| URL: | http://brazzers.bar/ |
| Full analysis: | https://app.any.run/tasks/429b8d1f-904e-4564-bb8a-5ad11663ef33 |
| Verdict: | No threats detected |
| Analysis date: | April 23, 2020, 14:02:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E5BC1B090089250E89F051D5C25D4ED2 |
| SHA1: | 8AE6962263CB98E1F7E96D320B37016DC68D0474 |
| SHA256: | 65EC5241F3A39225C962551F756CDEA5B6320C1DA24A0C2E8B9C44DAC0BEEEB9 |
| SSDEEP: | 3:N1Kc6kan:Ccla |
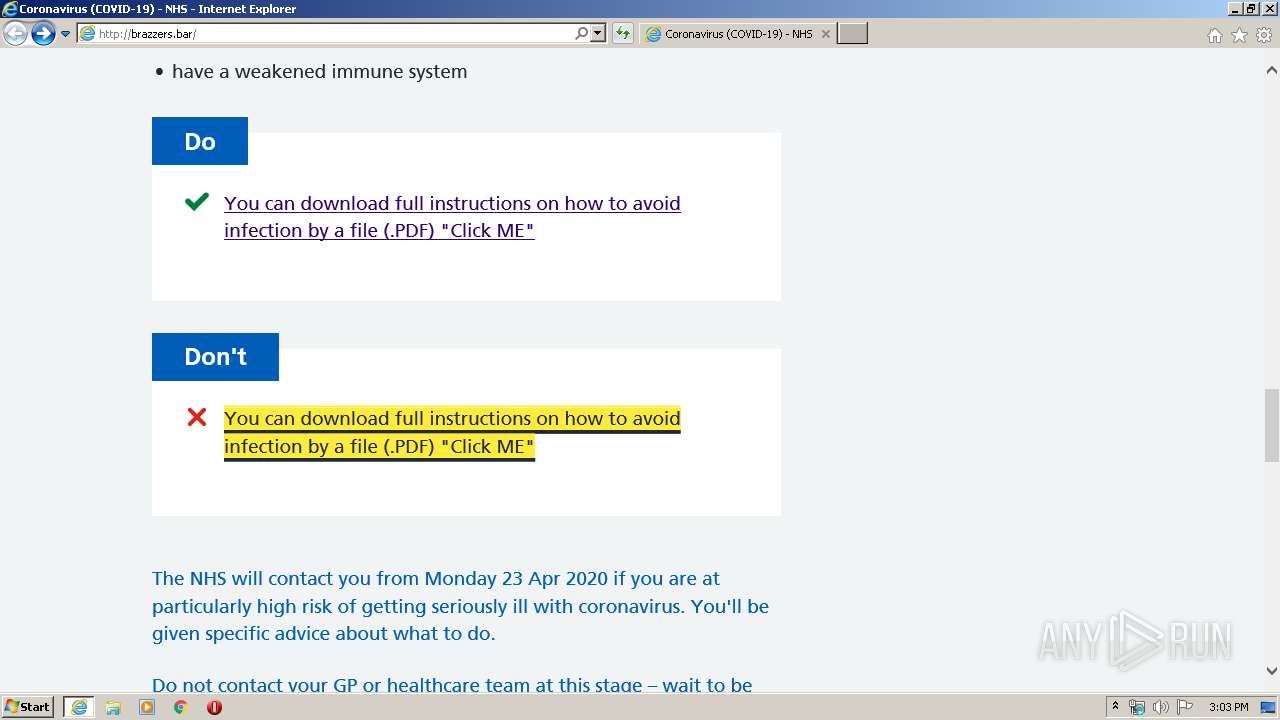
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3300)
Changes internet zones settings
- iexplore.exe (PID: 3300)
Application launched itself
- iexplore.exe (PID: 3300)
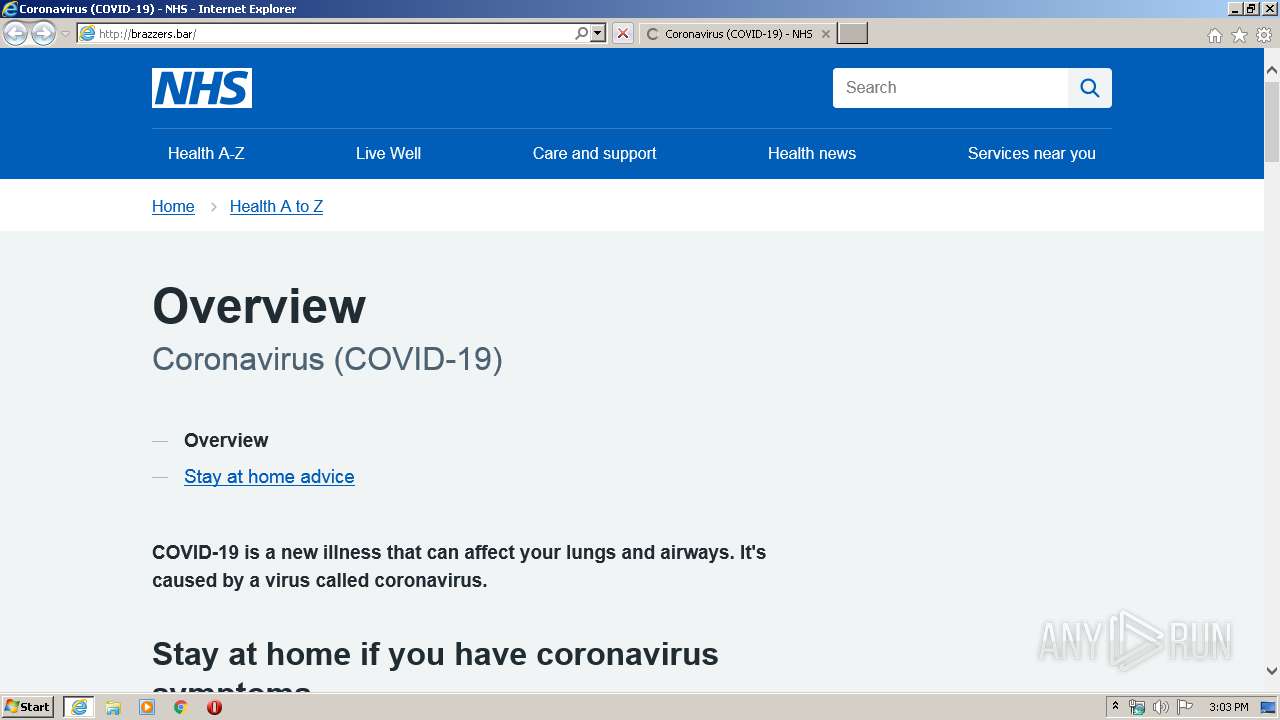
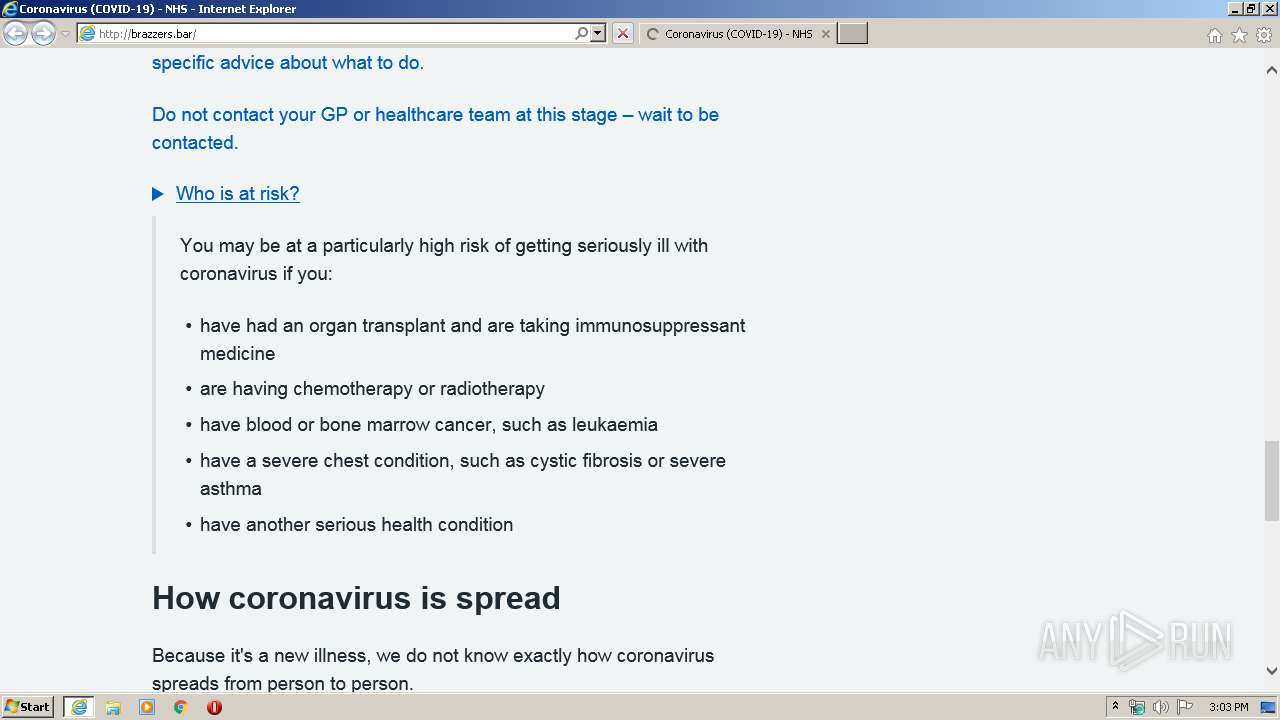
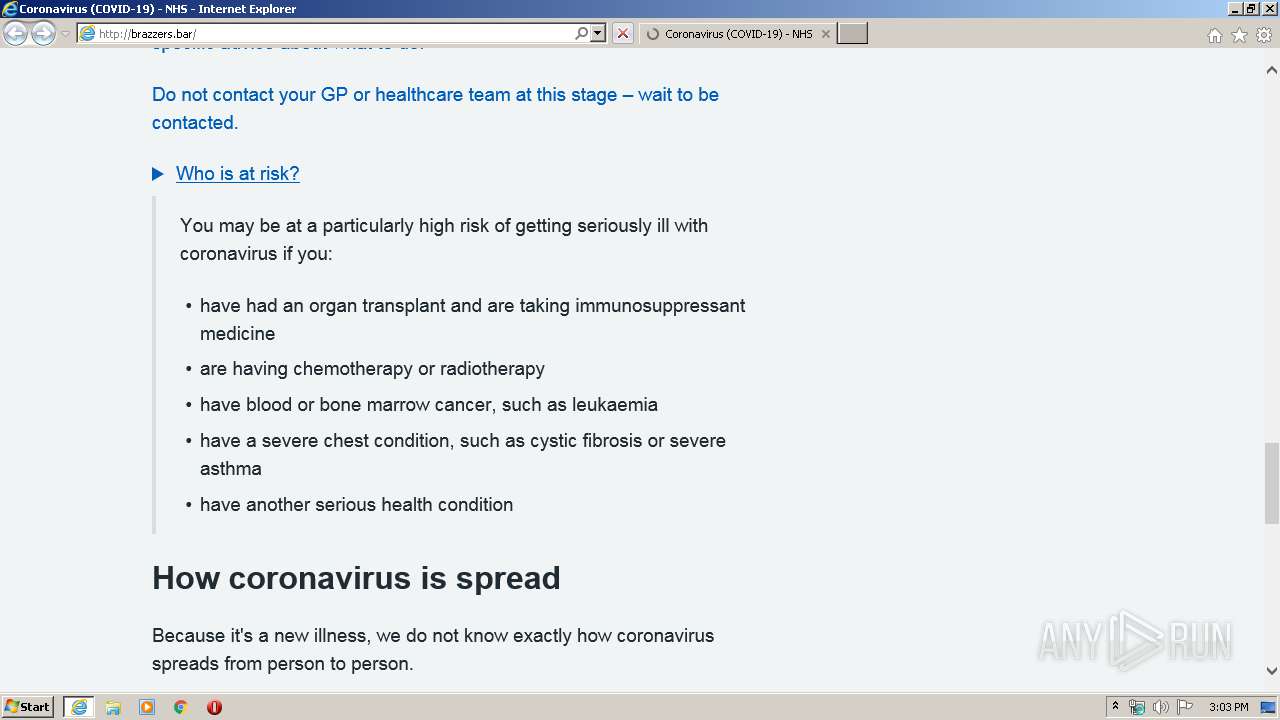
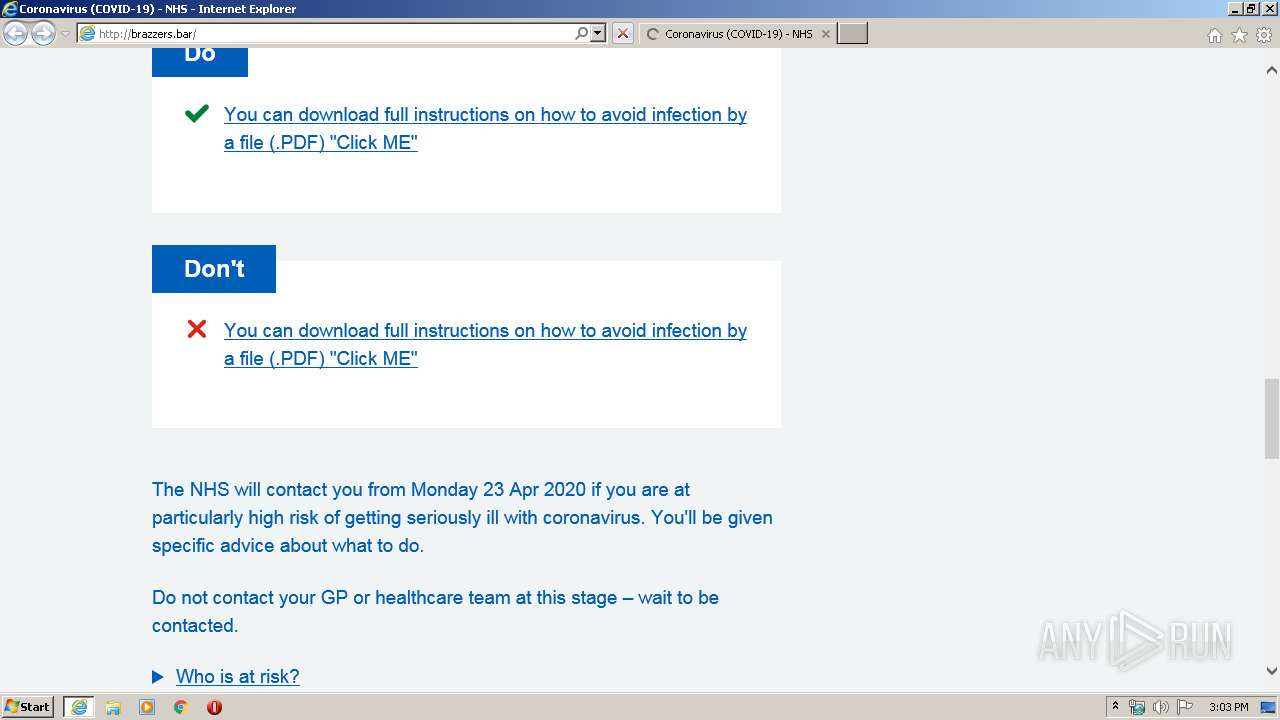
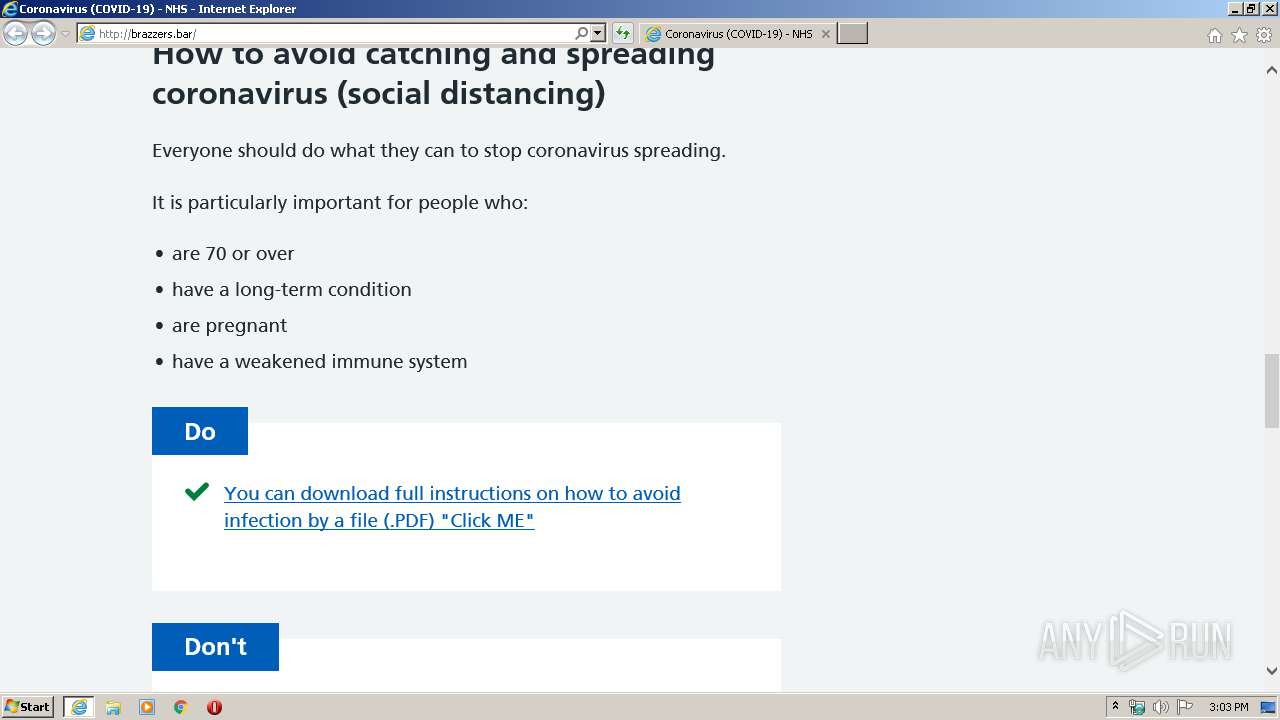
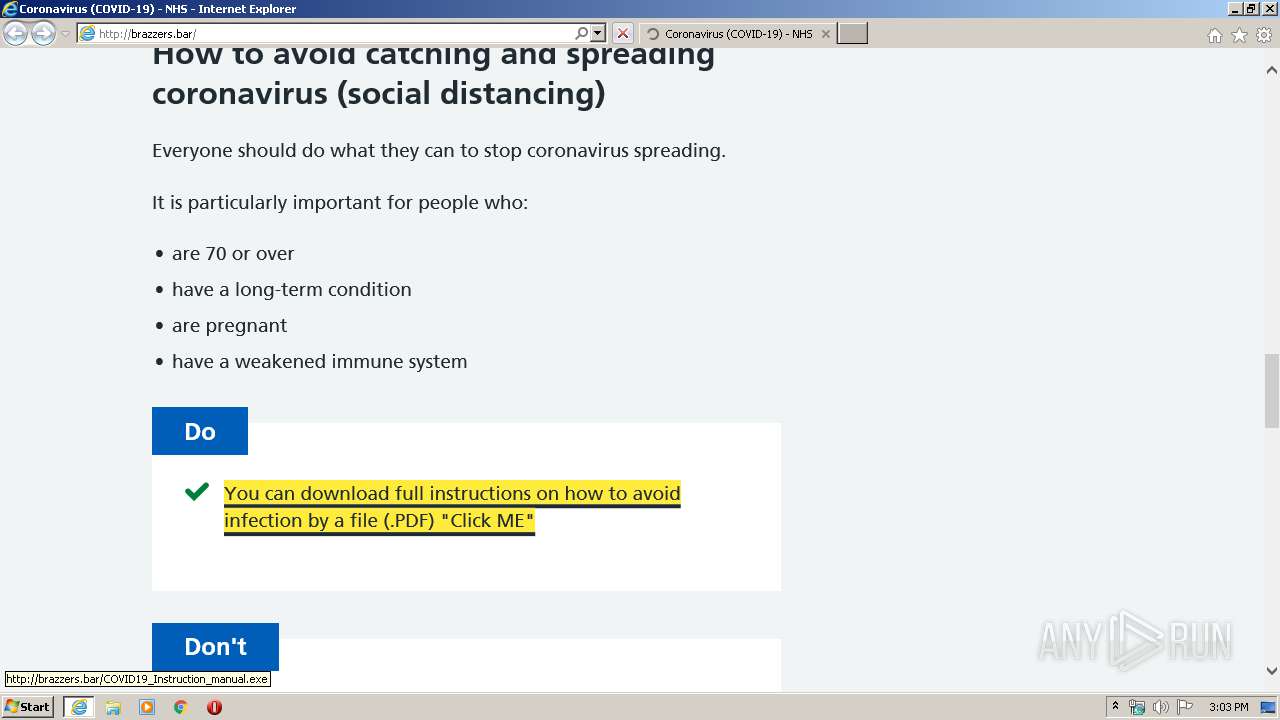
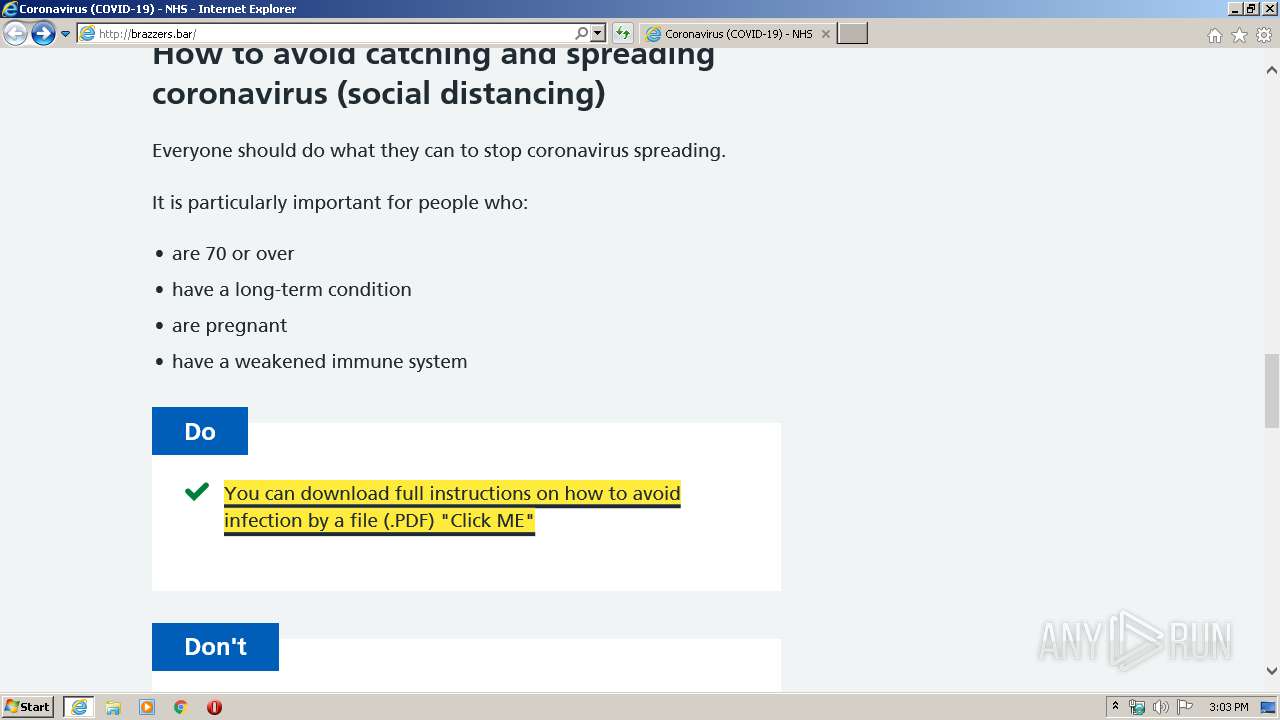
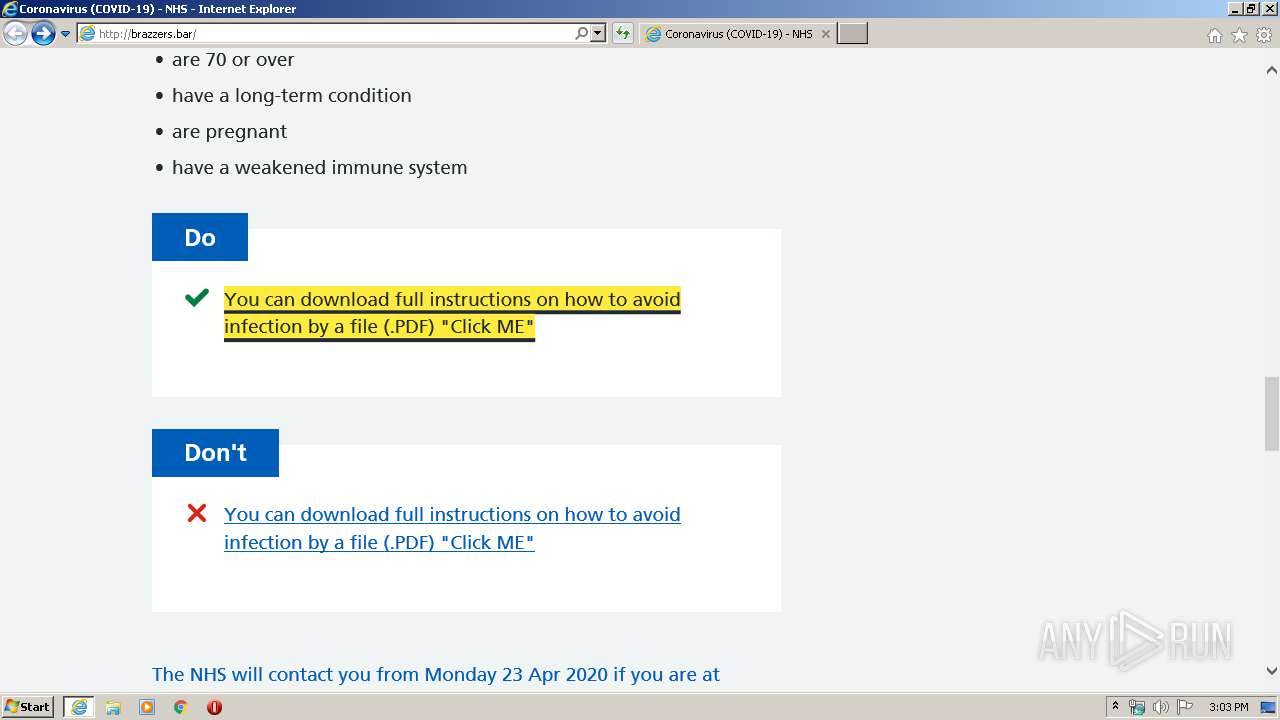
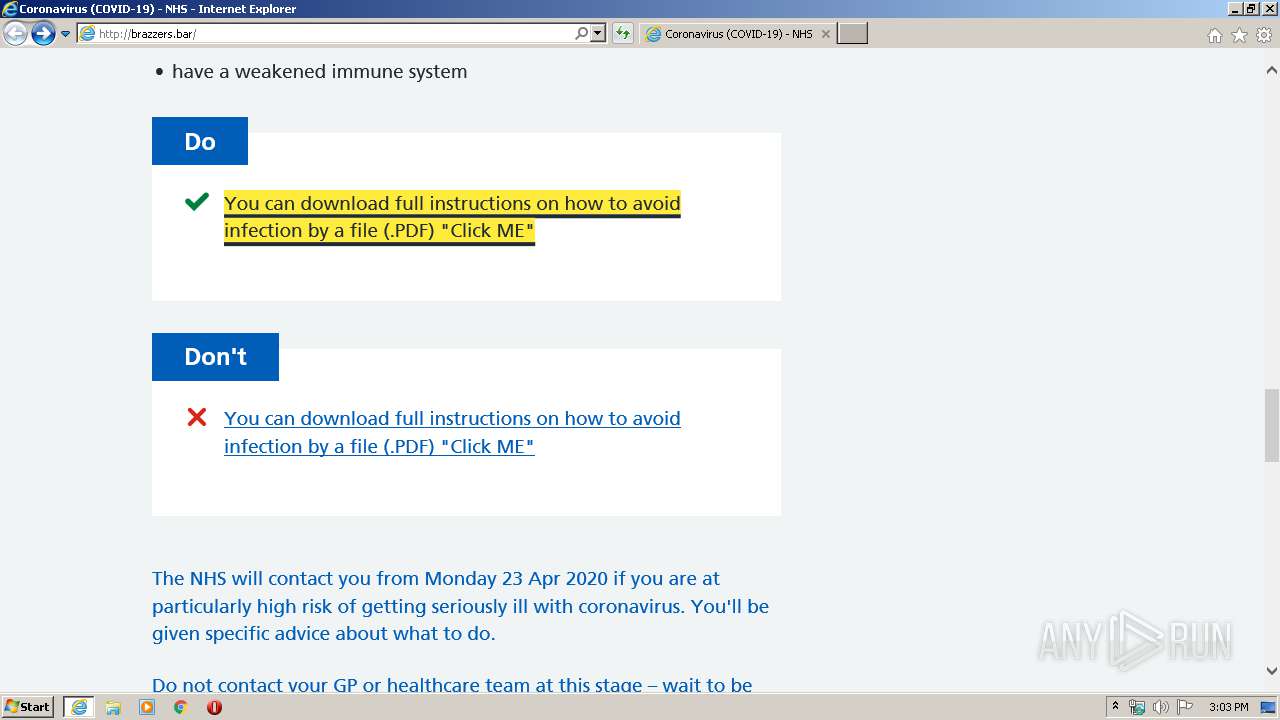
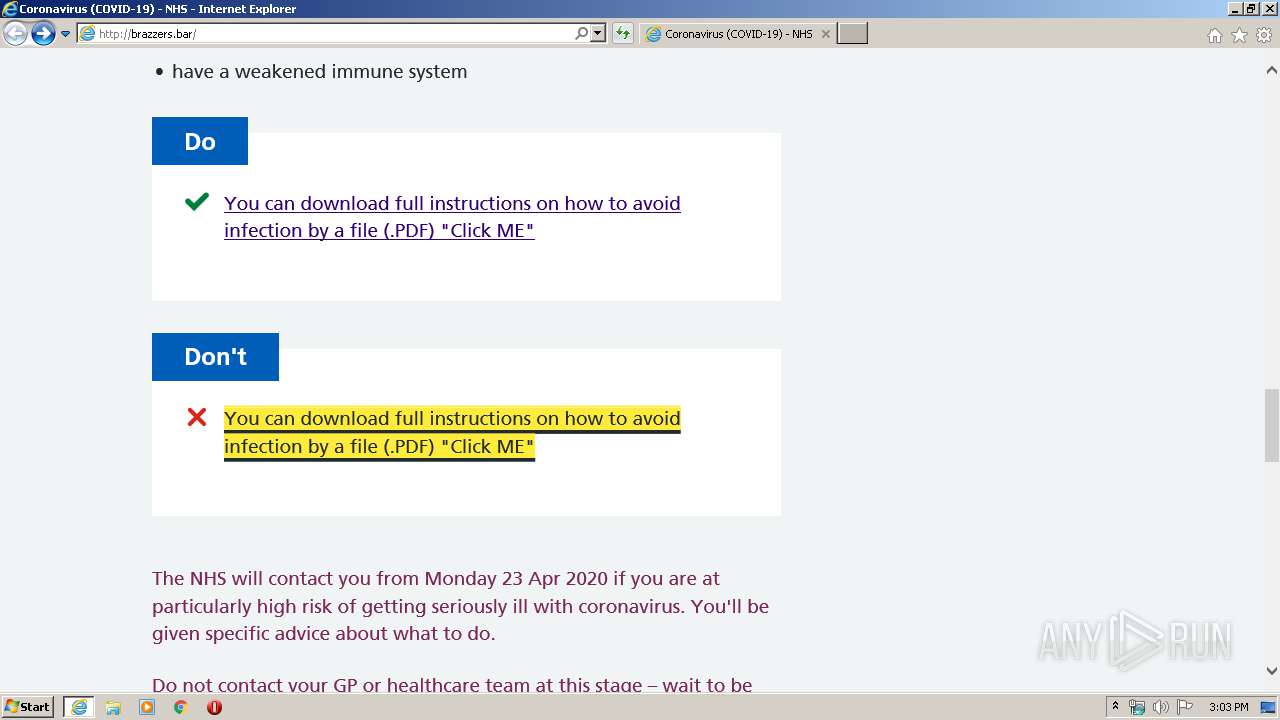
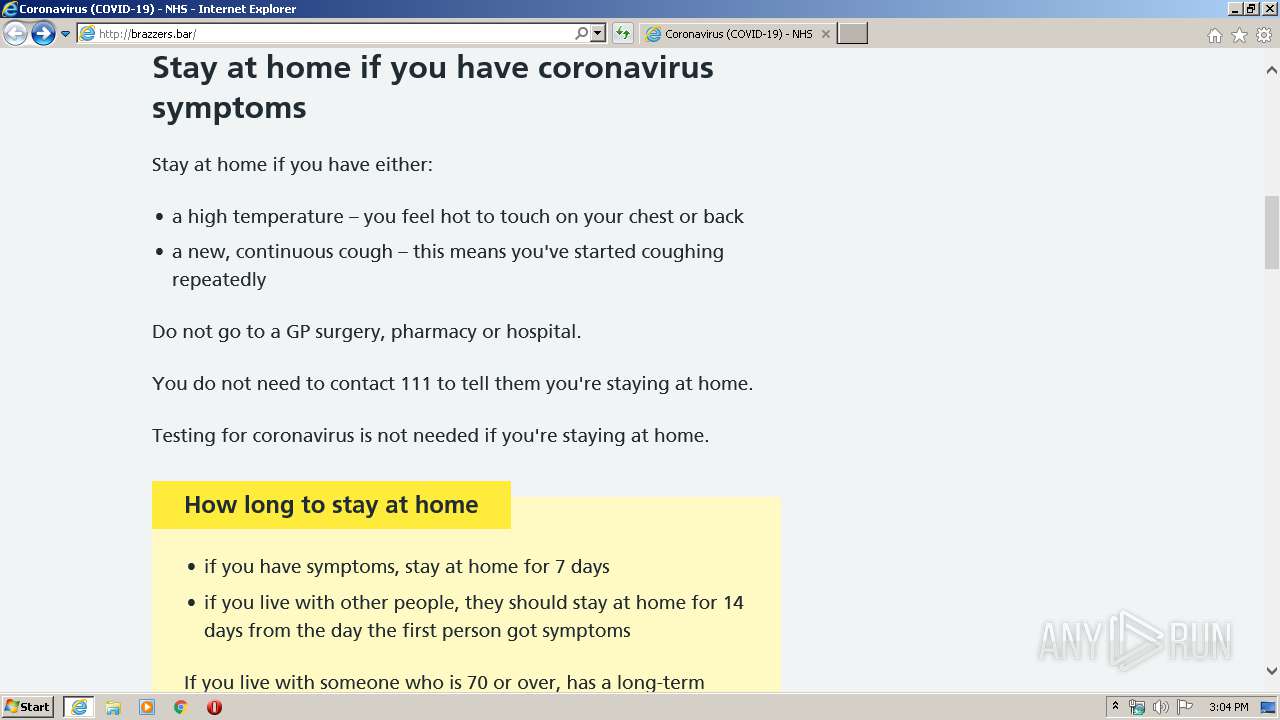
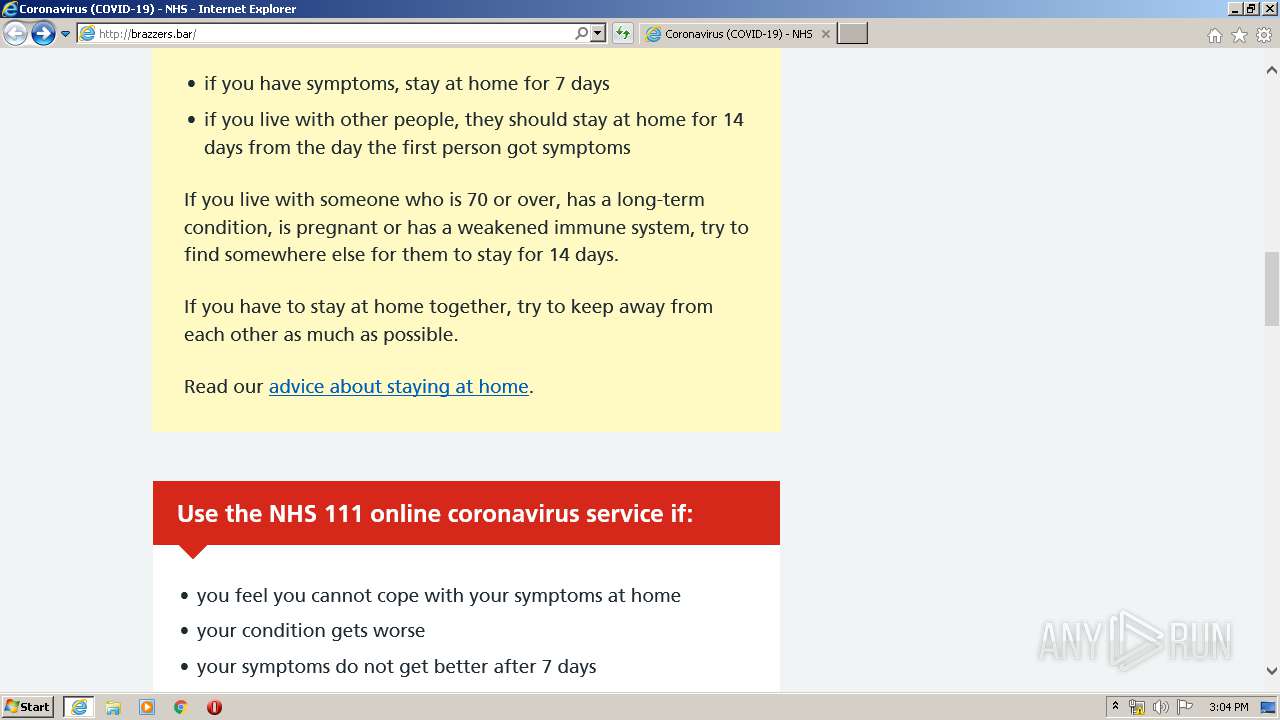
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 3340)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
Reads settings of System Certificates
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3340)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3300)
Changes settings of System certificates
- iexplore.exe (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3300 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://brazzers.bar/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3300 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 058
Read events
454
Write events
3 082
Delete events
1 522
Modification events
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4260046556 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30808439 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
13
Text files
34
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2416.tmp | — | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2417.tmp | — | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\launch-ENe7f6cdd7cc05409b86547d9153429788.min.js[1].js | text | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\main.06fd46dc643d[1].css | text | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\cookie-consent.js[1].js | text | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\3PLWVN89.htm | html | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jquery-3.4.1.min.220afd743d9e.js[1].js | text | |
MD5:220AFD743D9E9643852E31A135A9F3AE | SHA256:0925E8AD7BD971391A8B1E98BE8E87A6971919EB5B60C196485941C3C1DF089A | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\translateelement[1].css | text | |
MD5:DBC4C9FA52A475411EB75595DA532797 | SHA256:6149F95C1EBDDE5391898E22A79821A810336F6BD74318291B4F49F23FBF0FA8 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
32
DNS requests
47
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3340 | iexplore.exe | GET | 200 | 195.2.92.82:80 | http://brazzers.bar/index_files/main.06fd46dc643d.css | RU | text | 17.4 Kb | suspicious |
3340 | iexplore.exe | GET | 200 | 195.2.92.82:80 | http://brazzers.bar/index_files/cookie-consent.js.download | RU | text | 33.7 Kb | suspicious |
3340 | iexplore.exe | GET | 200 | 195.2.92.82:80 | http://brazzers.bar/ | RU | html | 10.9 Kb | suspicious |
3340 | iexplore.exe | GET | 200 | 195.2.92.82:80 | http://brazzers.bar/index_files/launch-ENe7f6cdd7cc05409b86547d9153429788.min.js.download | RU | text | 46.3 Kb | suspicious |
3340 | iexplore.exe | GET | 200 | 195.2.92.82:80 | http://brazzers.bar/index_files/main.b3221de0baf1.js.download | RU | text | 16.4 Kb | suspicious |
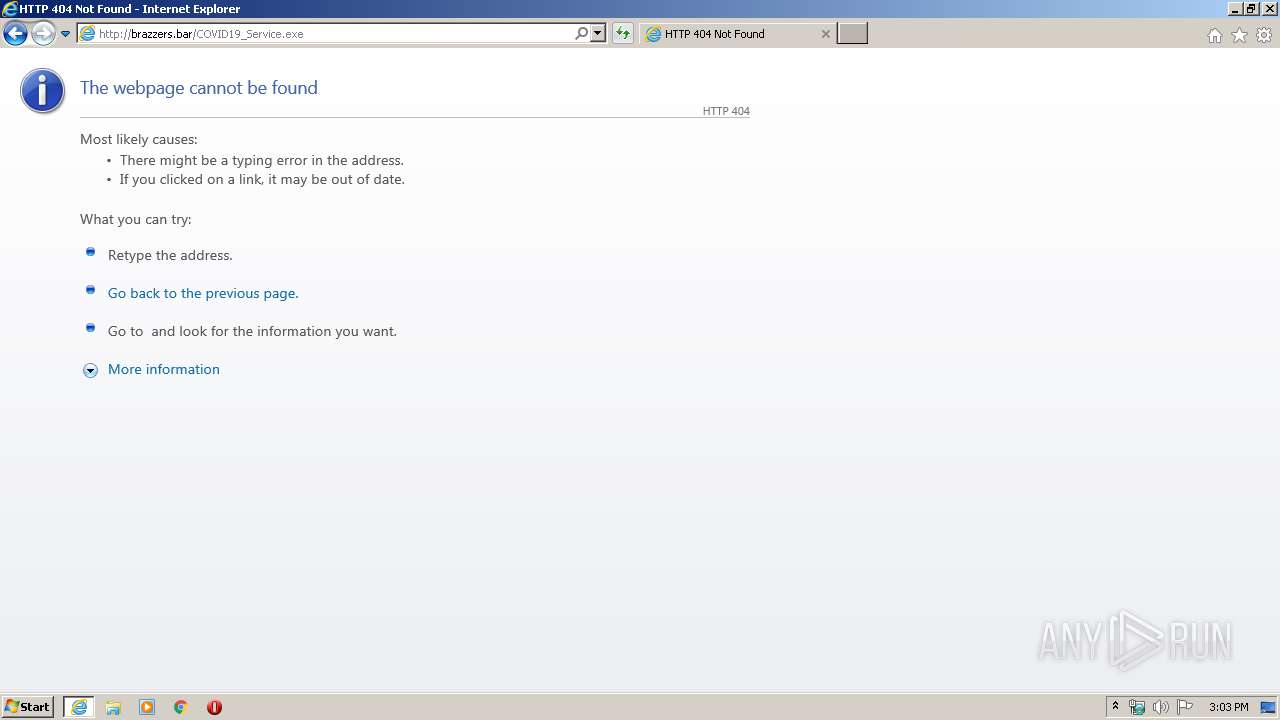
3340 | iexplore.exe | GET | 404 | 195.2.92.82:80 | http://brazzers.bar/externalservices/surveyfeedapi/api/bannerfeed | RU | html | 274 b | suspicious |
3340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
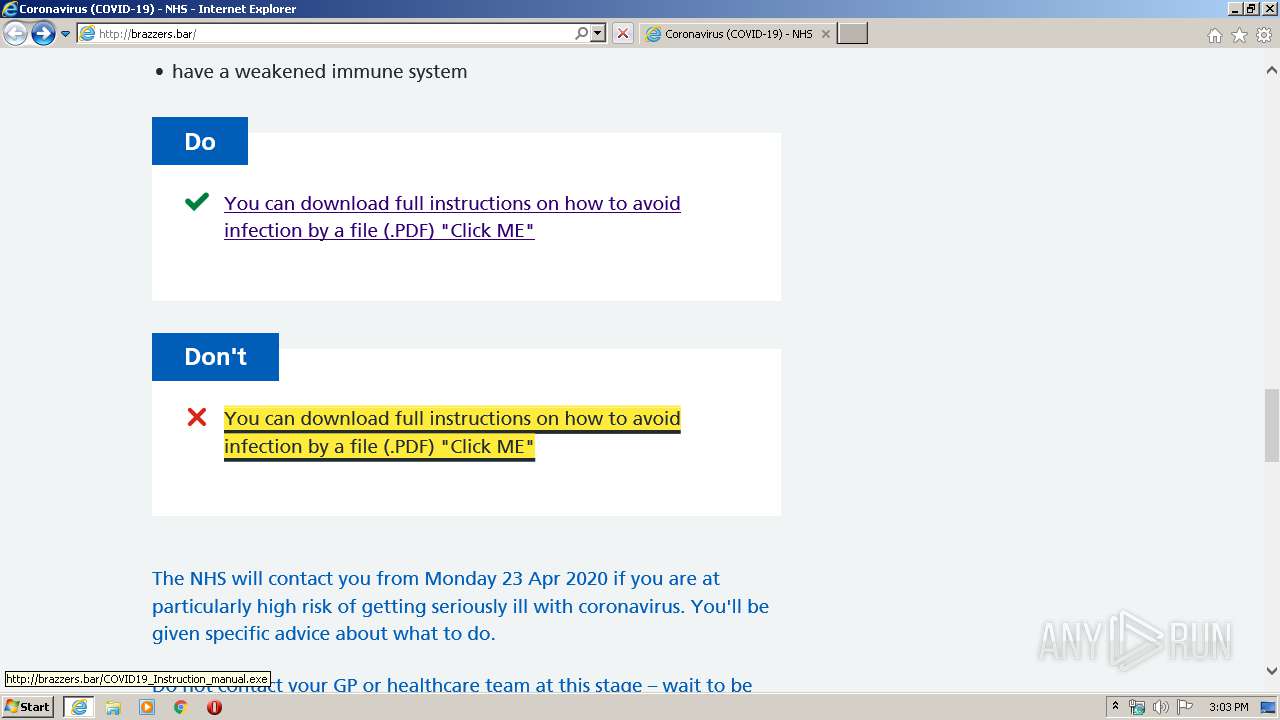
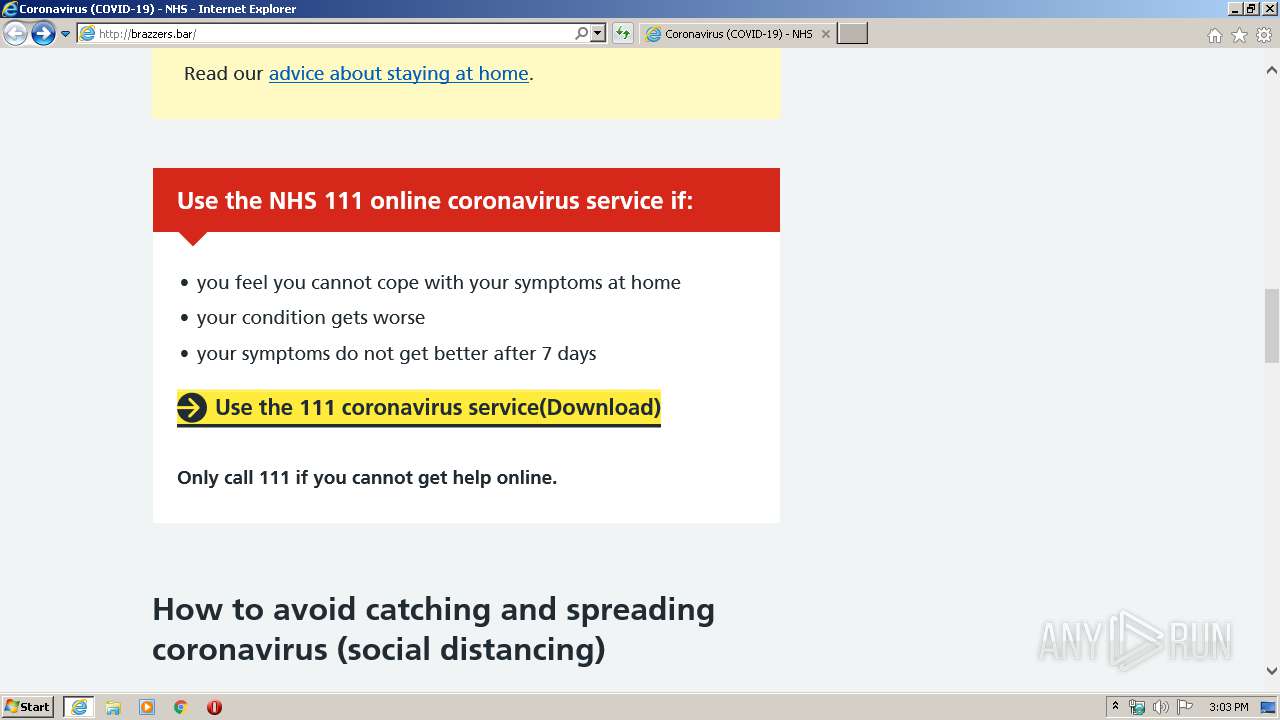
3340 | iexplore.exe | GET | 404 | 195.2.92.82:80 | http://brazzers.bar/COVID19_Instruction_manual.exe | RU | html | 274 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3340 | iexplore.exe | 195.2.92.82:80 | brazzers.bar | Zenon N.S.P. | RU | suspicious |
3300 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3340 | iexplore.exe | 23.198.77.215:443 | assets.nhs.uk | Akamai Technologies, Inc. | NL | unknown |
3340 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 172.217.17.131:80 | www.gstatic.com | Google Inc. | US | whitelisted |
3340 | iexplore.exe | 104.92.75.187:443 | www.nhs.uk | Akamai Technologies, Inc. | NL | unknown |
3300 | iexplore.exe | 104.92.75.187:443 | www.nhs.uk | Akamai Technologies, Inc. | NL | unknown |
— | — | 104.92.75.187:443 | www.nhs.uk | Akamai Technologies, Inc. | NL | unknown |
— | — | 195.2.92.82:80 | brazzers.bar | Zenon N.S.P. | RU | suspicious |
3300 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
brazzers.bar |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
assets.nhs.uk |
| suspicious |
www.gstatic.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.nhs.uk |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3340 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3340 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3340 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |