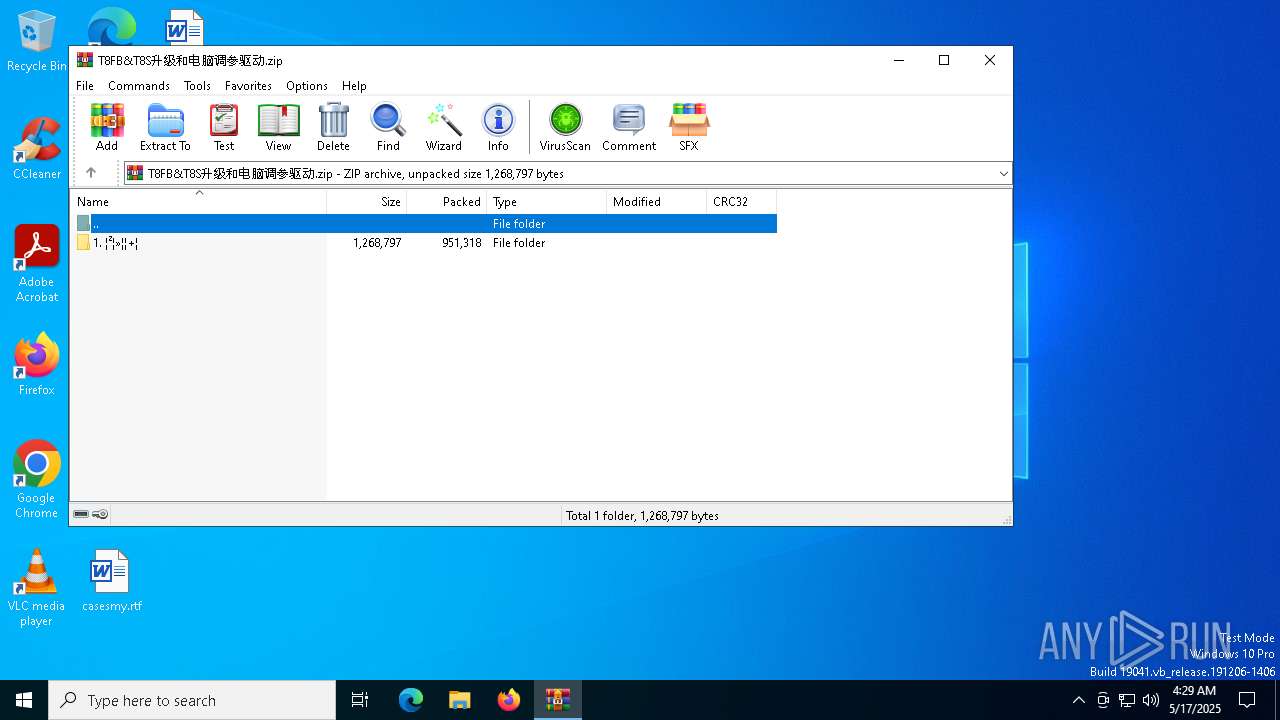
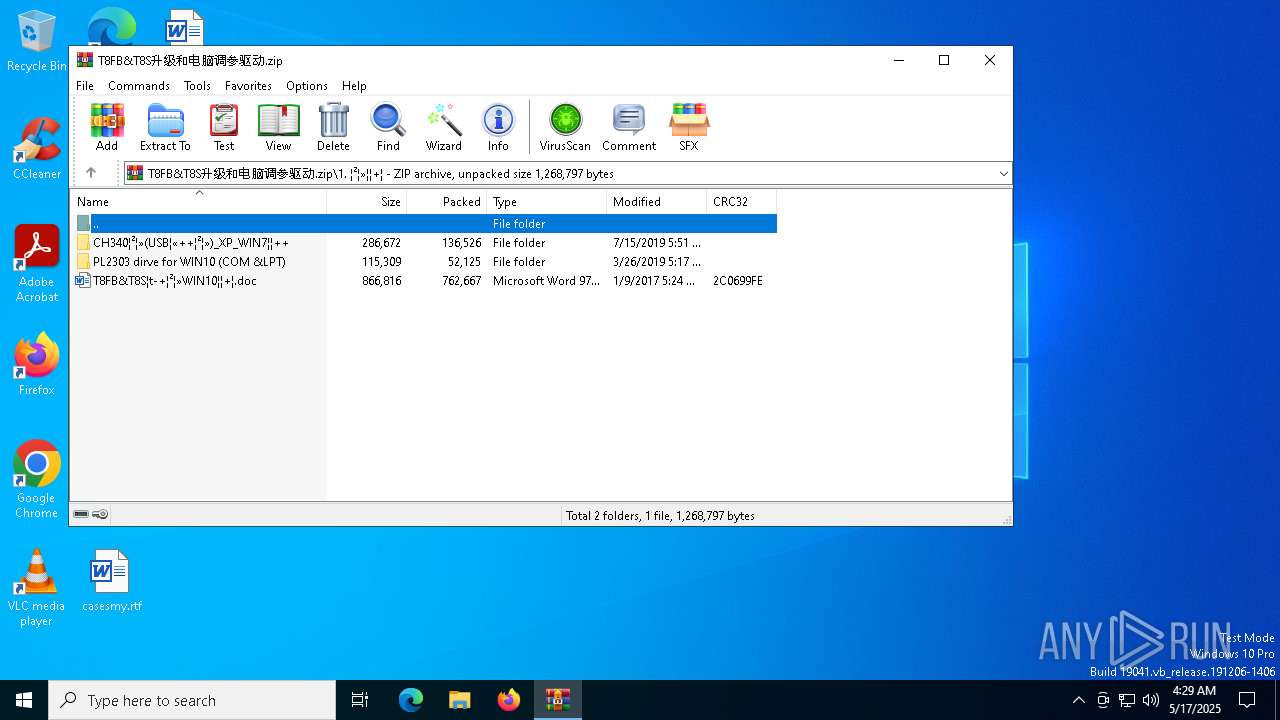
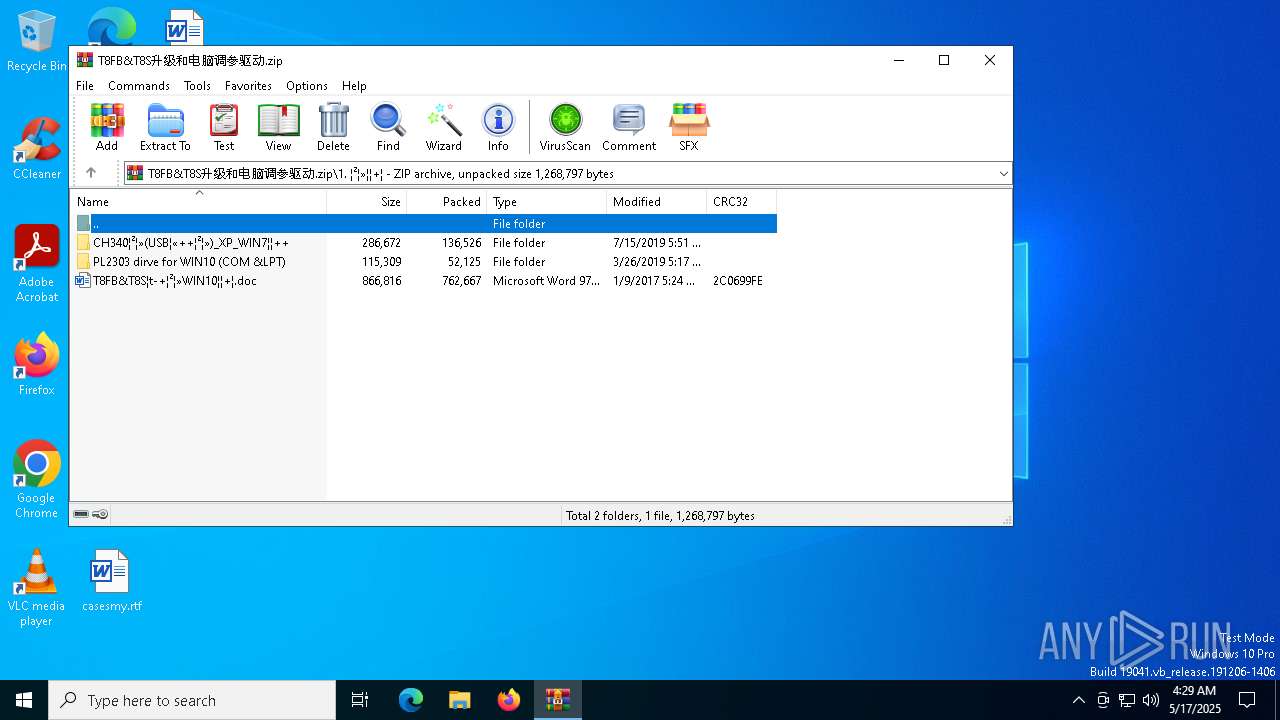
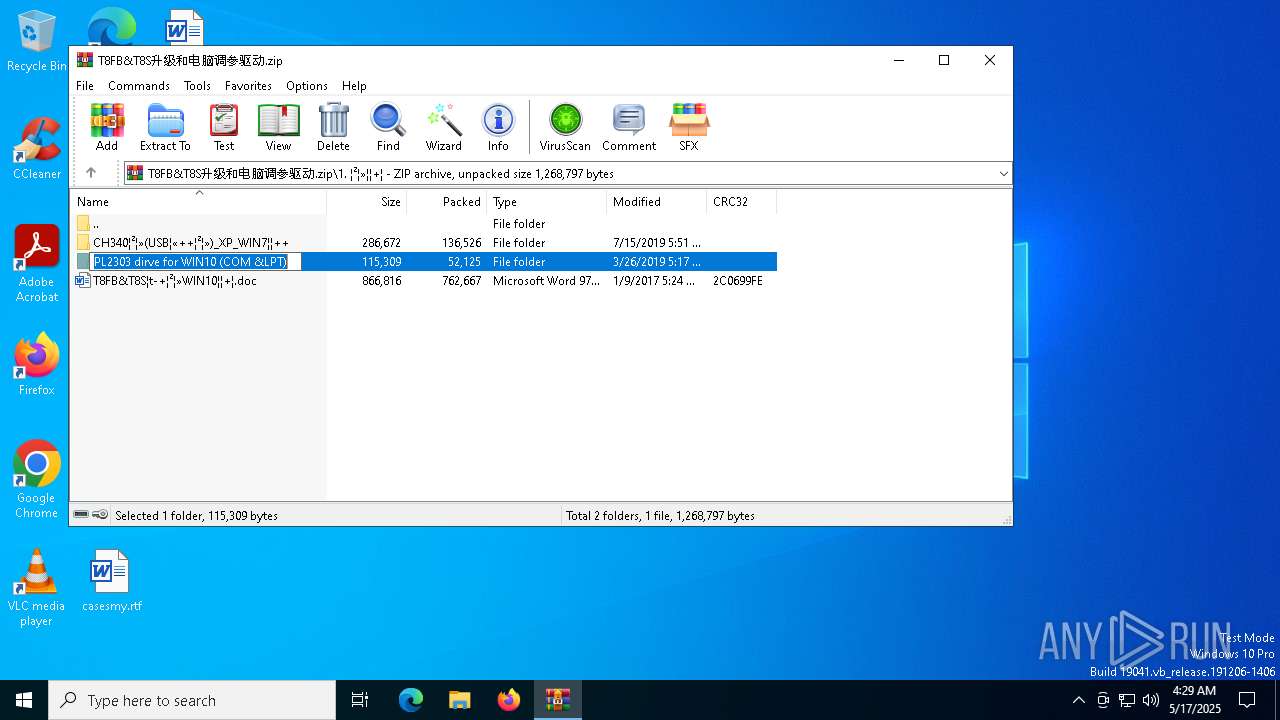
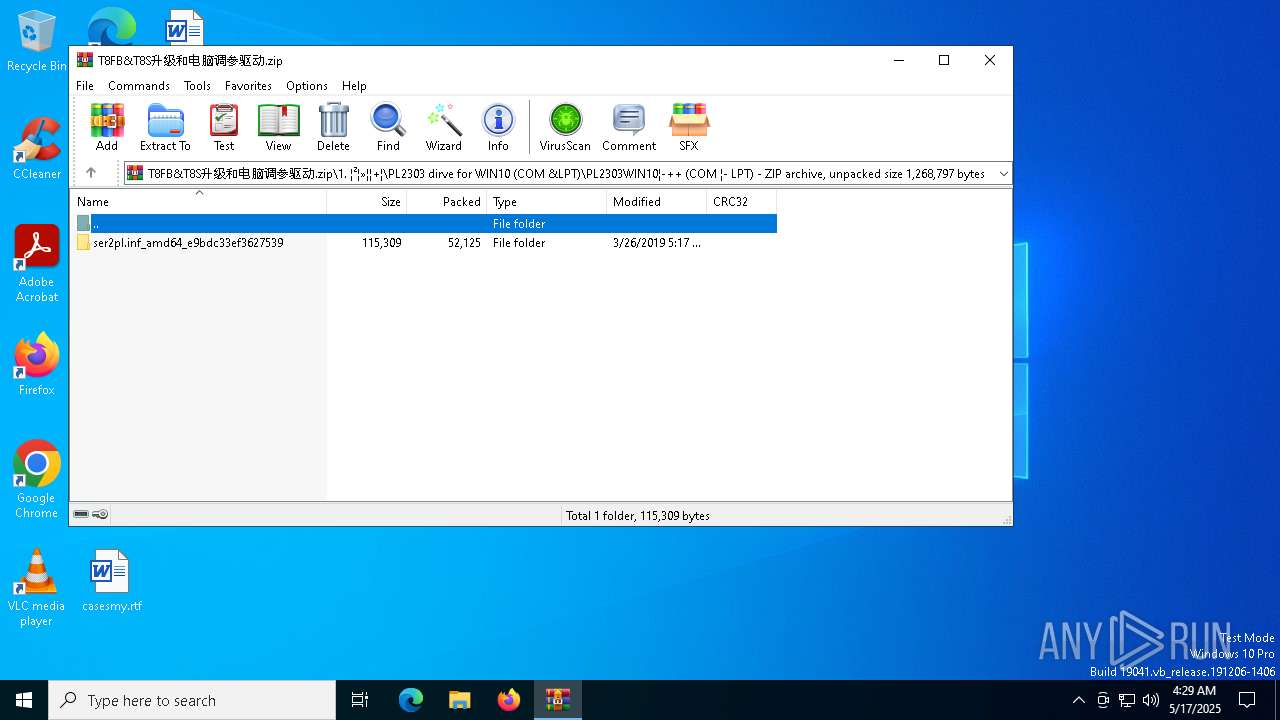
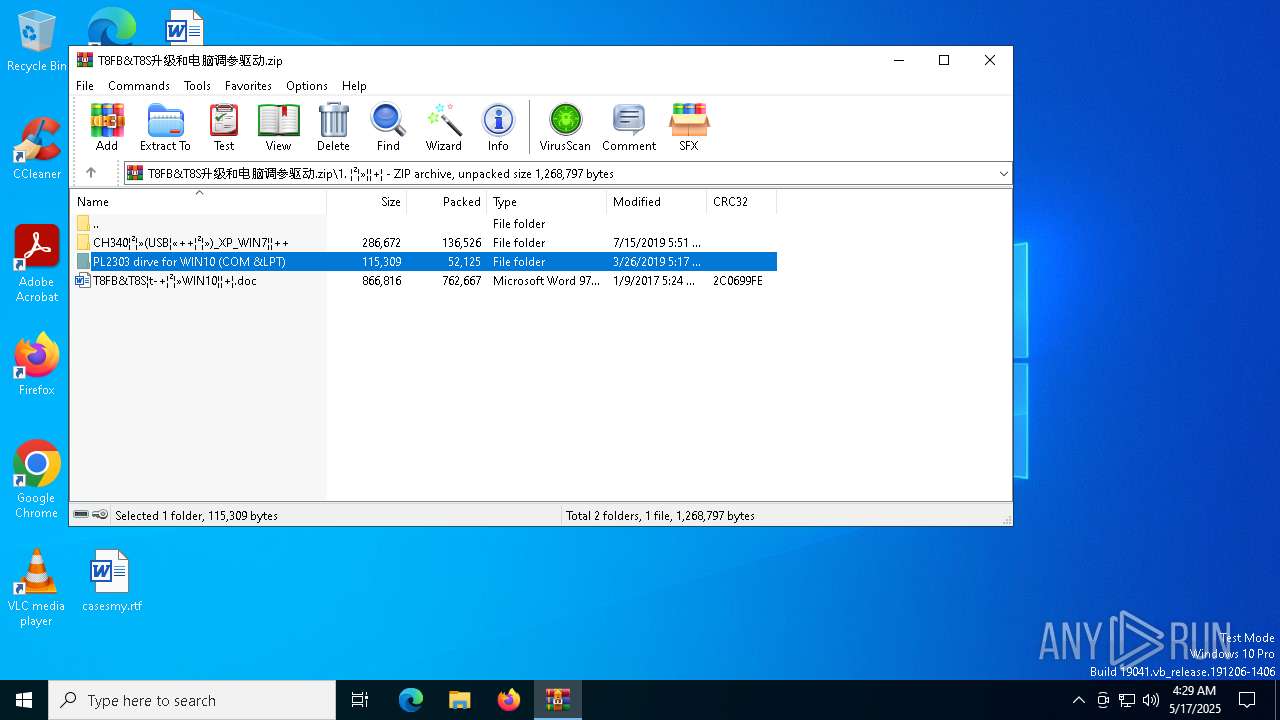
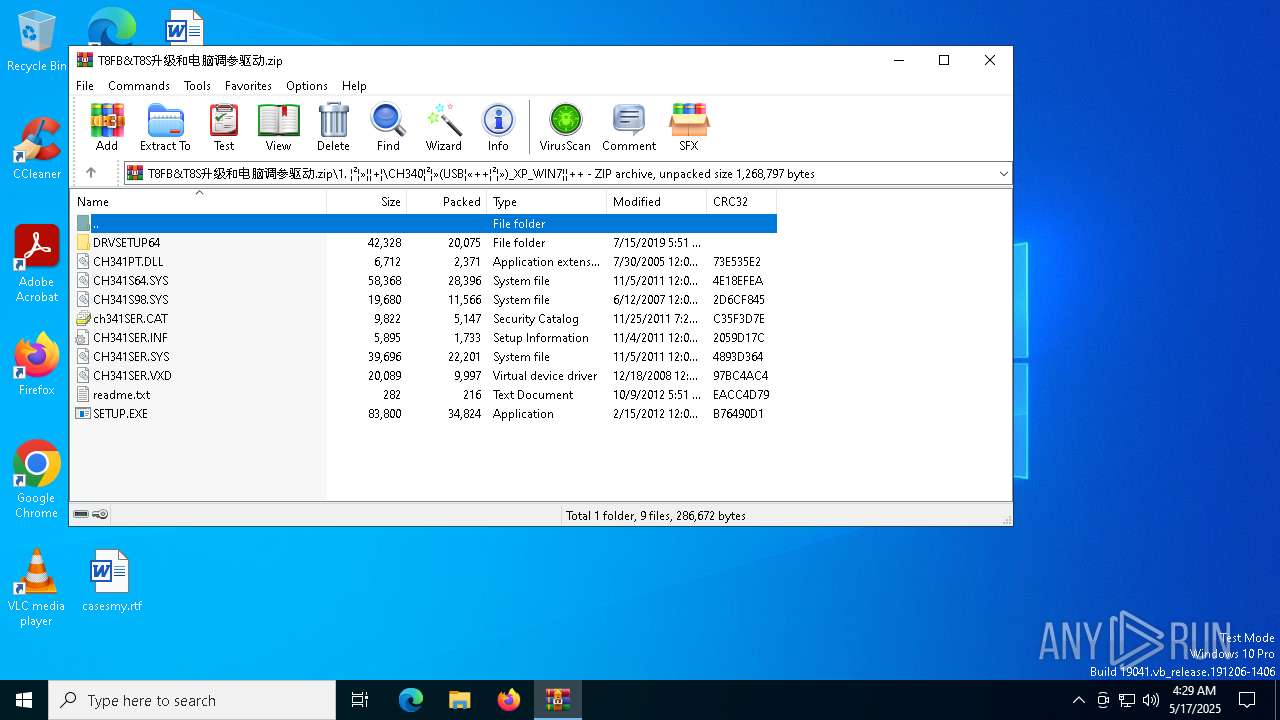
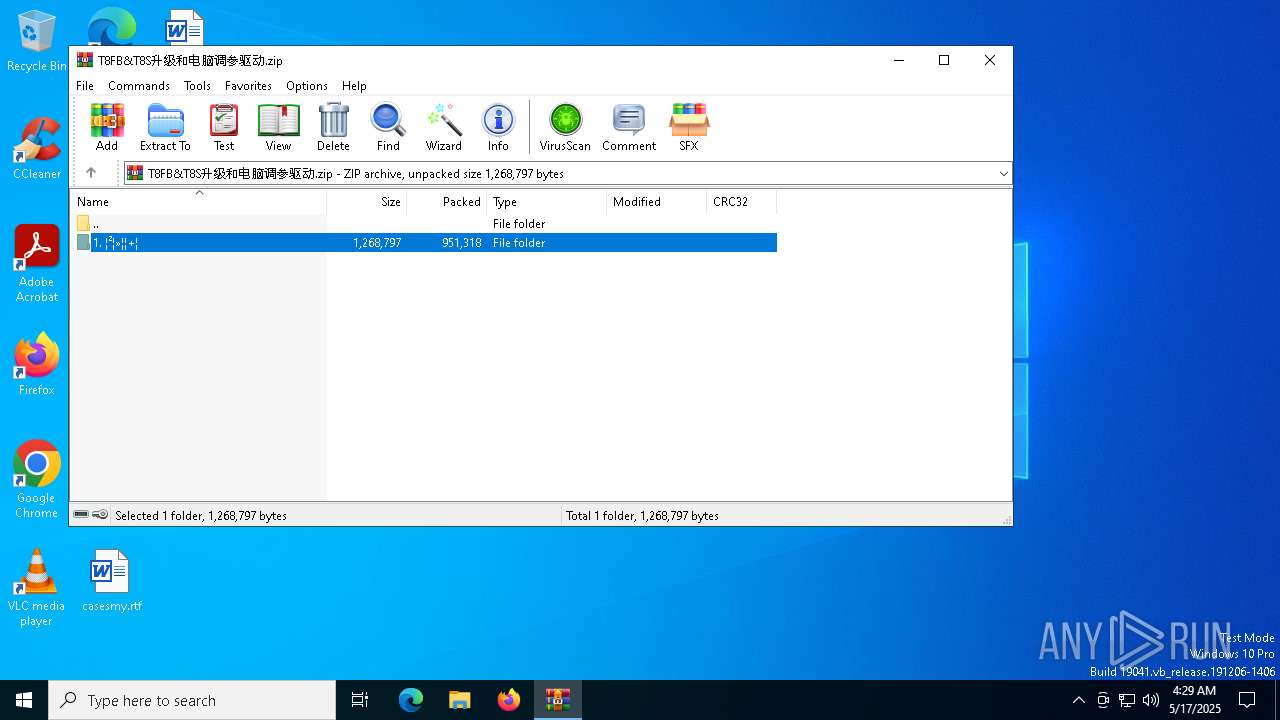
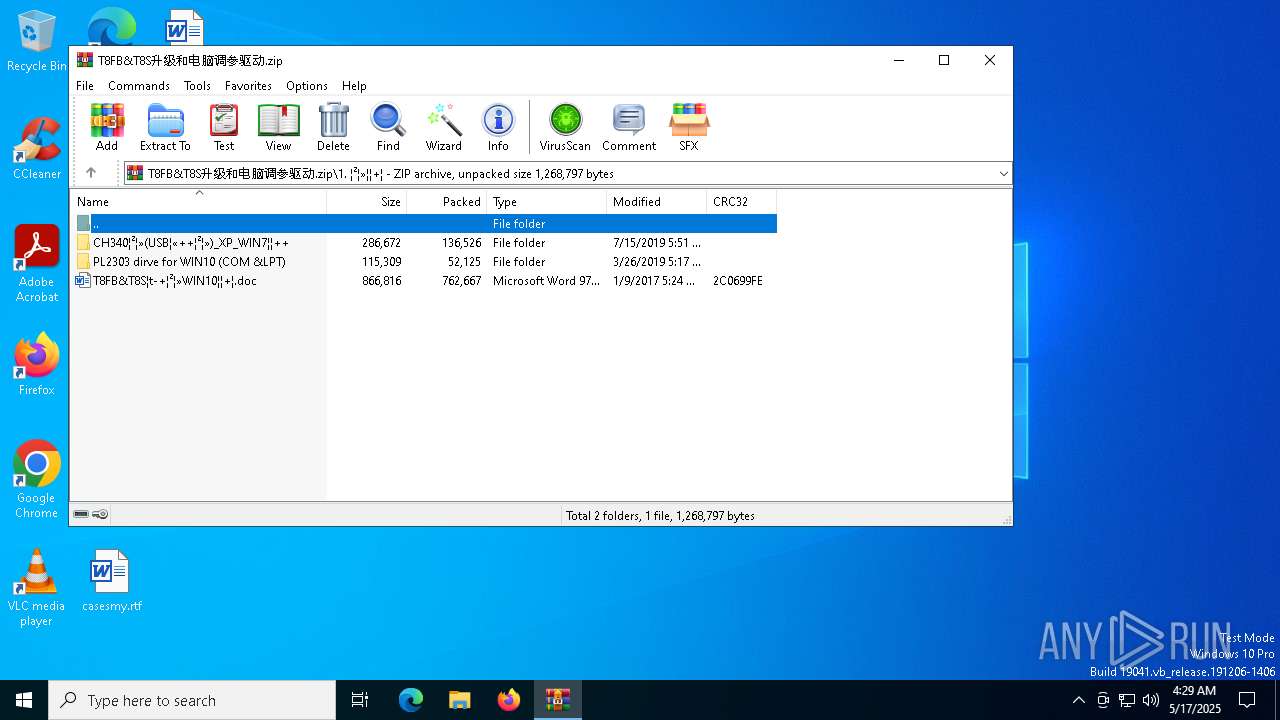
| File name: | T8FB&T8S升级和电脑调参驱动.zip |
| Full analysis: | https://app.any.run/tasks/c0280ba4-bebf-4db3-8cec-e6212f4e96da |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 04:28:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 78330910F44F1E7A2F252EEE6ADAA9C5 |
| SHA1: | 2051884446555C022CEDE35E8BB36F797FF15A48 |
| SHA256: | 661455C8E37E50D45CB8E52FEAE3ED1AF0DB079392BF409528AE4BD684160C60 |
| SSDEEP: | 49152:sn8iQ33gnX9Wpsc0VK73wtzewCdJJp3tvyXm0OvIK6ITFXwi4Kpx8iti6TOZk5CZ:Z1qXWp00baxCVHqXmvgITFXvZ0io6qZD |
MALICIOUS
Generic archive extractor
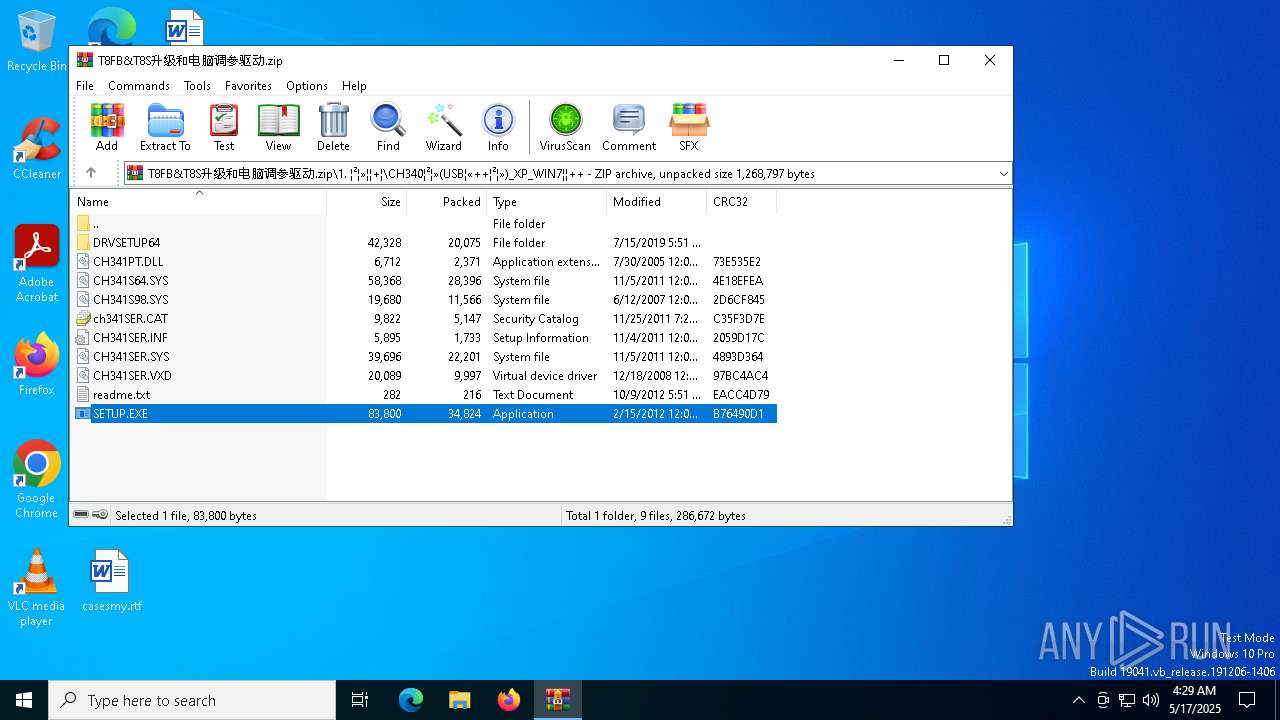
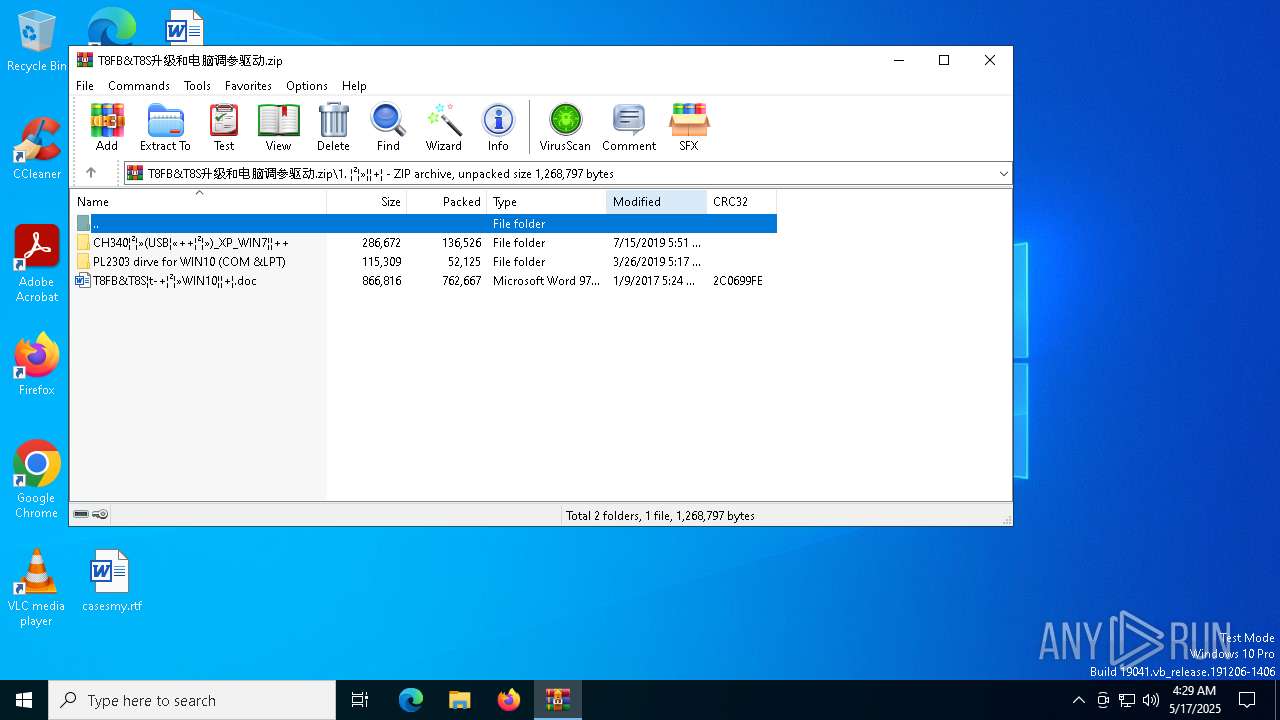
- WinRAR.exe (PID: 5116)
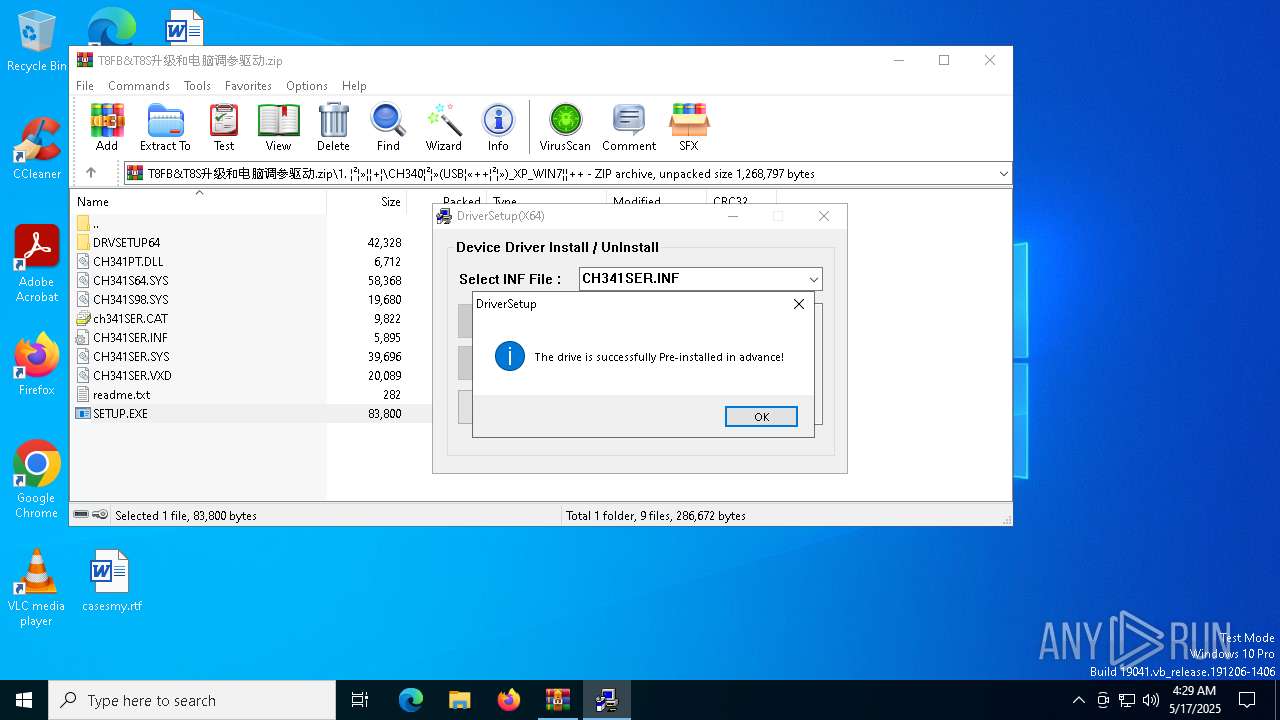
Executing a file with an untrusted certificate
- SETUP.EXE (PID: 4408)
- SETUP.EXE (PID: 6404)
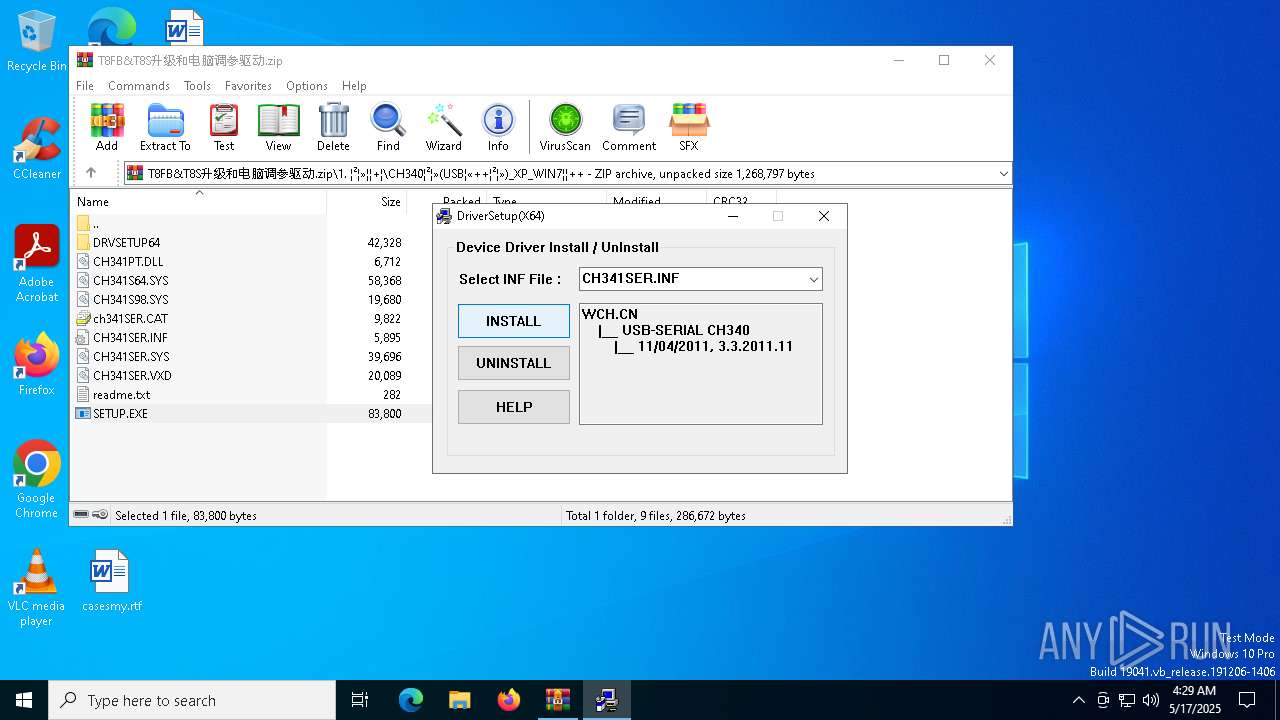
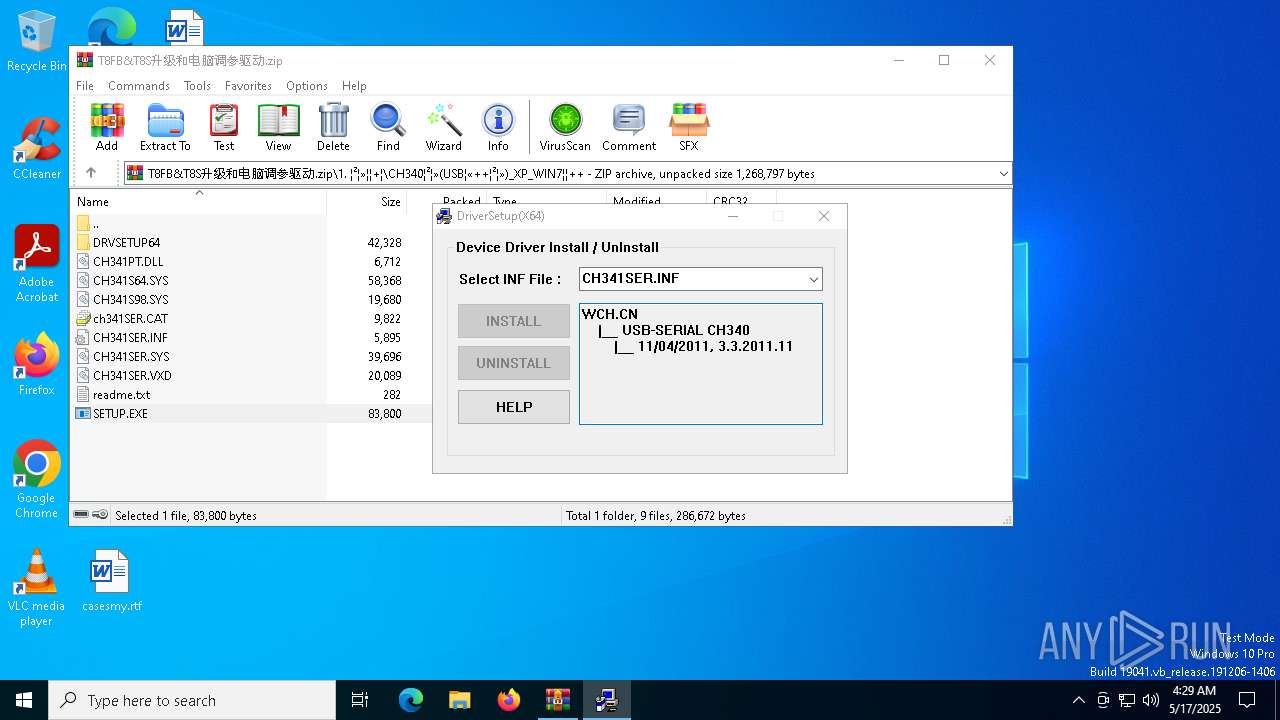
- DRVSETUP64.exe (PID: 1072)
SUSPICIOUS
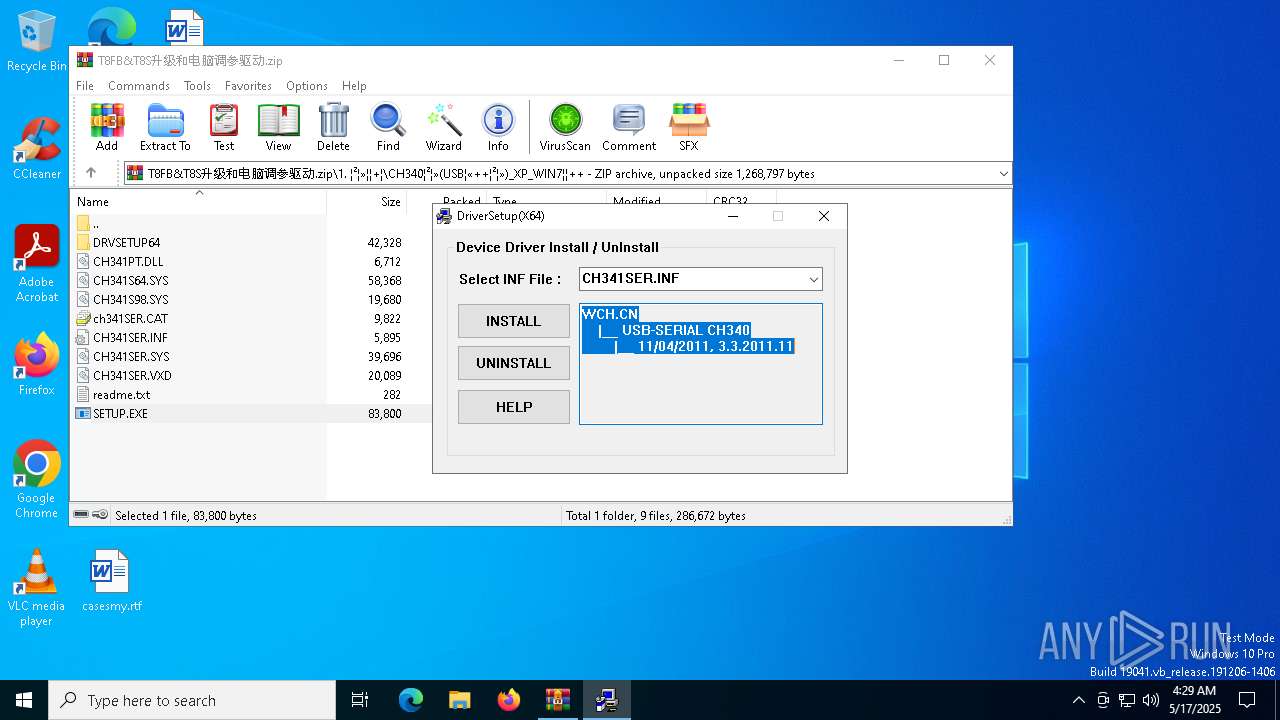
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 5116)
- drvinst.exe (PID: 5892)
- DRVSETUP64.exe (PID: 1072)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5116)
Executable content was dropped or overwritten
- DRVSETUP64.exe (PID: 1072)
- drvinst.exe (PID: 5892)
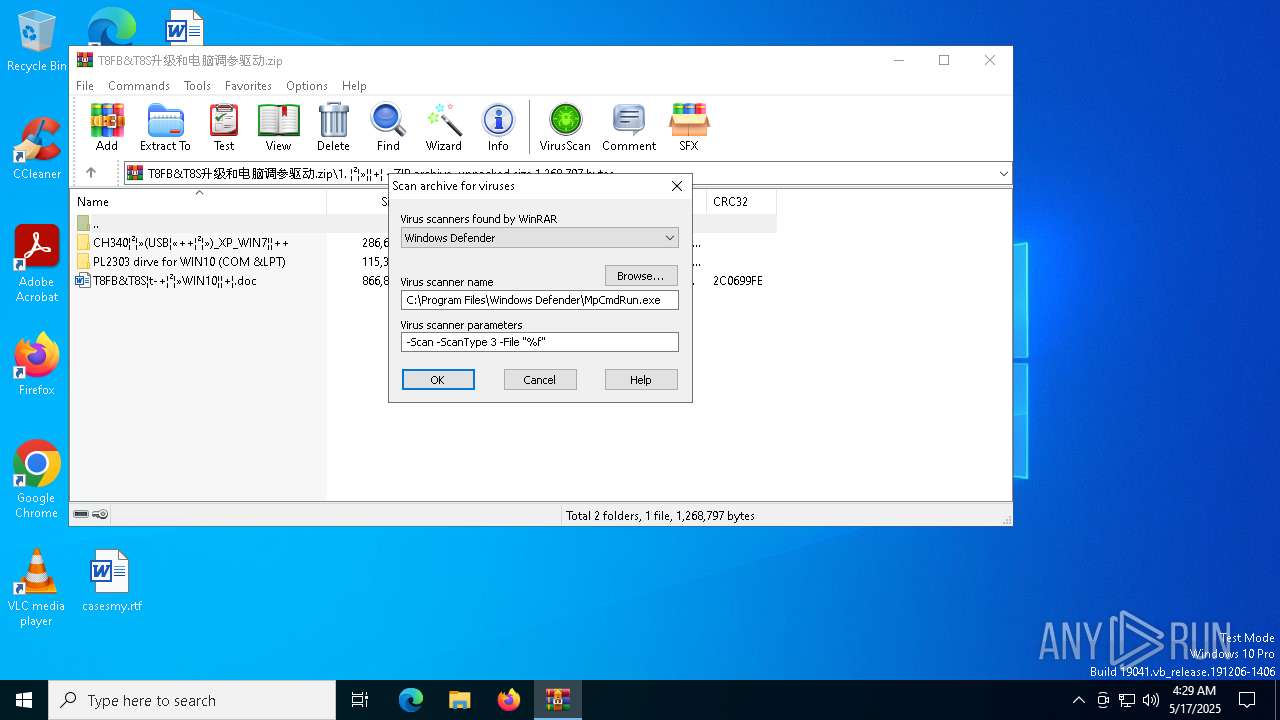
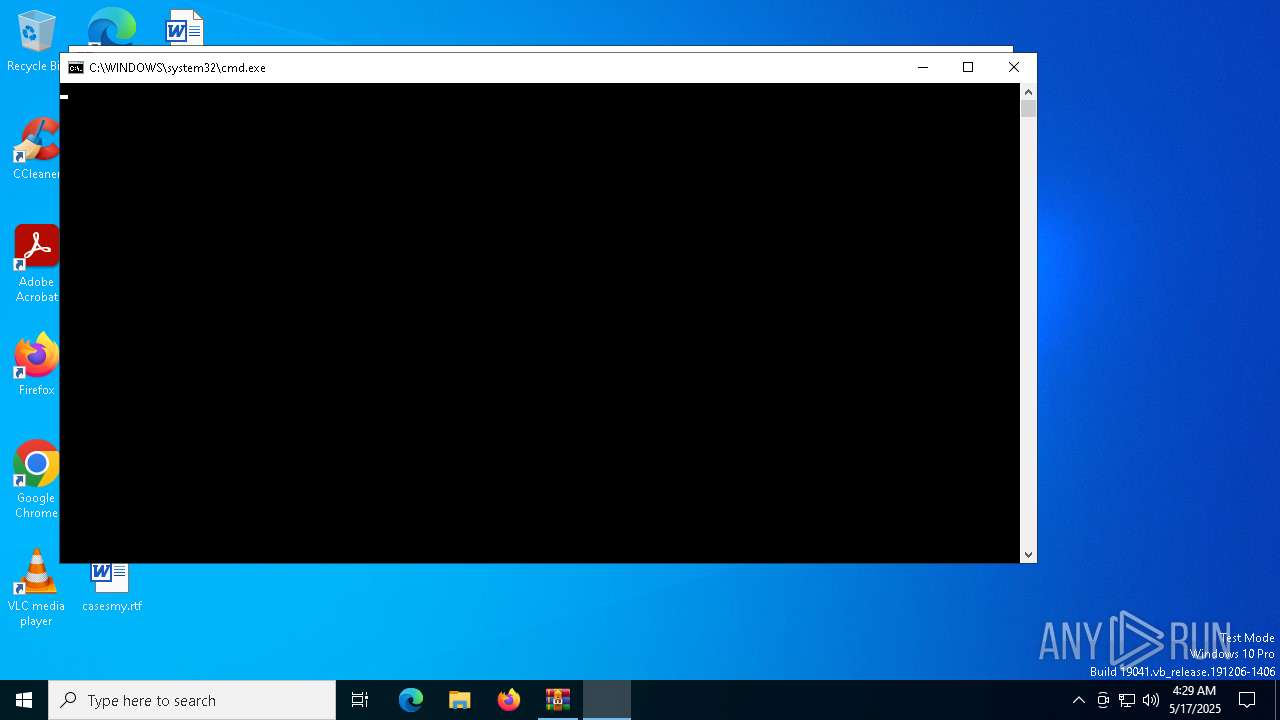
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 5116)
Creates files in the driver directory
- DRVSETUP64.exe (PID: 1072)
- drvinst.exe (PID: 5892)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 5116)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5116)
The sample compiled with chinese language support
- WinRAR.exe (PID: 5116)
The sample compiled with english language support
- WinRAR.exe (PID: 5116)
- DRVSETUP64.exe (PID: 1072)
- drvinst.exe (PID: 5892)
Checks supported languages
- DRVSETUP64.exe (PID: 1072)
- SETUP.EXE (PID: 6404)
- drvinst.exe (PID: 5892)
- MpCmdRun.exe (PID: 3300)
Reads the computer name
- DRVSETUP64.exe (PID: 1072)
- MpCmdRun.exe (PID: 3300)
- drvinst.exe (PID: 5892)
Create files in a temporary directory
- DRVSETUP64.exe (PID: 1072)
- MpCmdRun.exe (PID: 3300)
Reads the machine GUID from the registry
- drvinst.exe (PID: 5892)
Reads the software policy settings
- drvinst.exe (PID: 5892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
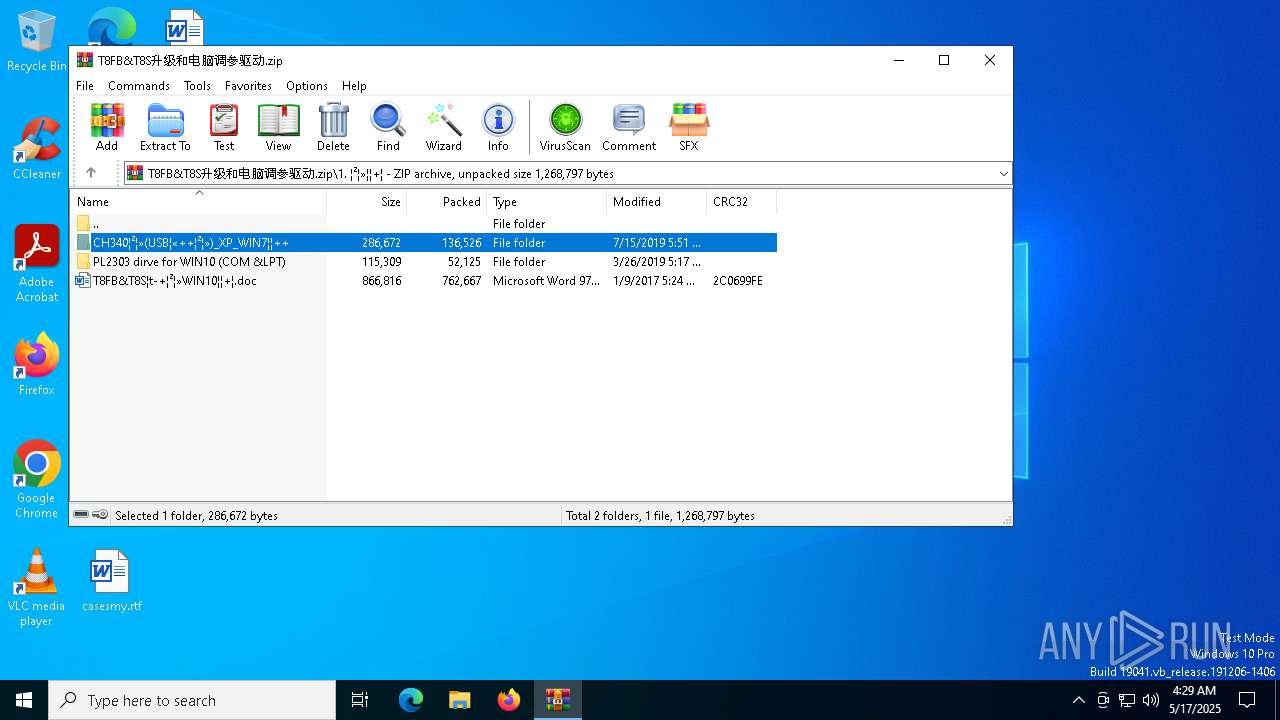
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:07:15 17:51:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
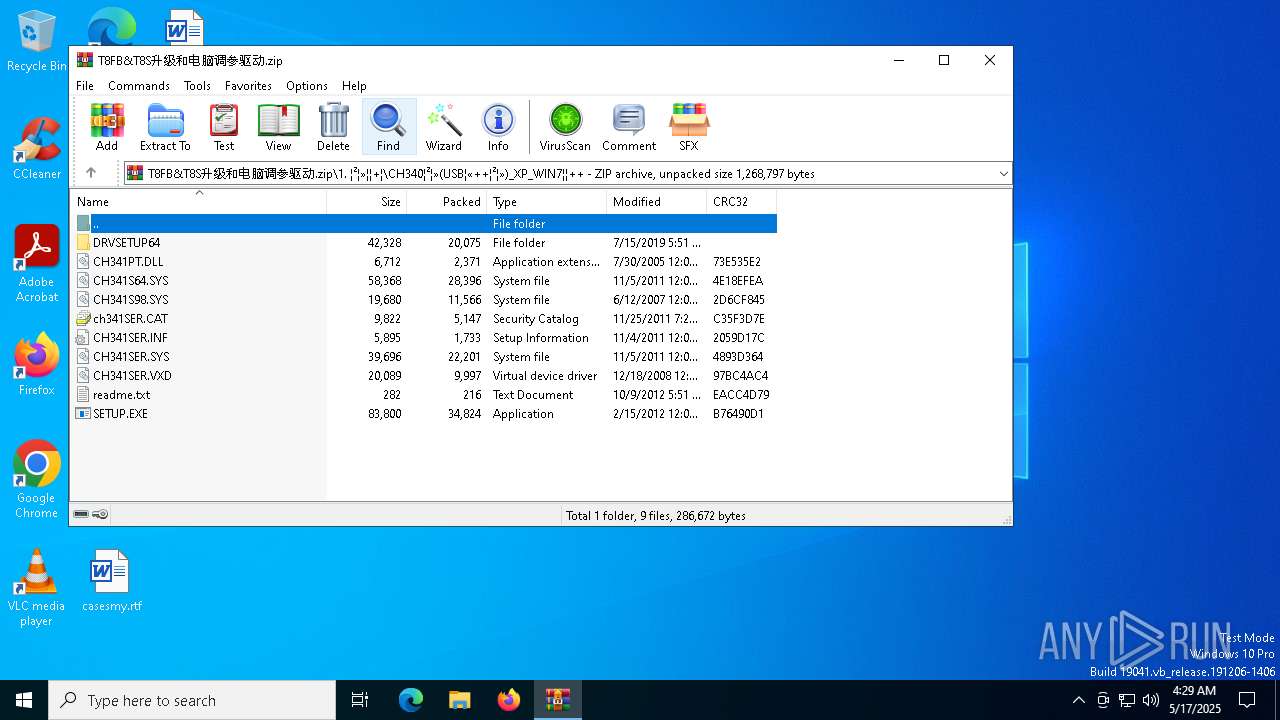
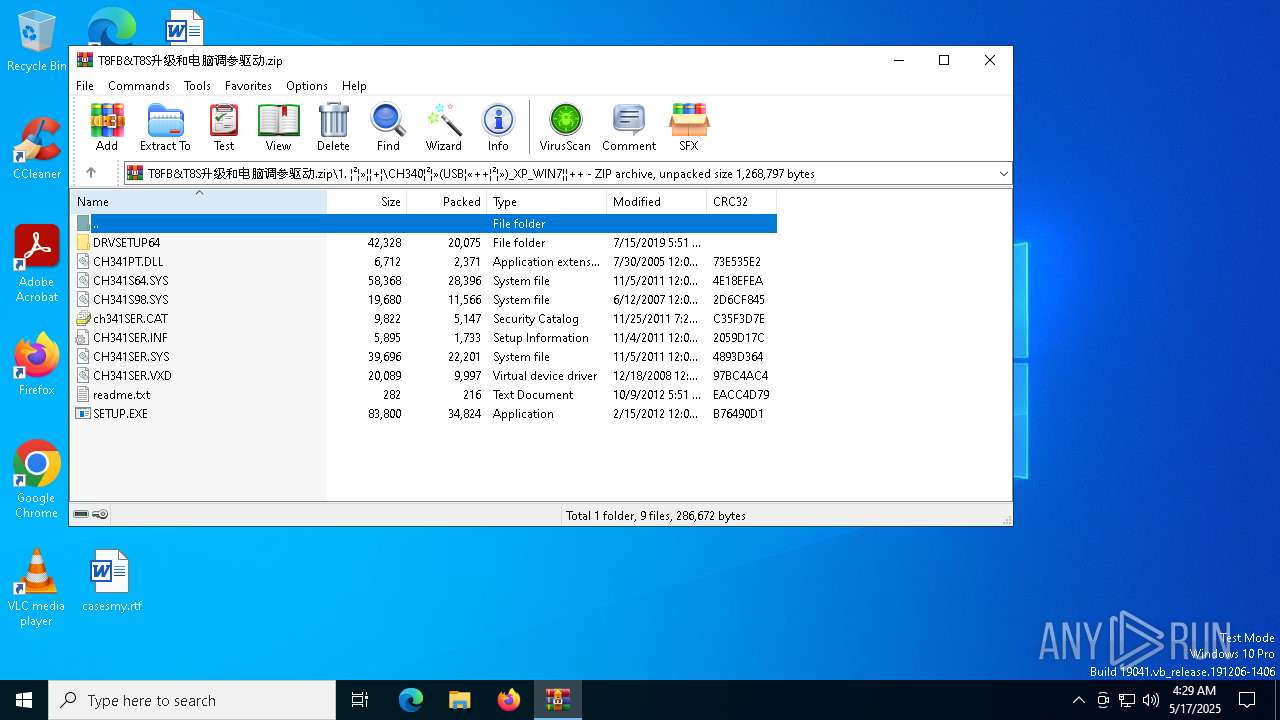
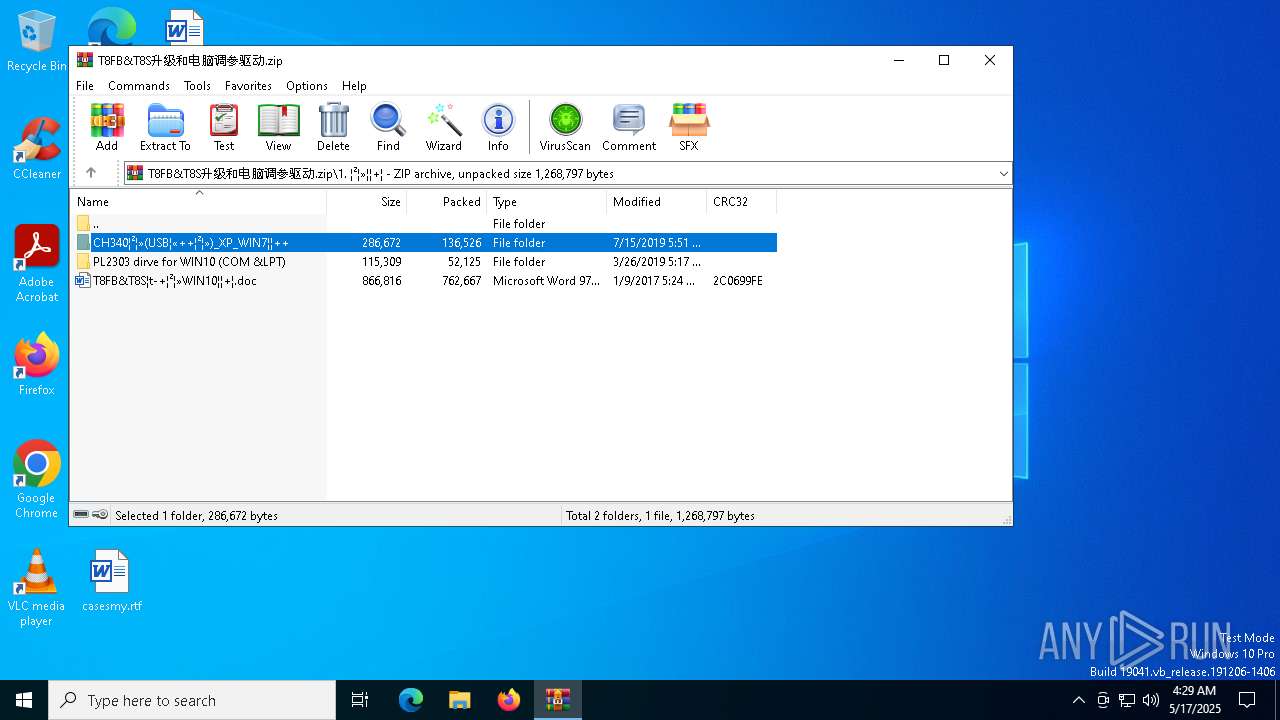
| ZipFileName: | 1. ??????װ/CH340????(USB????????)_XP_WIN7????/ |
Total processes
139
Monitored processes
10
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
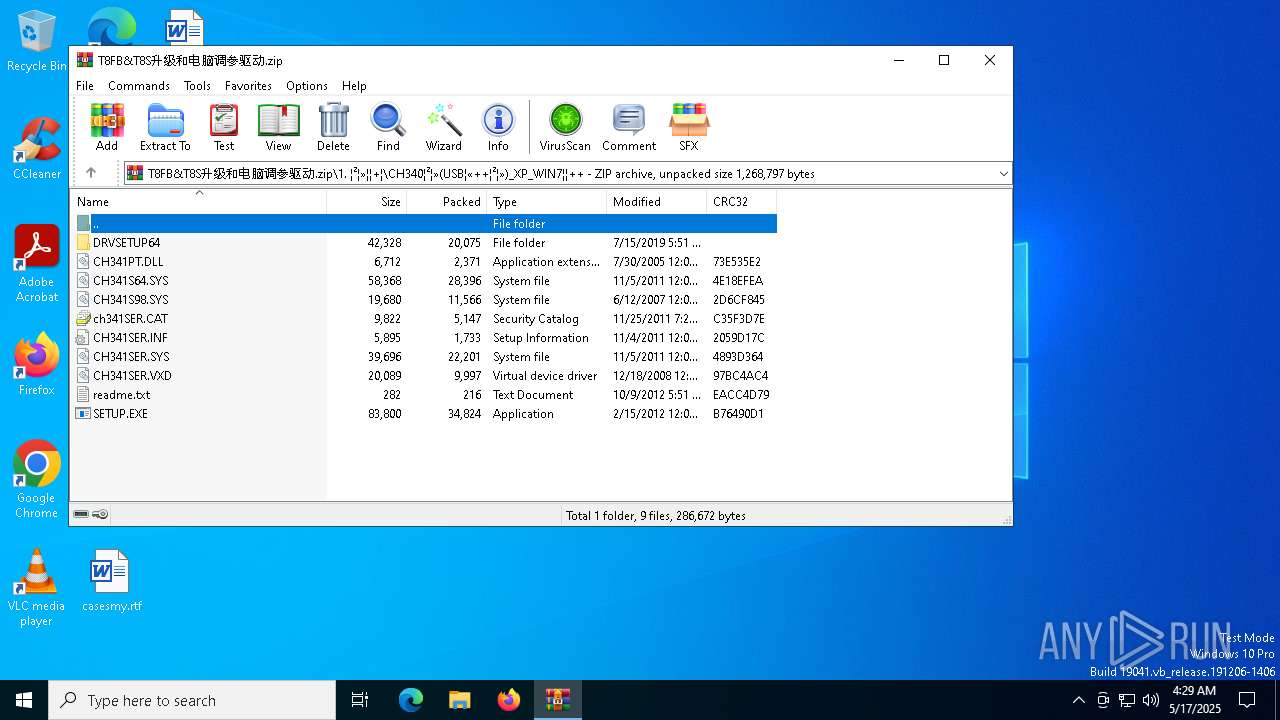
| 1072 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\DRVSETUP64\DRVSETUP64.EXE" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\DRVSETUP64\DRVSETUP64.exe | SETUP.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: EXE For Driver Installation Exit code: 1 Version: 1, 6, 0, 0 Modules
| |||||||||||||||
| 3300 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR5116.622" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\SETUP.EXE" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\SETUP.EXE | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: EXE For Driver Installation Exit code: 3221226540 Version: 1, 6, 0, 0 Modules
| |||||||||||||||
| 5116 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\T8FB&T8S升级和电脑调参驱动.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5164 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5228 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR5116.622\Rar$Scan51790.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{258f0c6b-3b49-5b41-9620-d29e3d2ad1f0}\CH341SER.INF" "9" "4e9cc54c7" "00000000000001D0" "WinSta0\Default" "00000000000001EC" "208" "C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\SETUP.EXE" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\SETUP.EXE | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: EXE For Driver Installation Exit code: 0 Version: 1, 6, 0, 0 Modules
| |||||||||||||||
Total events
8 335
Read events
8 325
Write events
10
Delete events
0
Modification events
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\T8FB&T8S升级和电脑调参驱动.zip | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1072) DRVSETUP64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (5116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
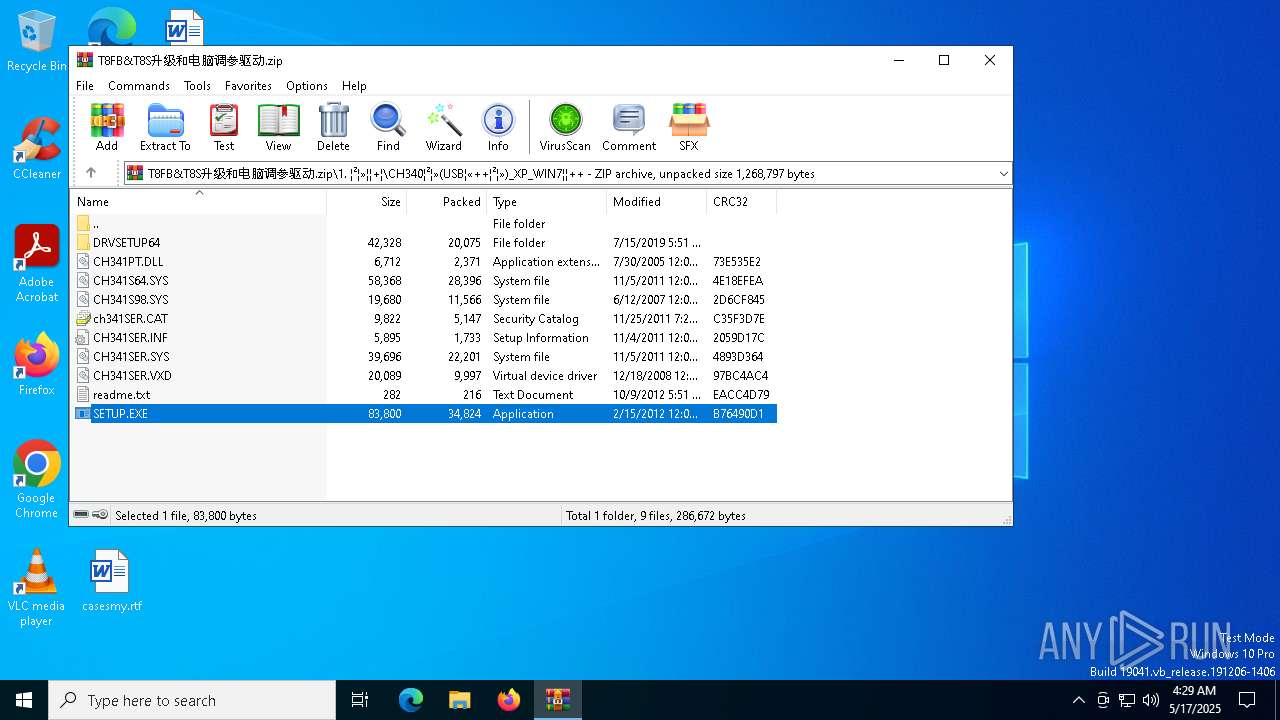
Executable files
49
Suspicious files
22
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\CH341PT.DLL | executable | |
MD5:69B6FEC924C30042D329AE56CA8925CC | SHA256:45494CE819C1B5C21ABB72DC47A0CA36807E0ED74CE55B631DA174C77A9B24DB | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\ch341SER.CAT | binary | |
MD5:1F7FE778164D85076E97B10363661CFB | SHA256:18FAB08BA0A79CC57B7A0CE8724CD17E0724B3E0A51BDBA364AE9C236D02DDDC | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\CH341SER.VXD | executable | |
MD5:BE7438420F1DA854917F58CAD557476D | SHA256:2A946F316EDD7E1185DEEAFDC2DE52B2D2843198BE098A724233C12F9CCD0DAE | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\DRVSETUP64\DRVSETUP64.exe | executable | |
MD5:6DCD5BC85A93D86C24F03942541A5678 | SHA256:552E57F3100BBF78BDA39CCE9E9CF0E3016551A9197C0757A9746E7A08E71ABA | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\CH341S98.SYS | executable | |
MD5:B6F4A83911336E84BEAD8F8905285FAB | SHA256:0ECD1222627271EA31D3B64796992B6DAF5133D64CC26D43B3873CBE32FD59CB | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\readme.txt | text | |
MD5:AB3EFFEC63DB736A6F68714DA0A97748 | SHA256:A66EFEB1AB68D09BC37DB31027EA1FE73BF02C5A11018B0D5F3F448B2F538388 | |||
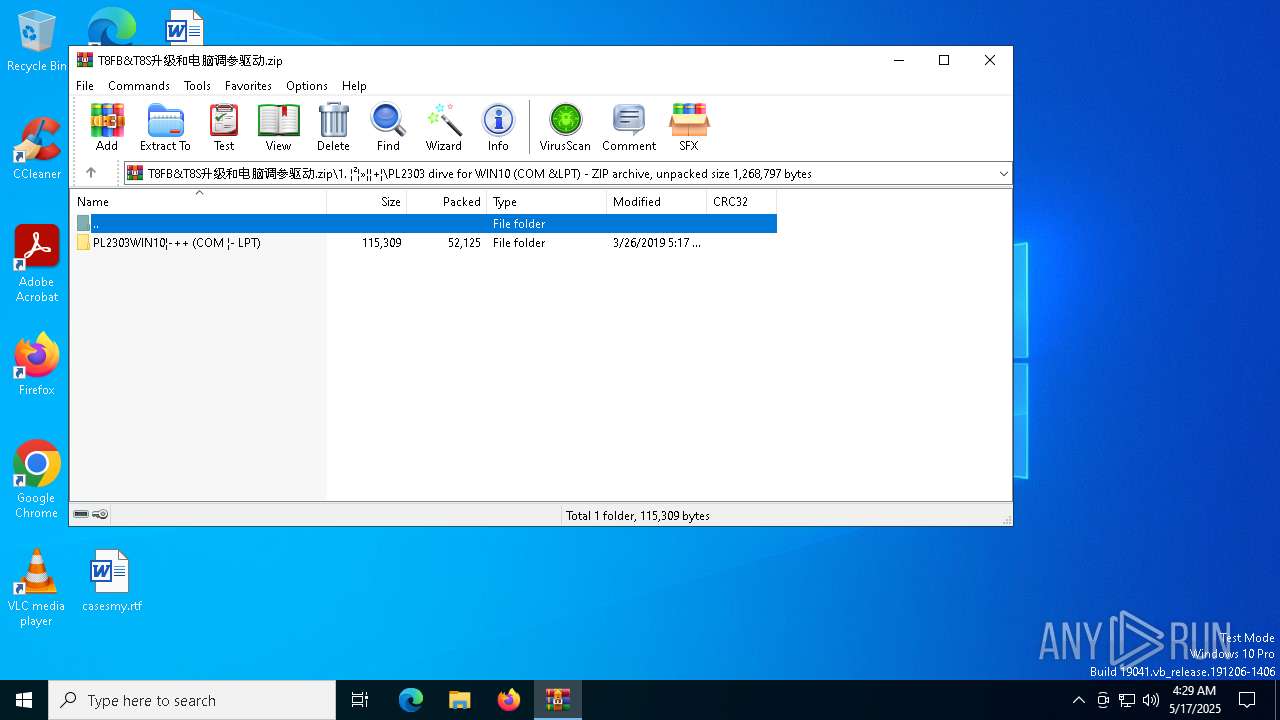
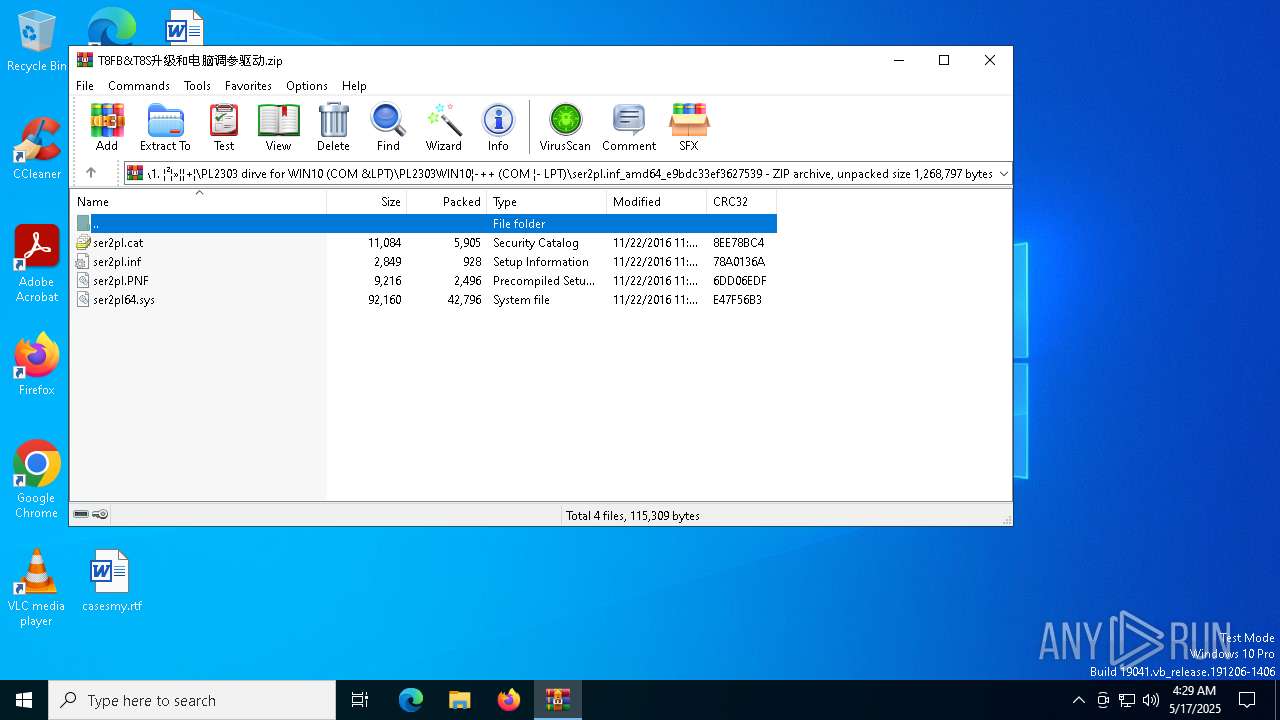
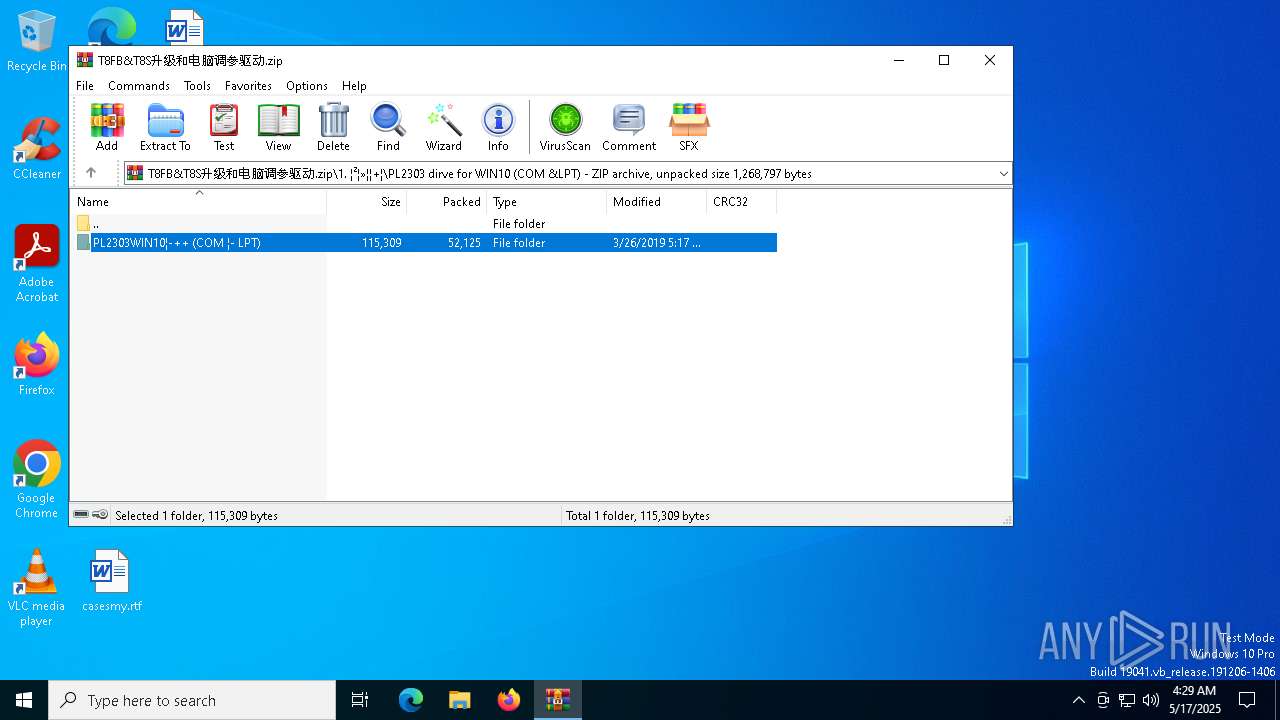
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\PL2303 dirve for WIN10 (COM &LPT)\PL2303WIN10¦-++ (COM ¦- LPT)\ser2pl.inf_amd64_e9bdc33ef3627539\ser2pl64.sys | executable | |
MD5:C284622531B1238E41DF70E84B7524CE | SHA256:EF7A48E0C14BA5305656B388D37D71B483FA94269D5E96D03CA5996B2D50A369 | |||
| 1072 | DRVSETUP64.exe | C:\Windows\INF\setupapi.dev.log | text | |
MD5:49124C259C947DC04C2AC7E2C0910275 | SHA256:405F3125A073ED08C44B9F9FFFBFF25954AD7E4E7DFB2198E3D4EC73118D1FB6 | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\CH340¦²¦»(USB¦«++¦²¦»)_XP_WIN7¦¦++\CH341S64.SYS | executable | |
MD5:C58EC27035731337ADD1326880086B16 | SHA256:1A48A57D7FF5332AD380AF7884F516548DB535CFE23F3AE7D5AF291307CBC435 | |||
| 5116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5116.48086\1. ¦²¦»¦¦+¦\PL2303 dirve for WIN10 (COM &LPT)\PL2303WIN10¦-++ (COM ¦- LPT)\ser2pl.inf_amd64_e9bdc33ef3627539\ser2pl.PNF | binary | |
MD5:CFFC986C24F3B5B69FAEB51424887BC9 | SHA256:511536245FC4D9DE1A8752A8119F141DF0DC05AAD20267DB2AB4AE09C1CEEBE1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |