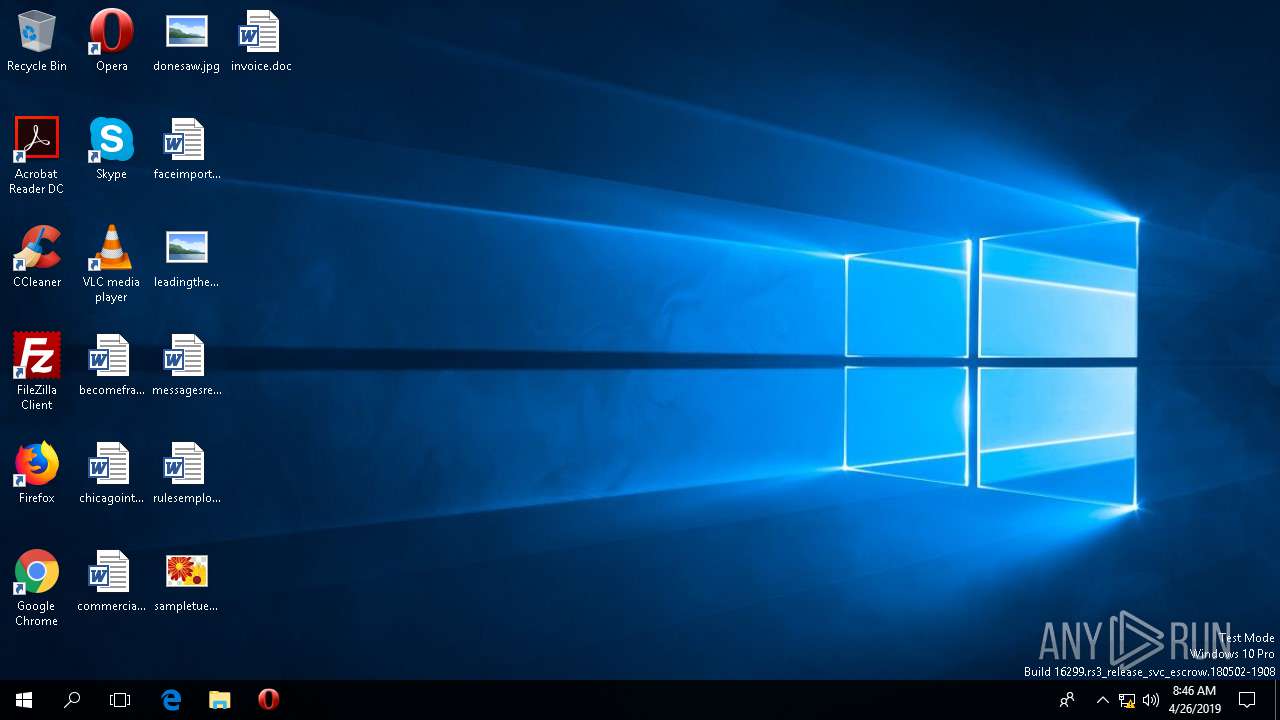
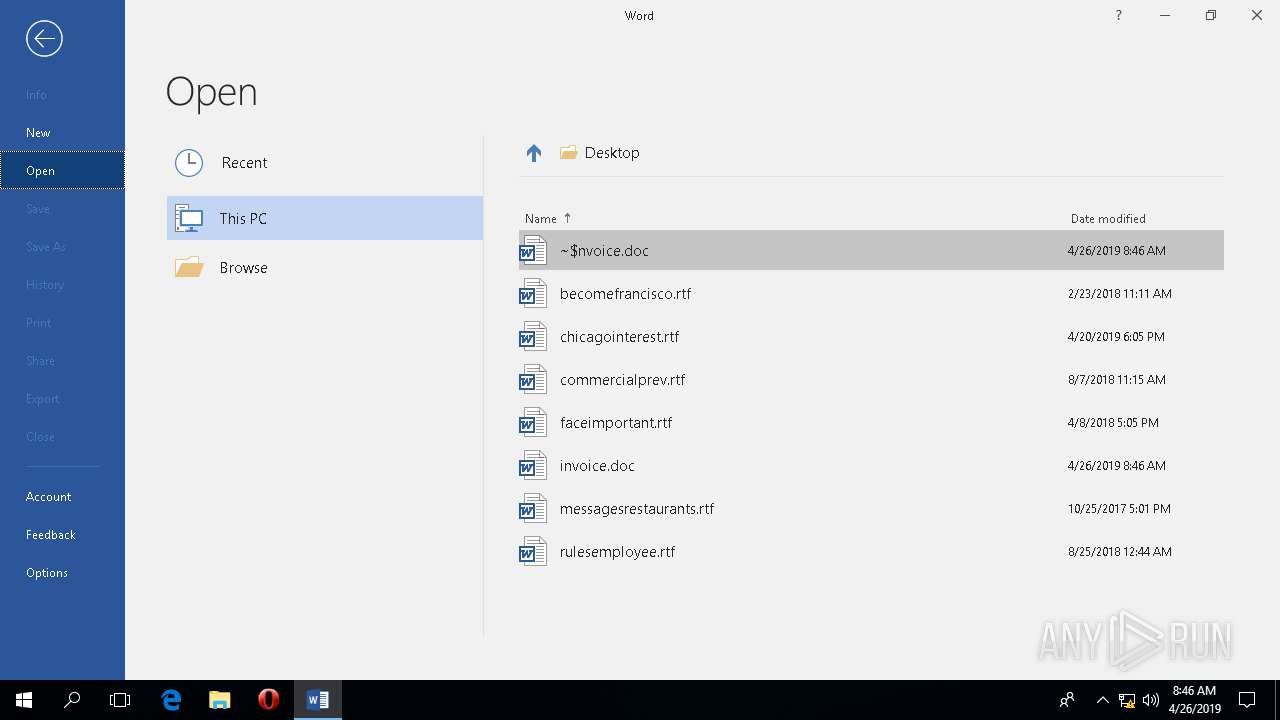
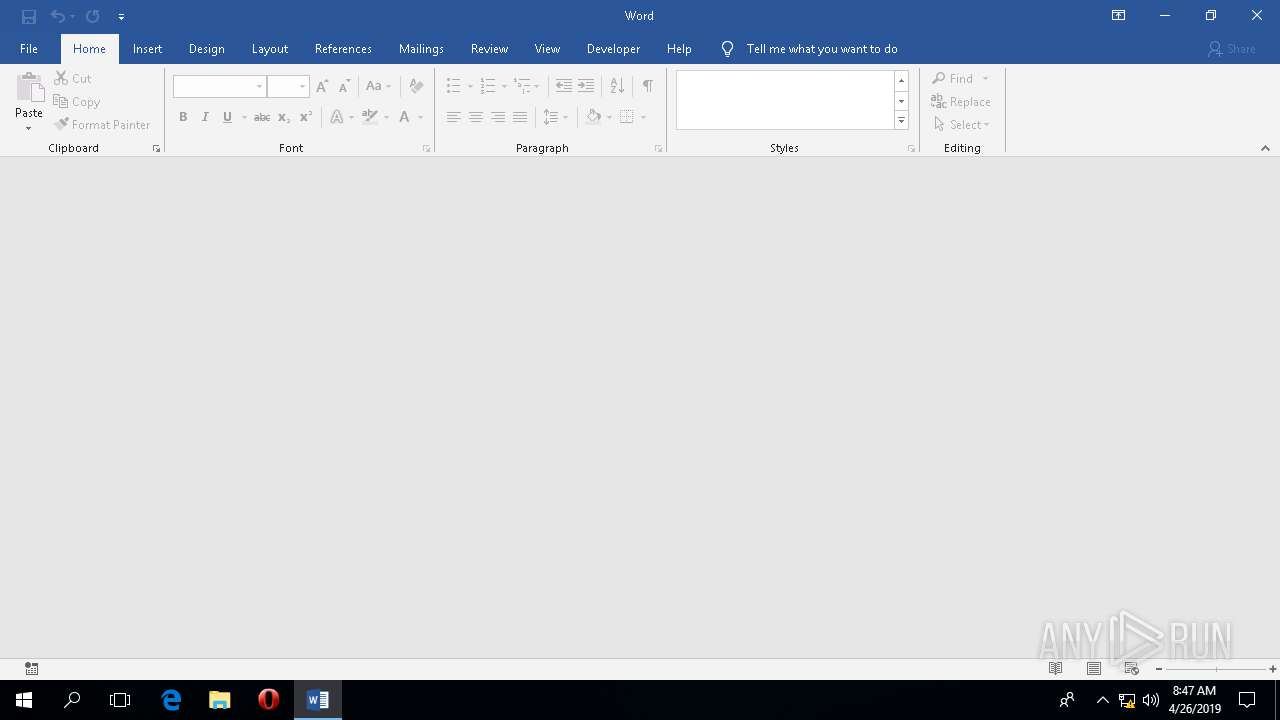
| File name: | invoice.doc |
| Full analysis: | https://app.any.run/tasks/8e18a492-d64f-48ab-bdaf-966989ae9512 |
| Verdict: | No threats detected |
| Analysis date: | April 26, 2019, 08:45:56 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/CDFV2 |
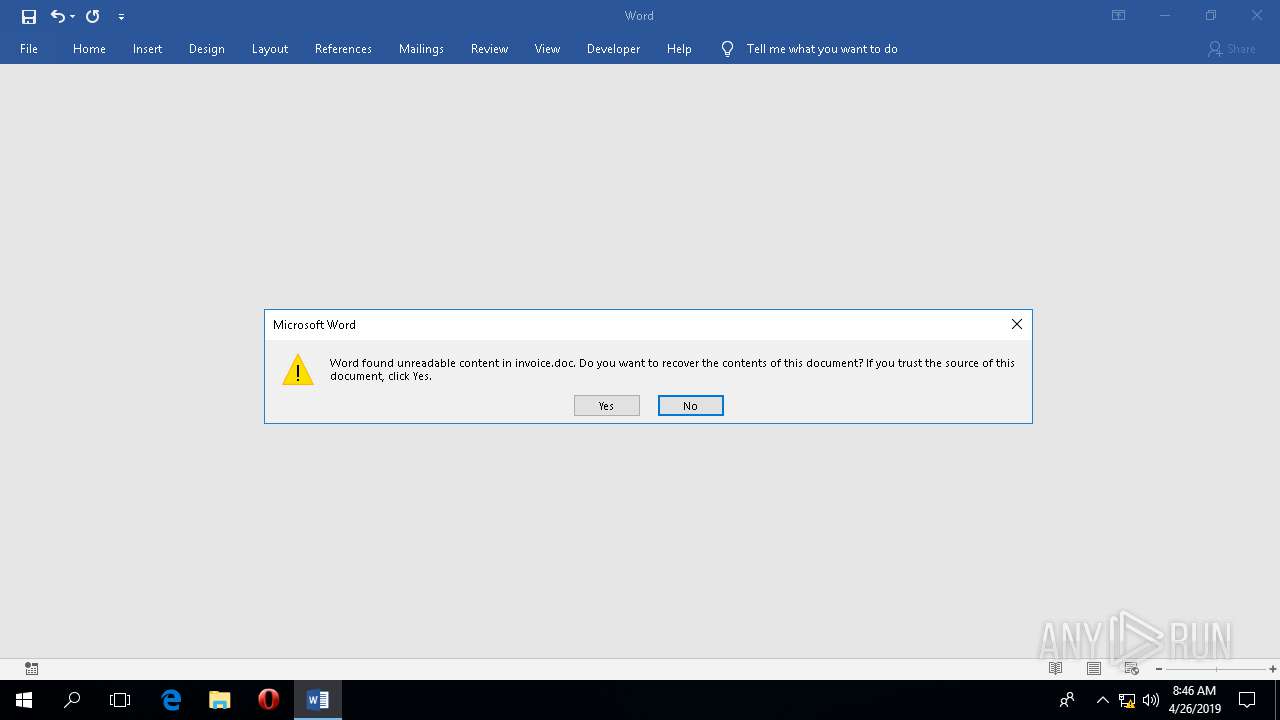
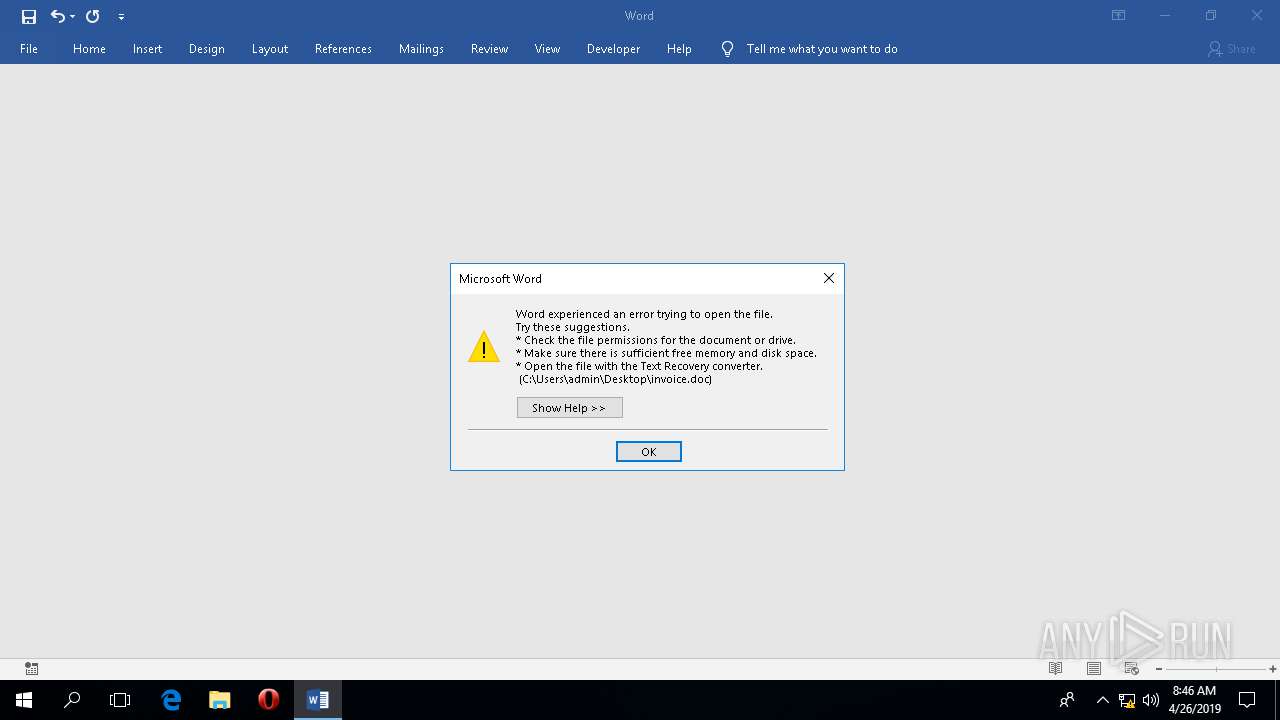
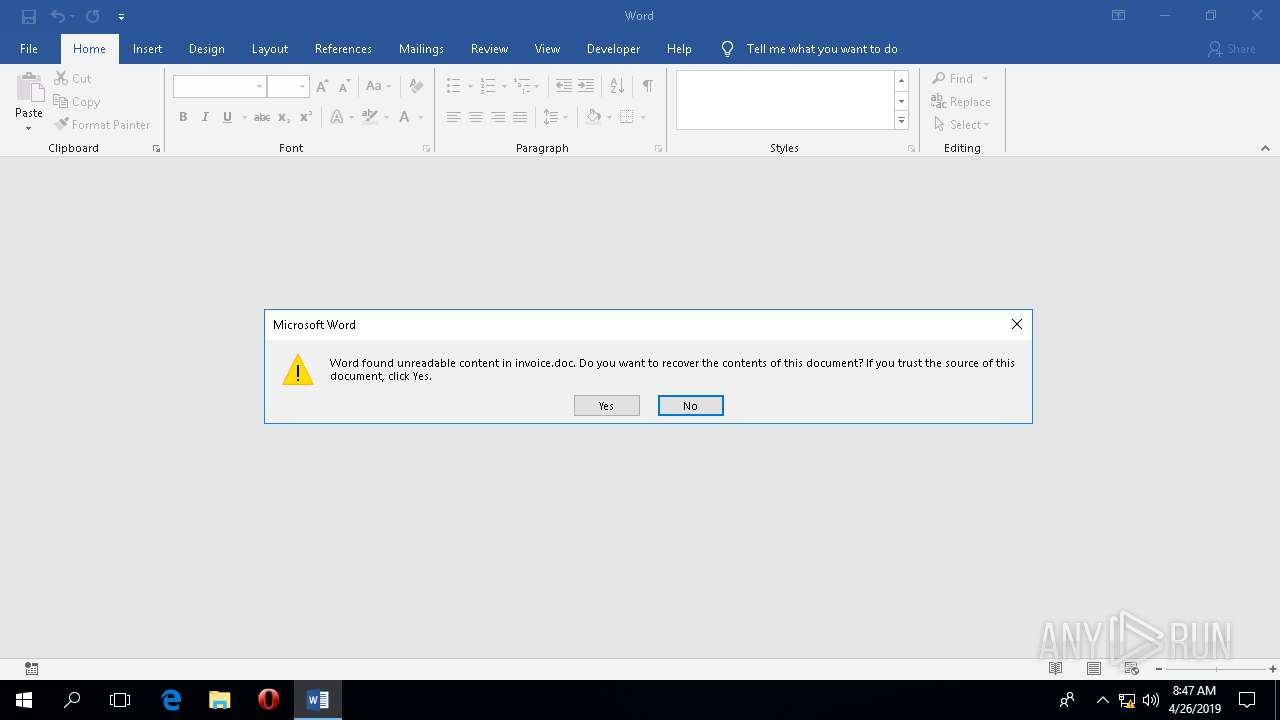
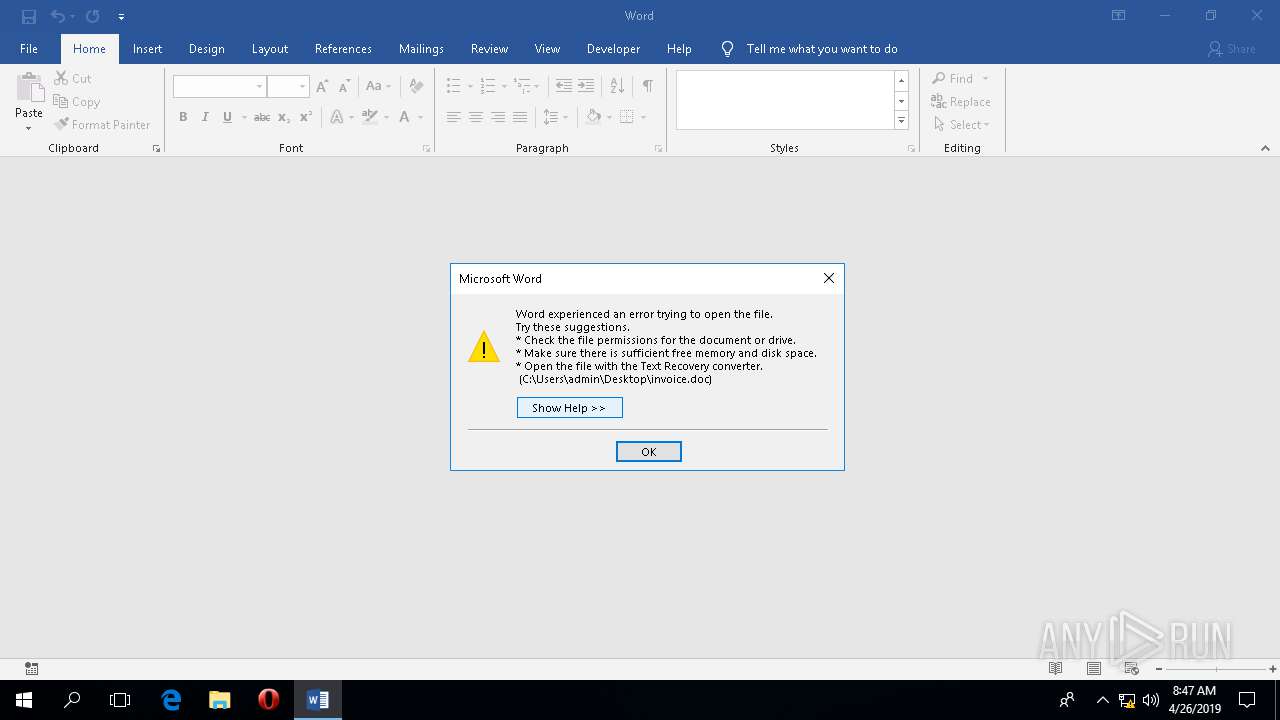
| File info: | Composite Document File V2 Document, Can't read directory |
| MD5: | BF7269E0DAE0640835BCEAFA4FA72E11 |
| SHA1: | 0F35A470F899AA294E98E587E7F8048FC5F23B34 |
| SHA256: | 65DE20D71DBB9182D0F62CC9BA63309DD98EE98AEC2CE4A4EA9D00629EA0D34A |
| SSDEEP: | 768:9+FKSZ7Y3bvKFV4fJdWmUWZbhNLDPDT4ty/g:9xSZ7+GI6mUWZbhNvv4U/ |
MALICIOUS
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 2828)
SUSPICIOUS
Reads Environment values
- WINWORD.EXE (PID: 2828)
INFO
Reads settings of System Certificates
- WINWORD.EXE (PID: 2828)
Reads the software policy settings
- WINWORD.EXE (PID: 2828)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2828)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
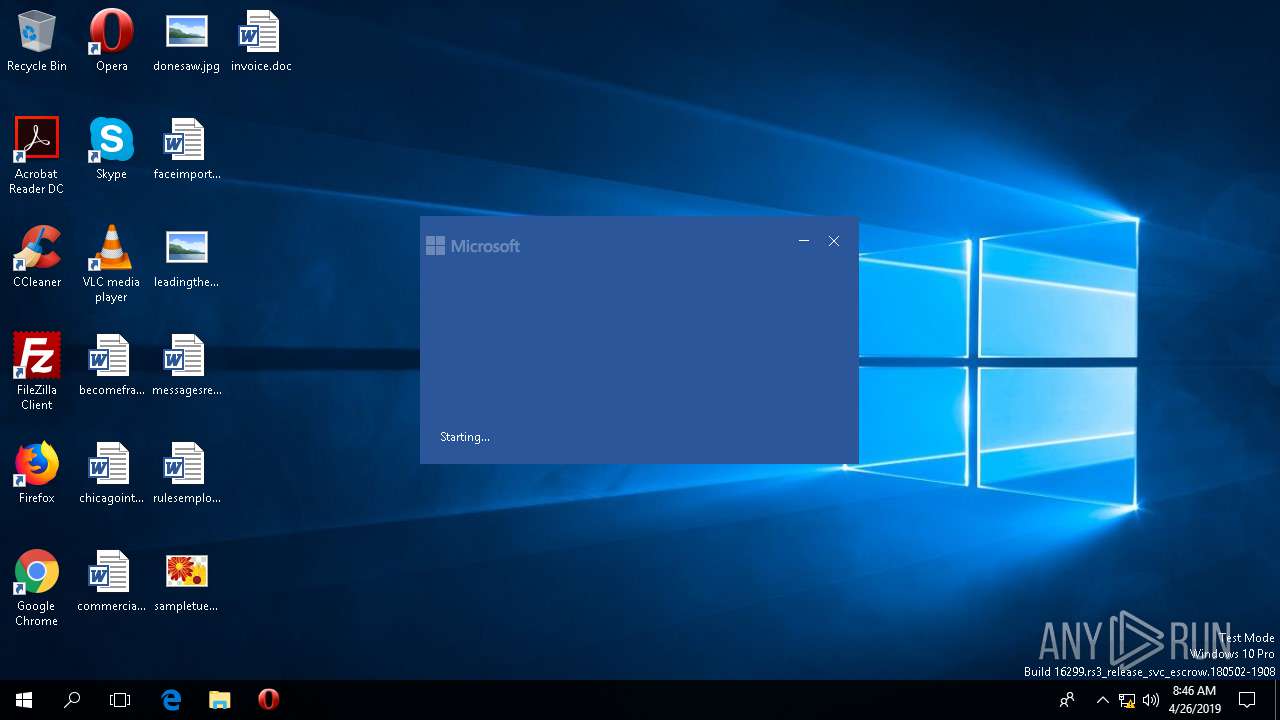
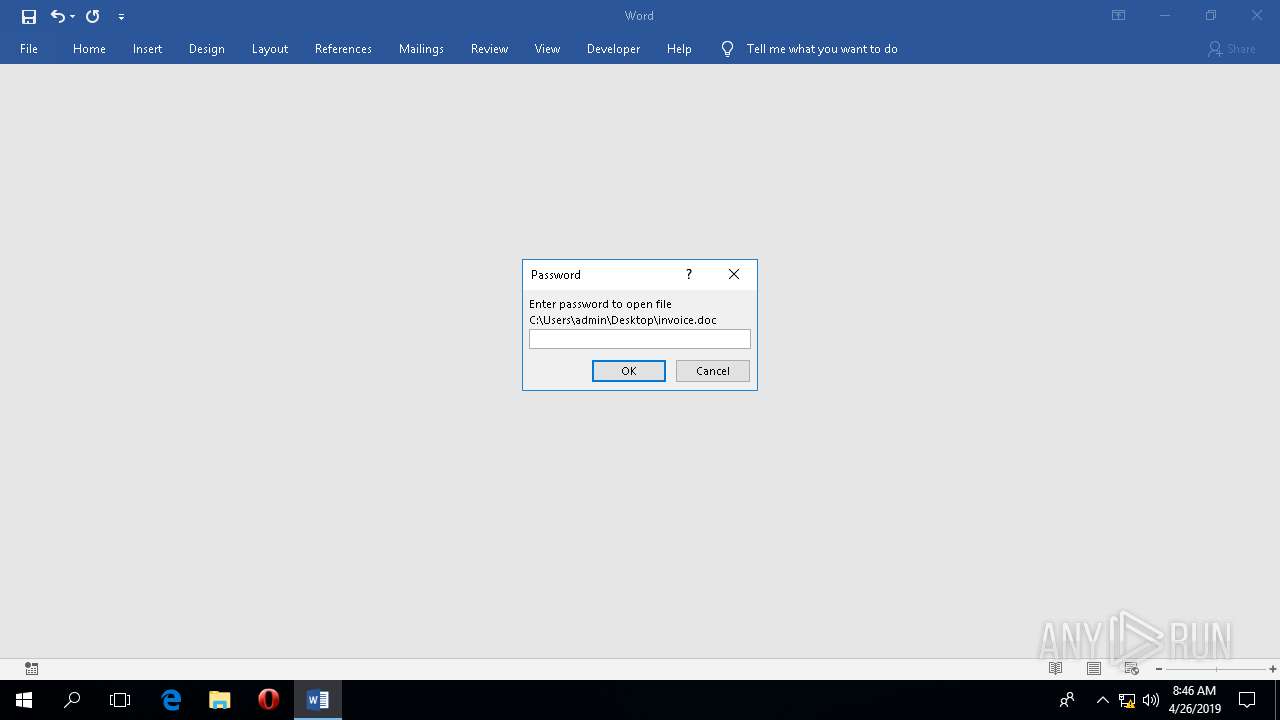
| 2828 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\invoice.doc" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
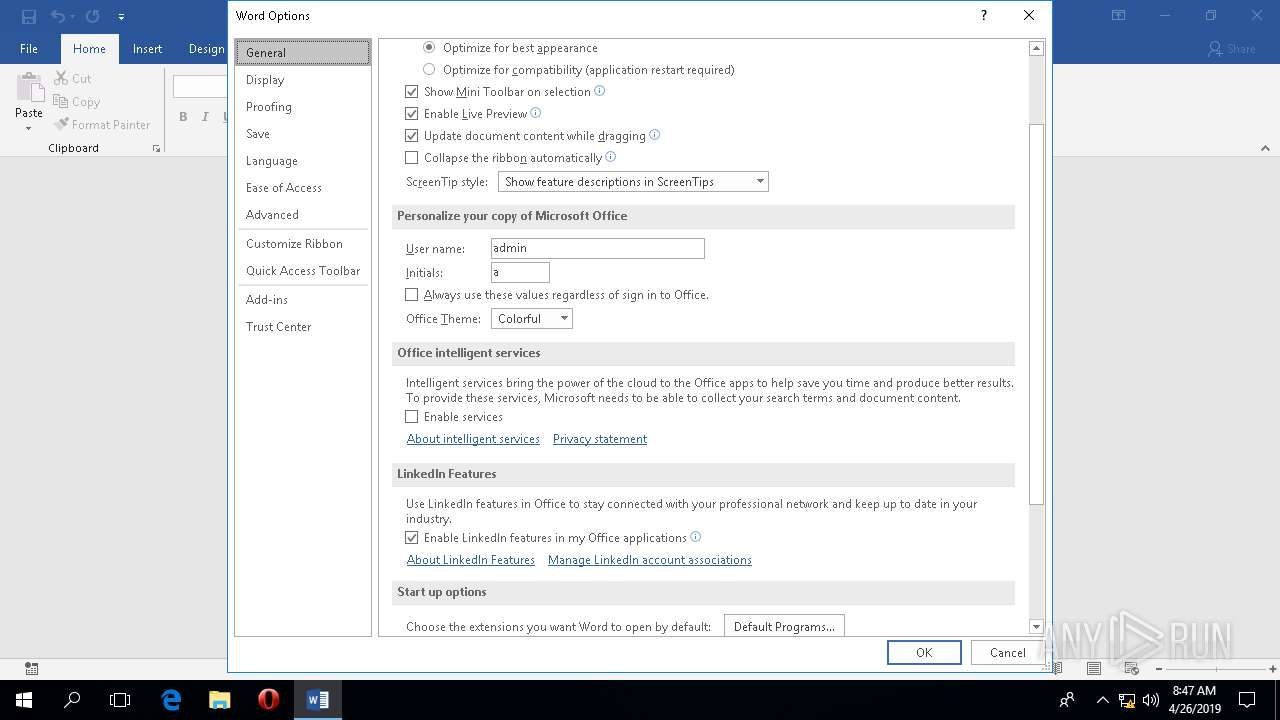
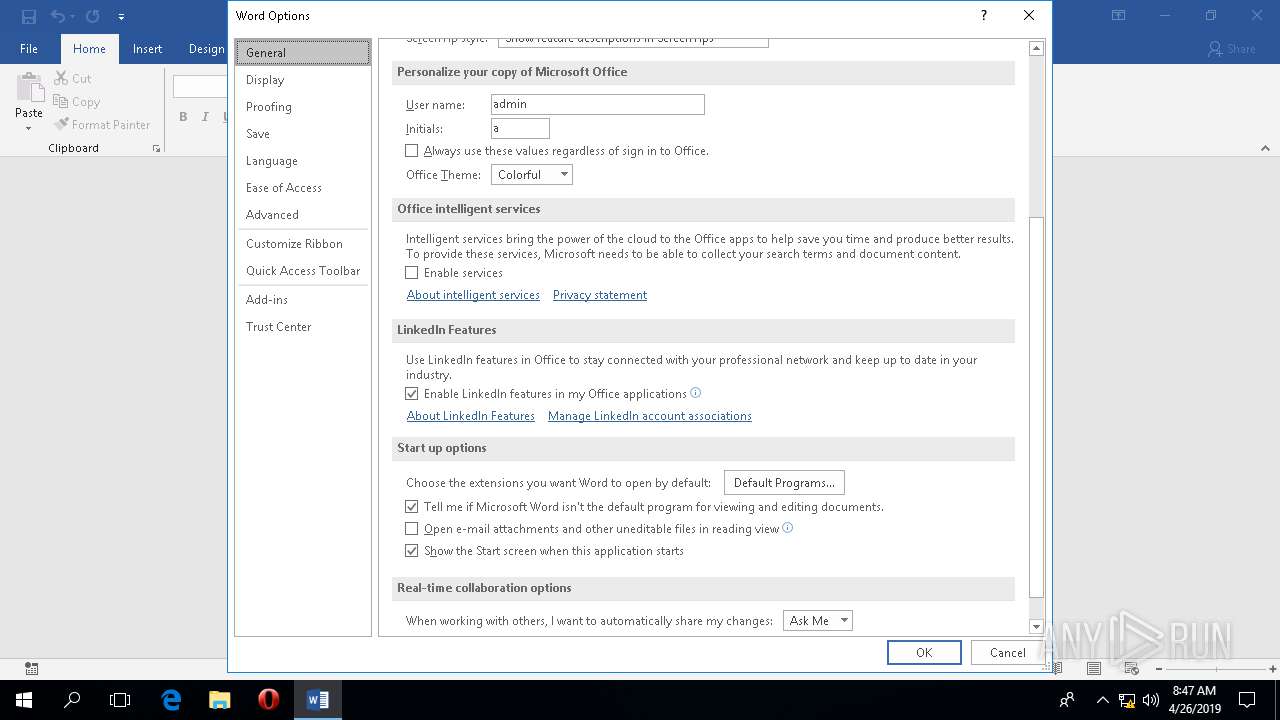
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.11328.20158 Modules
| |||||||||||||||
Total events
1 140
Read events
993
Write events
114
Delete events
33
Modification events
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000BE4E402C03000000000000000300000000000000 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 1 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v;9 |
Value: 763B39000C0B0000010000000000000072D68A810CFCD40100000000 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | w;9 |
Value: 773B39000C0B0000000004400100000072D68A810CFCD401D206000011931E3AAE77EA4D8CF26EBF773FC03472D68A810CFCD4010000000000001000BE4E402C0000000006000000040004000200000000000000000000000000556E6B6E6F776E00000000000000000000000000000000000000000000000000000000000000000000000000000000000DF0ADDE0DF0ADDE0DF0ADDE0DF0ADDE440045004600410055004C005400000000001BCDE501000002000000FF7F000000000000000000000000000000000000F8AAD09DBD000000200000000000000030000000000000002BAB253BFF7F000000000000000000003000000000000000C01213CDE50100000000000000000000000013CDE5010000F80023CFE50100001000000000000000200000000000000040000000000000002BAB253BFF7F00004000000000000000C00C13CDE50100002B000000000000004000000000000000800023CFE50100000000000000000000001513CDE501000000000000FF7F0000000013CDE5010000D8260BCFE50100004000000000000000300000000000000000001BCDE5010000D289025BFF7F00004000000000000000C00C13CDE501000023000000000000007000000000000000B0A9D09DBD000000000000000000000000000000000000002C00000000000000000000000000000007000000000000007000000000000000600000000000000000001BCDE5010000D289025BFF7F0000400000000000000000000000BD000000600000000000000000000000BD000000001513CDE50100000000000000000000000013CDE5010000D8260BCFE501000030000000000000002BAB253BFF7F000030000000000000007668025BFF7F0000C0A9D09DBD000000C00C13CDE50100002F0000000000000070000000000000003000000000000000440045004600410055004C0054000000A200000000000000000000000000000007000000000000007000000000000000600000000000000000001BCDE5010000D289025BFF7F0000400000000000000000000000E50100006000000000000000000000000000000000001BCDE50100009CBB025BFF7F0000F006000000000000020000000000000000000000000000009D29163BFF7F00004000000000000000C00C13CDE501000000000000E50100000000000000000000000000000000000001000000000000000000000000000000701A20CFE50100001000000000000000790000000A0000000000000000000000601A20CFE5010000601A20CFE501000080000000FF7F00006F00000000000000C8030000000000000A000000000000000A000000000000000A00000000000000CFA2253BFF7F000060000000000000000000000000000000000000000000000000000000000000008E8AFFFF6D0000000000000081FFFFFF30000000000000000C031BCDE501000050011BCDE50100007900000000000000B9ABD09DBD000000000000000000000000031BCDE50100000A00000000000000A0570BCFE5010000FEFFFFFFFFFFFFFFA0260BCFE5010000A0B821CDE50100002C0000000000000050480BCFE50100002C00000000000000F00600000000000038822C3BFF7F00007668025BFF7F00000A000000000000001E00000000000000440045004600410055004C0054000000B9ABD09DBD00000002000002FF7F0000040000000000000080ABD09DBD000000800023CFE5010000F80000F8FF7F00000400000000000000E175089CFF7F0000B8ABD09DBD00000002000002BD00000038822C3BFF7F000090ACD09DBD00000000000000000000000A00000AFF7F0000002625CFE50100000A00000ABD000000F00925CDE5010000149E253BFF7F0000F8ACD09DBD00000090ABD09DBD00000068E42C3BFF7F000040E42C3BFF7F000000000000000000000000000000000000A20000000000000000000000000000006F00000000000000F00600000000000000001BCDE5010000AB8E025BFF7F000000001BCDE50100000200000000000000E006000000000000F00600000000000088061BCDE5010000B8ABD09DBD000000B0F525CFE501000003000000FF7F0000FEFFFFFFFFFFFFFF000000000000000088ACD09DBD00000046F4133BFF7F0000F0EF25CFE5010000E658EA35FF7F0000000000000000000070110BCFE5010000C01213CDE5010000E658EA35FF7F0000016E100000000000F0EE6F31FF7F0000A20000000000000000000000000000000800000000000000C3486C35FF7F0000E01A20CFE5010000E00600000000000060B0D09DBD0000000000000000000000701A20CFE5010000CB4B6C35FF7F0000801A20CFE501000060B0D09DBD00000054382DFDB1FCD401000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000056D92240 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LCCache\WordDocParts\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: D99C263528E7D401 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF87FAF77B80F05194.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFED2DF85EF7379676.TMP | — | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{27655A9E-C821-4DBF-A082-287E6F27FC9D}.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\winword.exe.db-shm | — | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\winword.exe.db-wal | — | |
MD5:— | SHA256:— | |||
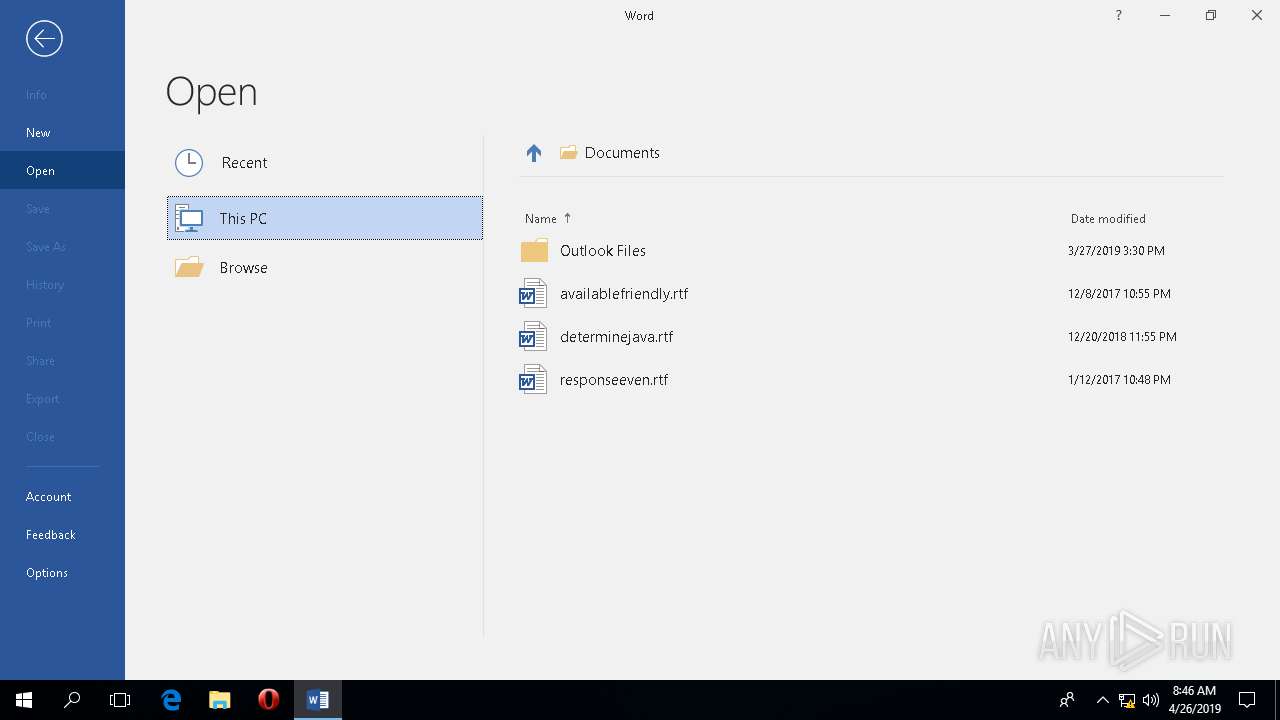
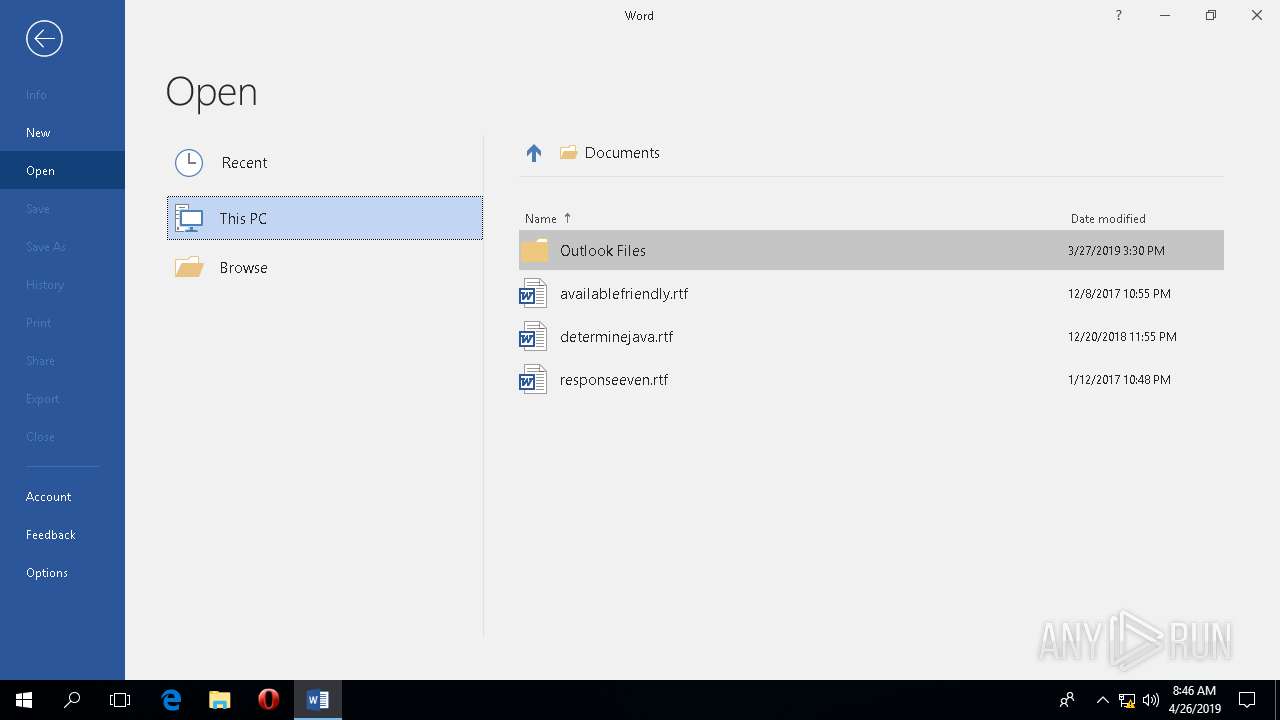
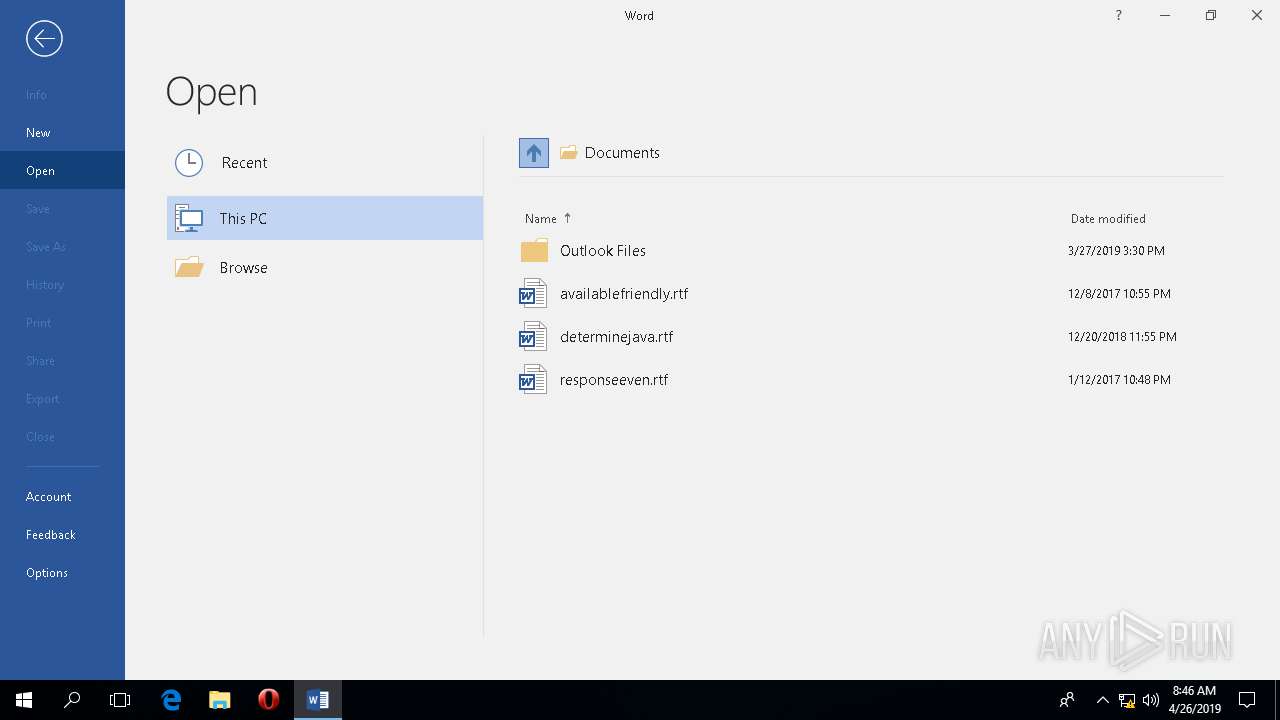
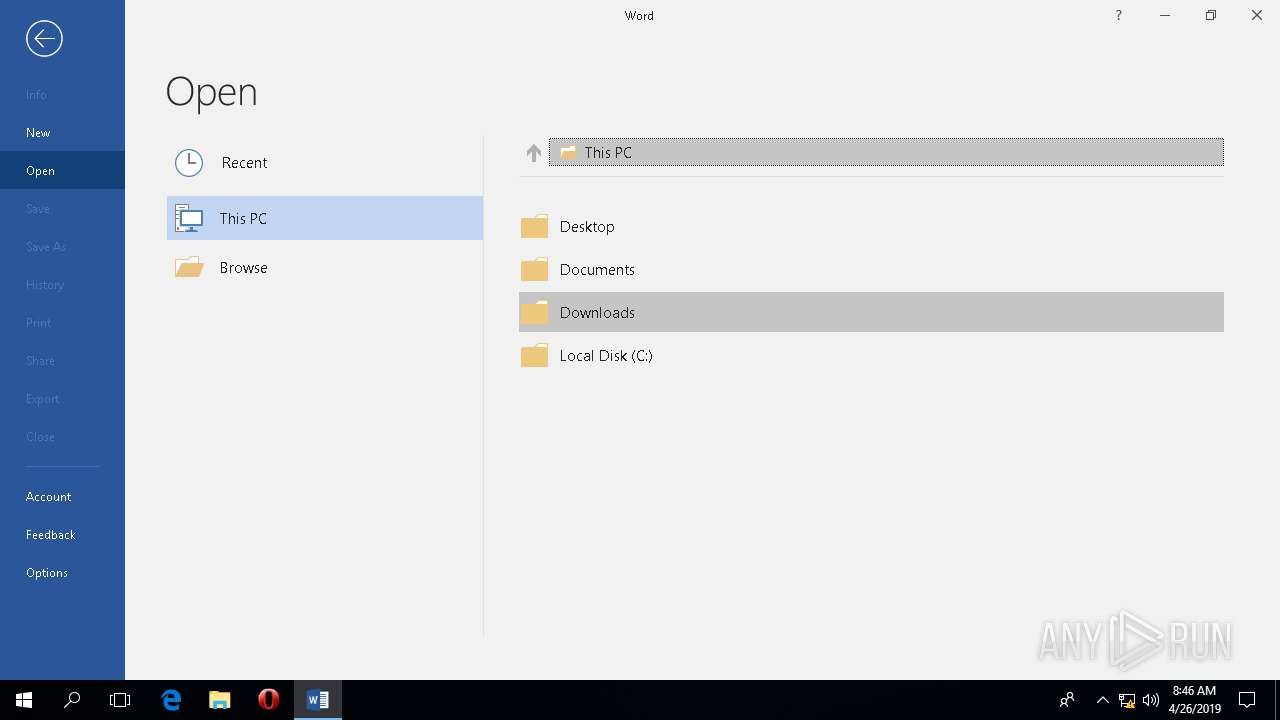
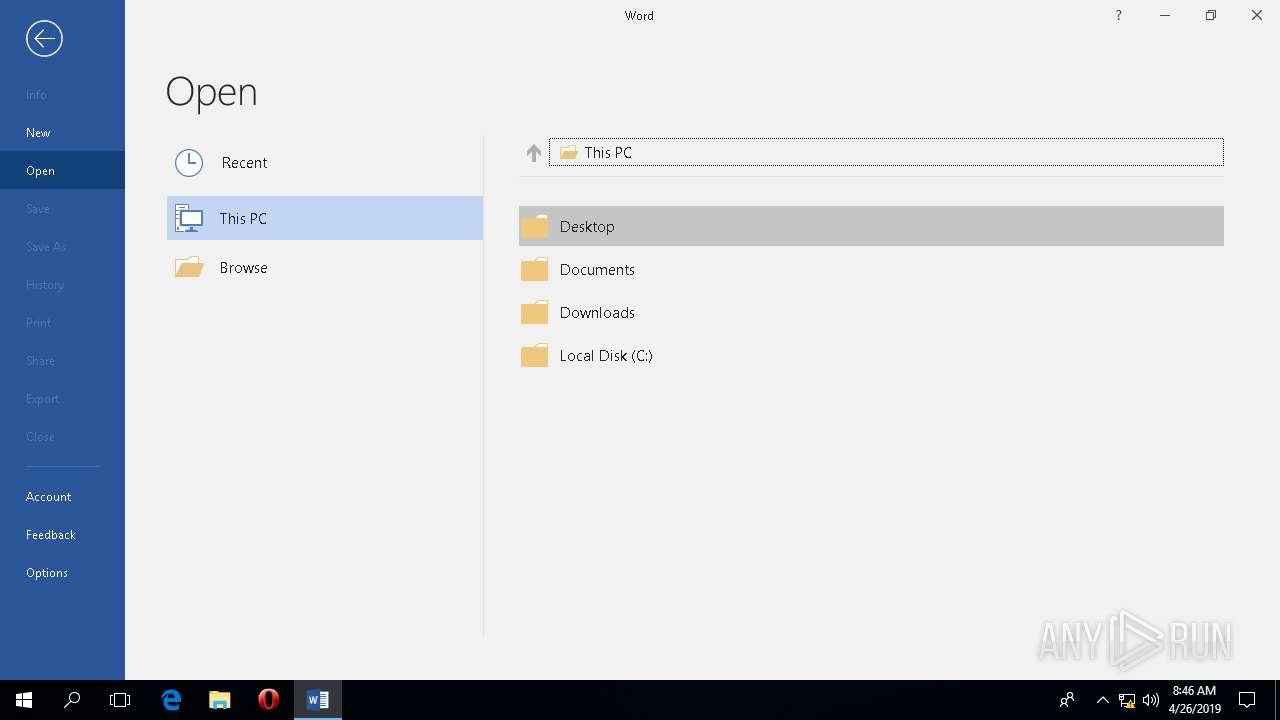
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\BackstageInAppNavCache\MyComputer\C3BE1627C50AB74859EDD189B3AC76690911FD5A37B36938A4CFC754379D0AEB.json | binary | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\Desktop\~$nvoice.doc | pgc | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\winword.exe.db | sqlite | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\aria-debug-2828.log | text | |
MD5:— | SHA256:— | |||
| 2828 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\BackstageInAppNavCache\MyComputer\416BDA1BE82F007E4C36B0D92A28419E80321EE47EBE1167210403D89431132B.json | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2828 | WINWORD.EXE | GET | 200 | 13.107.3.128:443 | https://config.edge.skype.com/config/v1/Office/16.0.11328.20158?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=word&Platform=win32&Version=16.0.11328.20158&MsoVersion=16.0.11328.20156&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&Channel=CC&InstallType=C2R&SessionId=%7b3A1E9311-77AE-4DEA-8CF2-6EBF773FC034%7d&LabMachine=false | US | text | 57.5 Kb | malicious |
2828 | WINWORD.EXE | POST | 200 | 52.114.32.7:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | JP | text | 64 b | whitelisted |
2828 | WINWORD.EXE | POST | 200 | 52.114.32.7:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | JP | text | 9 b | whitelisted |
2828 | WINWORD.EXE | POST | 200 | 52.114.32.7:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | JP | text | 52 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2828 | WINWORD.EXE | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
2828 | WINWORD.EXE | 52.114.32.7:443 | self.events.data.microsoft.com | Microsoft Corporation | JP | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | 2019-04-26 08:47:28.984 T#2220 <E> [AriaSDK.PAL] PAL is already shutdown!
|