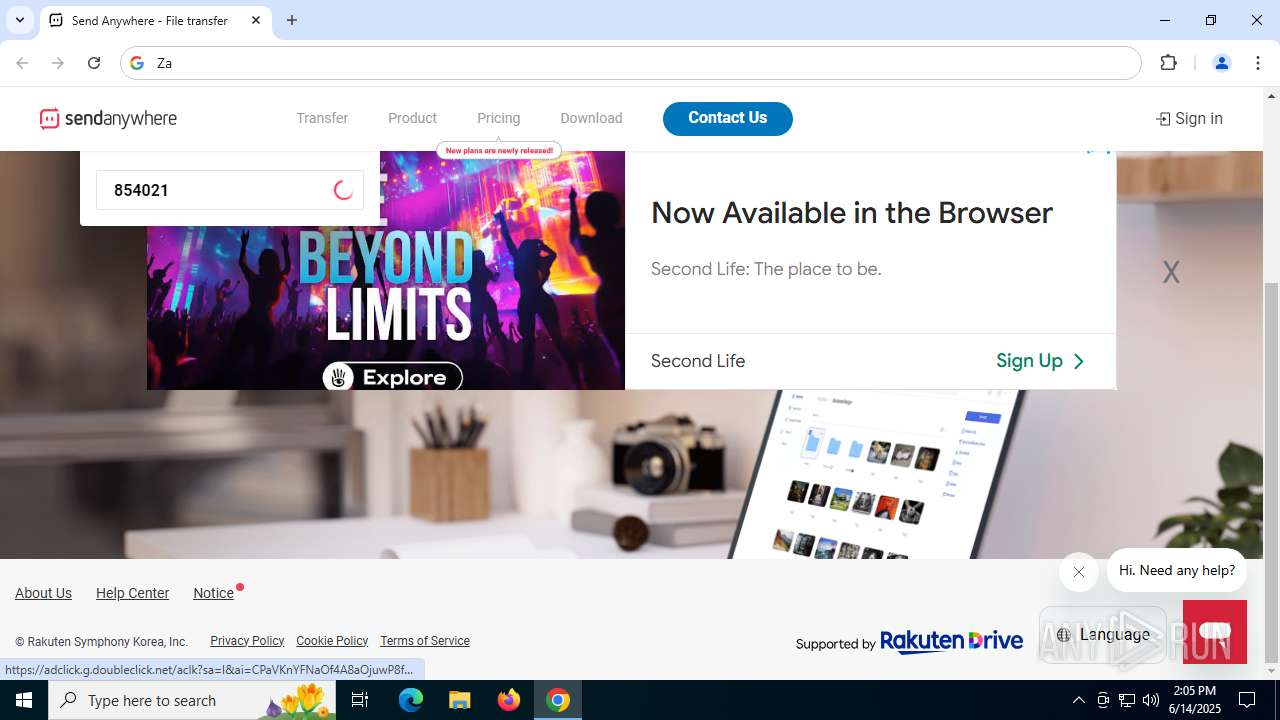
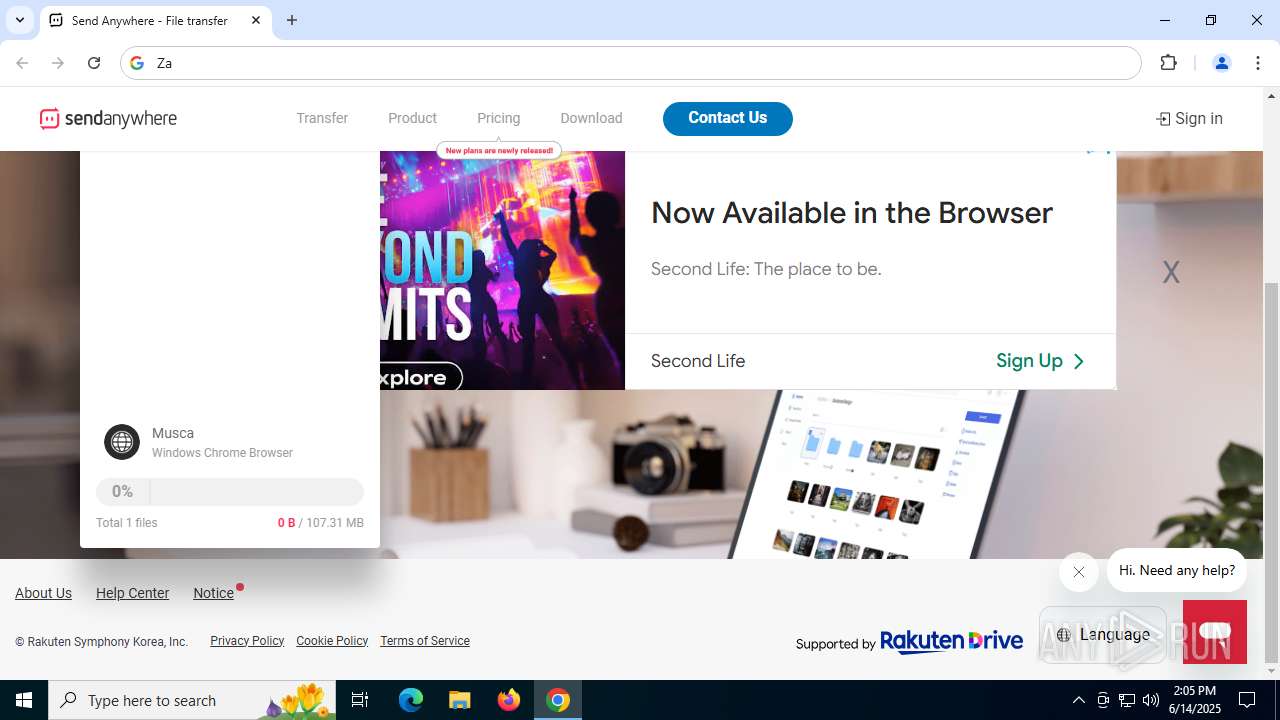
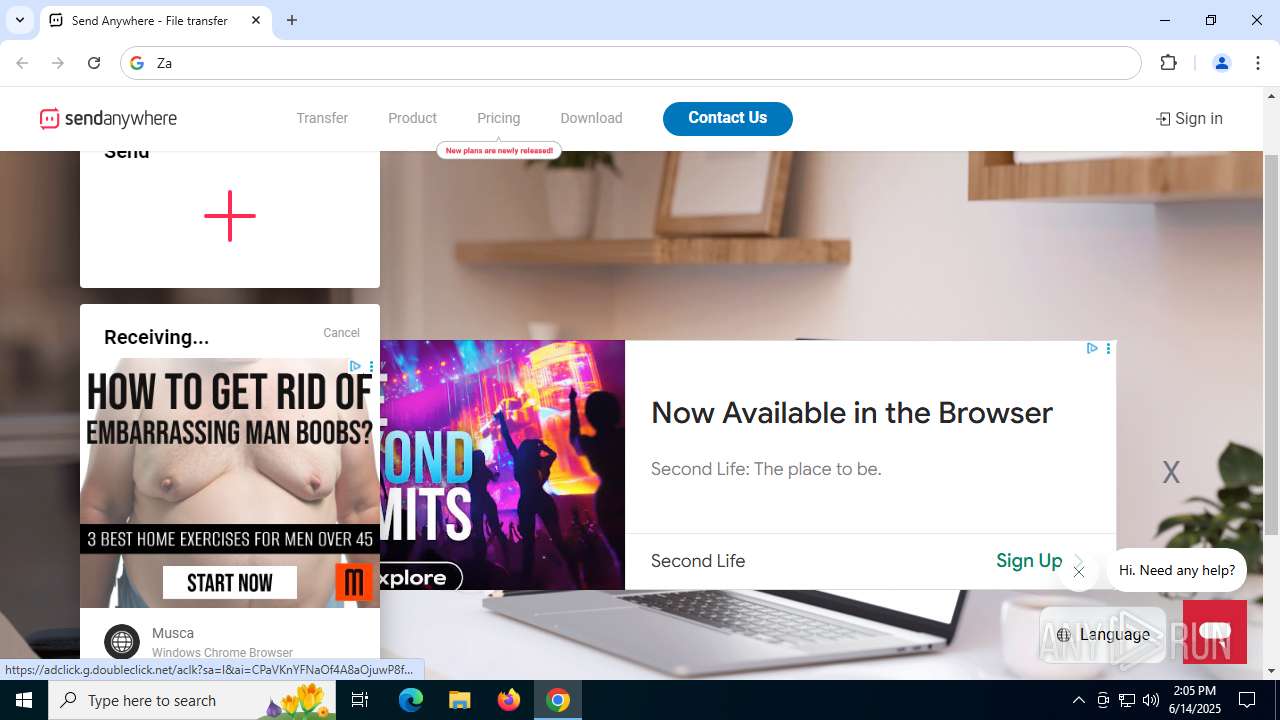
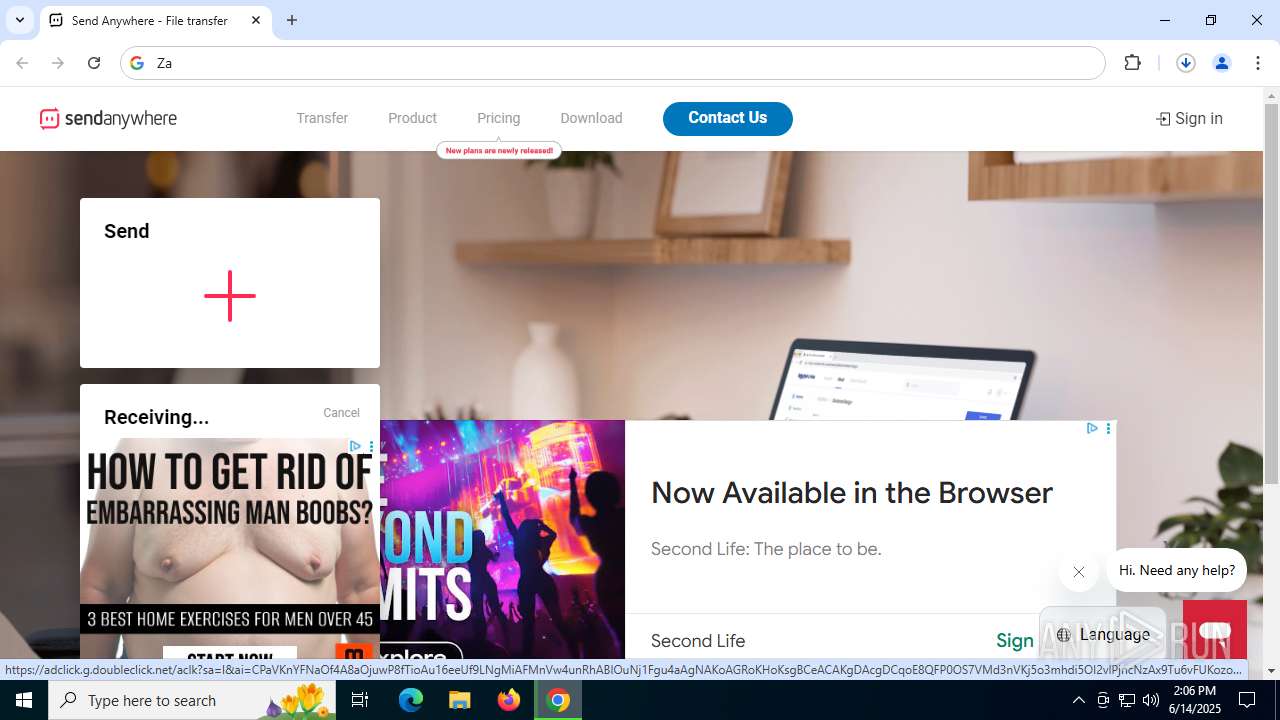
| URL: | https://send-anywhere.com/ |
| Full analysis: | https://app.any.run/tasks/786eac21-05b4-4e36-a1b4-e48aa35d11f5 |
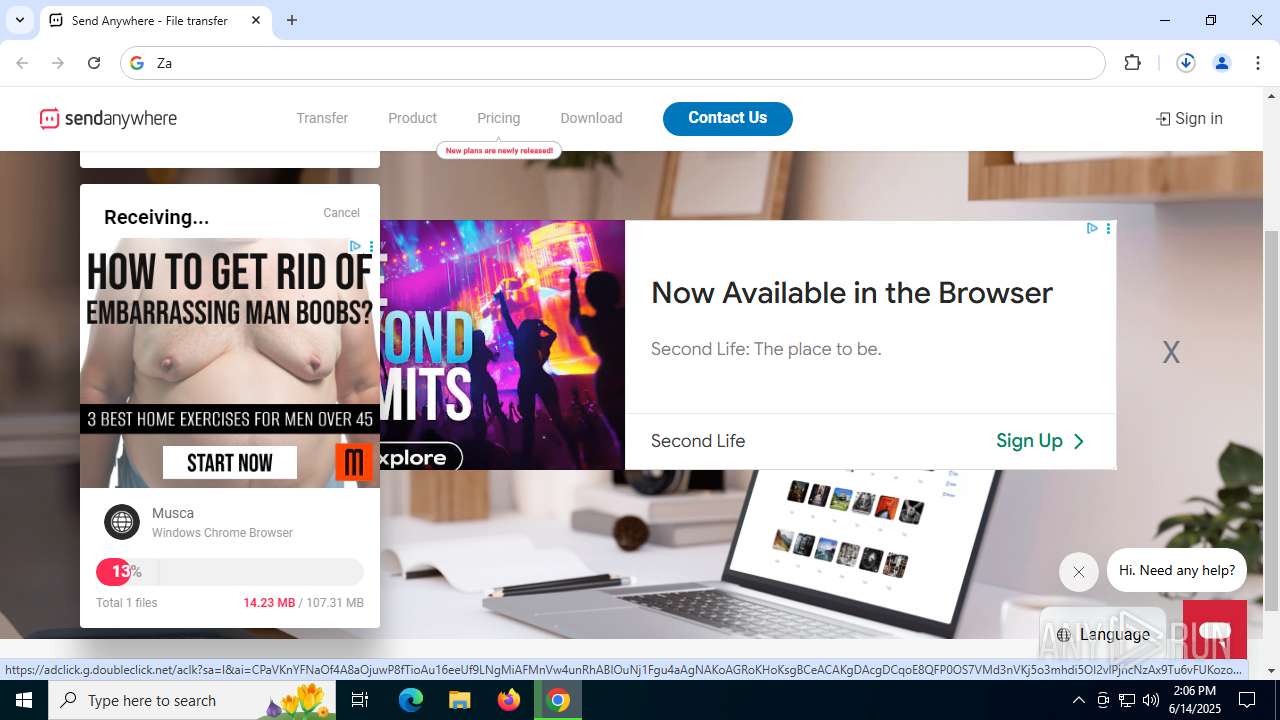
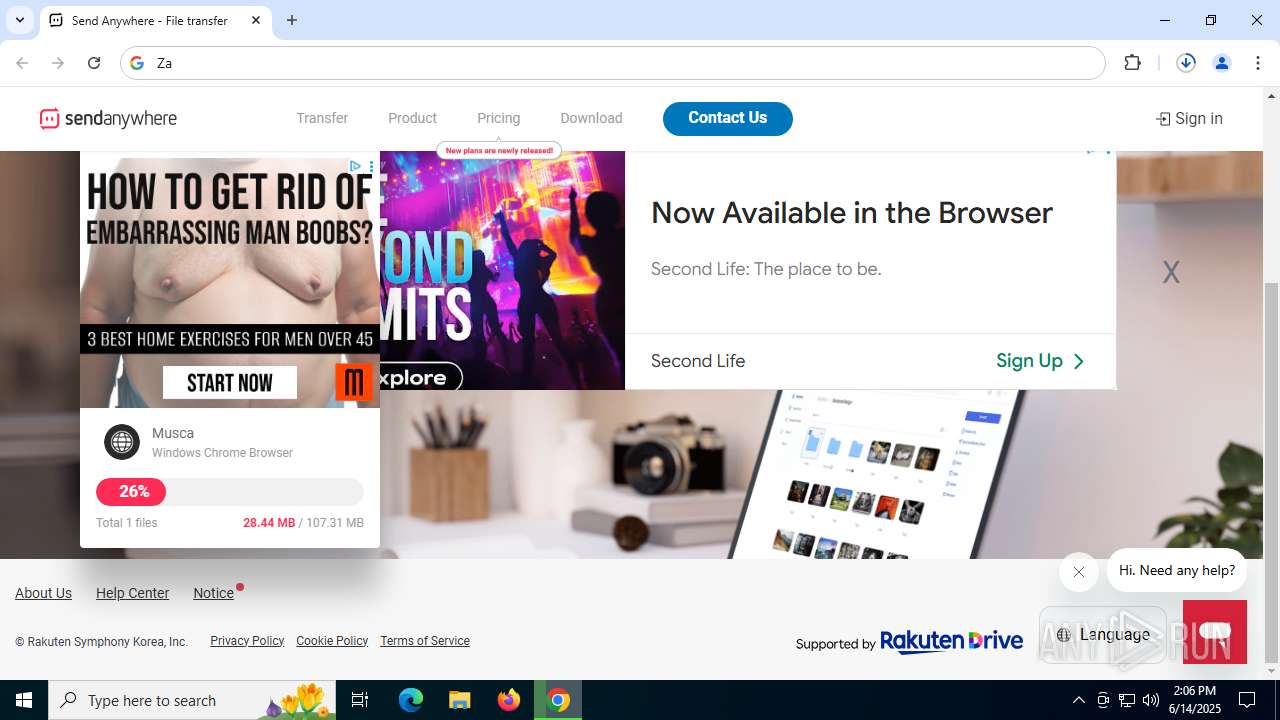
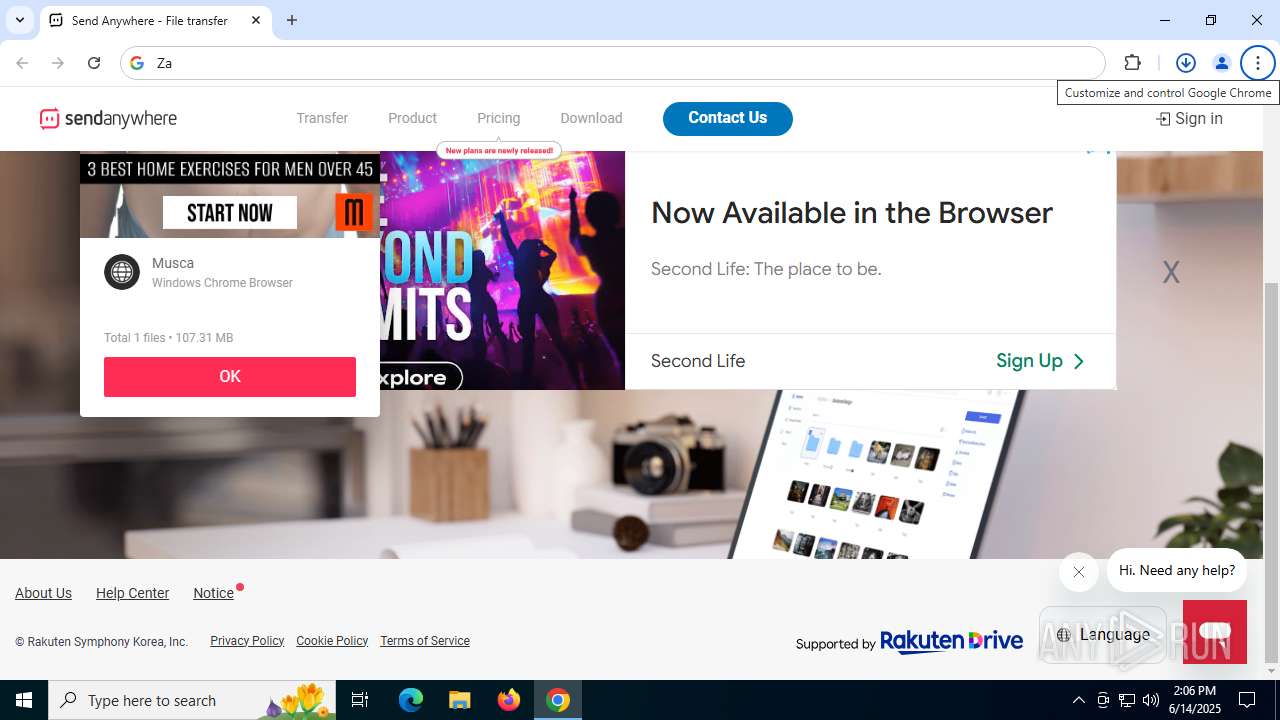
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 14:05:05 |
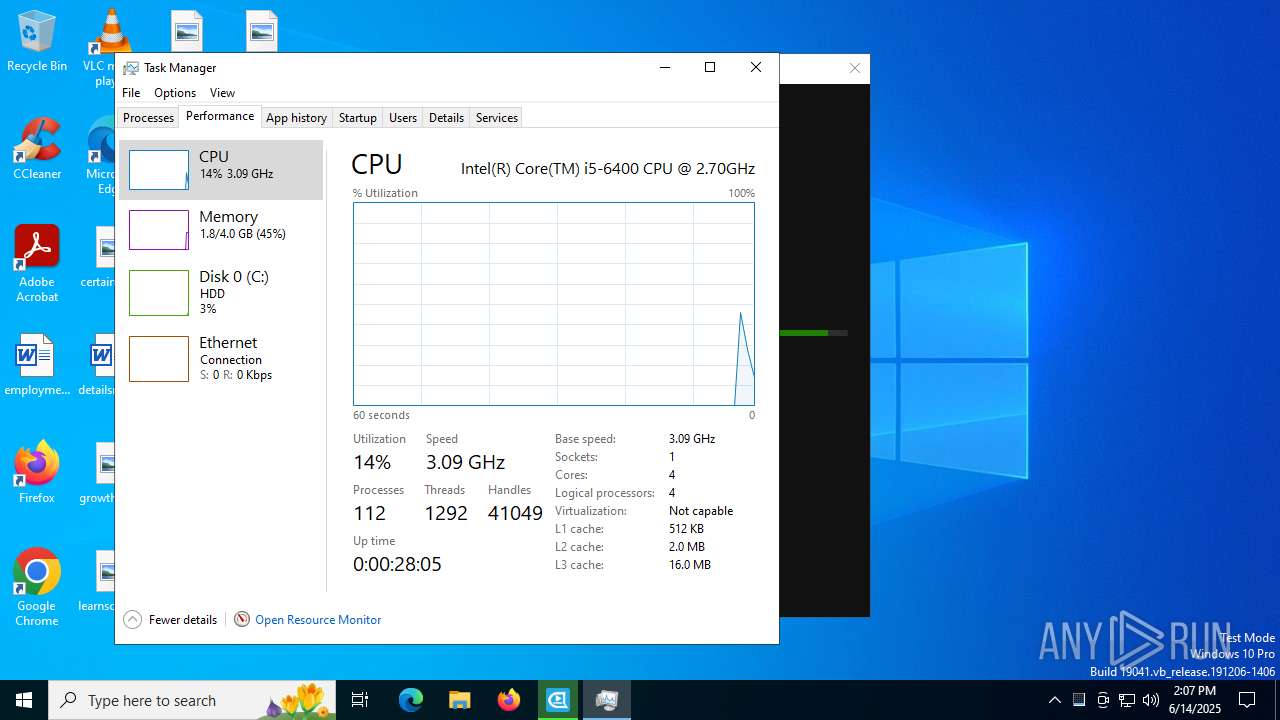
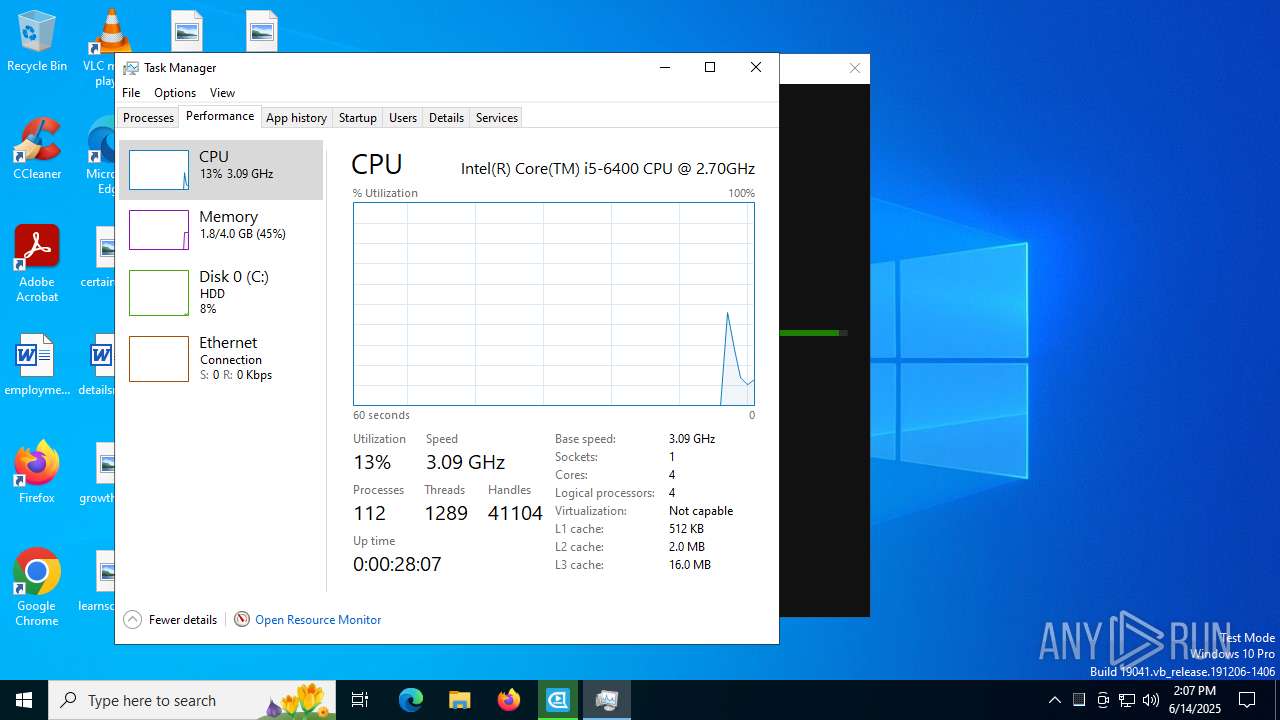
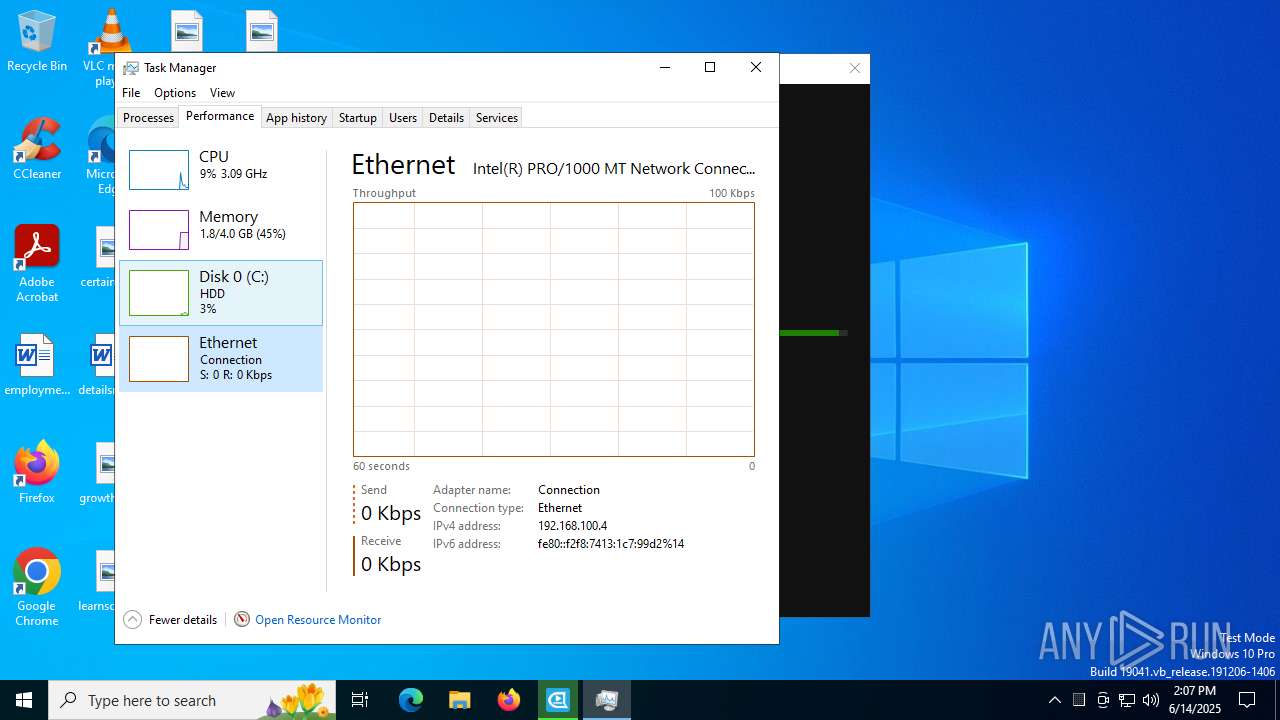
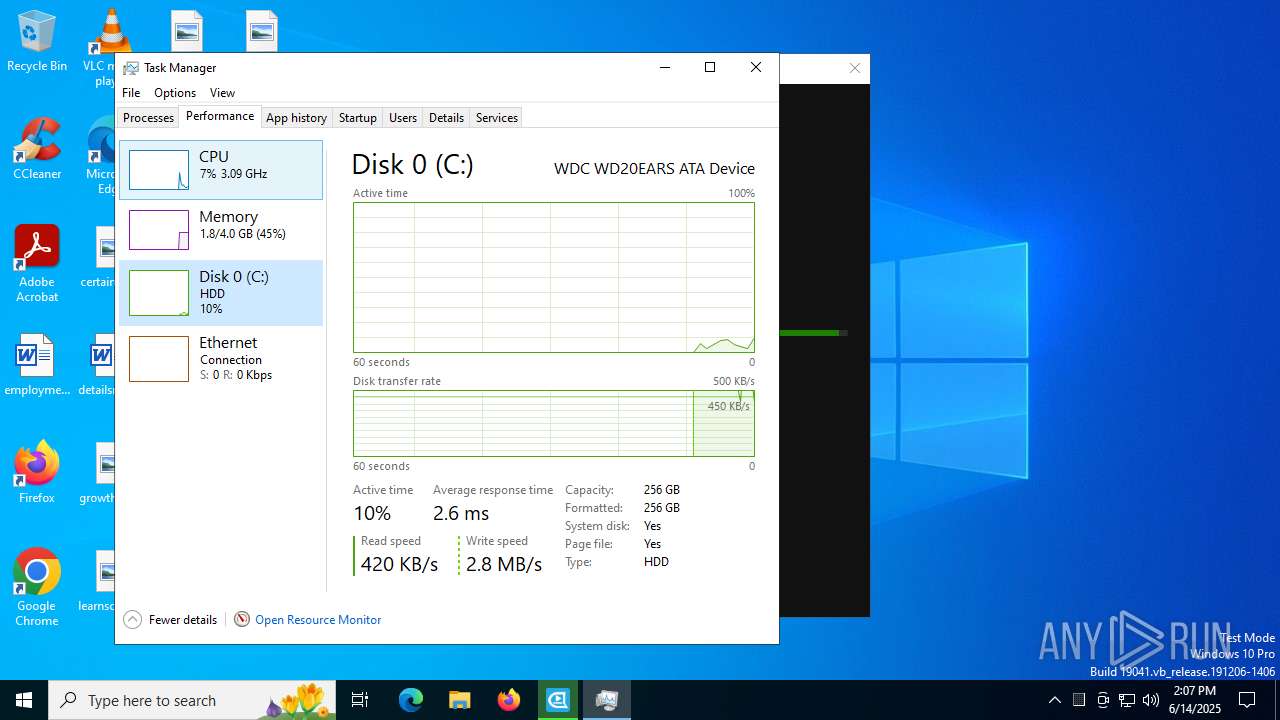
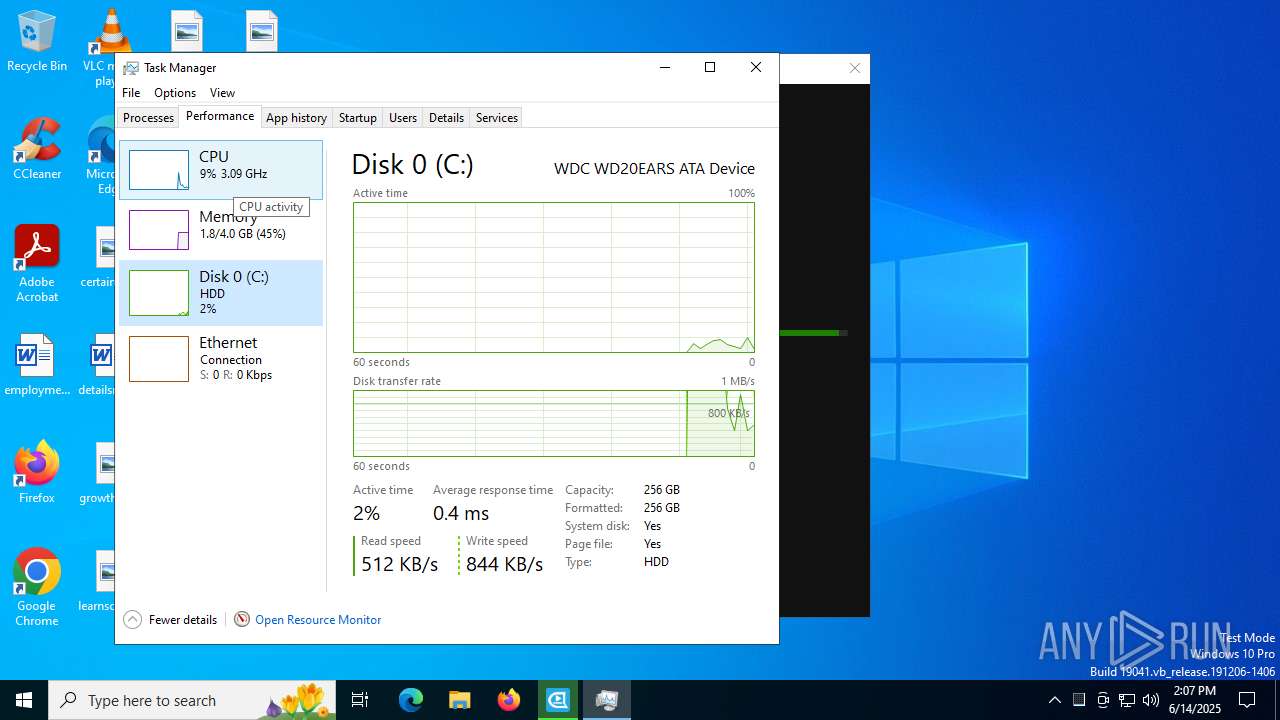
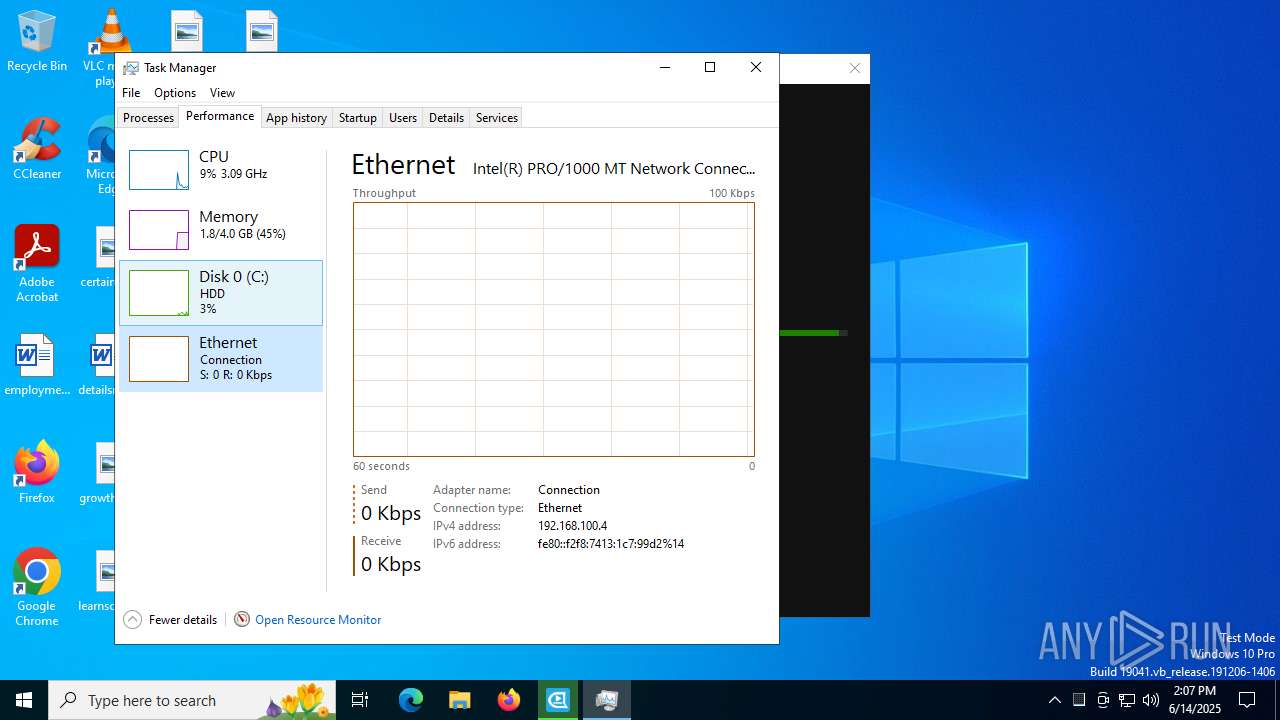
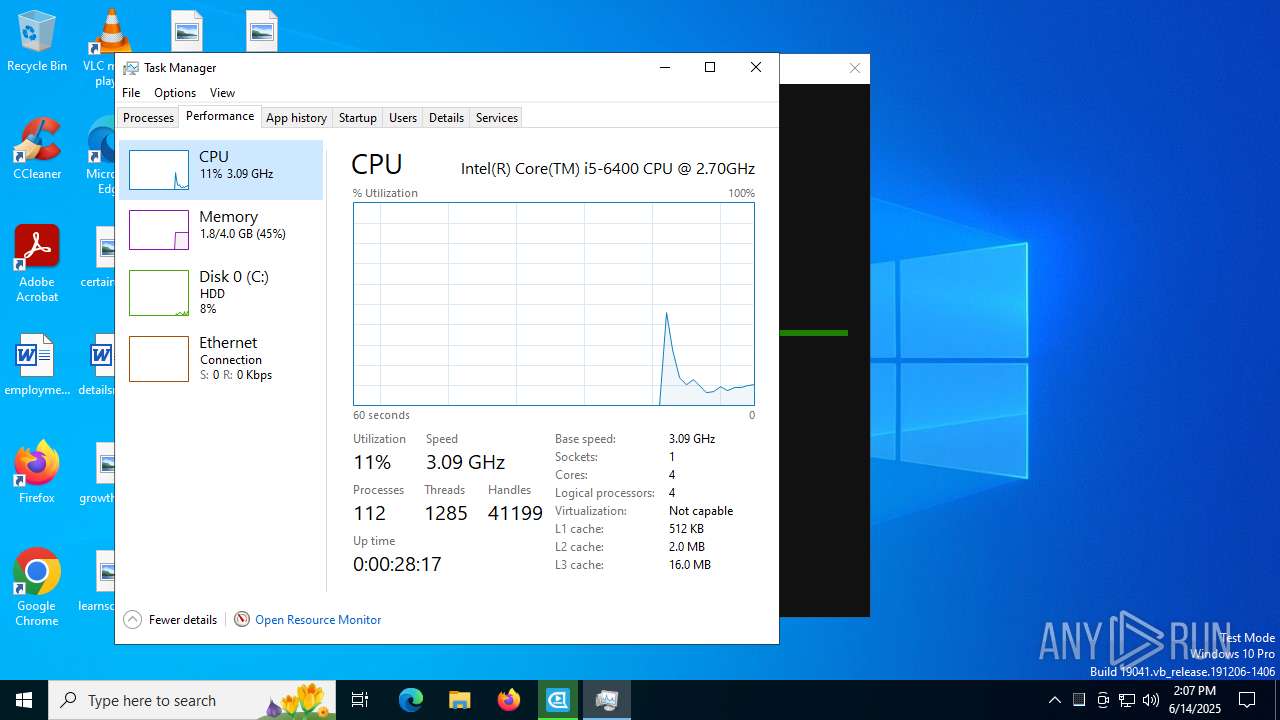
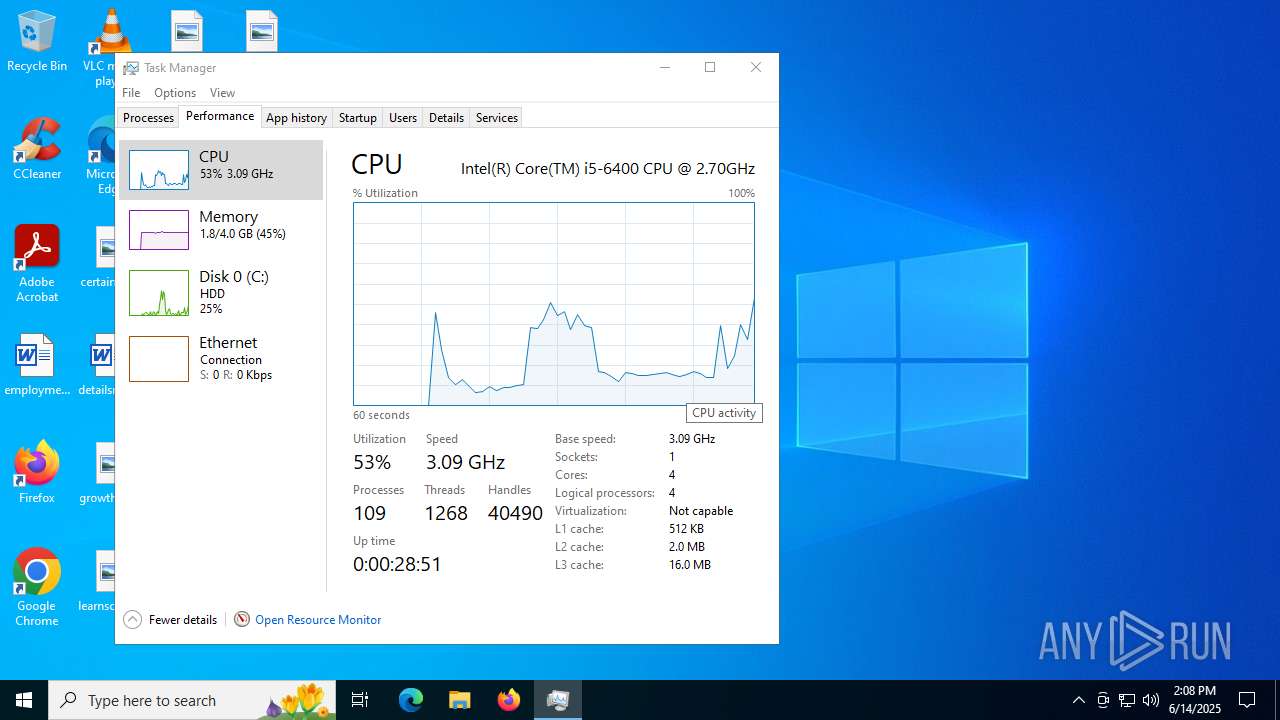
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C35AB5493506D122B1C3459EA3D33164 |
| SHA1: | FB368540A503A54343DD583E46683F27BCD7464D |
| SHA256: | 65D7F47F3A081EA4F51E3C648A38A56FD8D4CEC0BE1CCF5C5A1D205390F0DCA2 |
| SSDEEP: | 3:N8NHPSeKK:2hPSeR |
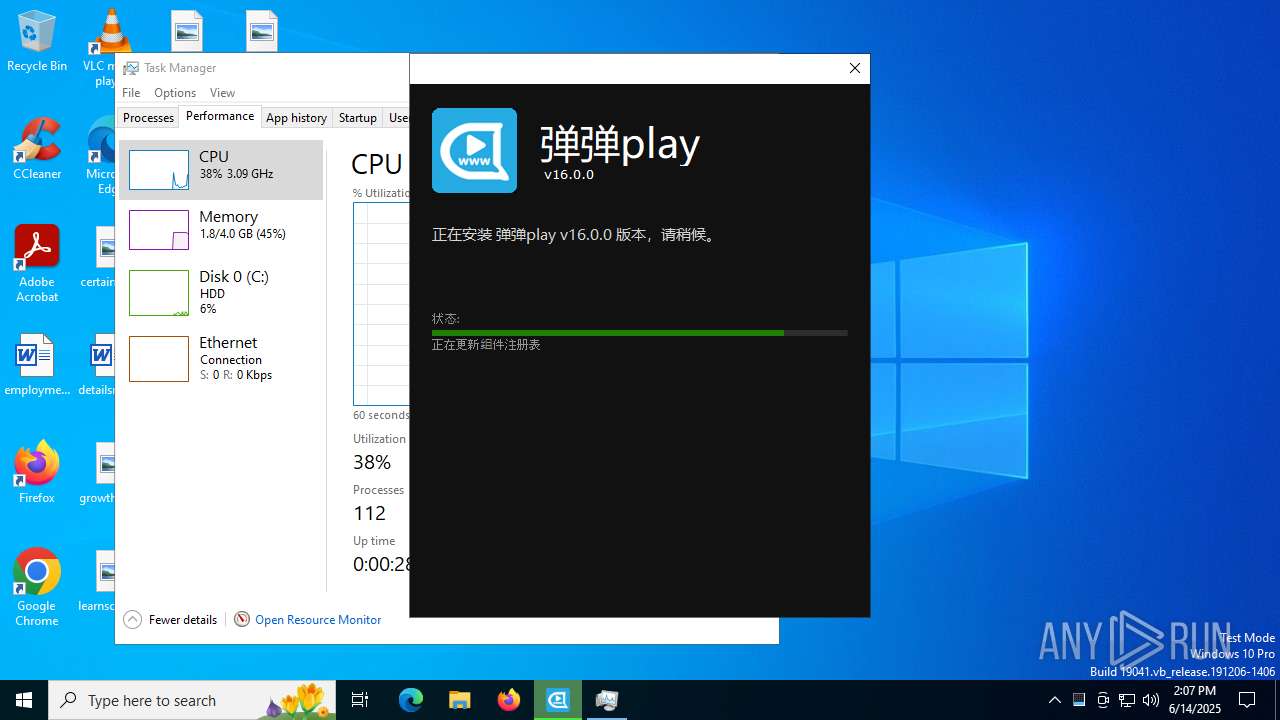
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7060)
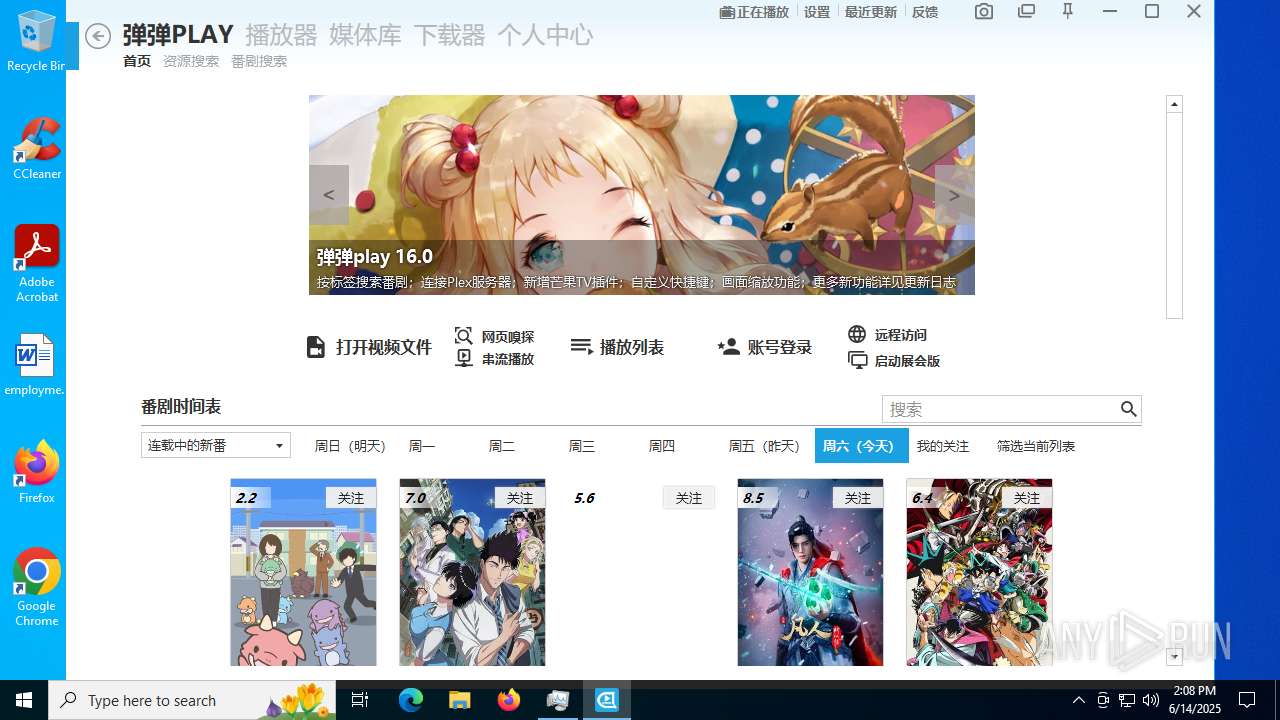
BITTORRENT has been detected (SURICATA)
- dandanplay.exe (PID: 2632)
SUSPICIOUS
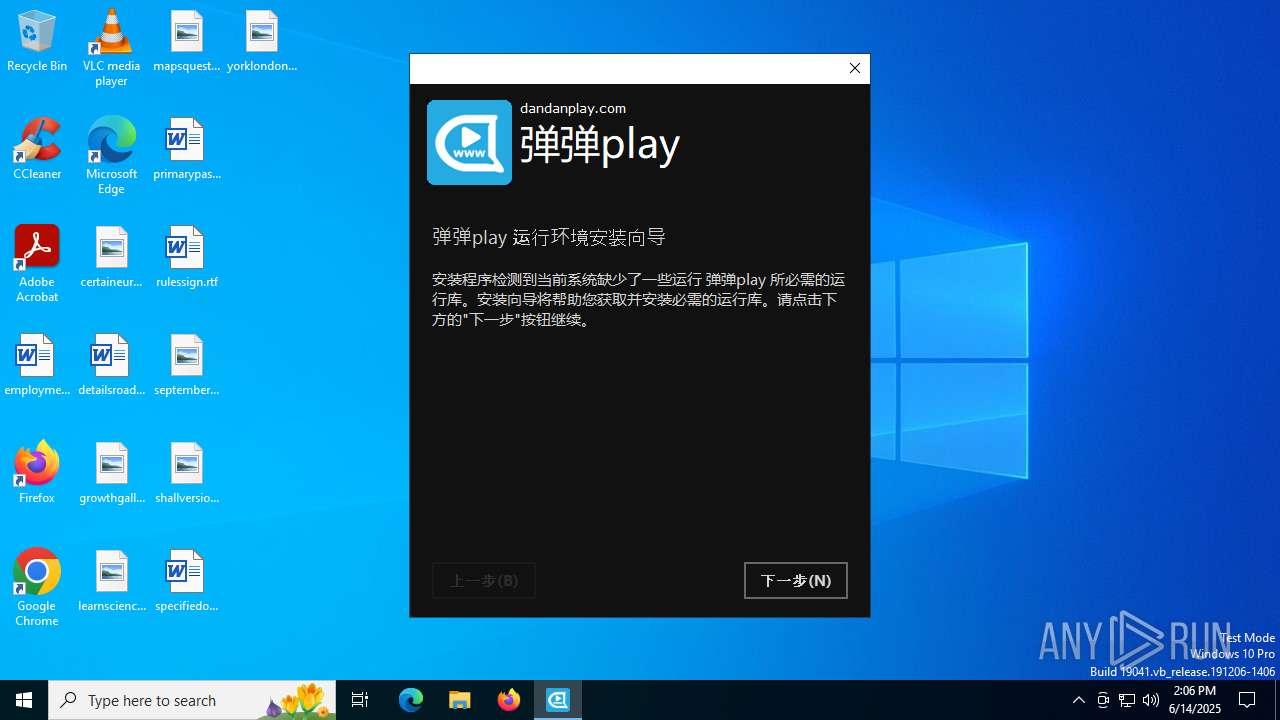
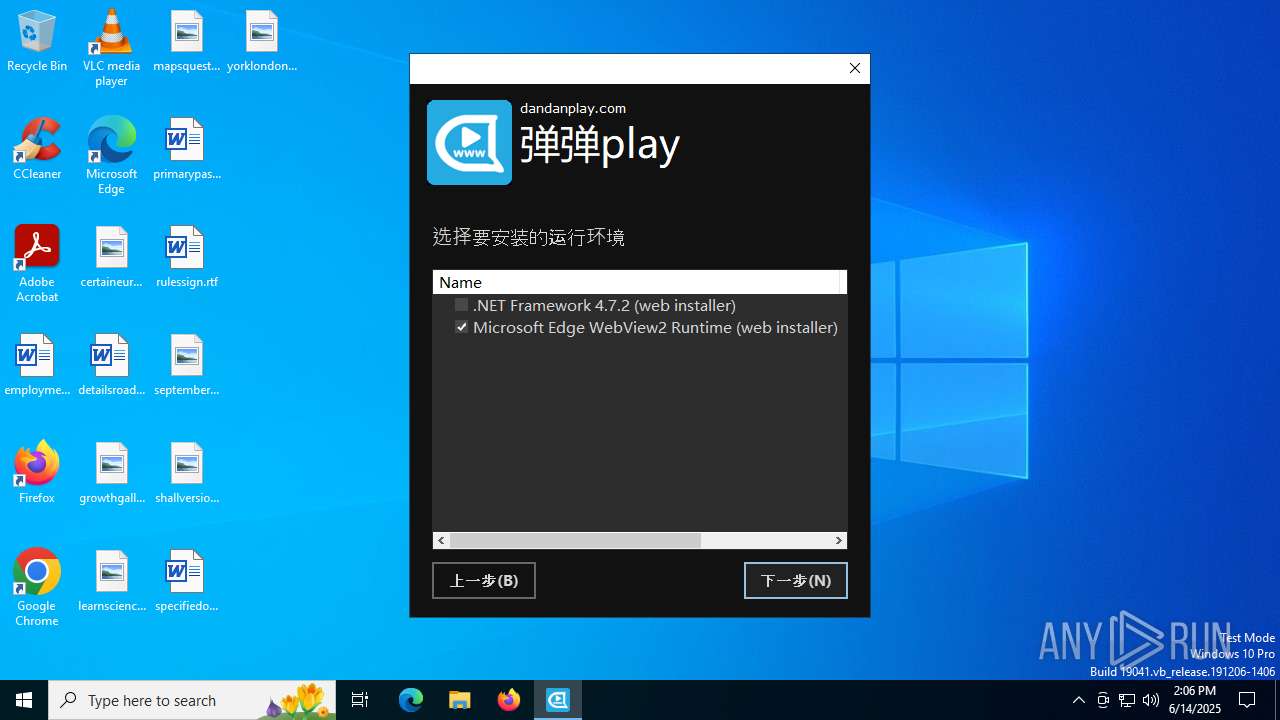
ADVANCEDINSTALLER mutex has been found
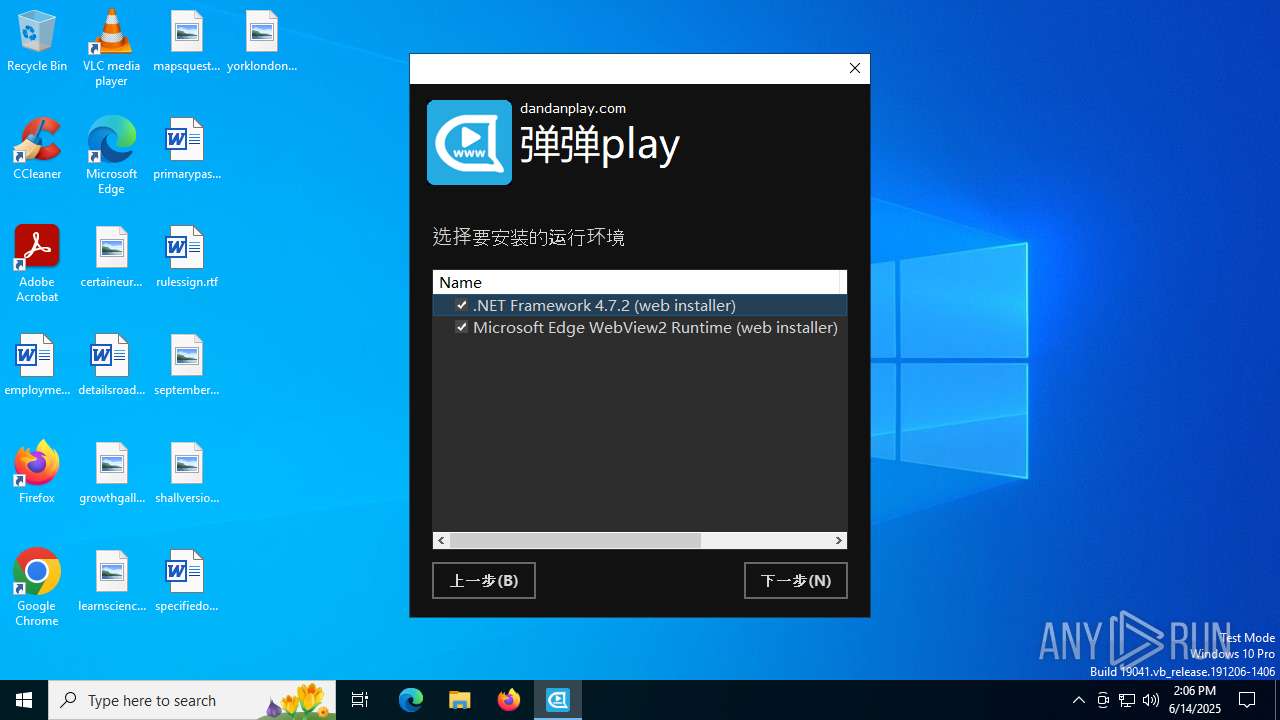
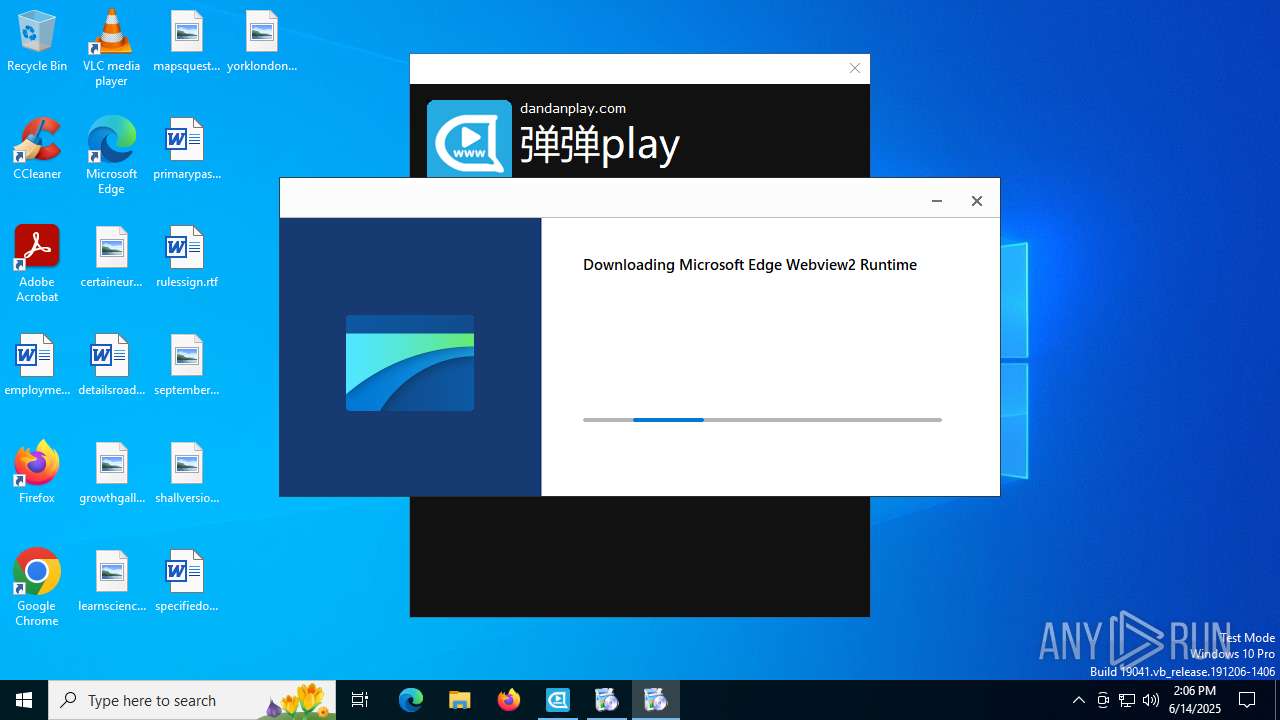
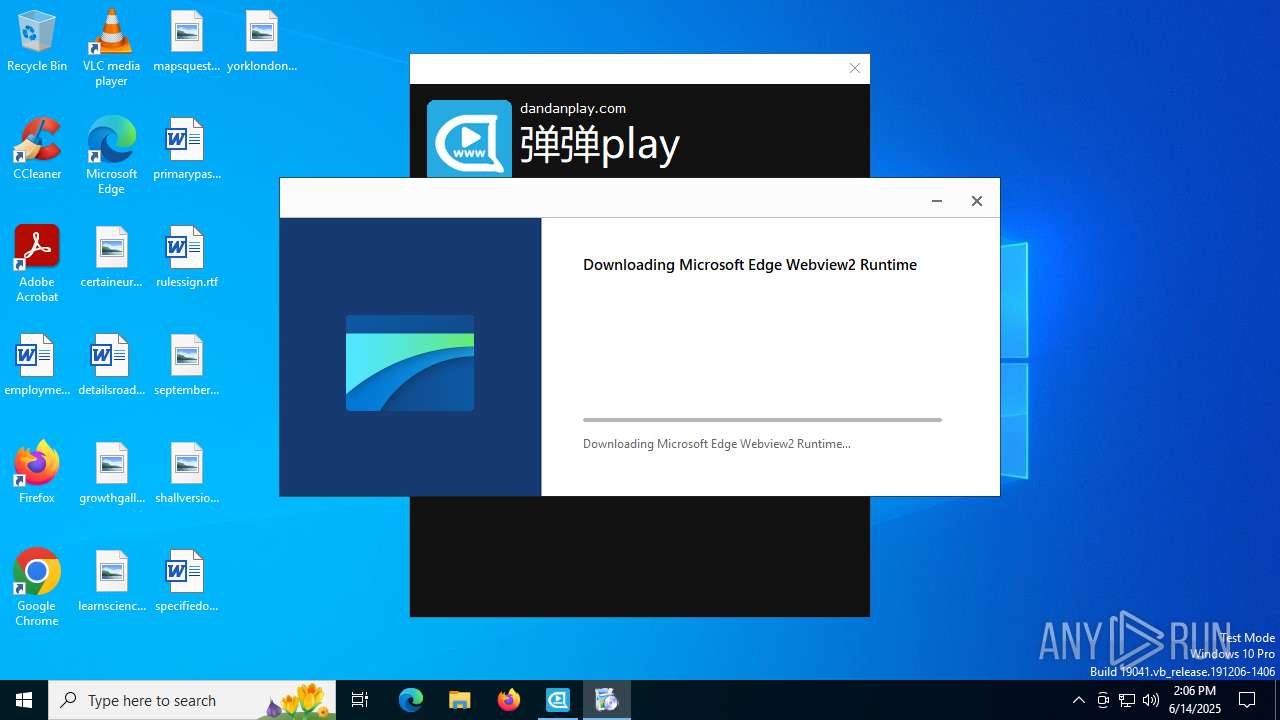
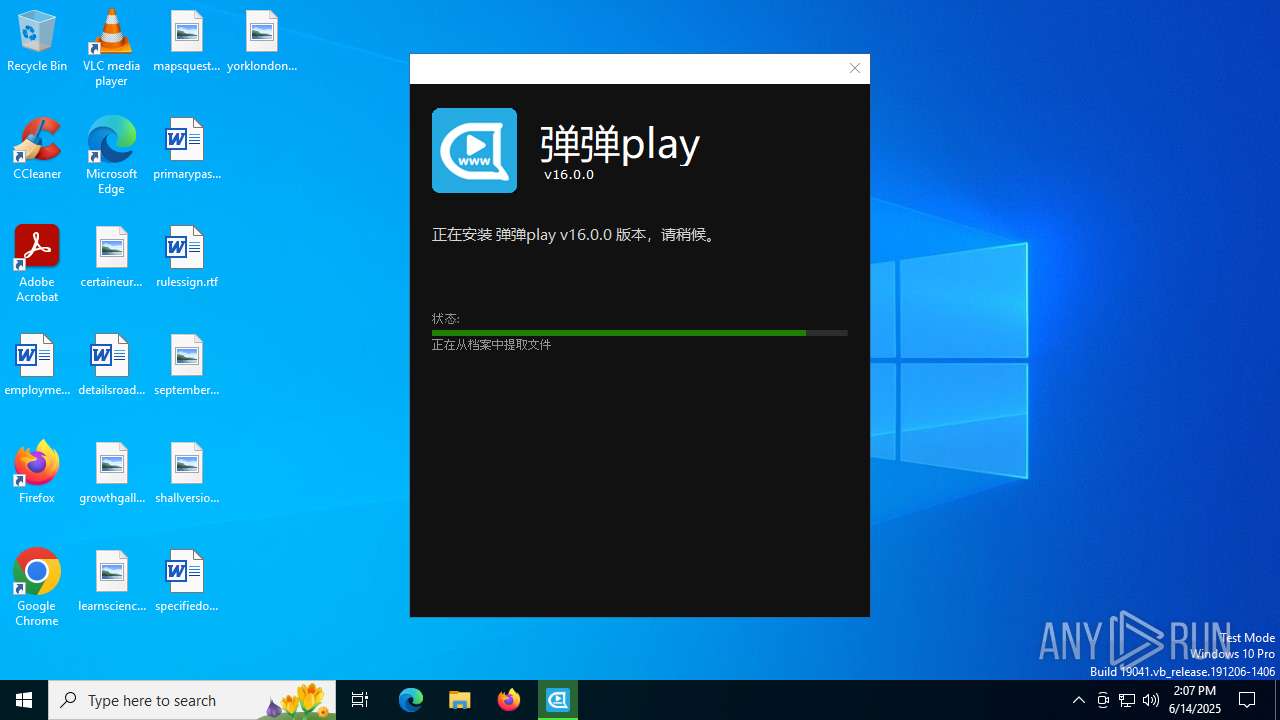
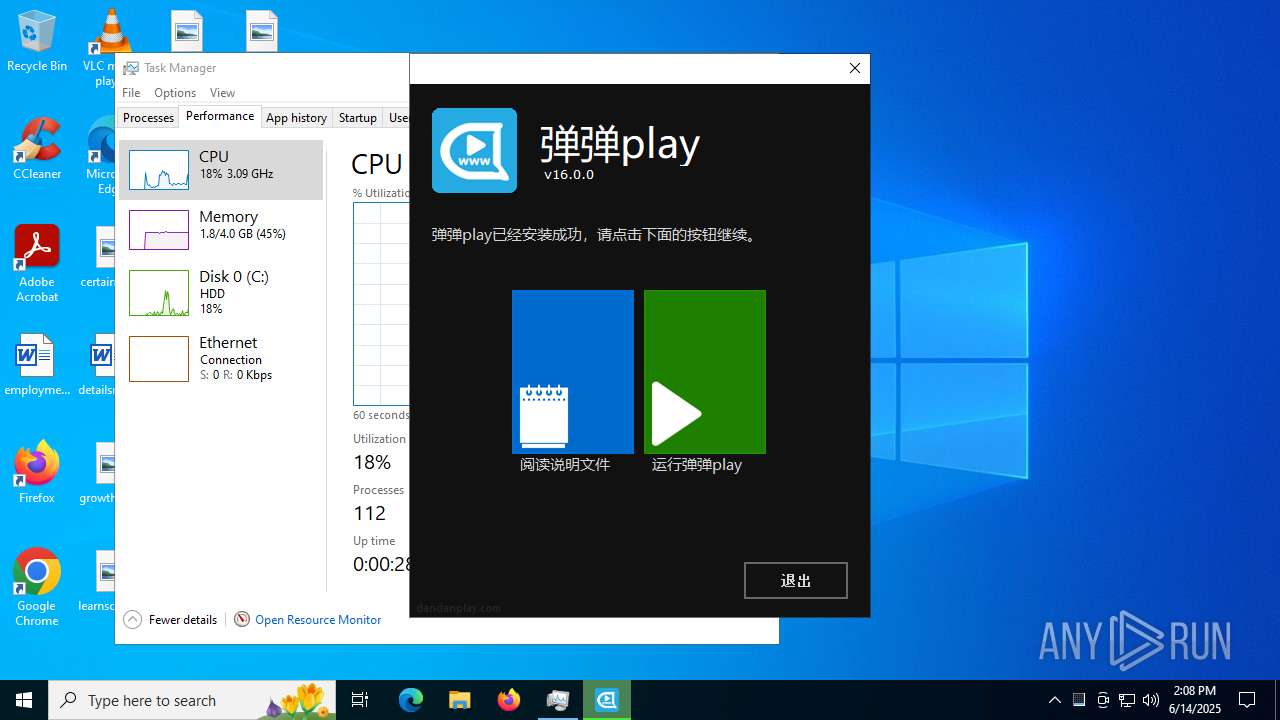
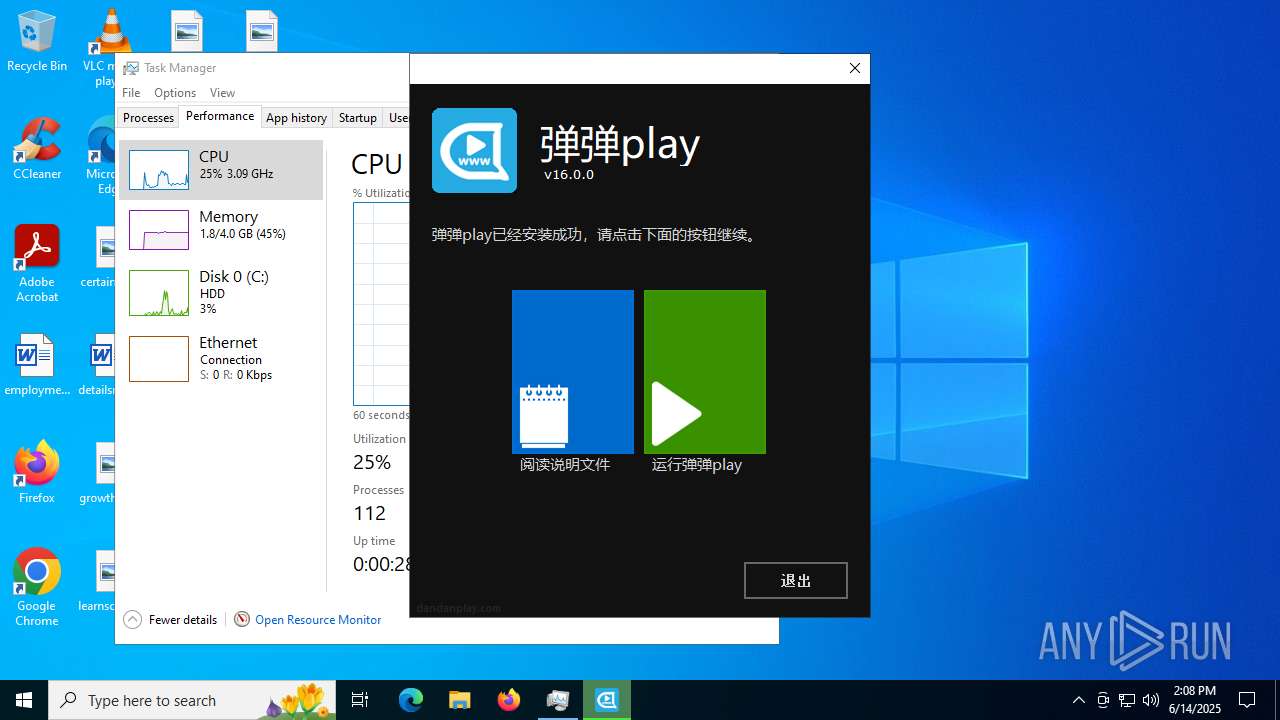
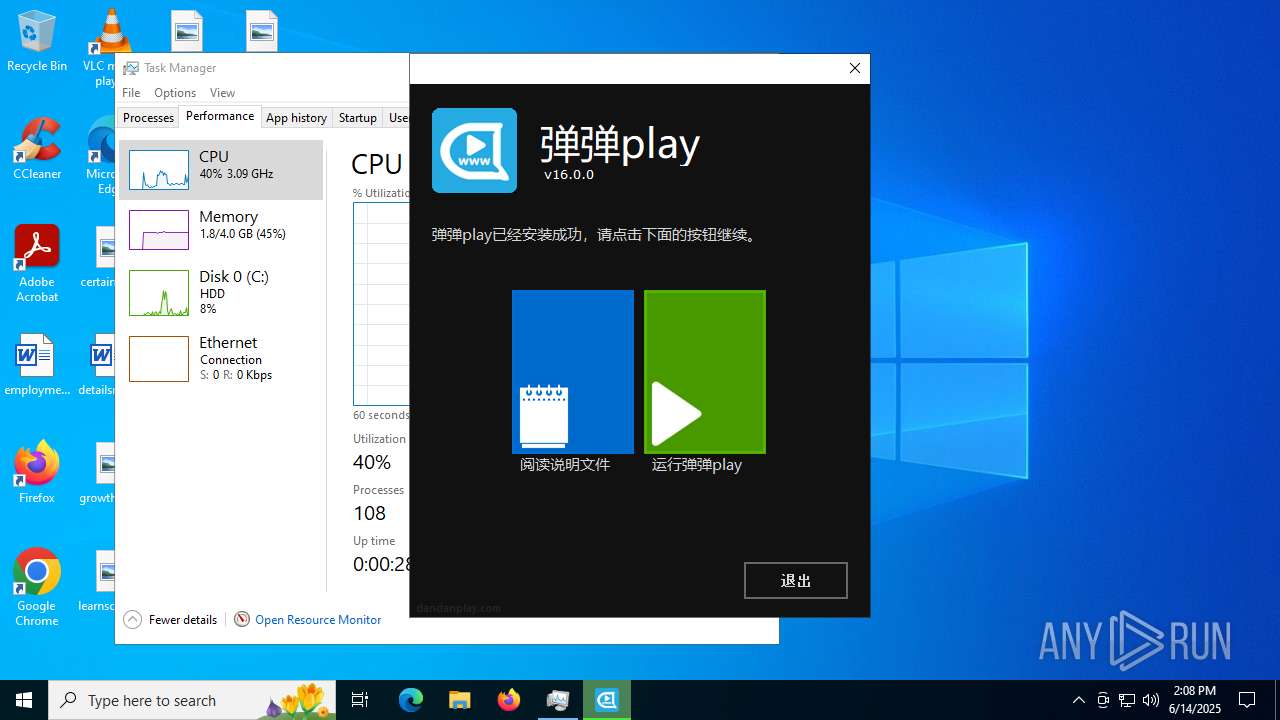
- dandanplay-x64_16.0.0.exe (PID: 1472)
Reads security settings of Internet Explorer
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdgeUpdate.exe (PID: 7768)
Reads the Windows owner or organization settings
- dandanplay-x64_16.0.0.exe (PID: 1472)
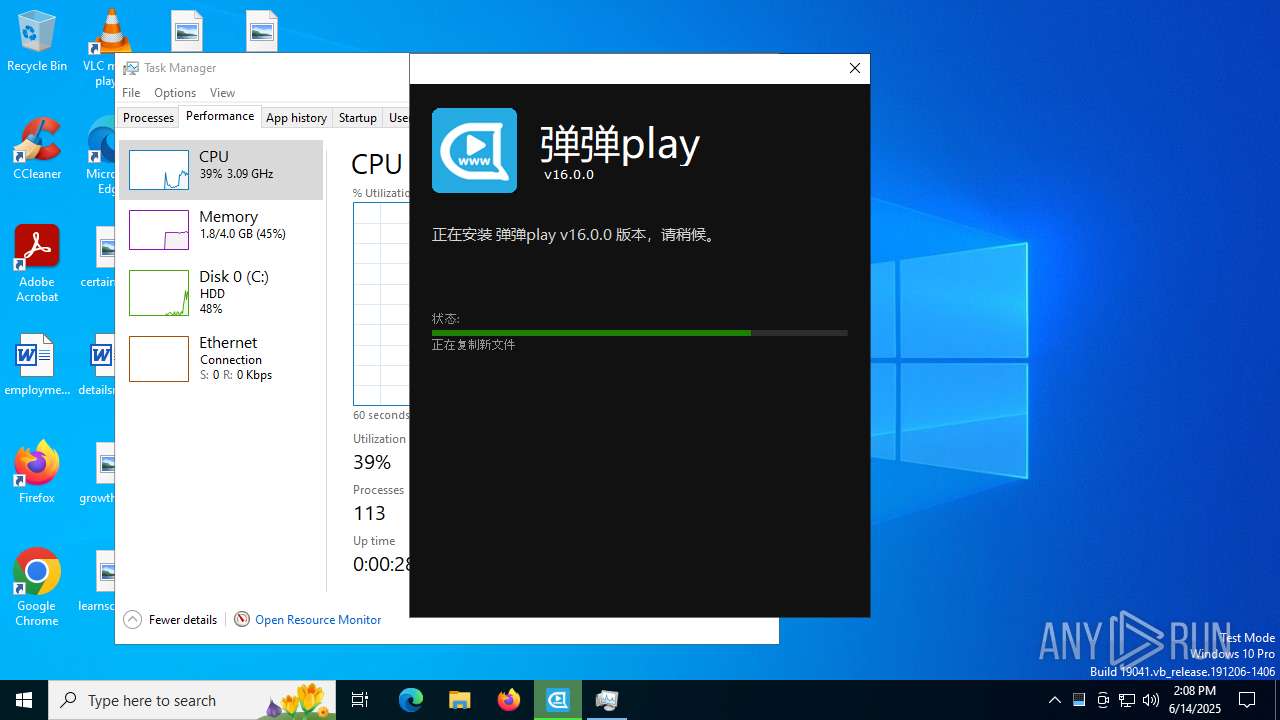
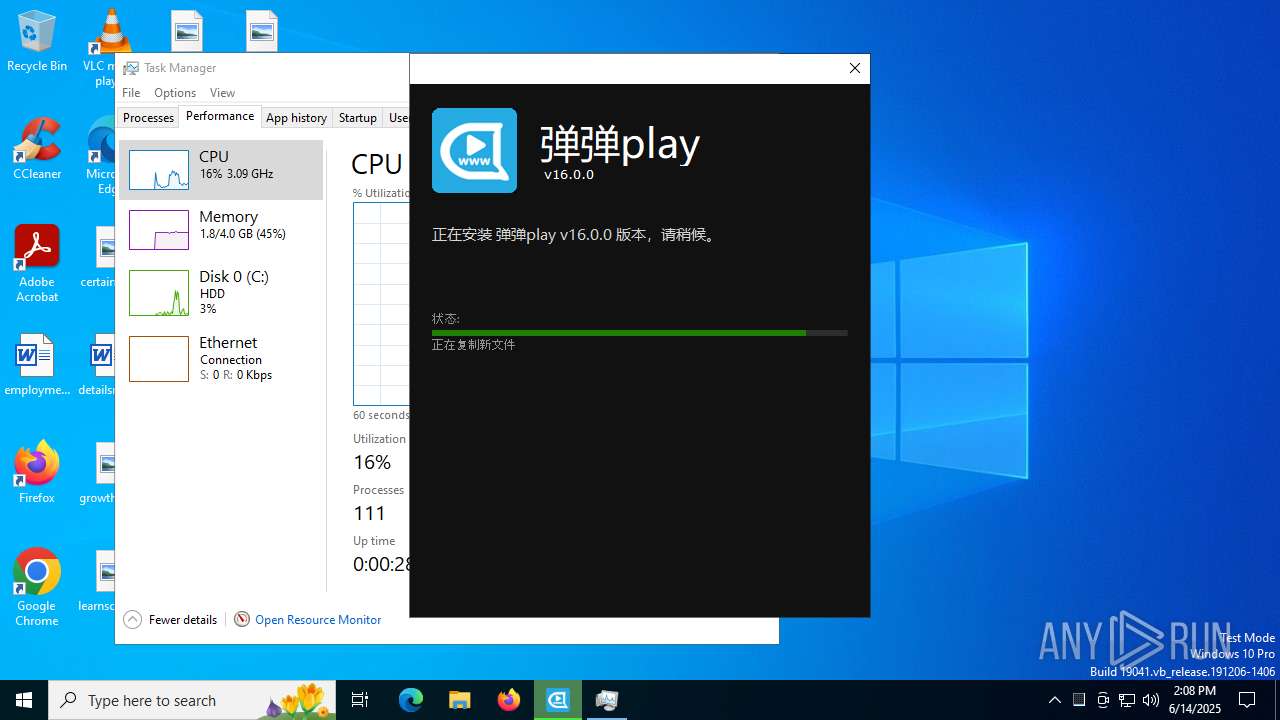
Executable content was dropped or overwritten
- dandanplay-x64_16.0.0.exe (PID: 1472)
- dandanplay-x64_16.0.0.exe (PID: 7628)
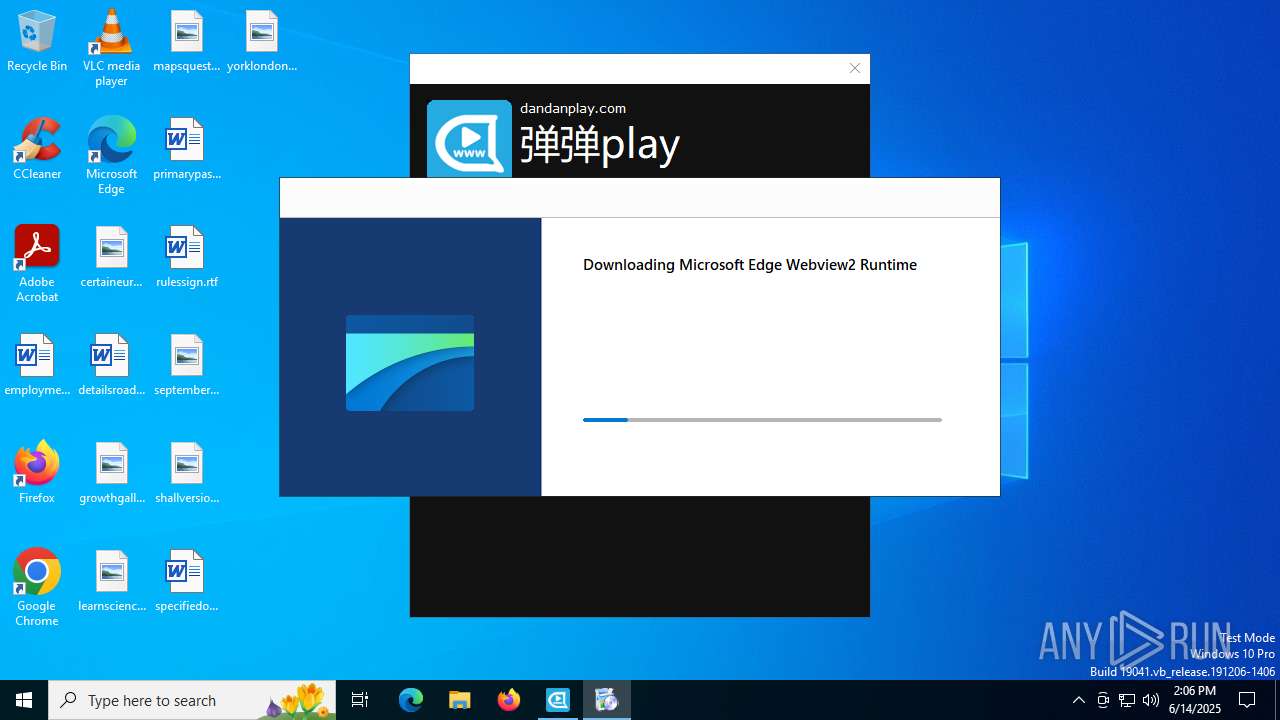
- MicrosoftEdgeWebview2Setup.exe (PID: 6700)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1520)
- setup.exe (PID: 3160)
- dandanplay-x64_16.0.0.exe (PID: 6292)
Process drops legitimate windows executable
- dandanplay-x64_16.0.0.exe (PID: 7628)
- MicrosoftEdgeWebview2Setup.exe (PID: 6700)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1520)
- setup.exe (PID: 3160)
- msiexec.exe (PID: 6320)
- dandanplay-x64_16.0.0.exe (PID: 1472)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 7060)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7672)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7728)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 432)
- MicrosoftEdgeUpdate.exe (PID: 3196)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7060)
There is functionality for taking screenshot (YARA)
- dandanplay-x64_16.0.0.exe (PID: 1472)
- dandanplay-x64_16.0.0.exe (PID: 6292)
Application launched itself
- setup.exe (PID: 3160)
- MicrosoftEdgeUpdate.exe (PID: 7768)
- dandanplay-x64_16.0.0.exe (PID: 1472)
Detects AdvancedInstaller (YARA)
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 7504)
- dandanplay-x64_16.0.0.exe (PID: 6292)
Searches for installed software
- setup.exe (PID: 3160)
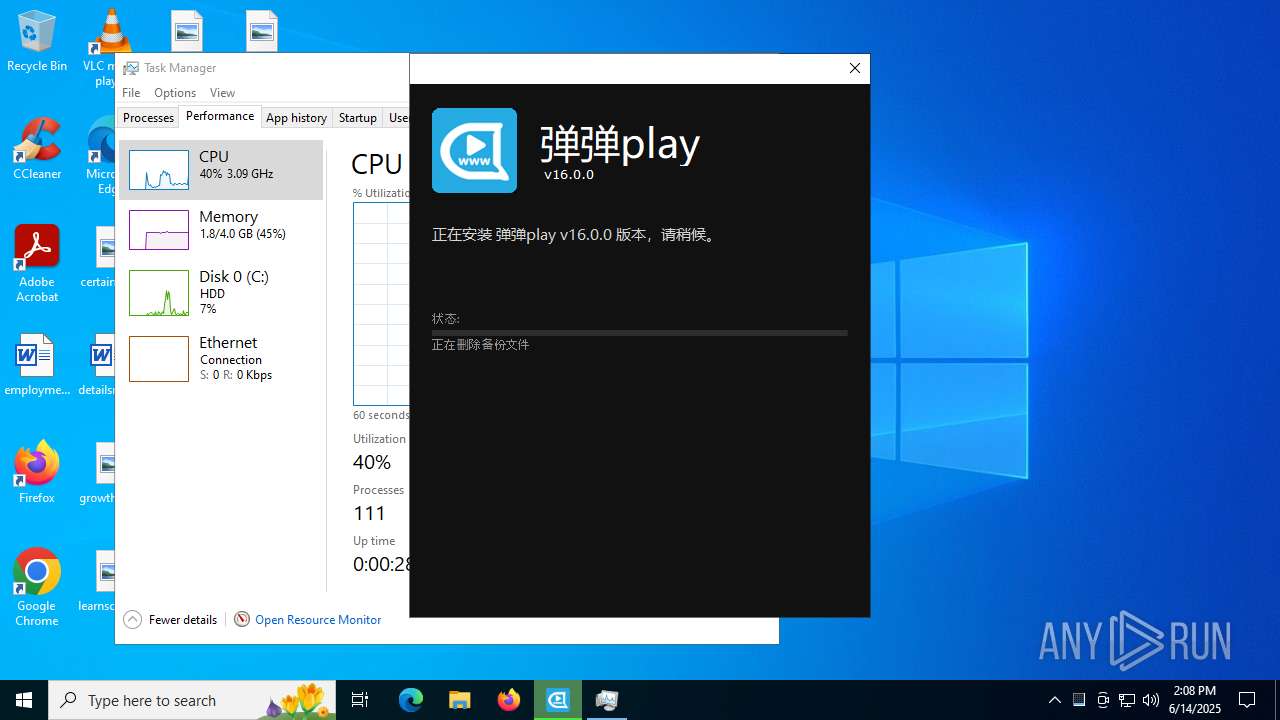
Creates a software uninstall entry
- setup.exe (PID: 3160)
The process drops C-runtime libraries
- msiexec.exe (PID: 6320)
- dandanplay-x64_16.0.0.exe (PID: 1472)
Reads Internet Explorer settings
- dandanplay-x64_16.0.0.exe (PID: 1472)
INFO
Checks supported languages
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 6320)
- msiexec.exe (PID: 7504)
- dandanplay-x64_16.0.0.exe (PID: 7628)
- MicrosoftEdgeWebview2Setup.exe (PID: 6700)
- MicrosoftEdgeUpdate.exe (PID: 3196)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7672)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7728)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 432)
- MicrosoftEdgeUpdate.exe (PID: 7768)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdgeUpdate.exe (PID: 4664)
- MicrosoftEdgeUpdate.exe (PID: 2064)
- setup.exe (PID: 592)
- setup.exe (PID: 3160)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1520)
- MicrosoftEdgeUpdate.exe (PID: 2976)
Application launched itself
- chrome.exe (PID: 4216)
Creates files or folders in the user directory
- dandanplay-x64_16.0.0.exe (PID: 1472)
- dandanplay-x64_16.0.0.exe (PID: 7628)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdgeUpdate.exe (PID: 7768)
- setup.exe (PID: 592)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1520)
- setup.exe (PID: 3160)
Executable content was dropped or overwritten
- chrome.exe (PID: 4216)
- msiexec.exe (PID: 6320)
Reads the computer name
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 6320)
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 3196)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7672)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7728)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdgeUpdate.exe (PID: 4664)
- MicrosoftEdgeUpdate.exe (PID: 7768)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 432)
- MicrosoftEdgeUpdate.exe (PID: 2064)
- setup.exe (PID: 3160)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1520)
- MicrosoftEdgeUpdate.exe (PID: 2976)
Reads Environment values
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 2064)
- MicrosoftEdgeUpdate.exe (PID: 2976)
Reads the machine GUID from the registry
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7768)
Reads the software policy settings
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 2064)
- MicrosoftEdgeUpdate.exe (PID: 7768)
- slui.exe (PID: 7936)
- MicrosoftEdgeUpdate.exe (PID: 2976)
The sample compiled with english language support
- dandanplay-x64_16.0.0.exe (PID: 1472)
- dandanplay-x64_16.0.0.exe (PID: 7628)
- MicrosoftEdgeWebview2Setup.exe (PID: 6700)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1520)
- setup.exe (PID: 3160)
- msiexec.exe (PID: 6320)
Create files in a temporary directory
- dandanplay-x64_16.0.0.exe (PID: 1472)
- MicrosoftEdgeWebview2Setup.exe (PID: 6700)
Process checks computer location settings
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7060)
- setup.exe (PID: 3160)
Launching a file from a Registry key
- msiexec.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7060)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 7768)
- MicrosoftEdgeUpdate.exe (PID: 2064)
- slui.exe (PID: 7936)
- MicrosoftEdgeUpdate.exe (PID: 2976)
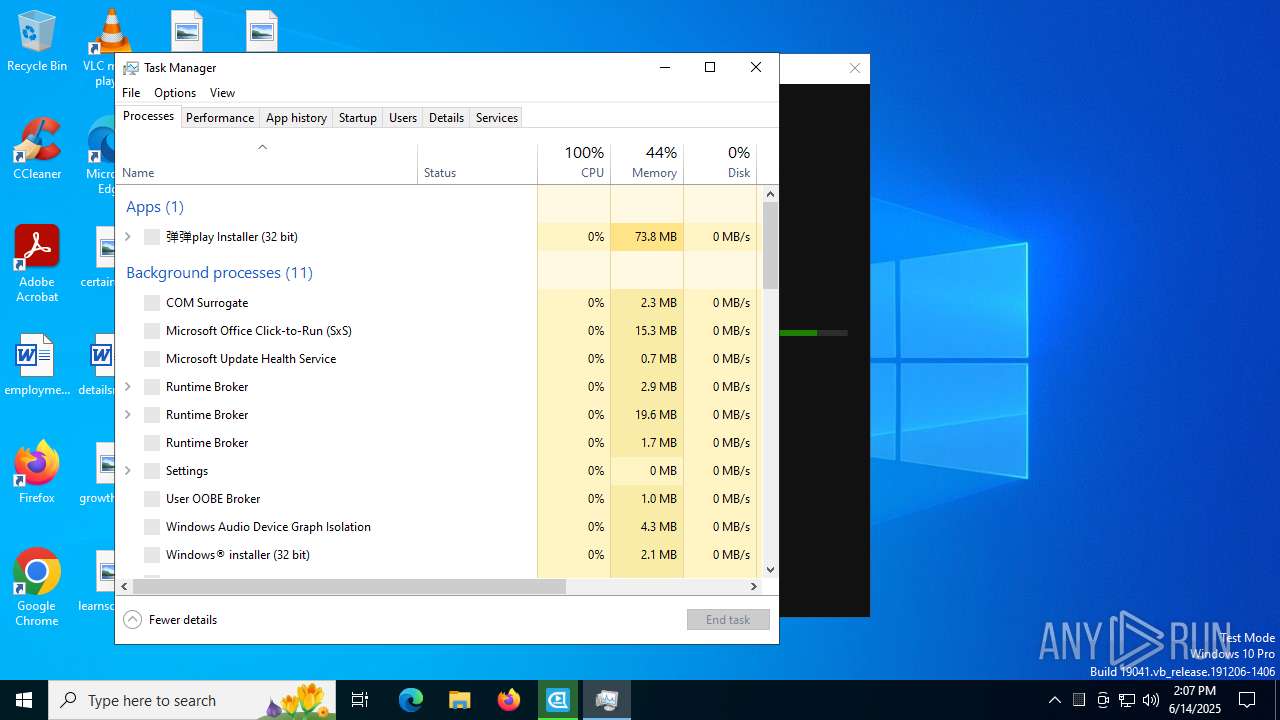
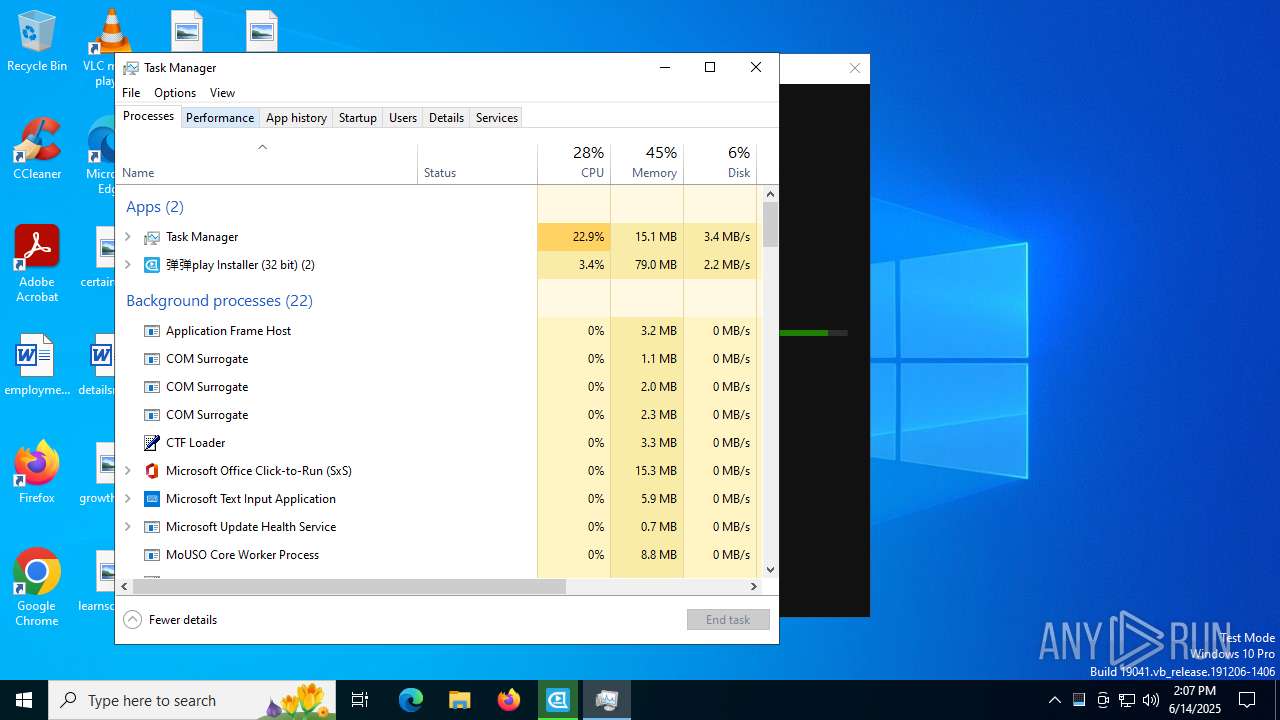
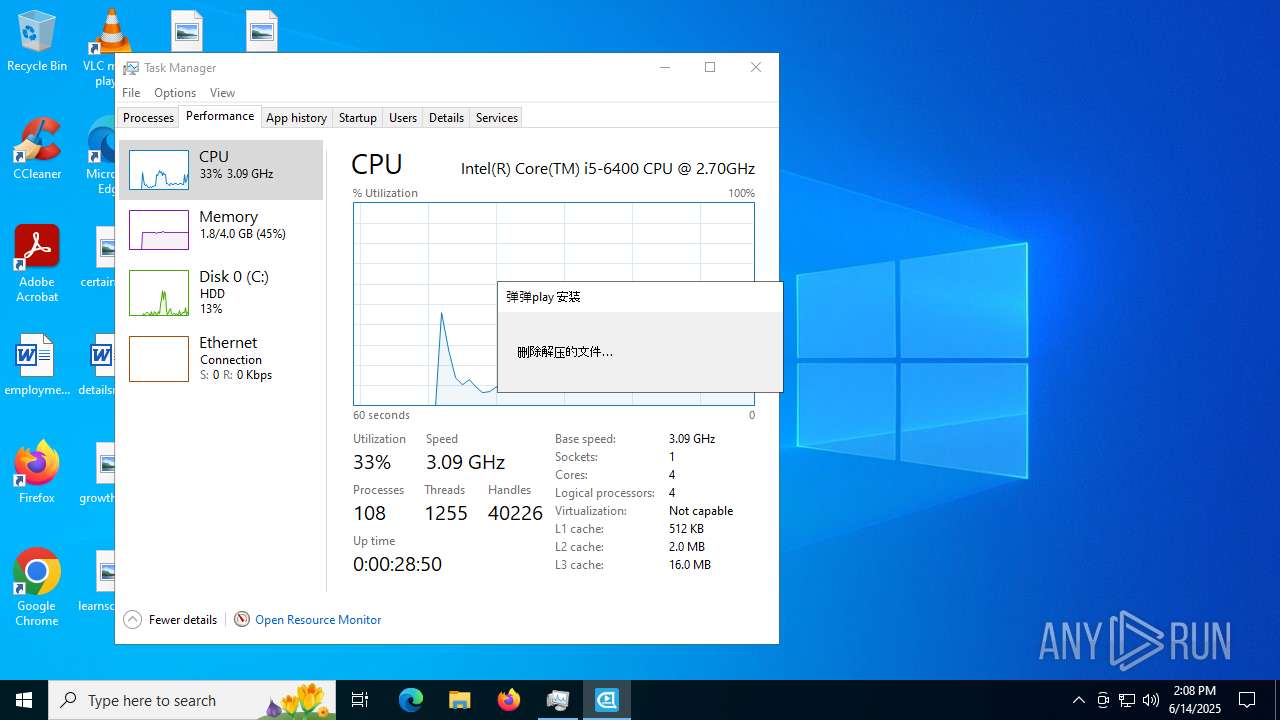
Manual execution by a user
- Taskmgr.exe (PID: 6620)
- Taskmgr.exe (PID: 7408)
The sample compiled with german language support
- dandanplay-x64_16.0.0.exe (PID: 1472)
- msiexec.exe (PID: 6320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
45
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.175.27\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.175.27\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.175.27 Modules
| |||||||||||||||
| 592 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{1C638FCC-70C2-42A1-A03A-40C4C45CE2F7}\EDGEMITMP_10614.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=137.0.7151.104 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{1C638FCC-70C2-42A1-A03A-40C4C45CE2F7}\EDGEMITMP_10614.tmp\setup.exe --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=137.0.3296.83 --initial-client-data=0x248,0x24c,0x250,0x224,0x254,0x7ff7096453f8,0x7ff709645404,0x7ff709645410 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{1C638FCC-70C2-42A1-A03A-40C4C45CE2F7}\EDGEMITMP_10614.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 137.0.3296.83 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc4383fff8,0x7ffc43840004,0x7ffc43840010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4344,i,5704000988227320772,7274291803251588950,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3420,i,5704000988227320772,7274291803251588950,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3452 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
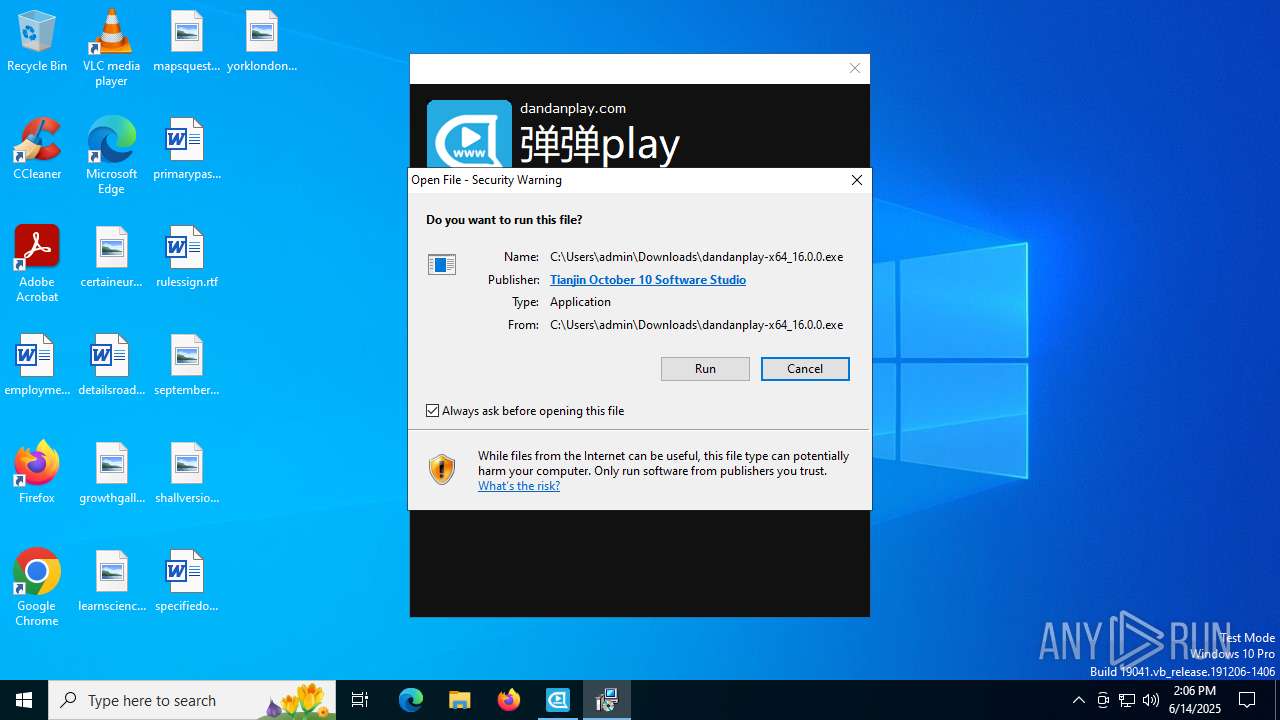
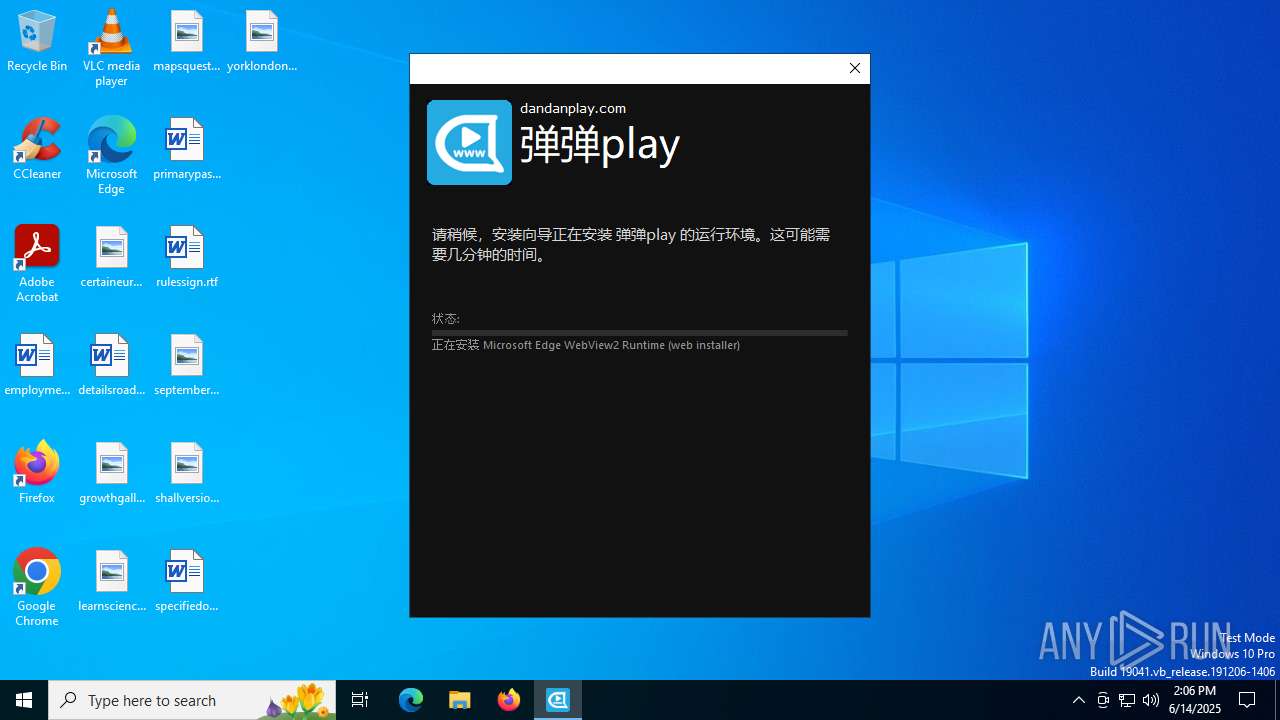
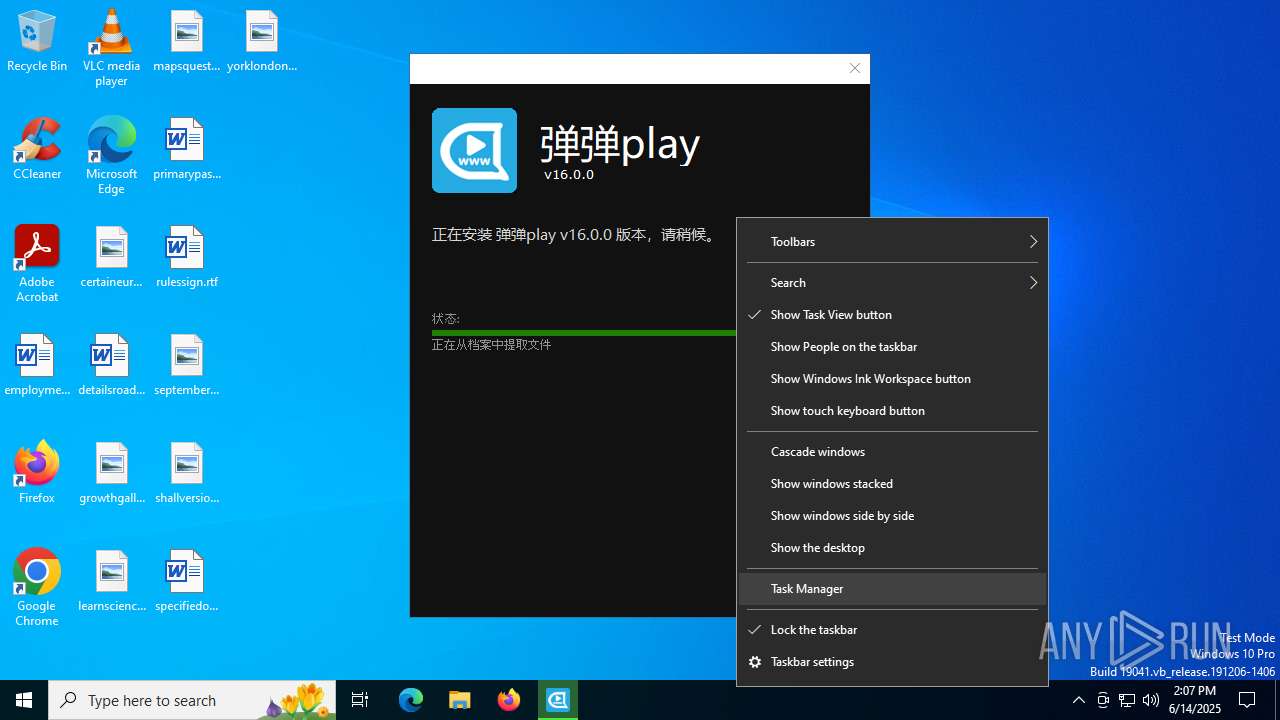
| 1472 | "C:\Users\admin\Downloads\dandanplay-x64_16.0.0.exe" | C:\Users\admin\Downloads\dandanplay-x64_16.0.0.exe | chrome.exe | ||||||||||||
User: admin Company: dandanplay.com Integrity Level: MEDIUM Description: 弹弹play Installer Exit code: 0 Version: 16.0.0 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{1C638FCC-70C2-42A1-A03A-40C4C45CE2F7}\MicrosoftEdge_X64_137.0.3296.83.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{1C638FCC-70C2-42A1-A03A-40C4C45CE2F7}\MicrosoftEdge_X64_137.0.3296.83.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 137.0.3296.83 Modules
| |||||||||||||||
| 1652 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{E2B3C97F-6AE1-41AC-817A-F6F92166D7DD} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4xNzUuMjciIHNoZWxsX3ZlcnNpb249IjEuMy4xNzUuMjciIGlzbWFjaGluZT0iMCIgc2Vzc2lvbmlkPSJ7NzBCQzNGMTUtNTk5MS00OTUxLUIzNUItRDY5NzJGQzEyQjBFfSIgdXNlcmlkPSJ7RDM2QUM4NDMtNTQwRi00RTUwLUJFQjAtMENGNUNEOEQwQzM2fSIgaW5zdGFsbHNvdXJjZT0idGFnZ2VkbWkiIHJlcXVlc3RpZD0iezYyNEJDQTFGLTQ5MzktNDJCNy1CRUNDLTVBMzNGMDc5MDk5N30iIGRlZHVwPSJjciIgZG9tYWluam9pbmVkPSIwIj48aHcgbG9naWNhbF9jcHVzPSI0IiBwaHlzbWVtb3J5PSI0IiBkaXNrX3R5cGU9IjIiIHNzZT0iMSIgc3NlMj0iMSIgc3NlMz0iMSIgc3NzZTM9IjEiIHNzZTQxPSIxIiBzc2U0Mj0iMSIgYXZ4PSIxIi8-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjEwLjAuMTkwNDUuNDA0NiIgc3A9IiIgYXJjaD0ieDY0IiBwcm9kdWN0X3R5cGU9IjQ4IiBpc193aXA9IjAiIGlzX2luX2xvY2tkb3duX21vZGU9IjAiLz48b2VtIHByb2R1Y3RfbWFudWZhY3R1cmVyPSJERUxMIiBwcm9kdWN0X25hbWU9IkRFTEwiLz48ZXhwIGV0YWc9IiIvPjxhcHAgYXBwaWQ9IntGM0M0RkUwMC1FRkQ1LTQwM0ItOTU2OS0zOThBMjBGMUJBNEF9IiB2ZXJzaW9uPSIiIG5leHR2ZXJzaW9uPSIxLjMuMTc1LjI3IiBsYW5nPSIiIGJyYW5kPSIiIGNsaWVudD0iIj48ZXZlbnQgZXZlbnR0eXBlPSIyIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBzeXN0ZW1fdXB0aW1lX3RpY2tzPSIxNjA5MzA3OTQxNiIgaW5zdGFsbF90aW1lX21zPSI1MTYiLz48L2FwcD48L3JlcXVlc3Q- | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.175.27 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
43 392
Read events
40 944
Write events
2 349
Delete events
99
Modification events
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (4216) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (7504) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\AiTemp |
| Operation: | delete value | Name: | C__Users_admin_Downloads_dandanplay-x64_16.0.0.exe |
Value: | |||
Executable files
1 453
Suspicious files
183
Text files
239
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF176ee6.TMP | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF176f15.TMP | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF176f15.TMP | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF176f15.TMP | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF176f15.TMP | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF176f15.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
240
DNS requests
183
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4012 | chrome.exe | GET | 200 | 142.250.74.206:80 | http://clients2.google.com/time/1/current?cup2key=8:_PphYDzhJNngFaO4RUVf8NbxpQwdszrjtWY8QMnL_9o&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7760 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4216 | chrome.exe | GET | 200 | 23.50.131.132:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQCZo4AKJlU7ZavcboSms%2Bo5 | unknown | — | — | whitelisted |
4216 | chrome.exe | GET | 200 | 23.50.131.150:80 | http://ccsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRxypYNH69rICCzQBIRXN0YAFa3AAQU3XRdTADbe5%2BgdMqxbvc8wDLAcM0CEEUmJwBlfYWjGvblyxt%2FyJc%3D | unknown | — | — | unknown |
7760 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8164 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwmiglbaq6quecjufmamfsqupsa_2025.5.21.0/niikhdgajlphfehepabhhblakbdgeefj_2025.05.21.00_all_msqewqxesfaohilvaerhlfagai.crx3 | unknown | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwmiglbaq6quecjufmamfsqupsa_2025.5.21.0/niikhdgajlphfehepabhhblakbdgeefj_2025.05.21.00_all_msqewqxesfaohilvaerhlfagai.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4960 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4012 | chrome.exe | 142.250.185.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
4012 | chrome.exe | 142.250.74.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
4012 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4012 | chrome.exe | 18.172.112.127:443 | send-anywhere.com | — | US | whitelisted |
4012 | chrome.exe | 104.18.87.42:443 | cdn.cookielaw.org | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
send-anywhere.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
apis.google.com |
| whitelisted |
wcs.naver.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (send-anywhere .com) |
4012 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (send-anywhere .com) |
4012 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (send-anywhere .com) |
4012 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4012 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4012 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (send-anywhere .com) |
4012 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (send-anywhere .com) |
4012 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4012 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4012 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (send-anywhere .com) |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |