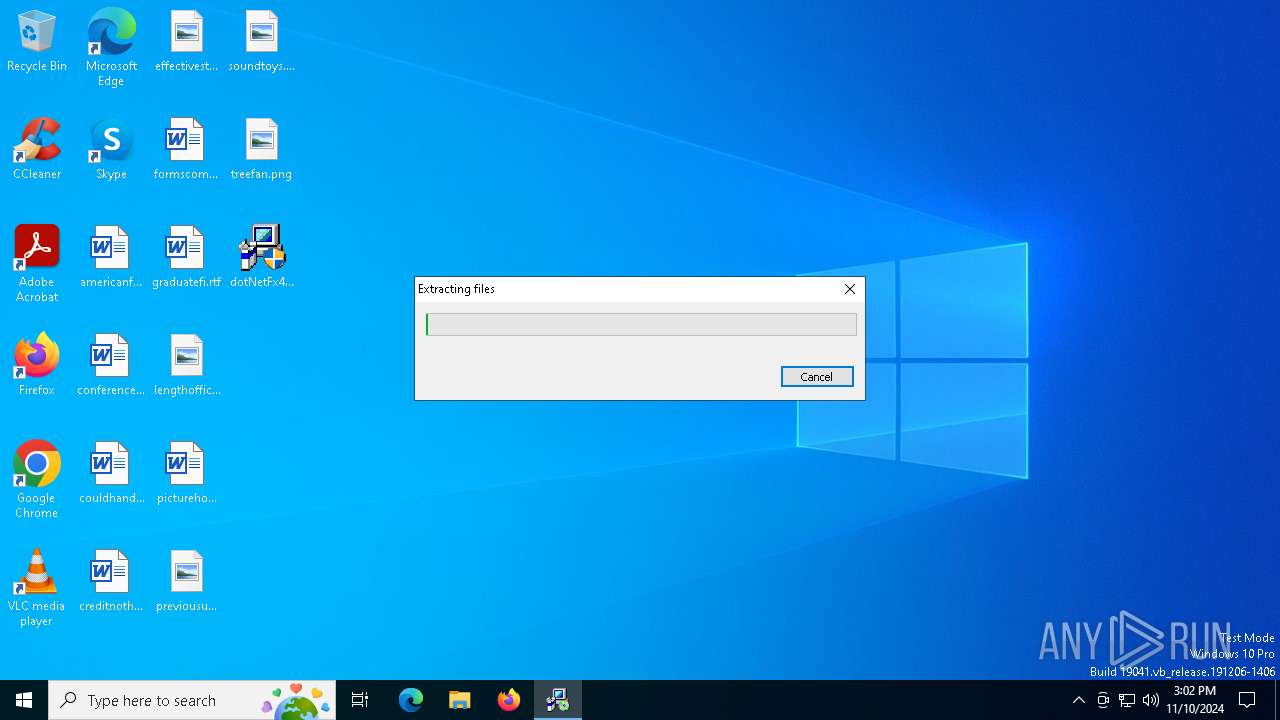
| File name: | dotNetFx40_Full_x86_x64.exe |
| Full analysis: | https://app.any.run/tasks/86da466e-7505-4b53-b2c8-e81980b7ca2b |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2024, 15:02:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 251743DFD3FDA414570524BAC9E55381 |
| SHA1: | 58DA3D74DB353AAD03588CBB5CEA8234166D8B99 |
| SHA256: | 65E064258F2E418816B304F646FF9E87AF101E4C9552AB064BB74D281C38659F |
| SSDEEP: | 1572864:cAVBjIQSzQe3cf7xOCHKYrLn+XxdjrALIjOqWY99v:VVBIbzQe3u7KYrCDS9299v |
MALICIOUS
No malicious indicators.SUSPICIOUS
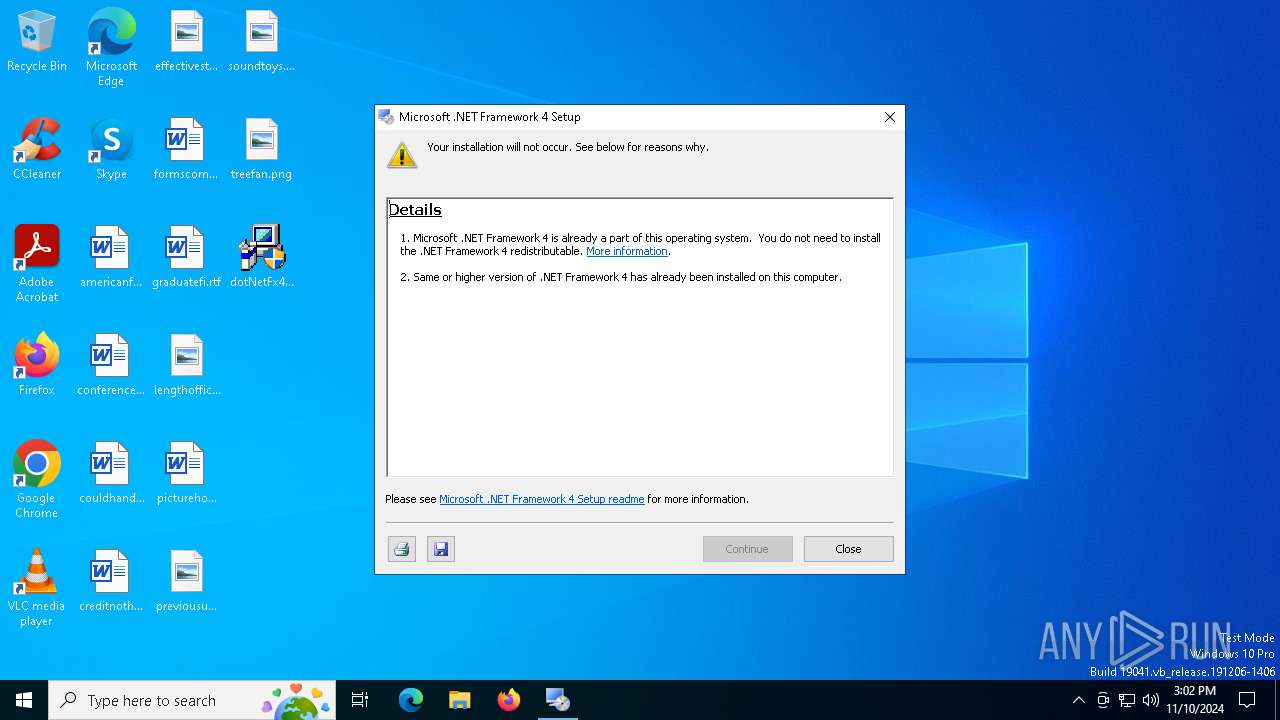
Starts a Microsoft application from unusual location
- dotNetFx40_Full_x86_x64.exe (PID: 4224)
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
Creates file in the systems drive root
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
Process drops legitimate windows executable
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
Executable content was dropped or overwritten
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
INFO
Reads the computer name
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
- Setup.exe (PID: 7084)
Reads the machine GUID from the registry
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
Create files in a temporary directory
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
- Setup.exe (PID: 7084)
Checks supported languages
- dotNetFx40_Full_x86_x64.exe (PID: 6208)
- Setup.exe (PID: 7084)
Reads CPU info
- Setup.exe (PID: 7084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:10:09 19:27:34+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 165376 |
| InitializedDataSize: | 24064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x191c6 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.30319.1 |
| ProductVersionNumber: | 4.0.30319.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft .NET Framework 4 Setup |
| FileVersion: | 4.0.30319.01 |
| InternalName: | dotNetFx40_Full_x86_x64.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | dotNetFx40_Full_x86_x64.exe |
| ProductName: | Microsoft .NET Framework 4 |
| ProductVersion: | 4.0.30319.01 |
Total processes
115
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4224 | "C:\Users\admin\Desktop\dotNetFx40_Full_x86_x64.exe" | C:\Users\admin\Desktop\dotNetFx40_Full_x86_x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4 Setup Exit code: 3221226540 Version: 4.0.30319.01 Modules
| |||||||||||||||
| 6208 | "C:\Users\admin\Desktop\dotNetFx40_Full_x86_x64.exe" | C:\Users\admin\Desktop\dotNetFx40_Full_x86_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4 Setup Version: 4.0.30319.01 Modules
| |||||||||||||||
| 7084 | C:\c9917c6ccf672f313689\\Setup.exe /x86 /x64 | C:\c9917c6ccf672f313689\Setup.exe | — | dotNetFx40_Full_x86_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
Total events
139
Read events
139
Write events
0
Delete events
0
Modification events
Executable files
36
Suspicious files
2
Text files
81
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\RGB9RAST_x64.msi | executable | |
MD5:4C424650C4187ADDA4C24F946099B437 | SHA256:9B4C00CA561FF1DEBA57C34FEF5C8610708E78774C2207411C593109C046FB3F | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\netfx_Core_x86.msi | executable | |
MD5:50D6022791EFDE93CAFD864014DED84C | SHA256:BC7B6B32157ED65023BB251E177F78480490EC1FA53EB54EC4441E8A44F33F36 | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\netfx_Extended_x86.msi | executable | |
MD5:A9EB4FCEFB05A5054009919042482AEC | SHA256:AFF90540E38BA99EFC5CA086F84C9F3C54754D5C6C2AC0F953D7316FAE59432D | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\netfx_Extended_x64.msi | executable | |
MD5:EADB43461CA9172AAA530AEC509C4082 | SHA256:070CEA34E4D275393DB78AB7683819DA98F59911B6436CC1DA34F50A37E610C8 | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\RGB9Rast_x86.msi | executable | |
MD5:674353068D0290B0884B35B3B925DFE2 | SHA256:62F384BF20E669180CBB45EFC0E9E3EE59FE18E58DE75DEB8FDCFD3DD9AC7073 | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\Graphics\Rotate3.ico | image | |
MD5:924FD539523541D42DAD43290E6C0DB5 | SHA256:02A7FE932029C6FA24D1C7CC06D08A27E84F43A0CBC47B7C43CAC59424B3D1F6 | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\Graphics\Rotate5.ico | image | |
MD5:3B4861F93B465D724C60670B64FCCFCF | SHA256:7237051D9AF5DB972A1FECF0B35CD8E9021471740782B0DBF60D3801DC9F5F75 | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\Graphics\Rotate1.ico | image | |
MD5:26A00597735C5F504CF8B3E7E9A7A4C1 | SHA256:37026C4EA2182D7908B3CF0CEF8A6F72BDDCA5F1CFBC702F35B569AD689CF0AF | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\SplashScreen.bmp | image | |
MD5:0966FCD5A4AB0DDF71F46C01EFF3CDD5 | SHA256:31C13ECFC0EB27F34036FB65CC0E735CD444EEC75376EEA2642F926AC162DCB3 | |||
| 6208 | dotNetFx40_Full_x86_x64.exe | C:\c9917c6ccf672f313689\Graphics\Rotate4.ico | image | |
MD5:BB55B5086A9DA3097FB216C065D15709 | SHA256:8D82FF7970C9A67DA8134686560FE3A6C986A160CED9D1CC1392F2BA75C698AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6944 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |