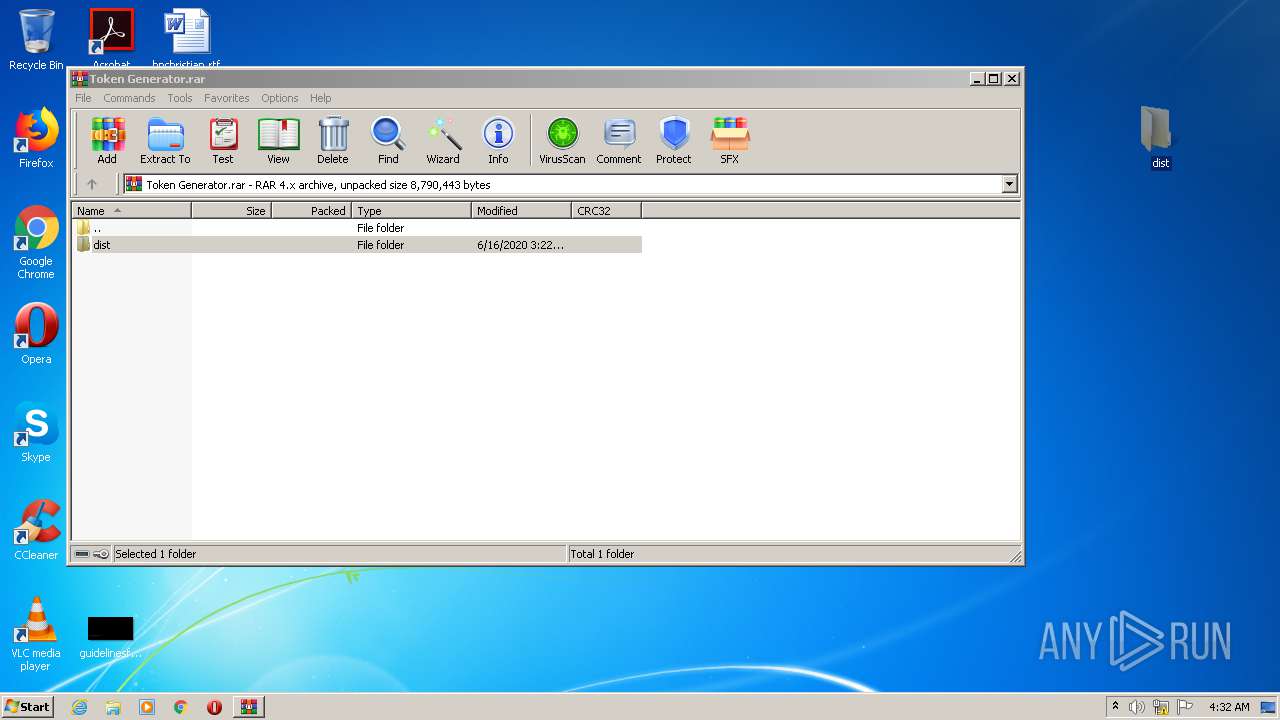
| File name: | Token Generator.rar |
| Full analysis: | https://app.any.run/tasks/fb34b18e-b626-4128-975f-da278324d59e |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 03:31:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
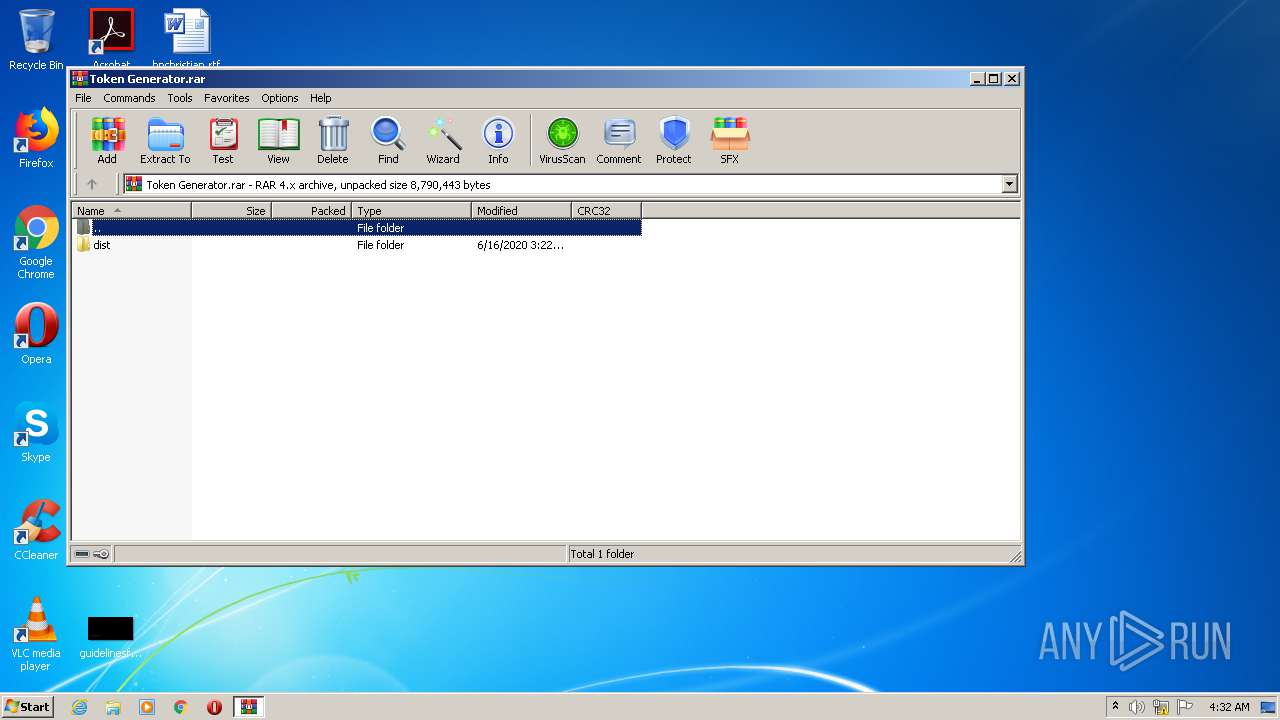
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 4AF45866888EC9E480AD1BF19DCC0728 |
| SHA1: | 7444110B68E17DF613DB3C03E4F1F232B293B3B7 |
| SHA256: | 6651CB1E6413552E2F6FF8C51E4426078F856CF7DC3069A76F4F8B1A2F53BB80 |
| SSDEEP: | 196608:qq9TARQjQpgeQCFe+OHIc0xEoWTD+ThtT+jWgv2jDeyE:qq1ARQ0pgSBBF6Wht9HeyE |
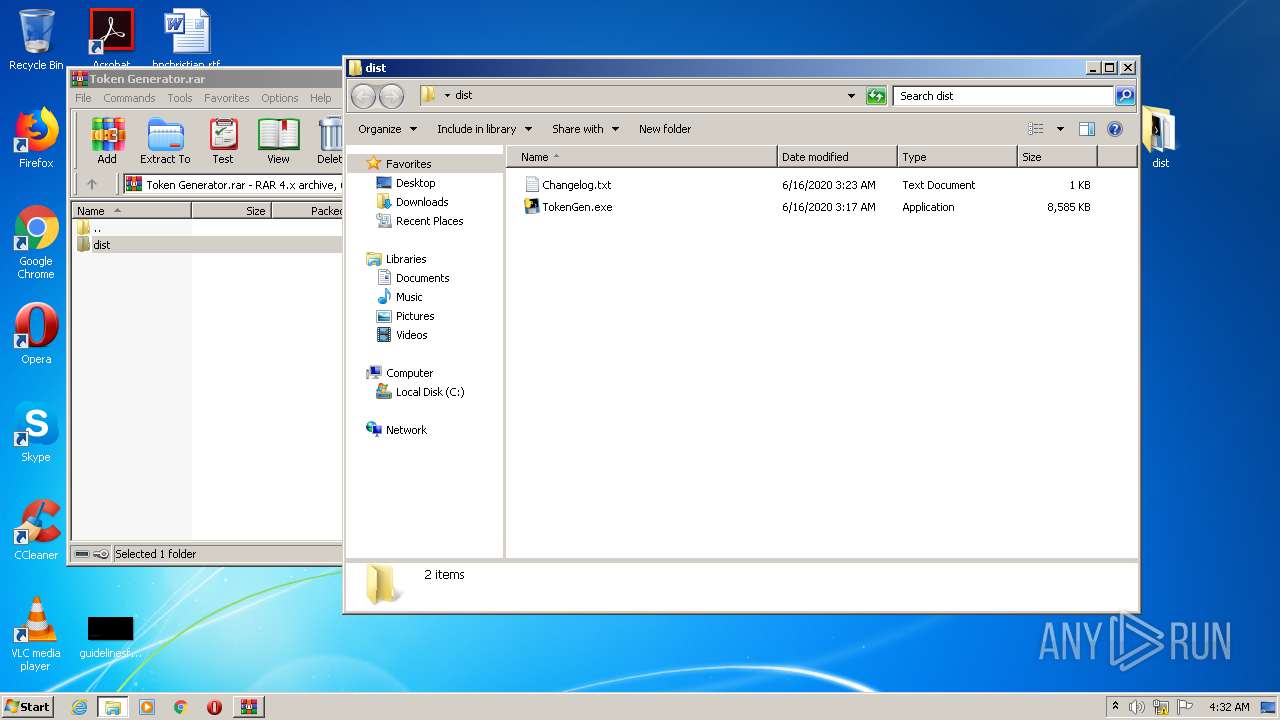
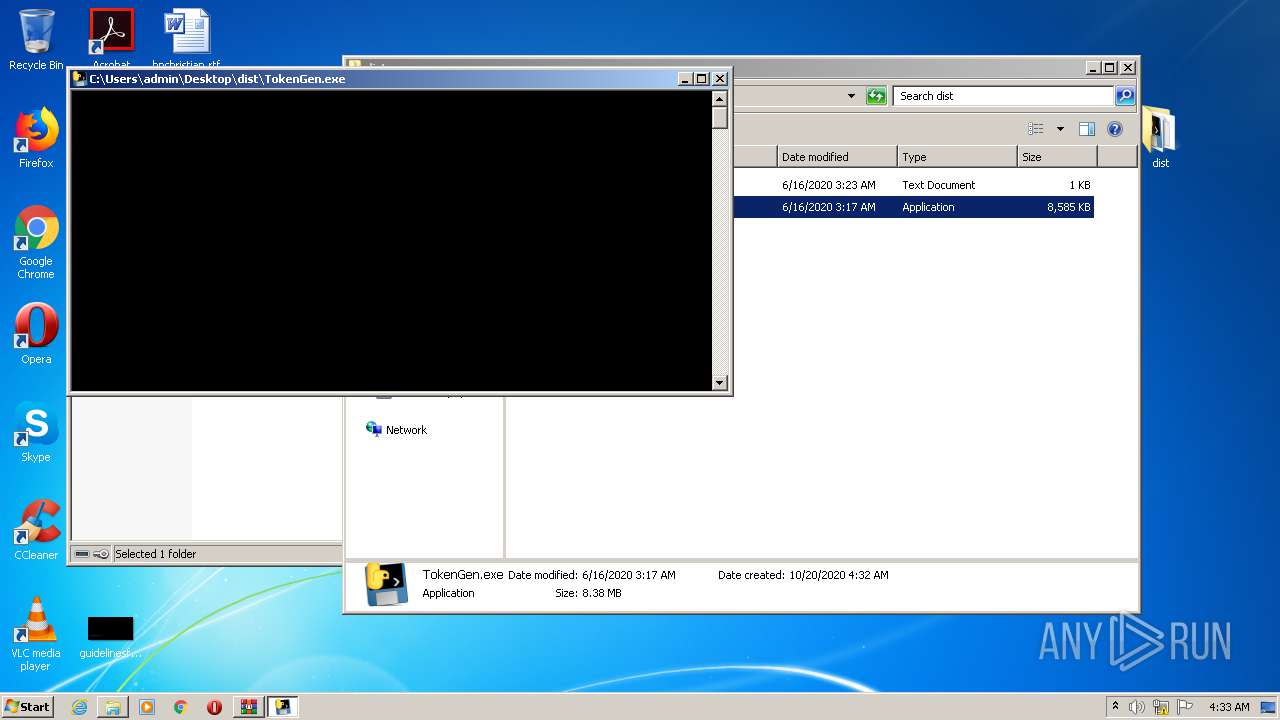
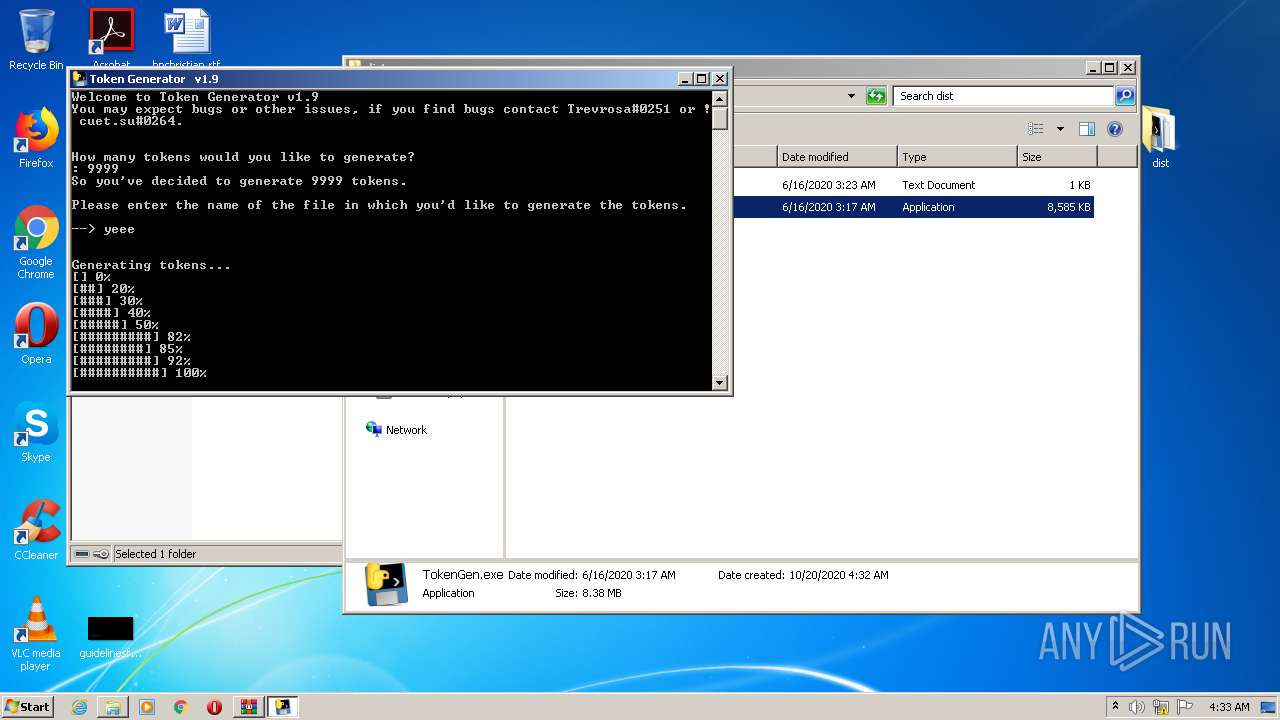
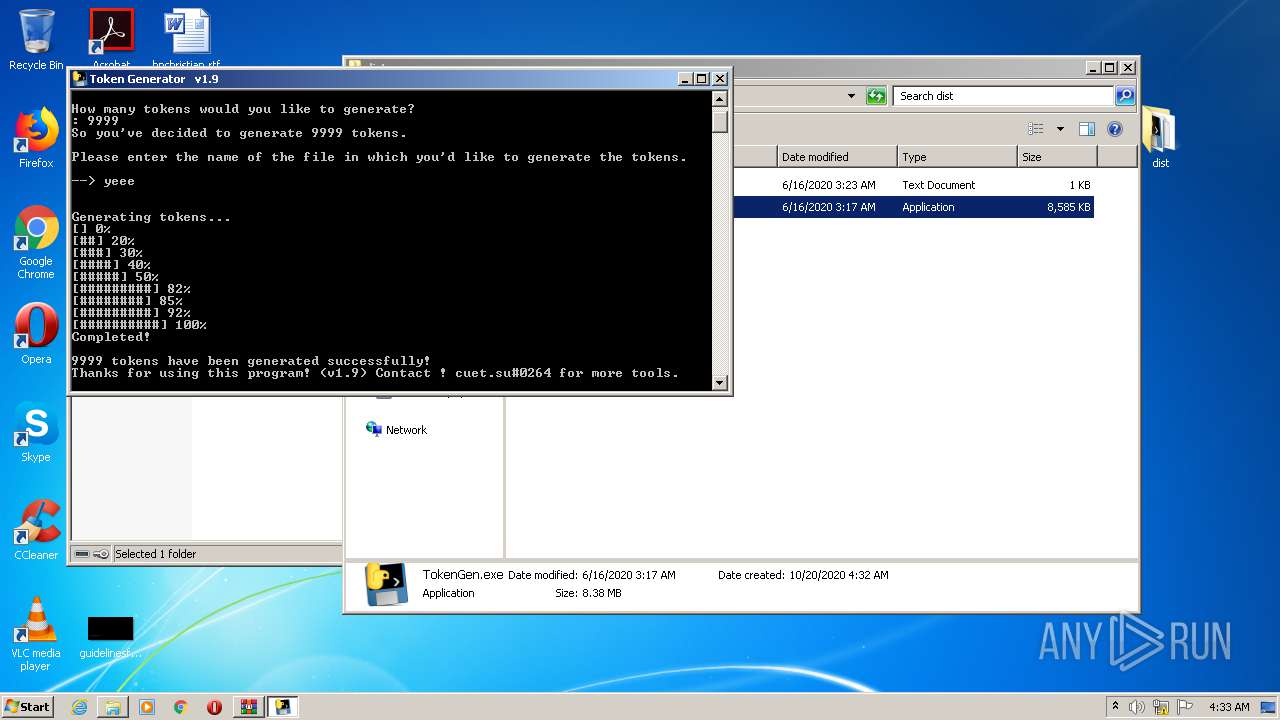
MALICIOUS
Application was dropped or rewritten from another process
- TokenGen.exe (PID: 3864)
- TokenGen.exe (PID: 2452)
Loads dropped or rewritten executable
- TokenGen.exe (PID: 2452)
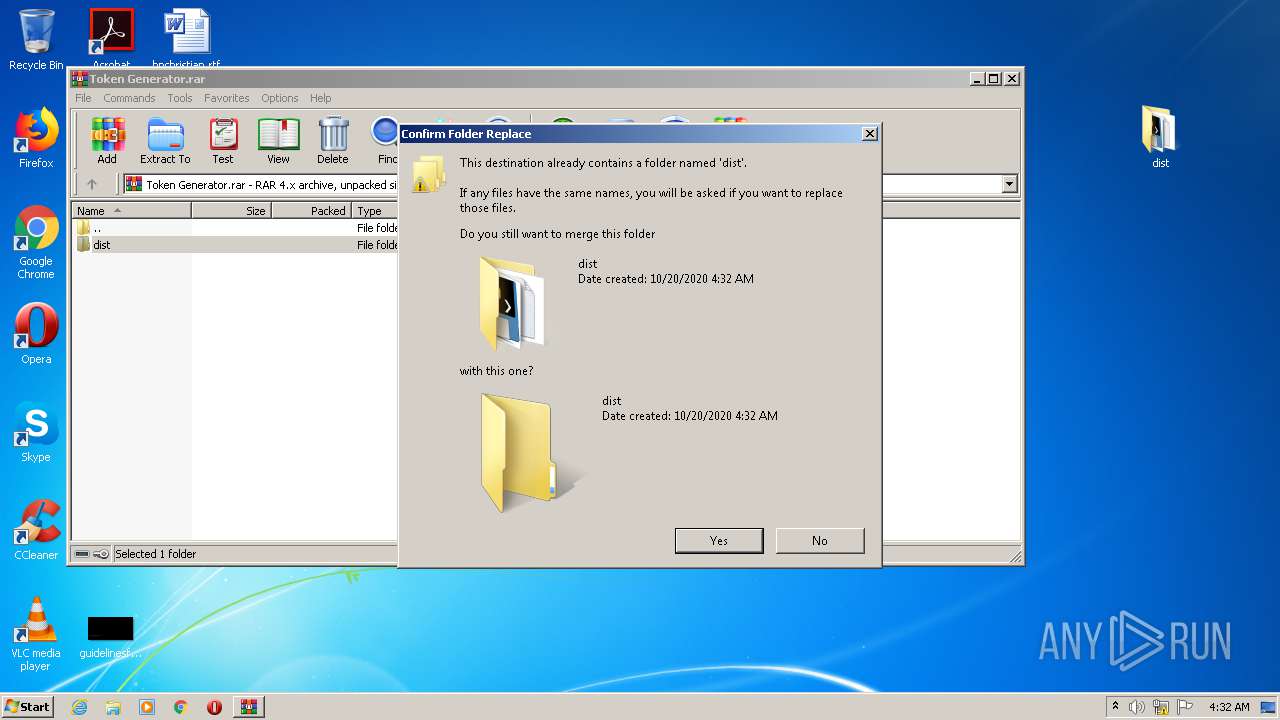
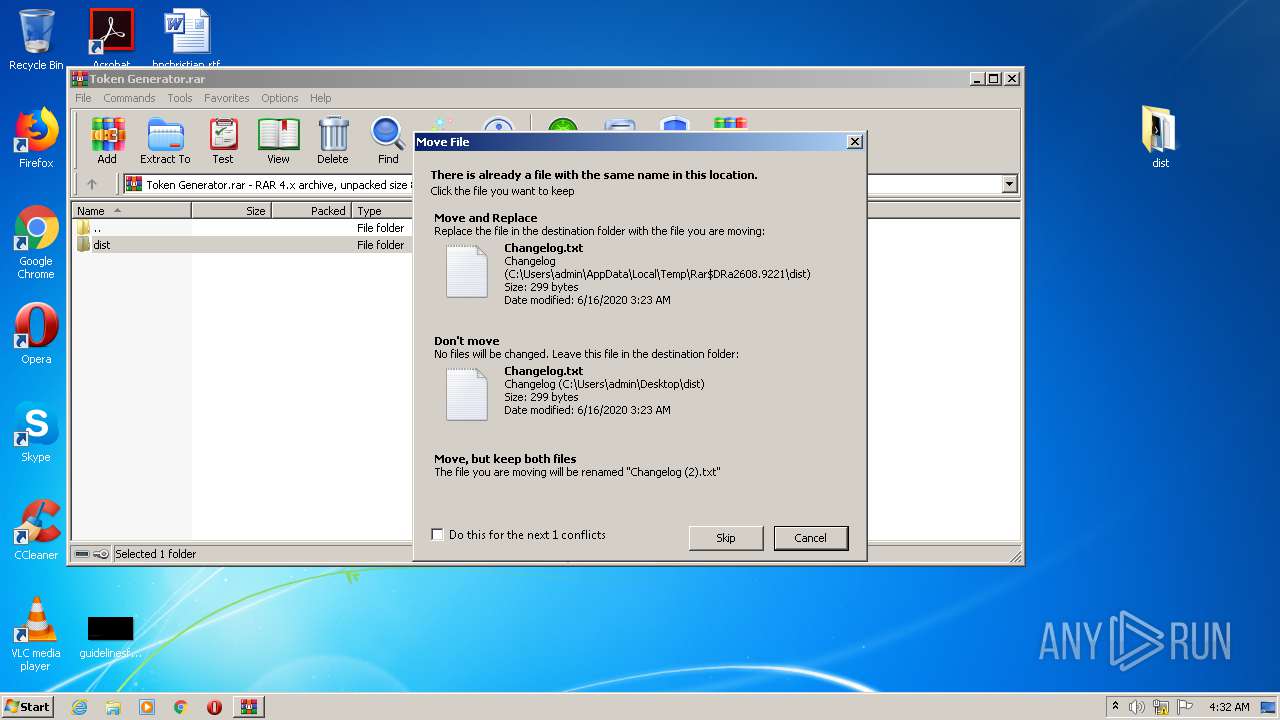
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2608)
- TokenGen.exe (PID: 3864)
Application launched itself
- TokenGen.exe (PID: 3864)
Loads Python modules
- TokenGen.exe (PID: 2452)
Starts CMD.EXE for commands execution
- TokenGen.exe (PID: 2452)
INFO
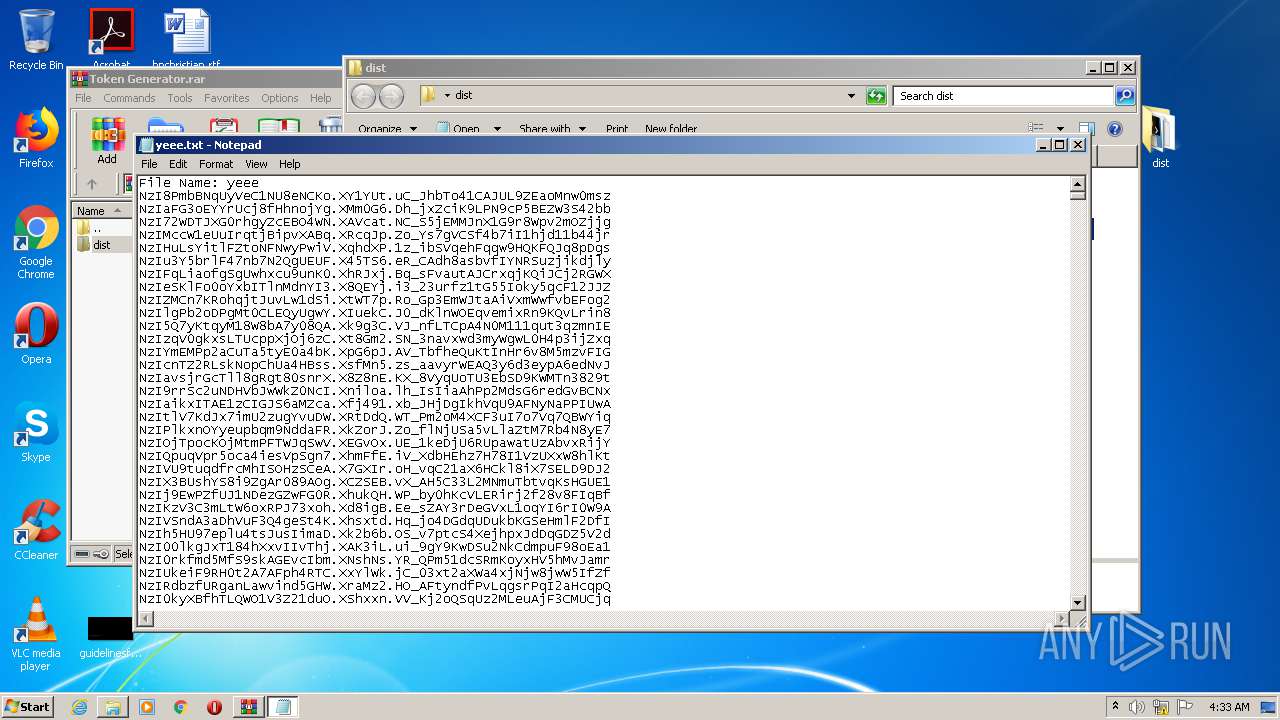
Dropped object may contain Bitcoin addresses
- TokenGen.exe (PID: 3864)
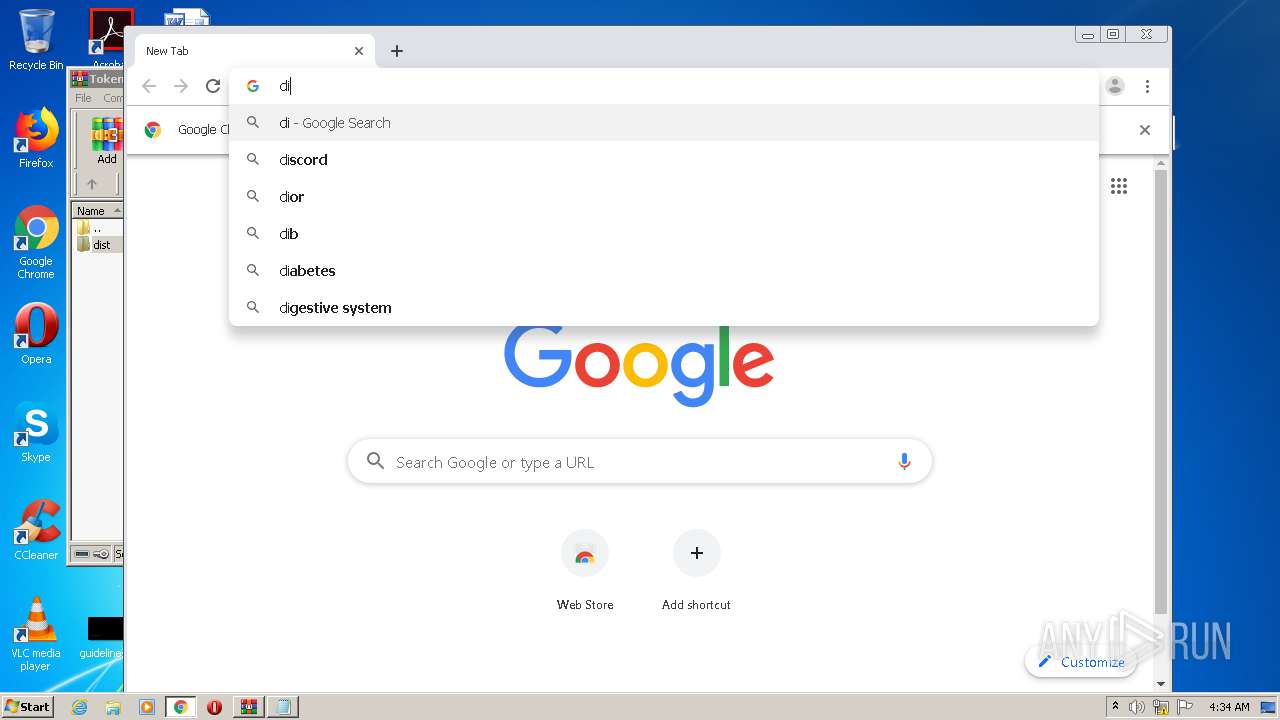
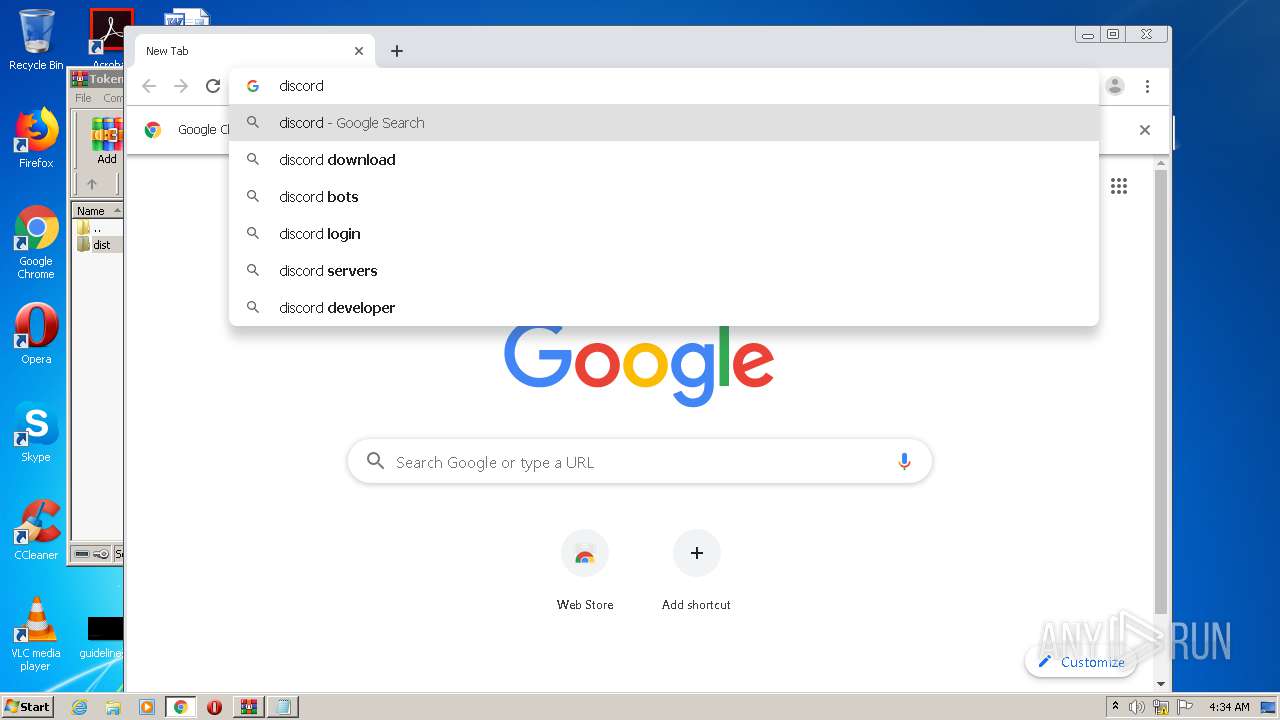
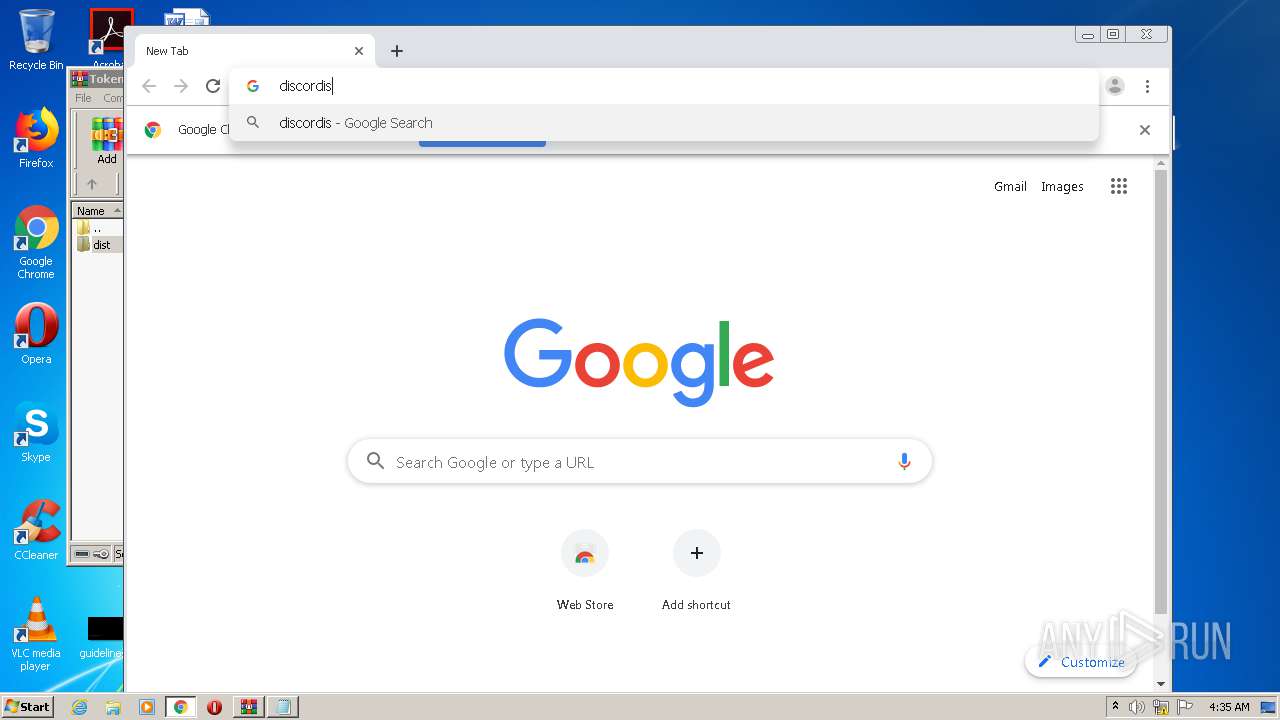
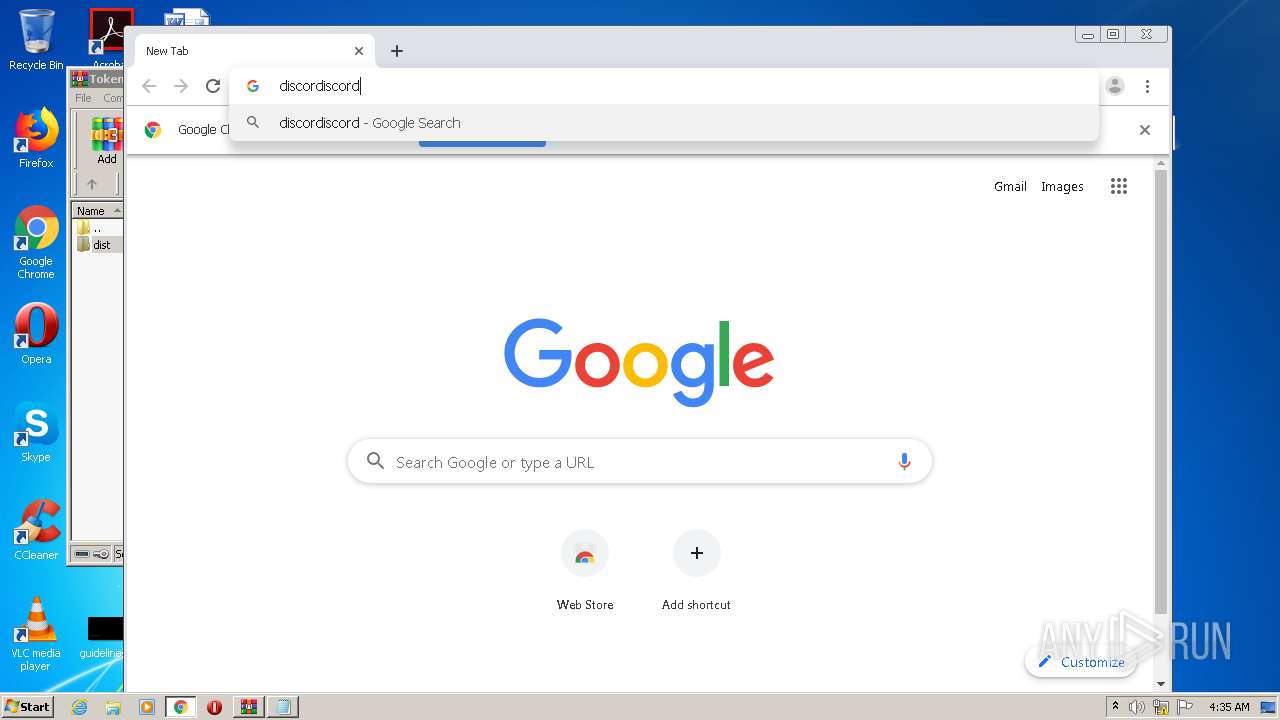
Manual execution by user
- TokenGen.exe (PID: 3864)
- chrome.exe (PID: 1632)
- NOTEPAD.EXE (PID: 3376)
Reads the hosts file
- chrome.exe (PID: 1632)
- chrome.exe (PID: 3720)
Application launched itself
- chrome.exe (PID: 1632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 231 |
|---|---|
| UncompressedSize: | 299 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2020:06:16 03:23:13 |
| PackingMethod: | Normal |
| ArchivedFileName: | dist\Changelog.txt |
Total processes
61
Monitored processes
20
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15007863531519905441,17387043514159023451,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7315408956152488077 --mojo-platform-channel-handle=3596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15007863531519905441,17387043514159023451,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1563436080596288595 --mojo-platform-channel-handle=3444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15007863531519905441,17387043514159023451,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11782387497788289593 --mojo-platform-channel-handle=3444 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2680 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\Desktop\dist\TokenGen.exe" | C:\Users\admin\Desktop\dist\TokenGen.exe | — | TokenGen.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
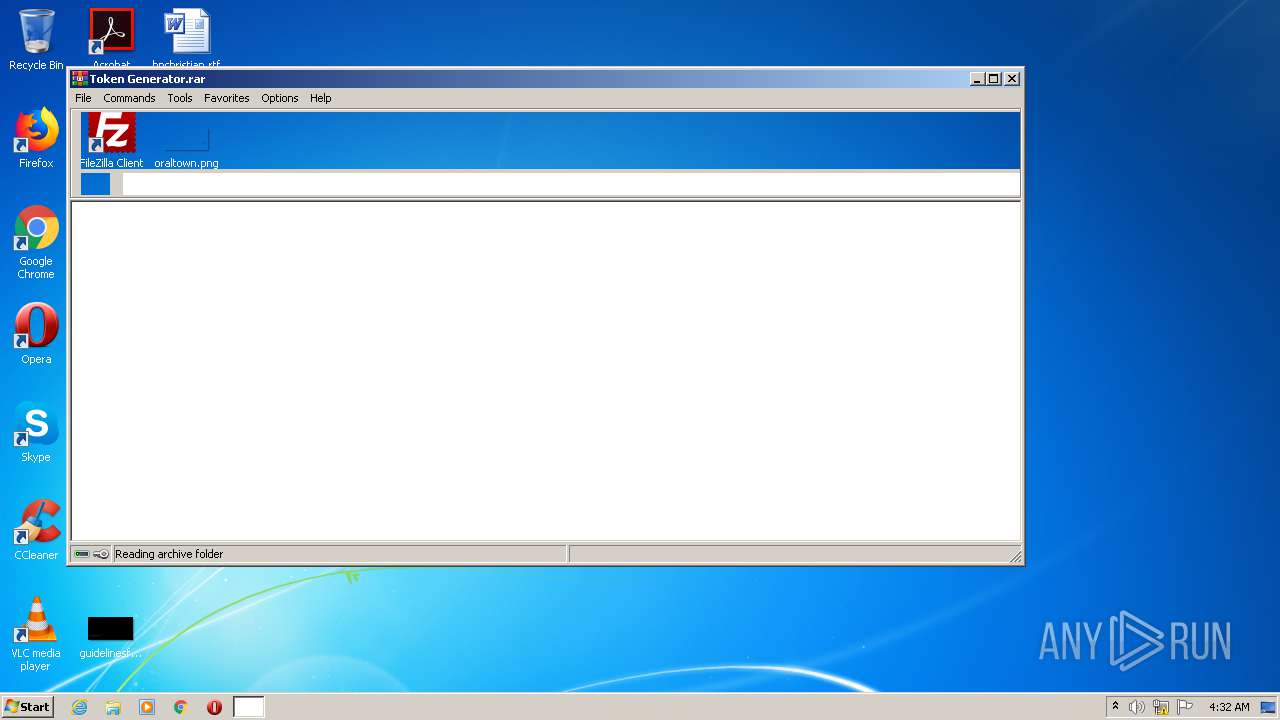
| 2608 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Token Generator.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,15007863531519905441,17387043514159023451,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1962352776662338299 --mojo-platform-channel-handle=3400 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,15007863531519905441,17387043514159023451,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15266322782050391060 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,15007863531519905441,17387043514159023451,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13597598242638628640 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 045
Read events
964
Write events
77
Delete events
4
Modification events
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Token Generator.rar | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2608) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1632) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1632) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
25
Suspicious files
17
Text files
986
Unknown types
2
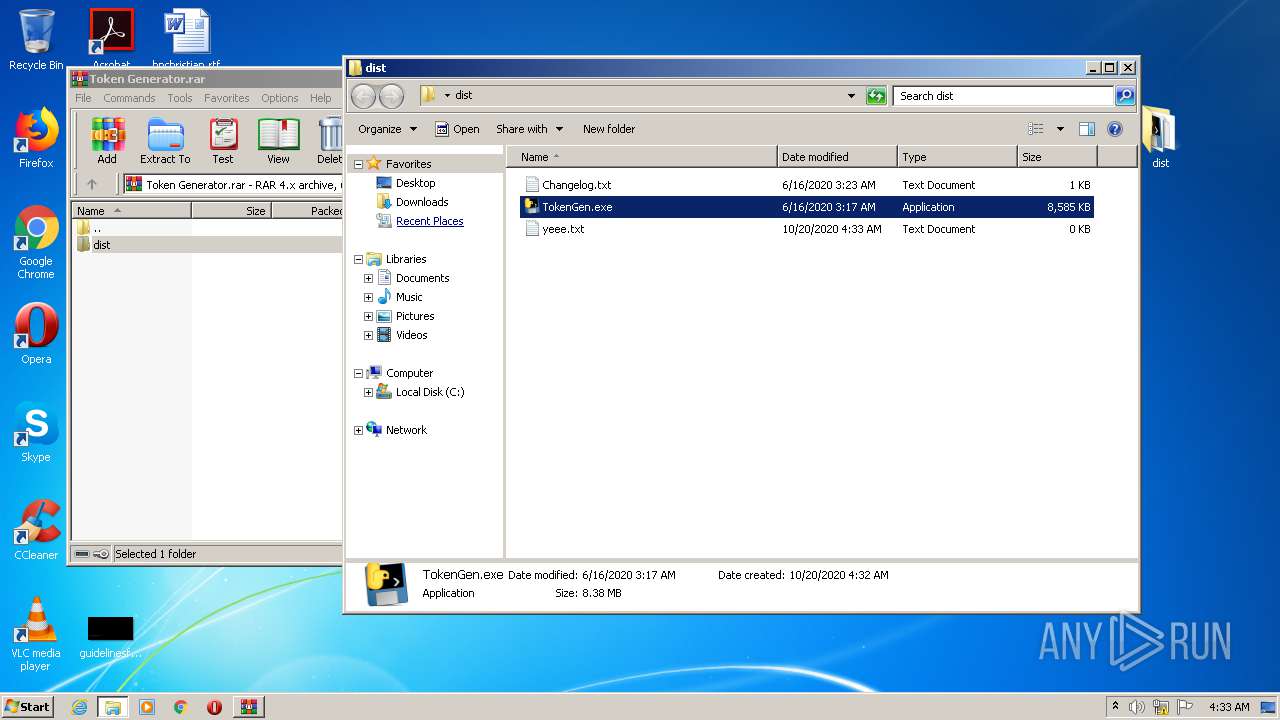
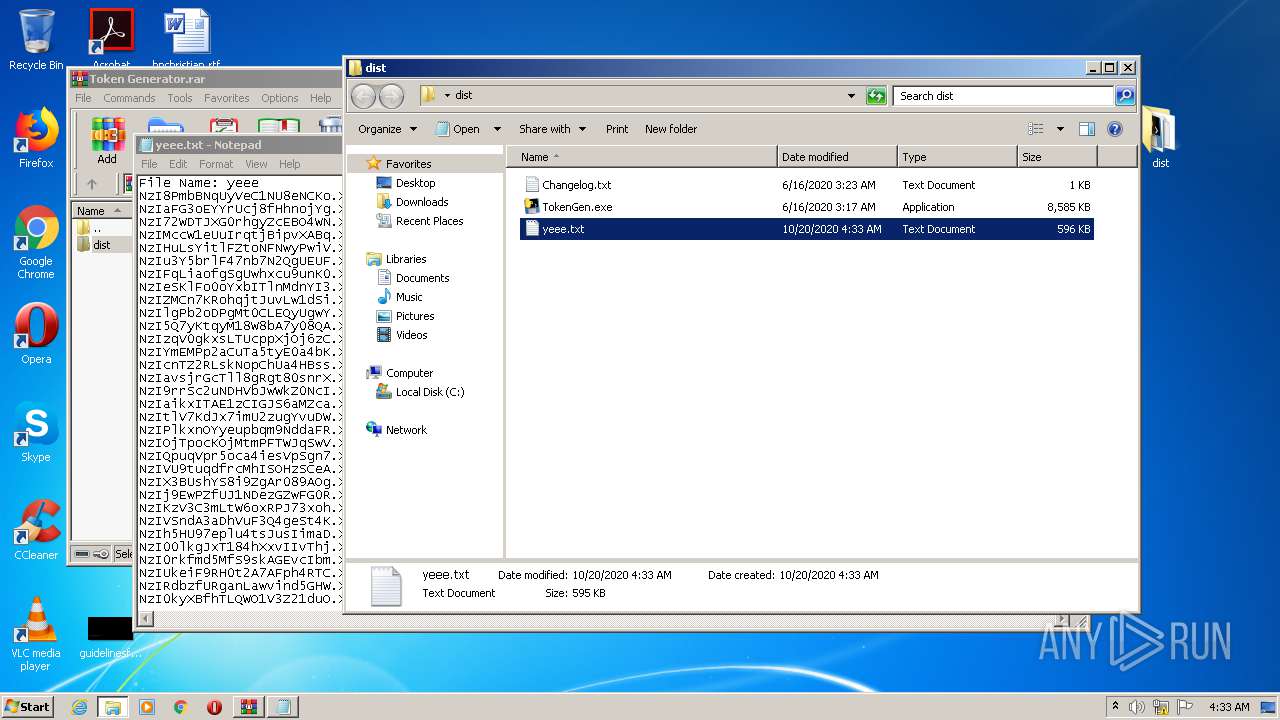
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2608.8593\dist\Changelog.txt | — | |
MD5:— | SHA256:— | |||
| 2608 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2608.8593\dist\TokenGen.exe | — | |
MD5:— | SHA256:— | |||
| 2608 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2608.9221\dist\TokenGen.exe | executable | |
MD5:— | SHA256:— | |||
| 3864 | TokenGen.exe | C:\Users\admin\AppData\Local\Temp\_MEI38642\TokenGen.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 2608 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2608.9221\dist\Changelog.txt | text | |
MD5:— | SHA256:— | |||
| 3864 | TokenGen.exe | C:\Users\admin\AppData\Local\Temp\_MEI38642\_asyncio.pyd | executable | |
MD5:5435CE08F40FBE43230CAE8D3DFF232C | SHA256:79FDA30CBFC95DB2BA60646FF53DFF45B5ADD57C12241C4A82FA798CB3B543DF | |||
| 3864 | TokenGen.exe | C:\Users\admin\AppData\Local\Temp\_MEI38642\_multiprocessing.pyd | executable | |
MD5:8901E96BB7A8EEAD994AF2BDF54A2447 | SHA256:823A96F080A3424F4C5327CF61FF517723E19A69679EBE93EA97061063D8D593 | |||
| 3864 | TokenGen.exe | C:\Users\admin\AppData\Local\Temp\_MEI38642\_socket.pyd | executable | |
MD5:CEA329CE0935E99A8BC01070F07FEFAF | SHA256:D1A4D66C557C2FE7DC441614CA62E67F37EC44BEF5A762BAC41BAC15D491A930 | |||
| 3864 | TokenGen.exe | C:\Users\admin\AppData\Local\Temp\_MEI38642\_queue.pyd | executable | |
MD5:BC5FCE7B8DE6CA765CBF79F9D0587164 | SHA256:A5DB4D041F40FB01761B5BAA907099DB89CF891B0DF0251D92DA2FBF9DC3897B | |||
| 3864 | TokenGen.exe | C:\Users\admin\AppData\Local\Temp\_MEI38642\_testcapi.pyd | executable | |
MD5:F33981092BFAE8CABF404AAB0199A979 | SHA256:5796A1D619CE13CC90B1E6EBFDDC374BE33EDBC1B3D9CB562DDD05007D6C845E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 216.58.212.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |