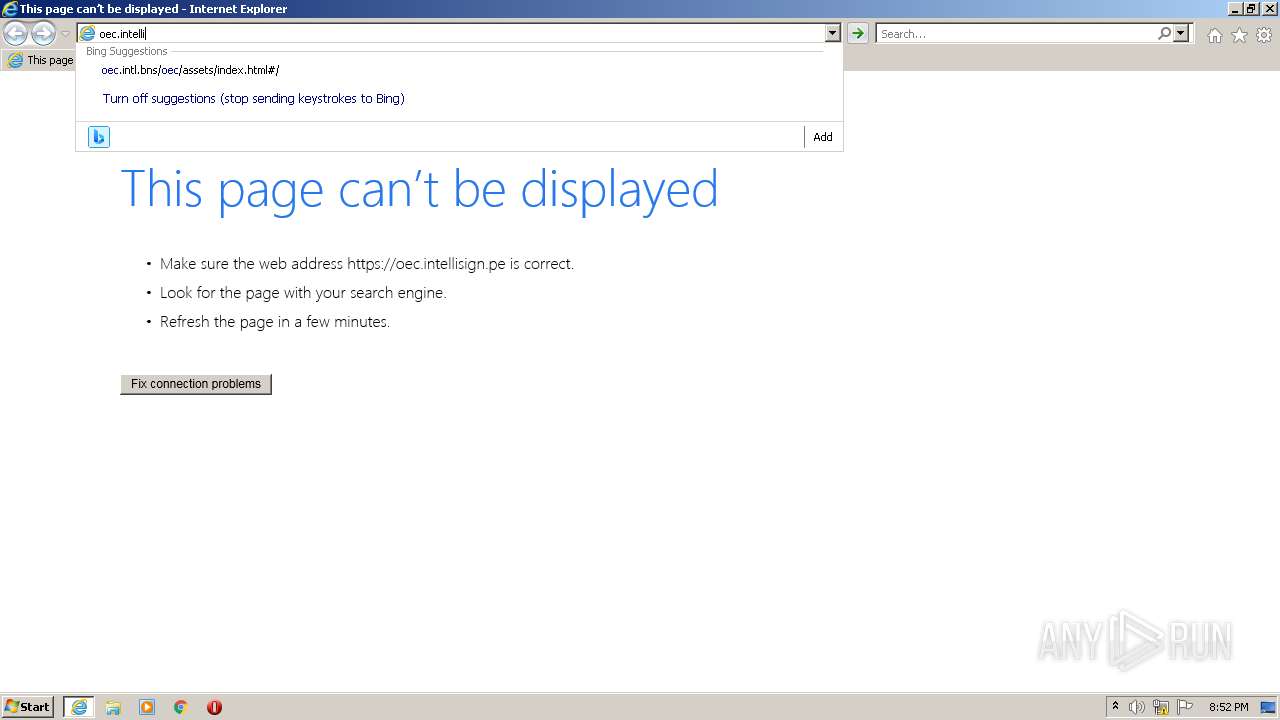
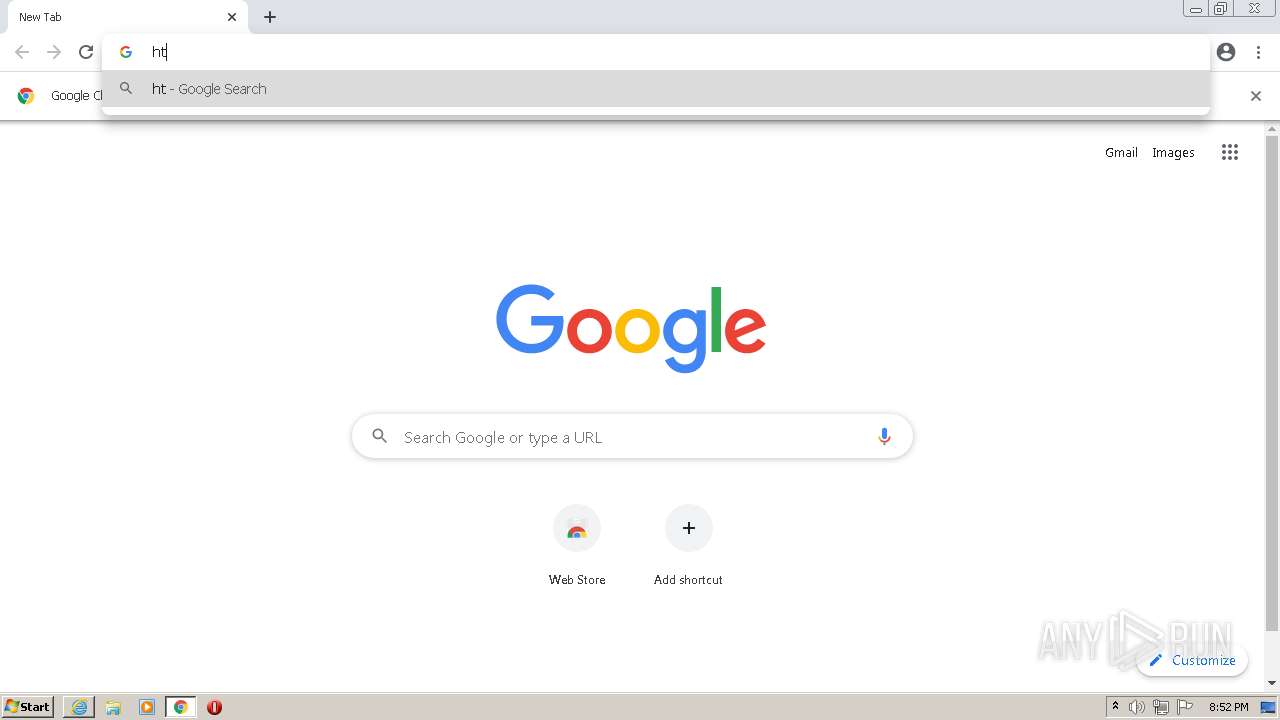
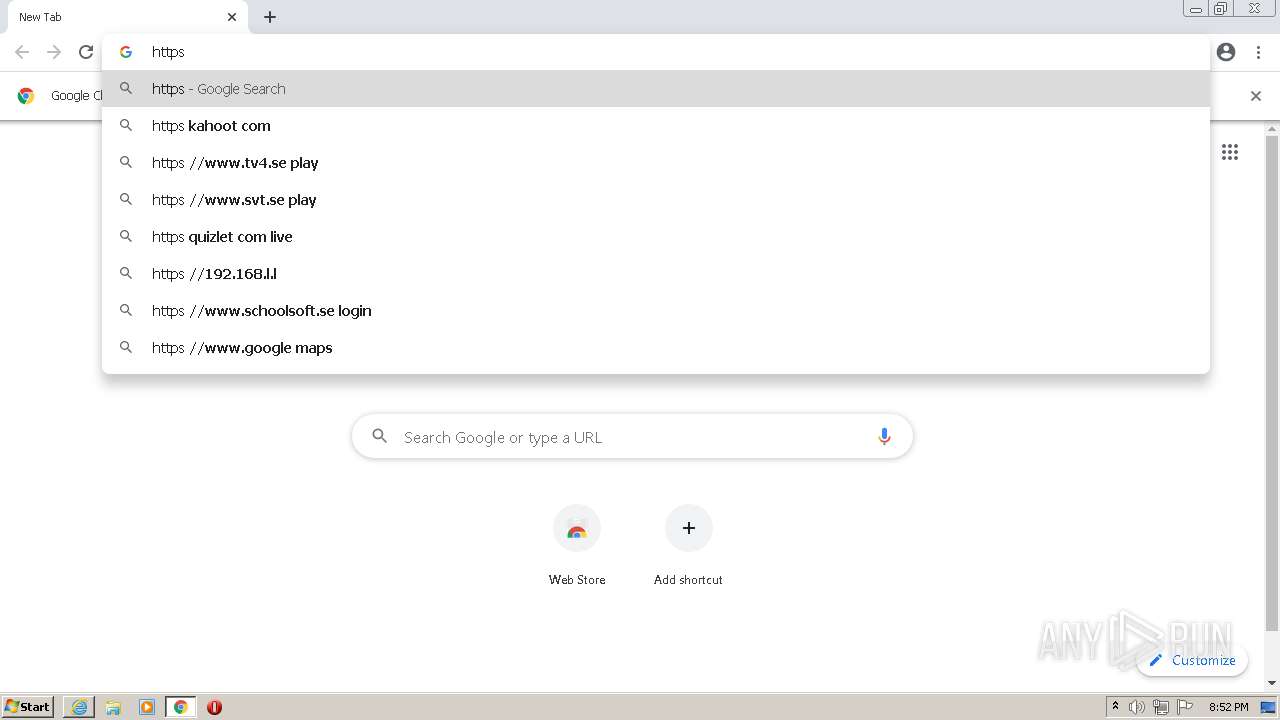
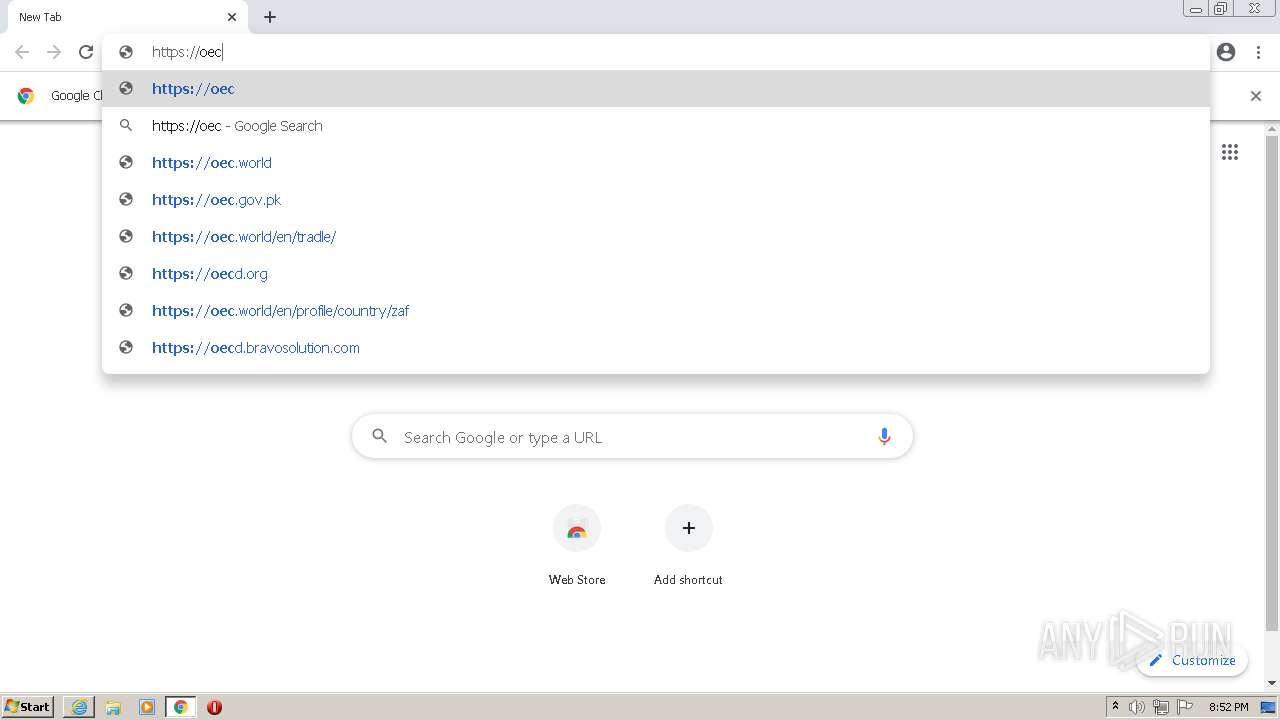
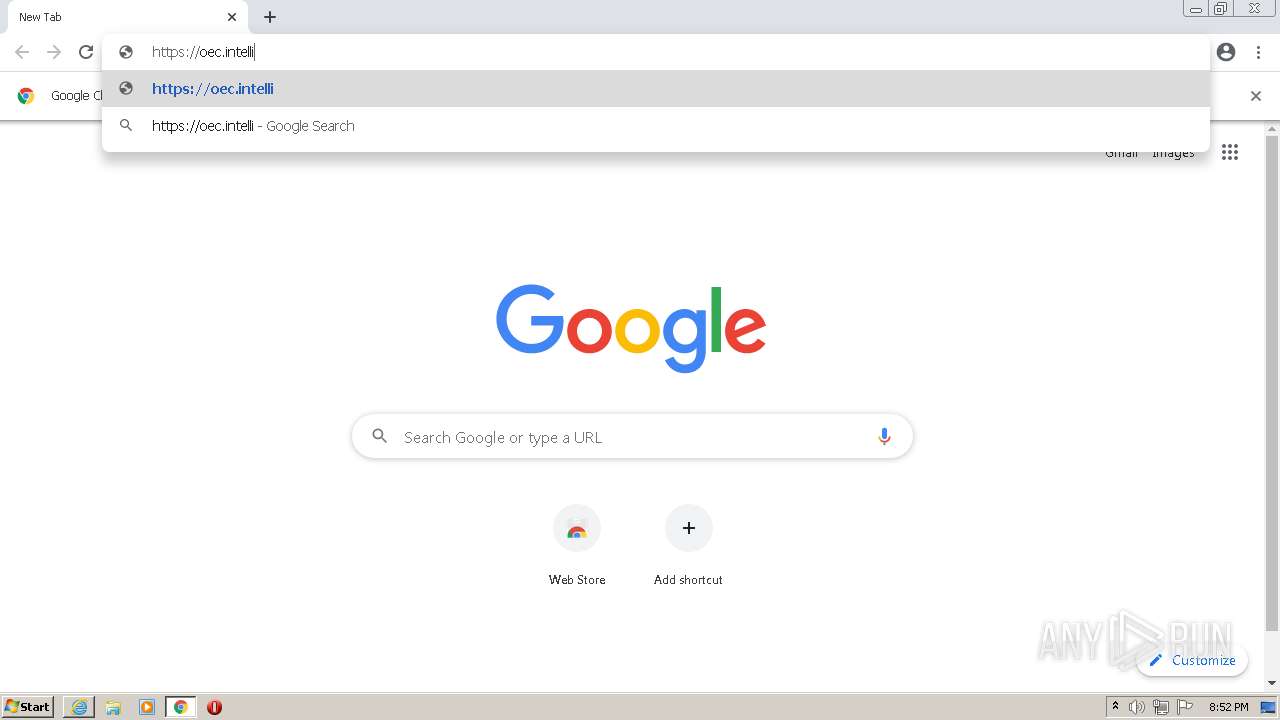
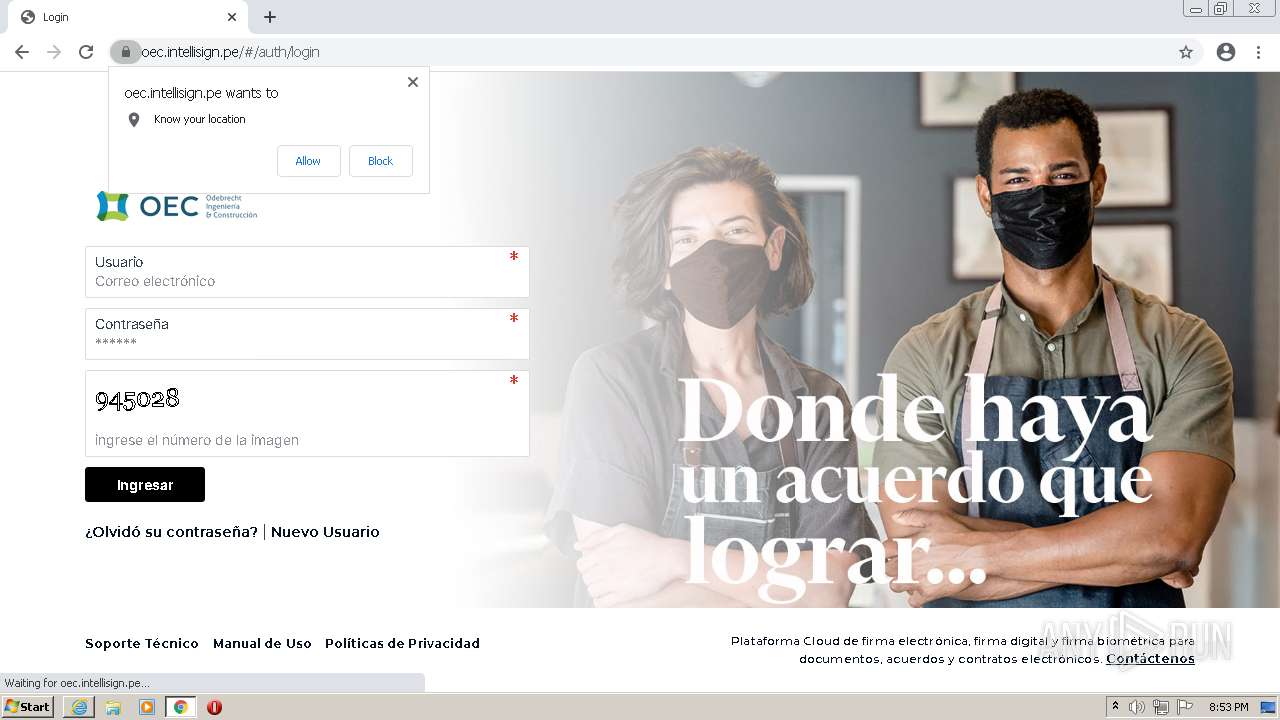
| URL: | https://oec.intellisign.pe |
| Full analysis: | https://app.any.run/tasks/f4697c02-3b30-4e1a-b308-d90298eb2640 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 19:50:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F18A324CD0F2B4FAF312BF35084AC8E4 |
| SHA1: | 4986CF0DA8A97ECB4565C33FE417498C6D1B01AF |
| SHA256: | 6649F3390B41DD5889CF3207F93088D6D814B4550389D4D3432D7CA24BE81346 |
| SSDEEP: | 3:N8JGG5CCn:2IG5CC |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 556)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1028)
- iexplore.exe (PID: 3048)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3692)
Drops a file with a compile date too recent
- chrome.exe (PID: 556)
Executable content was dropped or overwritten
- chrome.exe (PID: 556)
INFO
Checks supported languages
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 1028)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 864)
- chrome.exe (PID: 112)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3380)
- chrome.exe (PID: 1312)
- chrome.exe (PID: 580)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 1980)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 976)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 556)
Reads the computer name
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 1028)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 112)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 4012)
Changes internet zones settings
- iexplore.exe (PID: 3048)
Application launched itself
- iexplore.exe (PID: 3048)
- chrome.exe (PID: 3692)
Reads settings of System Certificates
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 1028)
- chrome.exe (PID: 3112)
Changes settings of System certificates
- iexplore.exe (PID: 3048)
Creates files in the user directory
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 1028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3048)
Reads internet explorer settings
- iexplore.exe (PID: 1028)
Checks Windows Trust Settings
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 1028)
Manual execution by user
- chrome.exe (PID: 3692)
Reads the hosts file
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3112)
Reads the date of Windows installation
- chrome.exe (PID: 3064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1008 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3048 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,8210475278250386249,11221871547783676739,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
31 264
Read events
30 984
Write events
270
Delete events
10
Modification events
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988330 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988330 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
206
Text files
425
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\49V5XY2O.txt | text | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\1EUTGUVR.txt | text | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\70KNFUHC.txt | text | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\U730ETHW.txt | text | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BRS1SC8J.txt | text | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\HEHFF5EI.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
122
DNS requests
70
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1028 | iexplore.exe | GET | 200 | 65.9.58.194:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1028 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSFvn094QJ%2BcWGTwWWEy%2BBXPZkW8AQUo8heZVTlMHjBBeoHCmpZzLn%2B3loCEAvX3vfCan3g4NSKil8i7k0%3D | US | der | 471 b | whitelisted |
1028 | iexplore.exe | GET | 200 | 99.86.1.61:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
1028 | iexplore.exe | GET | 200 | 99.86.1.61:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1028 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://zerossl.ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQILj%2F5BYz%2BinwYvRPv3x0WYHB6awQUyNl4aKLZGWjVPXLeXwo%2B3LWGhqYCEQDZ8YTGysdHnEaBbjF9lozw | US | der | 728 b | whitelisted |
3048 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1028 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1028 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEGxVq9vQB5LHnQcM2BGe1r8%3D | US | der | 2.18 Kb | whitelisted |
1028 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
1028 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3048 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1028 | iexplore.exe | 162.55.51.12:443 | oec.intellisign.pe | Hetzner Online GmbH | DE | suspicious |
3048 | iexplore.exe | 95.140.236.0:80 | ctldl.windowsupdate.com | LLNW | US | whitelisted |
3048 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3048 | iexplore.exe | 184.29.201.244:443 | go.microsoft.com | AKAMAI-AS | NL | suspicious |
3048 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3048 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3048 | iexplore.exe | 204.79.197.203:443 | www.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
1028 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1028 | iexplore.exe | 162.55.51.12:80 | oec.intellisign.pe | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
oec.intellisign.pe |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1028 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1028 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1028 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.xyz) |
1028 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1028 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.xyz) |
1028 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3112 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.xyz) |
3112 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |