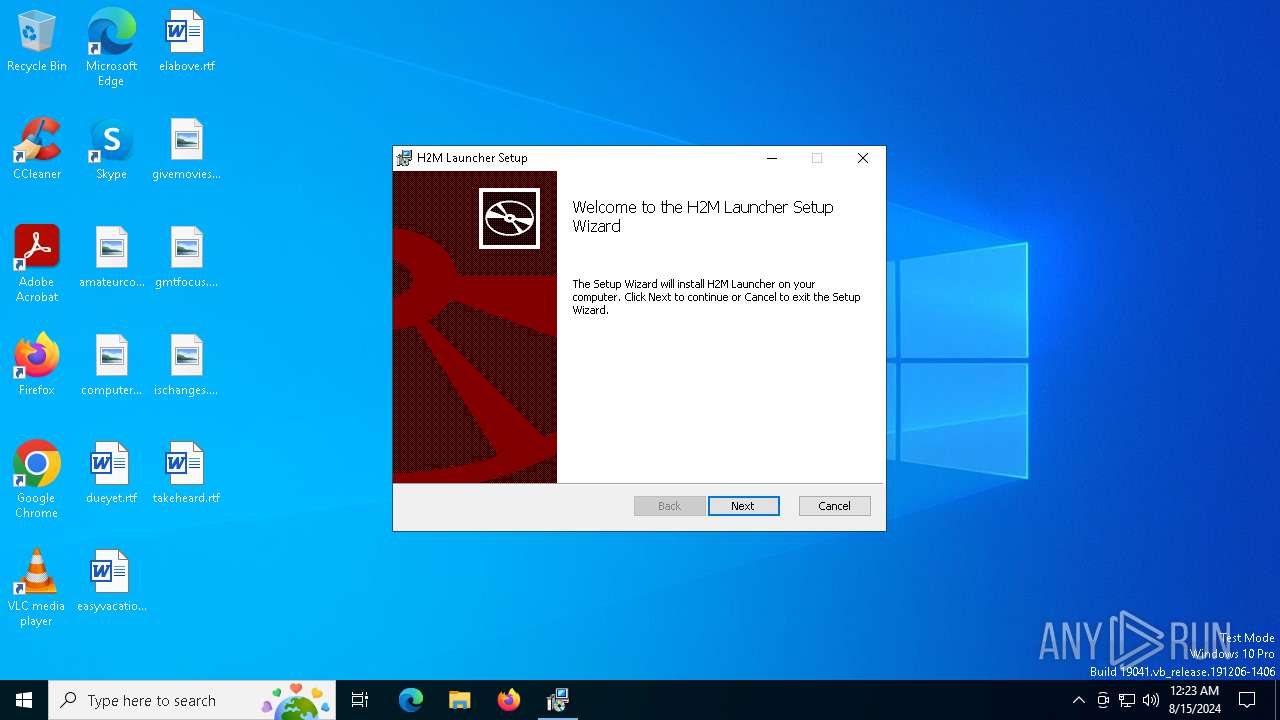
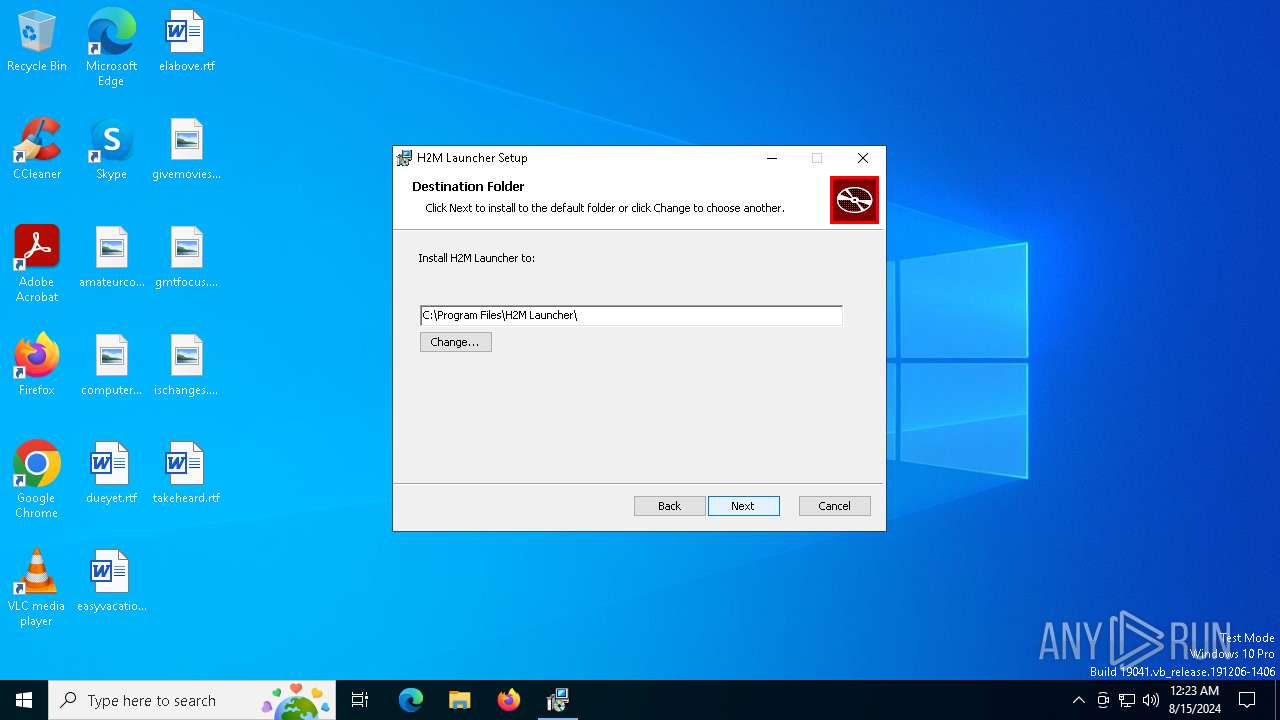
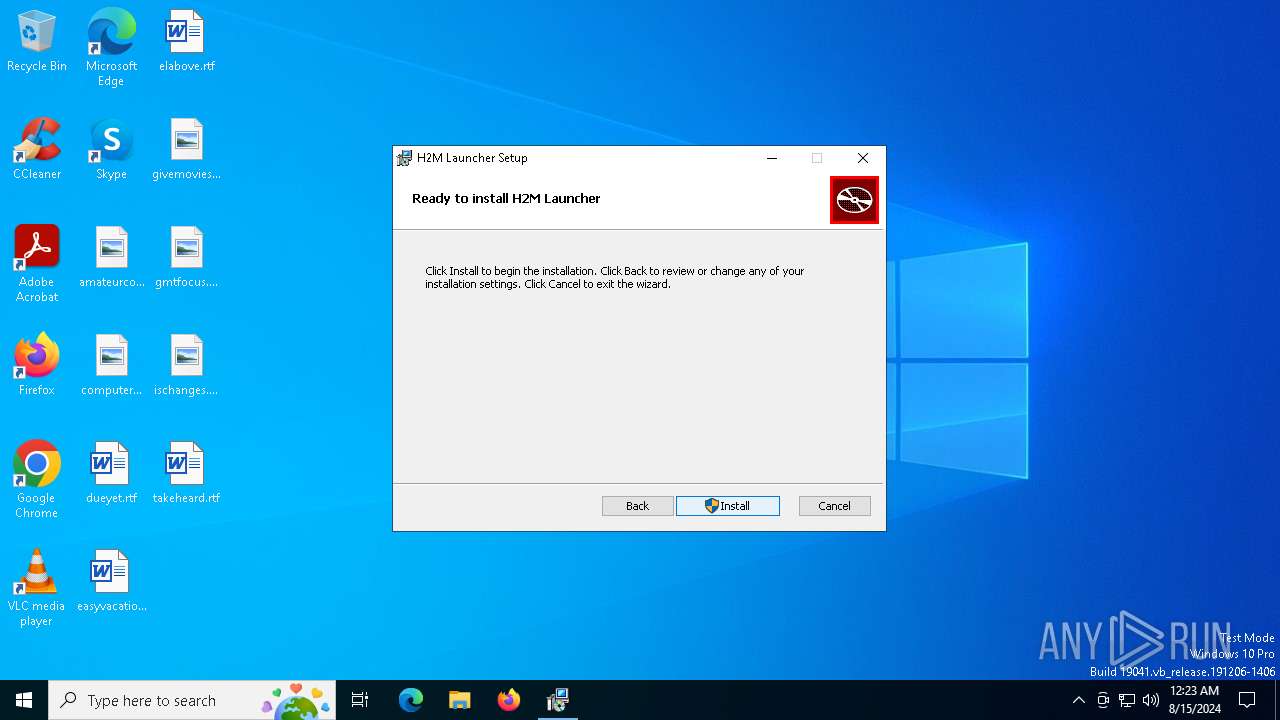
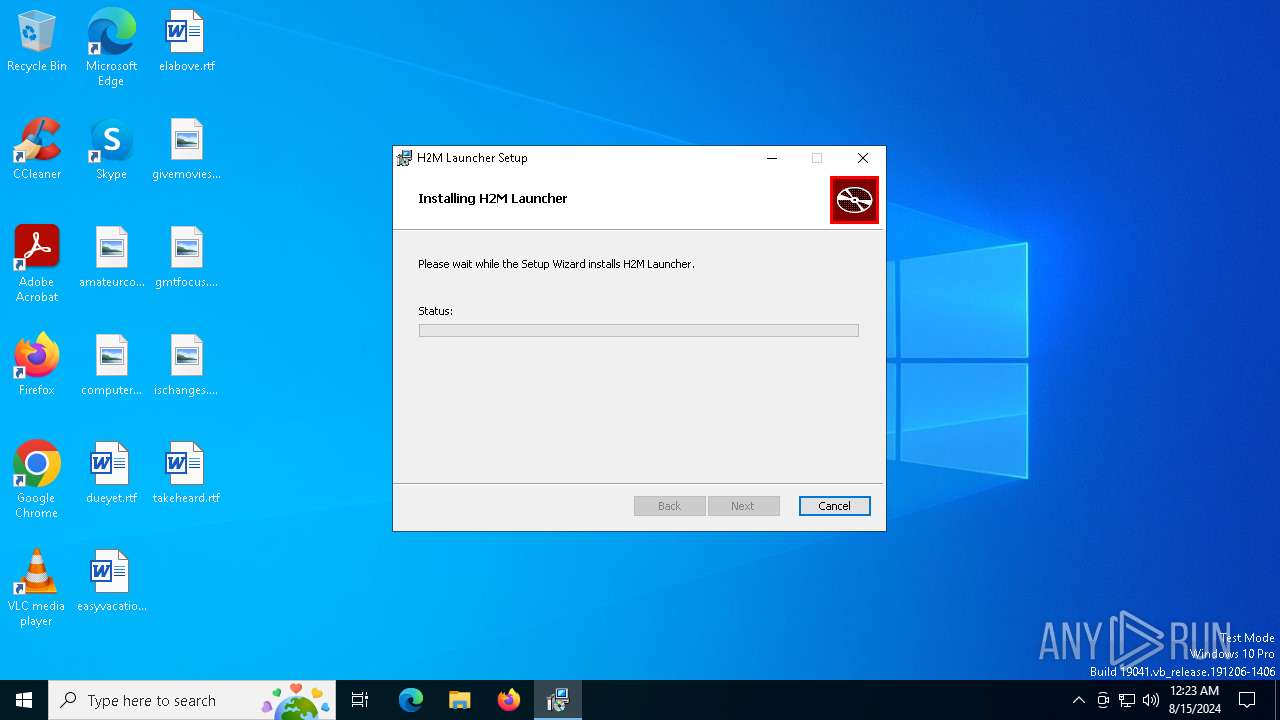
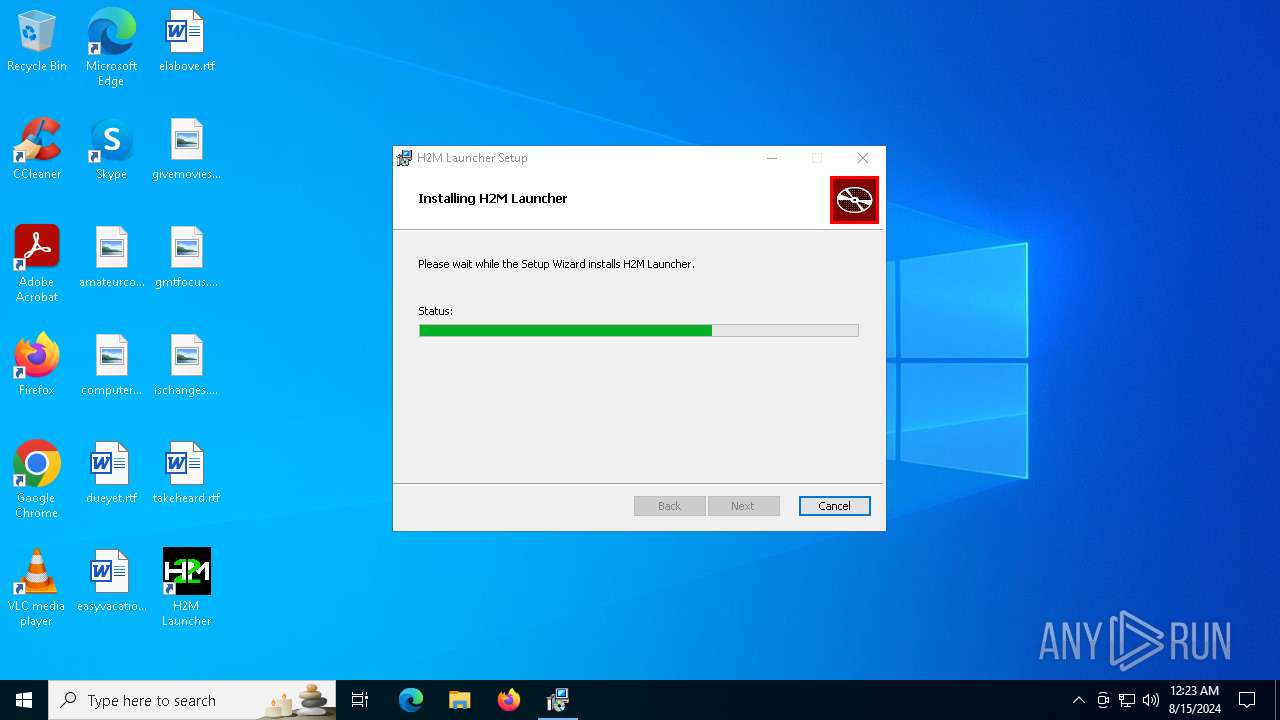
| File name: | H2M Launcher_0.12.0_x64_en-US (1).msi |
| Full analysis: | https://app.any.run/tasks/5f280f32-45ca-464d-91c2-63eea8f4ba33 |
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2024, 00:23:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: H2M Launcher, Author: h2m, Keywords: Installer, Comments: This installer database contains the logic and data required to install H2M Launcher., Template: x64;0, Revision Number: {F1B947B5-A93B-4494-A1B2-21F82EB56DB3}, Create Time/Date: Tue Aug 13 15:41:42 2024, Last Saved Time/Date: Tue Aug 13 15:41:42 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 8D970001C7E13B7E3CC4FD3A025A1770 |
| SHA1: | 38C1252823985EB212E2A8BFDAED2DF2D555B67D |
| SHA256: | 6659E4A6A0327DFA5D2580CA37B3E628FB4ADF9031C107E3209CAD1D9B29E711 |
| SSDEEP: | 98304:0U7xXeoD5s0NufVDmoYG4foCC9Z9V/153FM/kJmlZgEv0FPNIqNsyodi3e986VoK:xJ5sy+hBPHhxFRKSslHA |
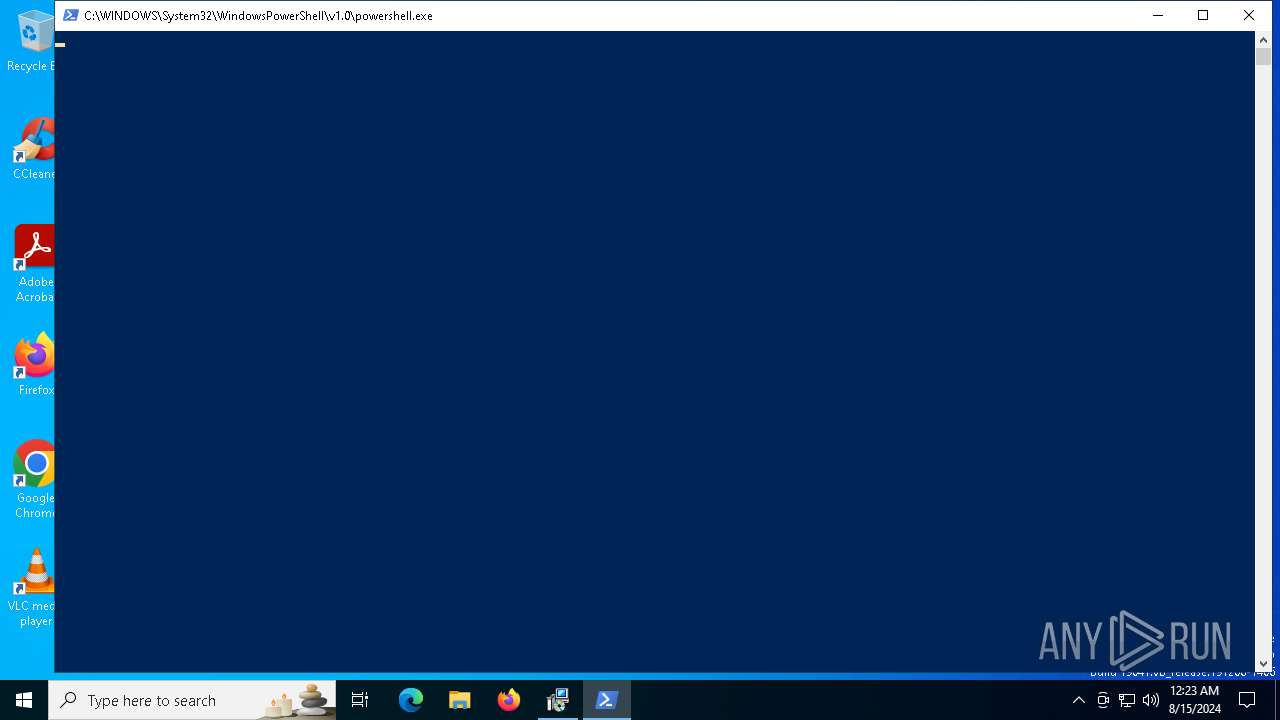
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6256)
SUSPICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 6492)
- msiexec.exe (PID: 6600)
- powershell.exe (PID: 6256)
- MicrosoftEdgeWebview2Setup.exe (PID: 1044)
- MicrosoftEdgeUpdate.exe (PID: 4592)
Executes as Windows Service
- VSSVC.exe (PID: 6732)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6600)
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 6600)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6600)
Powershell scripting: start process
- msiexec.exe (PID: 6600)
Downloads file from URI
- powershell.exe (PID: 6256)
Executable content was dropped or overwritten
- powershell.exe (PID: 6256)
- MicrosoftEdgeWebview2Setup.exe (PID: 1044)
- MicrosoftEdgeUpdate.exe (PID: 4592)
Process drops legitimate windows executable
- powershell.exe (PID: 6256)
- MicrosoftEdgeWebview2Setup.exe (PID: 1044)
- MicrosoftEdgeUpdate.exe (PID: 4592)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 1044)
- MicrosoftEdgeUpdate.exe (PID: 4592)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 4592)
INFO
Reads the computer name
- msiexec.exe (PID: 6600)
- msiexec.exe (PID: 6680)
Checks supported languages
- msiexec.exe (PID: 6680)
- msiexec.exe (PID: 6600)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6492)
- msiexec.exe (PID: 6600)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 1044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | H2M Launcher |
| Author: | h2m |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install H2M Launcher. |
| Template: | x64;0 |
| RevisionNumber: | {F1B947B5-A93B-4494-A1B2-21F82EB56DB3} |
| CreateDate: | 2024:08:13 15:41:42 |
| ModifyDate: | 2024:08:13 15:41:42 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
150
Monitored processes
17
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.195.15 | |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.15 | |||||||||||||||
| 4088 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.15\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.15\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.15 | |||||||||||||||
| 4592 | C:\Users\admin\AppData\Local\Temp\EUBD70.tmp\MicrosoftEdgeUpdate.exe /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EUBD70.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.15 | |||||||||||||||
| 4604 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4xOTUuMTUiIHNoZWxsX3ZlcnNpb249IjEuMy4xOTUuMTUiIGlzbWFjaGluZT0iMCIgc2Vzc2lvbmlkPSJ7ODNDMzYwNUQtNTAzMS00MTZFLUEyNTQtQzk2QkIyOEMxNDc3fSIgdXNlcmlkPSJ7QTBFMzE5RjMtQ0UzNi00MDAyLTg3QzQtOUY5RDFDMUJFMDZEfSIgaW5zdGFsbHNvdXJjZT0ib3RoZXJpbnN0YWxsY21kIiByZXF1ZXN0aWQ9InsxOTcyRUZGRC04QjUyLTQ0QTgtOTY3Qy0wRjA2MkJFRTREQTF9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IGxvZ2ljYWxfY3B1cz0iNCIgcGh5c21lbW9yeT0iNCIgZGlza190eXBlPSIyIiBzc2U9IjEiIHNzZTI9IjEiIHNzZTM9IjEiIHNzc2UzPSIxIiBzc2U0MT0iMSIgc3NlNDI9IjEiIGF2eD0iMSIvPjxvcyBwbGF0Zm9ybT0id2luIiB2ZXJzaW9uPSIxMC4wLjE5MDQ1LjQwNDYiIHNwPSIiIGFyY2g9Ing2NCIgcHJvZHVjdF90eXBlPSI0OCIgaXNfd2lwPSIwIiBpc19pbl9sb2NrZG93bl9tb2RlPSIwIi8-PG9lbSBwcm9kdWN0X21hbnVmYWN0dXJlcj0iREVMTCIgcHJvZHVjdF9uYW1lPSJERUxMIi8-PGV4cCBldGFnPSIiLz48YXBwIGFwcGlkPSJ7RjNDNEZFMDAtRUZENS00MDNCLTk1NjktMzk4QTIwRjFCQTRBfSIgdmVyc2lvbj0iIiBuZXh0dmVyc2lvbj0iMS4zLjE5NS4xNSIgbGFuZz0iIiBicmFuZD0iIiBjbGllbnQ9IiI-PGV2ZW50IGV2ZW50dHlwZT0iMiIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIgc3lzdGVtX3VwdGltZV90aWNrcz0iOTY4MDYwMDgxMyIgaW5zdGFsbF90aW1lX21zPSI3MTgiLz48L2FwcD48L3JlcXVlc3Q- | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.15 | |||||||||||||||
| 4920 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{83C3605D-5031-416E-A254-C96BB28C1477}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.15 | |||||||||||||||
| 4924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5388 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.15\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.15\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.15 | |||||||||||||||
| 6184 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.15\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.15\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.15 | |||||||||||||||
Total events
3 062
Read events
2 898
Write events
154
Delete events
10
Modification events
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000C575B055A9EEDA01C81900003C1A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000C575B055A9EEDA01C81900003C1A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000CFA1F555A9EEDA01C81900003C1A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000CFA1F555A9EEDA01C81900003C1A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000456AFA55A9EEDA01C81900003C1A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000004931FF55A9EEDA01C81900003C1A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000087DE6C56A9EEDA01C81900003C1A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6600) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000055436F56A9EEDA01C8190000C01A0000E80300000100000000000000000000005CFE757A5A013649B6EE2AB435CB467800000000000000000000000000000000 | |||
| (PID) Process: | (6732) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000086237B56A9EEDA014C1A00007C1A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
204
Suspicious files
12
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6600 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6600 | msiexec.exe | C:\Windows\Installer\ea062.msi | — | |
MD5:— | SHA256:— | |||
| 6600 | msiexec.exe | C:\Windows\Installer\ea064.msi | — | |
MD5:— | SHA256:— | |||
| 6600 | msiexec.exe | C:\Windows\Installer\{9E4D2DE9-2006-4A7E-B70E-3EDD52929379}\ProductIcon | image | |
MD5:8606D0F1F472BC892BE079EB357784B5 | SHA256:3A02F2C4E518F1A9C93C8C6F54B35BD3CACEF38841CF1A1DAC86FC669D446199 | |||
| 6492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI63B7.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 6600 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\H2M Launcher\H2M Launcher.lnk | lnk | |
MD5:3D3F3D4DEE707039D8187194A0131053 | SHA256:41C7C8268443BD17A94C5C3039ACE5744255E708A5CE6F06E5B6EE88C94A1705 | |||
| 6600 | msiexec.exe | C:\Windows\Installer\MSIA515.tmp | binary | |
MD5:7B83933809711BB82E9EB07BE7178AB1 | SHA256:253BD5C84D4ADCB61A9CBBEFCA7D5729062967687833446CA10E8FFA43F050CE | |||
| 6600 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{7a75fe5c-015a-4936-b6ee-2ab435cb4678}_OnDiskSnapshotProp | binary | |
MD5:A0AA00BEFA1C09B3B6A9F3DCBEC1EA5B | SHA256:27CAE3453D6427283D592B401F45DECC5D592A9BC5B74969E2017874E1A5F107 | |||
| 6600 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:3DAACDF9F243B713DC4D69917D5A8B17 | SHA256:BF3A9BC59516A15FB871AB4E1CD766770239176FF7F456AE387F0917E9D539D3 | |||
| 6600 | msiexec.exe | C:\Windows\Temp\~DF91E0087DB1F444D0.TMP | binary | |
MD5:3DAACDF9F243B713DC4D69917D5A8B17 | SHA256:BF3A9BC59516A15FB871AB4E1CD766770239176FF7F456AE387F0917E9D539D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
51
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7096 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7144 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | — | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/529a41cd-5c0c-4cd0-8061-b71feaa8a336?P1=1724286226&P2=404&P3=2&P4=DO%2fwqNt0eY3OQ5E9lLWpWJ9x9yl%2bgbSTe%2f5%2feN8U5ohhmO5c70Il7%2bhskTTS9yBrsUr%2bW213DGo%2bENEBC9Btgw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1120 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5388 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5336 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3376 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3376 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |