| File name: | unetbootin-windows-702.exe |
| Full analysis: | https://app.any.run/tasks/8752049f-5c79-4449-9520-65072654bbe6 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2024, 18:42:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | AC970460E91A32A128C813F9226ABE79 |
| SHA1: | DE3DCE853C08B385D43822AAAFC55D1E19F6055F |
| SHA256: | 65BA5FF090BE1CC96DEC40509C9002582F4663634CB63B311941321907701483 |
| SSDEEP: | 98304:c5j1ftNc6uZxPyiQ7BesOAIl9mUfn9HKzbg0bboER7QuK/4NLEk:K1fDtrN1xcmSn9HK/nRbqk |
MALICIOUS
Drops the executable file immediately after the start
- unetbootin-windows-702.exe (PID: 2380)
SUSPICIOUS
Searches for installed software
- unetbootin-windows-702.exe (PID: 2380)
Reads the Internet Settings
- unetbootin-windows-702.exe (PID: 2380)
Drops 7-zip archiver for unpacking
- unetbootin-windows-702.exe (PID: 2380)
Executable content was dropped or overwritten
- unetbootin-windows-702.exe (PID: 2380)
Starts CMD.EXE for commands execution
- unetbootin-windows-702.exe (PID: 2380)
Reads security settings of Internet Explorer
- unetbootin-windows-702.exe (PID: 2380)
The executable file from the user directory is run by the CMD process
- sevnz.exe (PID: 896)
INFO
Checks supported languages
- unetbootin-windows-702.exe (PID: 2380)
- wmpnscfg.exe (PID: 3084)
- sevnz.exe (PID: 896)
Reads the computer name
- unetbootin-windows-702.exe (PID: 2380)
- wmpnscfg.exe (PID: 3084)
Reads the machine GUID from the registry
- unetbootin-windows-702.exe (PID: 2380)
Manual execution by a user
- wmpnscfg.exe (PID: 3084)
Create files in a temporary directory
- unetbootin-windows-702.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.34 |
| CodeSize: | 4849664 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | 7311360 |
| EntryPoint: | 0xb98810 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1.1 |
| ProductVersionNumber: | 1.1.1.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Geza Kovacs |
| FileVersion: | |
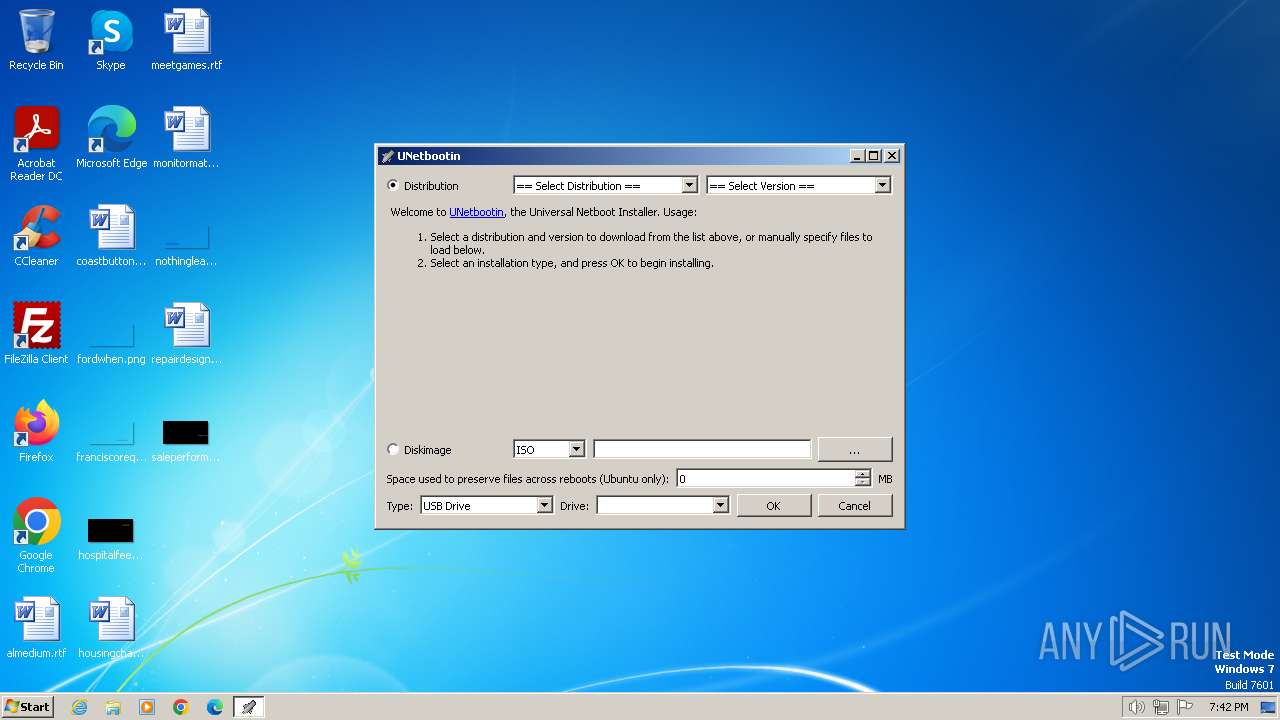
| FileDescription: | UNetbootin - Universal Netboot Installer - http://unetbootin.sourceforge.net |
| InternalName: | UNetbootin - Universal Netboot Installer |
| LegalCopyright: | Copyright - Geza Kovacs - License - GNU GPL v2+ |
| LegalTrademarks: | |
| OriginalFileName: | unetbootin.exe |
| ProductName: | UNetbootin - Universal Netboot Installer |
| ProductVersion: |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Users\admin\AppData\Local\Temp\sevnz.exe" -bd -slt l "C:/Users/admin/AppData/Local/Temp/un7408.iso" | C:\Users\admin\AppData\Local\Temp\sevnz.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 2 Version: 9.20 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\unetbootin-windows-702.exe" | C:\Users\admin\AppData\Local\Temp\unetbootin-windows-702.exe | explorer.exe | ||||||||||||
User: admin Company: Geza Kovacs Integrity Level: HIGH Description: UNetbootin - Universal Netboot Installer - http://unetbootin.sourceforge.net Version: Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\AppData\Local\Temp\unetbootin-windows-702.exe" | C:\Users\admin\AppData\Local\Temp\unetbootin-windows-702.exe | — | explorer.exe | |||||||||||
User: admin Company: Geza Kovacs Integrity Level: MEDIUM Description: UNetbootin - Universal Netboot Installer - http://unetbootin.sourceforge.net Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Windows\system32\cmd.exe" /c ""C:\Users\admin\AppData\Local\Temp\sevnz.exe" -bd -slt l "C:/Users/admin/AppData/Local/Temp/un7408.iso" > "C:/Users/admin/AppData/Local/Temp/un7549.ufl"" | C:\Windows\System32\cmd.exe | — | unetbootin-windows-702.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 065
Read events
1 056
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2380) unetbootin-windows-702.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: unetbootin-windows-702.exe | |||
| (PID) Process: | (2380) unetbootin-windows-702.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2380) unetbootin-windows-702.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2380) unetbootin-windows-702.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2380) unetbootin-windows-702.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | unetbootin-windows-702.exe | C:\unetbtin\ubnpathl.txt | — | |
MD5:— | SHA256:— | |||
| 2380 | unetbootin-windows-702.exe | C:\unetbtin\ubnfilel.txt | — | |
MD5:— | SHA256:— | |||
| 2380 | unetbootin-windows-702.exe | C:\Users\admin\AppData\Local\Temp\7z.dll | executable | |
MD5:04AD4B80880B32C94BE8D0886482C774 | SHA256:A1E1D1F0FFF4FCCCFBDFA313F3BDFEA4D3DFE2C2D9174A615BBC39A0A6929338 | |||
| 2380 | unetbootin-windows-702.exe | C:\Users\admin\AppData\Local\Temp\sevnz.exe | executable | |
MD5:A51D90F2F9394F5EA0A3ACAE3BD2B219 | SHA256:AC9674FEB8F2FAD20C1E046DE67F899419276AE79A60E8CC021A4BF472AE044F | |||
| 3236 | cmd.exe | C:\Users\admin\AppData\Local\Temp\un7549.ufl | text | |
MD5:2AE8E97EAA2284DF1DEE440FA481E77E | SHA256:4E3BB3B4DC82979B4E3B47F2B3321E4CBB2346424AEF3189A7F4FC7A6A3CCE56 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
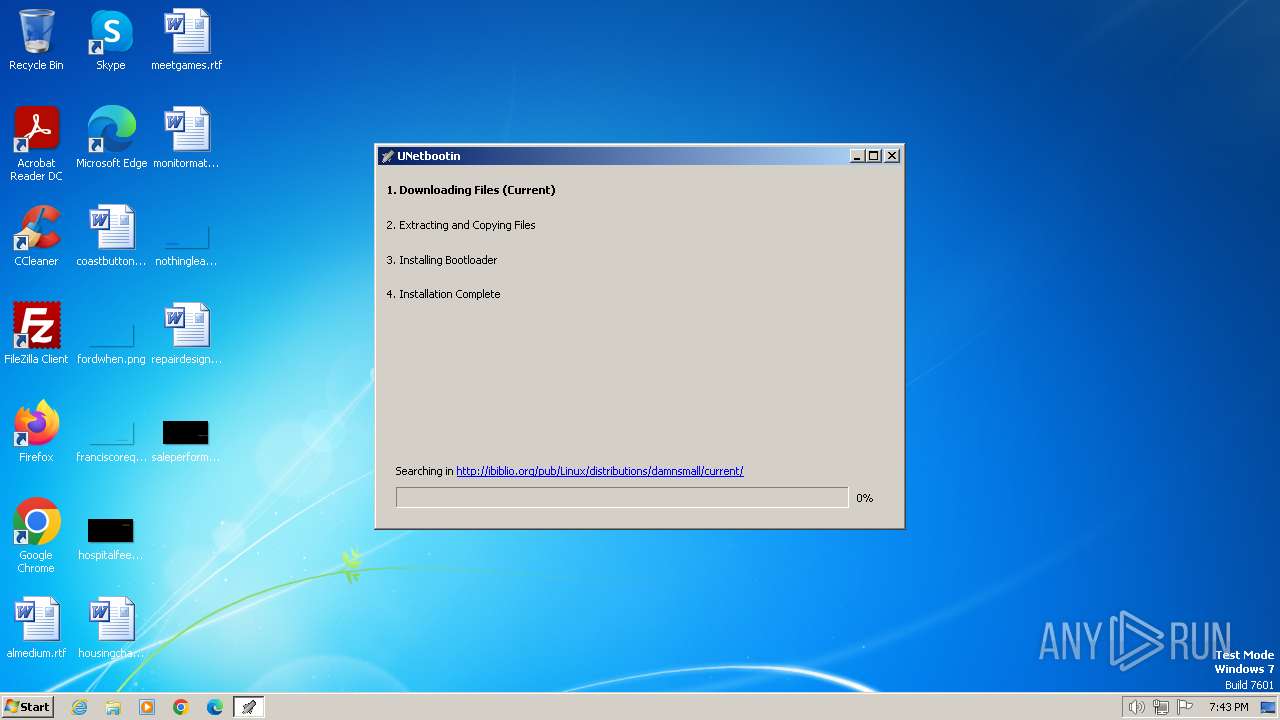
2380 | unetbootin-windows-702.exe | GET | 404 | 152.19.134.40:80 | http://ibiblio.org/pub/Linux/distributions/damnsmall/current/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2380 | unetbootin-windows-702.exe | 152.19.134.40:80 | ibiblio.org | UNC-CH | US | unknown |
2380 | unetbootin-windows-702.exe | 49.13.77.253:80 | gd.tuwien.ac.at | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ibiblio.org |
| unknown |
gd.tuwien.ac.at |
| unknown |
dns.msftncsi.com |
| shared |
Threats
3 ETPRO signatures available at the full report