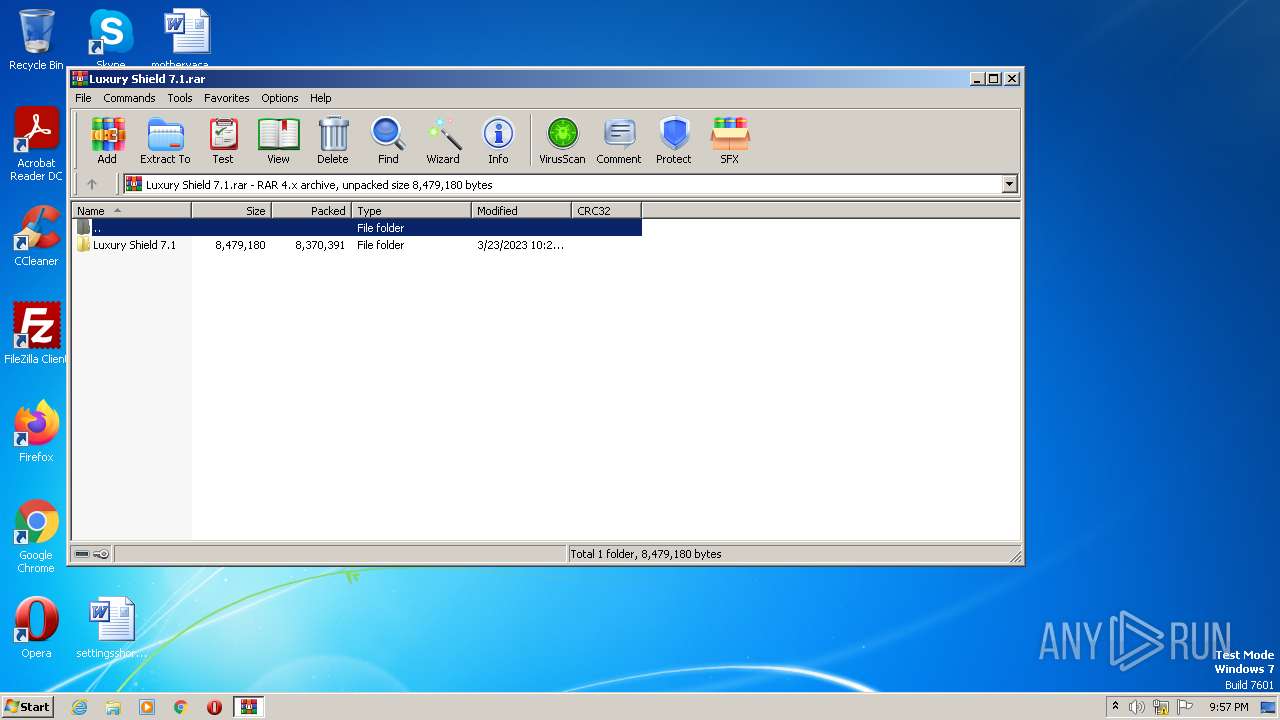
| File name: | Luxury Shield 7.1.rar |
| Full analysis: | https://app.any.run/tasks/699044fd-5883-4f10-be84-be89c85d62da |
| Verdict: | Malicious activity |
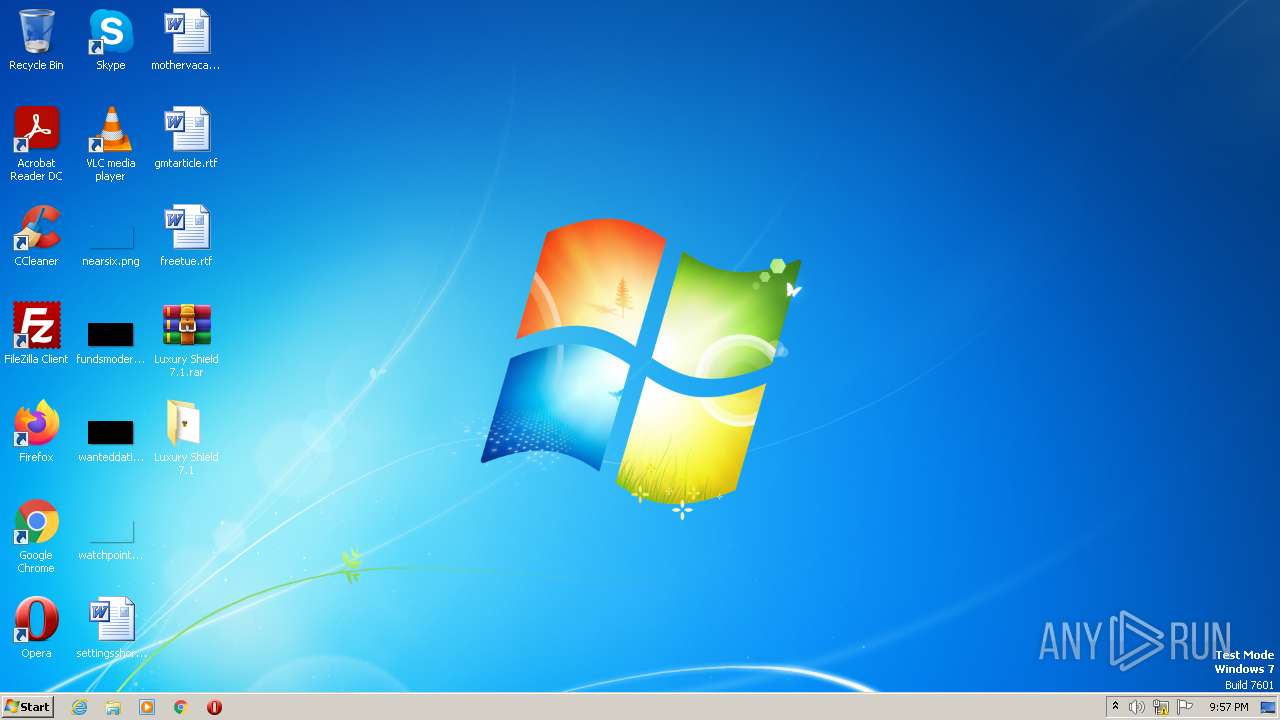
| Analysis date: | March 31, 2023, 20:57:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32, flags: RecoveryRecordPresent |
| MD5: | 96F765B91EBA925C6B262D89D1A6A8C9 |
| SHA1: | 65AAB7E376393E03D78D11C95E7543E1D95EFE72 |
| SHA256: | 65FAE68ECD6E5EFDD44A5A68B33349ADE1C172AE08EA7A1654343CEDF065A298 |
| SSDEEP: | 196608:c1roE5rz7tHv2TFc3xo3GJDKbEFYXi2vQeuQLr8HPHpXSU:c18y9v2TE2GoUD2vpr8HRJ |
MALICIOUS
Application was dropped or rewritten from another process
- Luxury Sheild v7.1.exe (PID: 3660)
- Luxury Sheild v7.1.exe (PID: 1800)
SUSPICIOUS
Reads the Internet Settings
- cmd.exe (PID: 4088)
- cmd.exe (PID: 1868)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4088)
- cmd.exe (PID: 1868)
Starts CMD.EXE for commands execution
- Luxury Sheild v7.1.exe (PID: 3660)
- Luxury Sheild v7.1.exe (PID: 1800)
INFO
Reads the computer name
- Luxury Sheild v7.1.exe (PID: 3660)
- Luxury Sheild v7.1.exe (PID: 1800)
Checks supported languages
- Luxury Sheild v7.1.exe (PID: 3660)
- Luxury Sheild v7.1.exe (PID: 1800)
The process checks LSA protection
- Luxury Sheild v7.1.exe (PID: 3660)
- powershell.exe (PID: 3140)
- cmd.exe (PID: 4088)
- Luxury Sheild v7.1.exe (PID: 1800)
- cmd.exe (PID: 1868)
- powershell.exe (PID: 2732)
Reads the machine GUID from the registry
- Luxury Sheild v7.1.exe (PID: 3660)
- Luxury Sheild v7.1.exe (PID: 1800)
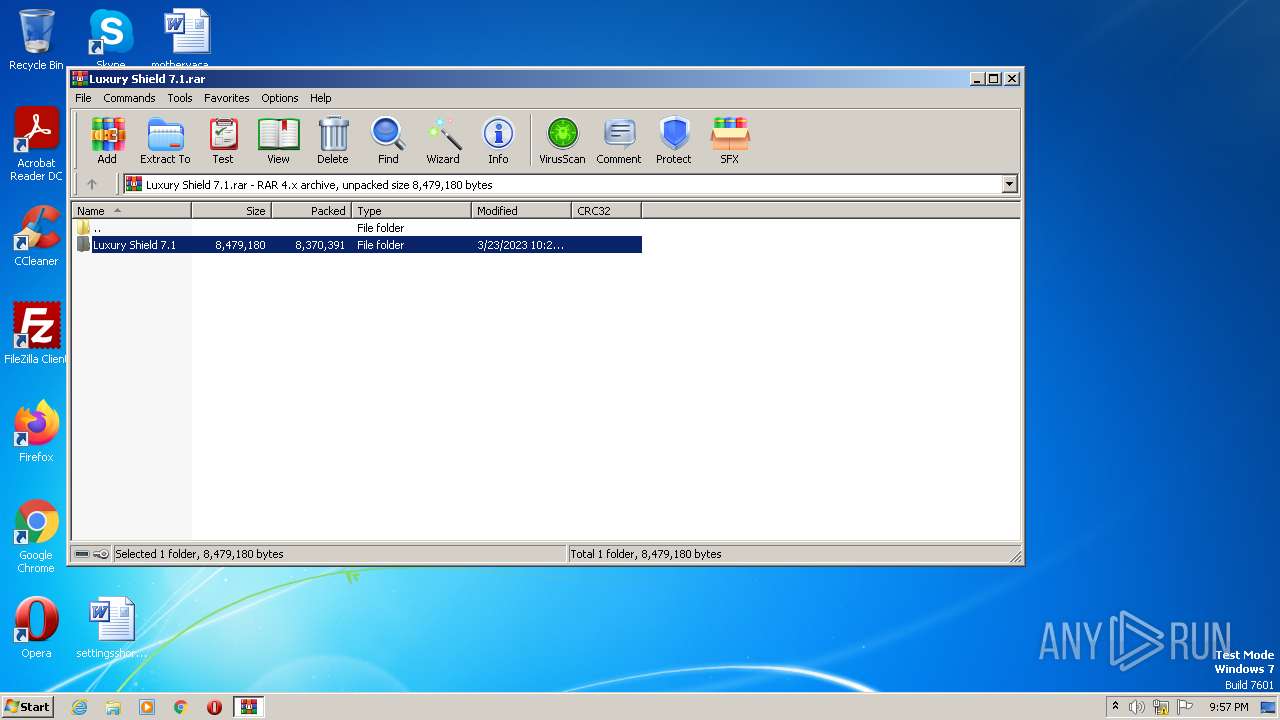
Executable content was dropped or overwritten
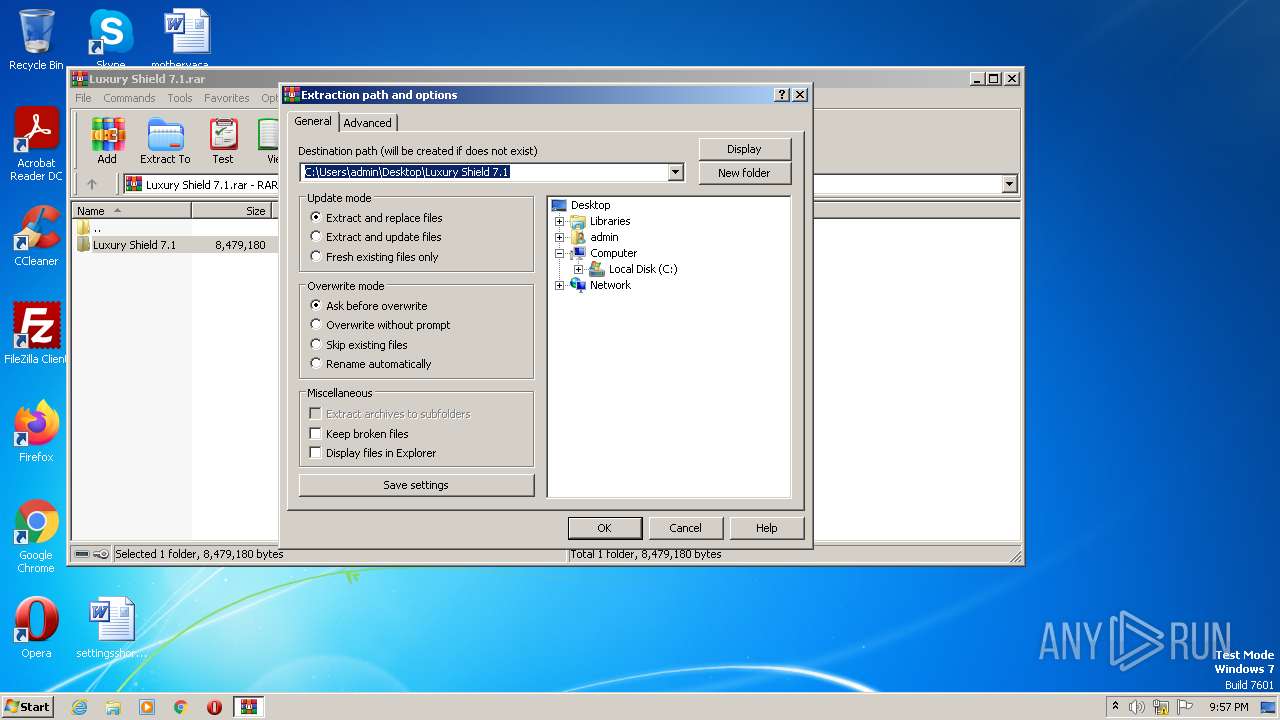
- WinRAR.exe (PID: 2668)
- WinRAR.exe (PID: 2952)
Manual execution by a user
- WinRAR.exe (PID: 2952)
- Luxury Sheild v7.1.exe (PID: 3660)
- Luxury Sheild v7.1.exe (PID: 1800)
Create files in a temporary directory
- powershell.exe (PID: 3140)
- powershell.exe (PID: 2732)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3140)
- powershell.exe (PID: 2732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
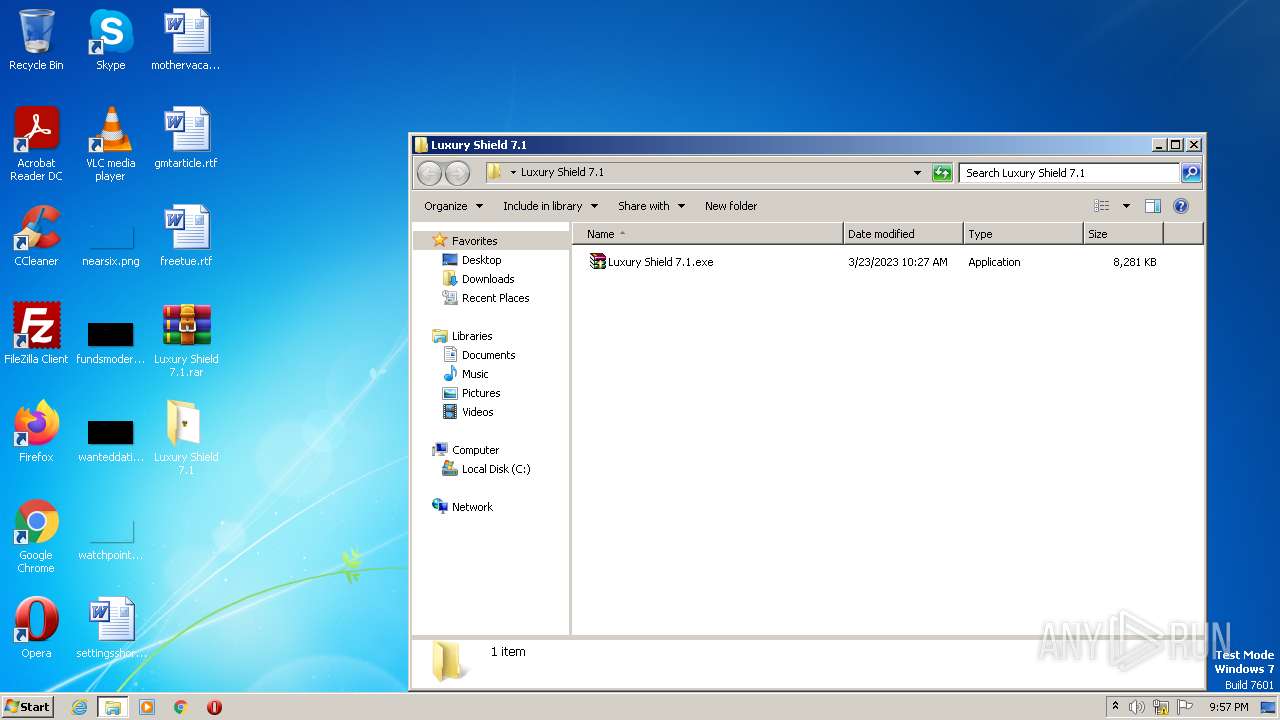
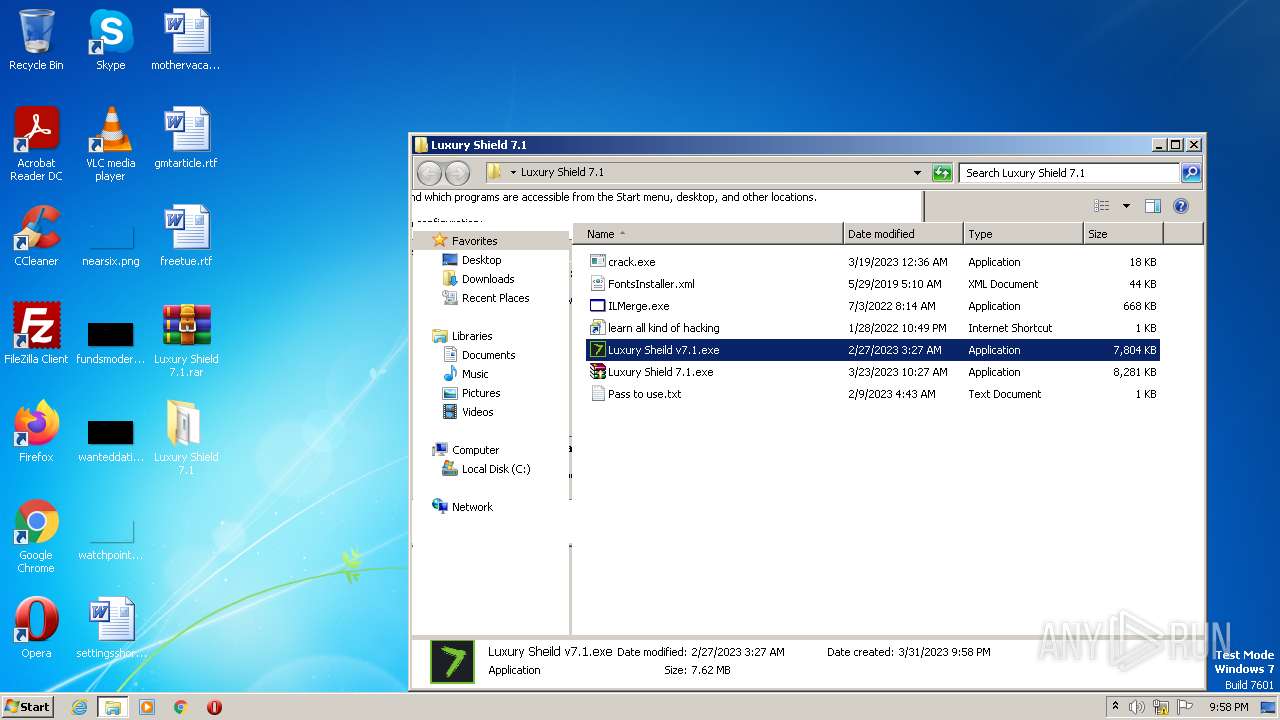
| ArchivedFileName: | Luxury Shield 7.1\Luxury Shield 7.1.exe |
|---|---|
| PackingMethod: | Normal |
| ModifyDate: | 2023:03:23 10:27:22 |
| OperatingSystem: | Win32 |
| UncompressedSize: | 8479180 |
| CompressedSize: | 8370456 |
Total processes
58
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
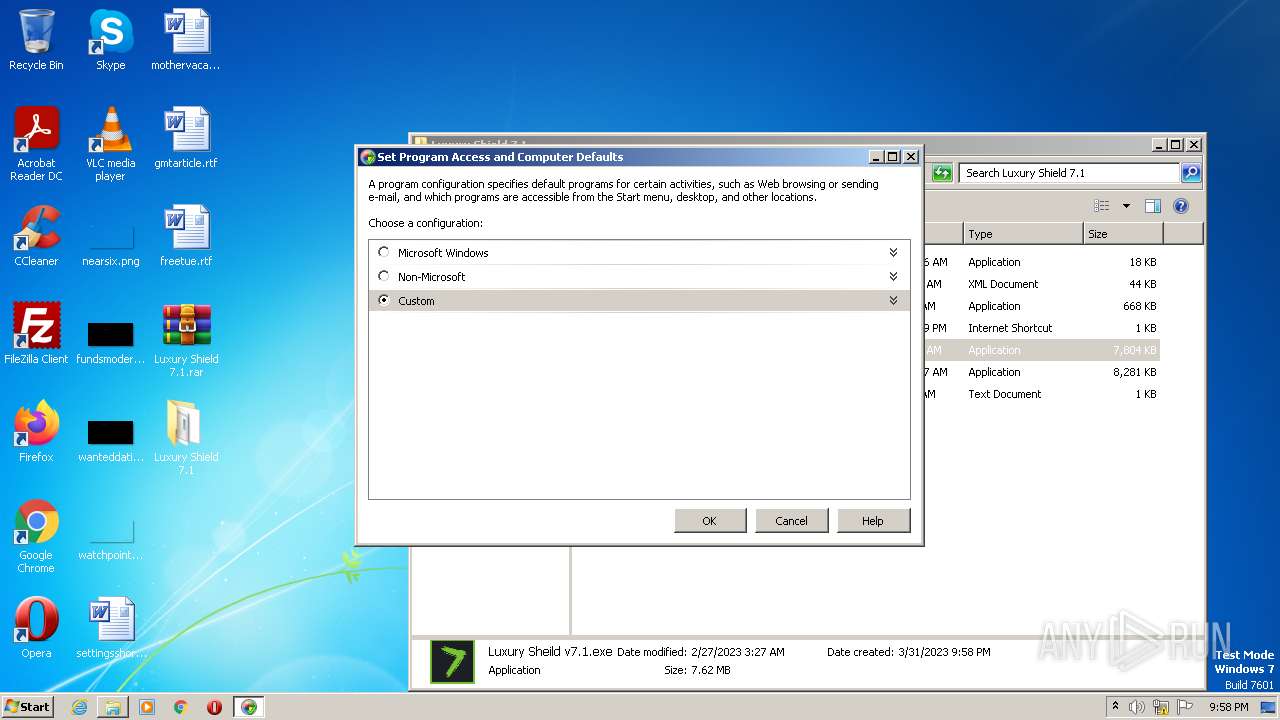
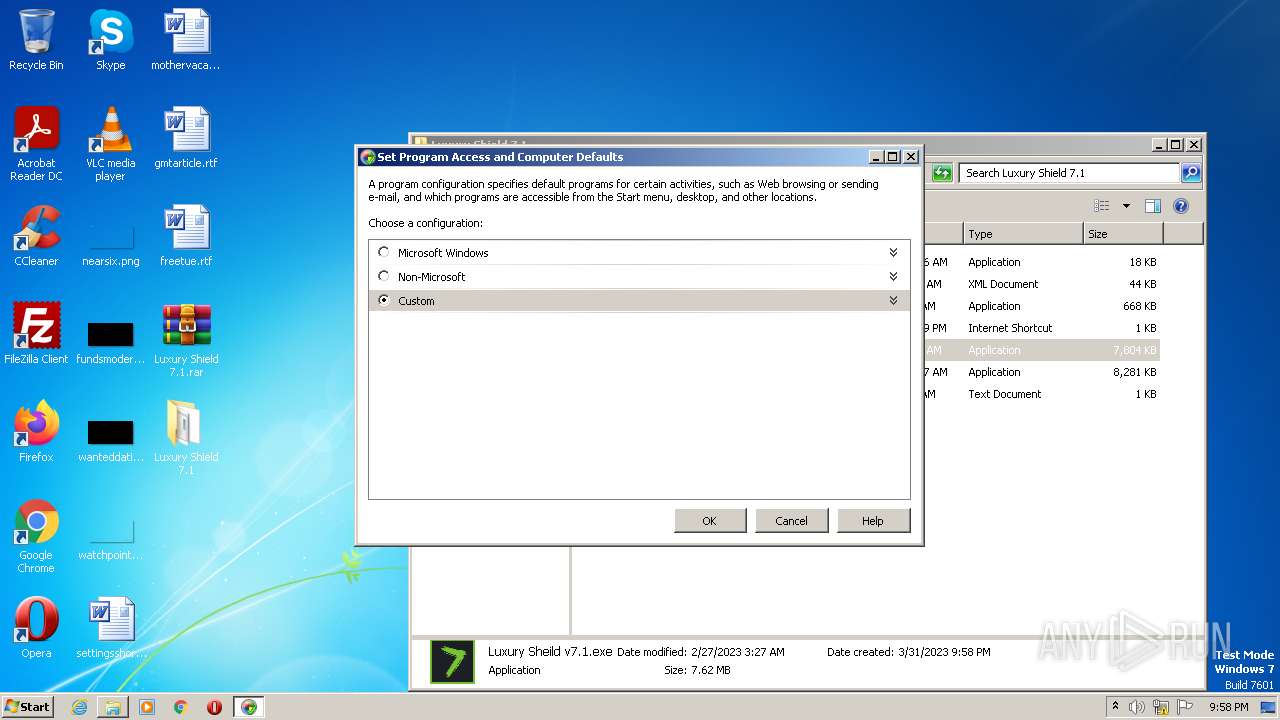
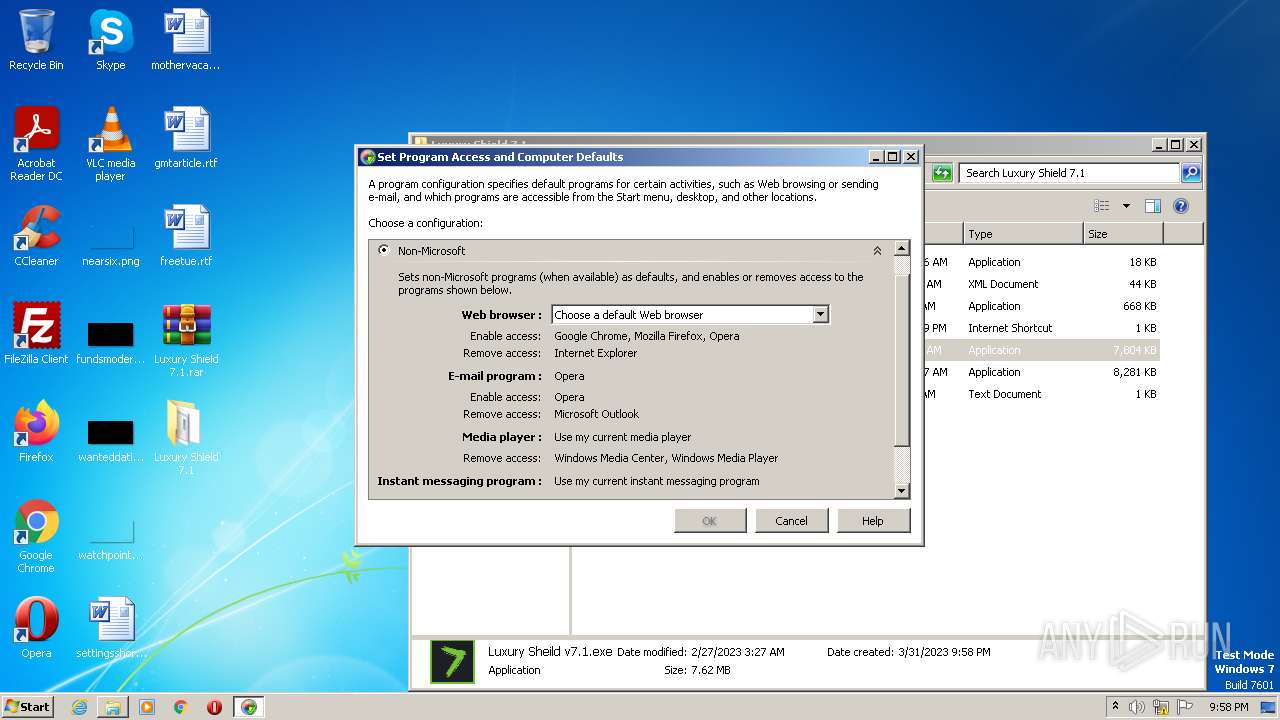
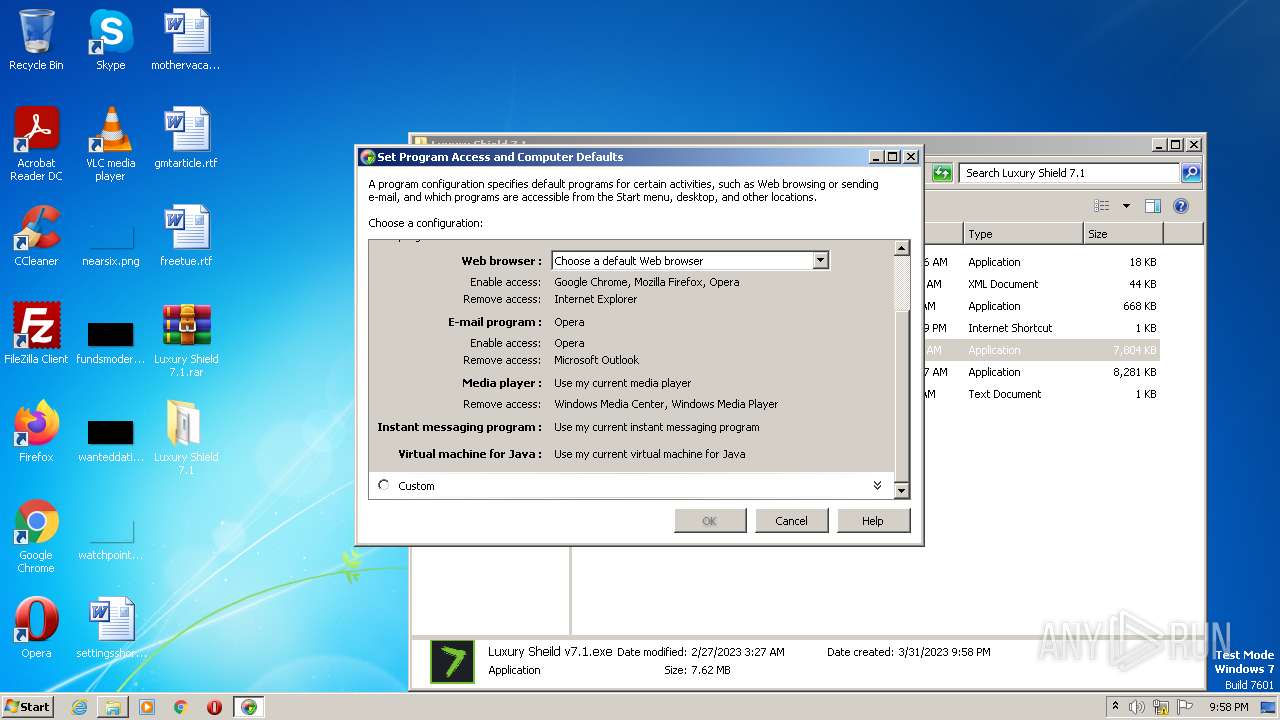
| 1584 | "C:\Windows\system32\ComputerDefaults.exe" | C:\Windows\System32\ComputerDefaults.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Set Program Access and Computer Defaults Control Panel Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\Desktop\Luxury Shield 7.1\Luxury Sheild v7.1.exe" | C:\Users\admin\Desktop\Luxury Shield 7.1\Luxury Sheild v7.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Luxury Shield Exit code: 0 Version: 7.1.0.0 Modules
| |||||||||||||||
| 1868 | "cmd.exe" /c start computerdefaults.exe && powershell.exe Remove-Item -Path HKCU:\Software\Classes\ms-settings\shell -Recurse | C:\Windows\System32\cmd.exe | — | Luxury Sheild v7.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2352 | computerdefaults.exe | C:\Windows\System32\ComputerDefaults.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Set Program Access and Computer Defaults Control Panel Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | "C:\Windows\system32\ComputerDefaults.exe" | C:\Windows\System32\ComputerDefaults.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Set Program Access and Computer Defaults Control Panel Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2668 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Luxury Shield 7.1.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2732 | powershell.exe Remove-Item -Path HKCU:\Software\Classes\ms-settings\shell -Recurse | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2836 | computerdefaults.exe | C:\Windows\System32\ComputerDefaults.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Set Program Access and Computer Defaults Control Panel Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Windows\system32\ComputerDefaults.exe" | C:\Windows\System32\ComputerDefaults.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Set Program Access and Computer Defaults Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Luxury Shield 7.1\Luxury Shield 7.1.exe" "C:\Users\admin\Desktop\Luxury Shield 7.1\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 884
Read events
4 784
Write events
88
Delete events
12
Modification events
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
8
Suspicious files
8
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
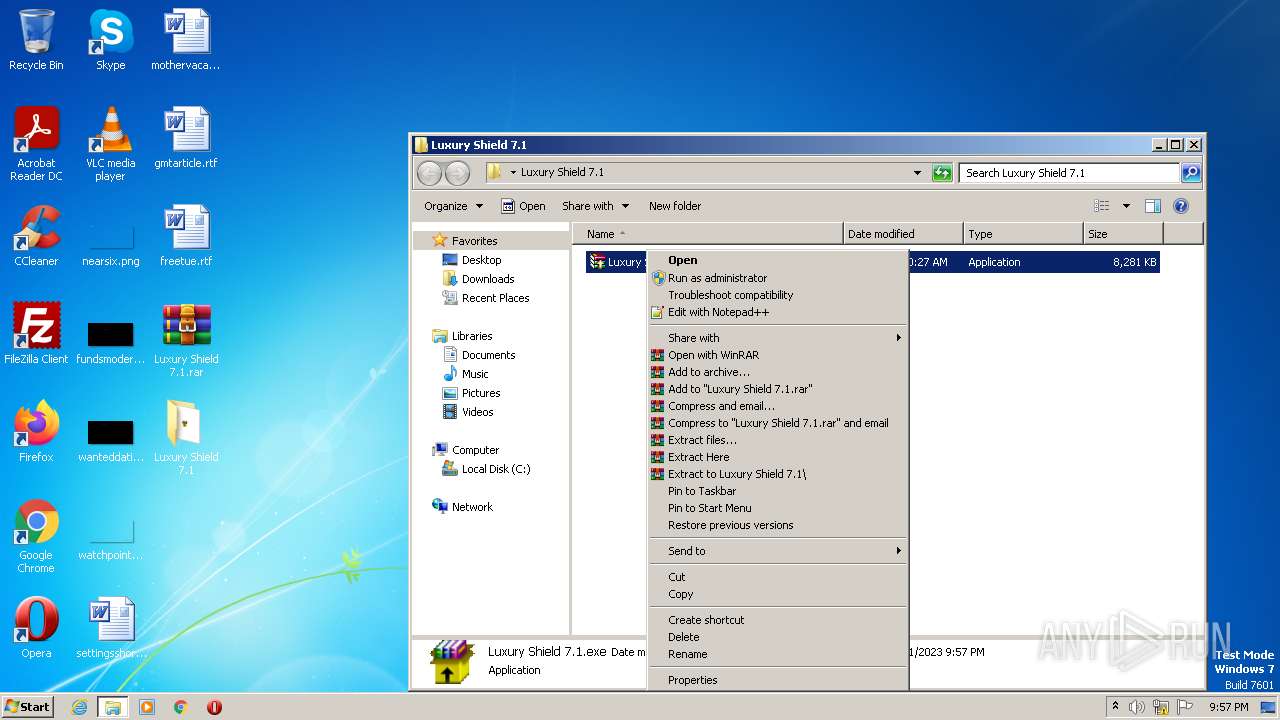
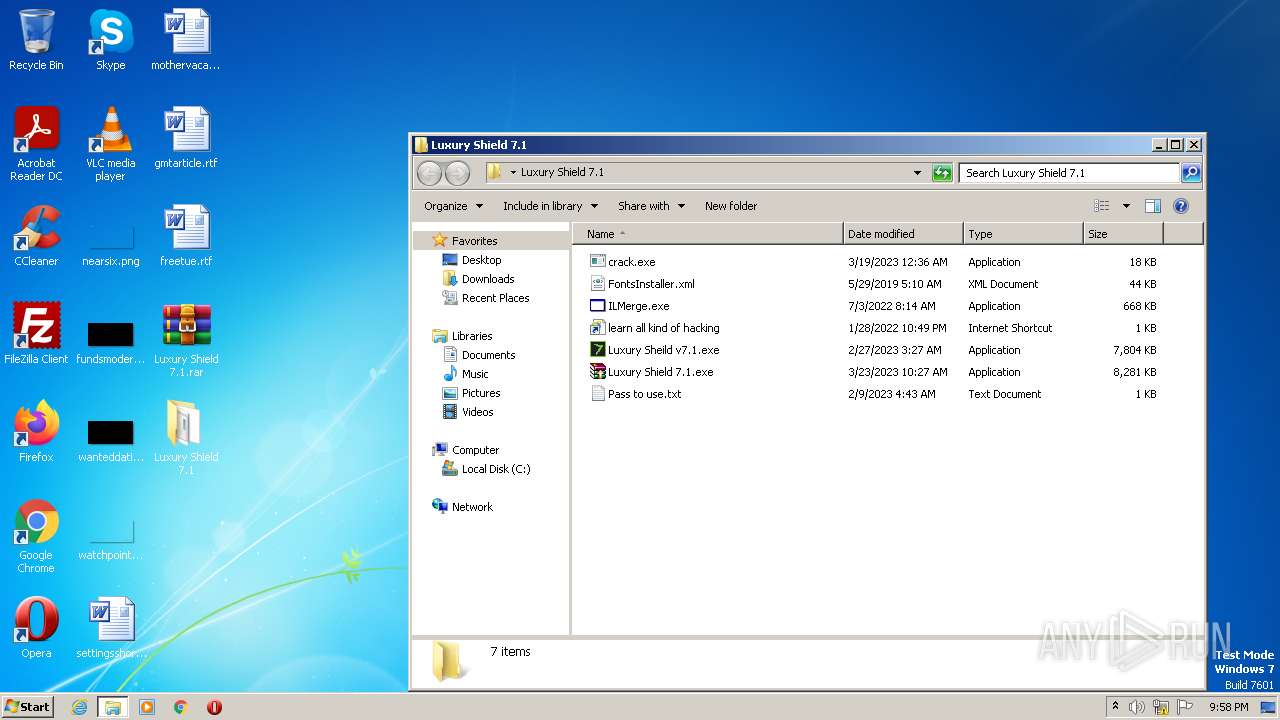
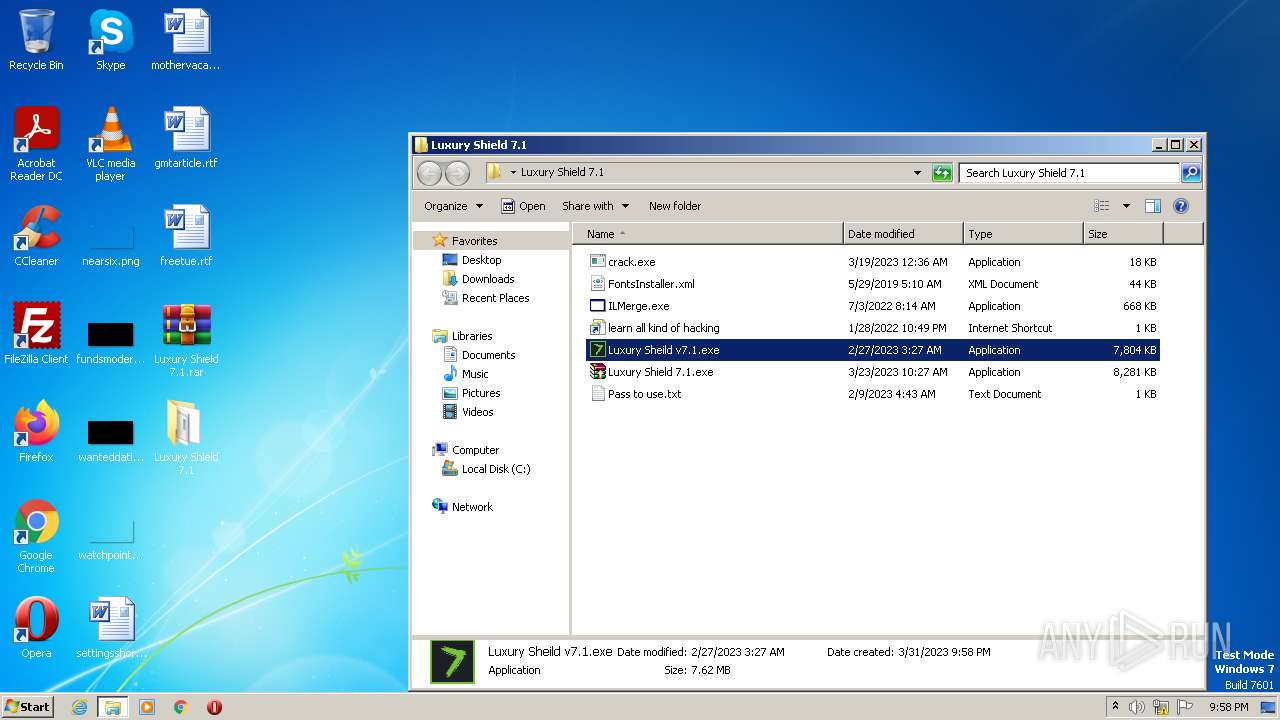
| 2668 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\Luxury Shield 7.1.exe | executable | |
MD5:E484D9F831BAE0A774F3AC0FCFF44512 | SHA256:CDB6B34EB4090B0BE2B503767A8463741BC17B5CAC2D2E22CAF52AA1676616A7 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\ILMerge.exe | executable | |
MD5:2BB6322885E6CA0986206DE174E842C9 | SHA256:8110D740B485BCB06FF406B17001714C3A146FE6517098C9DC90D812B83389FD | |||
| 3140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\elttshrs.gcq.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\Pass to use.txt | text | |
MD5:F2B0D578A79AC19B492E04BC5A7050F7 | SHA256:78F53709CCE69E858FBB201BE13803E63D7E0AA84D7CABE1353CE4989C68EEC7 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\Luxury Sheild v7.1.exe | executable | |
MD5:F145671C3C65072A5A49F1D1D68A4A3A | SHA256:D5DCDE7CED43245641793538F847C55E3271F5FF8EB45FA5616A00634B7E64A1 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\FontsInstaller.xml | xml | |
MD5:531F8BE30CBBCE50349DE56644C66E34 | SHA256:089C9B63CFED530C5BD6D492954D602F7FB94E34B8FAA72DB8A9E442B428FEC9 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\crack.exe | executable | |
MD5:B441B71B1CE23257D6F40BD7555703AC | SHA256:EEAACD0B7E68CC5E5A183DC5F6E8B489CF267A73EBD772B338873F9E04E2B7A4 | |||
| 2952 | WinRAR.exe | C:\Users\admin\Desktop\Luxury Shield 7.1\learn all kind of hacking.url | url | |
MD5:7ADE4A739CBD8F44D0EF52A2F1BC6E7B | SHA256:CC7649ED53C65E4851ACE414529564FE16801BB2BED4CB15588BFD6B4AC13616 | |||
| 3140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wum0hom0.j4u.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3140 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report