| download: | download |
| Full analysis: | https://app.any.run/tasks/4e1526c6-975a-4a30-87d9-3518f4a68c54 |
| Verdict: | Malicious activity |
| Analysis date: | June 15, 2018, 20:30:14 |
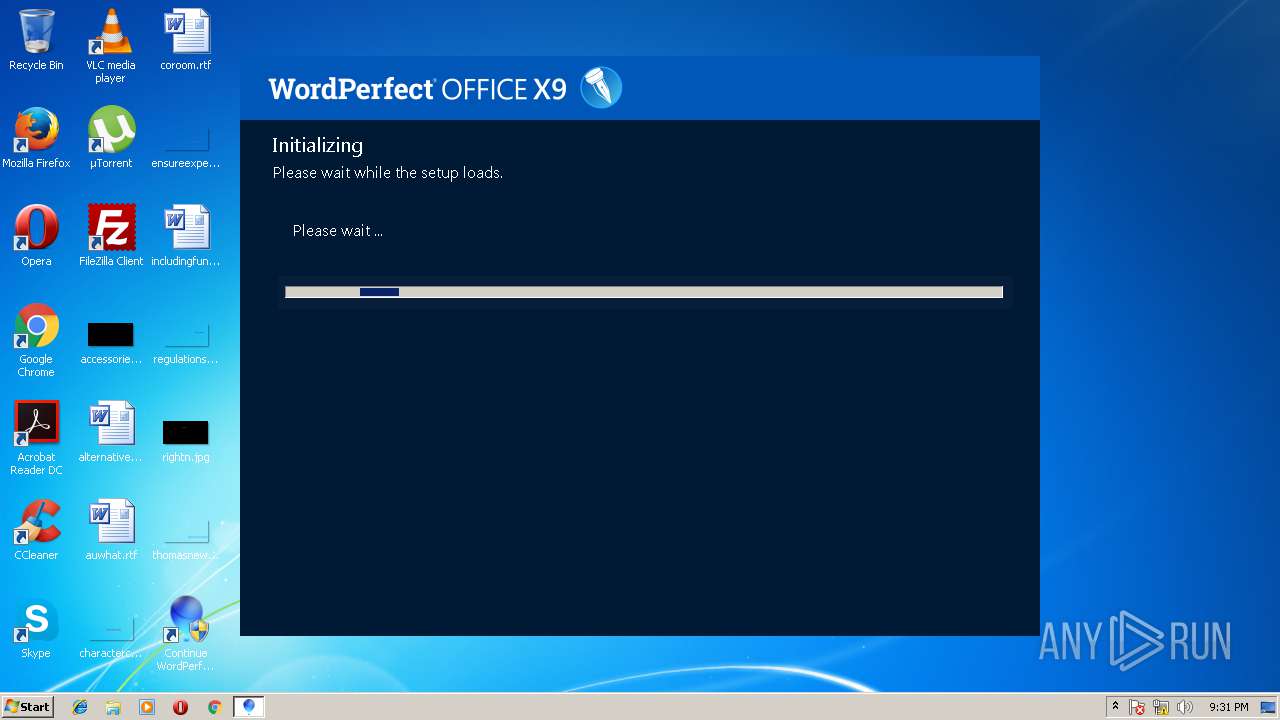
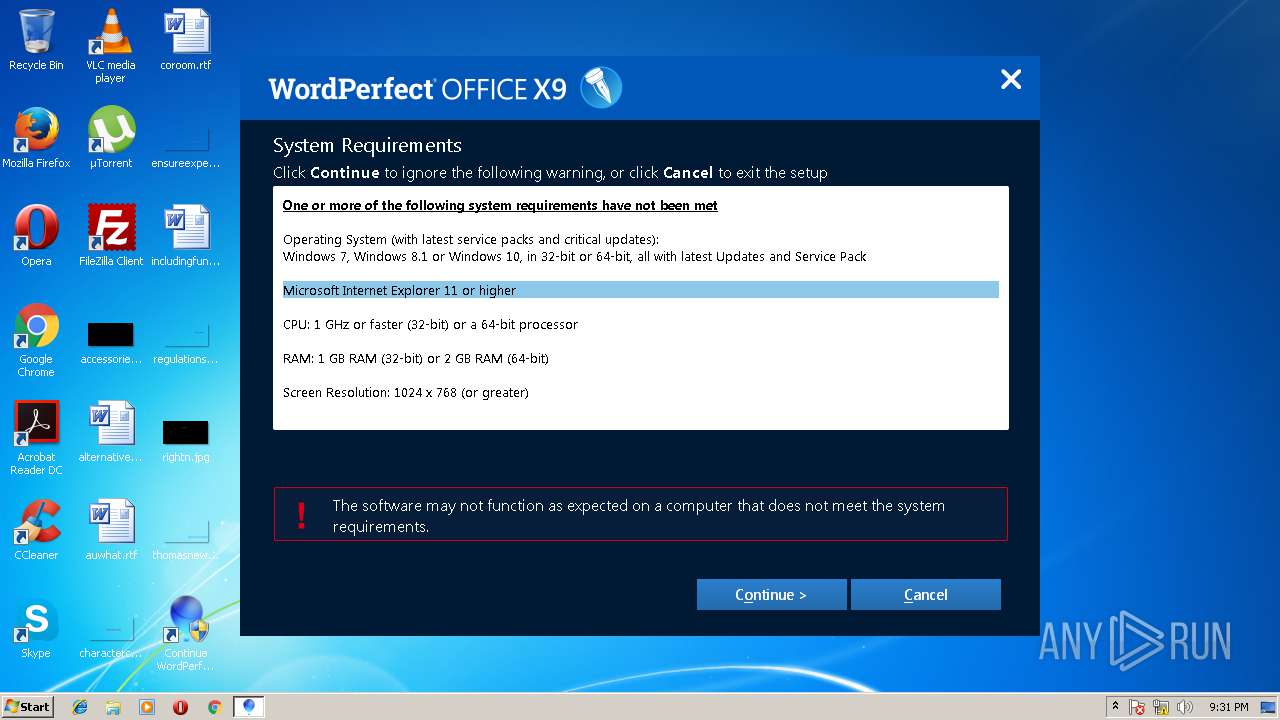
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E82261F069369C6747514D3846F1F52F |
| SHA1: | 05F6884AA37F10C0210C812E66510E89F61FE1E1 |
| SHA256: | 664C14F7A2312137EE8524A4DEEE8448B6290A85C10957938C6648CFE980623B |
| SSDEEP: | 24576:e5b2/IyLyoLb1lc8s4FeimMKkpLxjozQGm9Mq8J2HdC8jvcLiahC:HIloLb1lc8s4FeimM/8zQqqQ6dvbcLFM |
MALICIOUS
Loads dropped or rewritten executable
- setup.exe (PID: 2824)
- Cfg_BDE.exe (PID: 1380)
- svchost.exe (PID: 868)
- SearchFilterHost.exe (PID: 3720)
- SearchProtocolHost.exe (PID: 2620)
- regsvr32.exe (PID: 840)
- CUH.EXE (PID: 3560)
- iexplore.exe (PID: 3600)
- wpwin19.exe (PID: 2856)
- PsiService_2.exe (PID: 2884)
- regsvr32.exe (PID: 1440)
Application was dropped or rewritten from another process
- Cfg_BDE.exe (PID: 1380)
- PsiService_2.exe (PID: 3832)
- PsiService_2.exe (PID: 2884)
- setup.exe (PID: 2824)
- CUH.EXE (PID: 2960)
- CUH.EXE (PID: 3560)
- wpwin19.exe (PID: 2856)
Registers / Runs the DLL via REGSVR32.EXE
- msiexec.exe (PID: 788)
Uses Task Scheduler to run other applications
- msiexec.exe (PID: 788)
Loads the Task Scheduler COM API
- CUH.EXE (PID: 2960)
- schtasks.exe (PID: 3468)
- CUH.EXE (PID: 3560)
Changes internet zones settings
- setup.exe (PID: 2824)
SUSPICIOUS
Executable content was dropped or overwritten
- download.exe (PID: 2024)
- download.exe (PID: 2508)
- setup.exe (PID: 2824)
- MsiExec.exe (PID: 3404)
- msiexec.exe (PID: 788)
- MsiExec.exe (PID: 3016)
- MsiExec.exe (PID: 2888)
- CUH.EXE (PID: 3560)
- wpwin19.exe (PID: 2856)
Creates files in the program directory
- download.exe (PID: 2508)
- setup.exe (PID: 2824)
- PsiService_2.exe (PID: 2884)
Removes files from Windows directory
- MsiExec.exe (PID: 4052)
Creates files in the Windows directory
- MsiExec.exe (PID: 4052)
- msiexec.exe (PID: 788)
- svchost.exe (PID: 868)
Creates COM task schedule object
- setup.exe (PID: 2824)
- msiexec.exe (PID: 788)
- regsvr32.exe (PID: 840)
- regsvr32.exe (PID: 1440)
Reads internet explorer settings
- download.exe (PID: 2508)
- setup.exe (PID: 2824)
Modifies the open verb of a shell class
- msiexec.exe (PID: 788)
Changes the autorun value in the registry
- msiexec.exe (PID: 788)
Creates or modifies windows services
- PsiService_2.exe (PID: 3832)
- PsiService_2.exe (PID: 2884)
Starts Internet Explorer
- setup.exe (PID: 2824)
Creates files in the user directory
- CUH.EXE (PID: 3560)
- wpwin19.exe (PID: 2856)
Low-level read access rights to disk partition
- PsiService_2.exe (PID: 2884)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4052)
- MsiExec.exe (PID: 2596)
- MsiExec.exe (PID: 2612)
- MsiExec.exe (PID: 688)
- MsiExec.exe (PID: 560)
- MsiExec.exe (PID: 2180)
- MSI7489.tmp (PID: 3736)
- MsiExec.exe (PID: 1356)
- MsiExec.exe (PID: 3624)
- MsiExec.exe (PID: 2576)
- MsiExec.exe (PID: 2940)
- MsiExec.exe (PID: 3928)
- MsiExec.exe (PID: 3844)
- MsiExec.exe (PID: 3404)
- MsiExec.exe (PID: 2896)
- MsiExec.exe (PID: 3364)
- MsiExec.exe (PID: 3016)
- MsiExec.exe (PID: 3224)
- MsiExec.exe (PID: 2888)
- MsiExec.exe (PID: 3084)
- MsiExec.exe (PID: 1692)
- msiexec.exe (PID: 788)
- MsiExec.exe (PID: 1500)
- MsiExec.exe (PID: 1284)
Reads settings of System Certificates
- msiexec.exe (PID: 788)
Dropped object may contain URL's
- setup.exe (PID: 2824)
- download.exe (PID: 2508)
- svchost.exe (PID: 868)
- iexplore.exe (PID: 2532)
- CUH.EXE (PID: 3560)
- wpwin19.exe (PID: 2856)
- iexplore.exe (PID: 3600)
- msiexec.exe (PID: 788)
Starts application with an unusual extension
- msiexec.exe (PID: 788)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 788)
Creates files in the program directory
- MsiExec.exe (PID: 2896)
- msiexec.exe (PID: 788)
- MsiExec.exe (PID: 1284)
Creates a software uninstall entry
- msiexec.exe (PID: 788)
Application launched itself
- msiexec.exe (PID: 788)
- iexplore.exe (PID: 2532)
Reads internet explorer settings
- iexplore.exe (PID: 3600)
Changes internet zones settings
- iexplore.exe (PID: 2532)
Creates files in the user directory
- iexplore.exe (PID: 3600)
Changes settings of System certificates
- iexplore.exe (PID: 3600)
Reads Internet Cache Settings
- iexplore.exe (PID: 3600)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:11 16:50:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 486400 |
| InitializedDataSize: | 206336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4ab13 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.7.1 |
| ProductVersionNumber: | 19.0.7.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
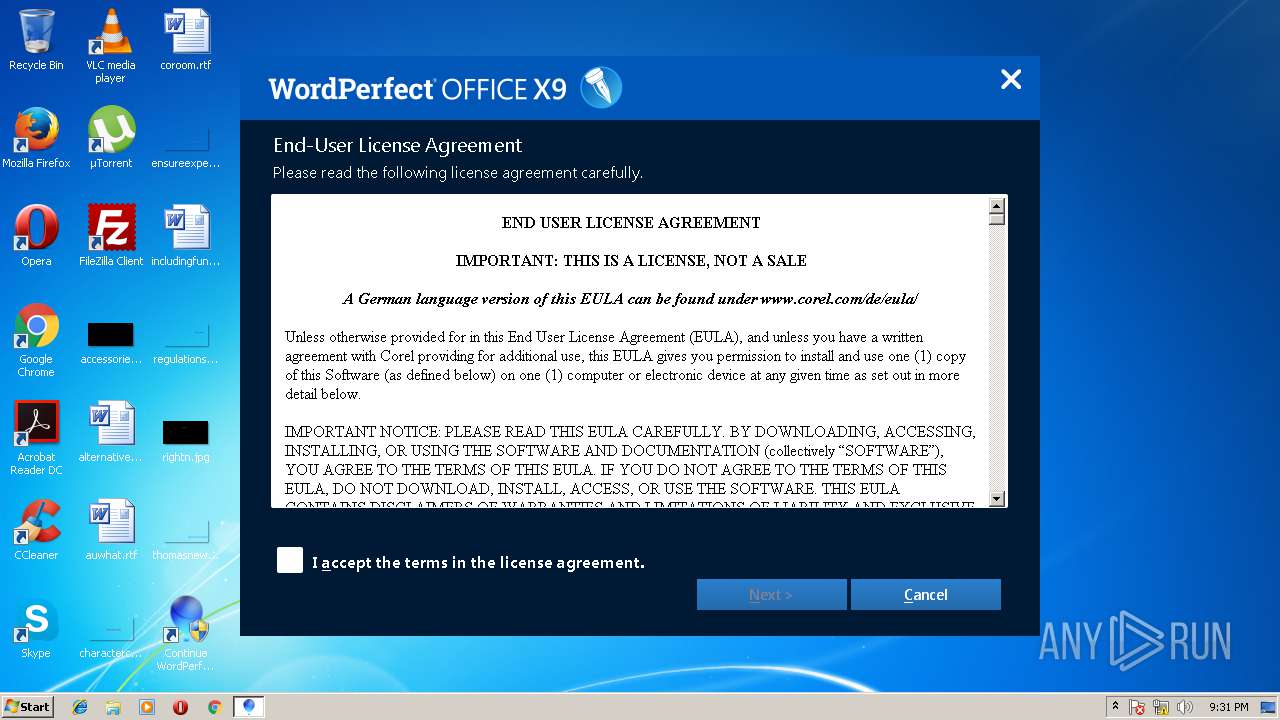
| CompanyName: | Corel Corporation |
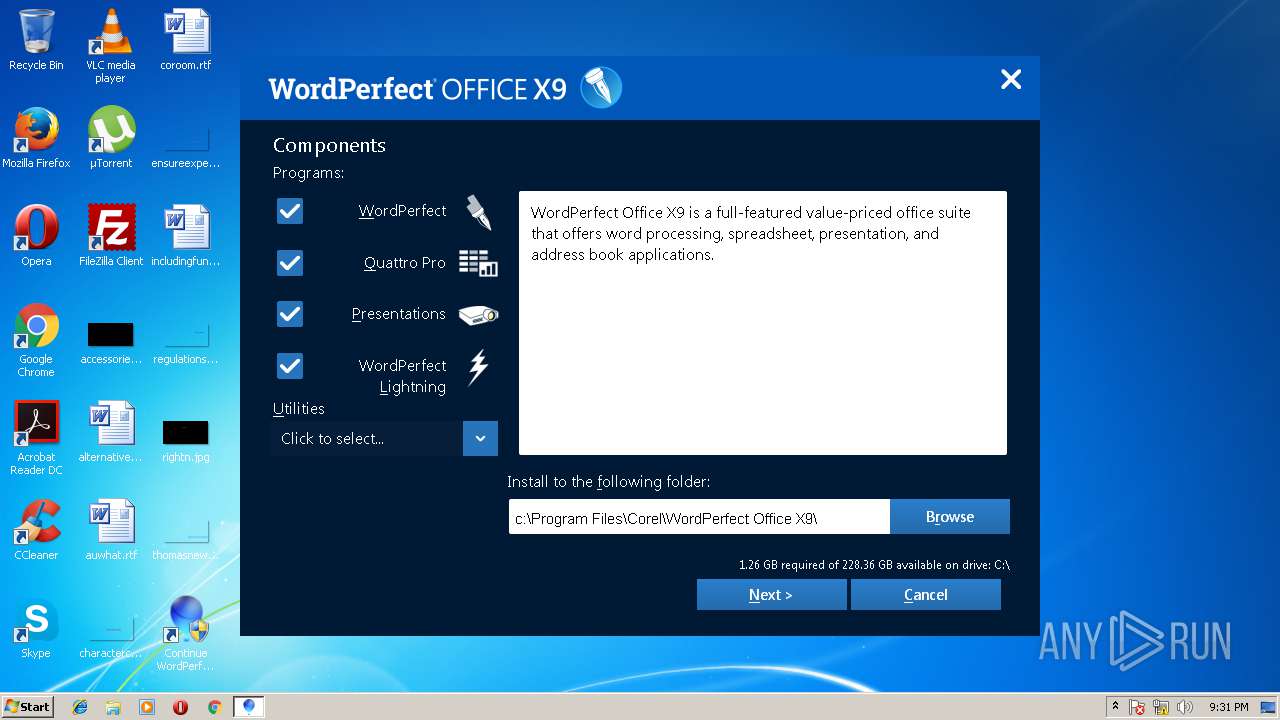
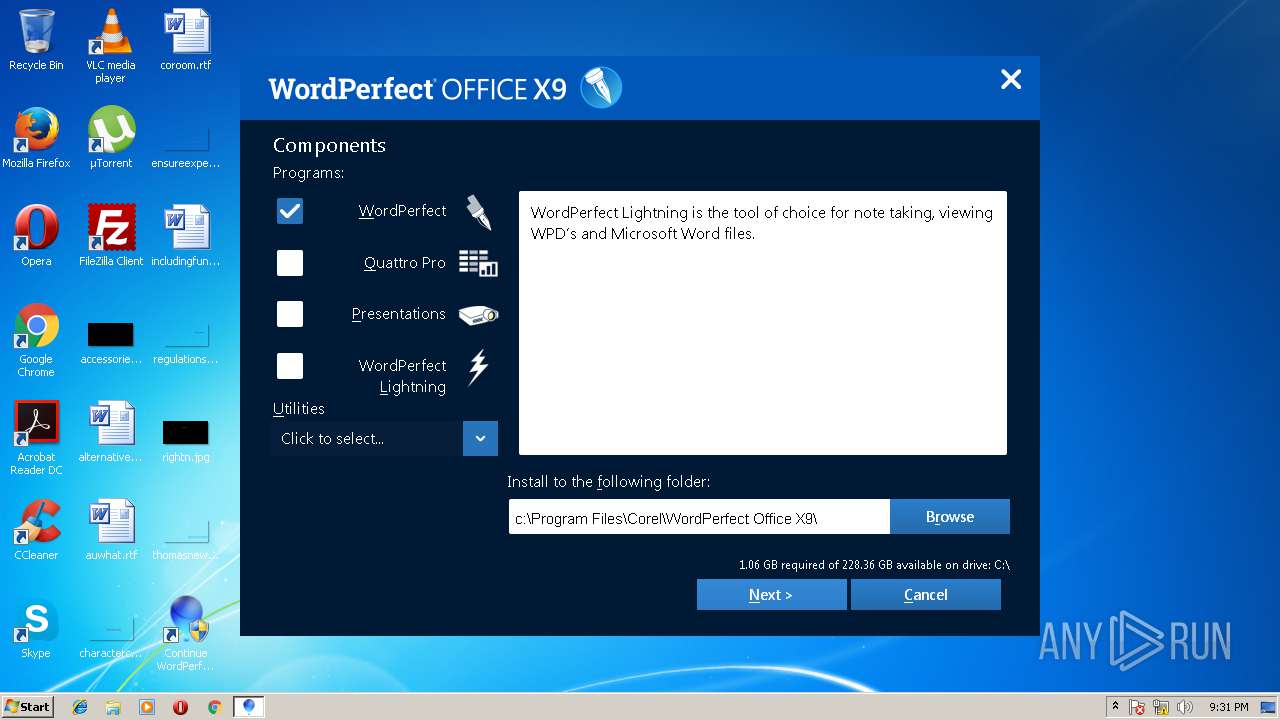
| FileDescription: | WordPerfectOffice |
| FileVersion: | 19.0.0.1 |
| InternalName: | WPO_X9.exe |
| LegalCopyright: | Copyright (C) 2018 Corel Corporation. All rights reserved. |
| ProductName: | WordPerfectOffice |
| ProductVersion: | 19.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-May-2018 14:50:24 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Corel Corporation |
| FileDescription: | WordPerfectOffice |
| FileVersion: | 19.0.0.1 |
| InternalName: | WPO_X9.exe |
| LegalCopyright: | Copyright (C) 2018 Corel Corporation. All rights reserved. |
| ProductName: | WordPerfectOffice |
| ProductVersion: | 19.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 11-May-2018 14:50:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00076BDC | 0x00076C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62655 |
.rdata | 0x00078000 | 0x0001F1BE | 0x0001F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02045 |
.data | 0x00098000 | 0x00003B0C | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.66141 |
.gfids | 0x0009C000 | 0x000007CC | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.97305 |
.tls | 0x0009D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0009E000 | 0x000089B0 | 0x00008A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36023 |
.reloc | 0x000A7000 | 0x0000624C | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59037 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16947 | 2013 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.16586 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.18397 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.51828 | 1128 | UNKNOWN | English - United States | RT_ICON |
101 | 2.62308 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
RPCRT4.dll |
USER32.dll (delay-loaded) |
Total processes
92
Monitored processes
52
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | c:\Windows\system32\MsiExec.exe -Embedding A57E38F8563C0138391817A30E8F340D | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 688 | c:\Windows\system32\MsiExec.exe -Embedding 432B15DC434DB032BC71D9DF6FA05B52 M Global\MSI0000 | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 788 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 840 | c:\Windows\system32\regsvr32.exe /s "c:\Program Files\Corel\PASMUtility\v1\PSIClientBridgeProxy.dll" | c:\Windows\system32\regsvr32.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | c:\Windows\system32\MsiExec.exe -Embedding 4FDC981A62F5F7E894B3ECE698F39DC8 M Global\MSI0000 | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | c:\Windows\system32\MsiExec.exe -Embedding 3143ABB2C70BD0AD005FBE1005FC766D | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "c:\Program Files\Common Files\Borland Shared\BDE\Cfg_BDE.exe" -MA "\DRIVERS\PARADOX\INIT" -MI "NET DIR" -RV c:\PROGRA~2\Borland\NetDir\ | c:\Program Files\Common Files\Borland Shared\BDE\Cfg_BDE.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1388 | c:\Windows\system32\MsiExec.exe -Embedding 41BB94C1A8B53C90094300315AB53ADB M Global\MSI0000 | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1440 | c:\Windows\system32\regsvr32.exe /s "c:\Program Files\Corel\PASMUtility\v1\PASMUTILITY.dll" | c:\Windows\system32\regsvr32.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 321
Read events
3 712
Write events
10 236
Delete events
373
Modification events
| (PID) Process: | (2508) download.exe | Key: | HKEY_CURRENT_USER\Software\Corel\stubframework\WPO\19 |
| Operation: | write | Name: | install_language |
Value: English | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_CURRENT_USER\Software\Corel\stubframework\WPO\19 |
| Operation: | write | Name: | status |
Value: 0 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_CURRENT_USER\Software\Corel\stubframework\WPO\19 |
| Operation: | write | Name: | channel |
Value: ppc_brkws | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2508) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
753
Suspicious files
416
Text files
1 833
Unknown types
712
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\common\css\common.css | text | |
MD5:— | SHA256:— | |||
| 2024 | download.exe | C:\Users\admin\AppData\Local\Temp\13f705\download.exe | executable | |
MD5:— | SHA256:— | |||
| 2508 | download.exe | C:\ProgramData\UniqueId\data | binary | |
MD5:— | SHA256:— | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\common\img\BG.png | image | |
MD5:— | SHA256:— | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\common\img\close_hover.png | image | |
MD5:5D79E2175E6F02D441656D3334693783 | SHA256:25264FDDF7457AD4CA1438D57058540C2F2BE3C0B9E61EBBB149020BEC15EE62 | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\common\js\stubparams.js | text | |
MD5:— | SHA256:— | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\common\img\close.png | image | |
MD5:FDE10DC070AC14EDA212A9E3736D3EE7 | SHA256:6ECB0F0EA0CF48CB55A9555968F4F1AB045869619E9B61D8F0E6C7459DA05252 | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\config\config.js | text | |
MD5:— | SHA256:— | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\config\installparams.js | text | |
MD5:— | SHA256:— | |||
| 2508 | download.exe | C:\Users\admin\AppData\Local\Temp\13f87c\config\lang.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
4
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
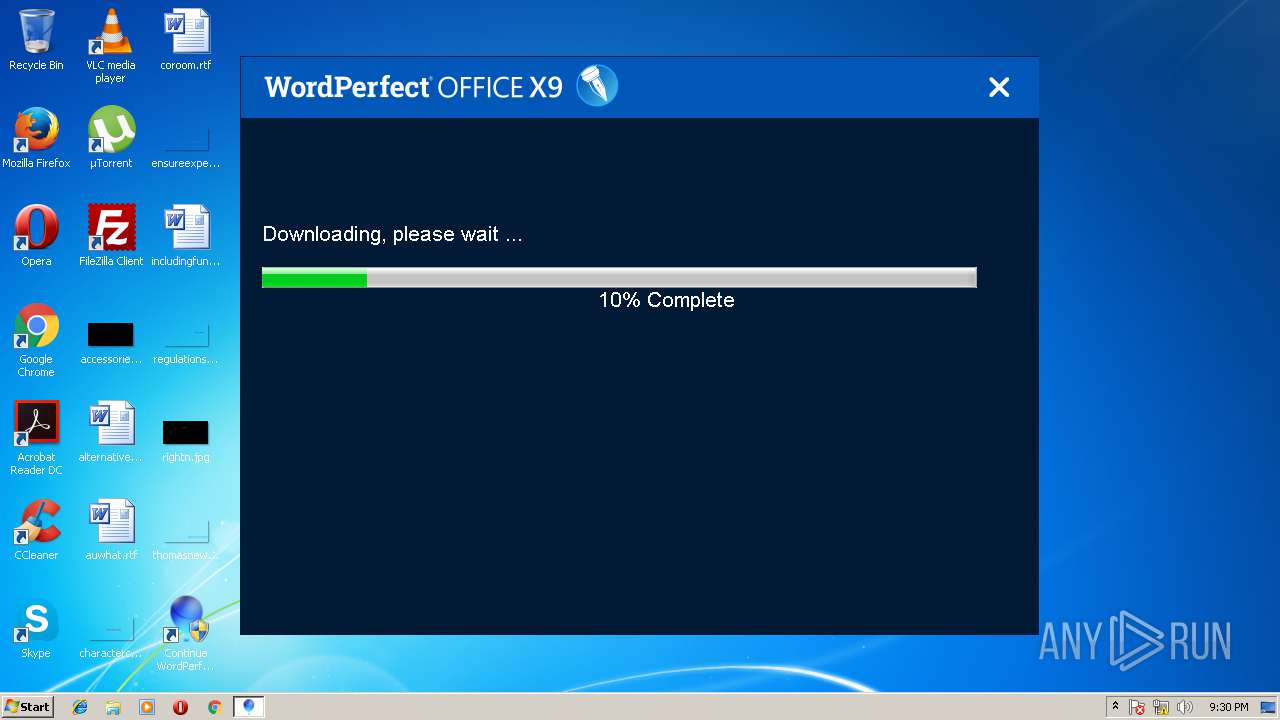
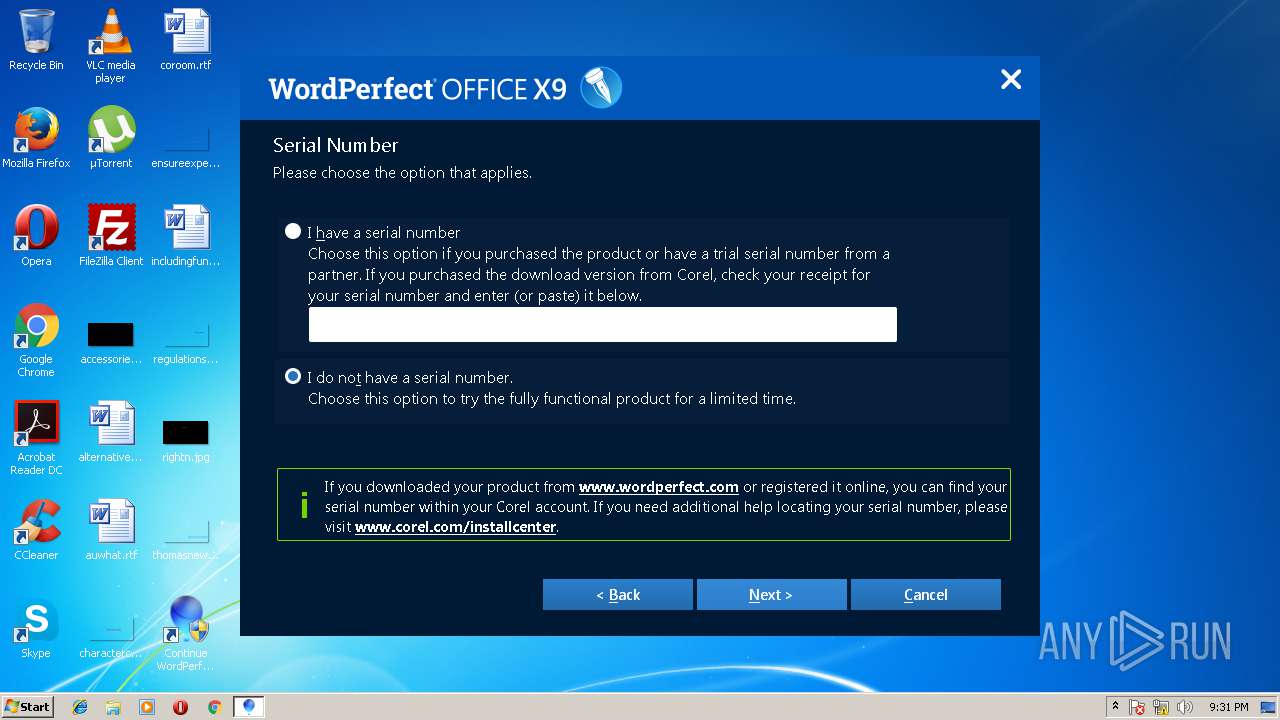
2508 | download.exe | GET | — | 23.67.142.164:80 | http://www.corel.com/akdlm/6763/downloads/pd/esd/WordPerfect/X9/Stub/Trial/WordPerfectOfficeX9STD_en.zip?__gda__=1529526636_56543bb3d91c16700e389d5ceb76b56e&ext=.zip | NL | — | — | whitelisted |
2508 | download.exe | POST | 200 | 52.35.122.223:80 | http://i.installportal.com/v1/logAnalytics | US | xml | 204 b | malicious |
2508 | download.exe | POST | 200 | 52.35.122.223:80 | http://www.installportal.com/v1/token | US | text | 239 b | malicious |
2508 | download.exe | POST | 200 | 52.35.122.223:80 | http://www.installportal.com/v1/token | US | text | 245 b | malicious |
2508 | download.exe | POST | 200 | 52.35.122.223:80 | http://www.installportal.com/v1/token | US | text | 239 b | malicious |
2508 | download.exe | POST | 200 | 52.35.122.223:80 | http://www.installportal.com/v1/token | US | text | 245 b | malicious |
2508 | download.exe | GET | — | 23.67.142.164:80 | http://www.corel.com/akdlm/6763/downloads/pd/esd/WordPerfect/X9/Stub/Trial/WordPerfectOfficeX9STD_en.zip?__gda__=1529526636_56543bb3d91c16700e389d5ceb76b56e&ext=.zip | NL | — | — | whitelisted |
2508 | download.exe | GET | 200 | 23.67.142.164:80 | http://www.corel.com/akdlm/6763/downloads/pd/esd/WordPerfect/X9/Stub/Trial/WordPerfectOfficeX9STD_en.zip.meta?__gda__=1529526636_016ee60c10d1bbe6076ccad5254af48e&ext=.meta | NL | binary | 7.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2508 | download.exe | 52.35.122.223:80 | i.installportal.com | Amazon.com, Inc. | US | malicious |
2508 | download.exe | 23.67.142.164:80 | www.corel.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i.installportal.com |
| unknown |
www.installportal.com |
| unknown |
www.corel.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3560 | CUH.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3560 | CUH.EXE | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |