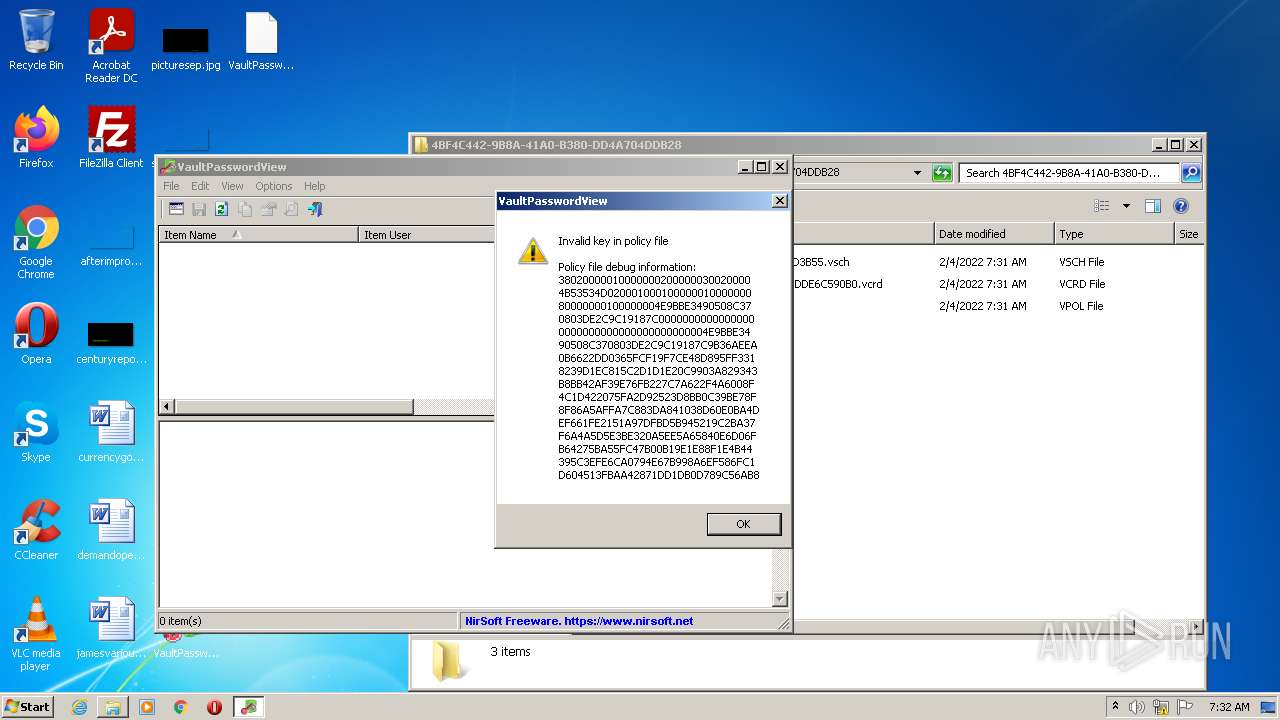
| File name: | VaultPasswordView.exe |
| Full analysis: | https://app.any.run/tasks/667324ab-40bc-48ec-98a8-132cee12f70f |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2022, 07:30:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D1893679CC3B56D6E2E8BBDEF957BEC2 |
| SHA1: | 928C6022F3166FC73CE3BAA1F668AEF429D70706 |
| SHA256: | 66226AF4C1DBF01C3835EFB83E18460598BBAECA062B1C96248BA6445794F9F7 |
| SSDEEP: | 3072:UcC4Dov7AK/M3y8gIAlU8TLiEkY0iDY7JXzL:UbJ7p0PAlU8vi/iGL |
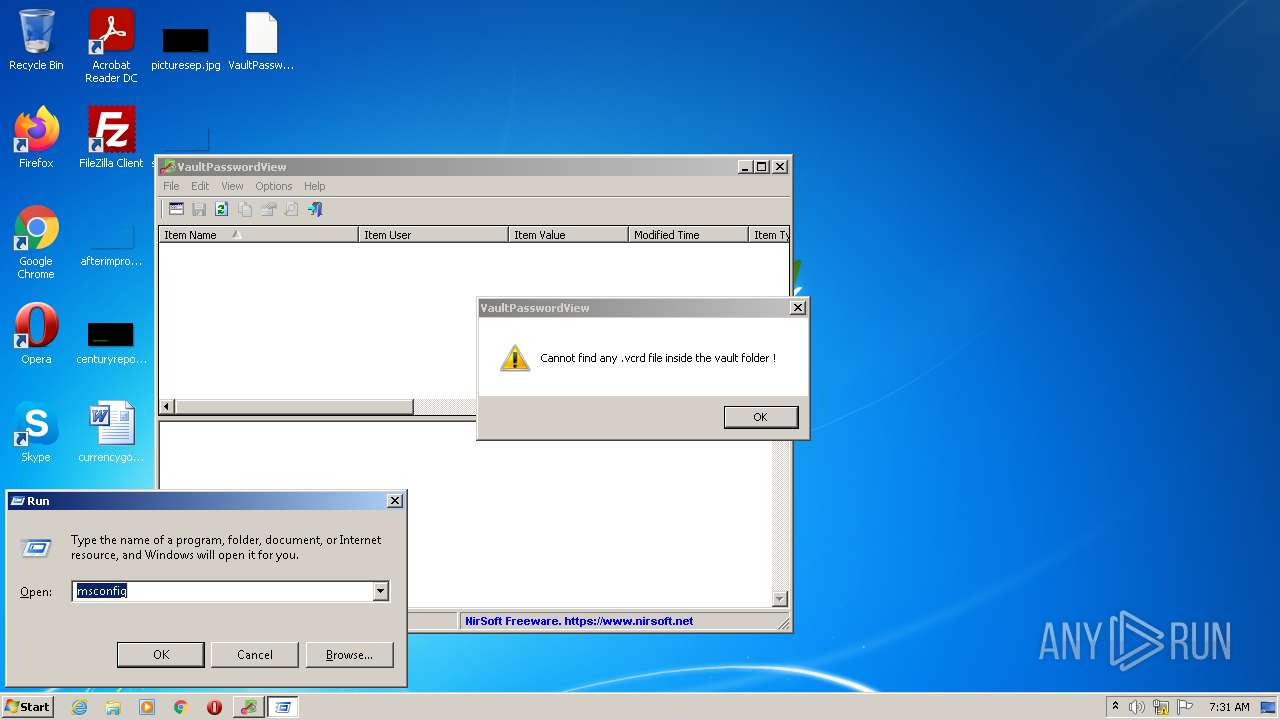
MALICIOUS
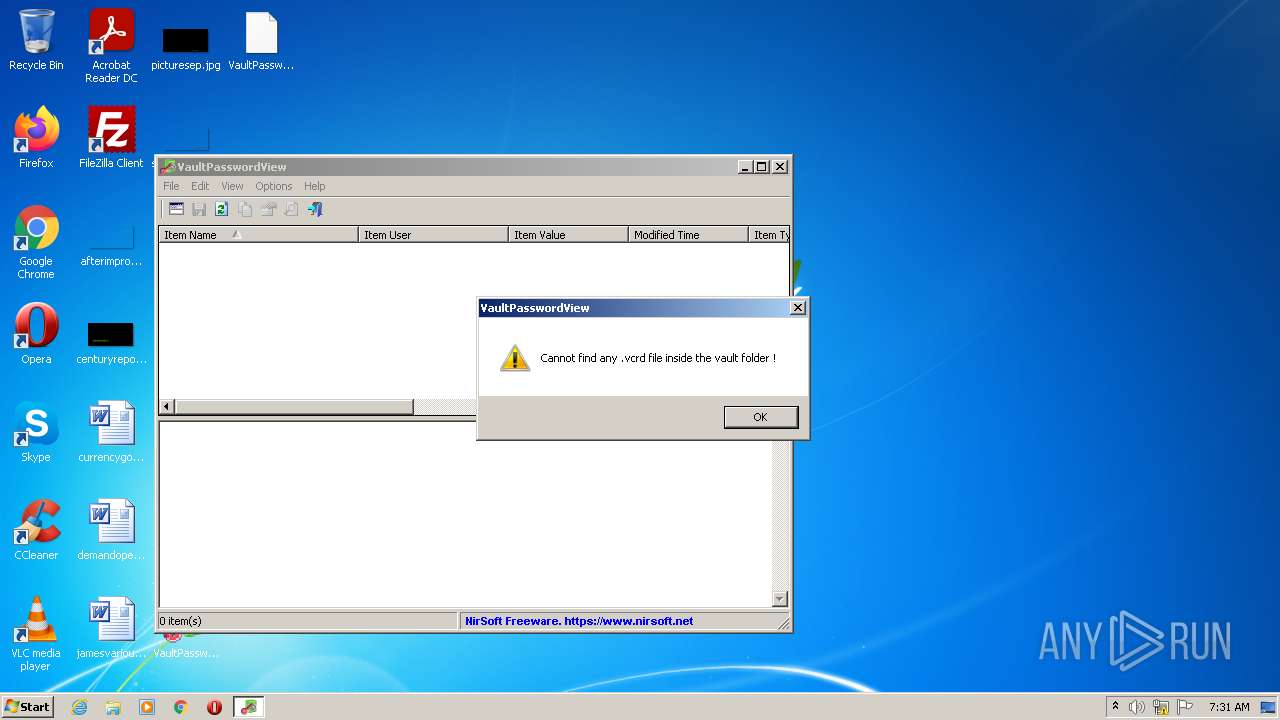
Application was injected by another process
- lsass.exe (PID: 992)
Runs injected code in another process
- VaultPasswordView.exe (PID: 3648)
- VaultPasswordView.exe (PID: 3644)
- VaultPasswordView.exe (PID: 1212)
SUSPICIOUS
Checks supported languages
- VaultPasswordView.exe (PID: 1148)
- VaultPasswordView.exe (PID: 4016)
- VaultPasswordView.exe (PID: 2912)
- VaultPasswordView.exe (PID: 3648)
- VaultPasswordView.exe (PID: 3644)
- VaultPasswordView.exe (PID: 1972)
- VaultPasswordView.exe (PID: 1212)
Reads the computer name
- VaultPasswordView.exe (PID: 1148)
- VaultPasswordView.exe (PID: 4016)
- VaultPasswordView.exe (PID: 2912)
- VaultPasswordView.exe (PID: 1972)
- VaultPasswordView.exe (PID: 3648)
- VaultPasswordView.exe (PID: 1212)
- VaultPasswordView.exe (PID: 3644)
Application launched itself
- VaultPasswordView.exe (PID: 2912)
- VaultPasswordView.exe (PID: 1972)
INFO
Checks supported languages
- VaultCmd.exe (PID: 3452)
Reads the computer name
- VaultCmd.exe (PID: 3452)
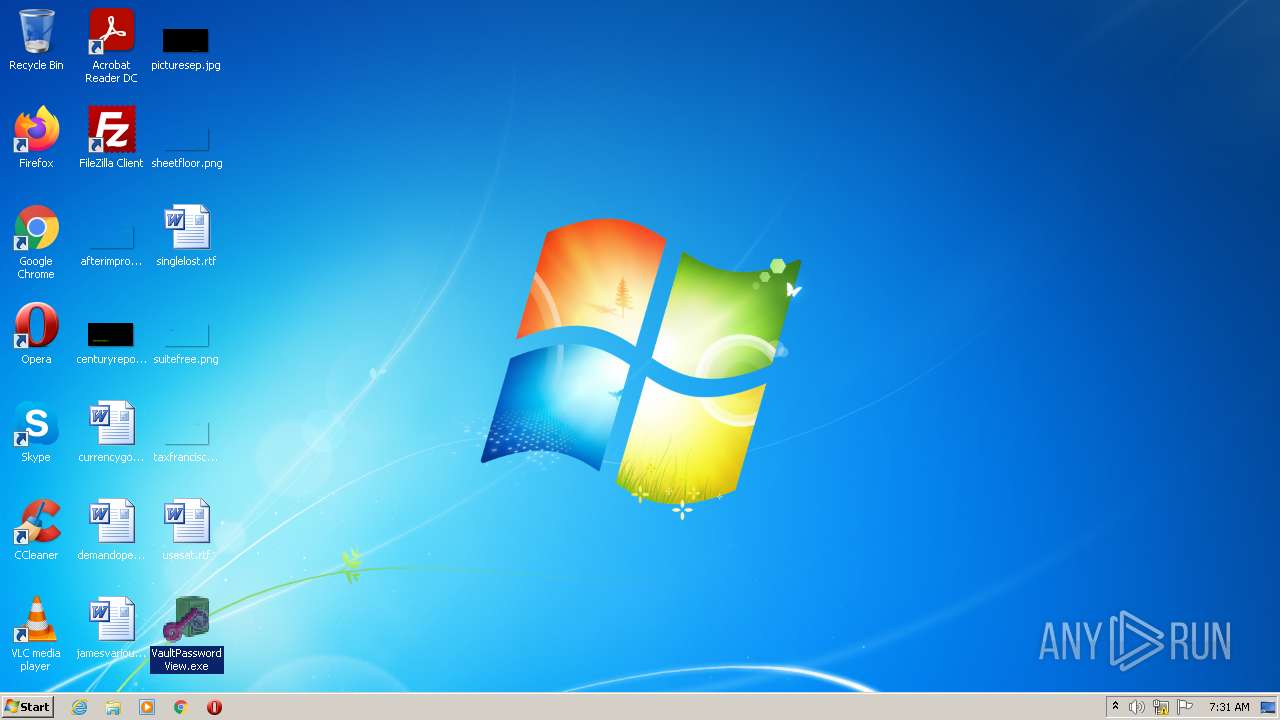
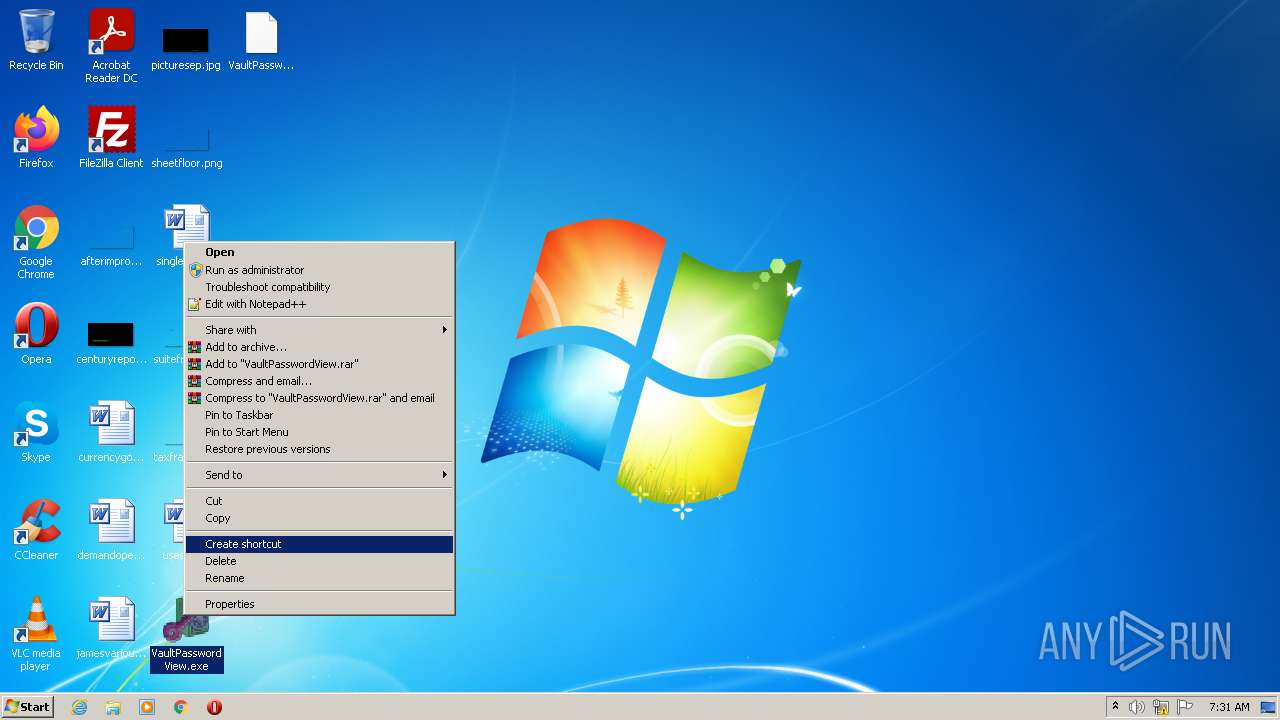
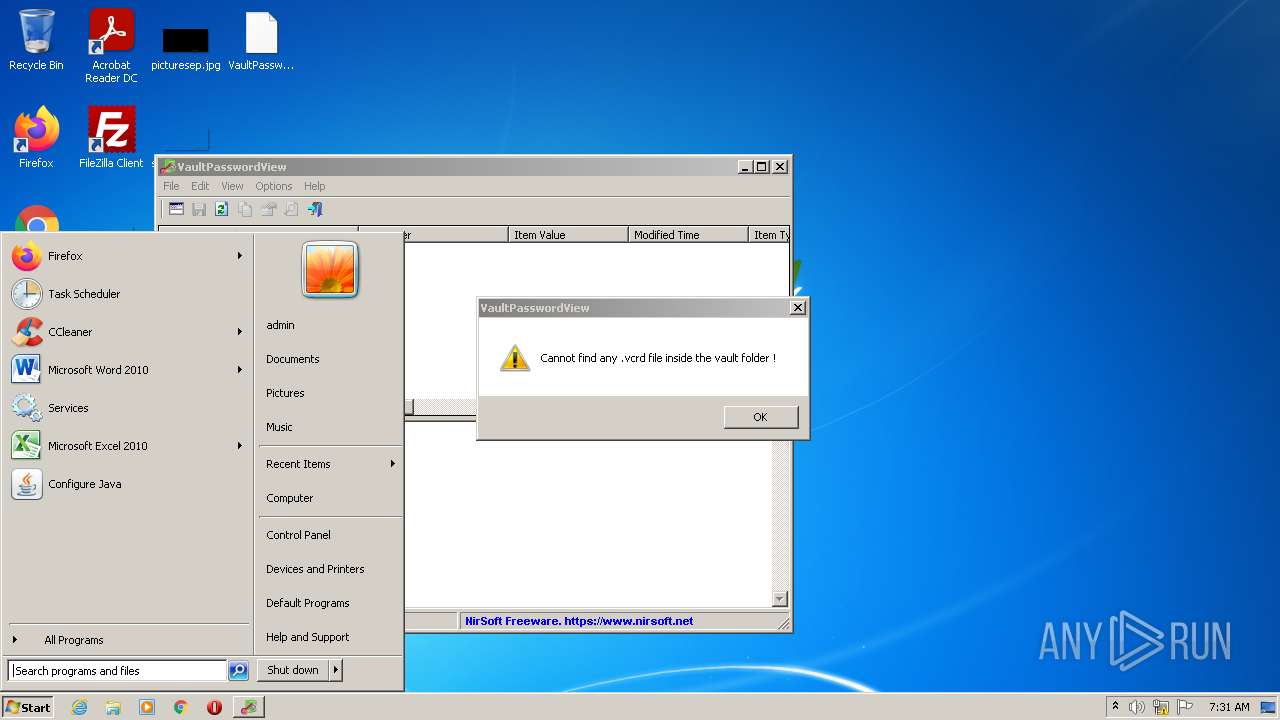
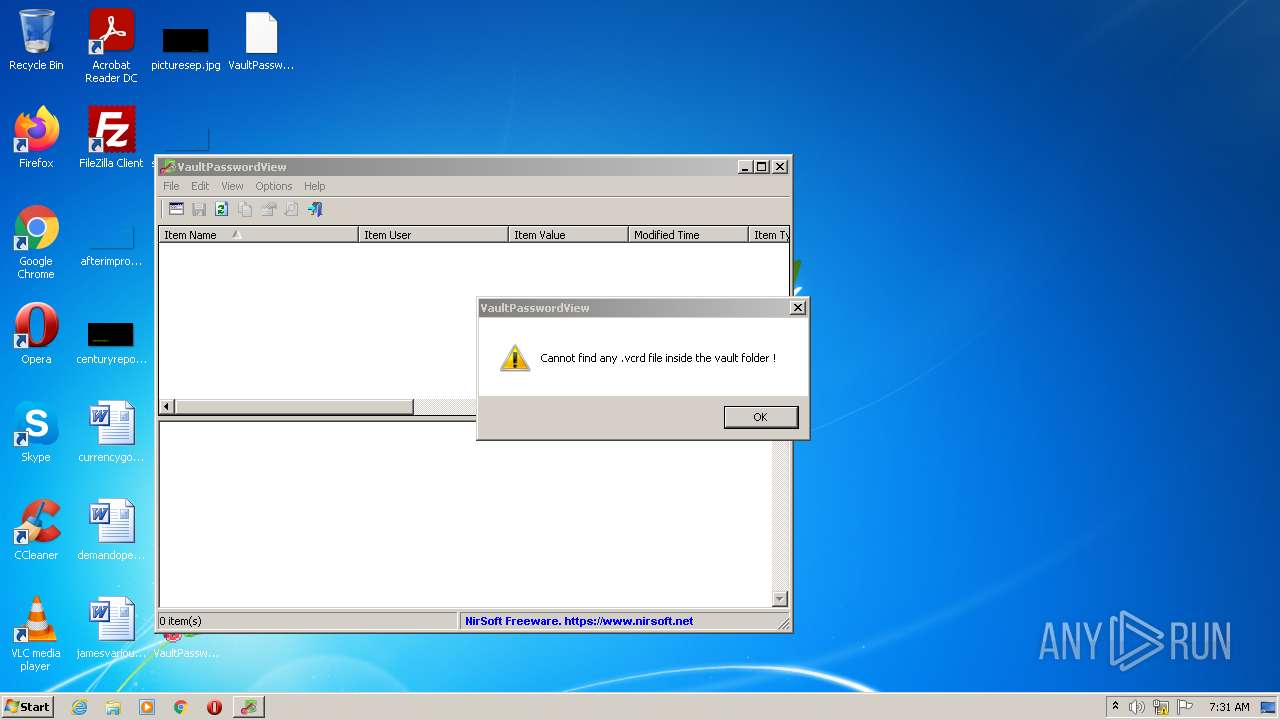
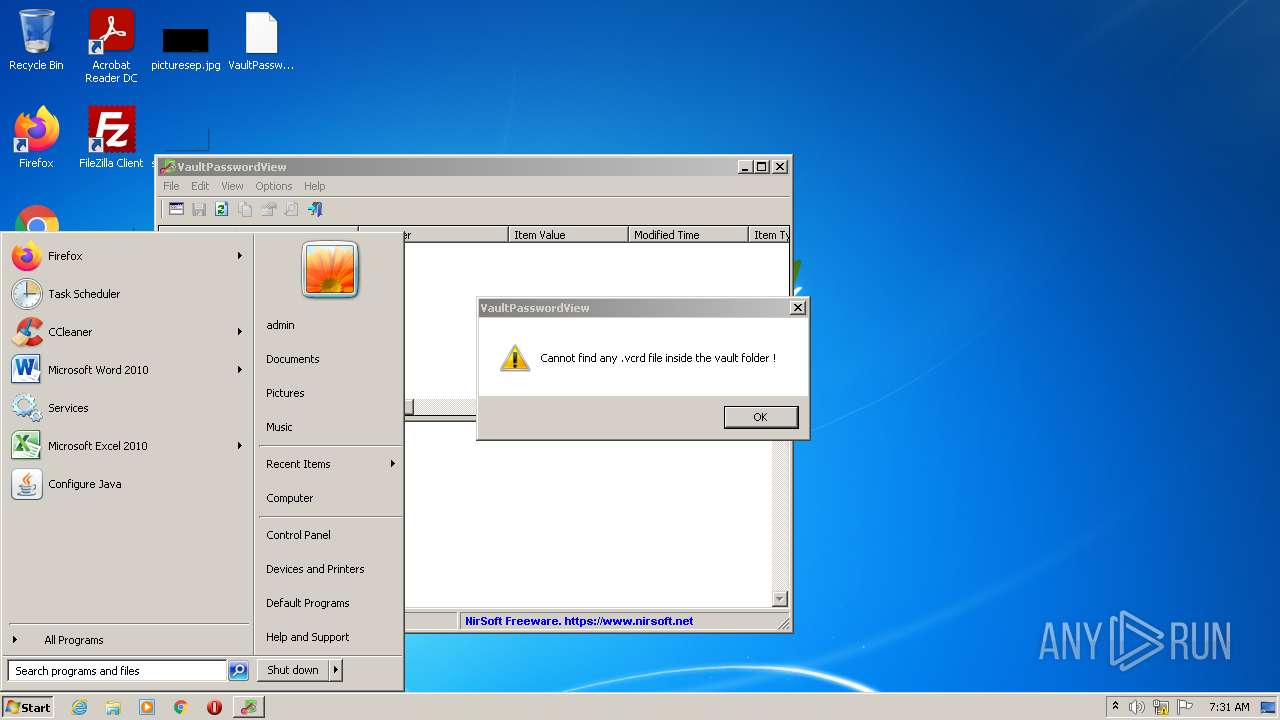
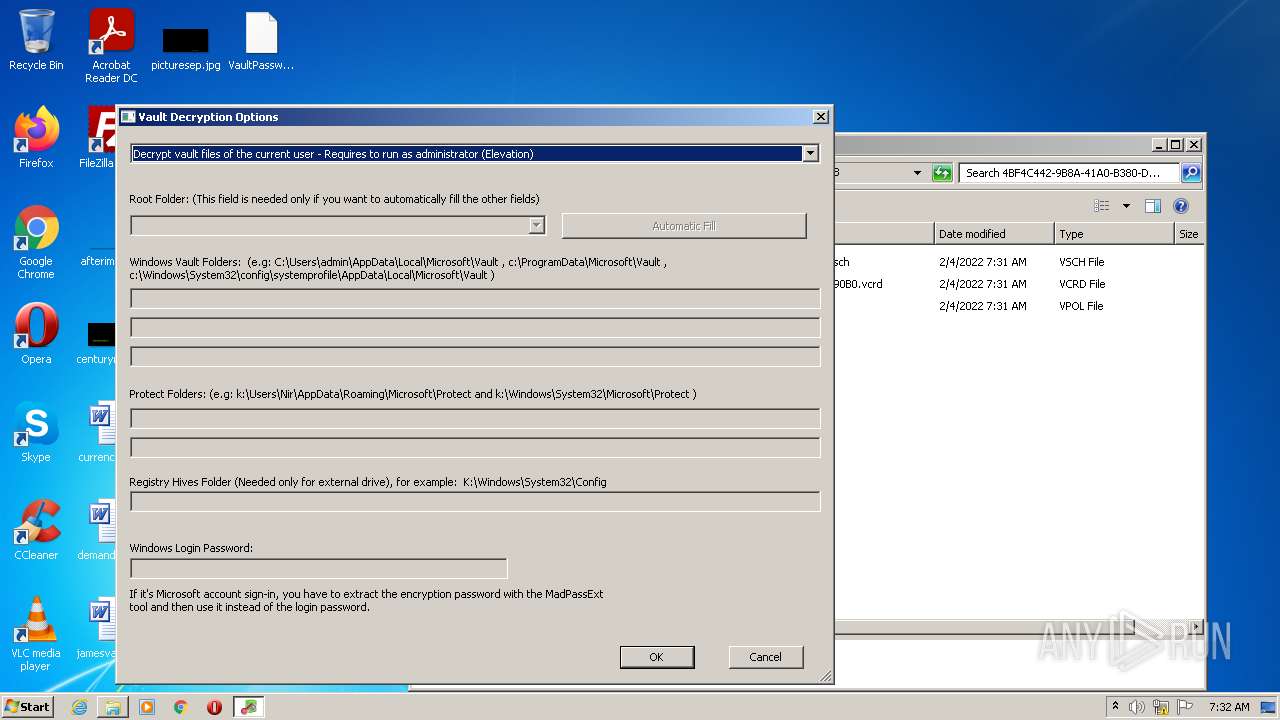
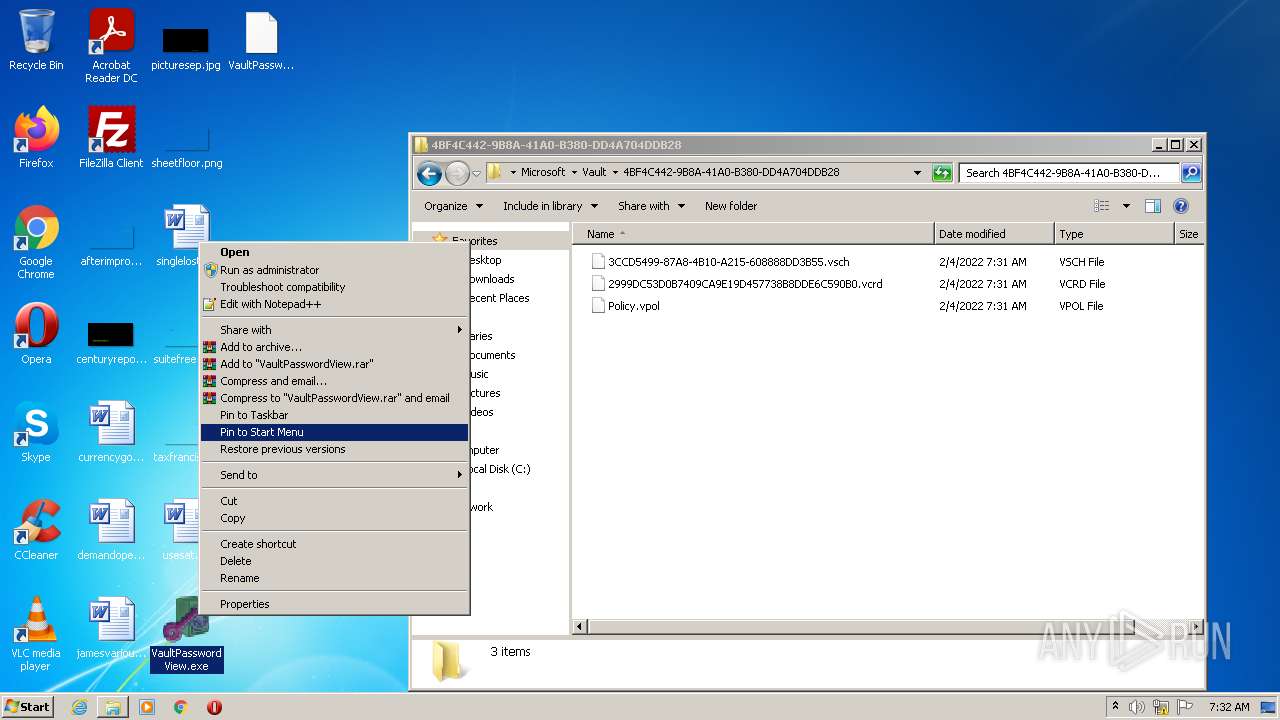
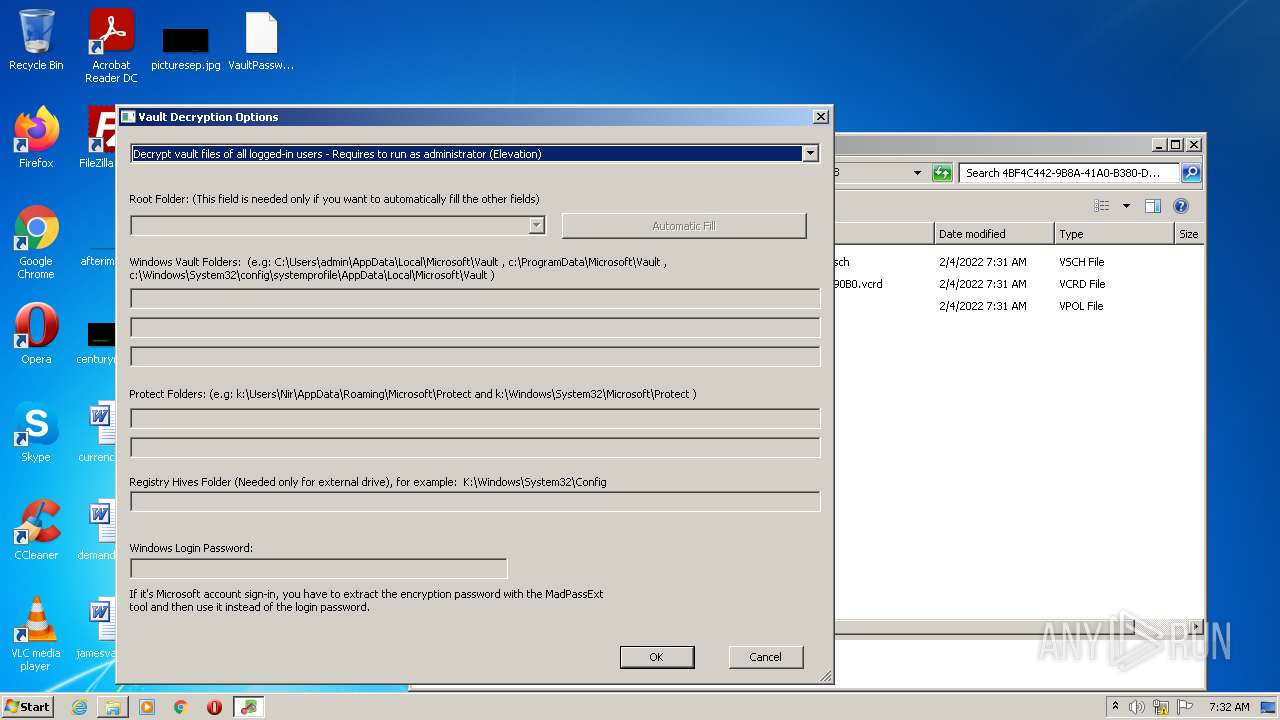
Manual execution by user
- VaultPasswordView.exe (PID: 1148)
- VaultPasswordView.exe (PID: 4016)
- VaultPasswordView.exe (PID: 2912)
- VaultPasswordView.exe (PID: 1972)
- VaultPasswordView.exe (PID: 3648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| ProductVersion: | 1.11 |
|---|---|
| ProductName: | VaultPasswordView |
| OriginalFileName: | VaultPasswordView.exe |
| LegalCopyright: | Copyright © 2016 - 2021 Nir Sofer |
| InternalName: | VaultPasswordView |
| FileVersion: | 1.11 |
| FileDescription: | VaultPasswordView |
| CompanyName: | NirSoft |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.1.1.0 |
| FileVersionNumber: | 1.1.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1228 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 39936 |
| CodeSize: | 72704 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2021:12:26 13:45:56+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Dec-2021 12:45:56 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | NirSoft |
| FileDescription: | VaultPasswordView |
| FileVersion: | 1.11 |
| InternalName: | VaultPasswordView |
| LegalCopyright: | Copyright © 2016 - 2021 Nir Sofer |
| OriginalFilename: | VaultPasswordView.exe |
| ProductName: | VaultPasswordView |
| ProductVersion: | 1.11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Dec-2021 12:45:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011A13 | 0x00011C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41205 |
.rdata | 0x00013000 | 0x00003840 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81562 |
.data | 0x00017000 | 0x00001BCC | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.1731 |
.rsrc | 0x00019000 | 0x00005D90 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09121 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40431 | 1093 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.27305 | 308 | Latin 1 / Western European | Hebrew - Israel | RT_CURSOR |
3 | 5.64941 | 4264 | Latin 1 / Western European | Hebrew - Israel | RT_ICON |
4 | 6.12408 | 1128 | Latin 1 / Western European | Hebrew - Israel | RT_ICON |
5 | 2.29623 | 296 | Latin 1 / Western European | Hebrew - Israel | RT_ICON |
32 | 3.03744 | 280 | Latin 1 / Western European | English - United States | RT_STRING |
51 | 3.05945 | 524 | Latin 1 / Western European | English - United States | RT_STRING |
57 | 3.11618 | 672 | Latin 1 / Western European | English - United States | RT_STRING |
58 | 2.5562 | 128 | Latin 1 / Western European | English - United States | RT_STRING |
63 | 2.91969 | 176 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
comdlg32.dll |
msvcrt.dll |
Total processes
61
Monitored processes
9
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | C:\Windows\system32\lsass.exe | C:\Windows\system32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7601.24545 (win7sp1_ldr_escrow.200102-1707) Modules
| |||||||||||||||
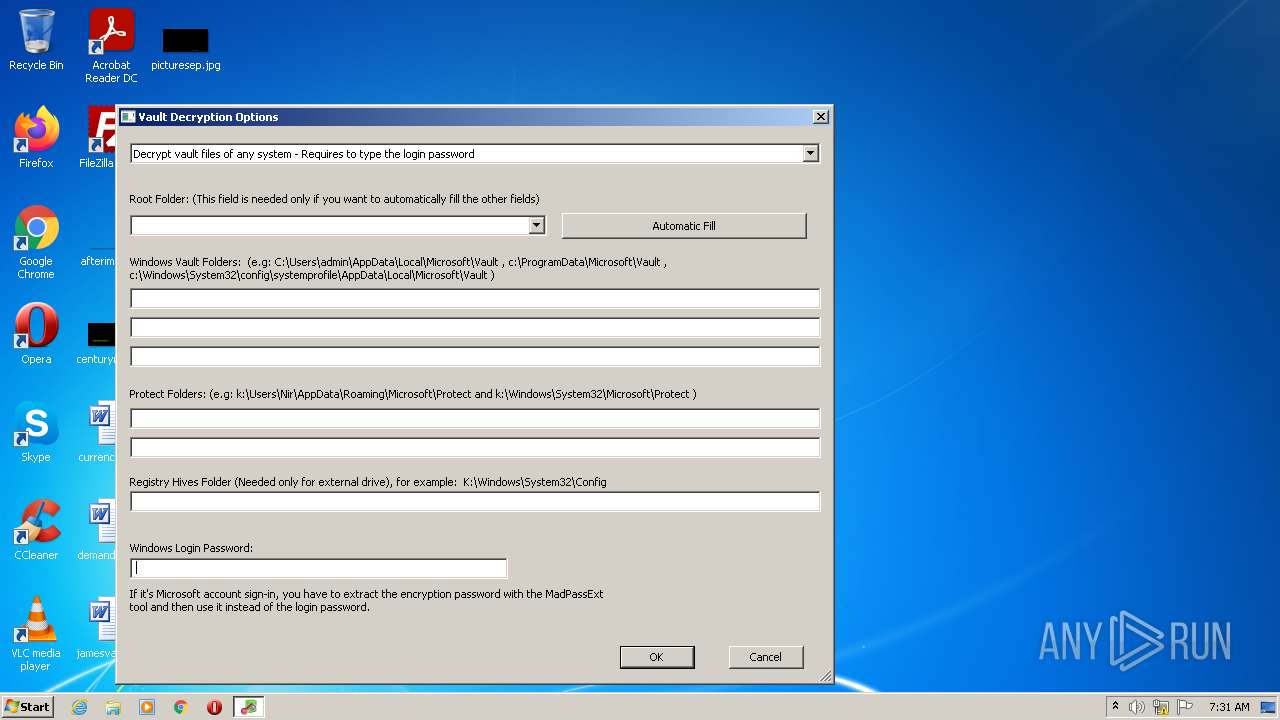
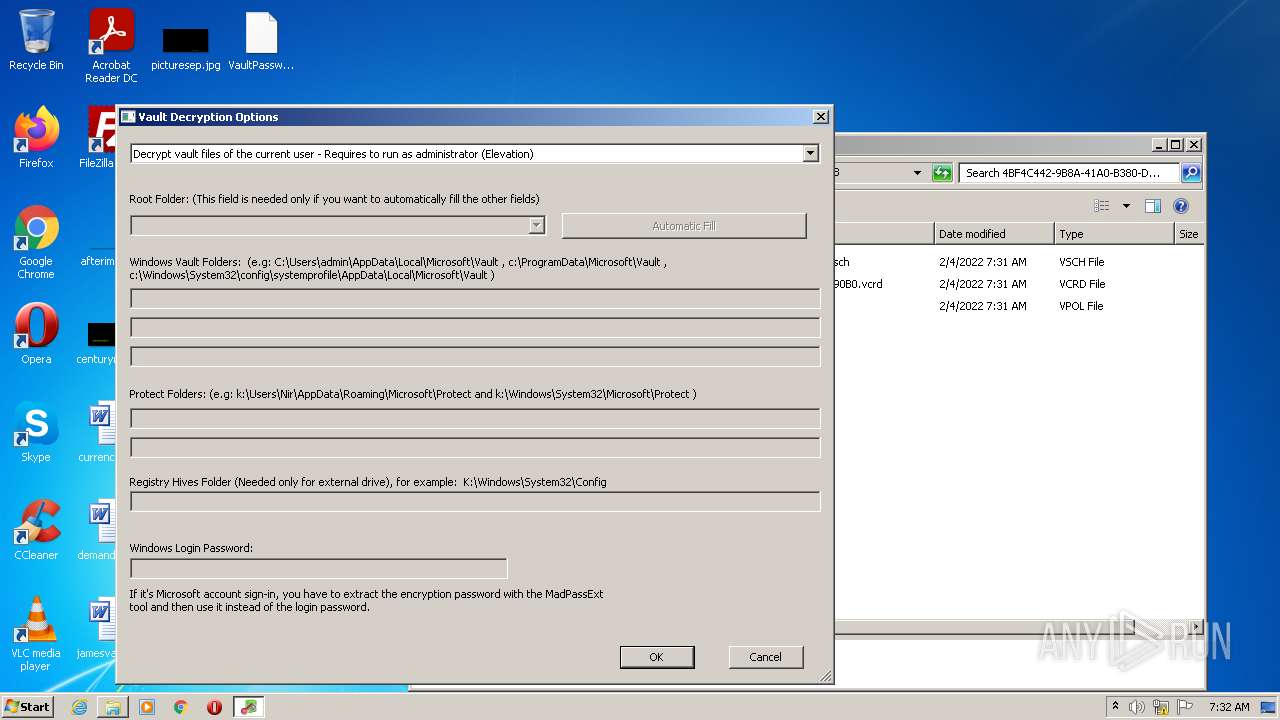
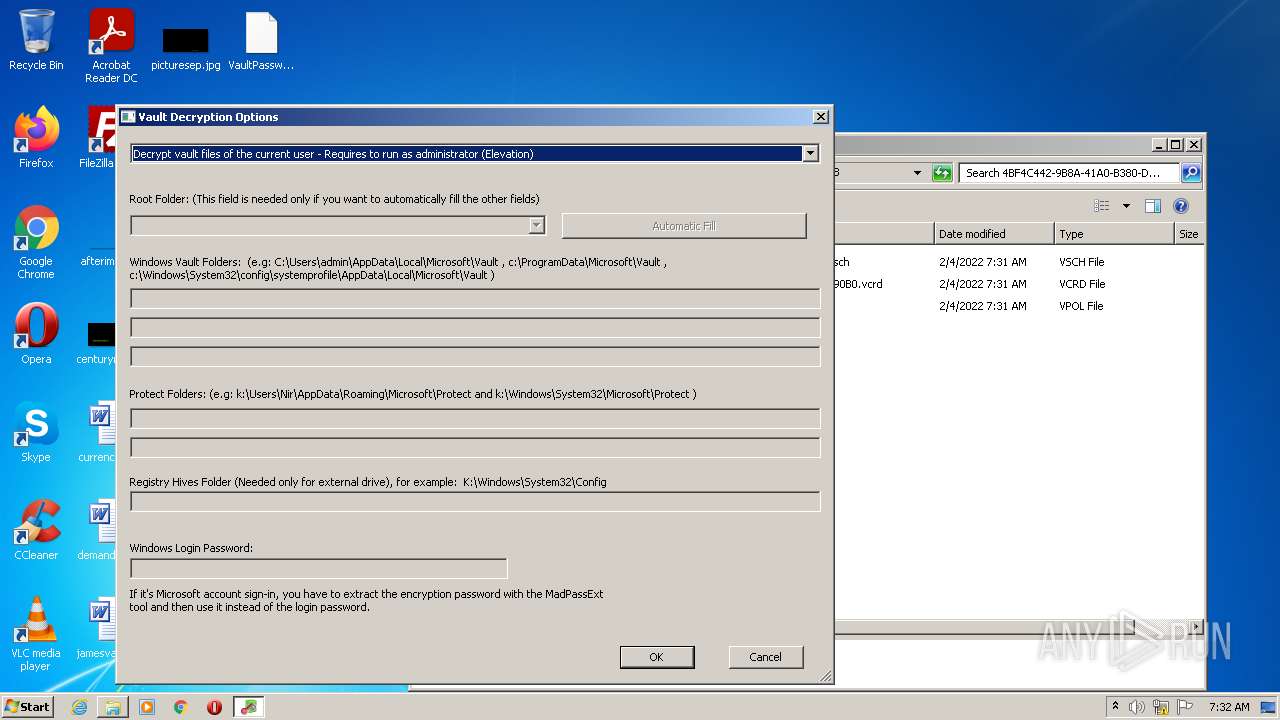
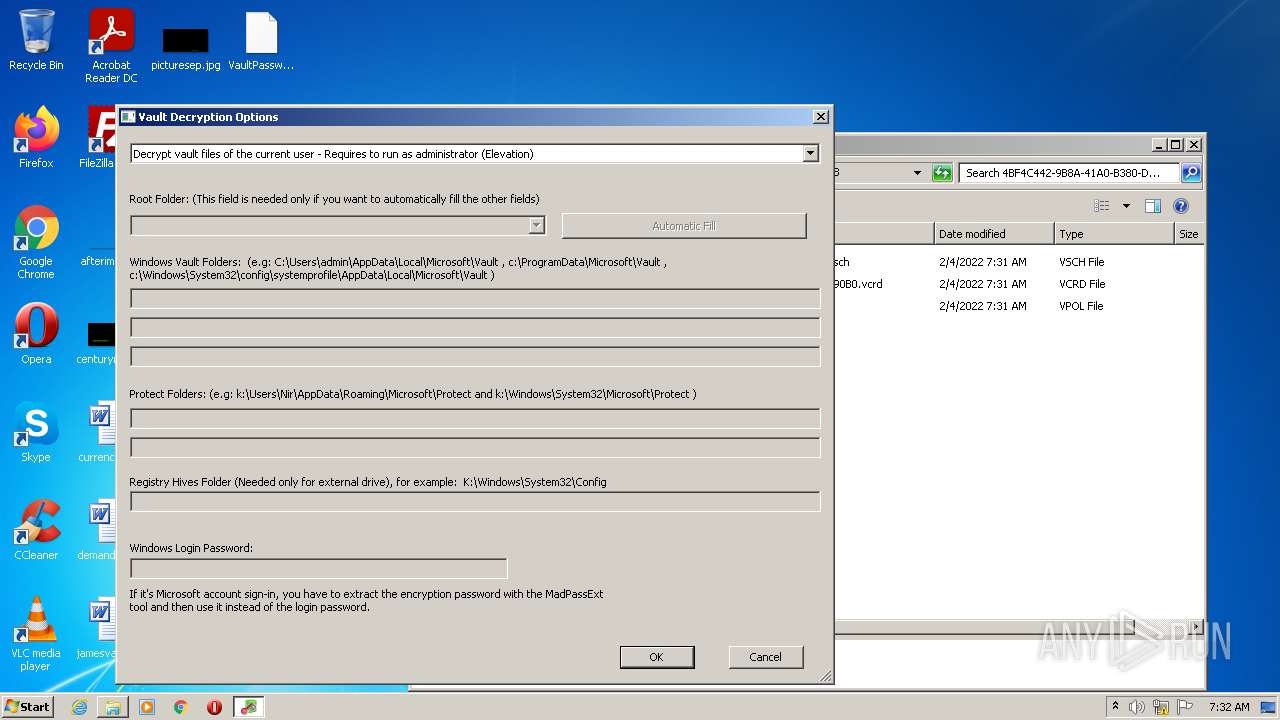
| 1148 | "C:\Users\admin\Desktop\VaultPasswordView.exe" | C:\Users\admin\Desktop\VaultPasswordView.exe | — | Explorer.EXE | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
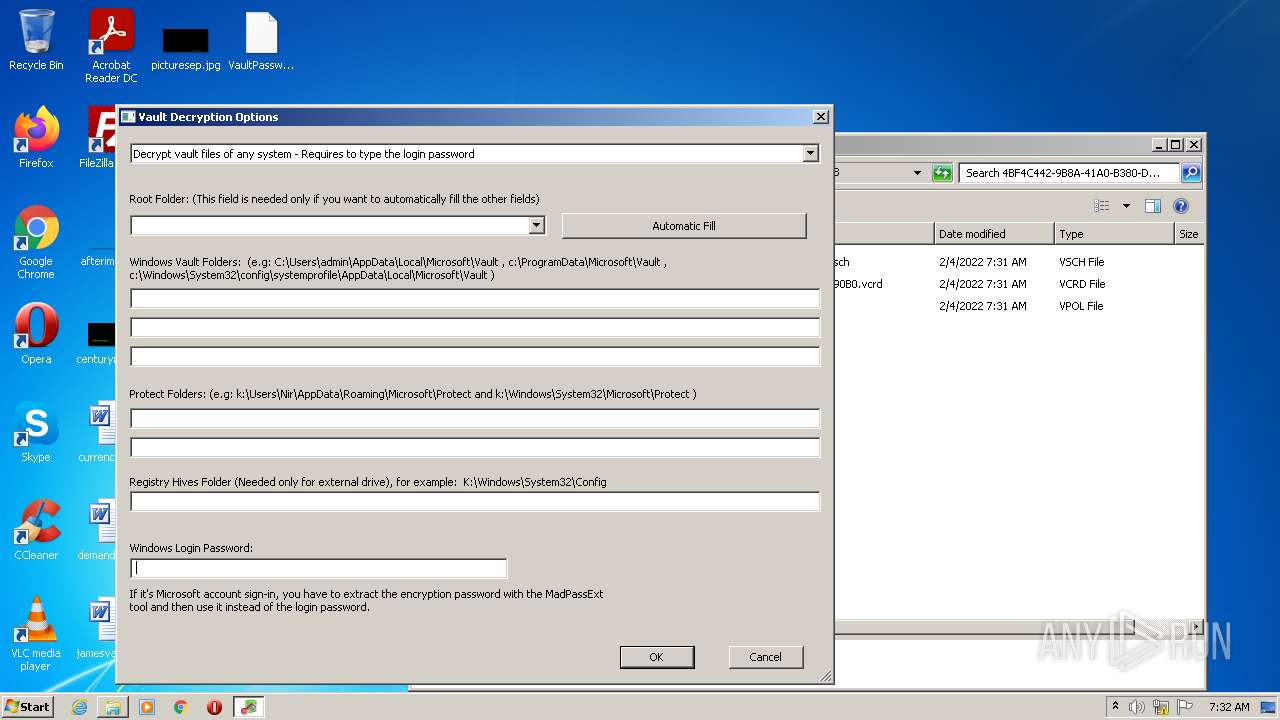
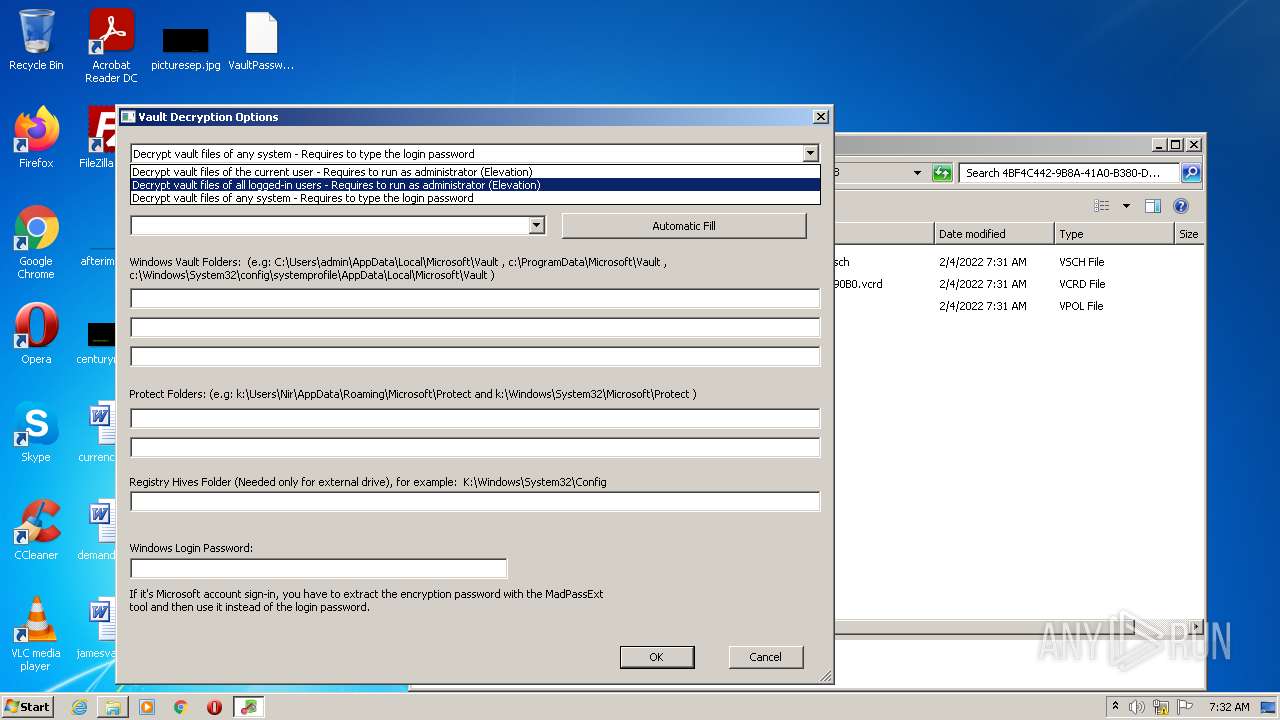
| 1212 | "C:\Users\admin\Desktop\VaultPasswordView.exe" /StartDecrypt | C:\Users\admin\Desktop\VaultPasswordView.exe | VaultPasswordView.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\Desktop\VaultPasswordView.exe" | C:\Users\admin\Desktop\VaultPasswordView.exe | — | Explorer.EXE | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
| 2912 | "C:\Users\admin\Desktop\VaultPasswordView.exe" | C:\Users\admin\Desktop\VaultPasswordView.exe | — | Explorer.EXE | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
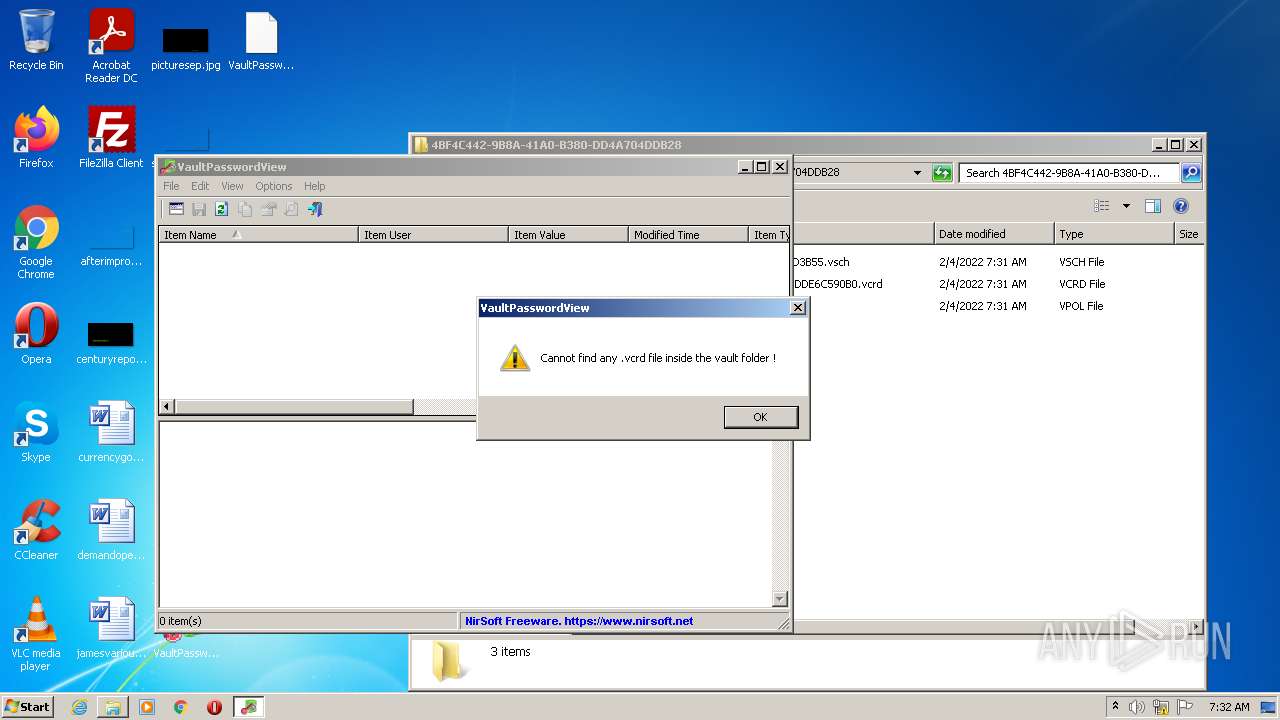
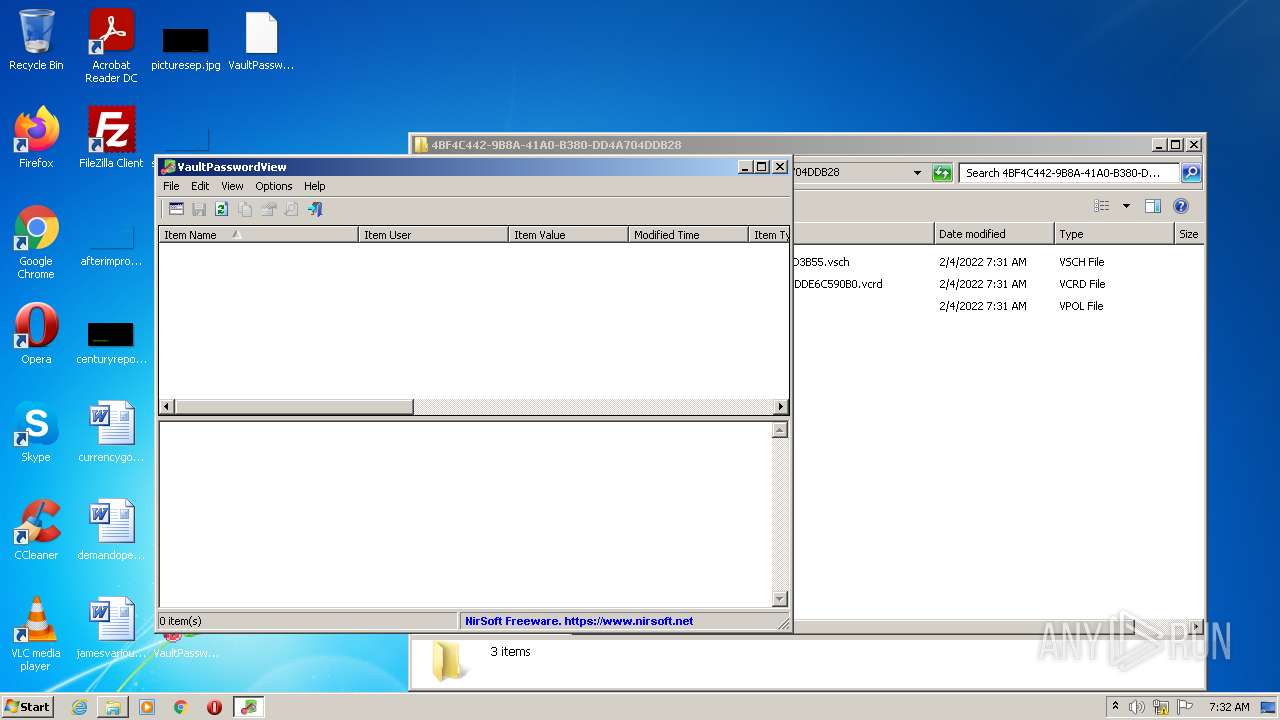
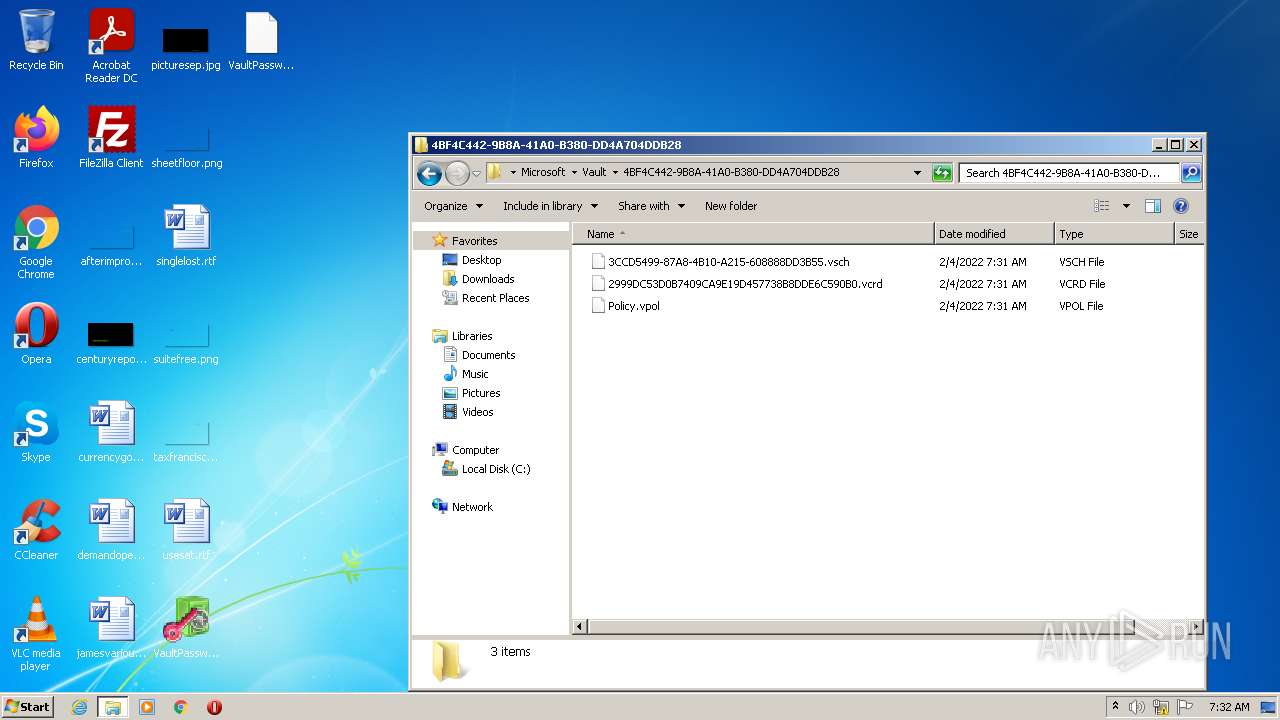
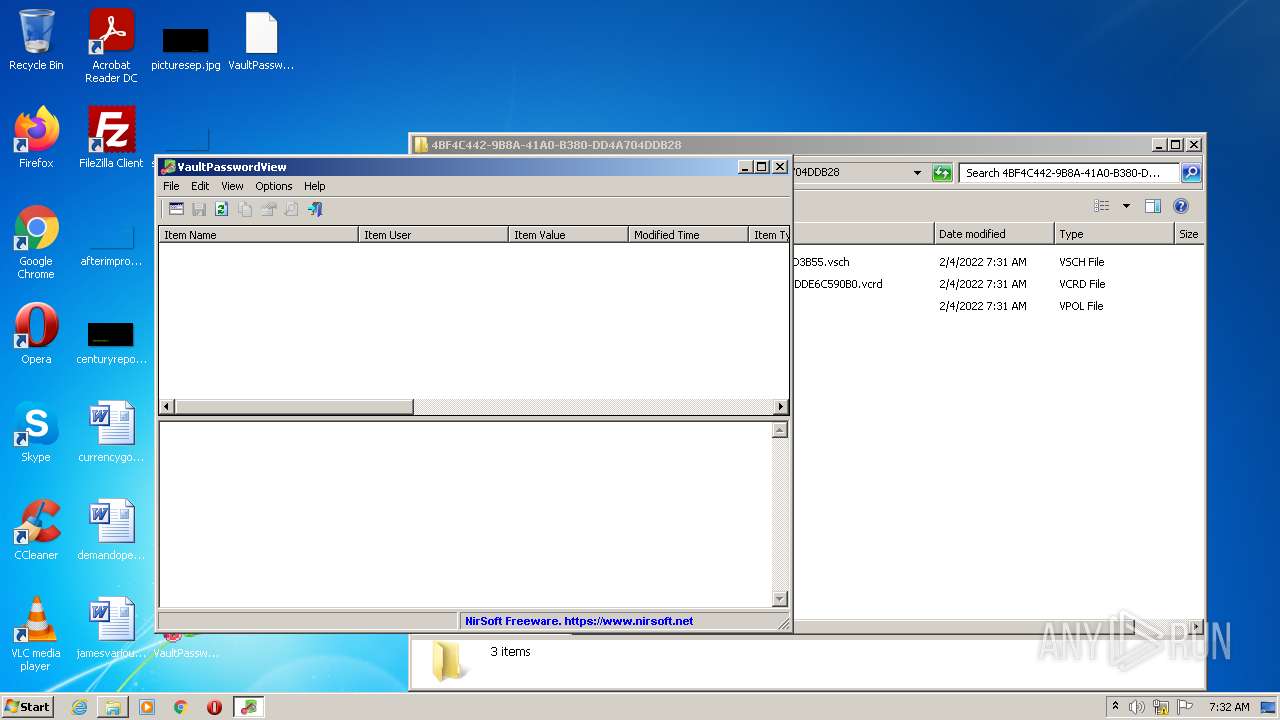
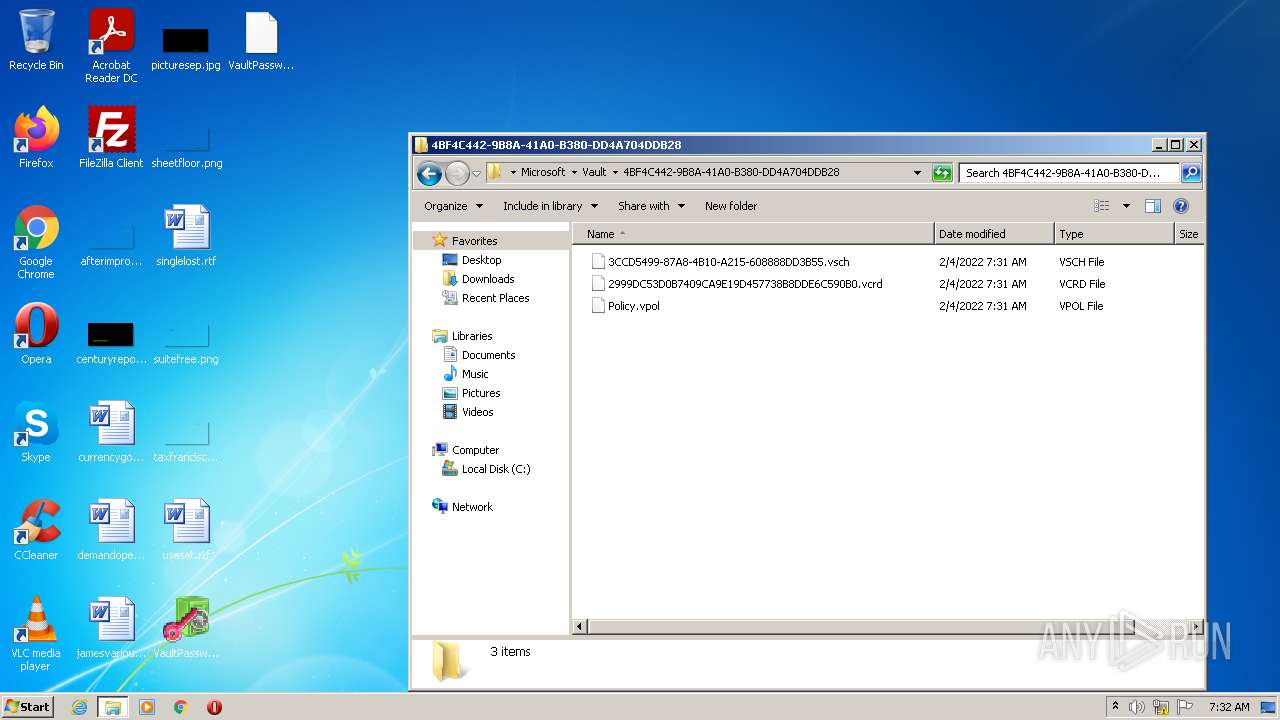
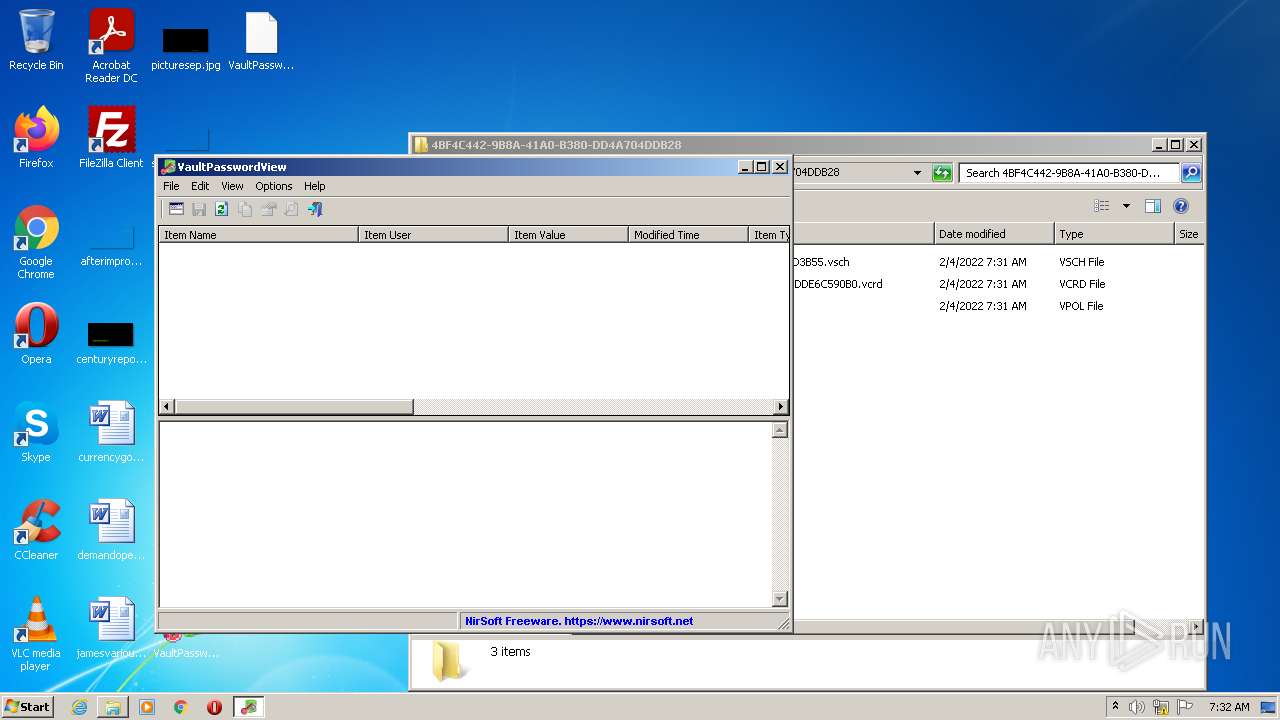
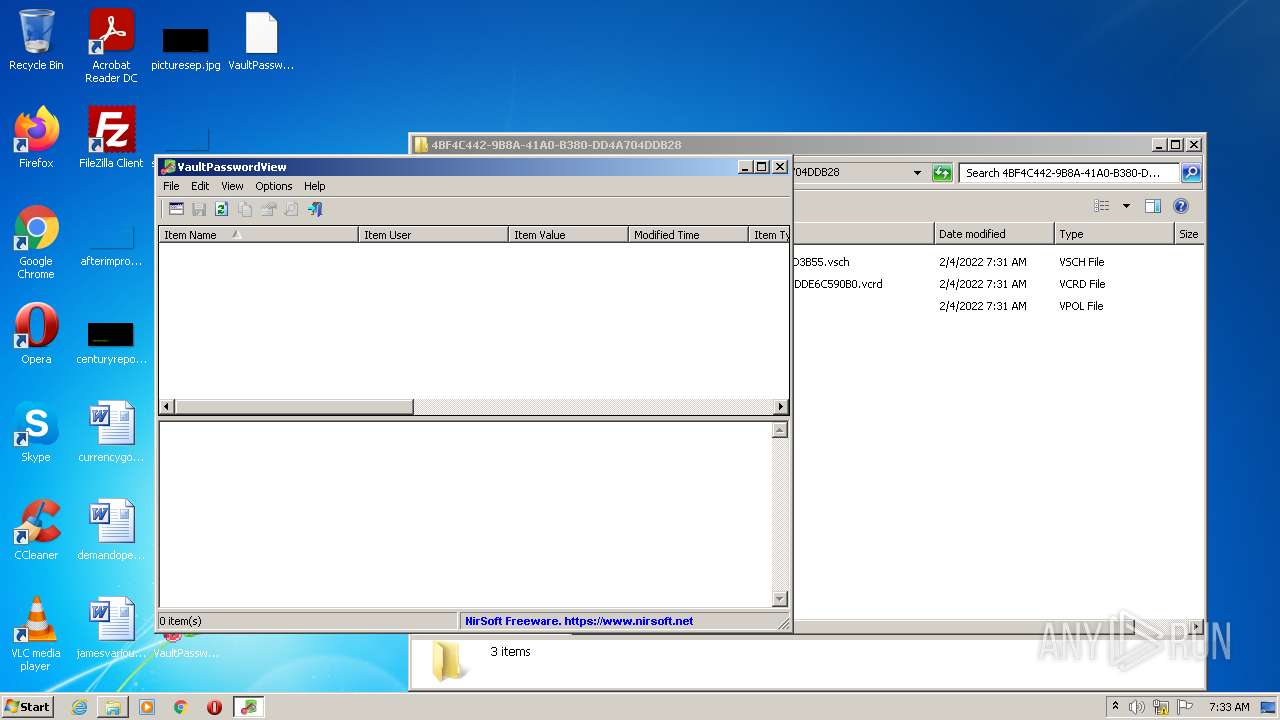
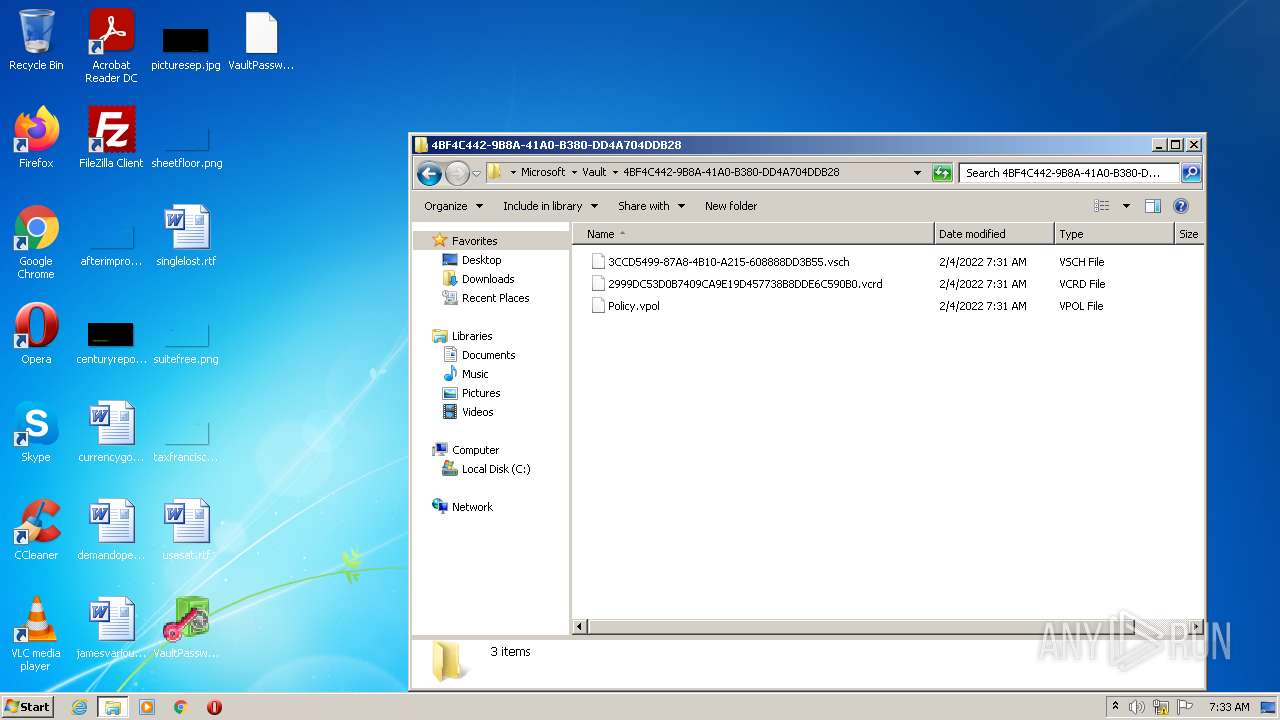
| 3452 | "C:\Windows\System32\VaultCmd.exe" /addcreds:{4BF4C442-9B8A-41A0-B380-DD4A704DDB28} /credtype:{3CCD5499-87A8-4B10-A215-608888DD3B55} /identity:TestCred /authenticator:Test /resource:Server /savedBy:Test | C:\Windows\System32\VaultCmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Vault cmdline Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3644 | "C:\Users\admin\Desktop\VaultPasswordView.exe" /StartDecrypt | C:\Users\admin\Desktop\VaultPasswordView.exe | VaultPasswordView.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\Desktop\VaultPasswordView.exe" | C:\Users\admin\Desktop\VaultPasswordView.exe | Explorer.EXE | ||||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
| 4016 | "C:\Users\admin\Desktop\VaultPasswordView.exe" | C:\Users\admin\Desktop\VaultPasswordView.exe | Explorer.EXE | ||||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: VaultPasswordView Exit code: 0 Version: 1.11 Modules
| |||||||||||||||
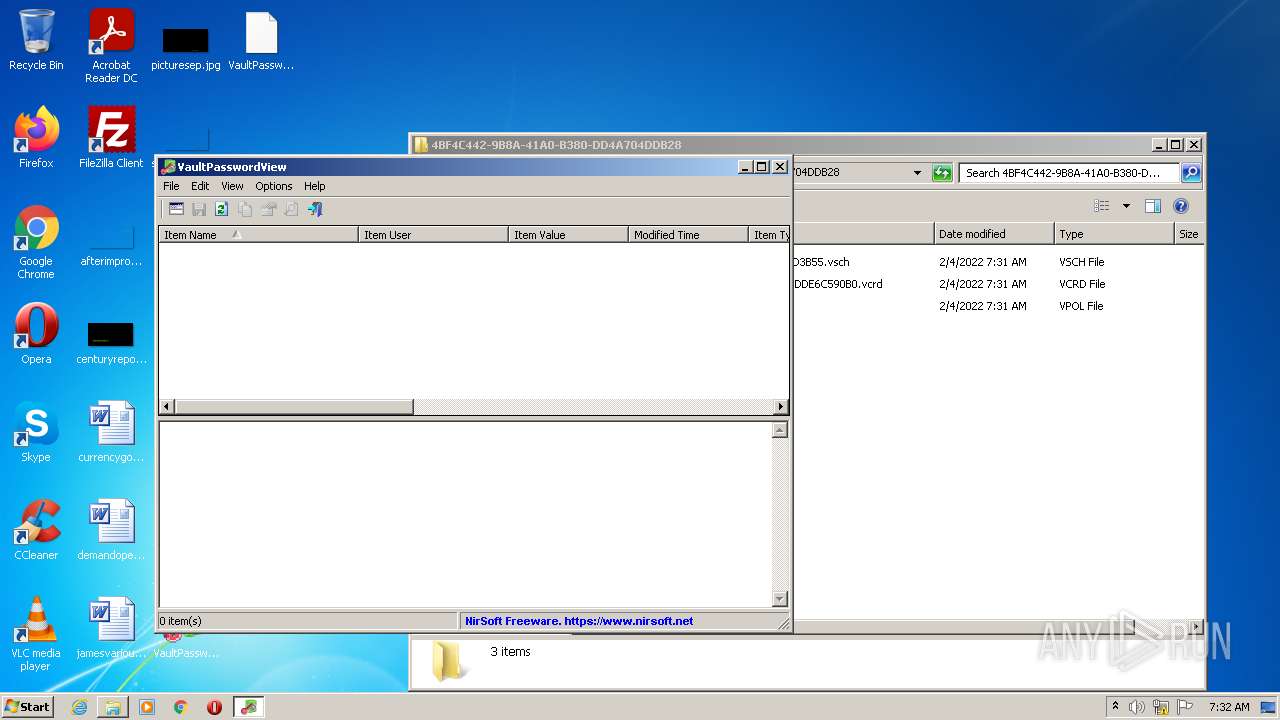
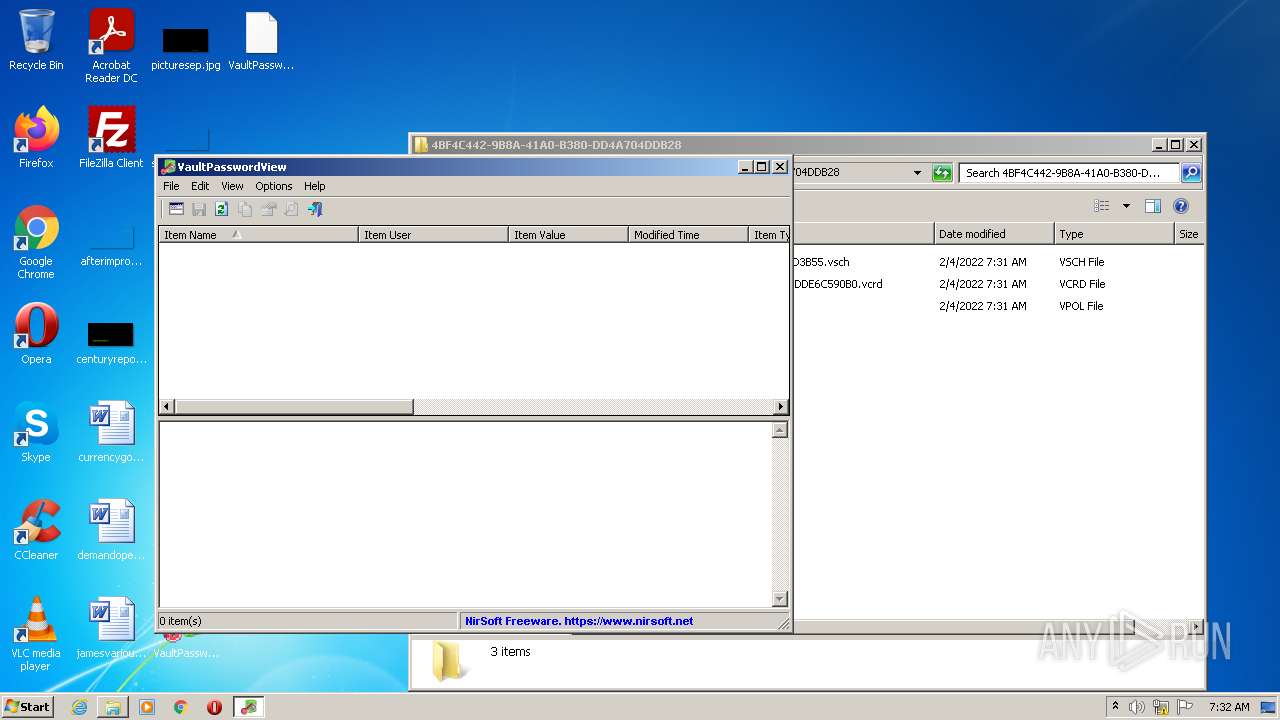
Total events
616
Read events
600
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2912) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2912) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2912) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2912) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1972) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1972) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1972) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1972) VaultPasswordView.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
1
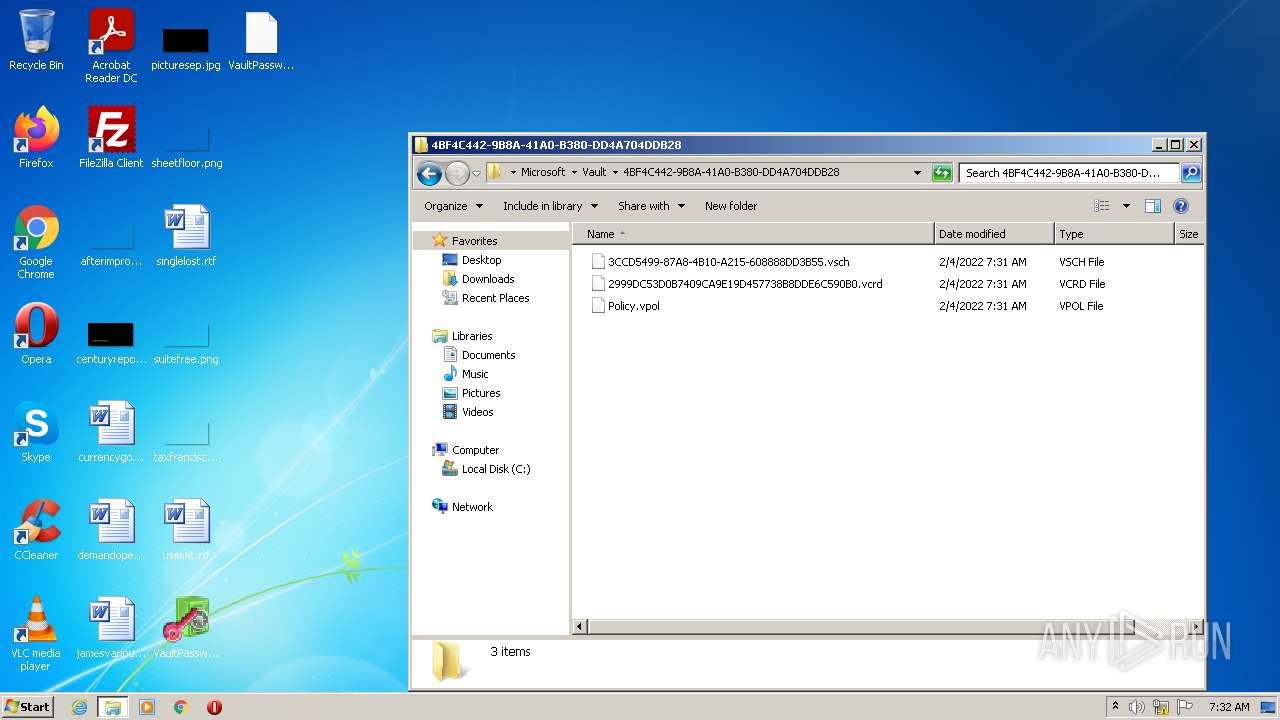
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
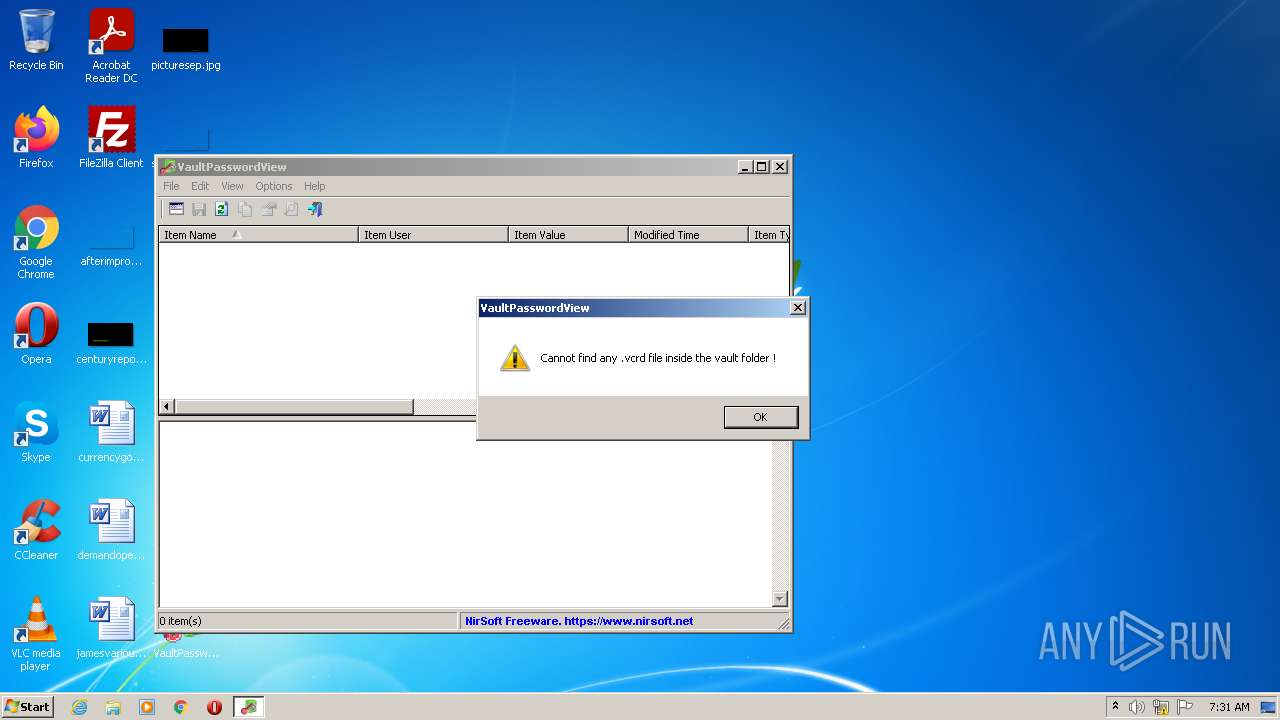
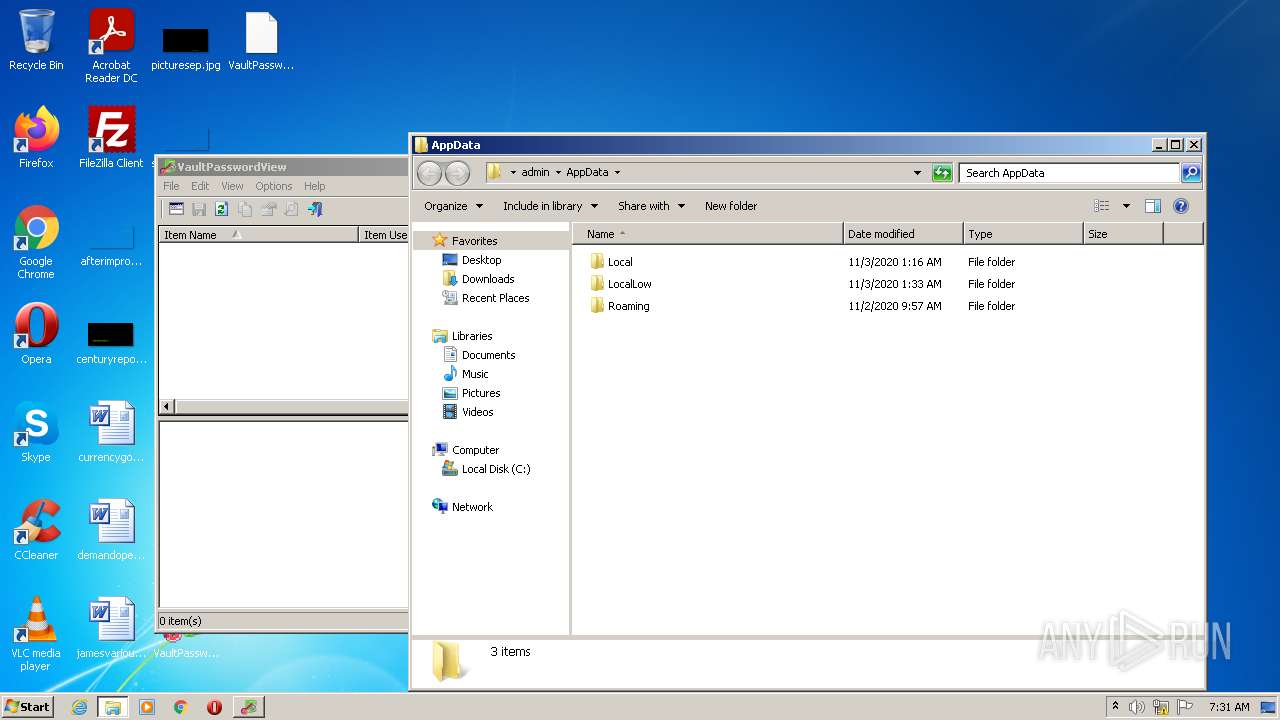
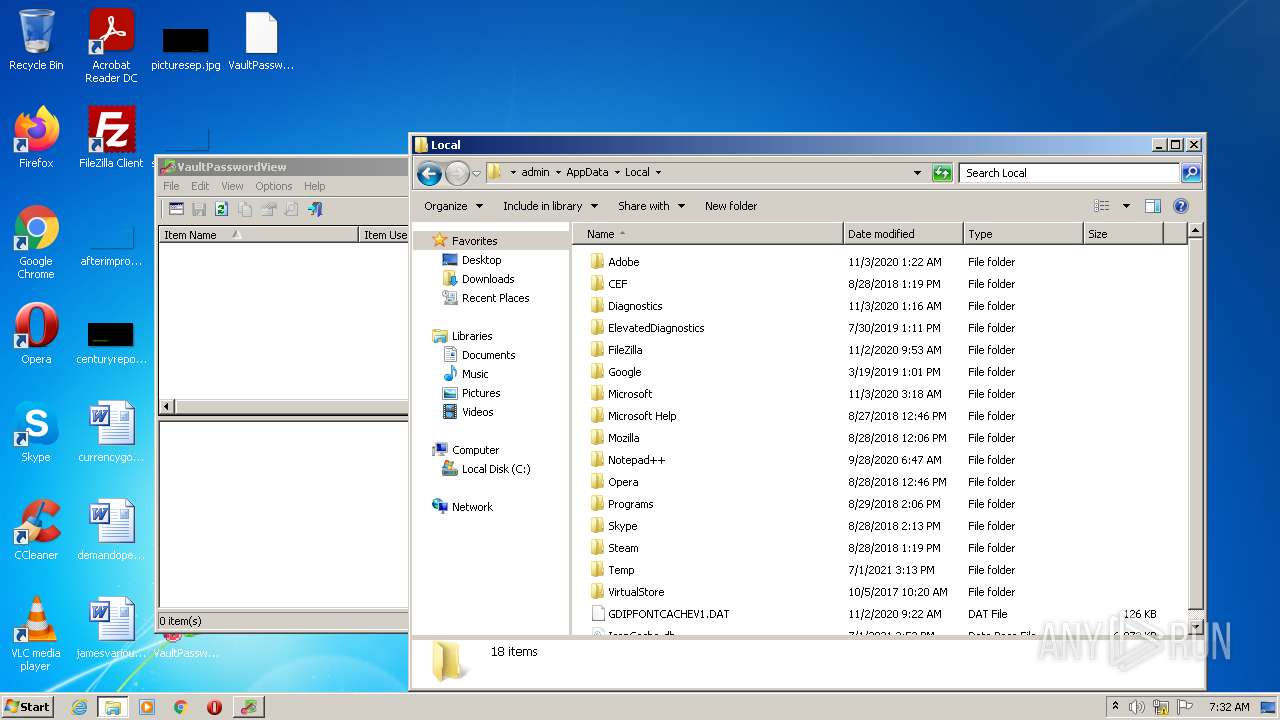
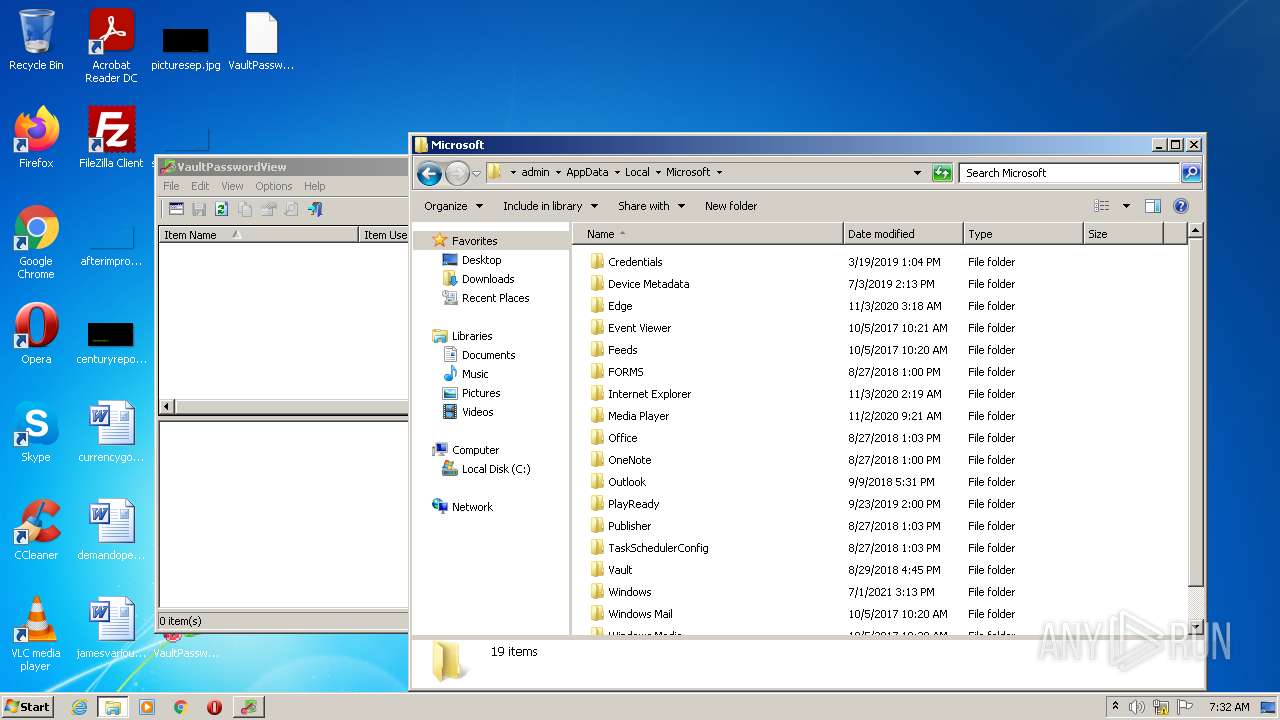
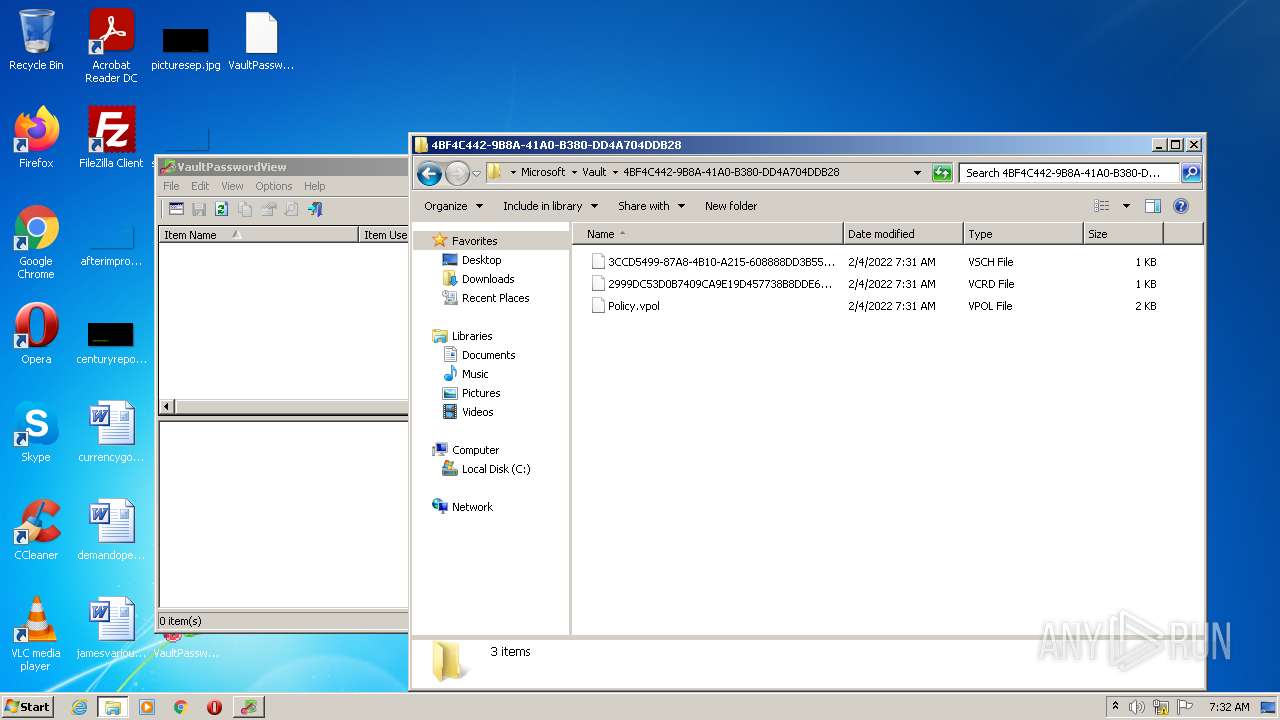
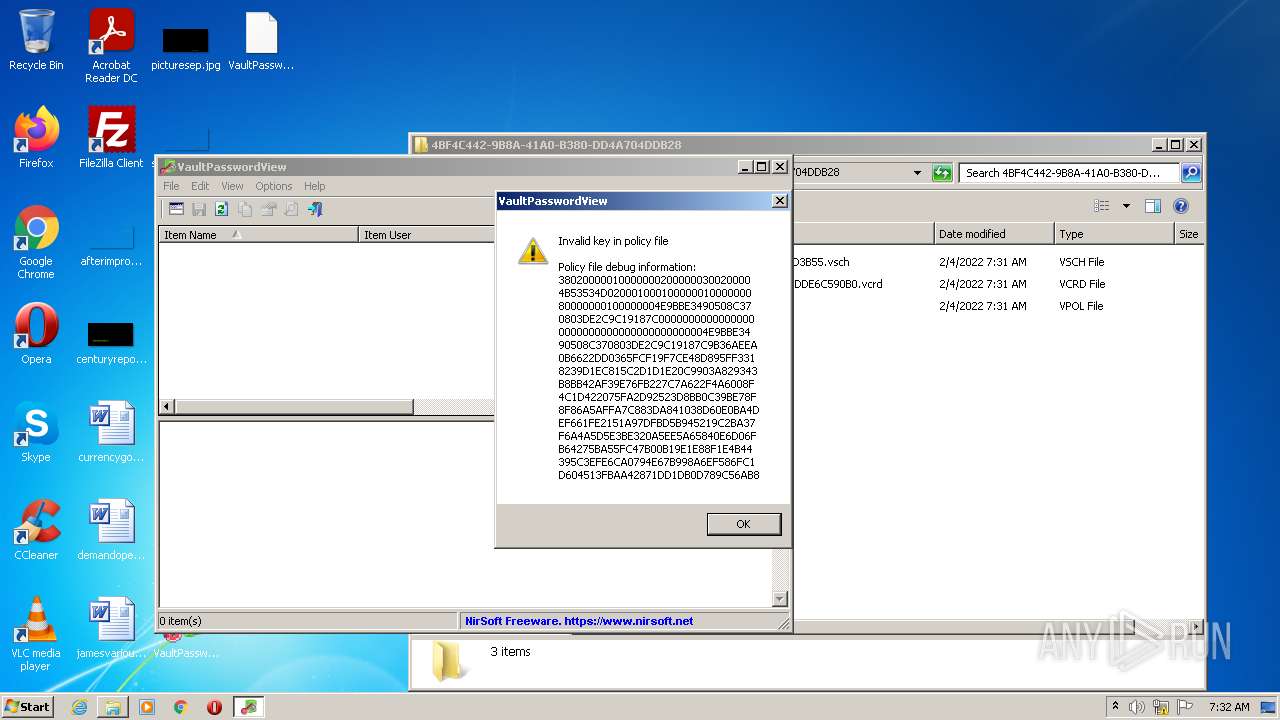
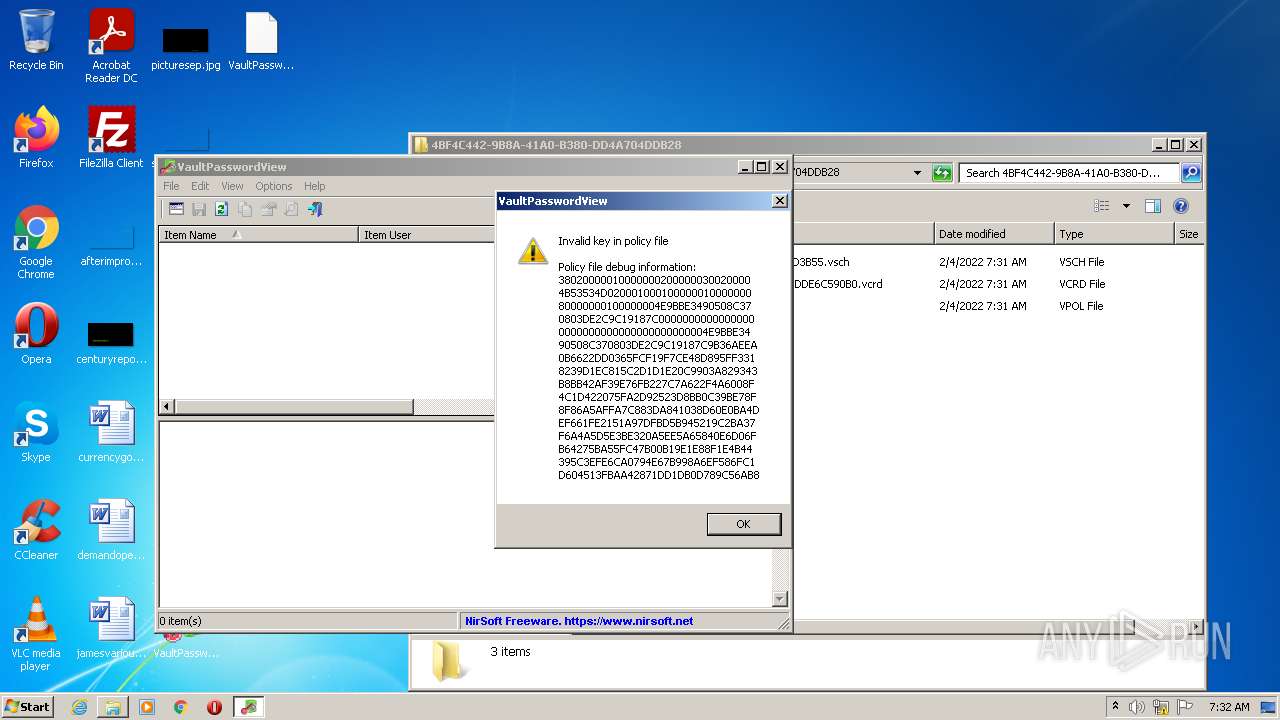
| 992 | lsass.exe | C:\ProgramData\Microsoft\Vault\AC658CB4-9126-49BD-B877-31EEDAB3F204\Policy.vpol | binary | |
MD5:5B6998A9ED99A56AFC7ADB3E62C3AF6F | SHA256:B8BFDC5E5E8D247046E74F89132595FF51FCC1CF359688C64B56FC03E1883D83 | |||
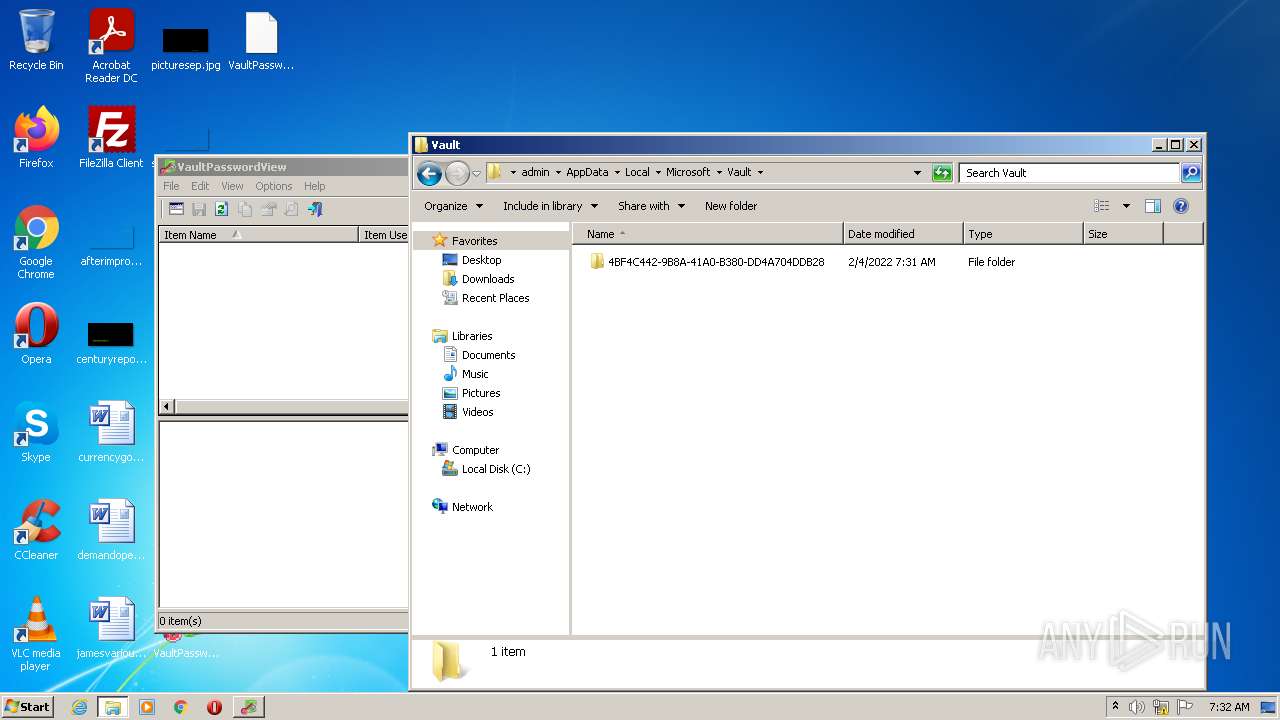
| 992 | lsass.exe | C:\Users\admin\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28\Policy.vpol | binary | |
MD5:87BDECE7133F671FA8BE42D3A7931CAE | SHA256:48538239C3C4D577431D58588E0C8A863346724DB1C232400DAF32B911A17DA6 | |||
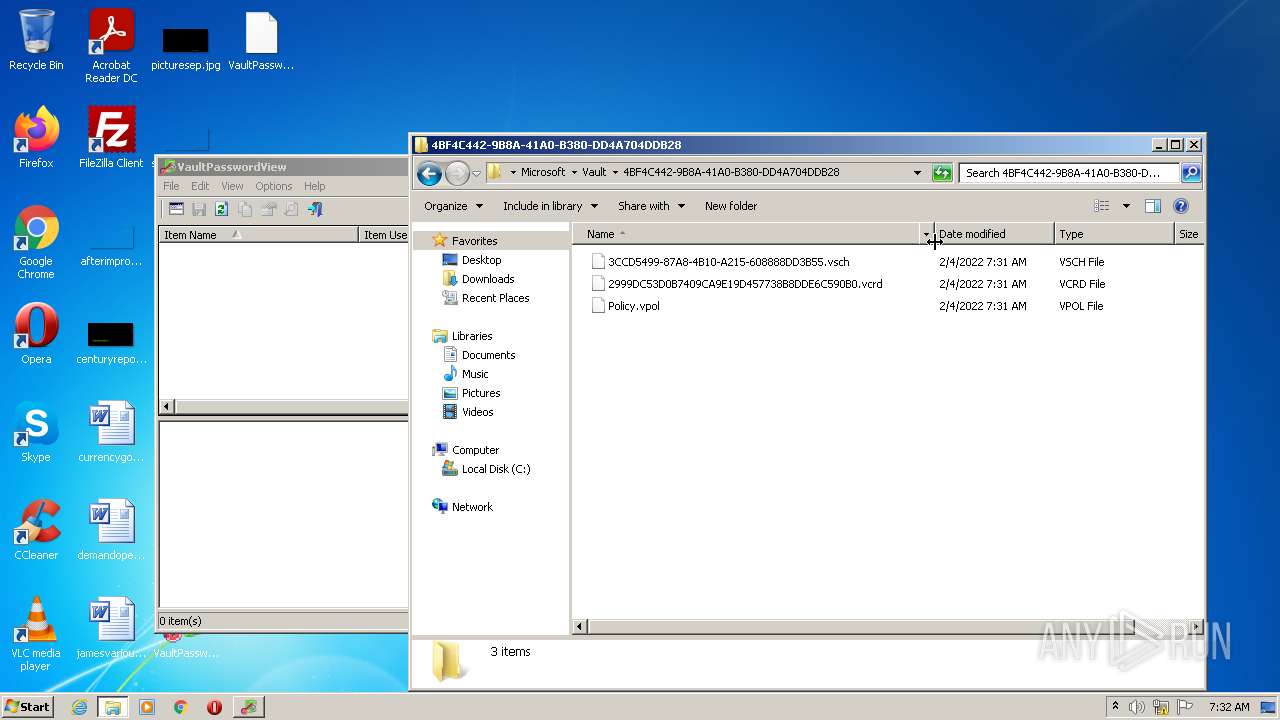
| 992 | lsass.exe | C:\Users\admin\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28\2999DC53D0B7409CA9E19D457738B8DDE6C590B0.vcrd | gpg | |
MD5:— | SHA256:— | |||
| 1148 | VaultPasswordView.exe | C:\Users\admin\Desktop\VaultPasswordView.cfg | text | |
MD5:54C65429619CC5CACFB5326E95EEBFF3 | SHA256:C206DD5D26917414D2E6087E958BDFB61F4AA1B8154BEB92F35D5C3A7737D996 | |||
| 992 | lsass.exe | C:\Users\admin\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28\3CCD5499-87A8-4B10-A215-608888DD3B55.vsch | binary | |
MD5:F66EE121A2EA92F67CEE224EADE2BA63 | SHA256:002BB5A917B093A16CD3EC97DC3ABA782A4676D20B1887281E5D0EAFA93BDD76 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report