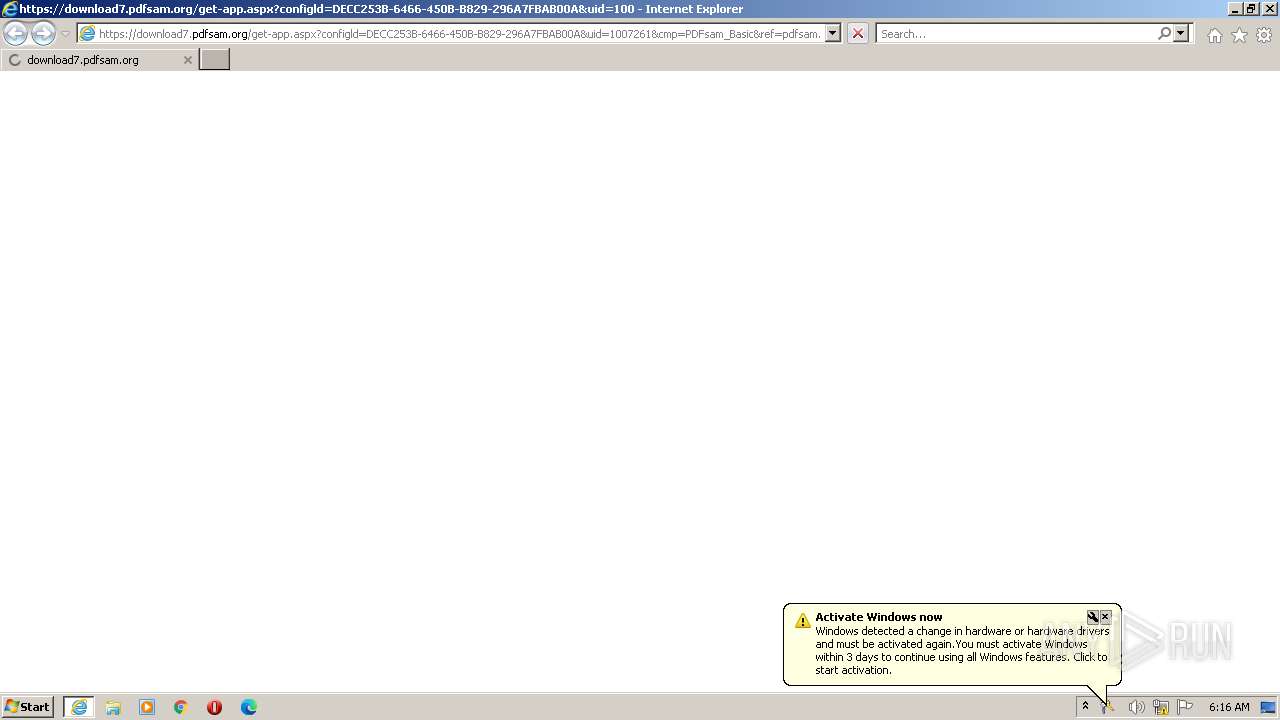
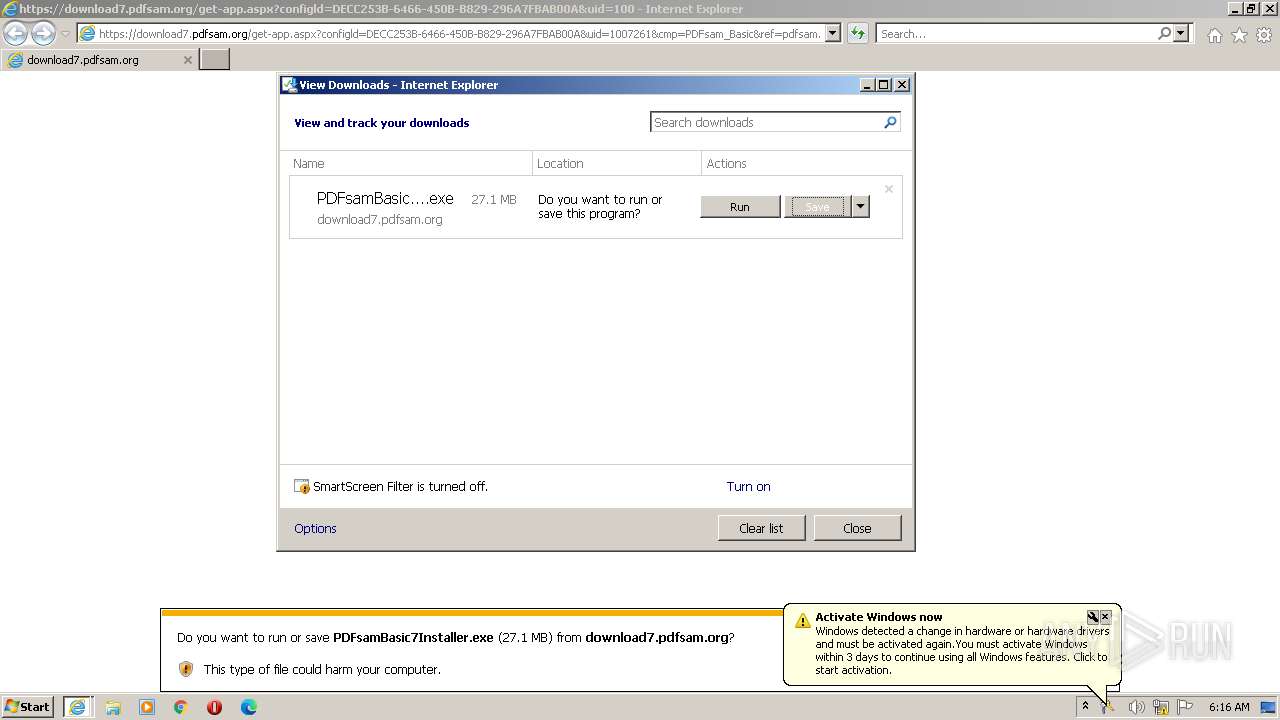
| URL: | https://download7.pdfsam.org/get-app.aspx?configld=DECC253B-6466-450B-B829-296A7FBAB00A&uid=1007261&cmp=PDFsam_Basic&ref=pdfsam.org/in-app&wid=6848 |
| Full analysis: | https://app.any.run/tasks/57b472ea-38f6-4eb6-a826-3168475f37fd |
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2023, 05:16:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E4B9E313A155F3C2B4239C97DA21E8C0 |
| SHA1: | CF49E14700AD90EEB88807AEF8F791324ECAAD22 |
| SHA256: | 663DEFF71DD3A60CEA014685D0FDE7E499D683A66693B111D1AC5CFF69DD850E |
| SSDEEP: | 3:N8SE8LTILKp7o8KuTg28MICA/kT5/kJIVYLEQXAEV1D2KuDS1d:2Sfo8Z8MIfkT5zVYwDi+Q |
MALICIOUS
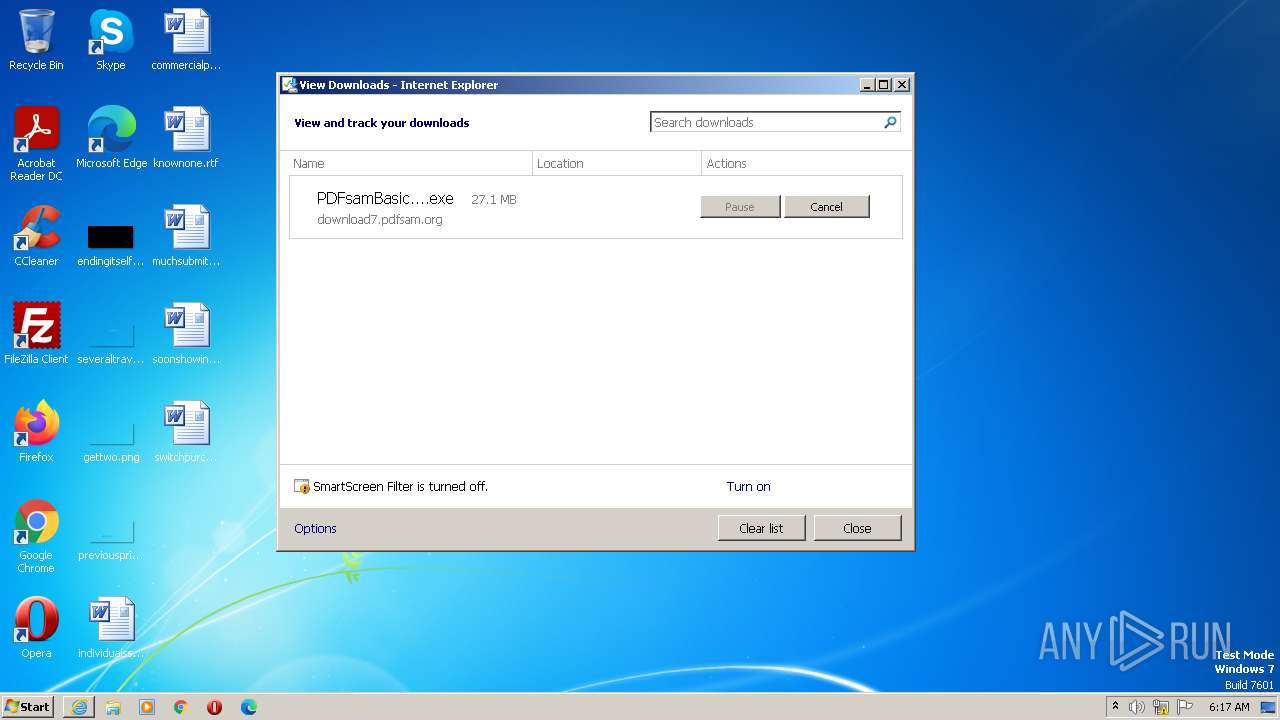
Application was dropped or rewritten from another process
- PDFsamBasic7Installer.exe (PID: 688)
- PDFsamBasic7Installer.exe (PID: 3424)
- PDFsam_Enhanced_7_Installer.exe (PID: 3180)
Registers / Runs the DLL via REGSVR32.EXE
- PDFsamBasic7Installer.exe (PID: 3424)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 4016)
- dllhost.exe (PID: 2704)
SUSPICIOUS
Reads the Internet Settings
- PDFsamBasic7Installer.exe (PID: 3424)
Reads settings of System Certificates
- PDFsamBasic7Installer.exe (PID: 3424)
Executable content was dropped or overwritten
- PDFsamBasic7Installer.exe (PID: 3424)
Checks Windows Trust Settings
- PDFsamBasic7Installer.exe (PID: 3424)
Reads security settings of Internet Explorer
- PDFsamBasic7Installer.exe (PID: 3424)
Adds/modifies Windows certificates
- iexplore.exe (PID: 3404)
INFO
Application launched itself
- iexplore.exe (PID: 3404)
- msedge.exe (PID: 2808)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3568)
Creates files in the program directory
- PDFsamBasic7Installer.exe (PID: 3424)
Checks supported languages
- PDFsamBasic7Installer.exe (PID: 3424)
- msiexec.exe (PID: 3200)
- PDFsam_Enhanced_7_Installer.exe (PID: 3180)
The process uses the downloaded file
- iexplore.exe (PID: 3404)
Reads the computer name
- PDFsamBasic7Installer.exe (PID: 3424)
- msiexec.exe (PID: 3200)
- PDFsam_Enhanced_7_Installer.exe (PID: 3180)
The process checks LSA protection
- PDFsamBasic7Installer.exe (PID: 3424)
- dllhost.exe (PID: 2704)
- msiexec.exe (PID: 3200)
Reads the machine GUID from the registry
- PDFsamBasic7Installer.exe (PID: 3424)
- msiexec.exe (PID: 3200)
Checks proxy server information
- PDFsamBasic7Installer.exe (PID: 3424)
Loads dropped or rewritten executable
- PDFsamBasic7Installer.exe (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 688 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\PDFsamBasic7Installer.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\PDFsamBasic7Installer.exe | — | iexplore.exe | |||||||||||
User: admin Company: Andrea Vacondio Integrity Level: MEDIUM Description: PDFsam Basic Installer Exit code: 3221226540 Version: 7.0.70.1815 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1504 --field-trial-handle=1256,i,16107199452697785701,9680329530134205661,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe" --from-ie-to-edge=3 --ie-frame-hwnd=20134 | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IEToEdge BHO Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1240 --field-trial-handle=1256,i,16107199452697785701,9680329530134205661,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe" --from-ie-to-edge=3 --ie-frame-hwnd=20134 | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: IEToEdge BHO Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2736 --field-trial-handle=1256,i,16107199452697785701,9680329530134205661,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe" --create-cache-container=0 | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: IEToEdge BHO Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe" --create-cache-container=0 | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\BHO\ie_to_edge_stub.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IEToEdge BHO Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1592 --field-trial-handle=1256,i,16107199452697785701,9680329530134205661,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2704 | C:\Windows\system32\DllHost.exe /Processid:{77EC23C5-BB68-4A7B-AE5C-F4AD0B6C678D} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 144
Read events
19 913
Write events
168
Delete events
63
Modification events
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3404) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
29
Text files
53
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF21feb2.TMP | — | |
MD5:— | SHA256:— | |||
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF21fec2.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:61FE7896F9494DCDF53480A325F4FB85 | SHA256:ACFD3CD36E0DFCF1DCB67C7F31F2A5B9BA0815528A0C604D4330DFAA9E683E51 | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4B3D1CD03E2BE9D4F9CDDE390F5EFE31_FF56184787F7D49B5E867B72B3D823DD | binary | |
MD5:4A5F045011D551F0615FE8F21556A56E | SHA256:8612E526341A6740CF97D750733D13965D5977A5001799177853937EDA0FEE9D | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:39119423BA06A66D128E916D4E45E997 | SHA256:DFF2584213AA7E17F2CF2AB7713350C0C7688BAB6B9C670B7727E2BC90560CA9 | |||
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\7f9ba9ba-25d0-47ee-9642-479e714c411d.tmp | text | |
MD5:0009C36CA7761CD8D8A132AB78028EDB | SHA256:DEE4EE3C386957B71A17571C1C01818057D4B1F8C6B449435904F3A6CC71D28D | |||
| 2808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:A2B913D3BC9B6344C76B056712064197 | SHA256:CC7E7F39A2B36FFD7D6EC45A4AA70BFB8DBEBC58EEB784D08218B0036D3AD564 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
38
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | PDFsamBasic7Installer.exe | GET | 301 | 188.114.97.3:80 | http://pdfsam.org/msi-v3/ | US | — | — | malicious |
3568 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e76df639bacde33e | US | compressed | 4.70 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?21968b665342f966 | US | compressed | 4.70 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEH1NQqkrQx1%2BZFPnwZqNWHc%3D | US | binary | 1.41 Kb | whitelisted |
3404 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/alphasslcasha256g4/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSPdwLcDiHQXlVfp8h37hrpMerTggQUT8usqMLvq92Db2u%2Fzpg9XFgldhUCDHVdlFc8LqTiH1q02w%3D%3D | US | binary | 1.40 Kb | whitelisted |
3404 | iexplore.exe | GET | — | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bb453cf6997c3af9 | US | — | — | whitelisted |
3404 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3568 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?775cbff18d4e327b | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1068 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3568 | iexplore.exe | 64.15.159.234:443 | api-updateservice.pdfsam.org | IWEB-AS | CA | suspicious |
3568 | iexplore.exe | 104.84.243.180:443 | go.microsoft.com | AKAMAI-AS | GB | suspicious |
3568 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3568 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3404 | iexplore.exe | 2.18.66.48:443 | www.bing.com | Akamai International B.V. | GB | suspicious |
3568 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
config.edge.skype.com |
| malicious |
edge.microsoft.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |