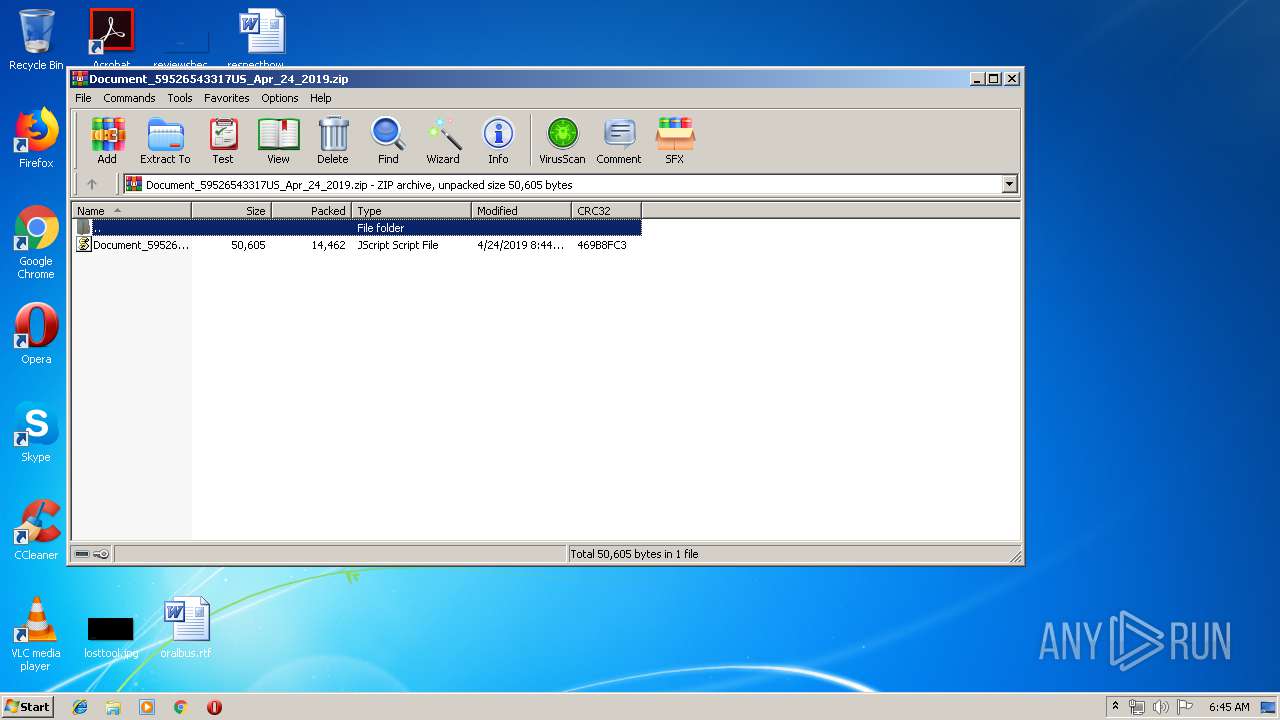
| File name: | Document_59526543317US_Apr_24_2019.zip |
| Full analysis: | https://app.any.run/tasks/be5ce64c-8dec-45a9-b3c3-73742e9be903 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 05:44:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D75FA32D015C1E7B426603913C067B0E |
| SHA1: | 9DF7CCF92F577BEB62063BD3CA6F5925B1A5052D |
| SHA256: | 6652E7F061260CCA047FBE543D6B4CC59016E0C629350810659D633D617E90B1 |
| SSDEEP: | 384:sNZ1OvLoQ9HxbK2XeZh/9e7J0nz2xJ5BlrNGSvZ7yP05c:IZE0Q6hVe7J0qxJ3iSvZePn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 3384)
Executes scripts
- WinRAR.exe (PID: 2172)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:24 08:44:06 |
| ZipCRC: | 0x469b8fc3 |
| ZipCompressedSize: | 14462 |
| ZipUncompressedSize: | 50605 |
| ZipFileName: | Document_59526543317US_Apr_24_2019.js |
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
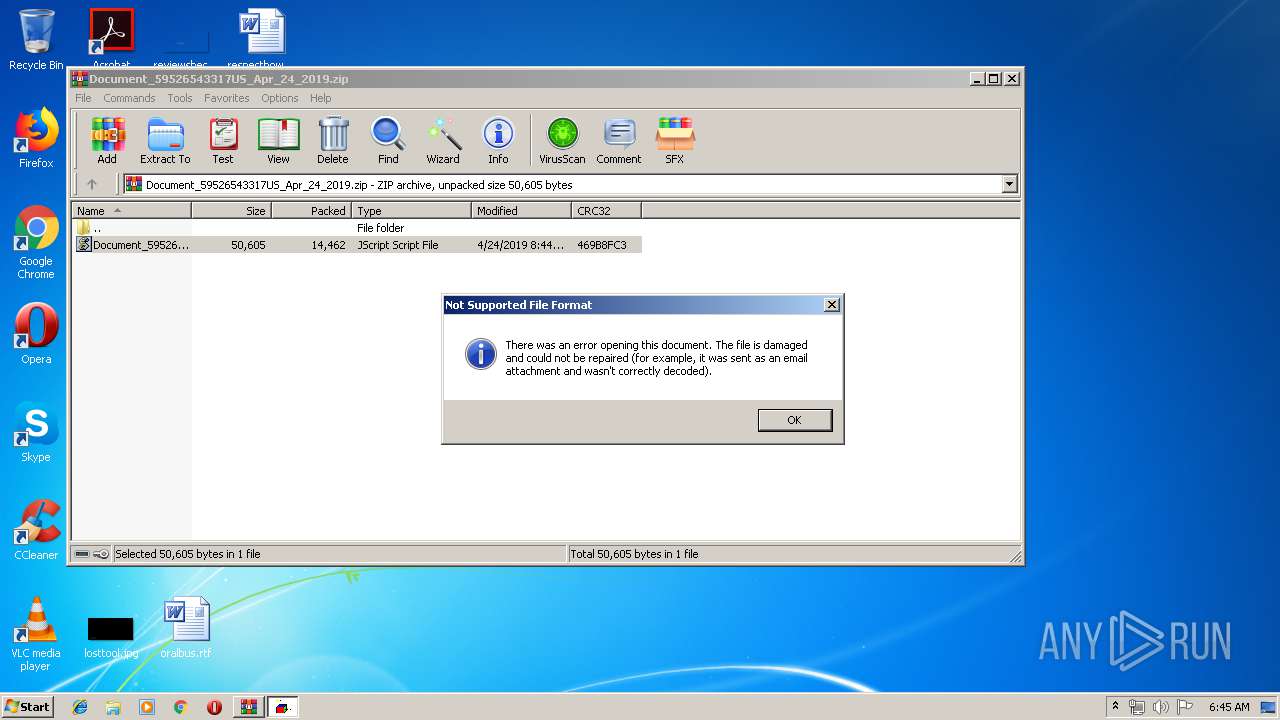
| 2172 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Document_59526543317US_Apr_24_2019.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3384 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2172.20739\Document_59526543317US_Apr_24_2019.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
486
Read events
454
Write events
32
Delete events
0
Modification events
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Document_59526543317US_Apr_24_2019.zip | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2172.20739\Document_59526543317US_Apr_24_2019.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | WScript.exe | GET | 404 | 192.169.140.162:80 | http://shawktech.com/shawktech.com/5_nW/ | US | xml | 345 b | malicious |
3384 | WScript.exe | GET | 404 | 112.175.184.38:80 | http://shot.co.kr/yupdduk717/Zd_R/ | KR | xml | 345 b | suspicious |
3384 | WScript.exe | GET | 404 | 201.148.107.46:80 | http://sapporo.com.pe/cH_2/ | CL | xml | 345 b | suspicious |
3384 | WScript.exe | GET | 404 | 185.11.240.11:80 | http://robertwatton.co.uk/uo_LL/ | GB | xml | 345 b | suspicious |
3384 | WScript.exe | GET | 404 | 81.19.186.241:80 | http://search4.ie/includes/O_gK/ | GB | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3384 | WScript.exe | 185.11.240.11:80 | robertwatton.co.uk | UK Webhosting Ltd | GB | suspicious |
3384 | WScript.exe | 201.148.107.46:80 | sapporo.com.pe | Gtd Internet S.A. | CL | suspicious |
3384 | WScript.exe | 81.19.186.241:80 | search4.ie | UKDedicated LTD | GB | unknown |
3384 | WScript.exe | 112.175.184.38:80 | shot.co.kr | Korea Telecom | KR | suspicious |
3384 | WScript.exe | 192.169.140.162:80 | shawktech.com | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
robertwatton.co.uk |
| suspicious |
sapporo.com.pe |
| suspicious |
search4.ie |
| unknown |
shot.co.kr |
| suspicious |
shawktech.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3384 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3384 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3384 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3384 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |