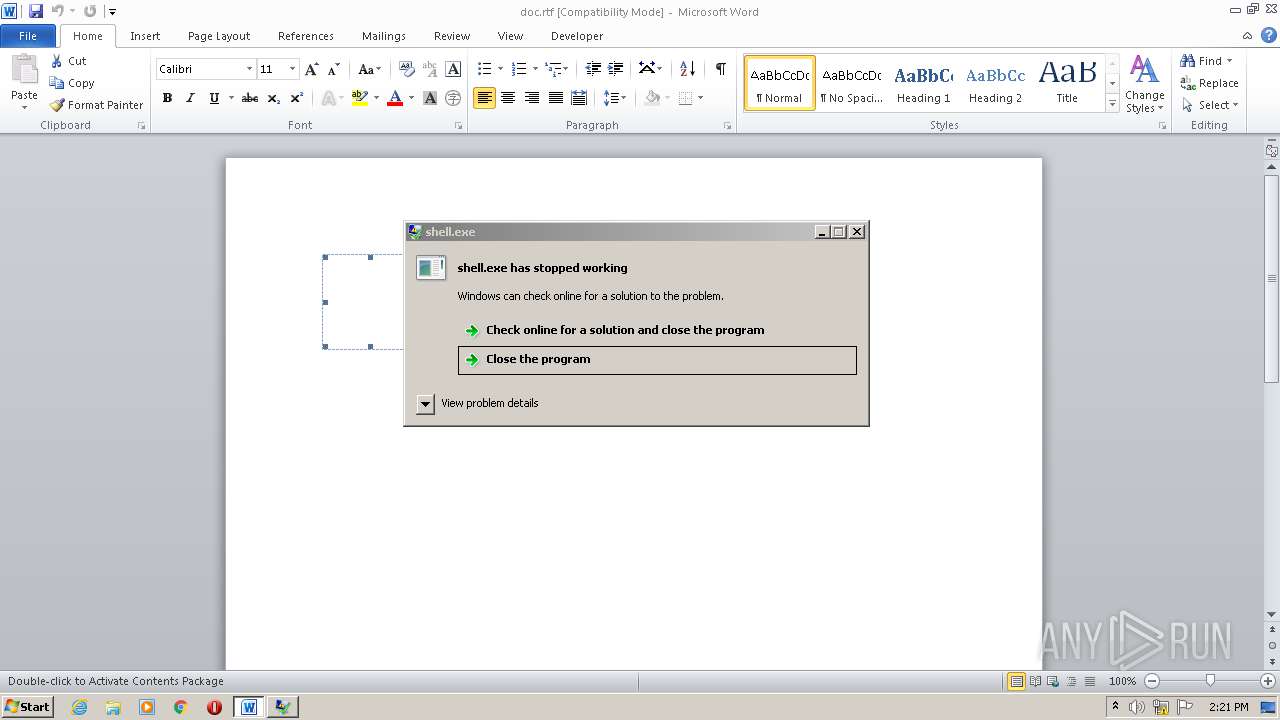
Application was dropped or rewritten from another process
- shell.exe (PID: 2568)
- shell.exe (PID: 2372)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2208)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 1764)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2208)
Creates files in the user directory
- WINWORD.EXE (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1764 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\AppData\Local\Temp\shell.exe" | C:\Users\admin\AppData\Local\Temp\shell.exe | — | WINWORD.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\shell.exe" | C:\Users\admin\AppData\Local\Temp\shell.exe | WINWORD.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225620 Modules
| |||||||||||||||
Total events
1 861
Read events
1 059
Write events
665
Delete events
137
Modification events
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2dd |
Value: 32646400A0080000010000000000000000000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7CA3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\shell.exe | executable | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\991A21E6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB22CD39.wmf | wmf | |
MD5:95BB648D6EB9265EEAF0F889731B1E23 | SHA256:9639441A9D36E7E4FDA980961B75EEB334540B8CFBCEE71EB3CD857E0A838E0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report