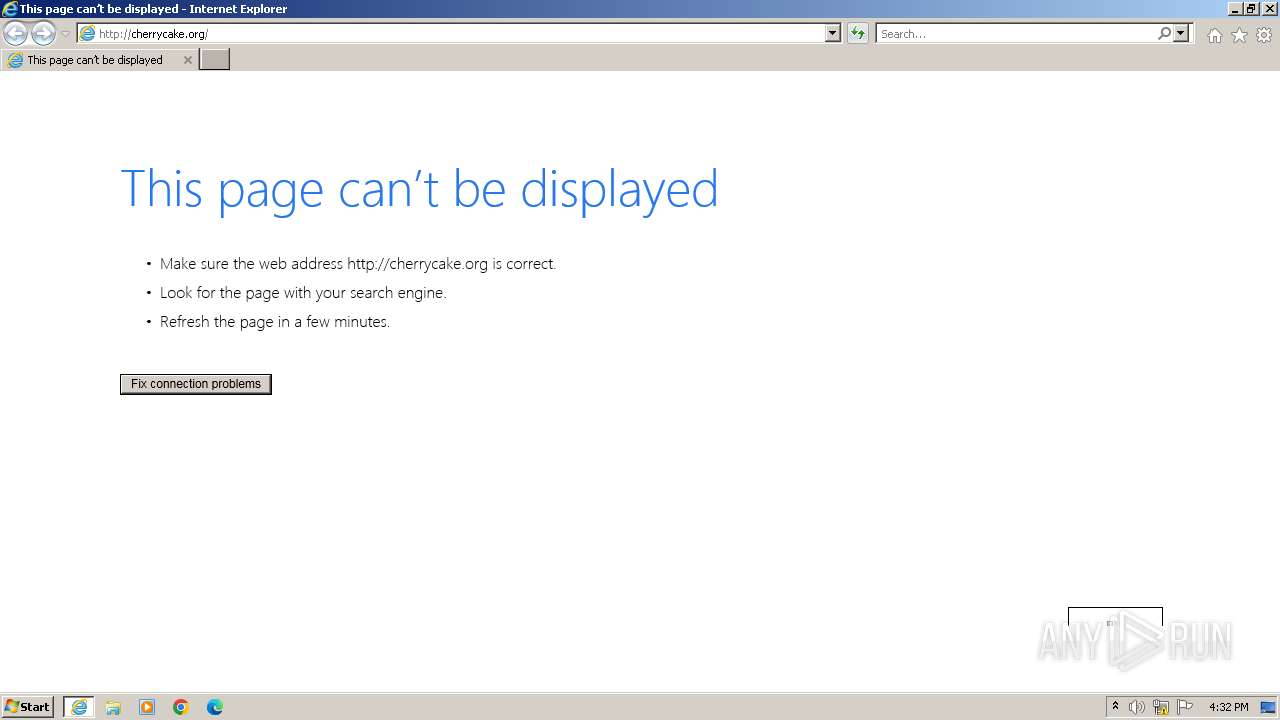
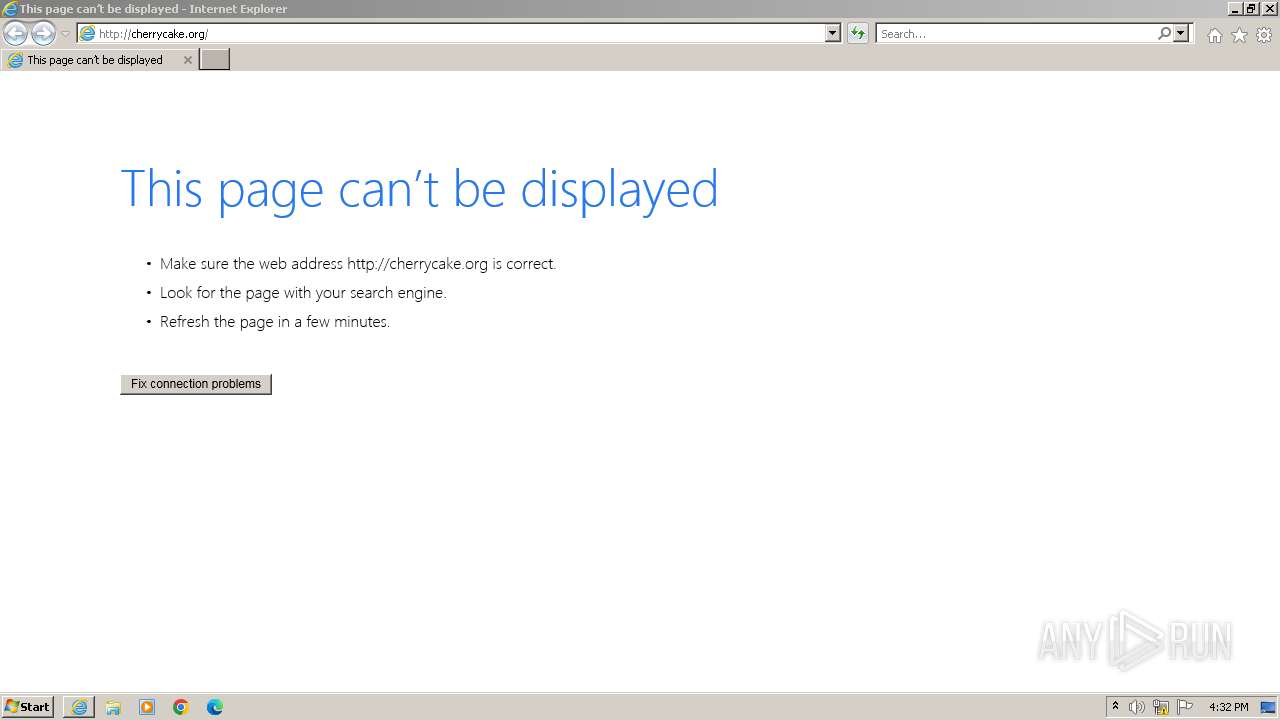
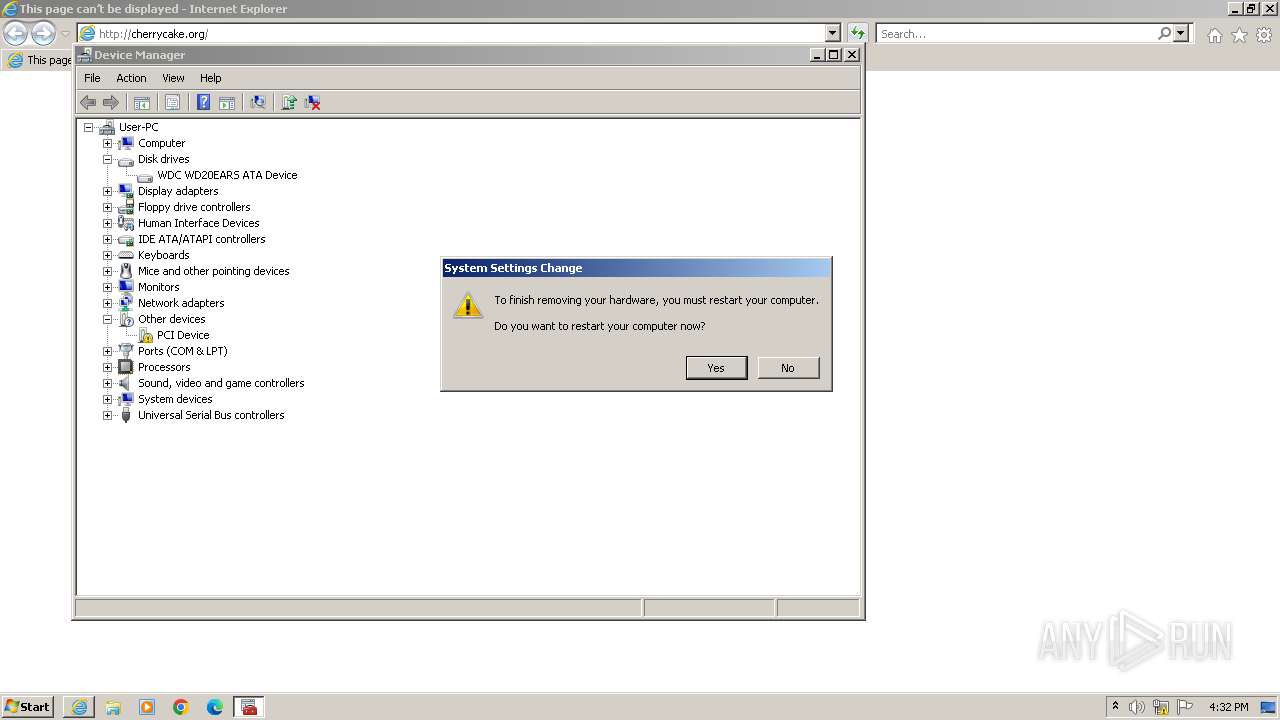
| URL: | cherrycake.org |
| Full analysis: | https://app.any.run/tasks/bcd137eb-8904-4d3a-bb49-aa96981dea3d |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2023, 16:31:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 679E00F68EFC046CC8E5065DA2428D60 |
| SHA1: | 6657067AD99496D5F57D553295F2B87F7B10D8AB |
| SHA256: | 65FF3A811858C435FF8DDD4D72636547274998A4B320674EA7C0BB7D112695D6 |
| SSDEEP: | 3:IGnw:ICw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- sdiagnhost.exe (PID: 644)
- sipnotify.exe (PID: 288)
Process drops legitimate windows executable
- msdt.exe (PID: 3276)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 644)
Reads settings of System Certificates
- msdt.exe (PID: 3276)
- sipnotify.exe (PID: 288)
The process executes via Task Scheduler
- sipnotify.exe (PID: 288)
- ctfmon.exe (PID: 1972)
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 644)
INFO
Create files in a temporary directory
- msdt.exe (PID: 3276)
- makecab.exe (PID: 3864)
- sdiagnhost.exe (PID: 644)
Drops the executable file immediately after the start
- msdt.exe (PID: 3276)
- makecab.exe (PID: 3864)
- msedge.exe (PID: 3424)
Application launched itself
- iexplore.exe (PID: 1556)
- msedge.exe (PID: 3424)
- iexplore.exe (PID: 3928)
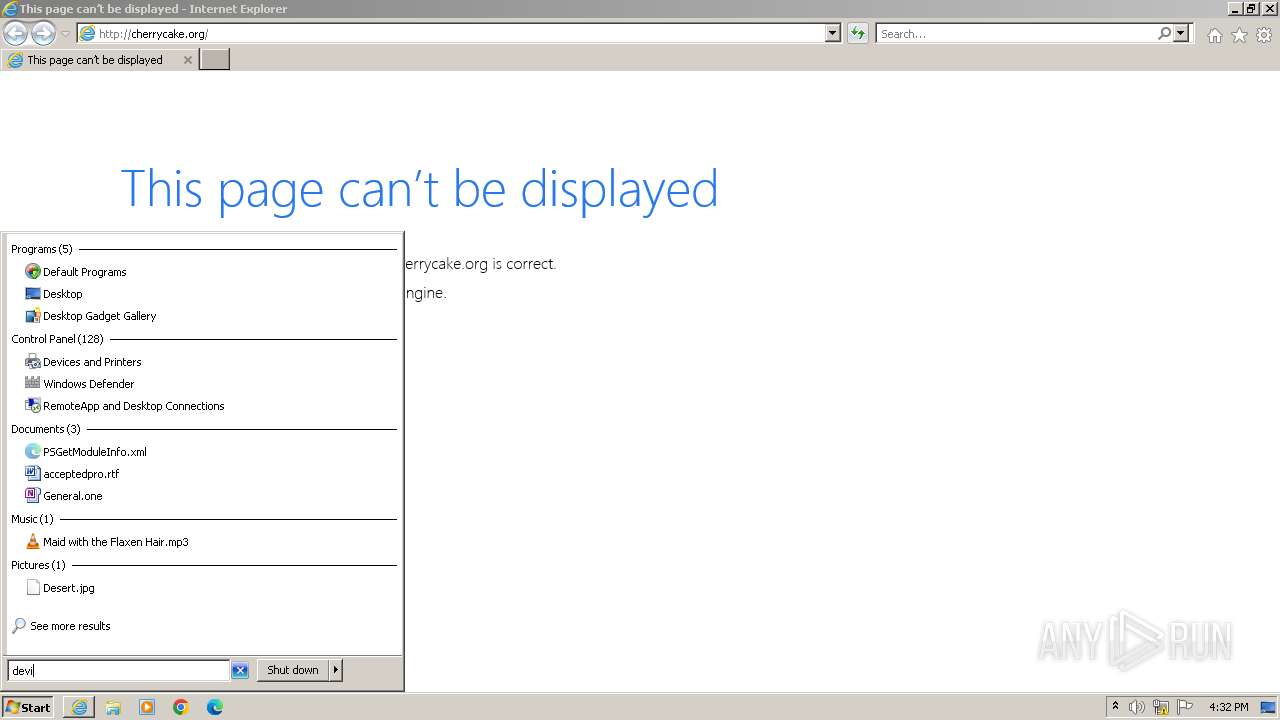
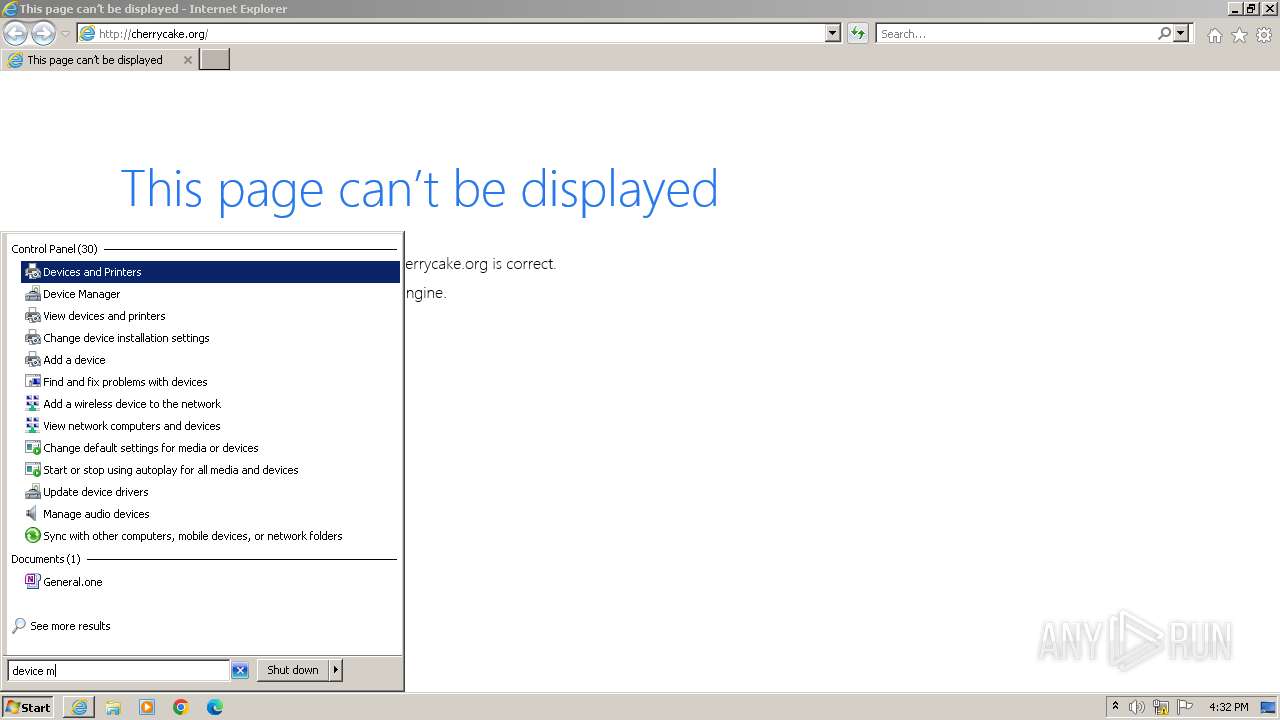
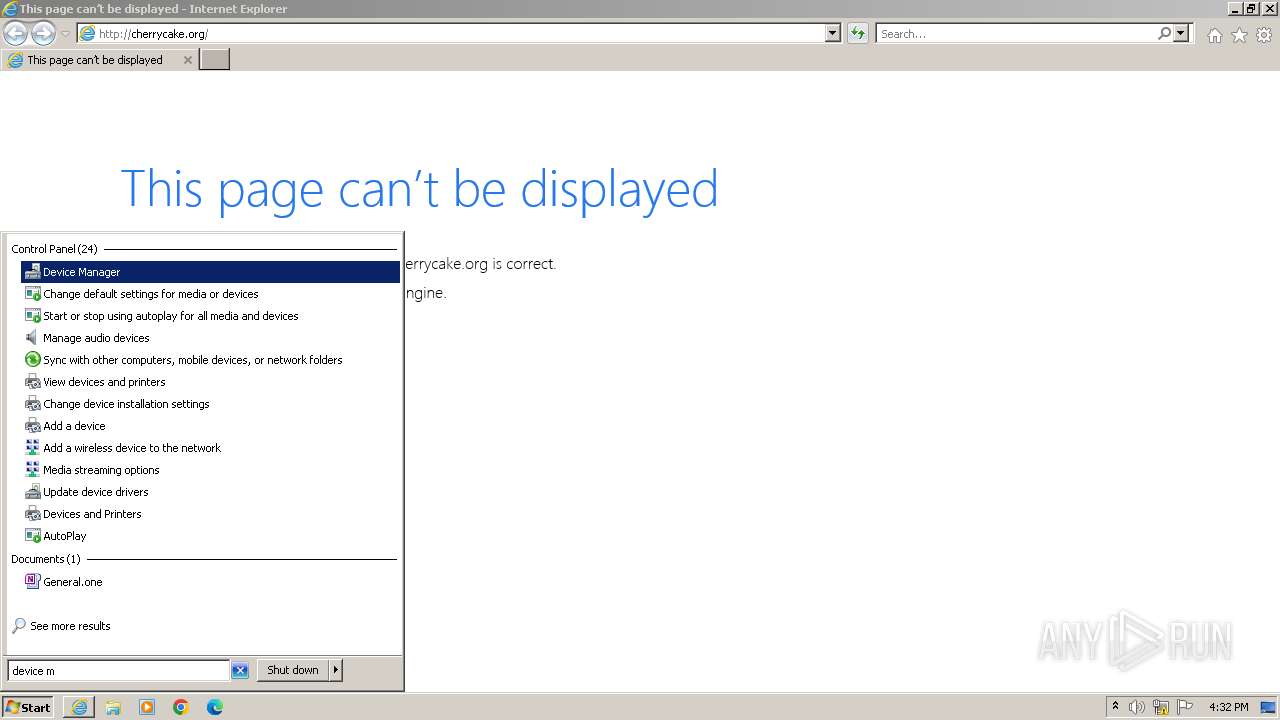
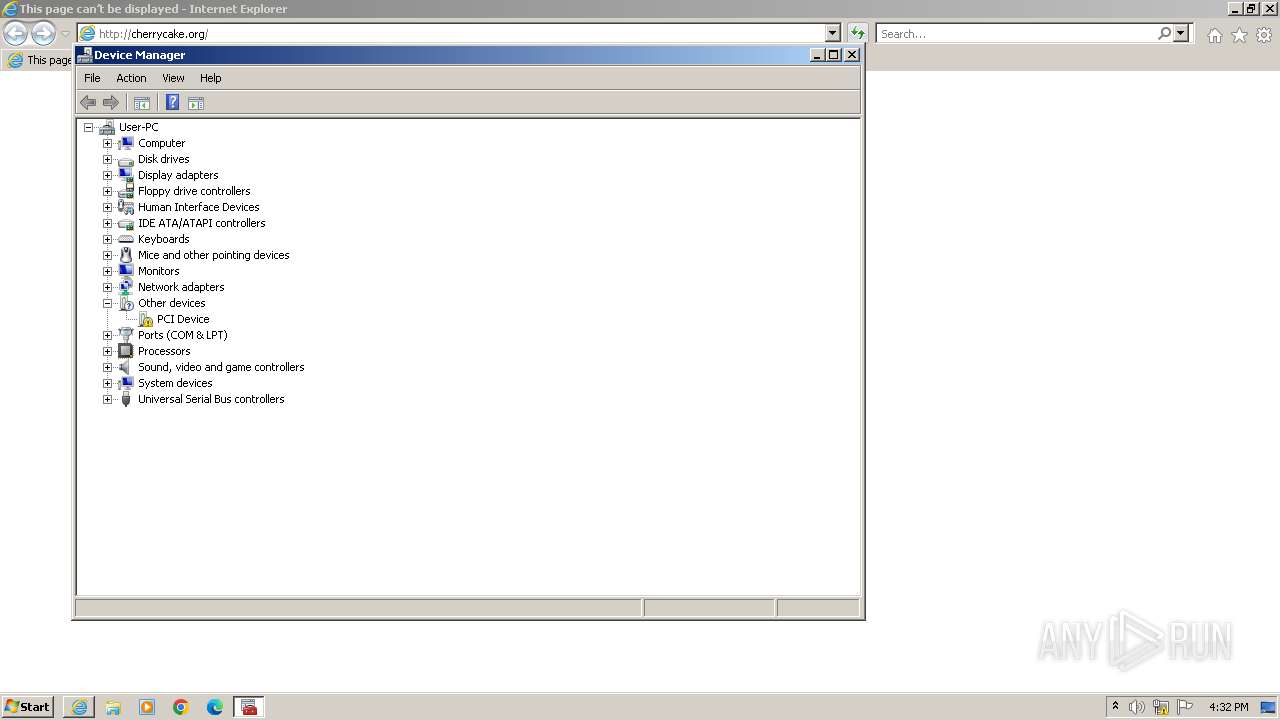
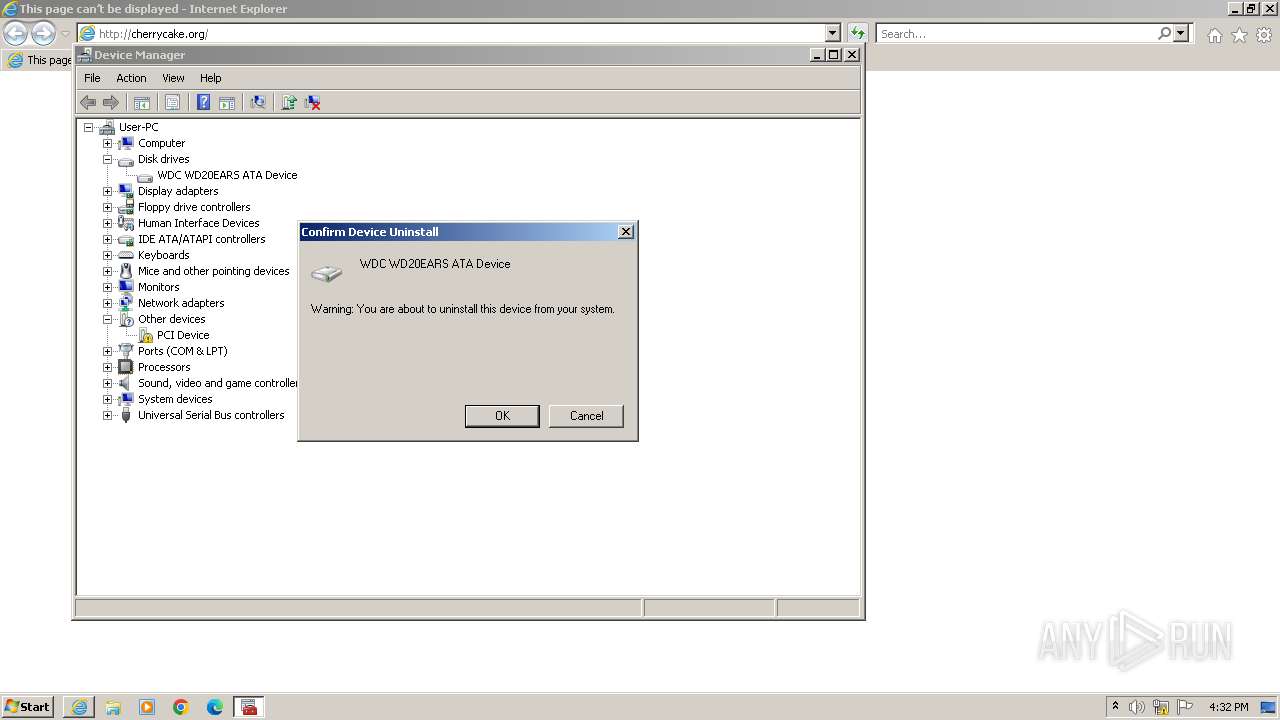
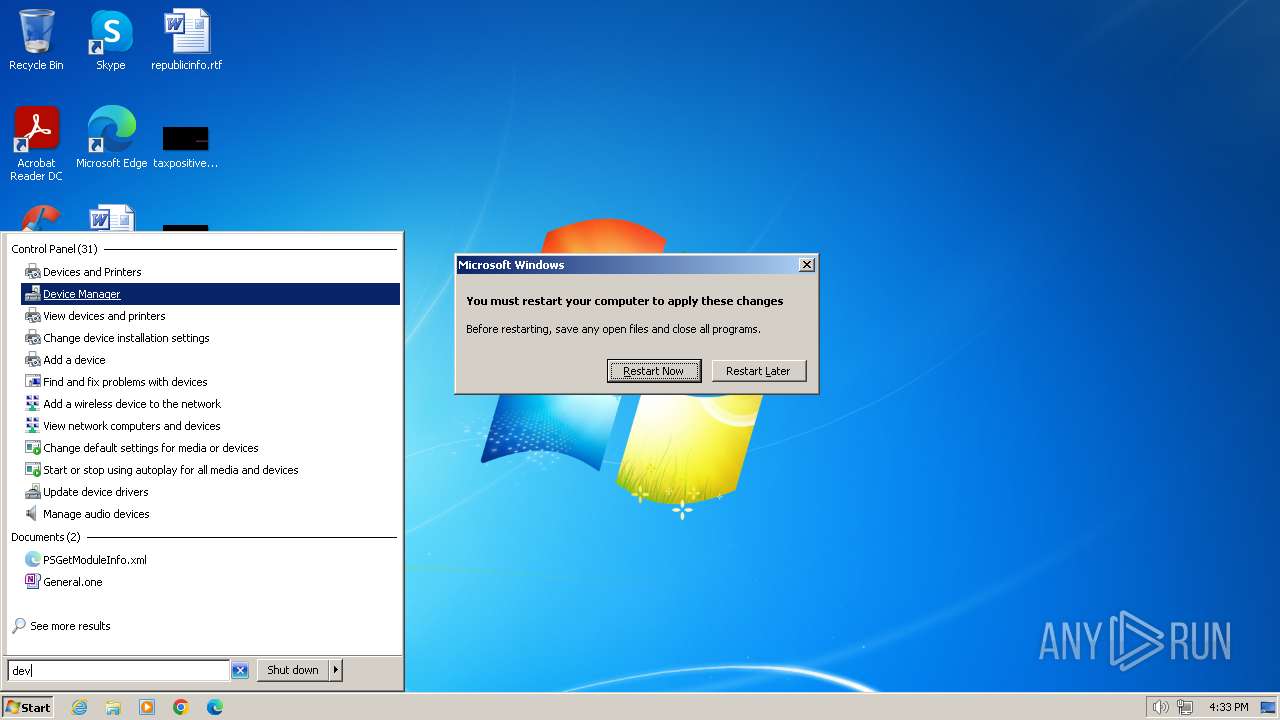
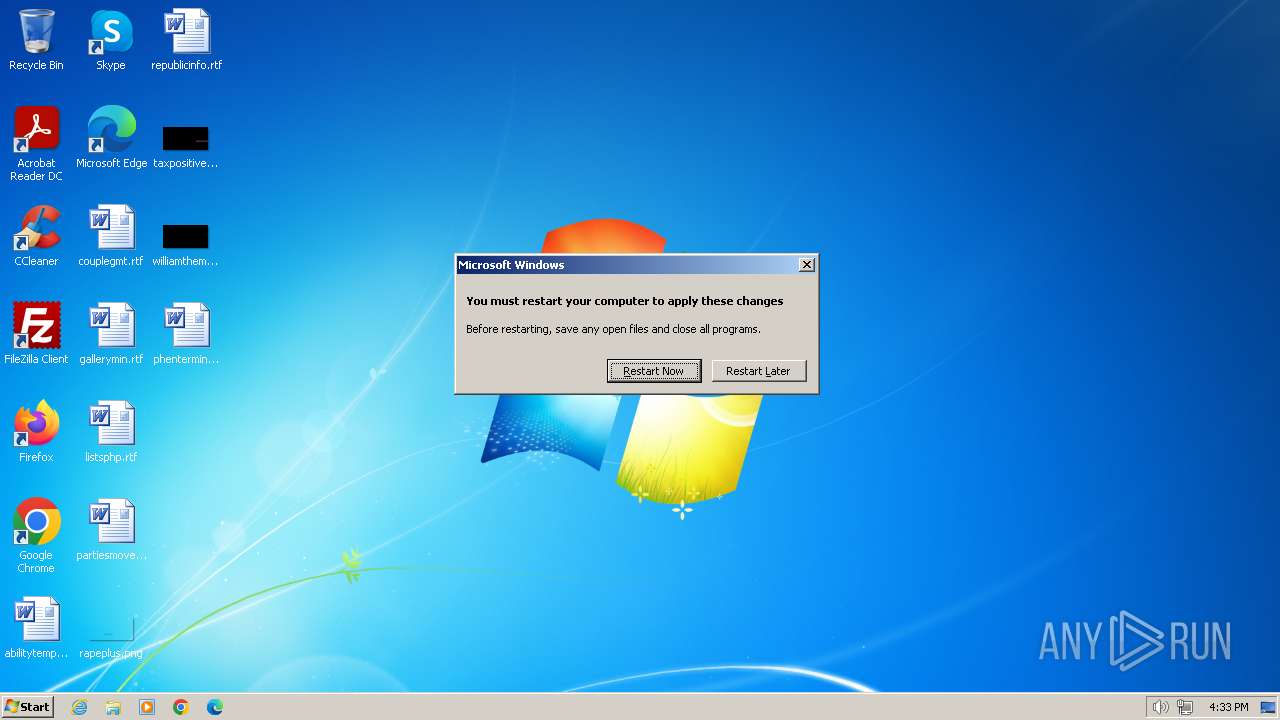
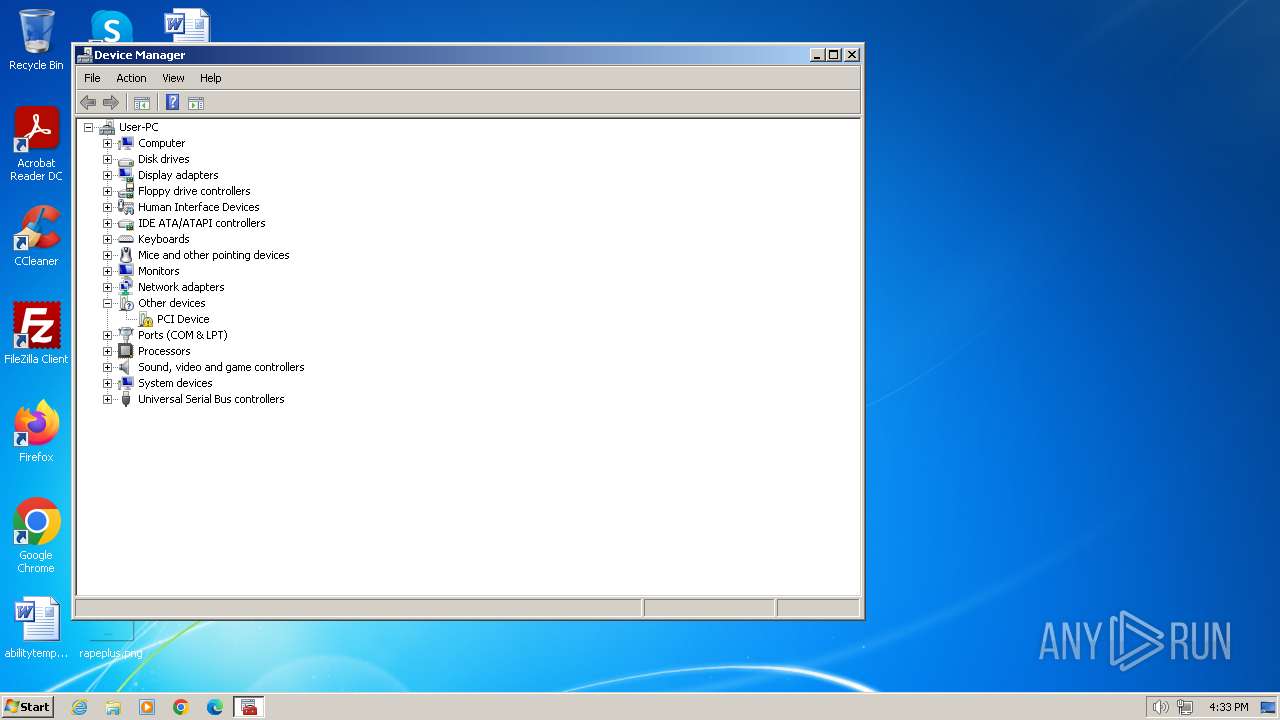
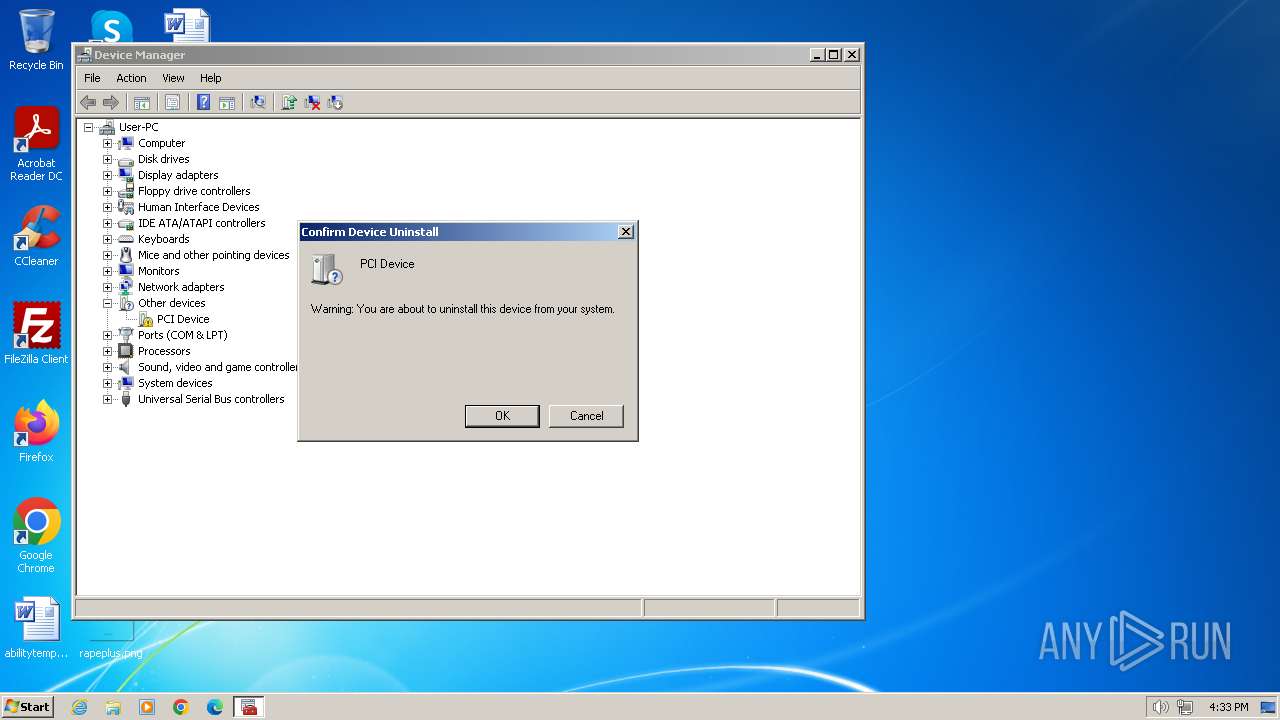
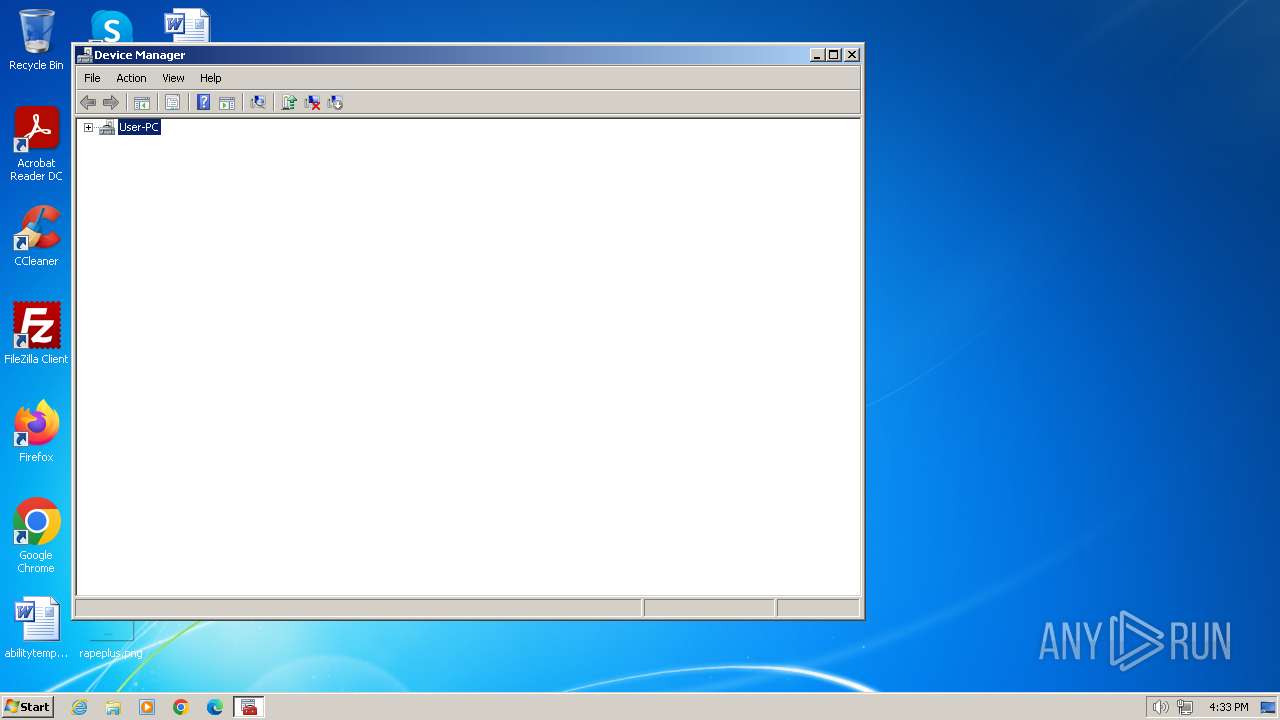
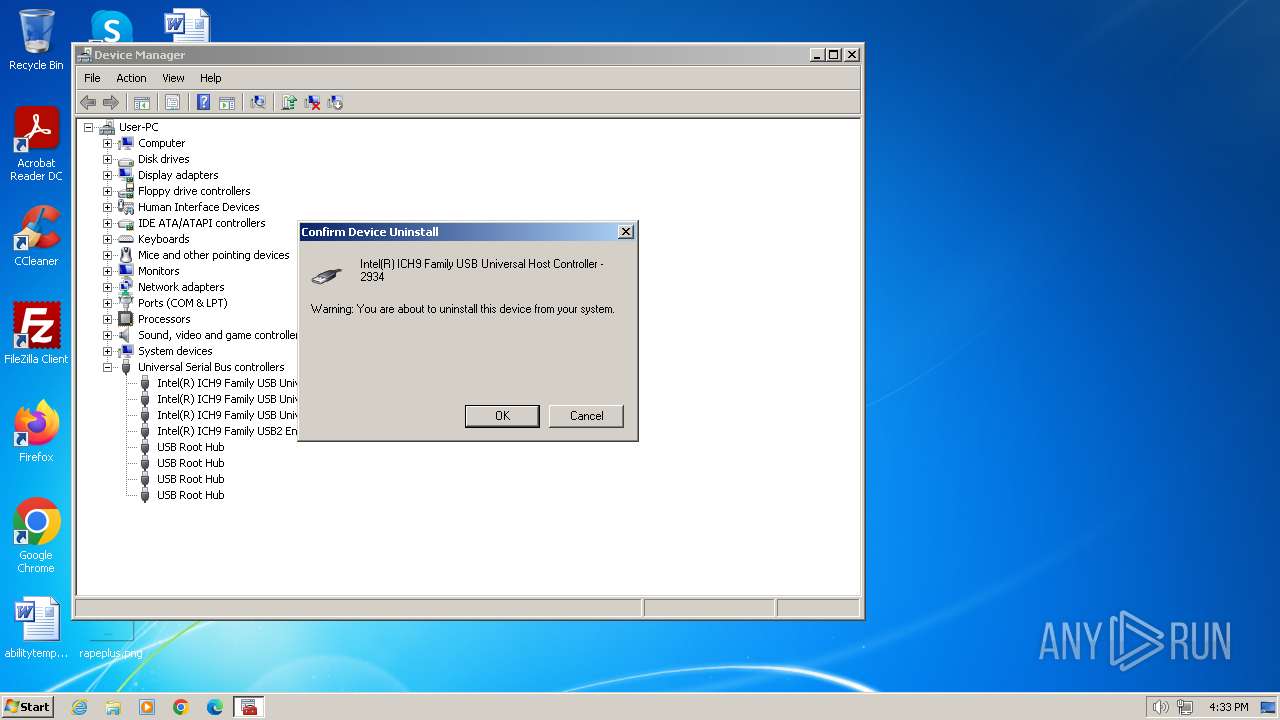
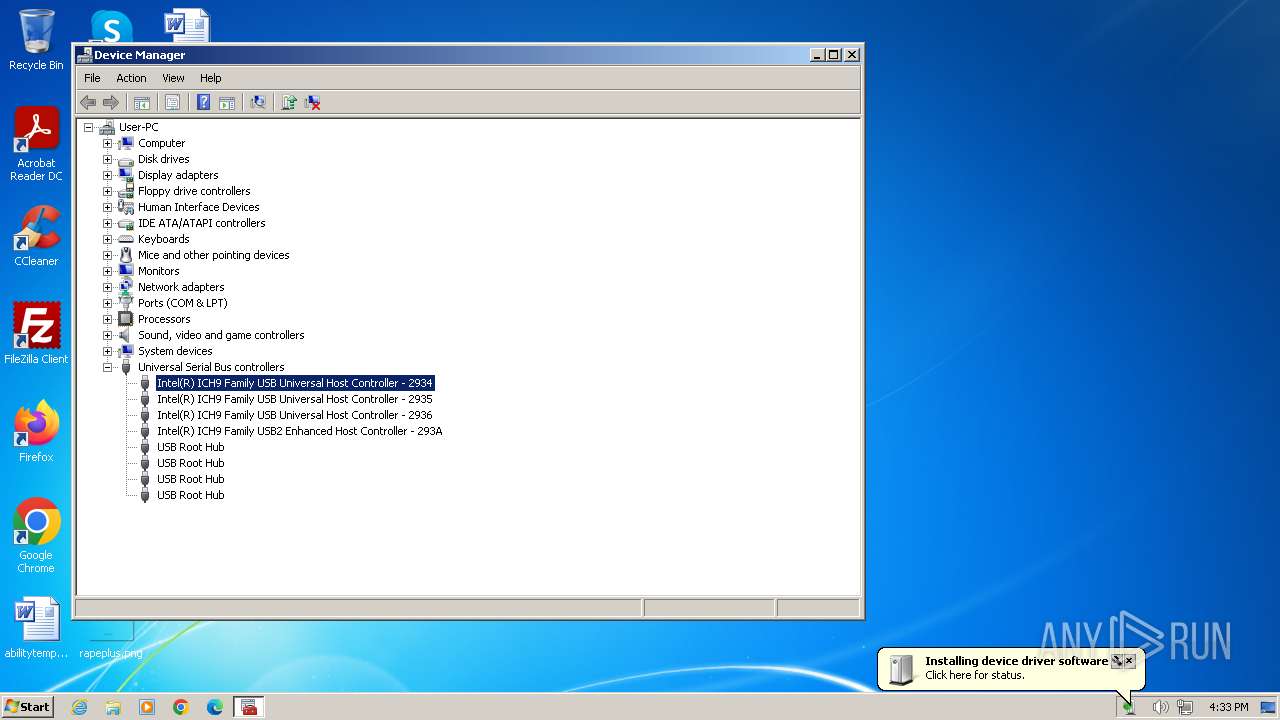
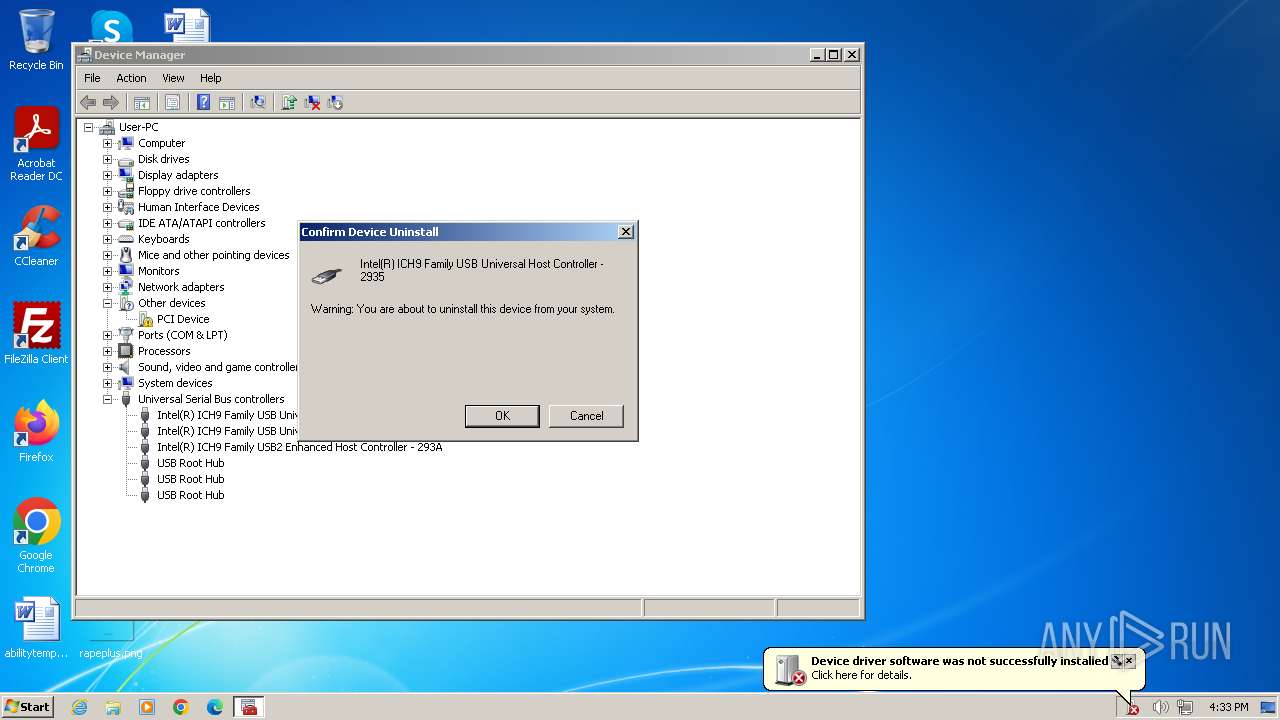
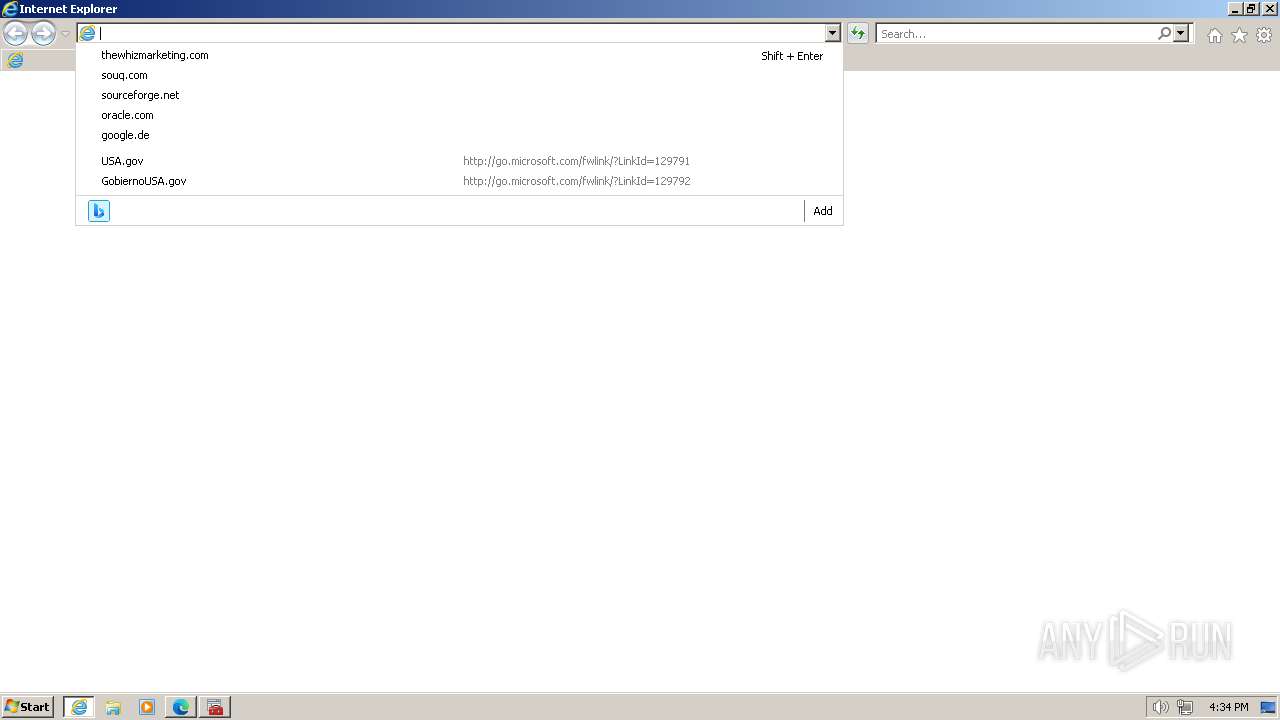
Manual execution by a user
- SndVol.exe (PID: 2492)
- mmc.exe (PID: 3356)
- mmc.exe (PID: 3012)
- IMEKLMG.EXE (PID: 2152)
- IMEKLMG.EXE (PID: 2160)
- wmpnscfg.exe (PID: 2644)
- mmc.exe (PID: 3148)
- mmc.exe (PID: 3036)
- iexplore.exe (PID: 3928)
- msedge.exe (PID: 3424)
- wmpnscfg.exe (PID: 2572)
Reads security settings of Internet Explorer
- msdt.exe (PID: 3276)
- sipnotify.exe (PID: 288)
- sdiagnhost.exe (PID: 644)
Creates files or folders in the user directory
- DeviceDisplayObjectProvider.exe (PID: 4004)
- msdt.exe (PID: 3276)
Reads the computer name
- IMEKLMG.EXE (PID: 2152)
- wmpnscfg.exe (PID: 2572)
- wmpnscfg.exe (PID: 2644)
- IMEKLMG.EXE (PID: 2160)
Checks supported languages
- IMEKLMG.EXE (PID: 2152)
- IMEKLMG.EXE (PID: 2160)
- wmpnscfg.exe (PID: 2572)
- wmpnscfg.exe (PID: 2644)
Process checks are UAC notifies on
- IMEKLMG.EXE (PID: 2152)
- IMEKLMG.EXE (PID: 2160)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2644)
- wmpnscfg.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
135
Monitored processes
32
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 316 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3864 --field-trial-handle=1308,i,16015306198612772253,4871666115002195510,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 644 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3868 --field-trial-handle=1308,i,16015306198612772253,4871666115002195510,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
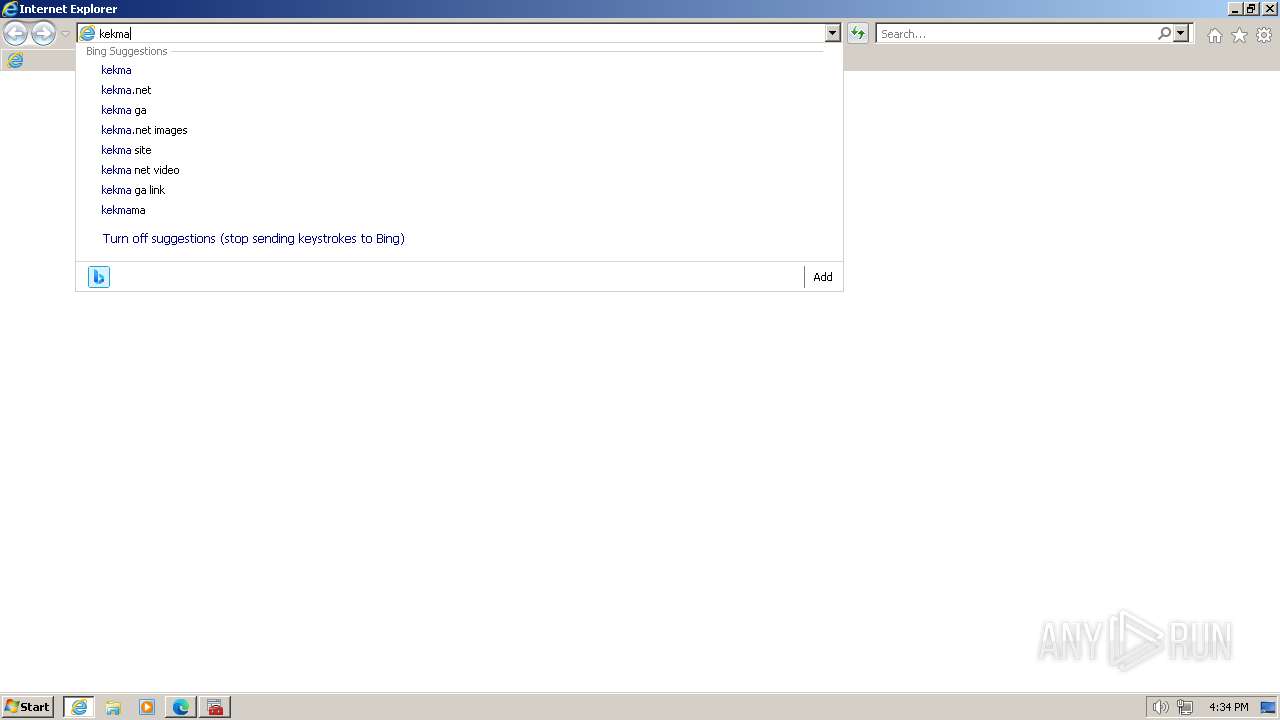
| 1556 | "C:\Program Files\Internet Explorer\iexplore.exe" "cherrycake.org" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1972 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1556 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2492 | SndVol.exe -f 46007409 9161 | C:\Windows\System32\SndVol.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
25 487
Read events
25 188
Write events
285
Delete events
14
Modification events
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005A010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
14
Suspicious files
176
Text files
114
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:49F911D34E224FE2ECDCC4BB6AD2C499 | SHA256:BDFB97D30CA9FF3963407ADB056AA9B4B7A8D629144B98BE7B514BA6DB40DCEF | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3276 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_50dd0a98-25f8-4f8a-aaa2-652a745d84fc\InteractiveRes.ps1 | text | |
MD5:25B8543DBF571F040118423BC3C7A75E | SHA256:D78E6291D6F27AC6FEBDCF0A4D5A34521E7F033AF8875E026DF21BA7513AB64A | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3276 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_50dd0a98-25f8-4f8a-aaa2-652a745d84fc\DiagPackage.diagpkg | xml | |
MD5:C9FB87FA3460FAE6D5D599236CFD77E2 | SHA256:CDE728C08A4E50A02FCFF35C90EE2B3B33AB24C8B858F180B6A67BFA94DEF35F | |||
| 3276 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_50dd0a98-25f8-4f8a-aaa2-652a745d84fc\NetworkDiagnosticsResolve.ps1 | text | |
MD5:A7B957F221C643580184665BE57E6AC8 | SHA256:8582EF50174CB74233F196F193E04C0CCBBEE2AED5CE50964CBB95822C218E7F | |||
| 3276 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_50dd0a98-25f8-4f8a-aaa2-652a745d84fc\DiagPackage.dll | executable | |
MD5:2433E09C08C21455000F7E36D7653759 | SHA256:EA9400E719FB15CD82D5DAB4B7D8E3870BB375BBE11BB95B0D957A84FEE2891C | |||
| 3276 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_50dd0a98-25f8-4f8a-aaa2-652a745d84fc\en-US\DiagPackage.dll.mui | executable | |
MD5:5D7936806E6855E2ECC2B095316D45D8 | SHA256:71A4559F9FD122914A95998E8685BE638B8F81E581987708497E8F8A7A2F4DCB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
52
DNS requests
67
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1556 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?947160355facb38e | unknown | compressed | 4.66 Kb | unknown |
1556 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
1556 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9c39c51ec95c49f5 | unknown | compressed | 4.66 Kb | unknown |
1556 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3988 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
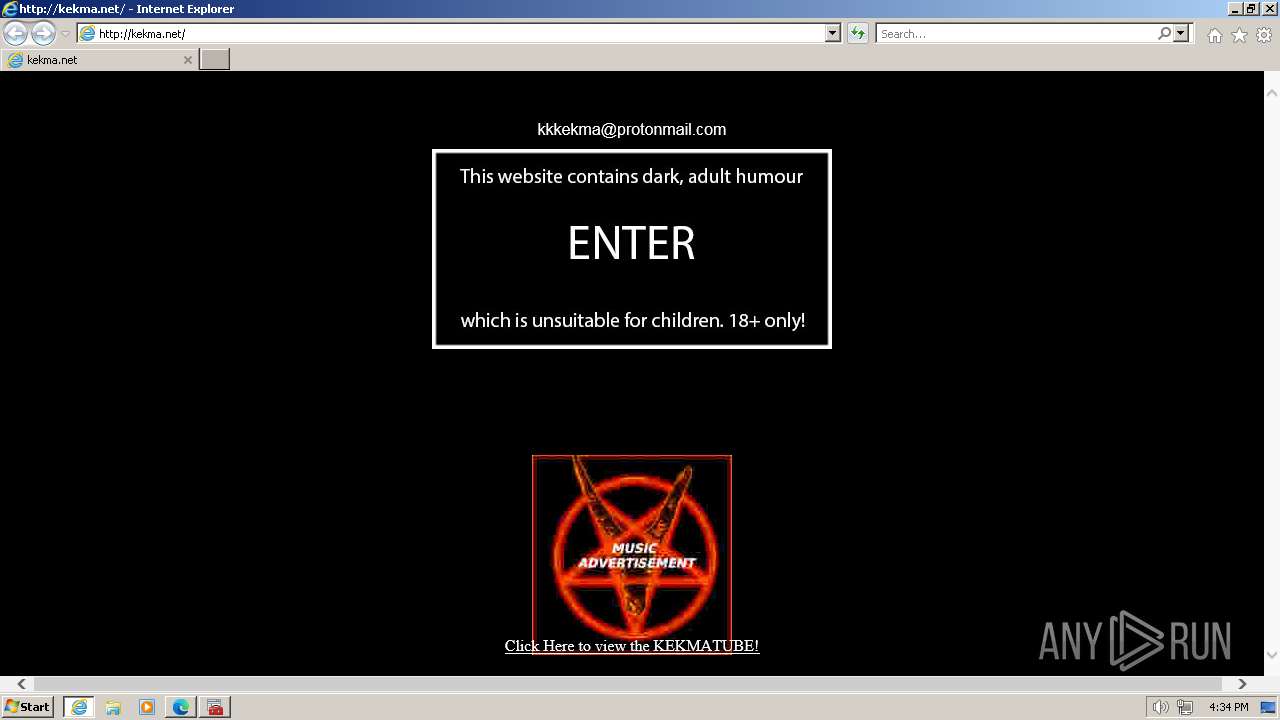
3988 | iexplore.exe | GET | 200 | 188.114.96.3:80 | http://kekma.net/button.jpg | unknown | image | 31.4 Kb | unknown |
3988 | iexplore.exe | GET | 200 | 188.114.96.3:80 | http://kekma.net/ | unknown | html | 1022 b | unknown |
3988 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
3988 | iexplore.exe | GET | 200 | 188.114.96.3:80 | http://kekma.net/scream.mp3 | unknown | binary | 646 Kb | unknown |
3988 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1556 | iexplore.exe | 23.53.43.177:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1556 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1556 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1556 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1116 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cherrycake.org |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3988 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |