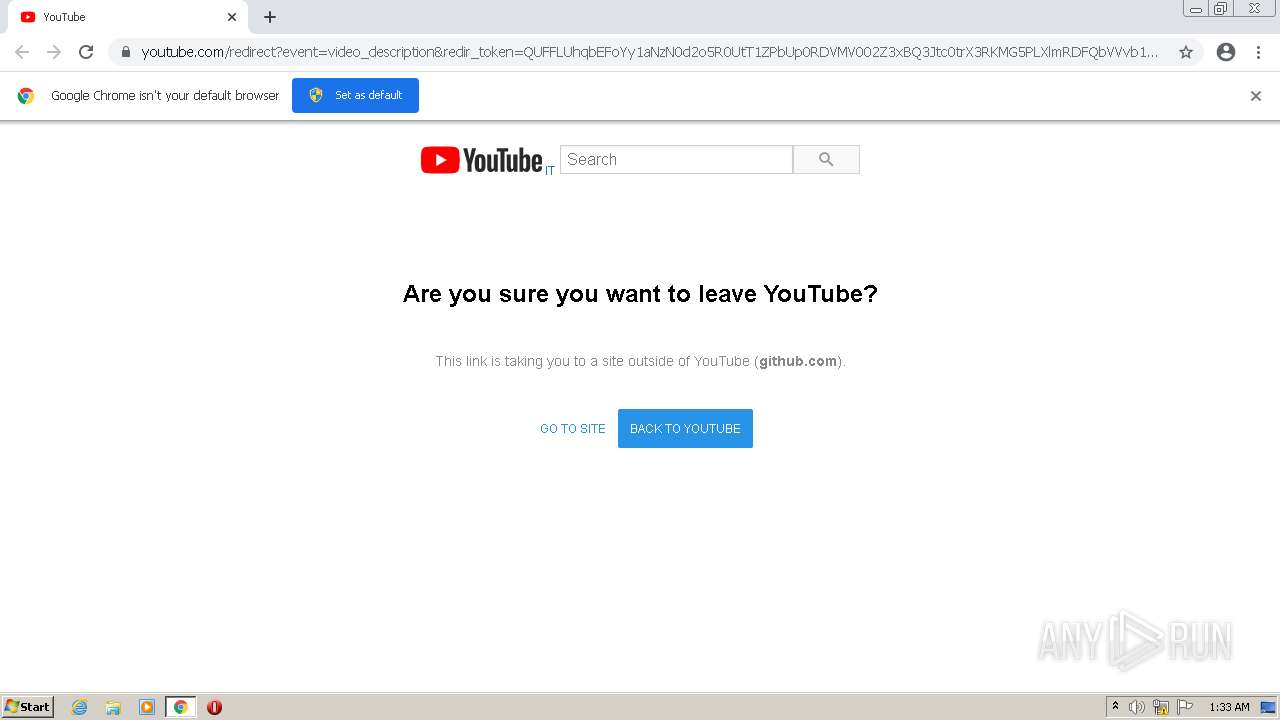
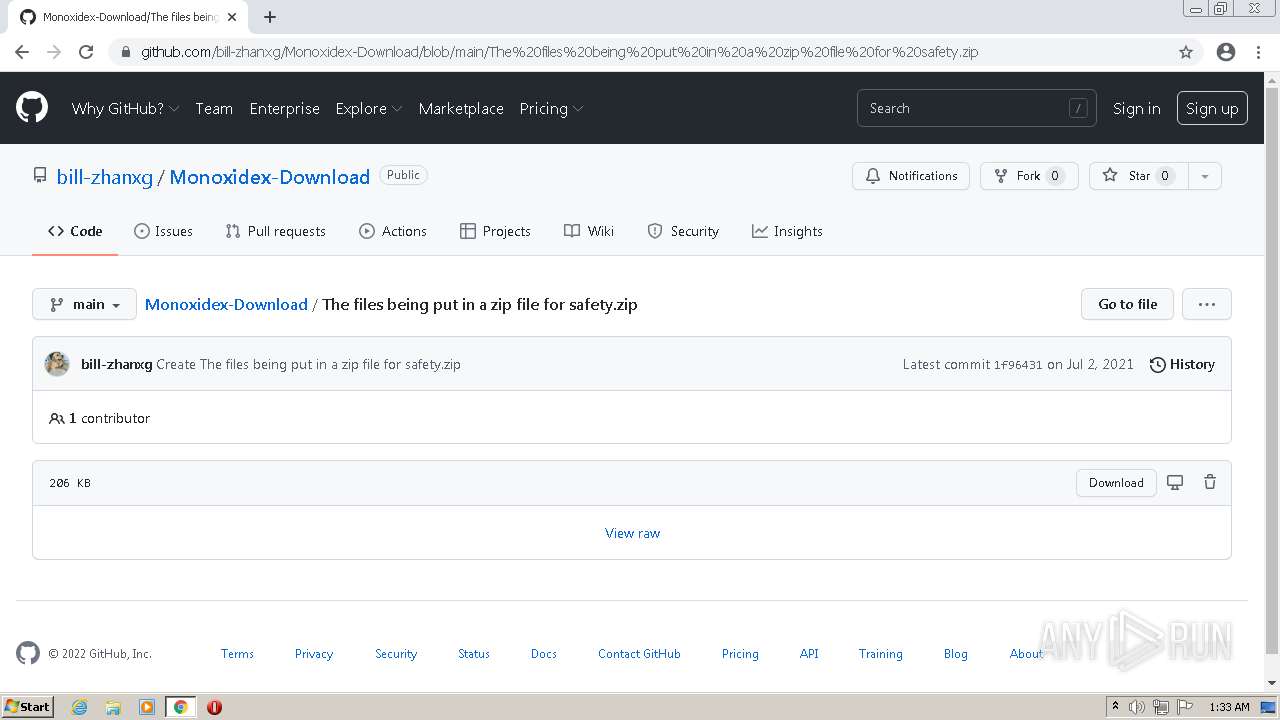
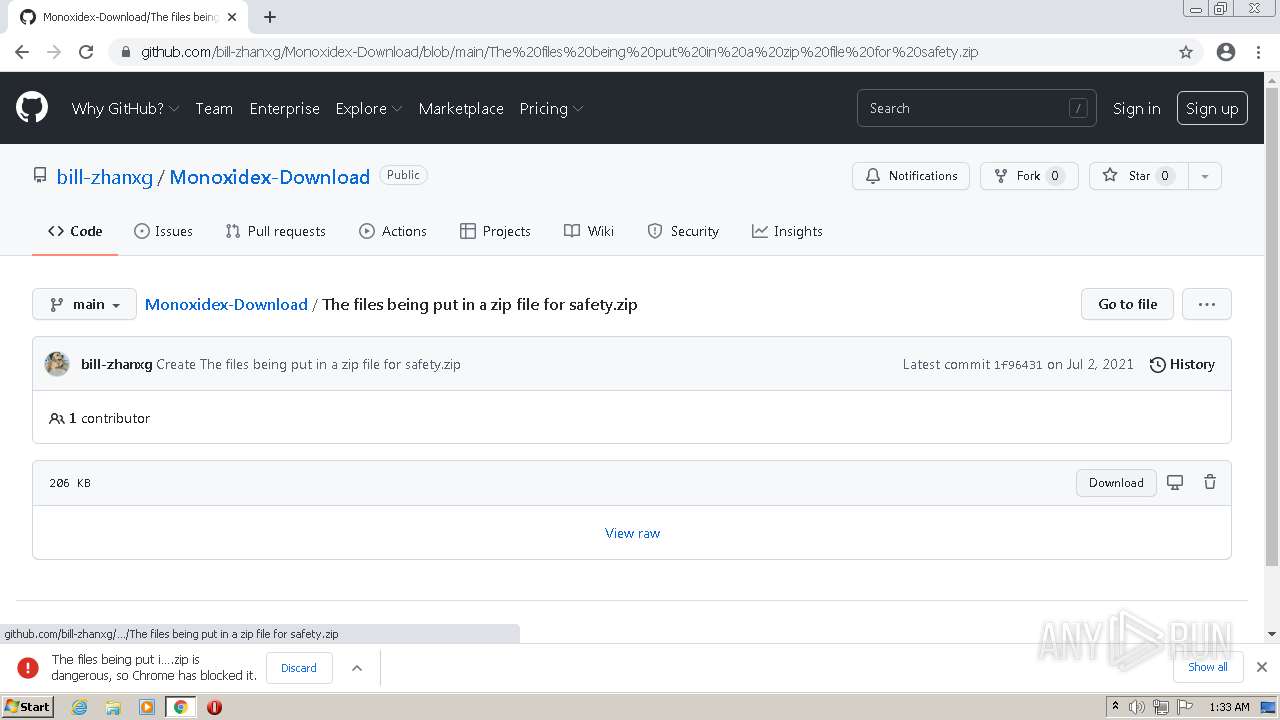
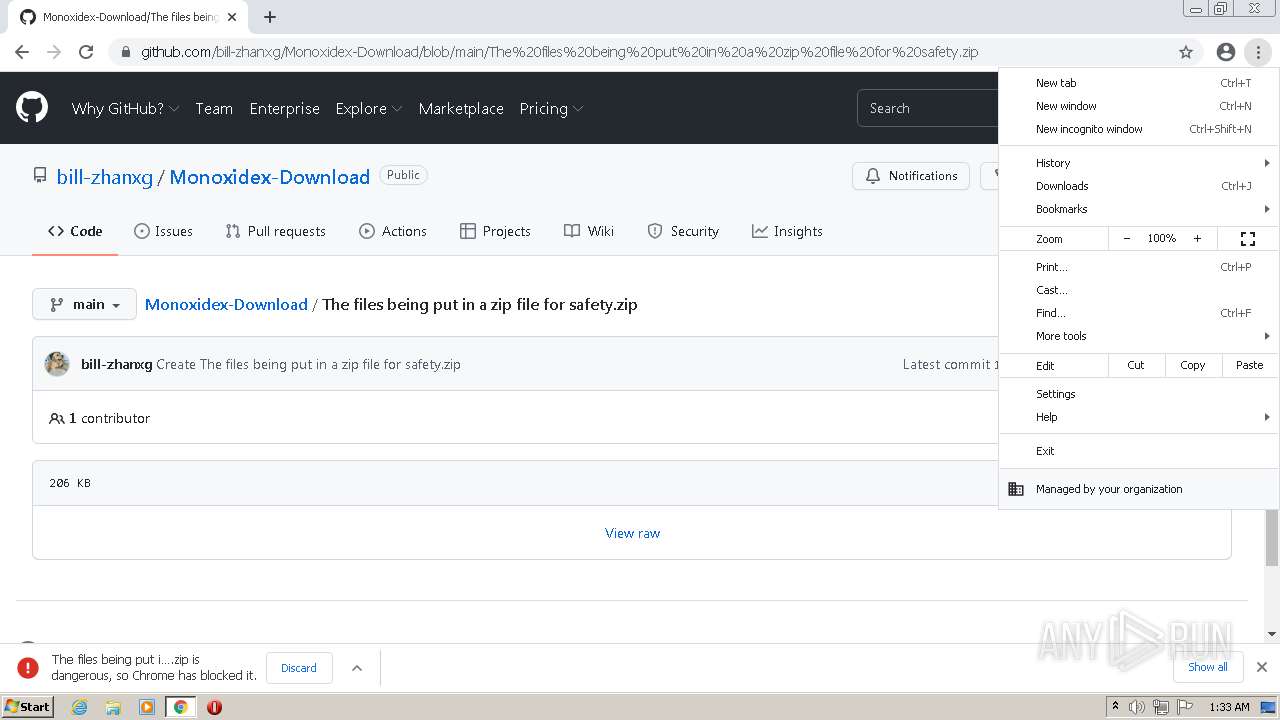
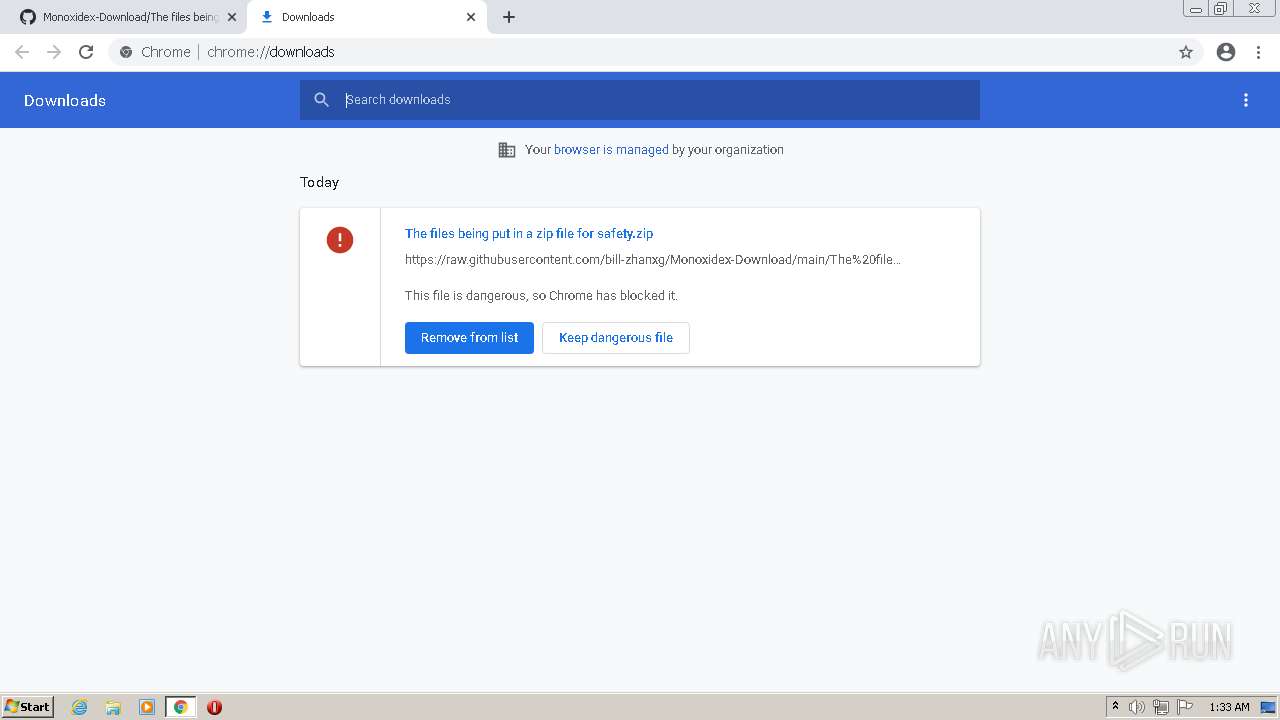
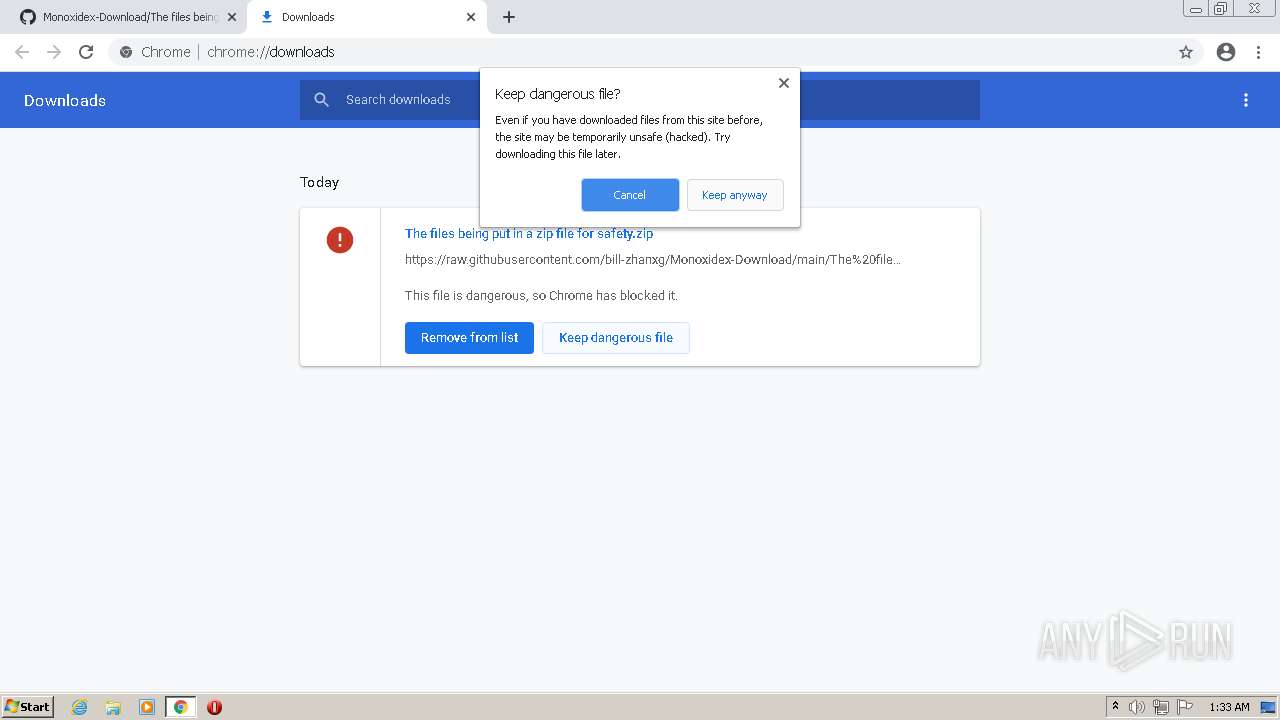
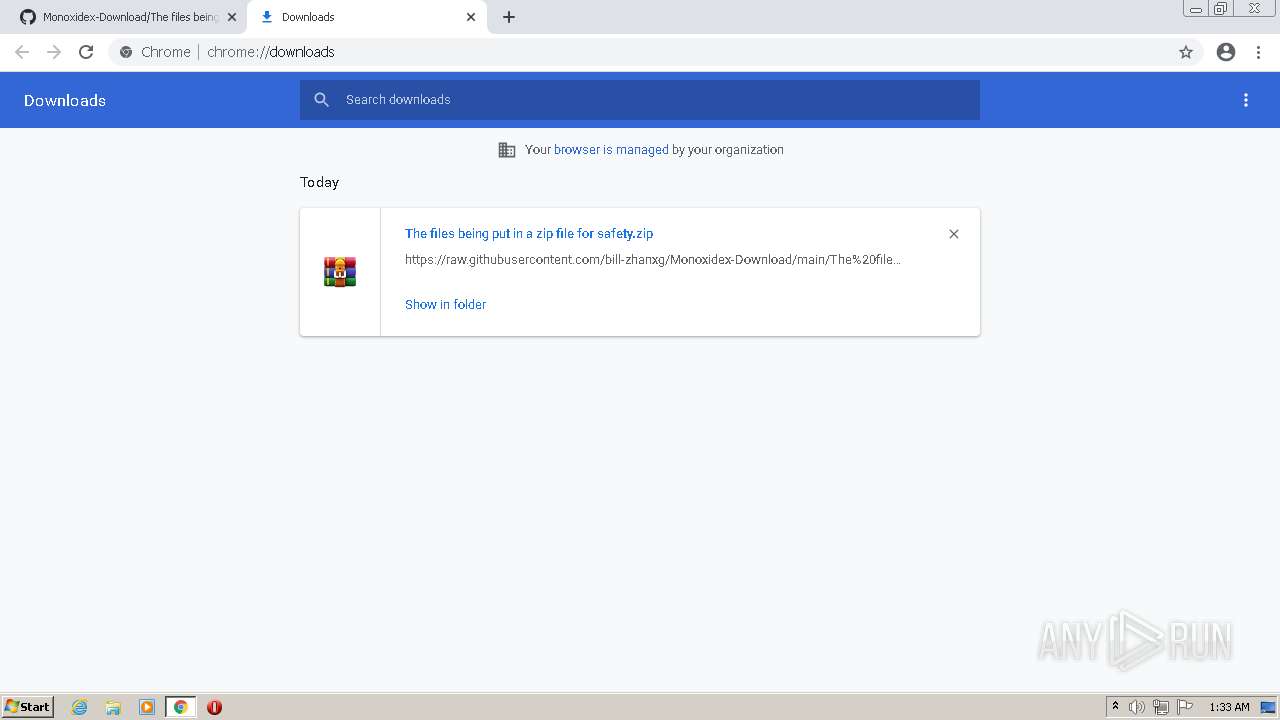
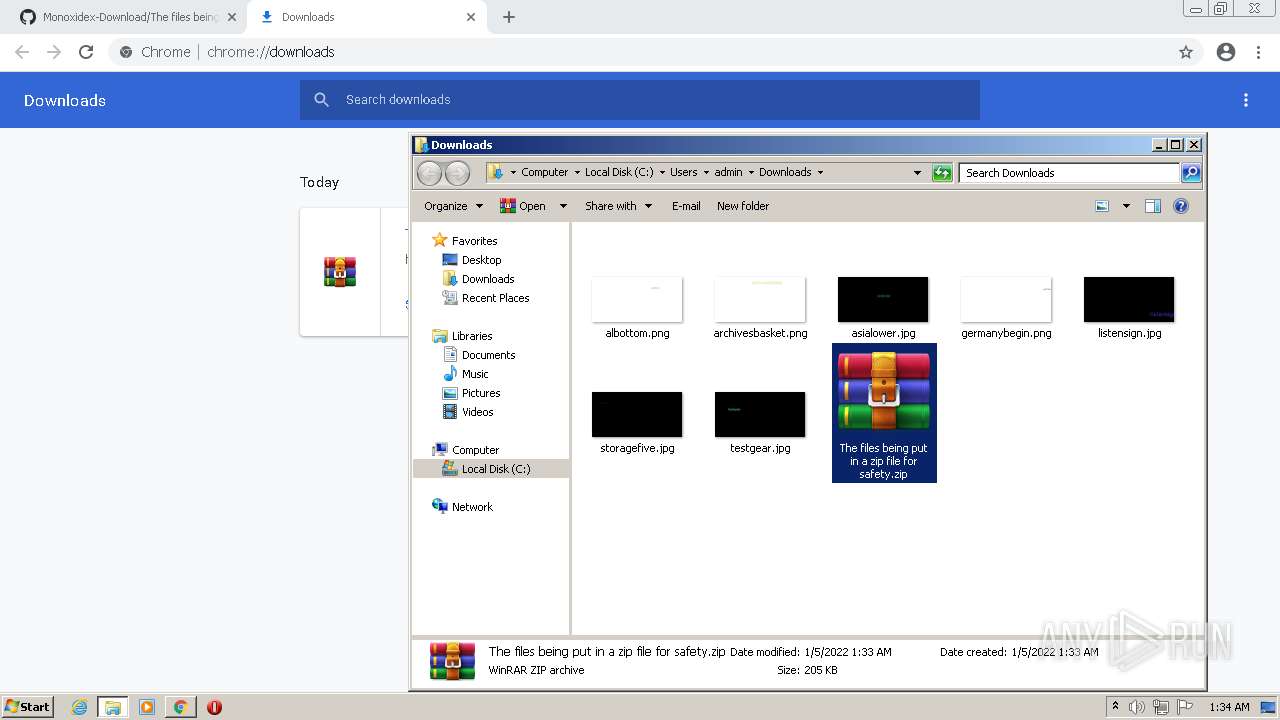
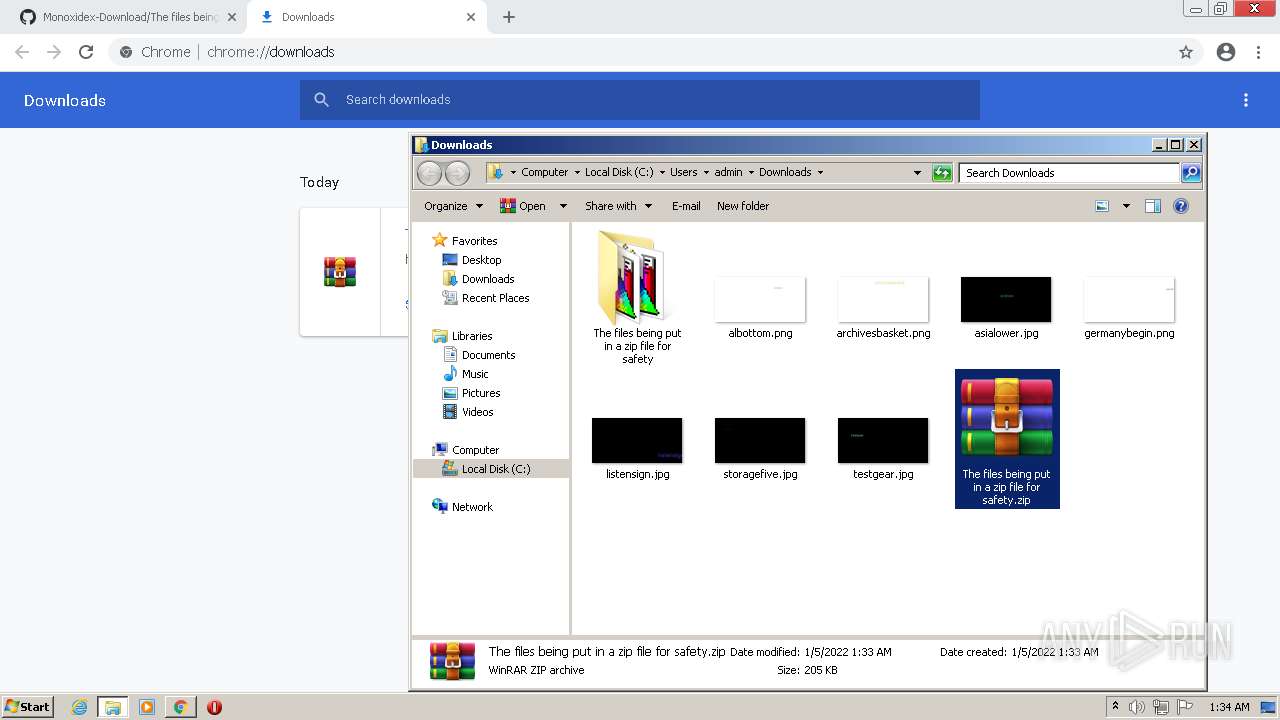
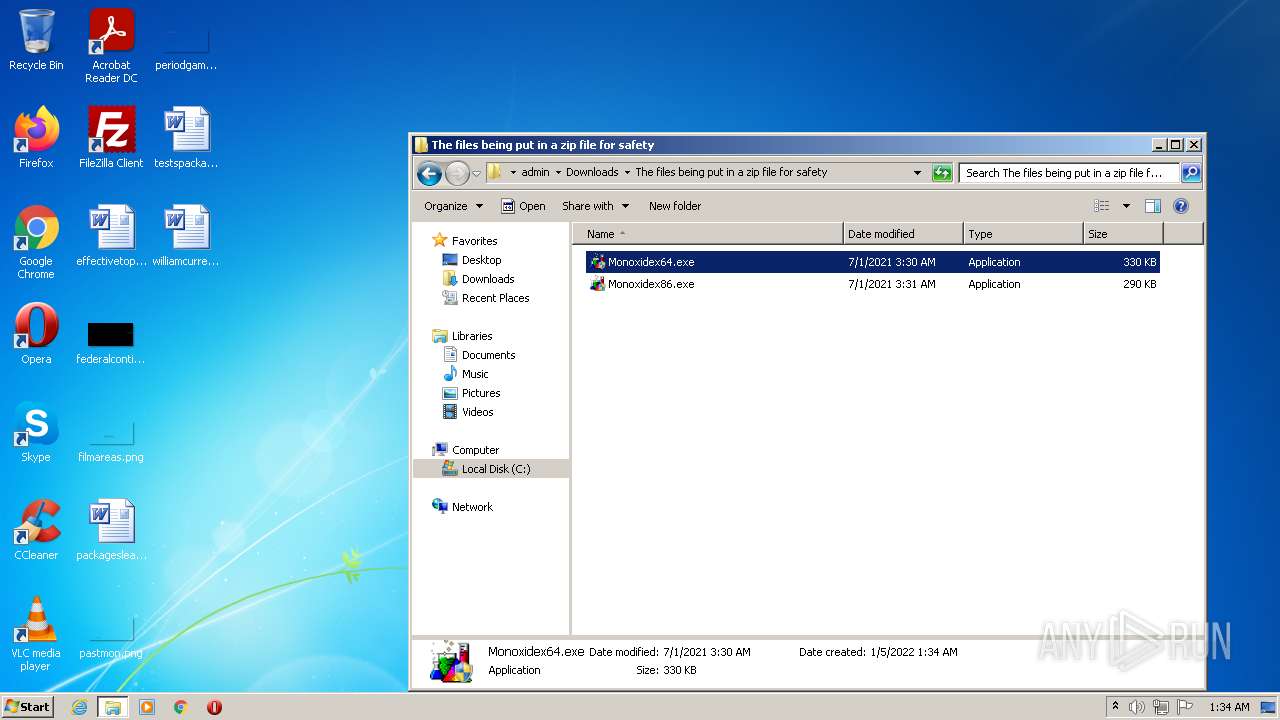
| URL: | https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbEFoYy1aNzN0d2o5R0UtT1ZPbUp0RDVMV002Z3xBQ3Jtc0trX3RKMG5PLXlmRDFQbVVvb1hWRHZ1cWdlWVp2TmpzMVJIVHlJUnhCcnFvUDVObUVPS1N2WXF2VDhYZGNVZm5PWk1Pa1c4em14R1EyLWNOaldLVFZuM1ByUEN4Q0xGcElfVlRQSE4yVGdYQ2k0SXAzMA&q=https%3A%2F%2Fgithub.com%2Fbill-zhanxg%2FMonoxidex-Download%2Fblob%2Fmain%2FThe%2520files%2520being%2520put%2520in%2520a%2520zip%2520file%2520for%2520safety.zip |
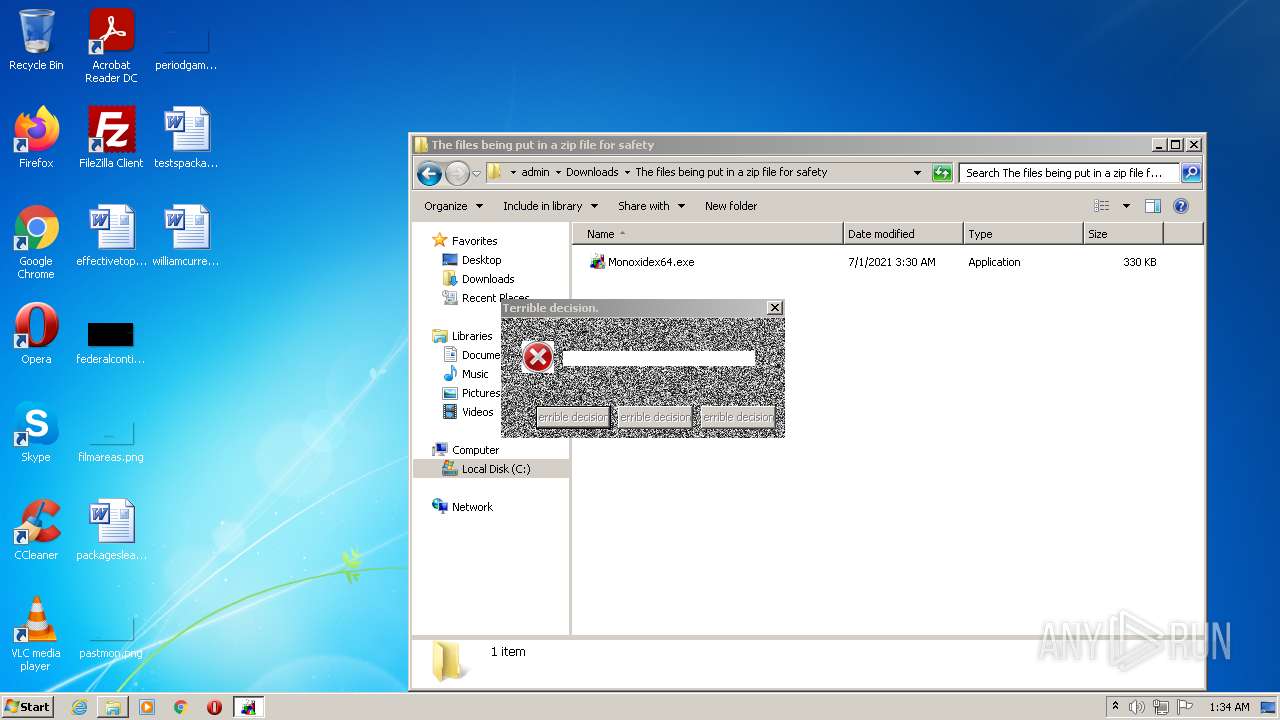
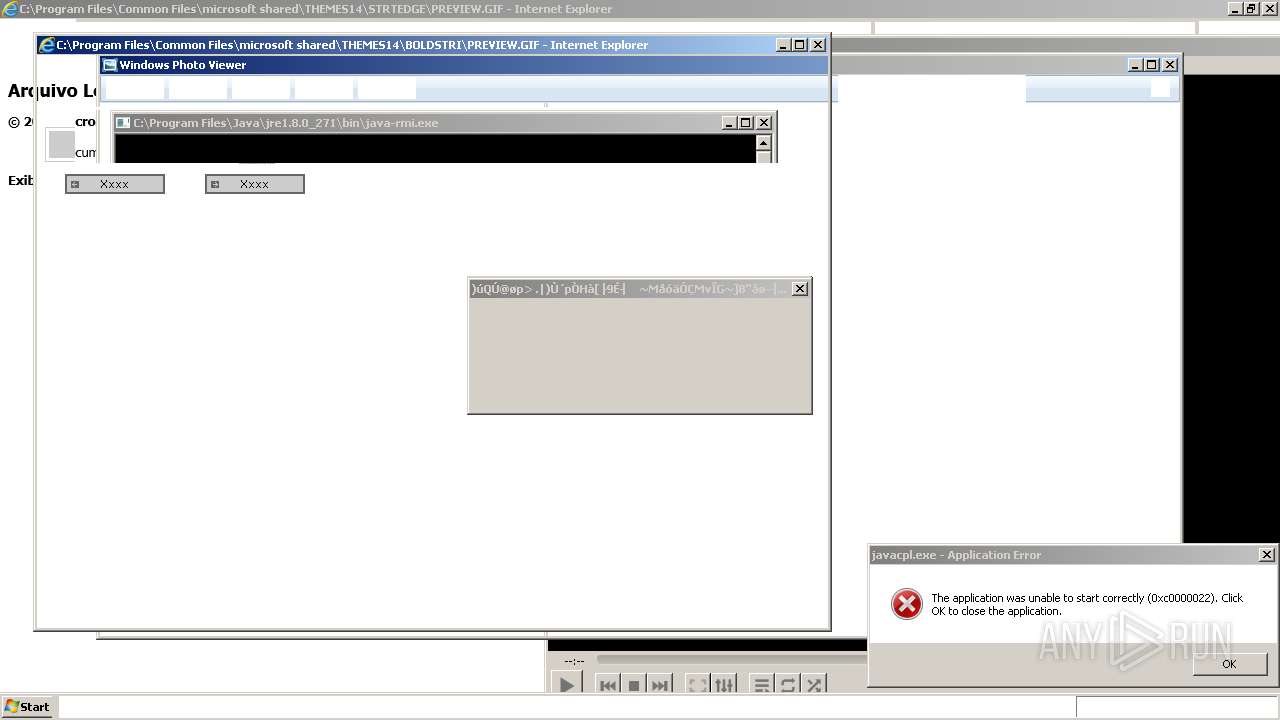
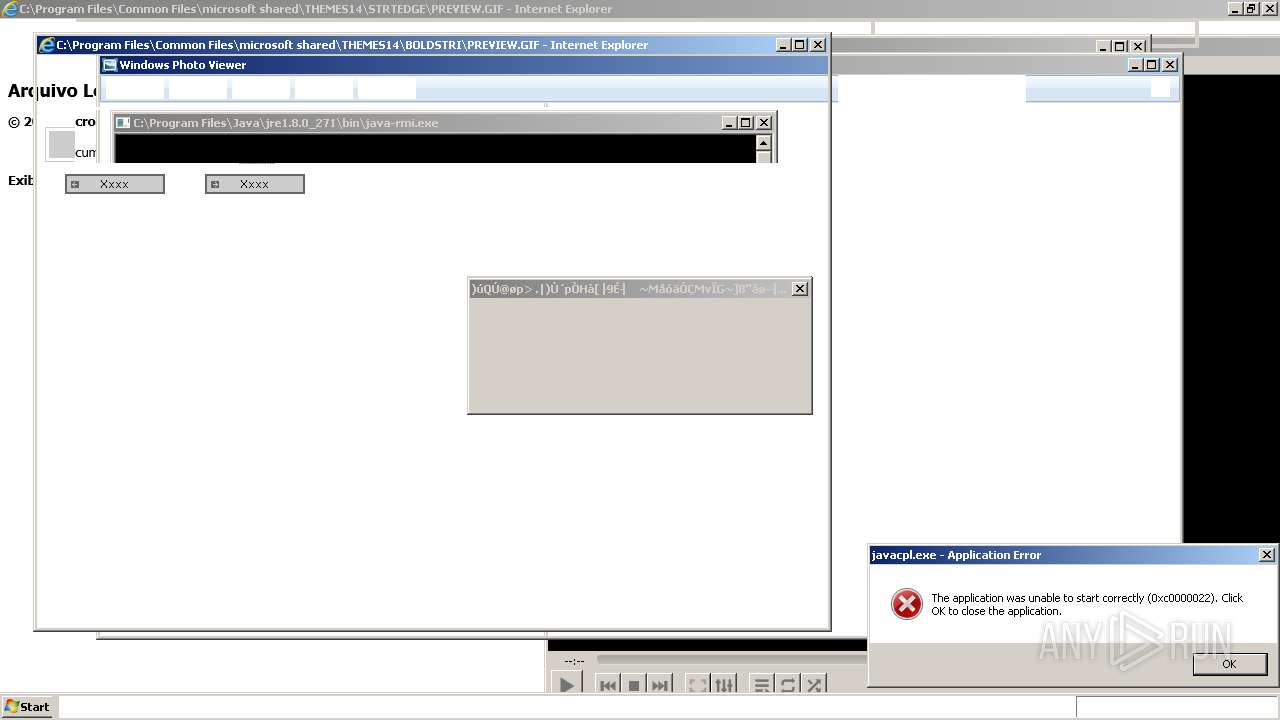
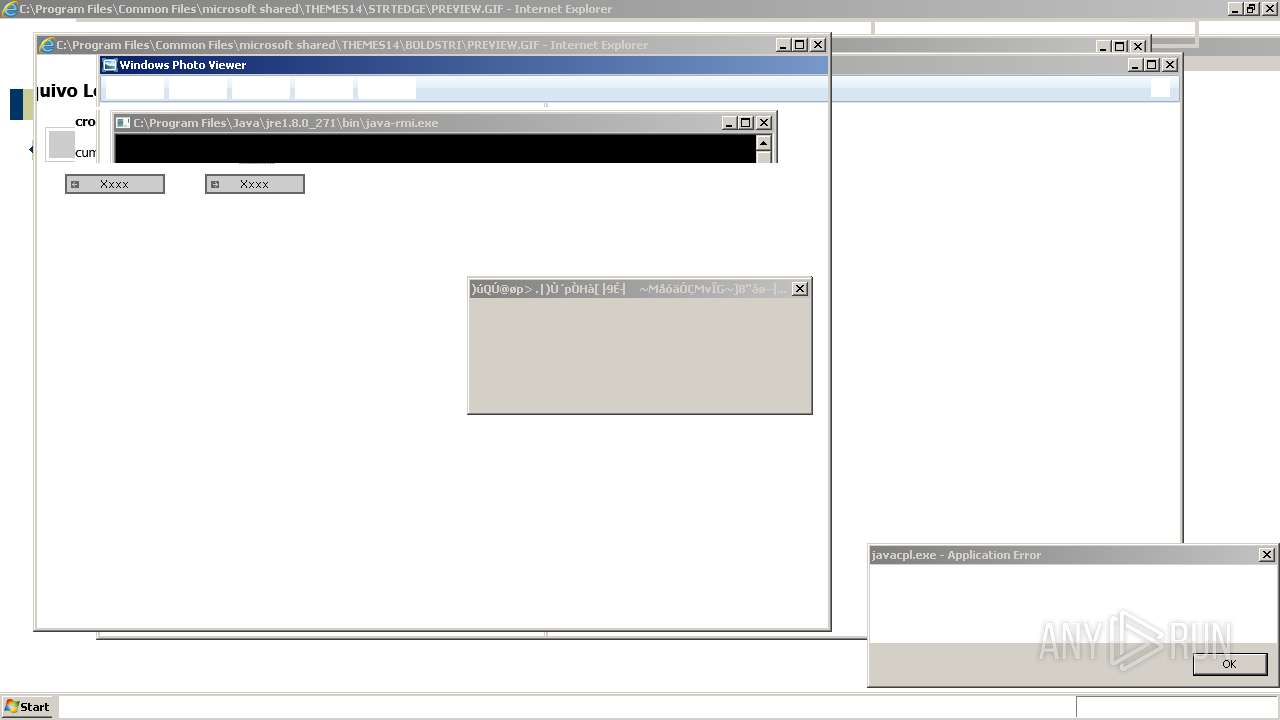
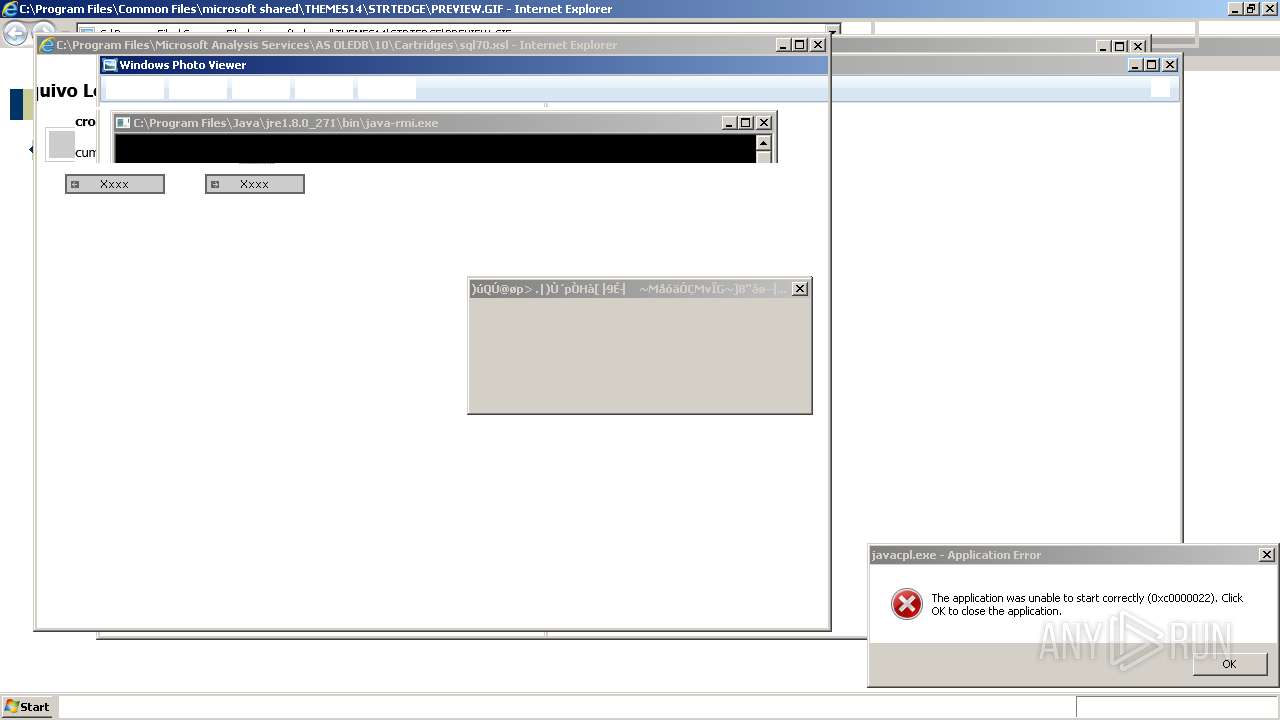
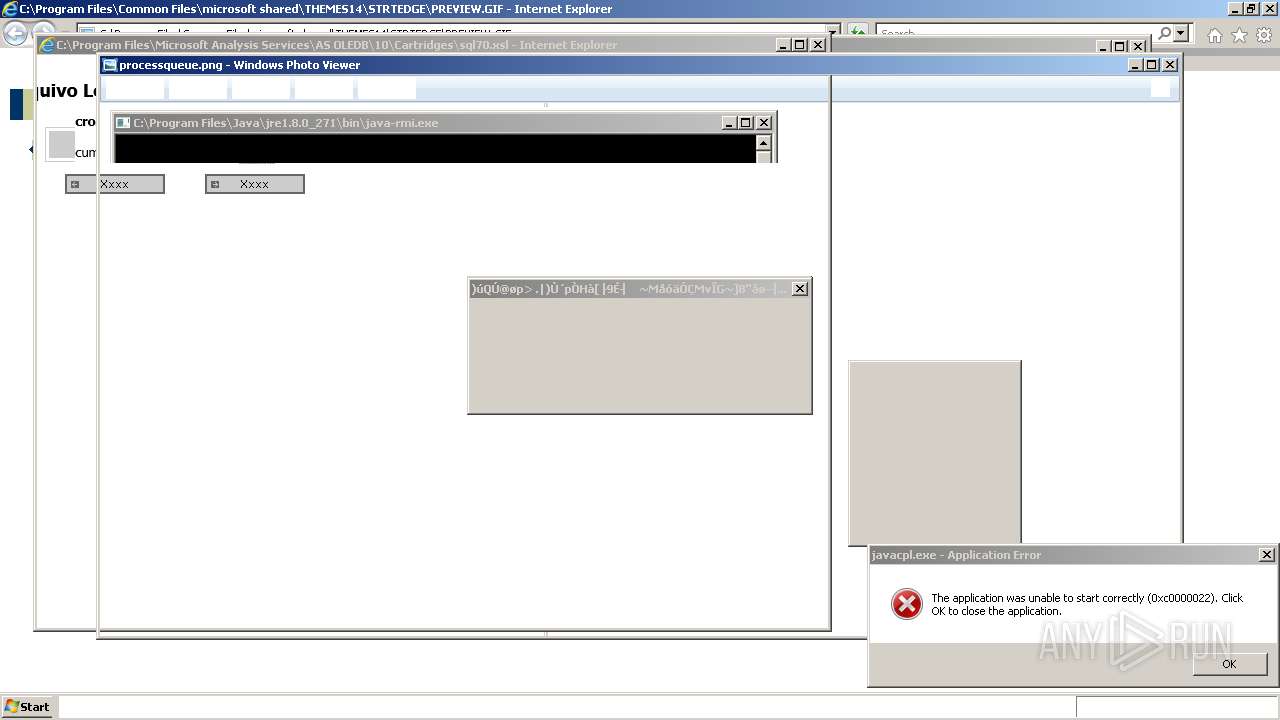
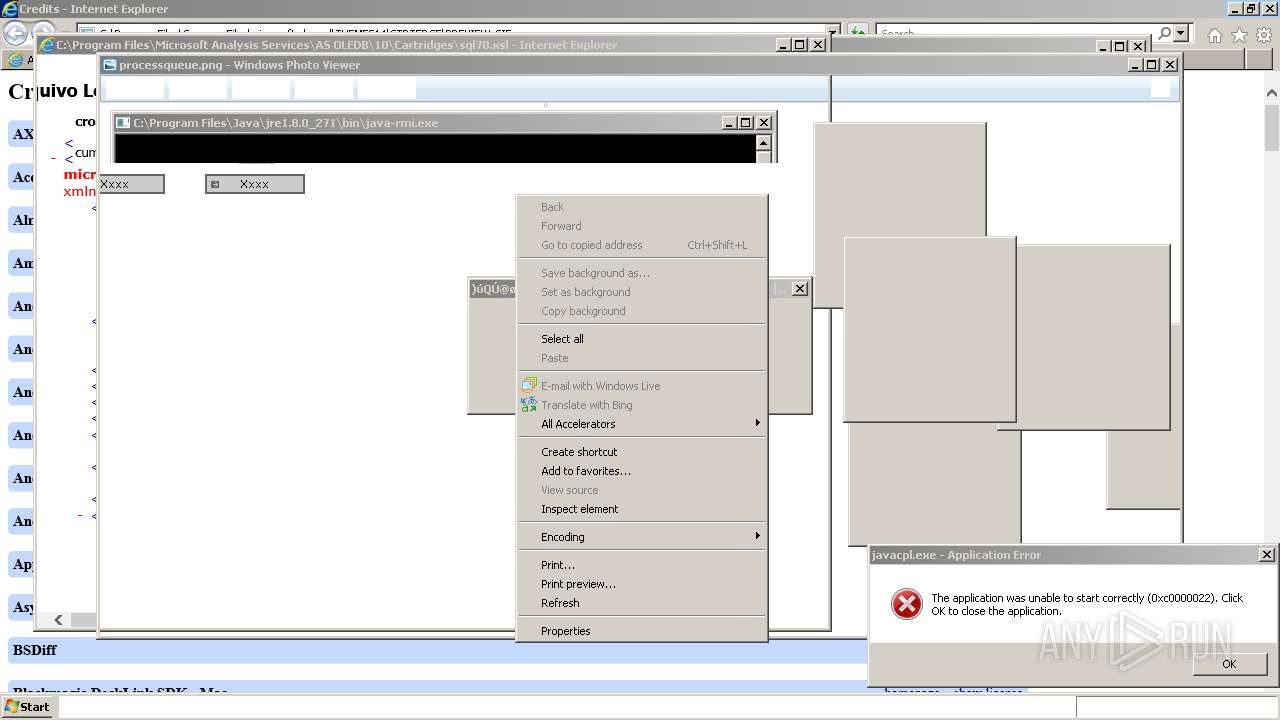
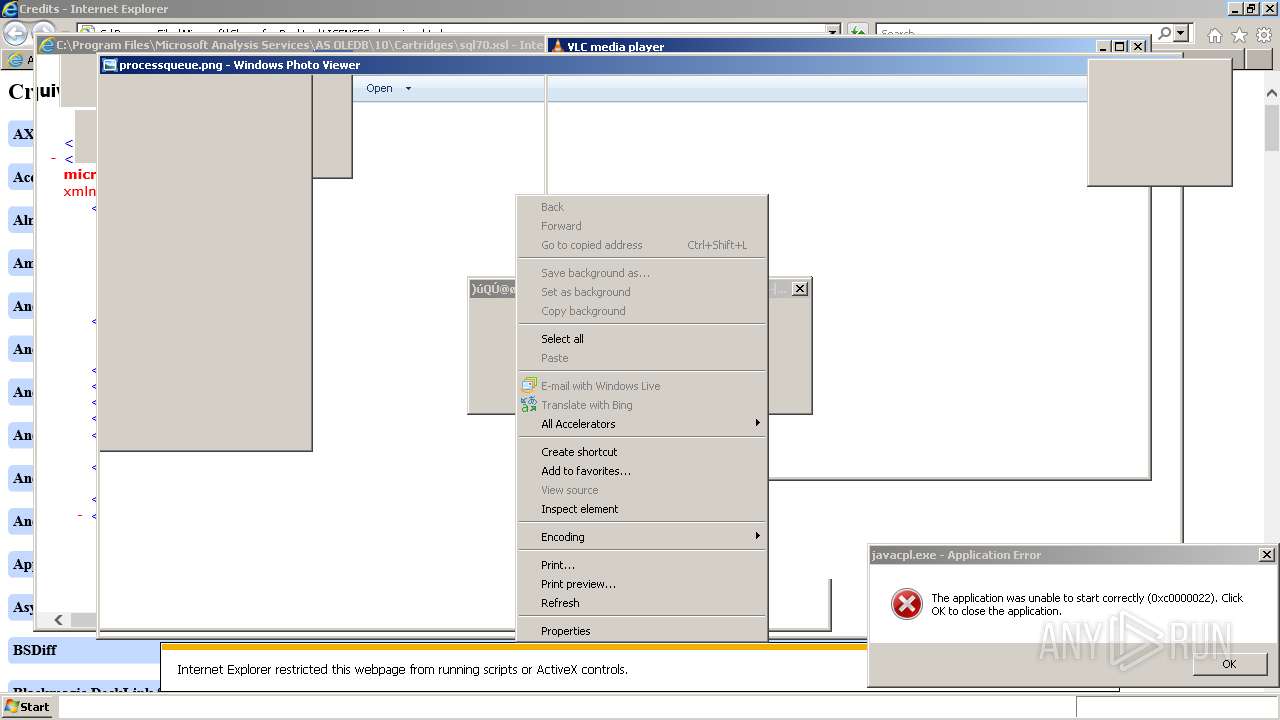
| Full analysis: | https://app.any.run/tasks/cc1c1ba8-d325-4ee6-9b9a-d7e1ea860740 |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2022, 01:33:28 |
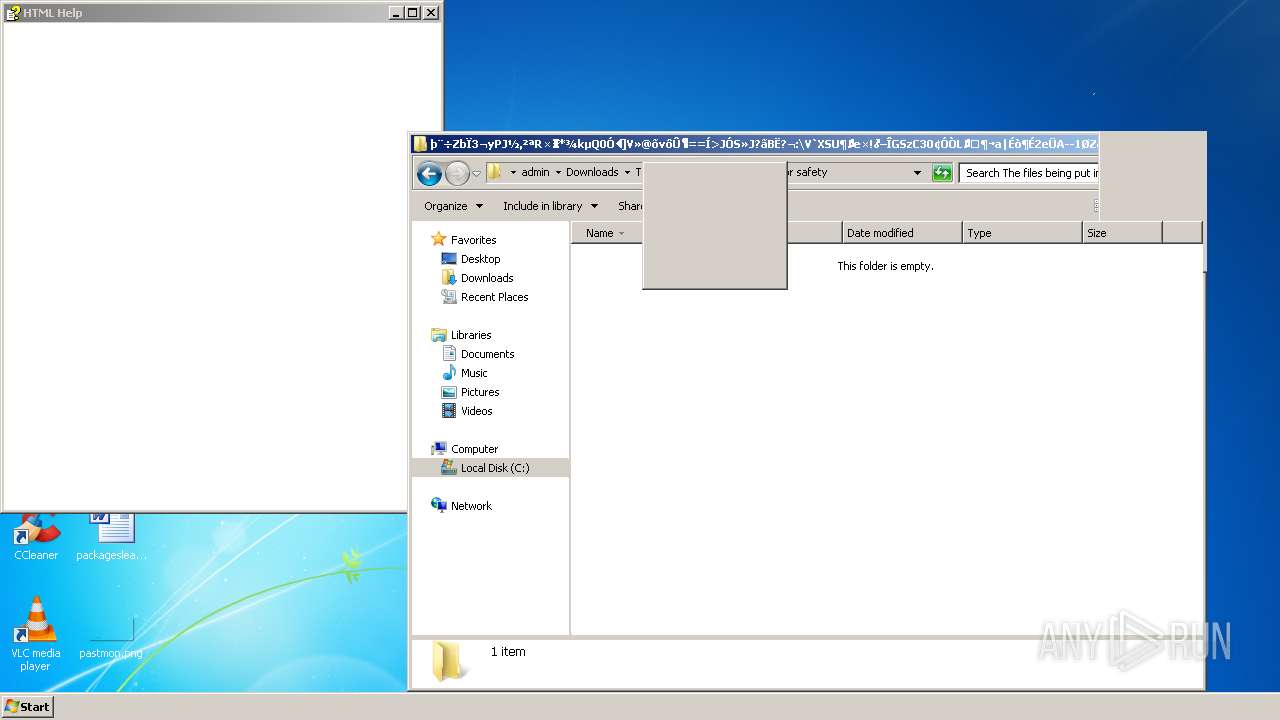
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 33D6A6C9B1079DEE3A5900D1E493F571 |
| SHA1: | 190DFB1398AEB7CD359329EDCBA252A0374FDD2A |
| SHA256: | 661E1FACE4154BD2A2542F686CB65BFA19D14C27589CF5064D67DB30427EC4D2 |
| SSDEEP: | 12:2jGRfdTja0Do0wZxf5Cu6DQRMvF6iFDDfys:26PPap0xxmMYiRr |
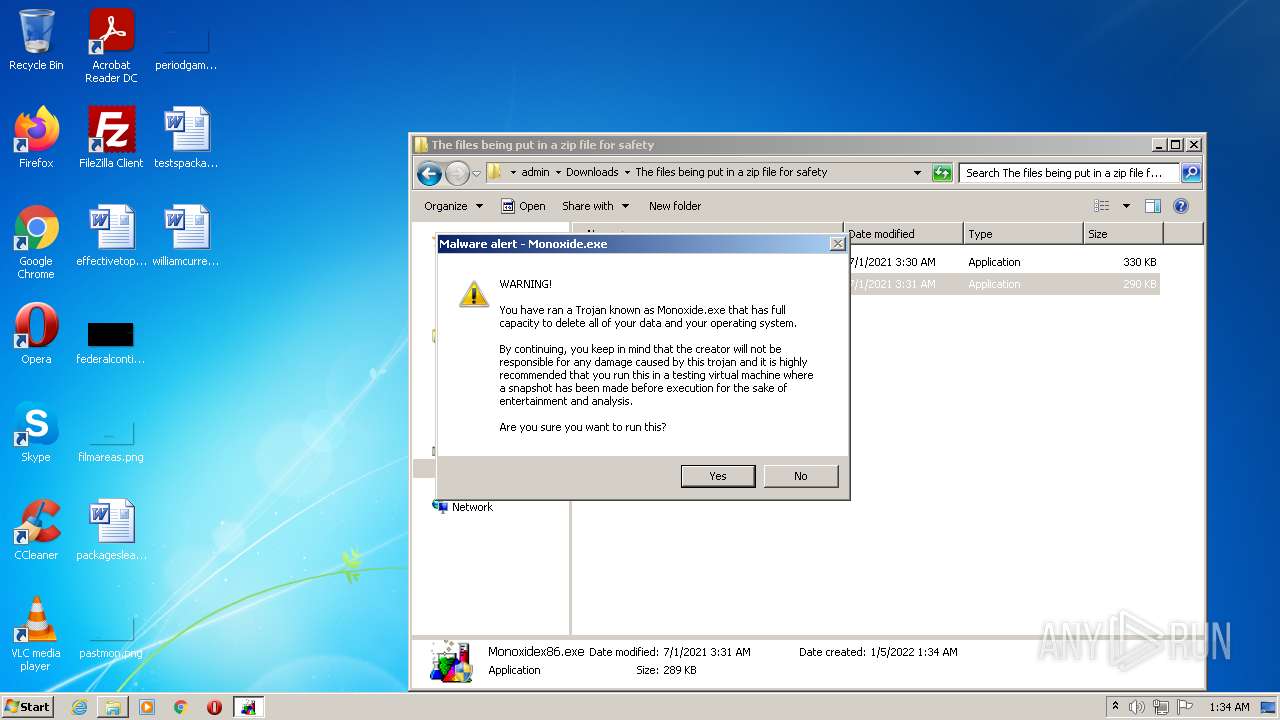
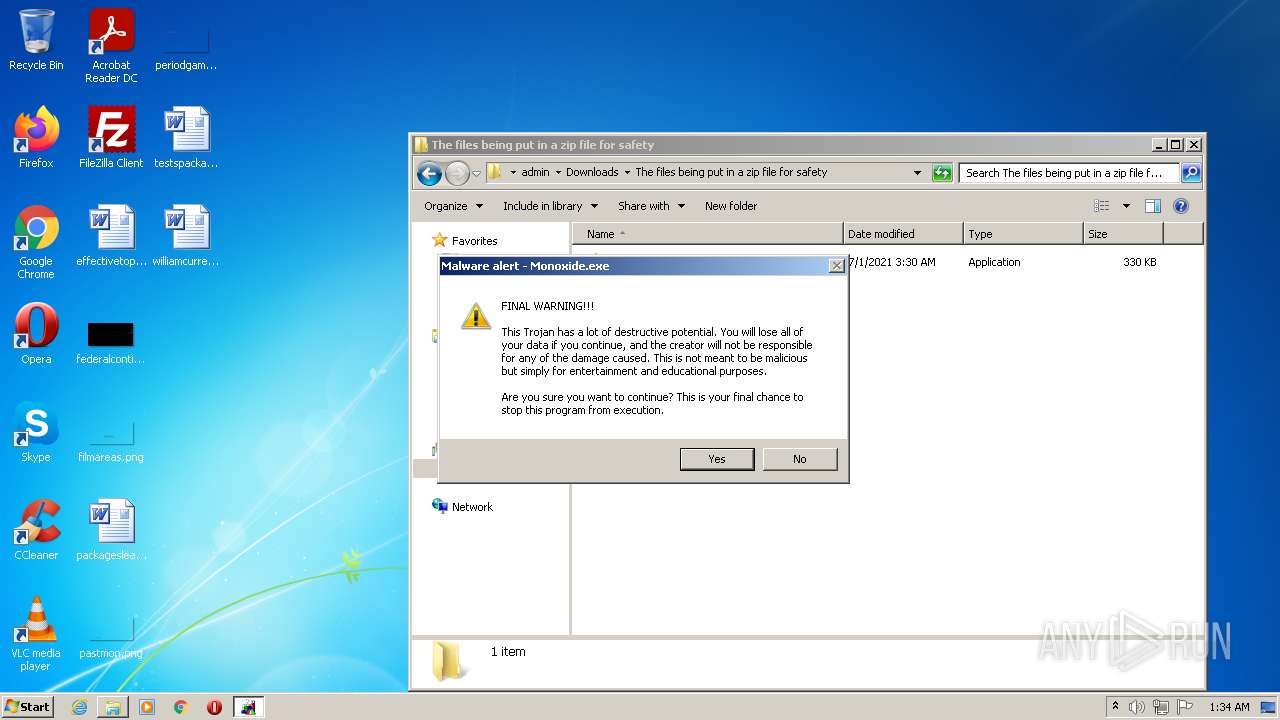
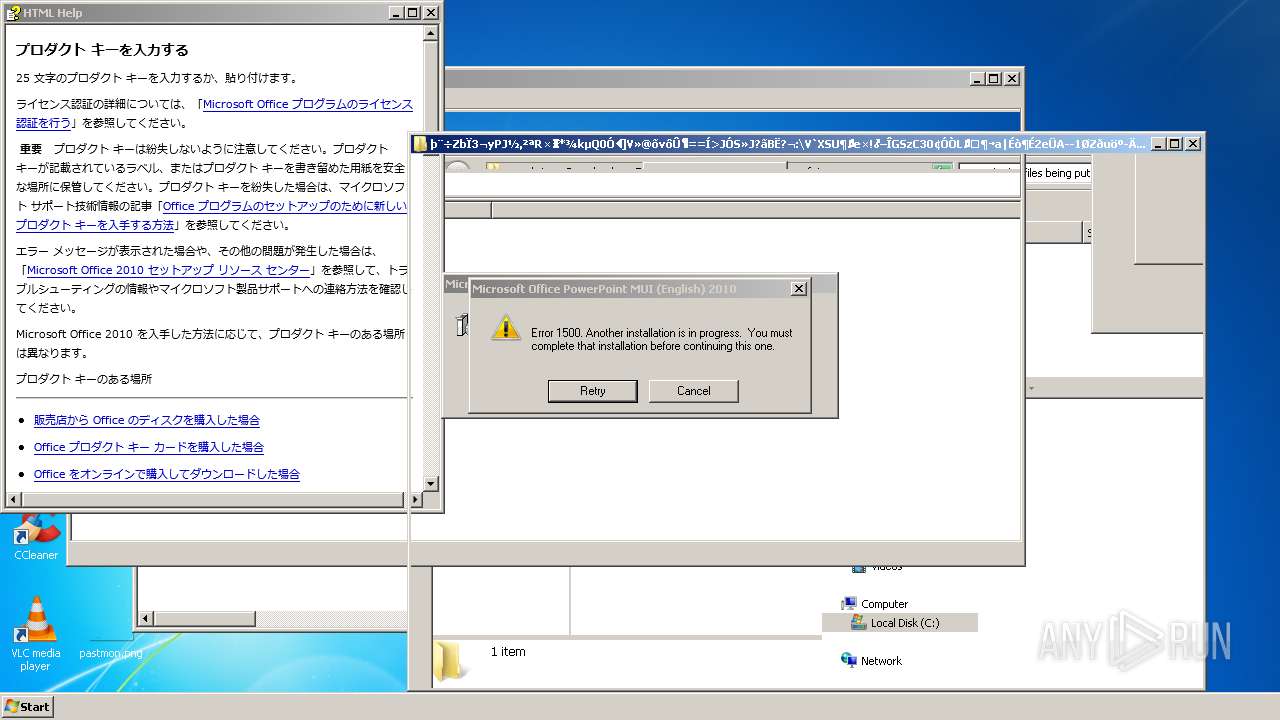
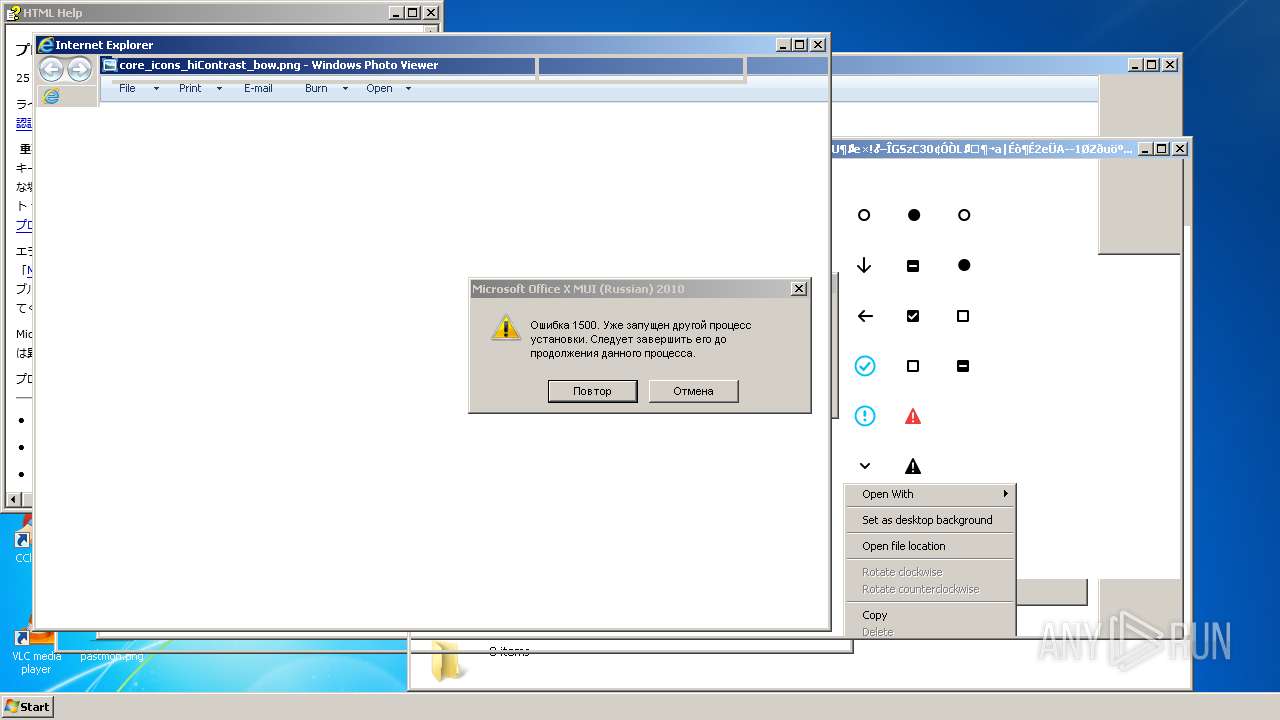
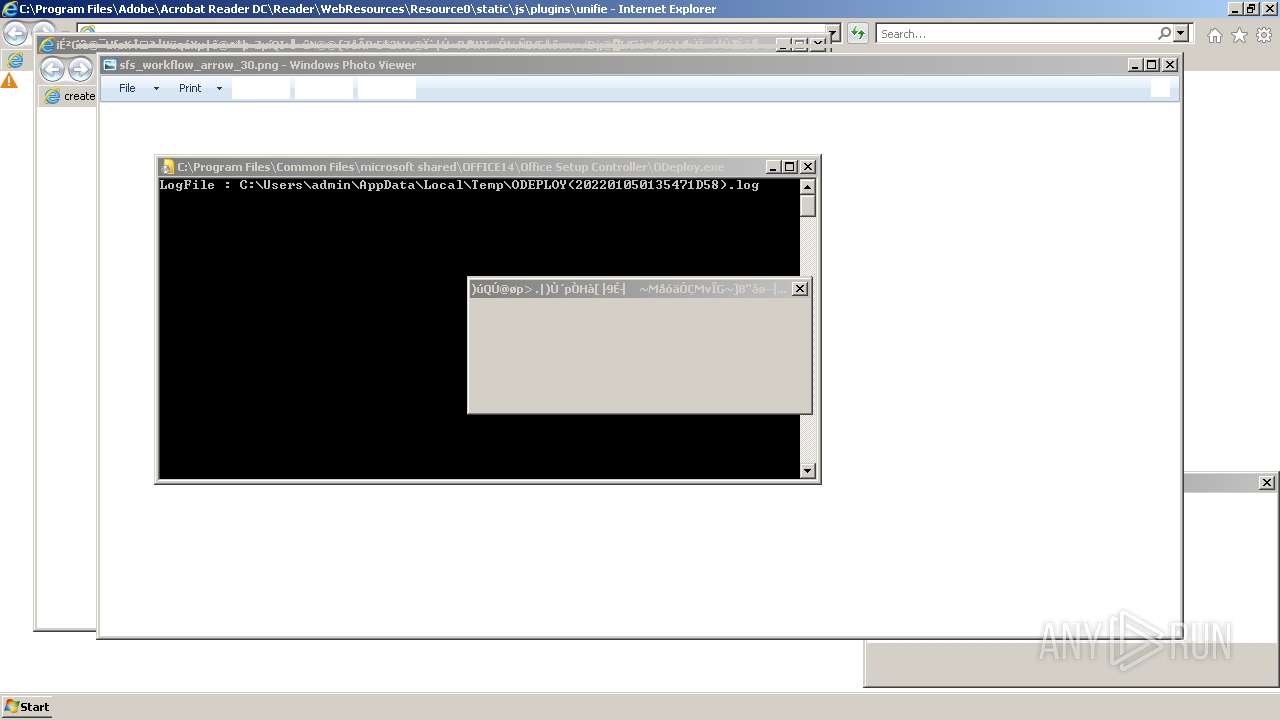
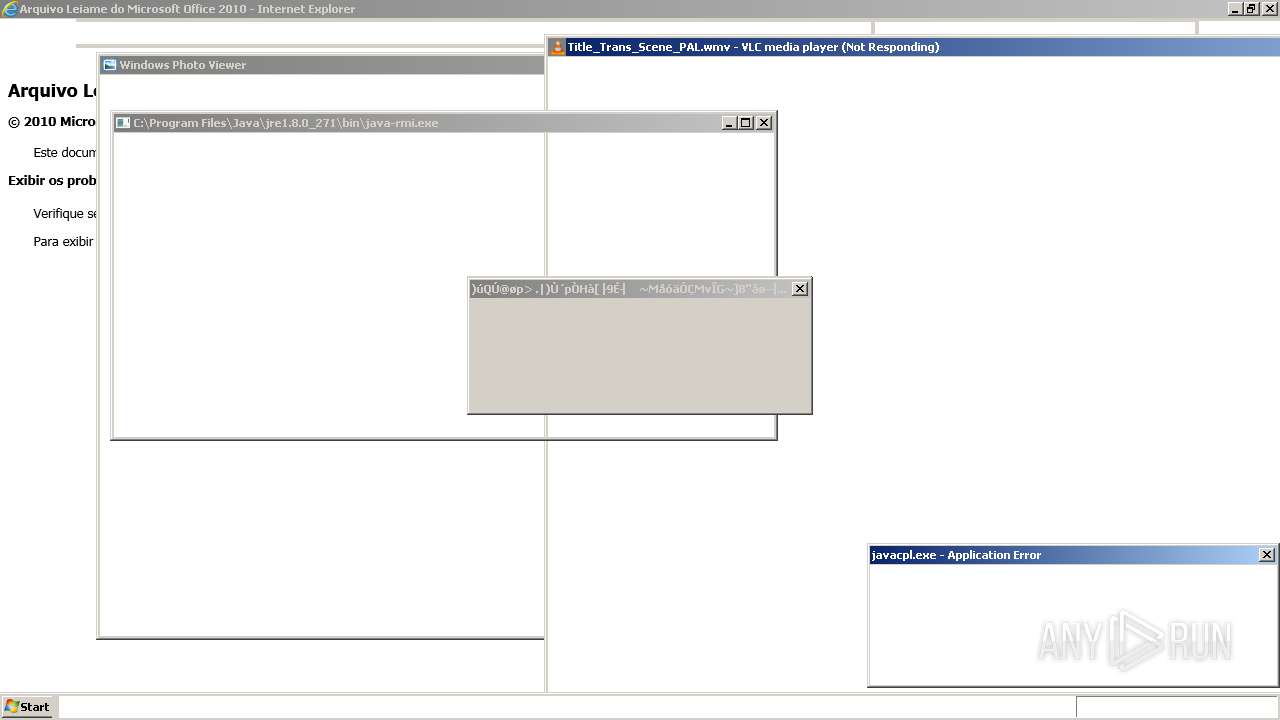
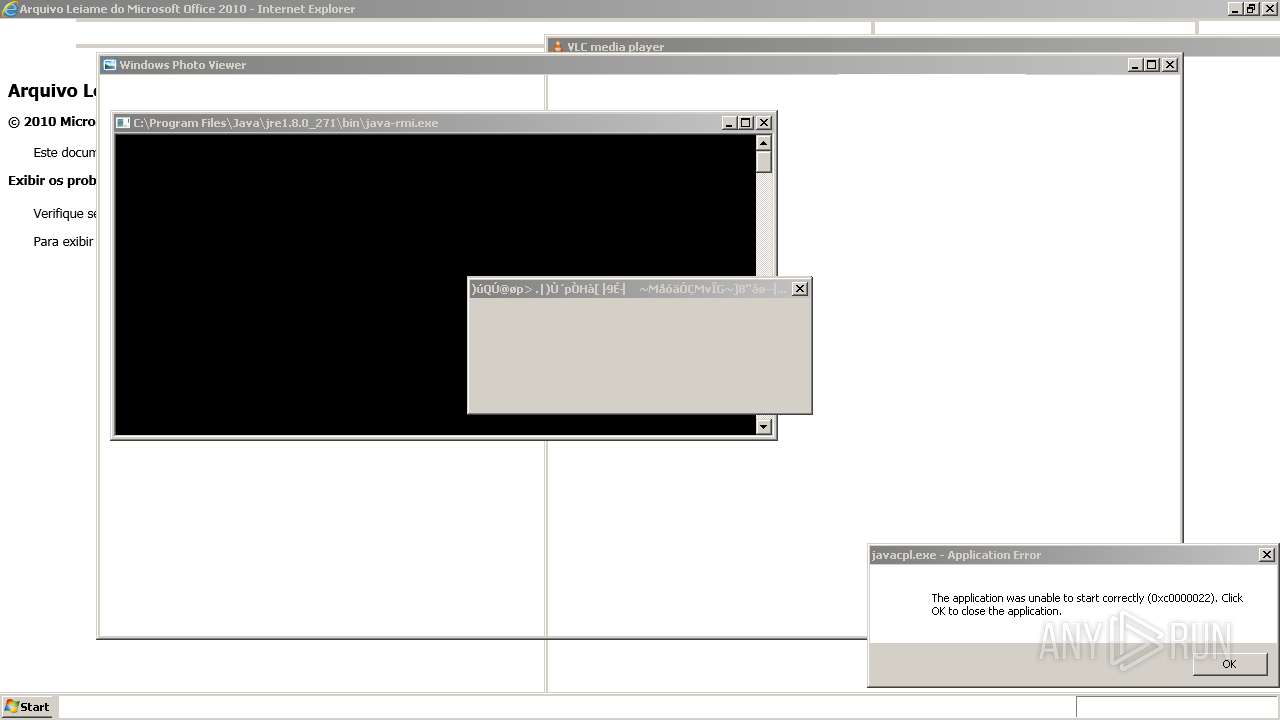
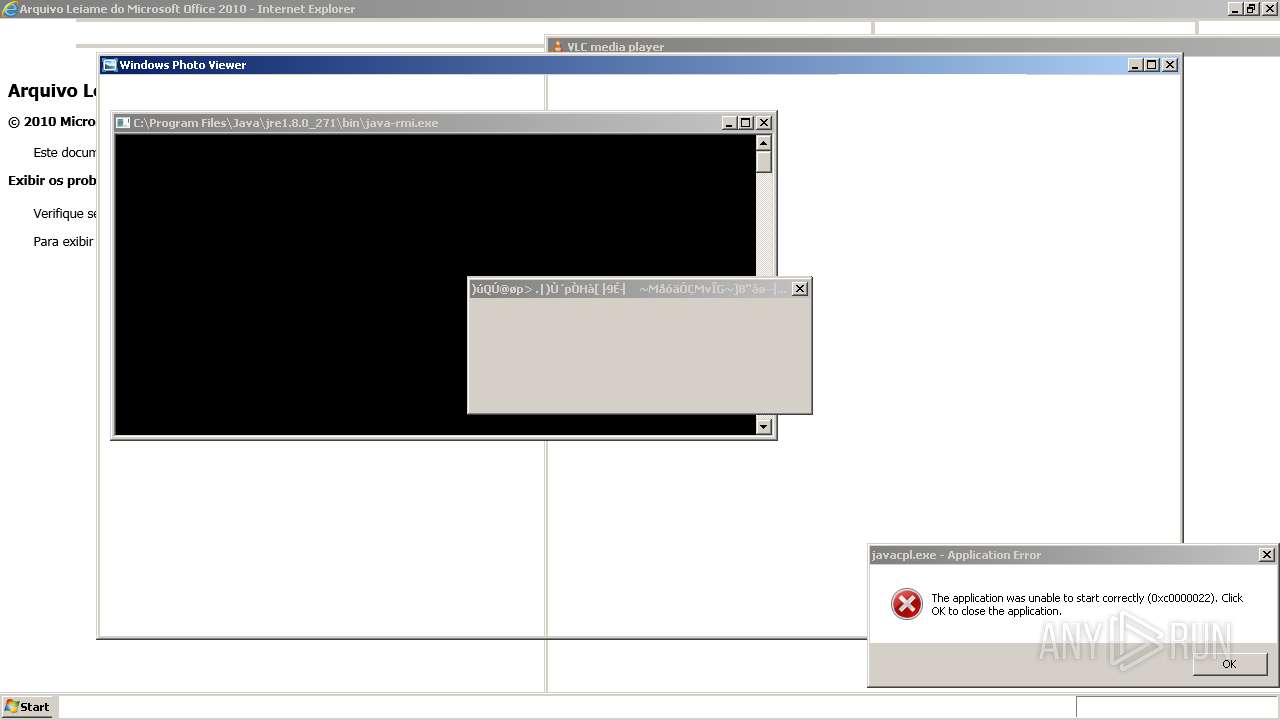
MALICIOUS
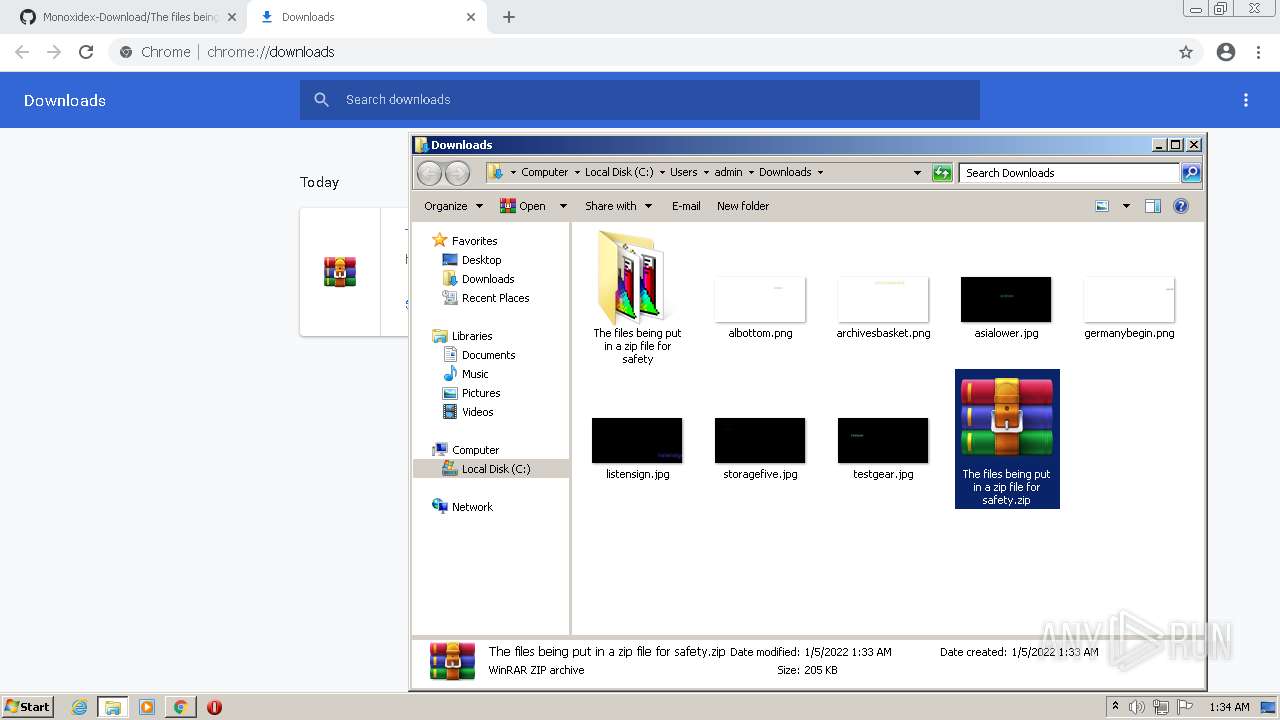
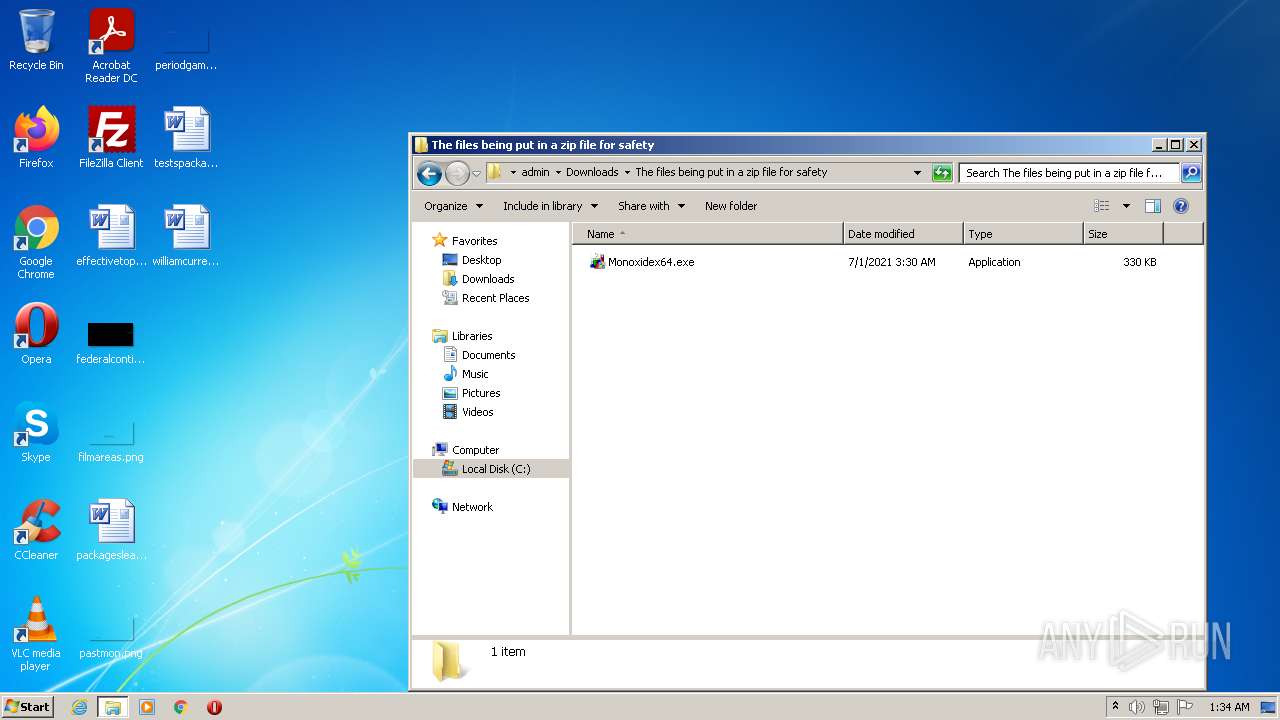
Drops executable file immediately after starts
- chrome.exe (PID: 676)
- Monoxidex86.exe (PID: 868)
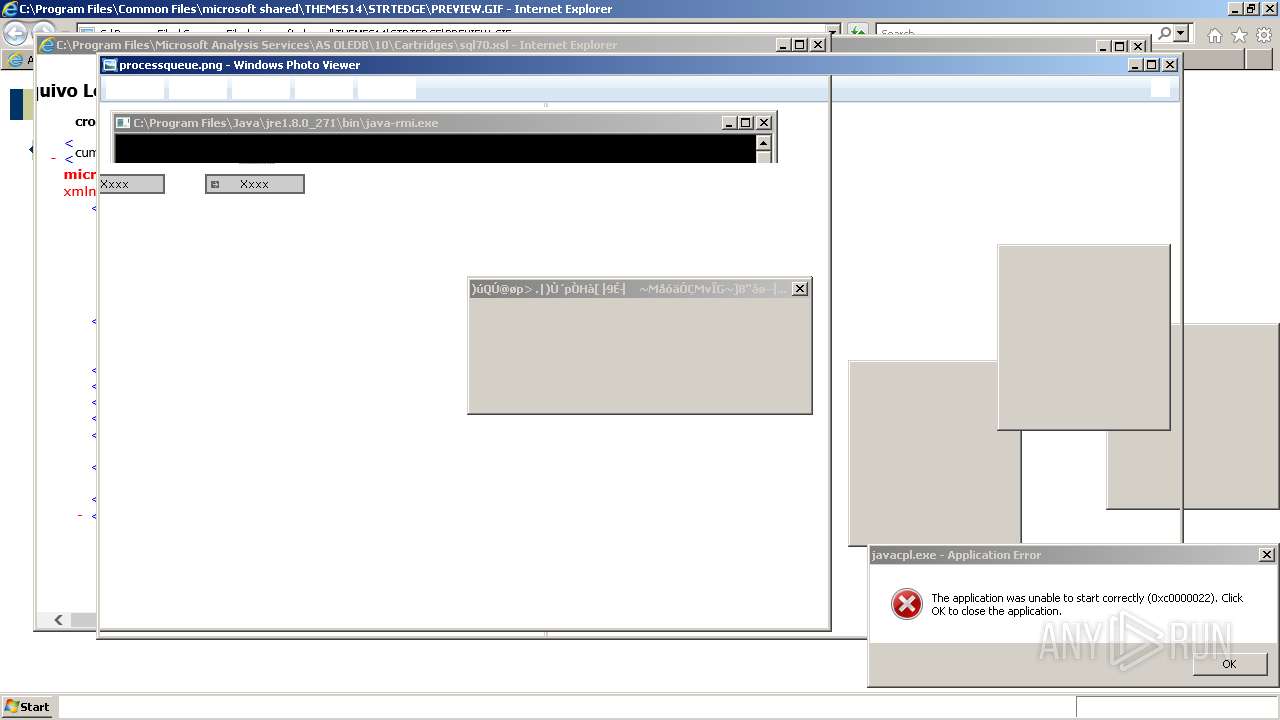
Application was dropped or rewritten from another process
- Monoxidex86.exe (PID: 968)
- Monoxidex86.exe (PID: 868)
- ????????????????.exe (PID: 1828)
Loads dropped or rewritten executable
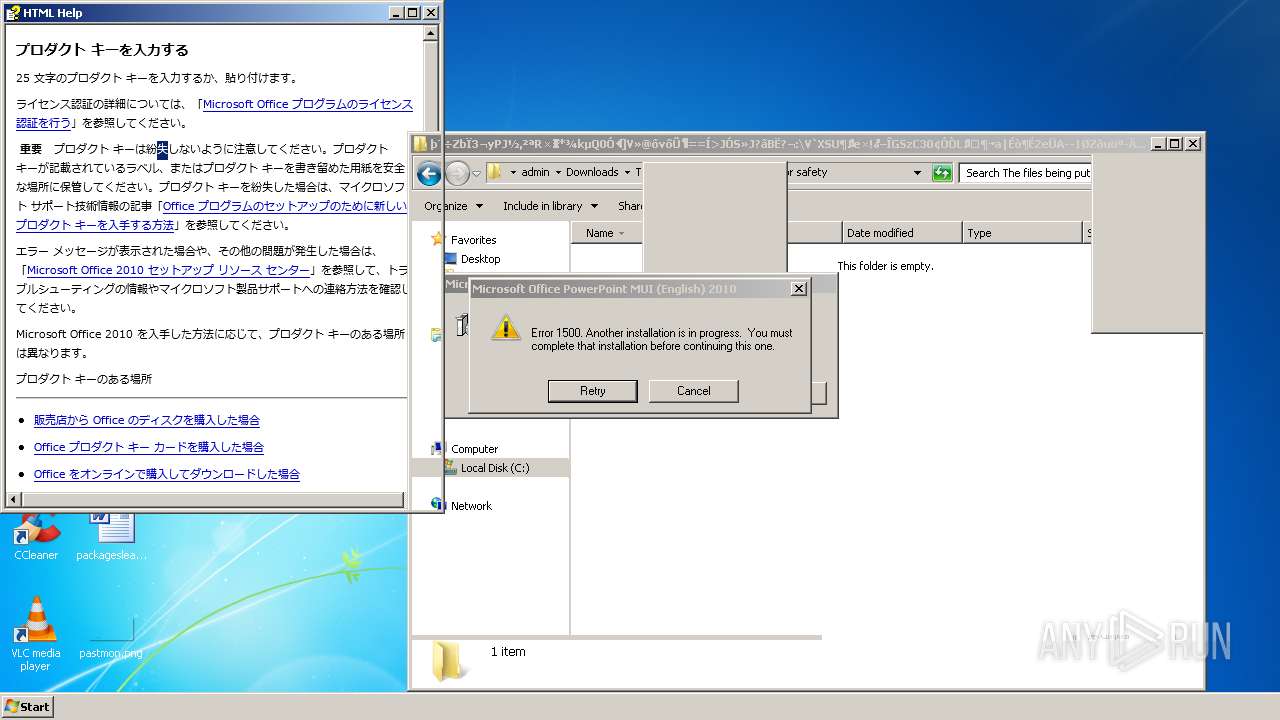
- MsiExec.exe (PID: 1412)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 676)
- WinRAR.exe (PID: 3708)
- Monoxidex86.exe (PID: 868)
- msiexec.exe (PID: 2992)
Reads the computer name
- WinRAR.exe (PID: 3708)
- WinRAR.exe (PID: 1936)
- ????????????????.exe (PID: 1828)
- WinRAR.exe (PID: 576)
- WinRAR.exe (PID: 2536)
- WinRAR.exe (PID: 3248)
- WinRAR.exe (PID: 1800)
- WinRAR.exe (PID: 3572)
- WinRAR.exe (PID: 976)
- AdobeCollabSync.exe (PID: 1404)
- AdobeCollabSync.exe (PID: 4020)
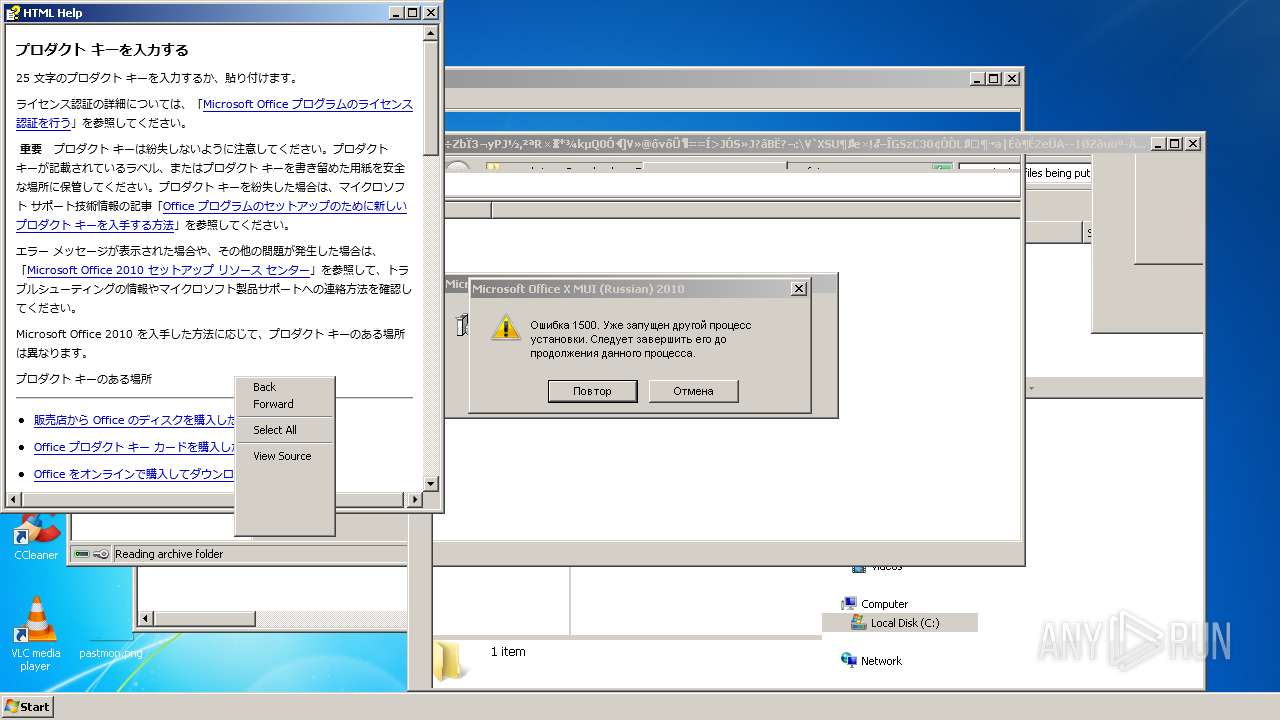
Checks supported languages
- WinRAR.exe (PID: 3708)
- Monoxidex86.exe (PID: 868)
- ????????????????.exe (PID: 1828)
- WinRAR.exe (PID: 1936)
- WinRAR.exe (PID: 576)
- WinRAR.exe (PID: 1800)
- WinRAR.exe (PID: 3248)
- WinRAR.exe (PID: 3572)
- WinRAR.exe (PID: 2536)
- WinRAR.exe (PID: 976)
- AdobeCollabSync.exe (PID: 4020)
- AdobeCollabSync.exe (PID: 1404)
Starts itself from another location
- Monoxidex86.exe (PID: 868)
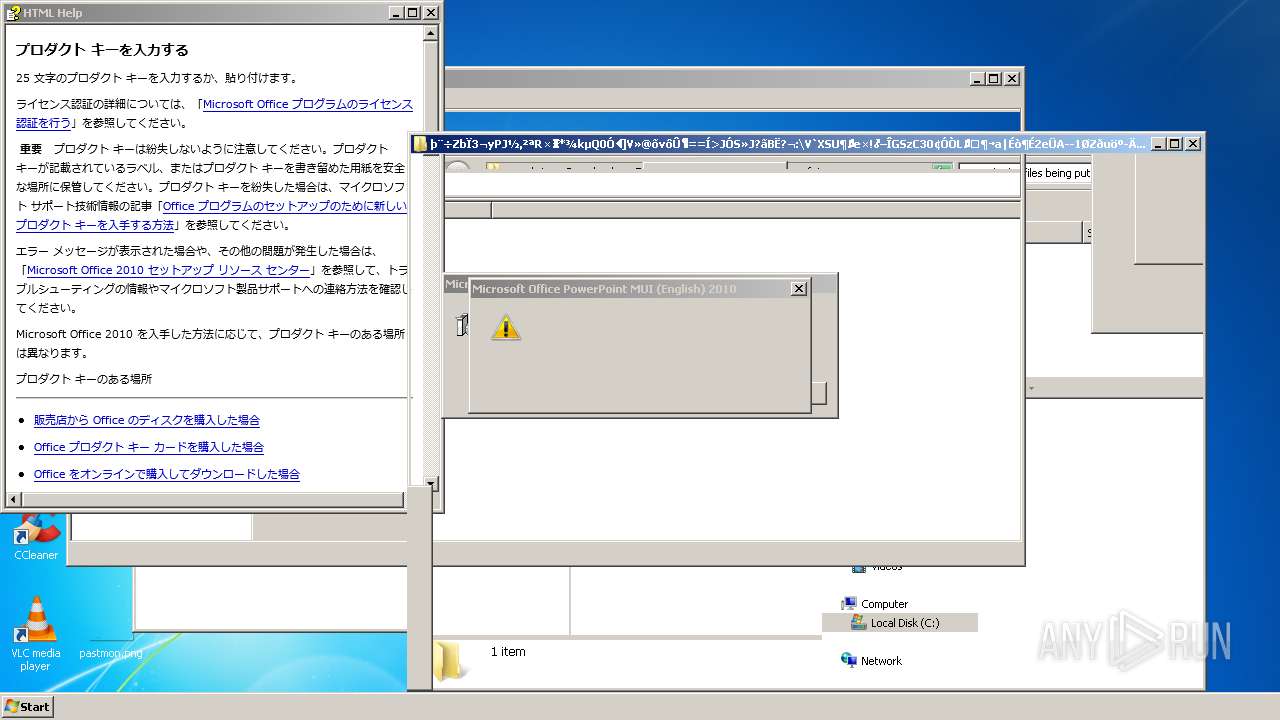
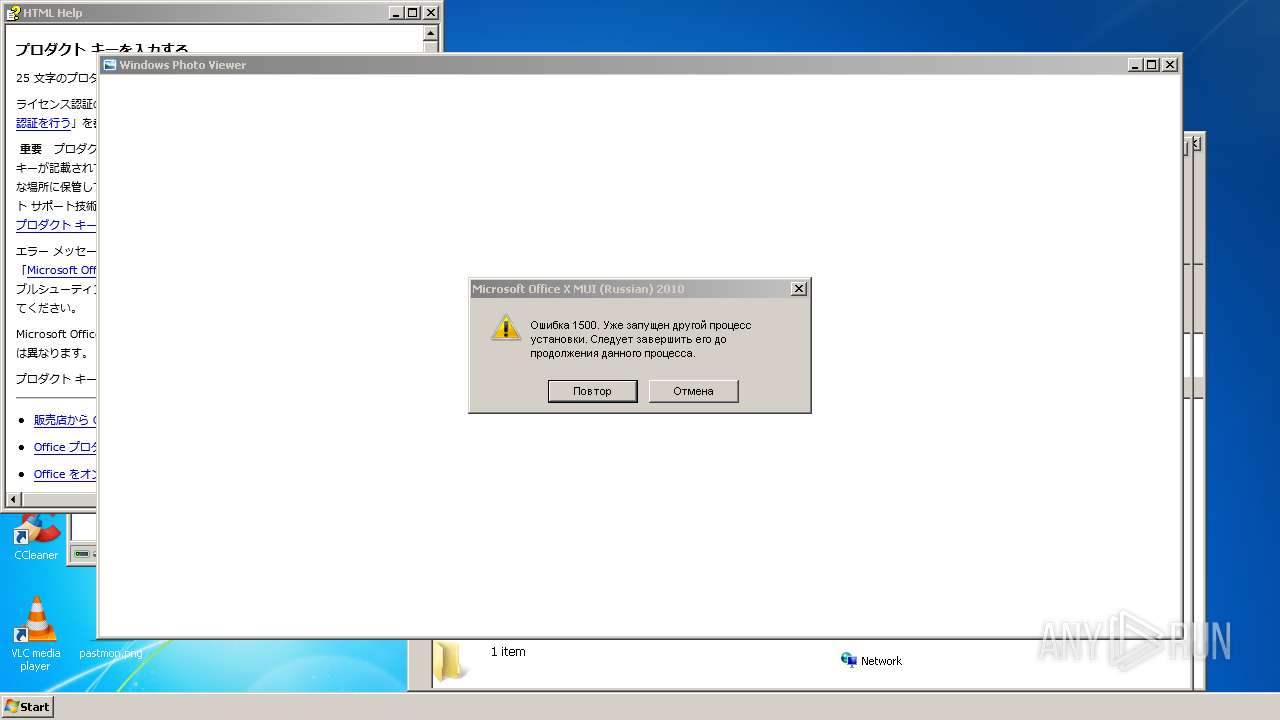
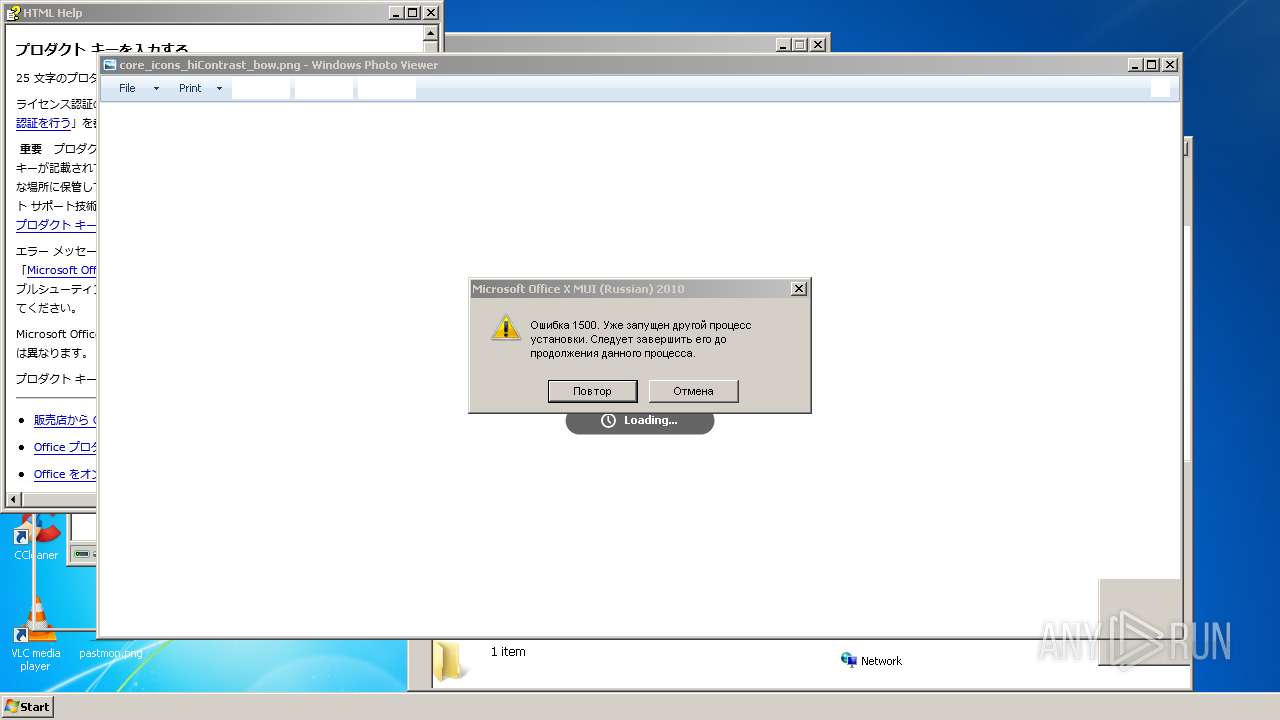
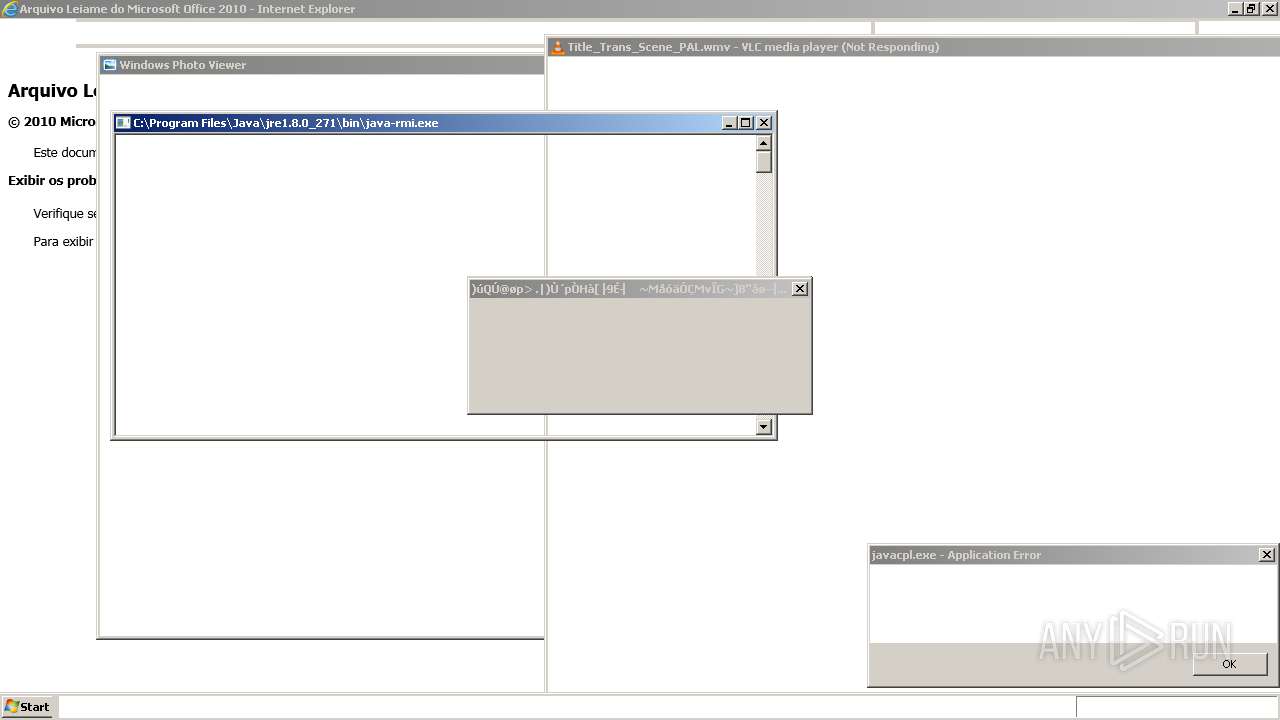
Starts Microsoft Installer
- ????????????????.exe (PID: 1828)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3220)
- msiexec.exe (PID: 1444)
- msiexec.exe (PID: 1240)
- msiexec.exe (PID: 2720)
- msiexec.exe (PID: 3432)
- msiexec.exe (PID: 2992)
Reads the date of Windows installation
- ????????????????.exe (PID: 1828)
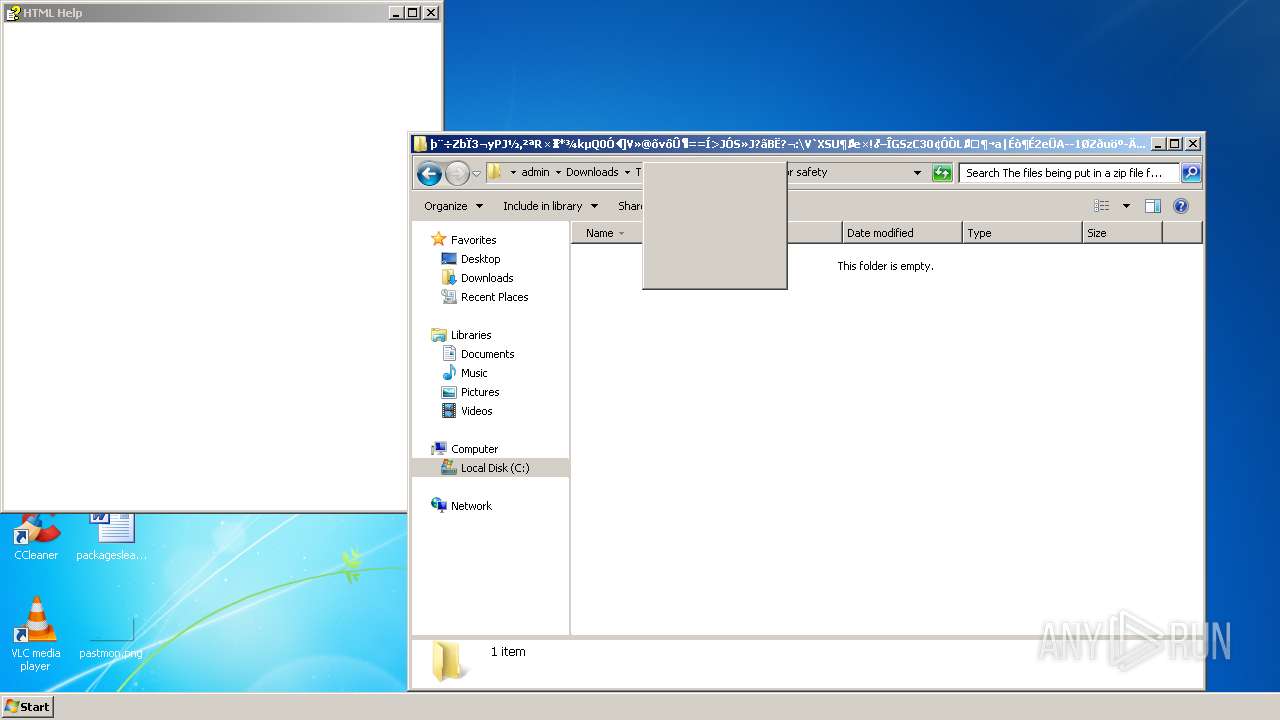
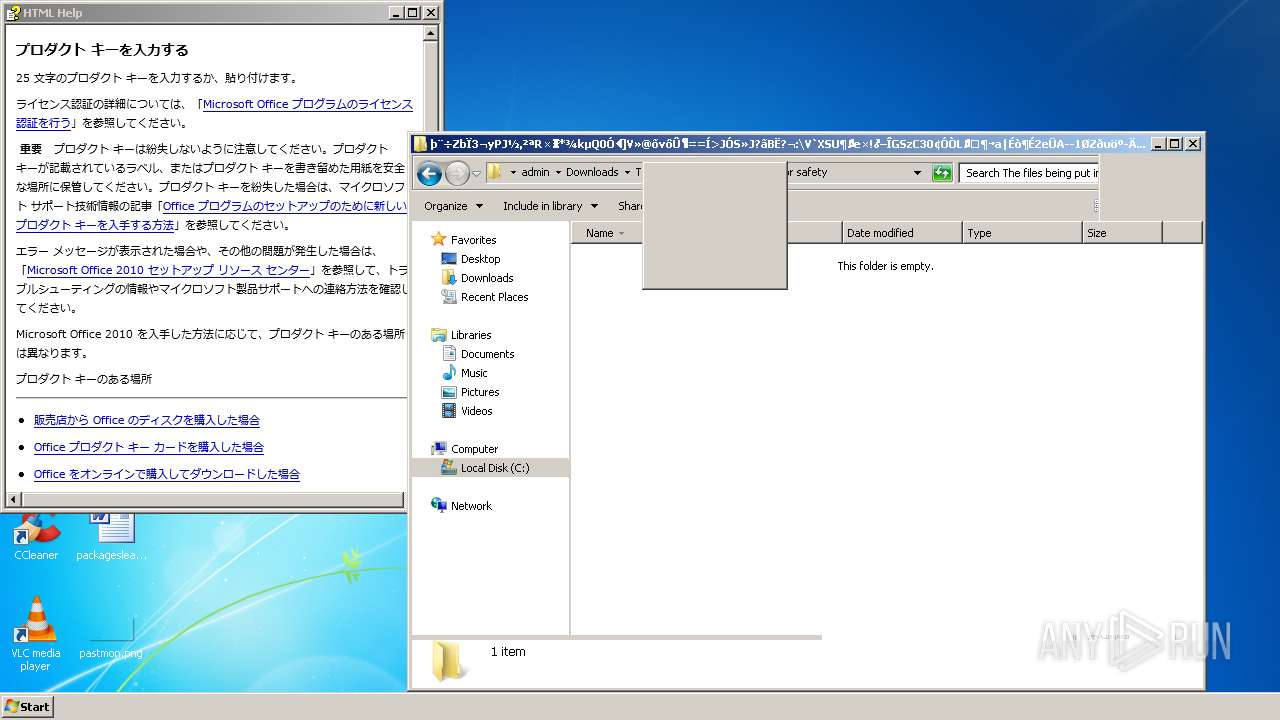
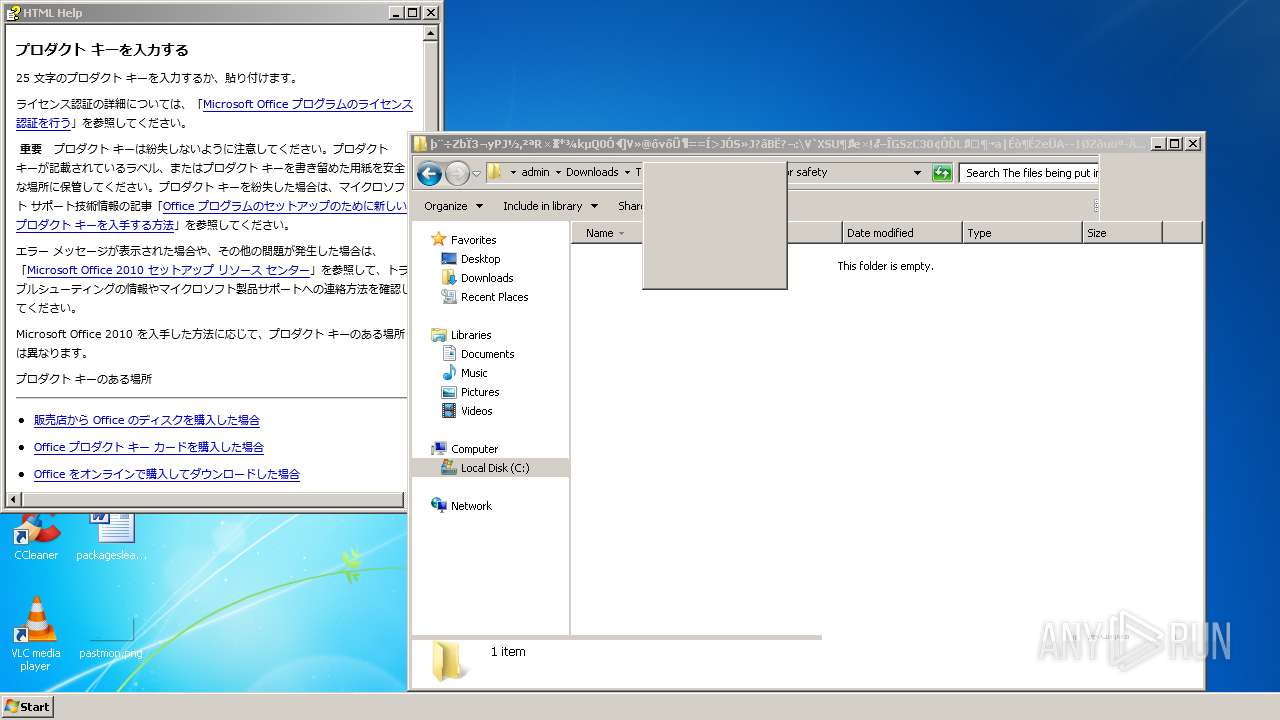
Reads Microsoft Outlook installation path
- hh.exe (PID: 3588)
Executed as Windows Service
- msiexec.exe (PID: 2992)
Reads the Windows organization settings
- msiexec.exe (PID: 3220)
- msiexec.exe (PID: 1444)
- msiexec.exe (PID: 1240)
- msiexec.exe (PID: 2720)
- msiexec.exe (PID: 3432)
- msiexec.exe (PID: 2992)
Reads default file associations for system extensions
- ????????????????.exe (PID: 1828)
Reads internet explorer settings
- hh.exe (PID: 3588)
Executed via COM
- DllHost.exe (PID: 3916)
Application launched itself
- AdobeCollabSync.exe (PID: 1404)
- msiexec.exe (PID: 2992)
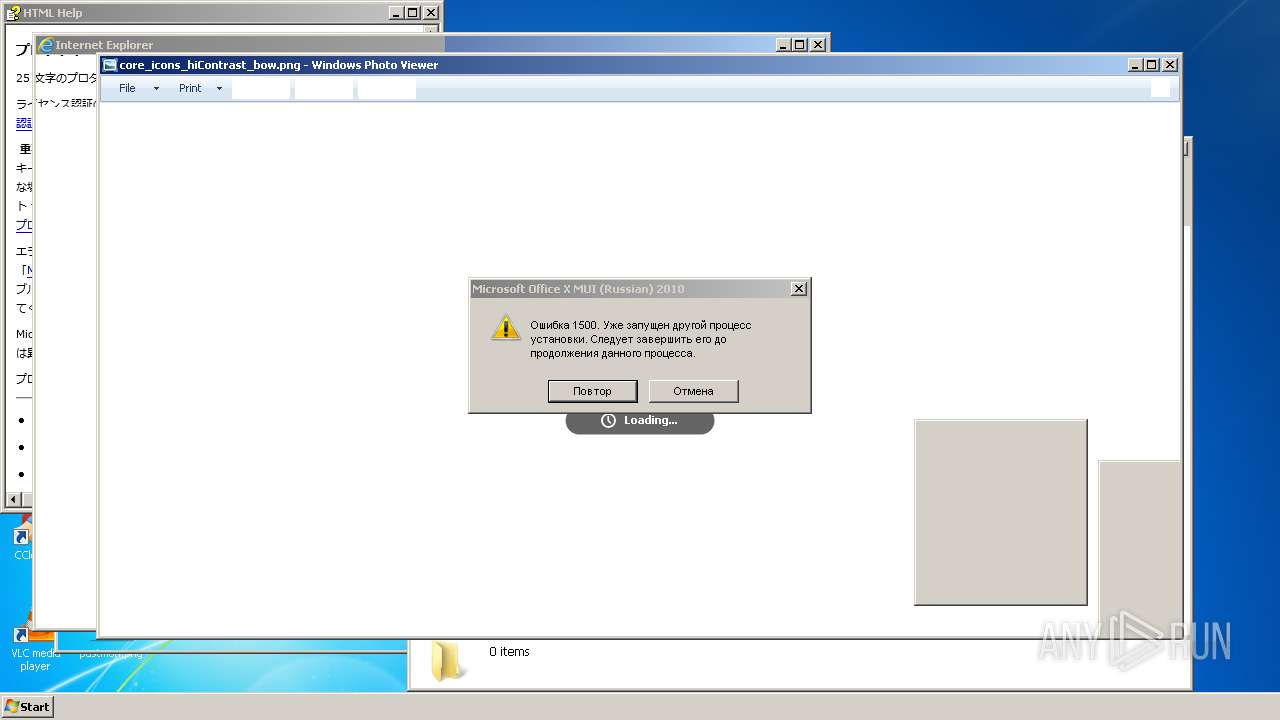
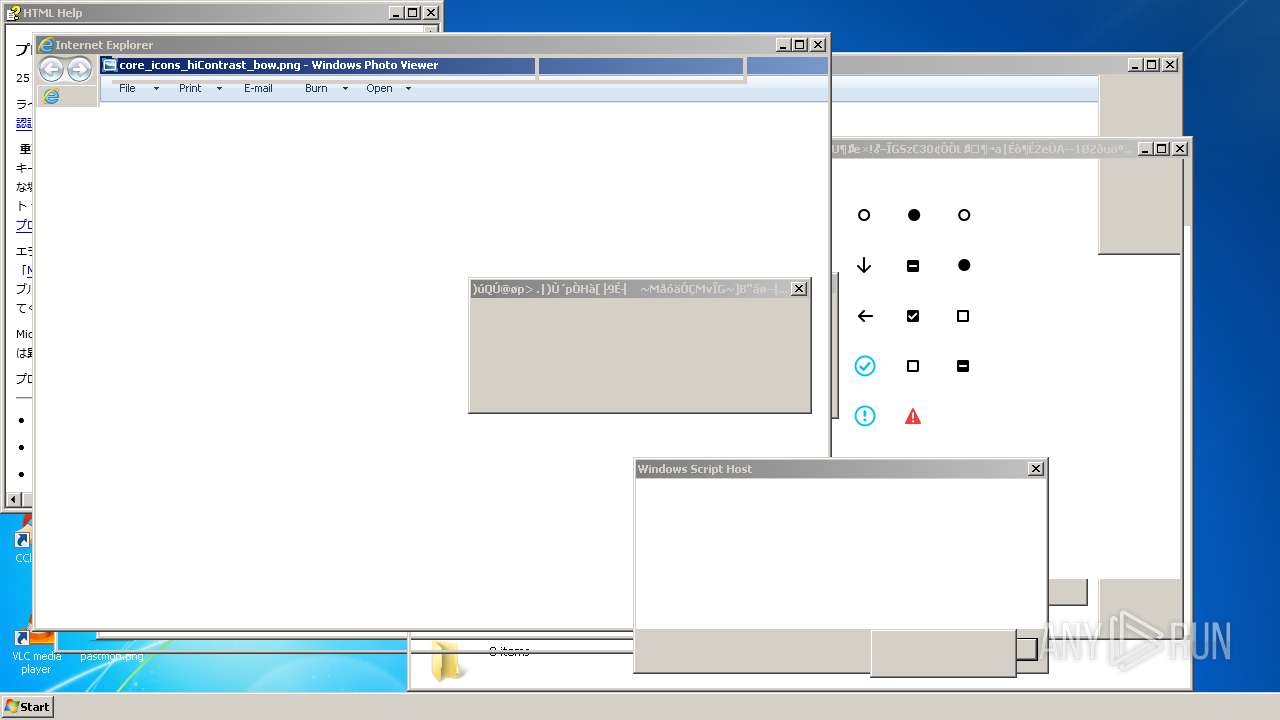
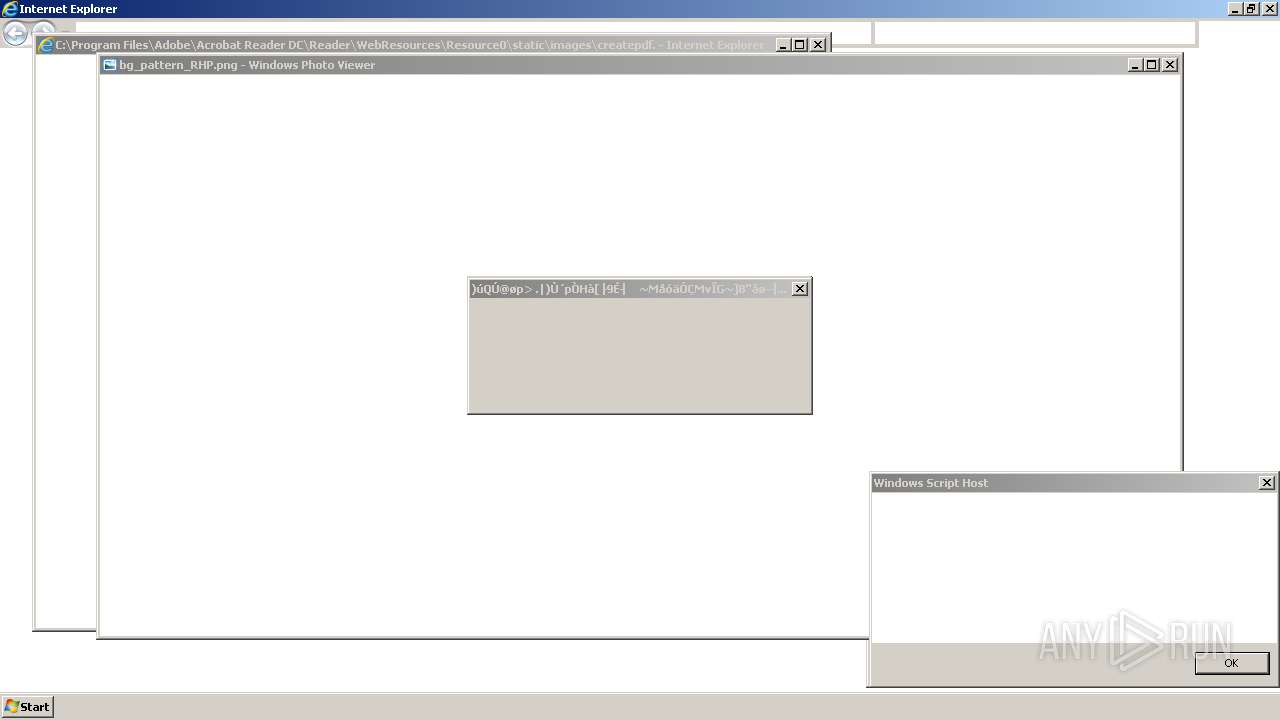
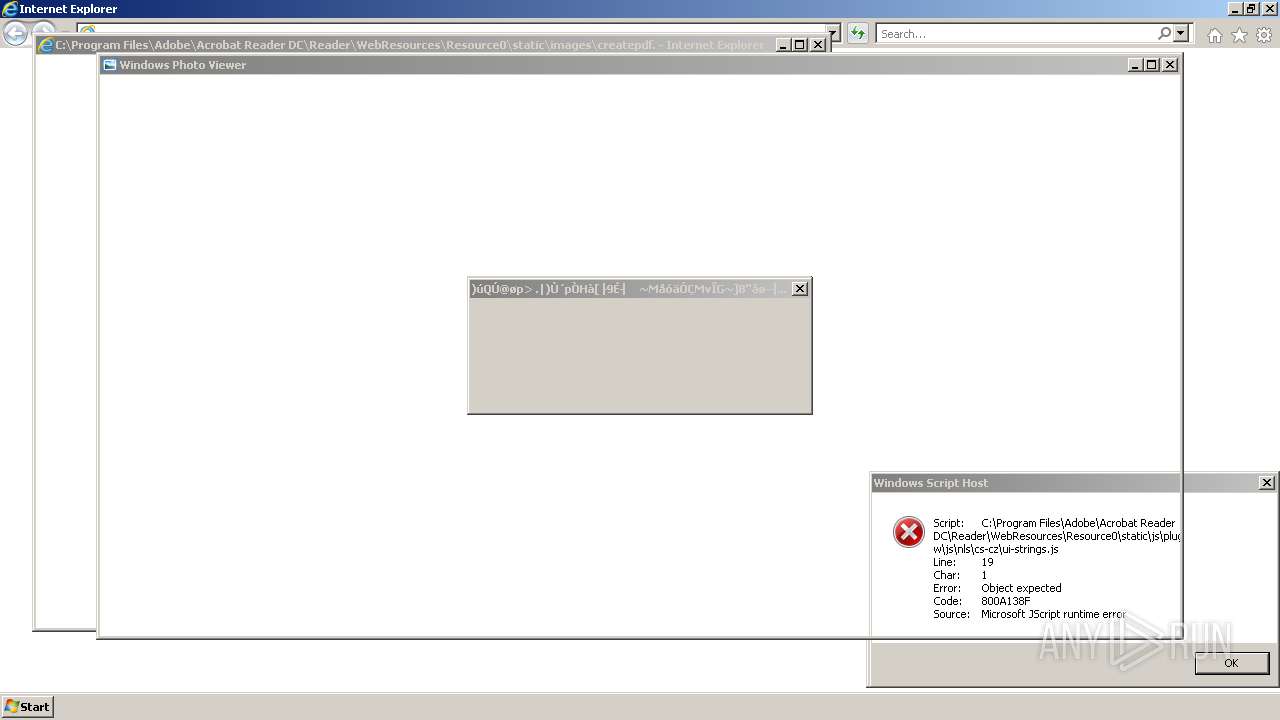
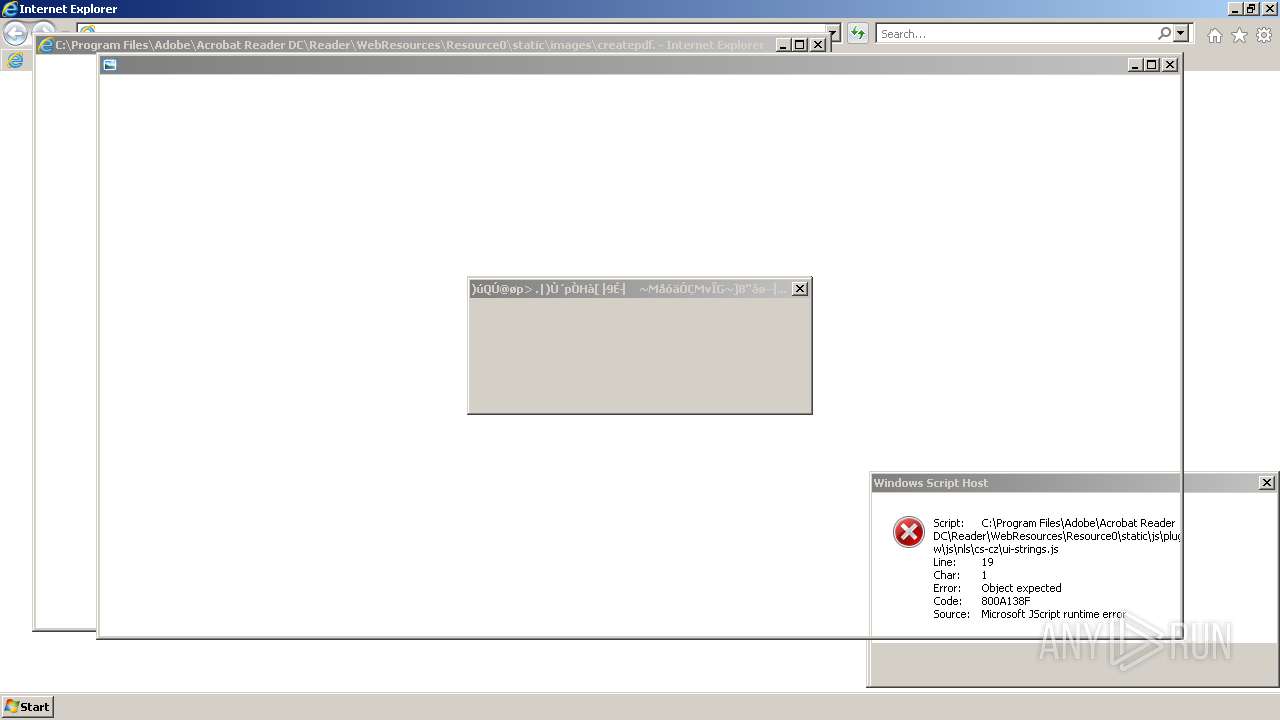
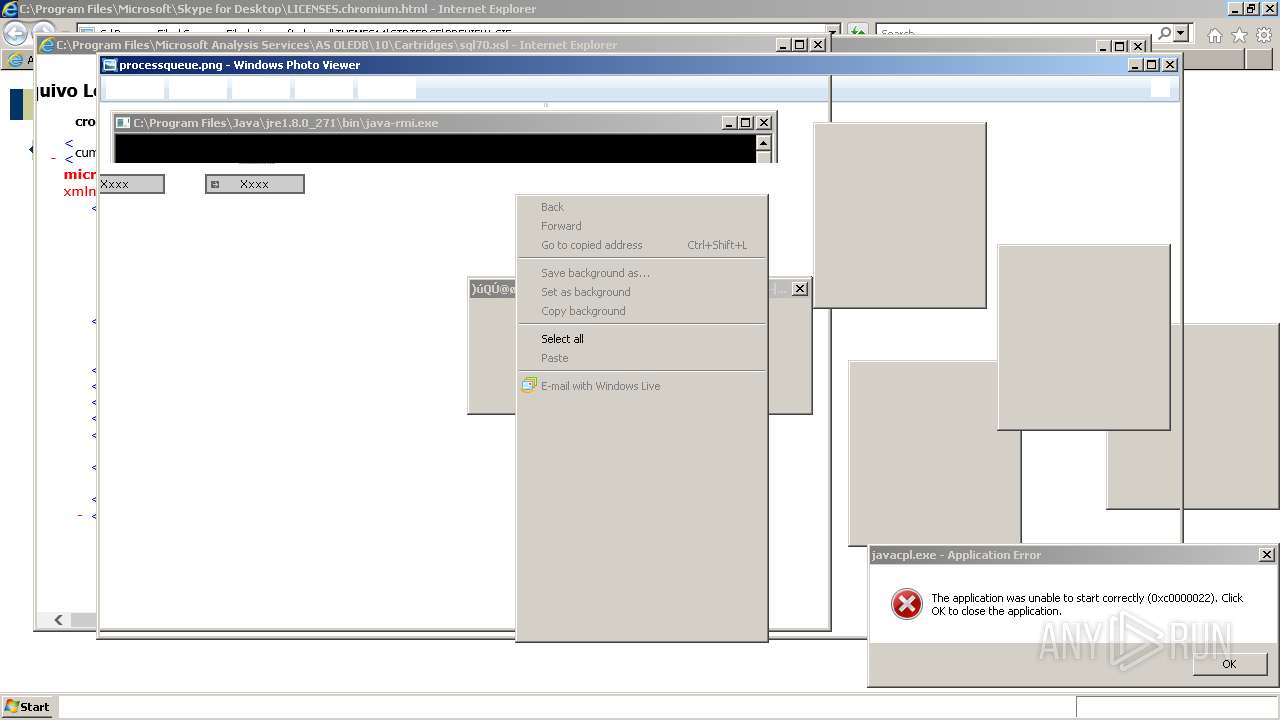
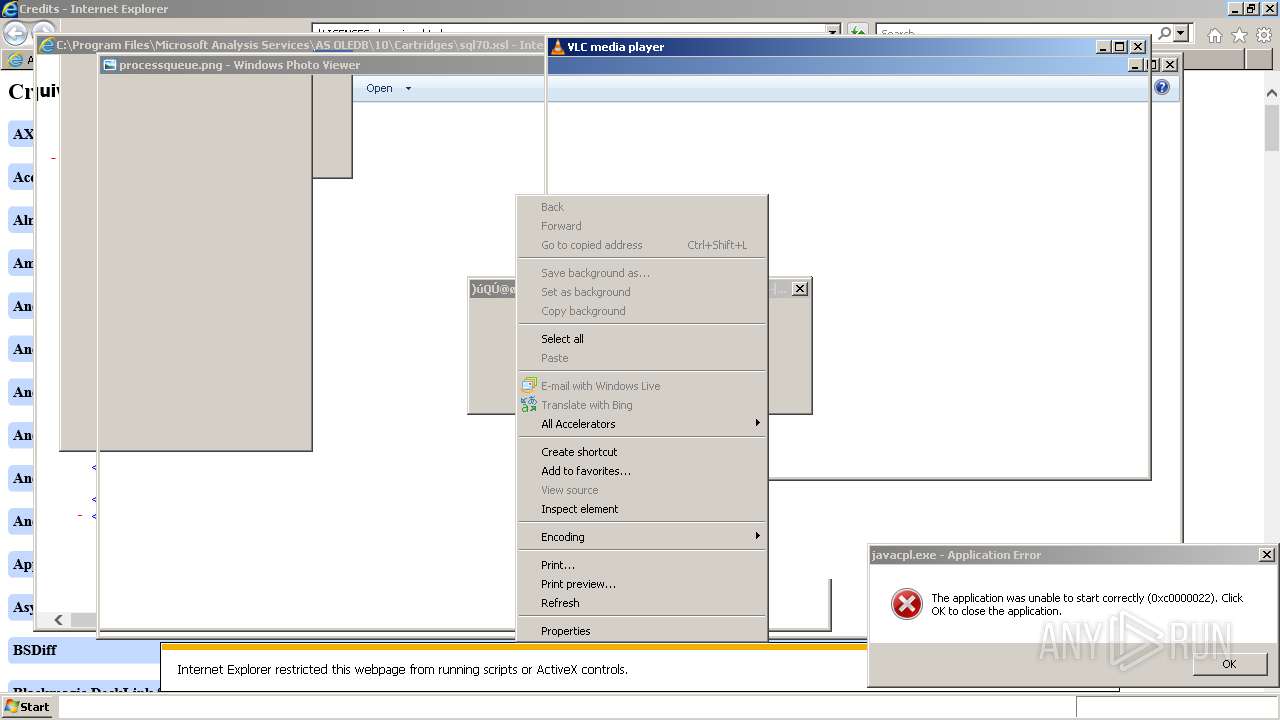
Starts Internet Explorer
- ????????????????.exe (PID: 1828)
- MSOXMLED.EXE (PID: 2888)
- MSOXMLED.EXE (PID: 2708)
- MSOXMLED.EXE (PID: 3960)
- MSOXMLED.EXE (PID: 2832)
- MSOXMLED.EXE (PID: 516)
- MSOXMLED.EXE (PID: 1564)
- MSOXMLED.EXE (PID: 4036)
- MSOXMLED.EXE (PID: 3444)
- MSOXMLED.EXE (PID: 2300)
- MSOXMLED.EXE (PID: 3412)
- MSOXMLED.EXE (PID: 2144)
- MSOXMLED.EXE (PID: 1272)
Drops a file with too old compile date
- msiexec.exe (PID: 2992)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 2992)
INFO
Reads the computer name
- chrome.exe (PID: 1372)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 636)
- chrome.exe (PID: 2376)
- MSOXMLED.EXE (PID: 4036)
- MSOXMLED.EXE (PID: 1564)
- MSOXMLED.EXE (PID: 2832)
- MSOXMLED.EXE (PID: 516)
- MSOXMLED.EXE (PID: 2888)
- MSOXMLED.EXE (PID: 3960)
- MSOXMLED.EXE (PID: 2380)
- MSOXMLED.EXE (PID: 2708)
- MSOXMLED.EXE (PID: 276)
- MSOXMLED.EXE (PID: 3500)
- MSOXMLED.EXE (PID: 2944)
- hh.exe (PID: 3588)
- MSOXMLED.EXE (PID: 2824)
- MSOXMLED.EXE (PID: 2144)
- MSOXMLED.EXE (PID: 2424)
- MSOXMLED.EXE (PID: 3444)
- msiexec.exe (PID: 3220)
- MSOXMLED.EXE (PID: 3412)
- MSOXMLED.EXE (PID: 2300)
- MSOXMLED.EXE (PID: 1272)
- msiexec.exe (PID: 1240)
- msiexec.exe (PID: 2992)
- msiexec.exe (PID: 1444)
- msiexec.exe (PID: 3432)
- msiexec.exe (PID: 2720)
Checks supported languages
- chrome.exe (PID: 1372)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 1340)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 676)
- chrome.exe (PID: 636)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 2376)
- MSOXMLED.EXE (PID: 1564)
- MSOXMLED.EXE (PID: 2832)
- MSOXMLED.EXE (PID: 4036)
- MSOXMLED.EXE (PID: 3960)
- MSOXMLED.EXE (PID: 516)
- MSOXMLED.EXE (PID: 2888)
- msiexec.exe (PID: 1240)
- msiexec.exe (PID: 3220)
- MSOXMLED.EXE (PID: 2708)
- MSOXMLED.EXE (PID: 276)
- MSOXMLED.EXE (PID: 2380)
- MSOXMLED.EXE (PID: 3500)
- MSOXMLED.EXE (PID: 2944)
- hh.exe (PID: 3588)
- MSOXMLED.EXE (PID: 2144)
- MSOXMLED.EXE (PID: 2824)
- MSOXMLED.EXE (PID: 3444)
- MSOXMLED.EXE (PID: 2424)
- msiexec.exe (PID: 1444)
- msiexec.exe (PID: 3432)
- MSOXMLED.EXE (PID: 2300)
- MSOXMLED.EXE (PID: 3412)
- MSOXMLED.EXE (PID: 1272)
- msiexec.exe (PID: 2992)
- msiexec.exe (PID: 2720)
Application launched itself
- chrome.exe (PID: 1372)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 684)
- iexplore.exe (PID: 3004)
- iexplore.exe (PID: 1256)
- iexplore.exe (PID: 4116)
- iexplore.exe (PID: 2528)
- iexplore.exe (PID: 4124)
- iexplore.exe (PID: 4352)
- iexplore.exe (PID: 4332)
- iexplore.exe (PID: 4720)
- iexplore.exe (PID: 4728)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 4136)
Reads the hosts file
- chrome.exe (PID: 1372)
- chrome.exe (PID: 2624)
Reads settings of System Certificates
- chrome.exe (PID: 2624)
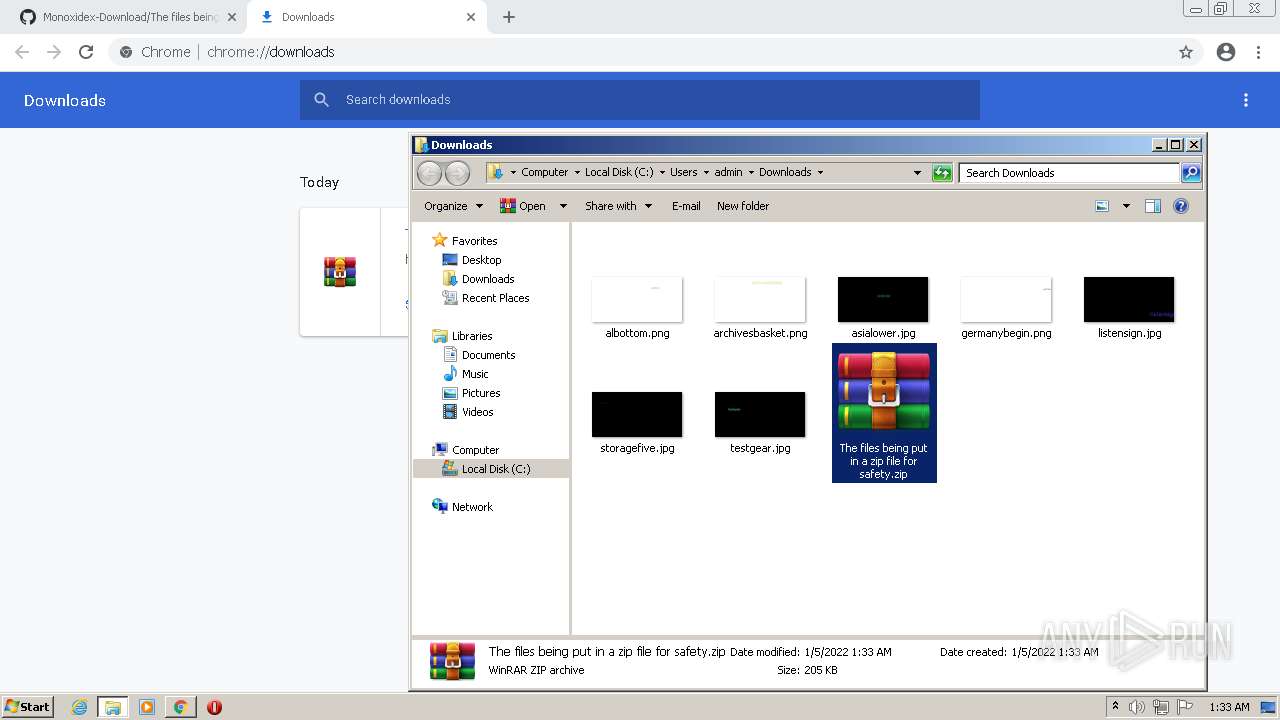
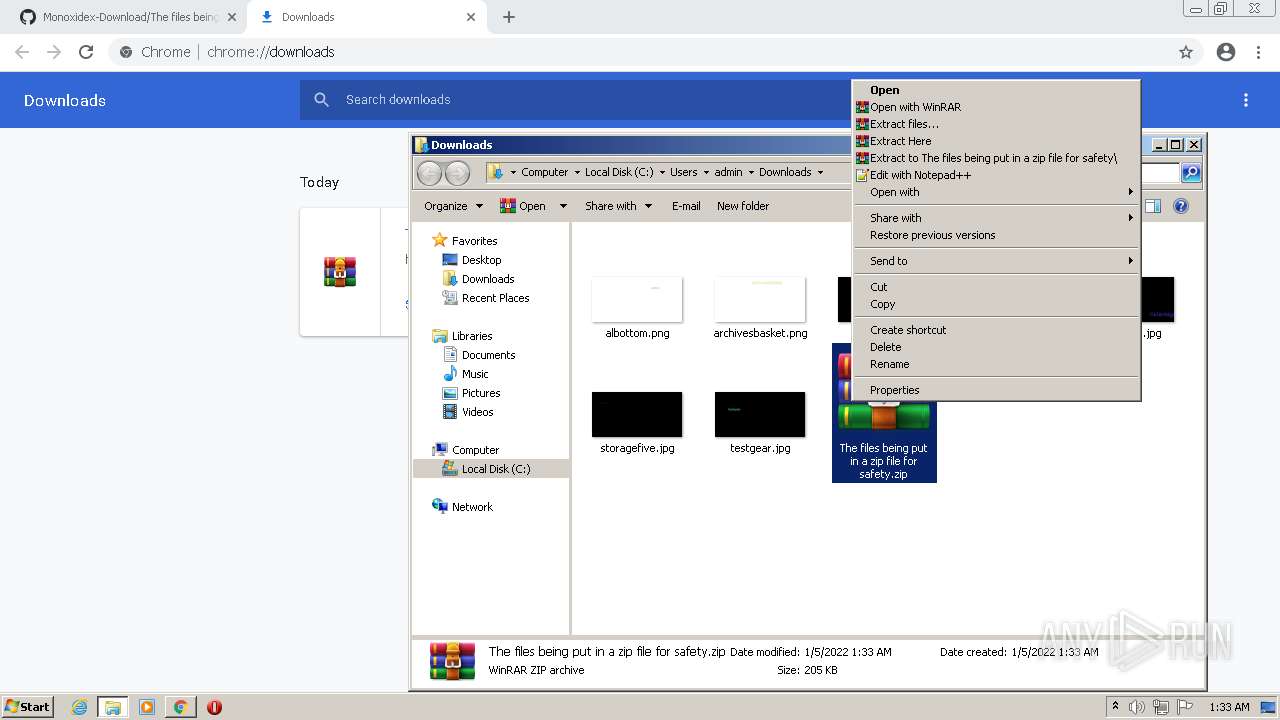
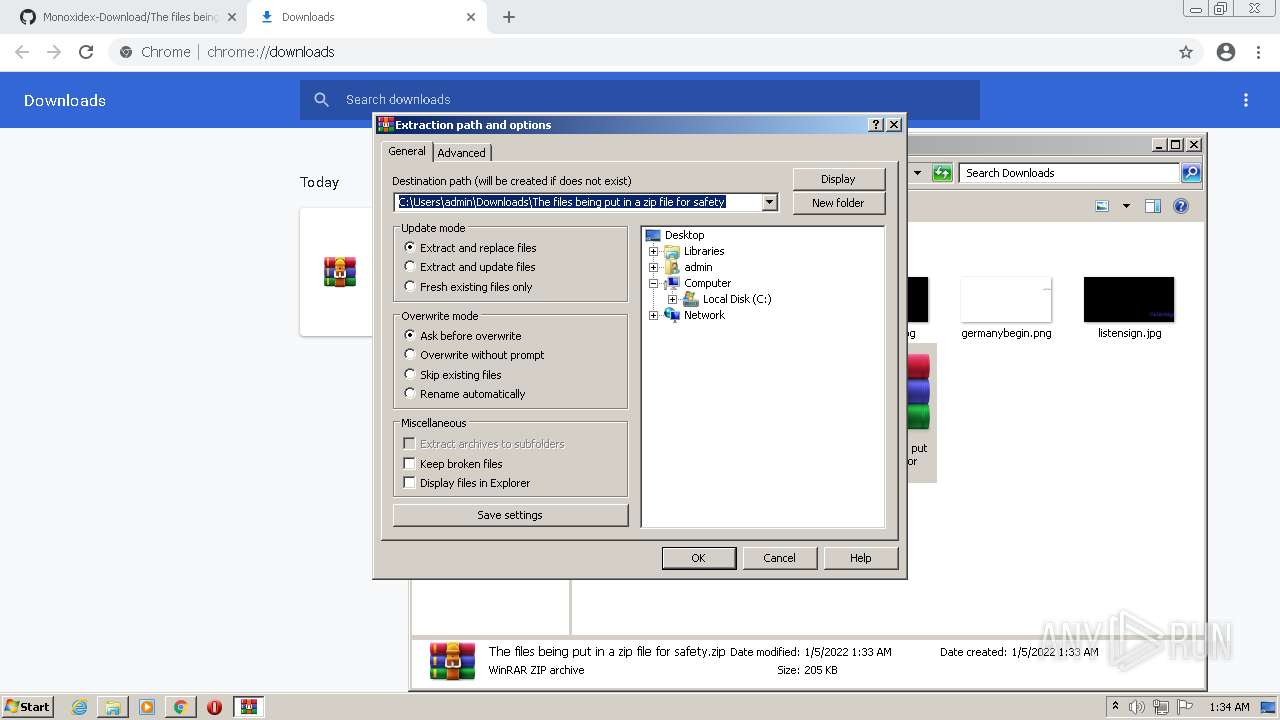
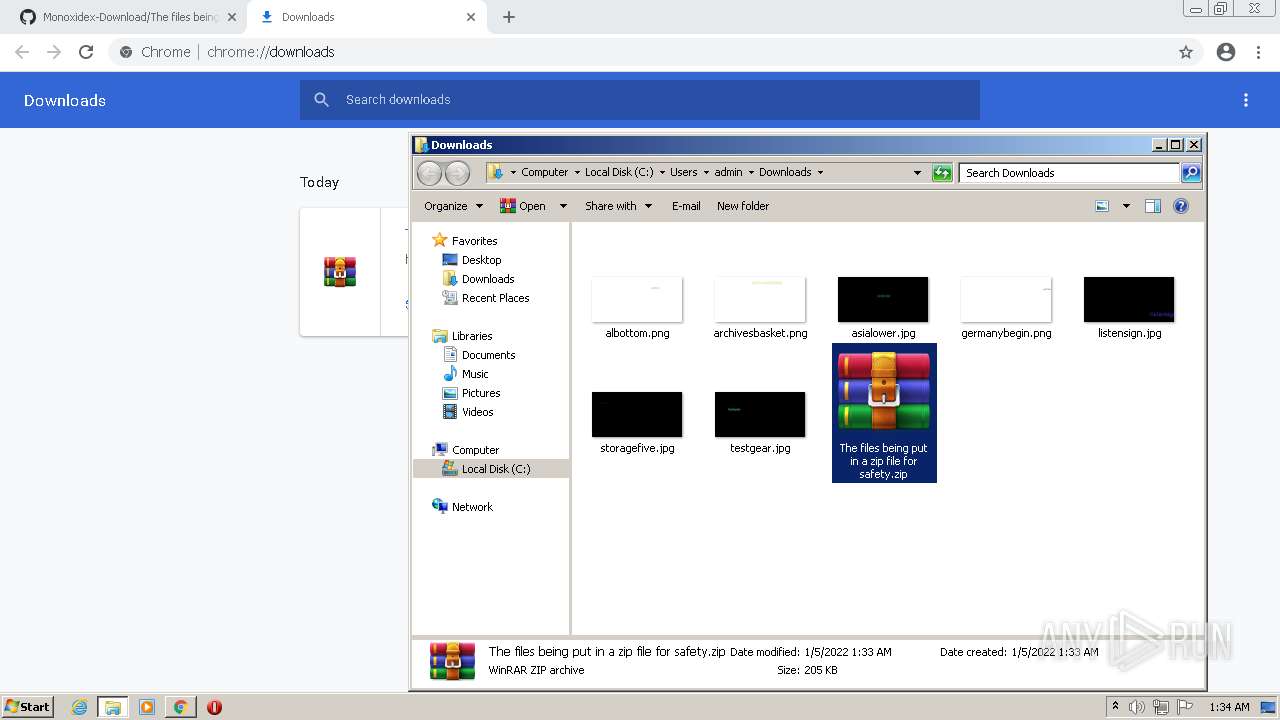
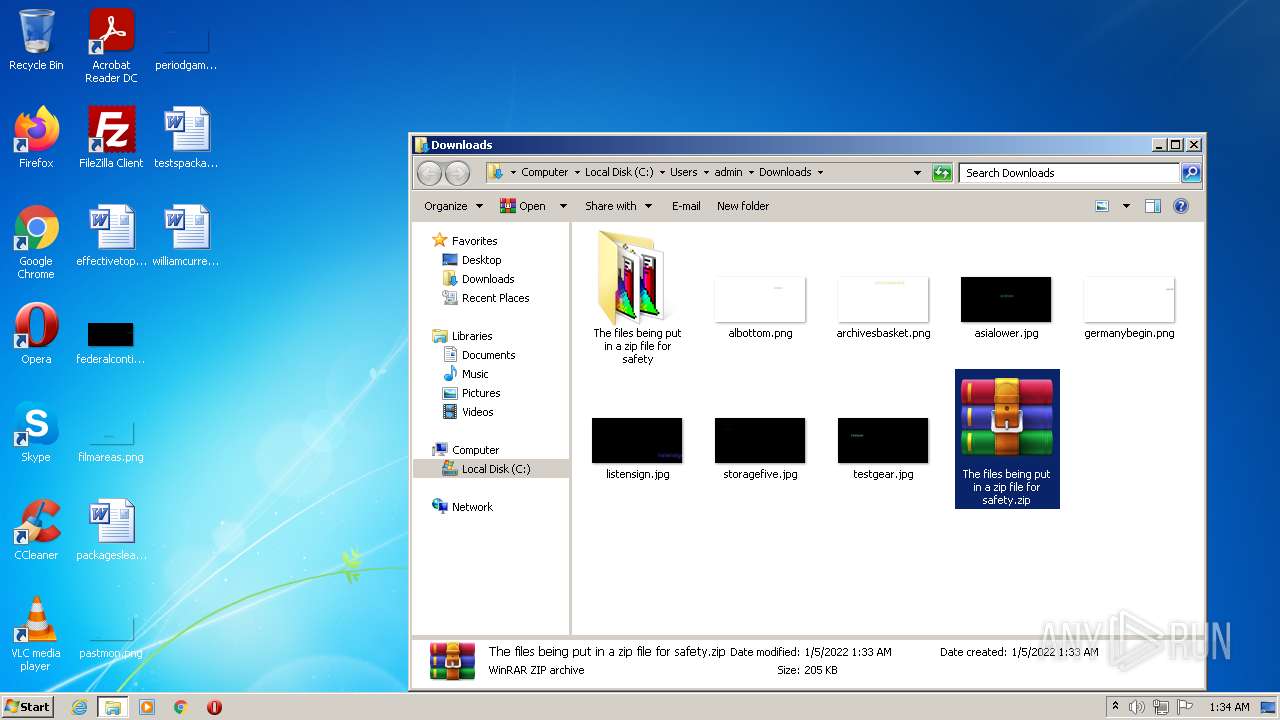
Manual execution by user
- Monoxidex86.exe (PID: 968)
- WinRAR.exe (PID: 3708)
- Monoxidex86.exe (PID: 868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
133
Monitored processes
91
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\MSOCache\All Users\{90140000-001A-0411-0000-0000000FF1CE}-C\Setup.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | ????????????????.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\MSOCache\All Users\{90140000-0016-040C-0000-0000000FF1CE}-C\ExcelMUI.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | ????????????????.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 576 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\MSOCache\All Users\{90140000-0017-0412-0000-0000000FF1CE}-C\SPDLR.cab" | C:\Program Files\WinRAR\WinRAR.exe | — | ????????????????.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1068,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource0\static\images\s_folder-hover_32.svg | C:\Program Files\Internet Explorer\iexplore.exe | — | ????????????????.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 824 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4116 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
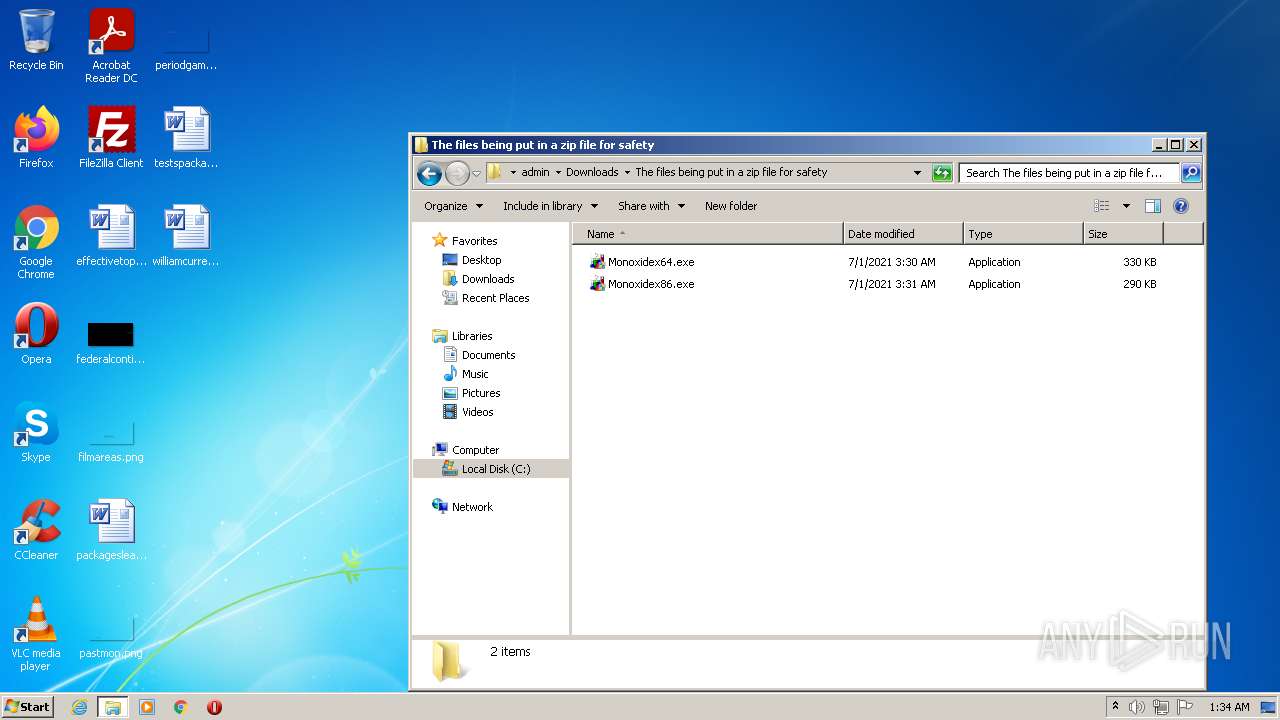
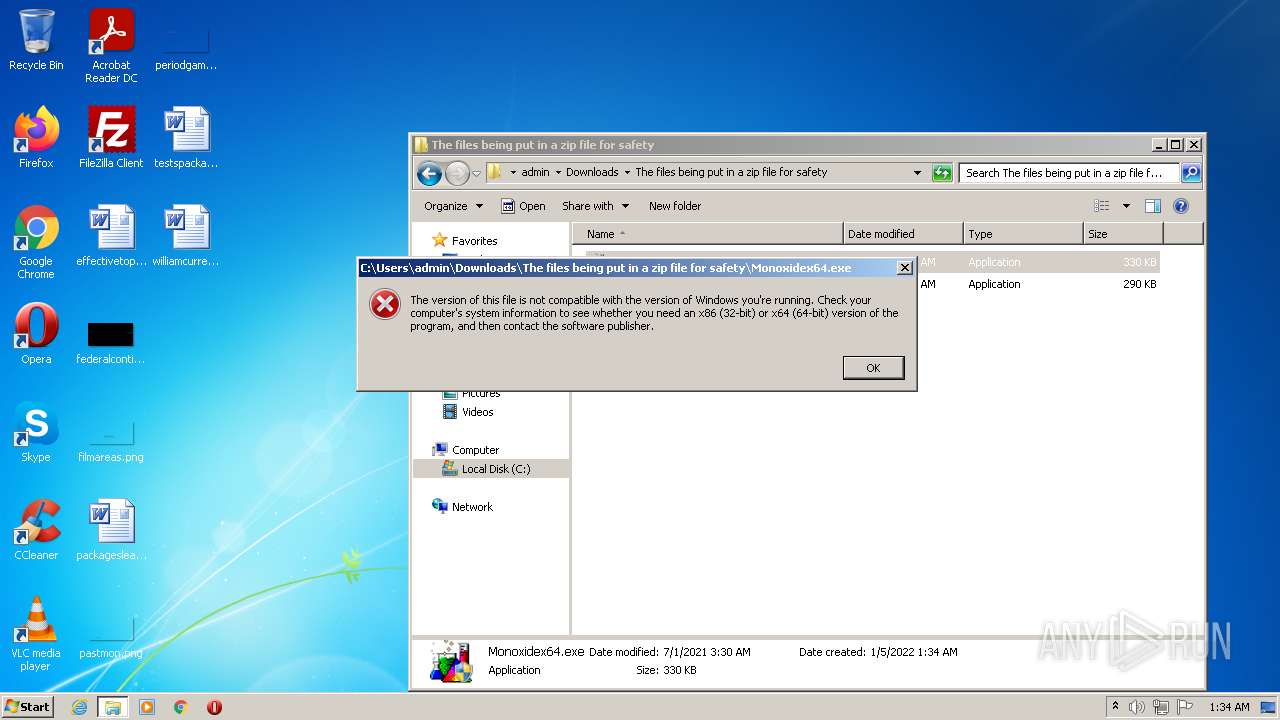
| 868 | "C:\Users\admin\Downloads\The files being put in a zip file for safety\Monoxidex86.exe" | C:\Users\admin\Downloads\The files being put in a zip file for safety\Monoxidex86.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 968 | "C:\Users\admin\Downloads\The files being put in a zip file for safety\Monoxidex86.exe" | C:\Users\admin\Downloads\The files being put in a zip file for safety\Monoxidex86.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\MSOCache\All Users\{90140000-00A1-0410-0000-0000000FF1CE}-C\OnoteLR.cab" | C:\Program Files\WinRAR\WinRAR.exe | — | ????????????????.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
32 889
Read events
32 480
Write events
409
Delete events
0
Modification events
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
18
Suspicious files
41
Text files
109
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61D4F56A-55C.pma | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5bedc9d6-ec16-420c-b18a-7d1f602185d6.tmp | text | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13e504.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ebb45fb-556a-43e4-9ef0-2ca153c55f92.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF13e62d.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13e504.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
138
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?25a830b55382a265 | unknown | compressed | 4.70 Kb | whitelisted |
— | — | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cbda7eee9a7d0ce6 | unknown | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2624 | chrome.exe | 142.250.186.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 142.250.186.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2624 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 142.250.184.234:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 142.250.185.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2624 | chrome.exe | 140.82.121.4:443 | github.com | — | US | malicious |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.youtube.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
github.com |
| malicious |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |