| File name: | dControl.exe |
| Full analysis: | https://app.any.run/tasks/ac1256fd-2b2f-44c1-b514-31cfb5c5467d |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2021, 01:21:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0A50081A6CD37AEA0945C91DE91C5D97 |
| SHA1: | 755309C6D9FA4CD13B6C867CDE01CC1E0D415D00 |
| SHA256: | 6606D759667FBDFAA46241DB7FFB4839D2C47B88A20120446F41E916CAD77D0B |
| SSDEEP: | 12288:baWzgMg7v3qnCiOErQohh0F49CJ8lnyzQpJ2KNP3A8wnqqF:uaHMv6Carj1nyzQpJ2KNPw/ |
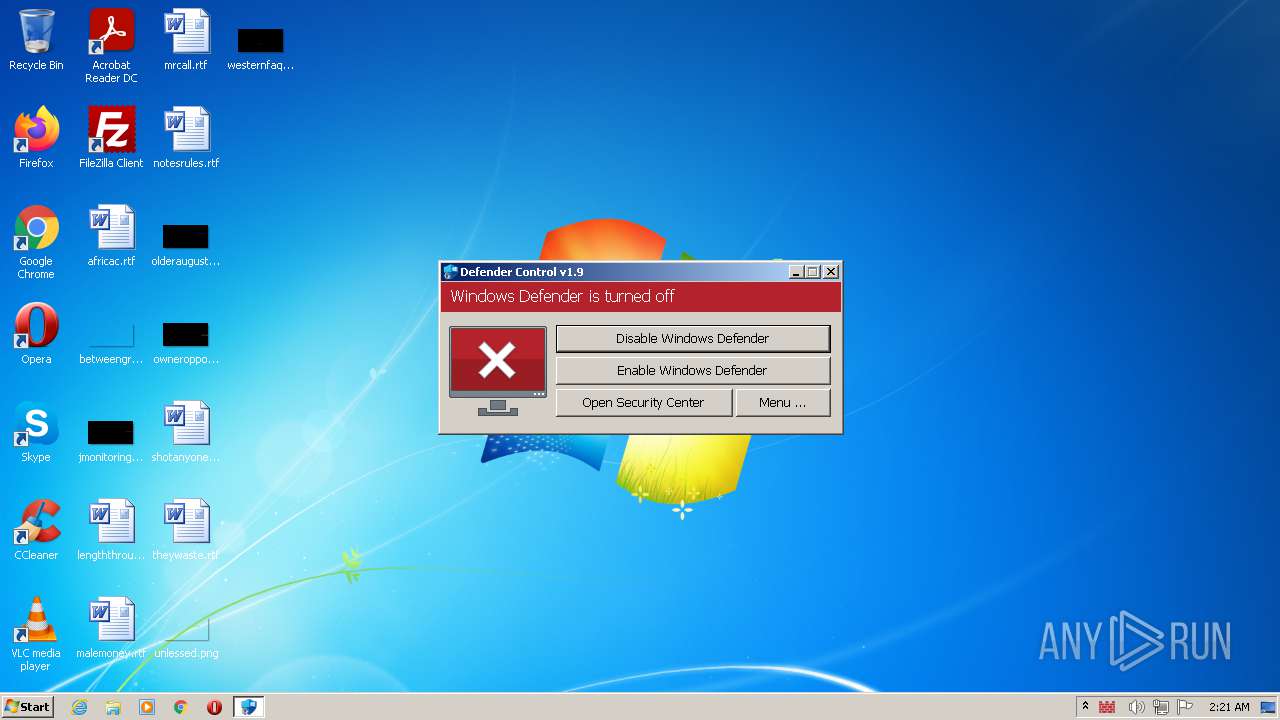
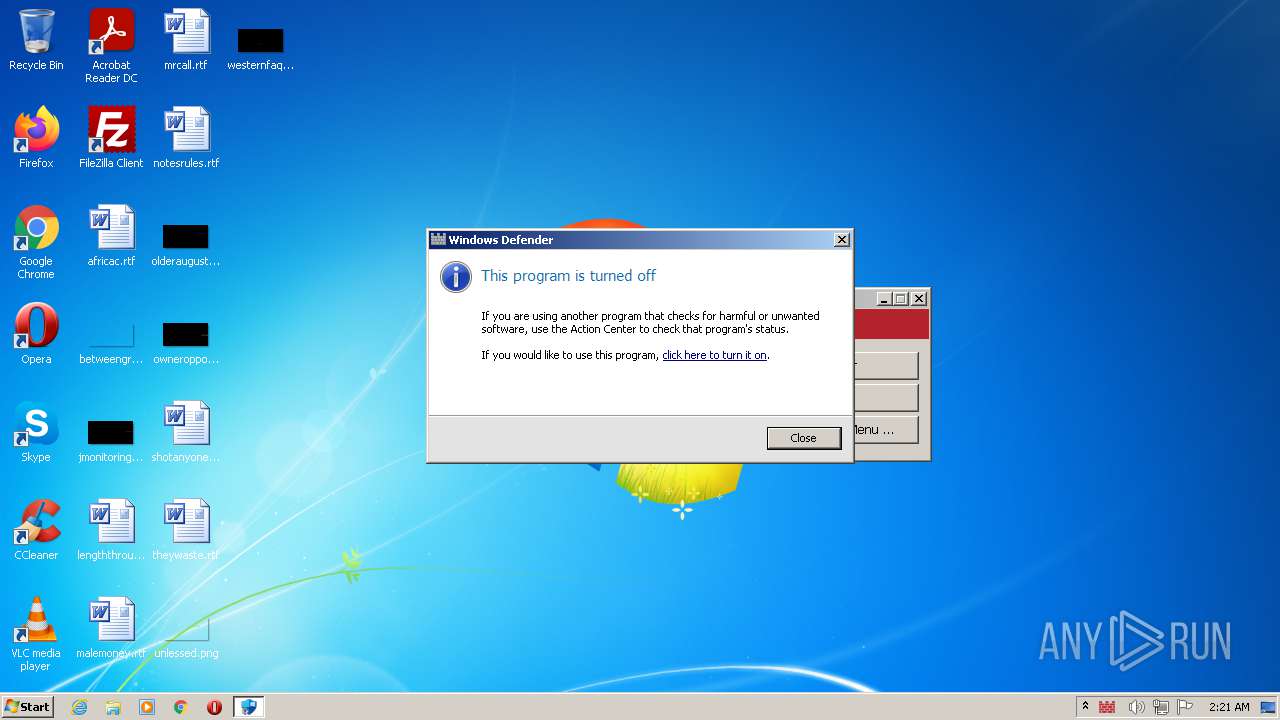
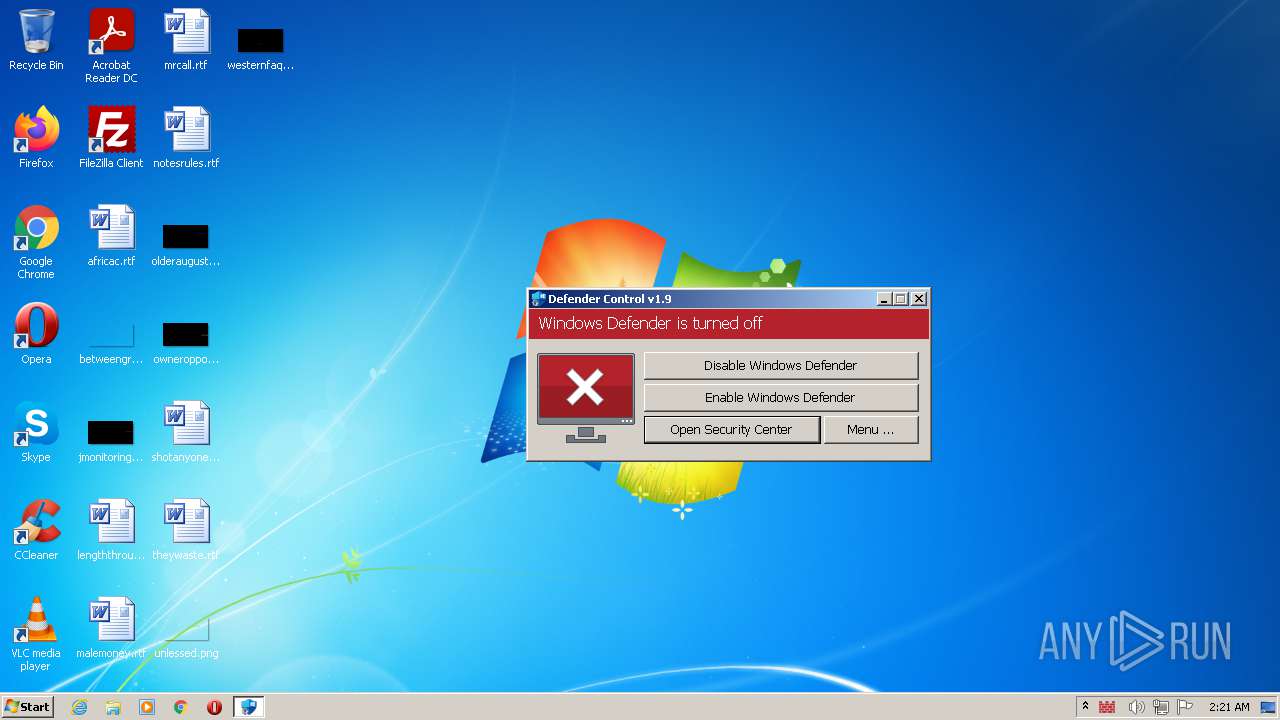
MALICIOUS
Modifies Windows Defender service settings
- dControl.exe (PID: 904)
- dControl.exe (PID: 3156)
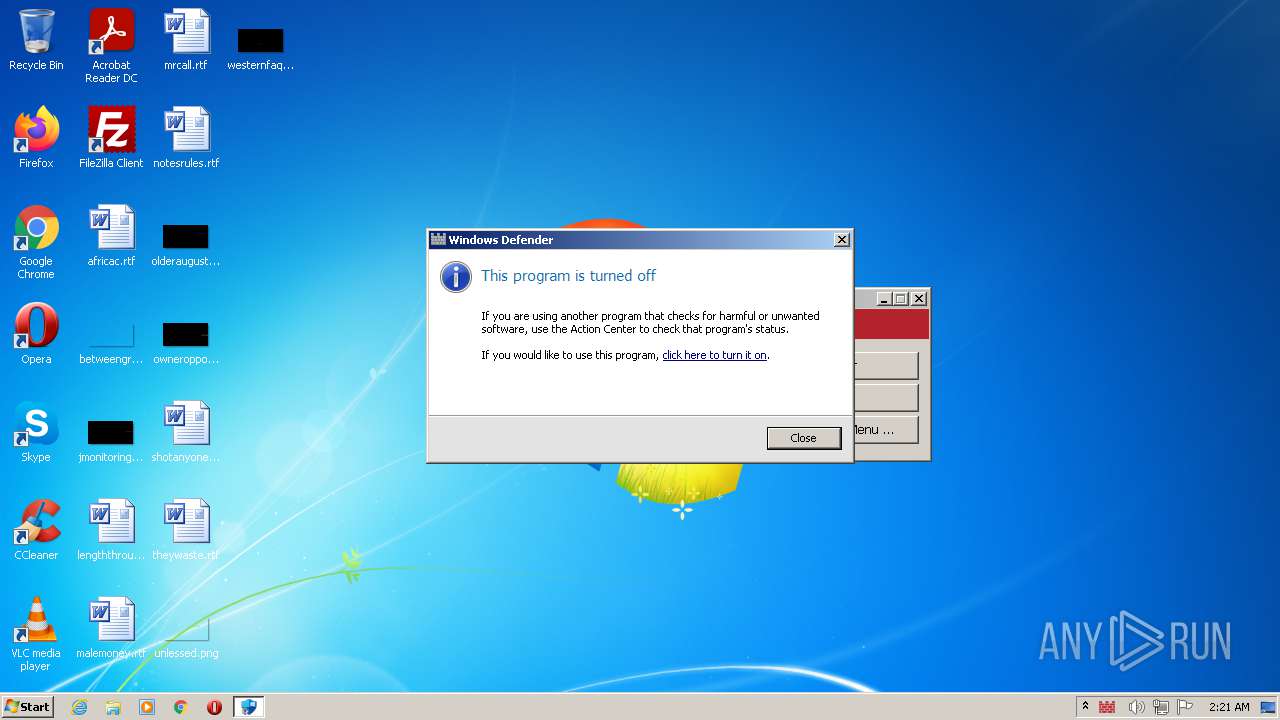
Disables Windows Defender
- dControl.exe (PID: 904)
- dControl.exe (PID: 3156)
SUSPICIOUS
Reads mouse settings
- dControl.exe (PID: 904)
- dControl.exe (PID: 3156)
Reads the computer name
- dControl.exe (PID: 904)
- dControl.exe (PID: 3156)
Checks supported languages
- dControl.exe (PID: 3156)
- dControl.exe (PID: 904)
- MSASCui.exe (PID: 3220)
- MSASCui.exe (PID: 3948)
Application launched itself
- dControl.exe (PID: 904)
Creates files in the Windows directory
- dControl.exe (PID: 3156)
Removes files from Windows directory
- dControl.exe (PID: 3156)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Coder: | By BlueLife |
|---|---|
| OriginalFileName: | dControl.exe |
| ProductVersion: | 1.9.0.0 |
| CompanyName: | www.sordum.org |
| LegalCopyright: | Copyright © 2015-2021 www.sordum.org All Rights Reserved. |
| FileDescription: | dControl v1.9 |
| Comments: | dControl v1.9 |
| FileVersion: | 1.9.0.0 |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.9.0.0 |
| FileVersionNumber: | 1.9.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x16310 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 141824 |
| CodeSize: | 524800 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2010:04:16 09:47:33+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Apr-2010 07:47:33 |
| Detected languages: |
|
| FileVersion: | 1.9.0.0 |
| Comments: | dControl v1.9 |
| FileDescription: | dControl v1.9 |
| LegalCopyright: | Copyright © 2015-2021 www.sordum.org All Rights Reserved. |
| CompanyName: | www.sordum.org |
| ProductVersion: | 1.9.0.0 |
| OriginalFilename: | dControl.exe |
| Coder: | By BlueLife |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Apr-2010 07:47:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00080017 | 0x00080200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6349 |
.rdata | 0x00082000 | 0x0000D95C | 0x0000DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.86699 |
.data | 0x00090000 | 0x0001A518 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.20196 |
.rsrc | 0x000AB000 | 0x0000E63C | 0x0000E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.04314 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25292 | 1182 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 3.66371 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.82922 | 1384 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 7.95701 | 31403 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 5.08829 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 5.38101 | 4264 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
13 | 0.916632 | 176 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
14 | 5.64947 | 2440 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
15 | 5.97994 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
50 | 3.61227 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Users\admin\AppData\Local\Temp\dControl.exe" | C:\Users\admin\AppData\Local\Temp\dControl.exe | Explorer.EXE | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: dControl v1.9 Exit code: 0 Version: 1.9.0.0 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\dControl.exe" | C:\Users\admin\AppData\Local\Temp\dControl.exe | — | Explorer.EXE | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: dControl v1.9 Exit code: 3221226540 Version: 1.9.0.0 Modules
| |||||||||||||||
| 3156 | "C:\Users\admin\AppData\Local\Temp\dControl.exe" /SYS 1 | C:\Users\admin\AppData\Local\Temp\dControl.exe | dControl.exe | ||||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v1.9 Exit code: 0 Version: 1.9.0.0 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Windows Defender\MSASCui.exe" | C:\Program Files\Windows Defender\MSASCui.exe | — | dControl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Defender User Interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | "C:\Program Files\Windows Defender\MSASCui.exe" | C:\Program Files\Windows Defender\MSASCui.exe | — | dControl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Defender User Interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
313
Read events
295
Write events
18
Delete events
0
Modification events
| (PID) Process: | (904) dControl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (904) dControl.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (3156) dControl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3156) dControl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3156) dControl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (3156) dControl.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (904) dControl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (904) dControl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (904) dControl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (904) dControl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 904 | dControl.exe | C:\Users\admin\AppData\Local\Temp\dControl.ini | text | |
MD5:319E0F66AD6B8CFAB53079CCBFB9D469 | SHA256:80D10D9FA5A7306D000C64FA6FA8269966EC8E7121C692A439DE76F2559E6338 | |||
| 904 | dControl.exe | C:\Users\admin\AppData\Local\Temp\wbfoxot | text | |
MD5:07232B64BE72593980CD952E8F85017E | SHA256:EF342BCC3C938C2FA9B38BC84019D8DCE94D018372F7D9C29A8EE7FF3F0FC3A8 | |||
| 3156 | dControl.exe | C:\Windows\TEMP\autD73D.tmp | binary | |
MD5:8D480A0FD29840481C0C9DEB3953A57A | SHA256:DACE58FA3CC9E42ADB073AFEAE10712529A4EF7E4AF6E2053439F1007ED76AE8 | |||
| 904 | dControl.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:18BD917DCFE60A77F3BDA05E1A35B407 | SHA256:657581D7C48DDB8643C3396C49A00C7177ACD7B4922CEC22D6F45F30A606DB7A | |||
| 904 | dControl.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:D15A332CBA4FC6D5062F42728CF751B4 | SHA256:9C064D5E80AB78FF046430CB6A6CA1B32266AF43500313CC13AD092534EE4A6F | |||
| 3156 | dControl.exe | C:\Windows\TEMP\hmwxlnp | text | |
MD5:07232B64BE72593980CD952E8F85017E | SHA256:EF342BCC3C938C2FA9B38BC84019D8DCE94D018372F7D9C29A8EE7FF3F0FC3A8 | |||
| 904 | dControl.exe | C:\Users\admin\AppData\Local\Temp\autB0D9.tmp | binary | |
MD5:8D480A0FD29840481C0C9DEB3953A57A | SHA256:DACE58FA3CC9E42ADB073AFEAE10712529A4EF7E4AF6E2053439F1007ED76AE8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report