| File name: | x64__installer___v4.7.5.msi |
| Full analysis: | https://app.any.run/tasks/249cec89-018f-4bdb-92e2-b1926e998c8f |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2024, 23:44:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {45BF3423-4EAA-4A0C-8D2E-F452ACEBFA1D}, Number of Words: 10, Subject: IcuApp, Author: Icuuq Cmpq, Name of Creating Application: IcuApp, Template: x64;2057, Comments: This installer database contains the logic and data required to install IcuApp., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Wed Jul 31 11:59:39 2024, Last Saved Time/Date: Wed Jul 31 11:59:39 2024, Last Printed: Wed Jul 31 11:59:39 2024, Number of Pages: 450 |
| MD5: | 8C96902F16CDA41DF6E8365443B5981F |
| SHA1: | 34CEBB174DA8B7DEEA983245088B40DE13F47088 |
| SHA256: | 65B5E28036D284429BF40698D3F8349680BBDE61381E1E19444A90C99C770716 |
| SSDEEP: | 196608:IFKDHPKOFfXWZQHvOJgdbOIkVBqjgnMn86M0WFd5ljUaWR261zVzgY/Dxqz:NrJZm7xBJnM86Q/BUaW/Jpn/ |
MALICIOUS
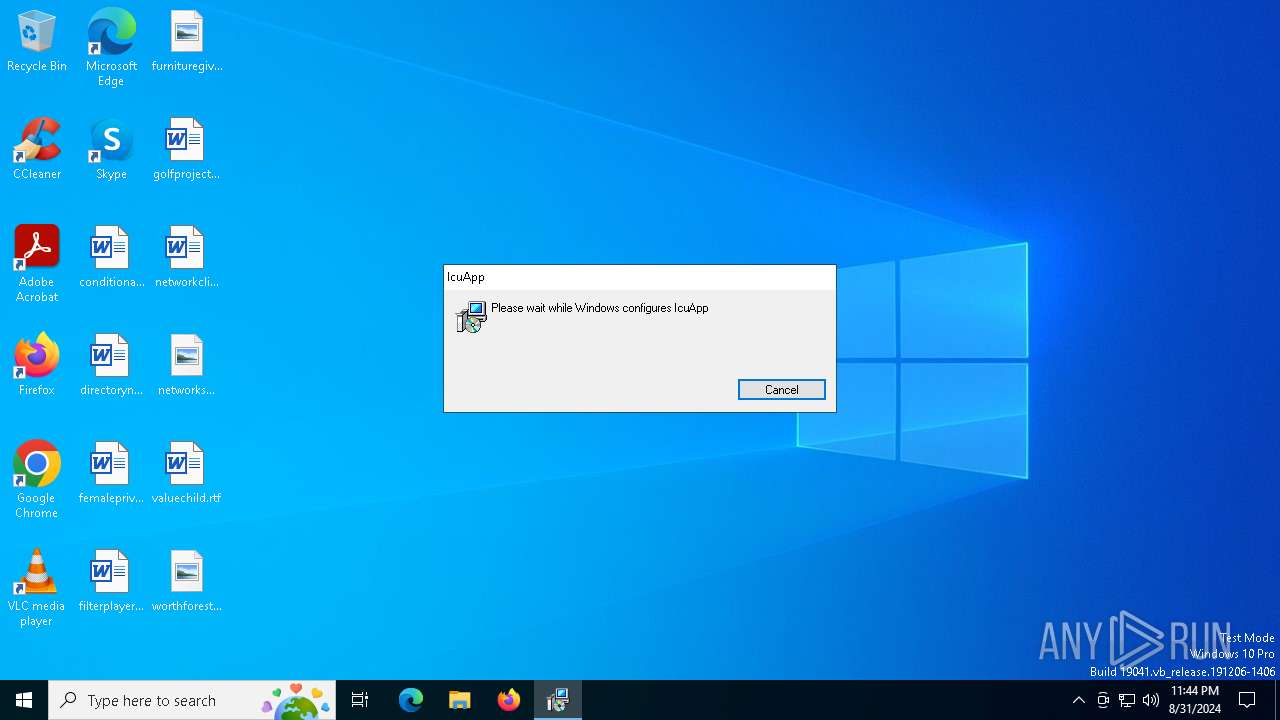
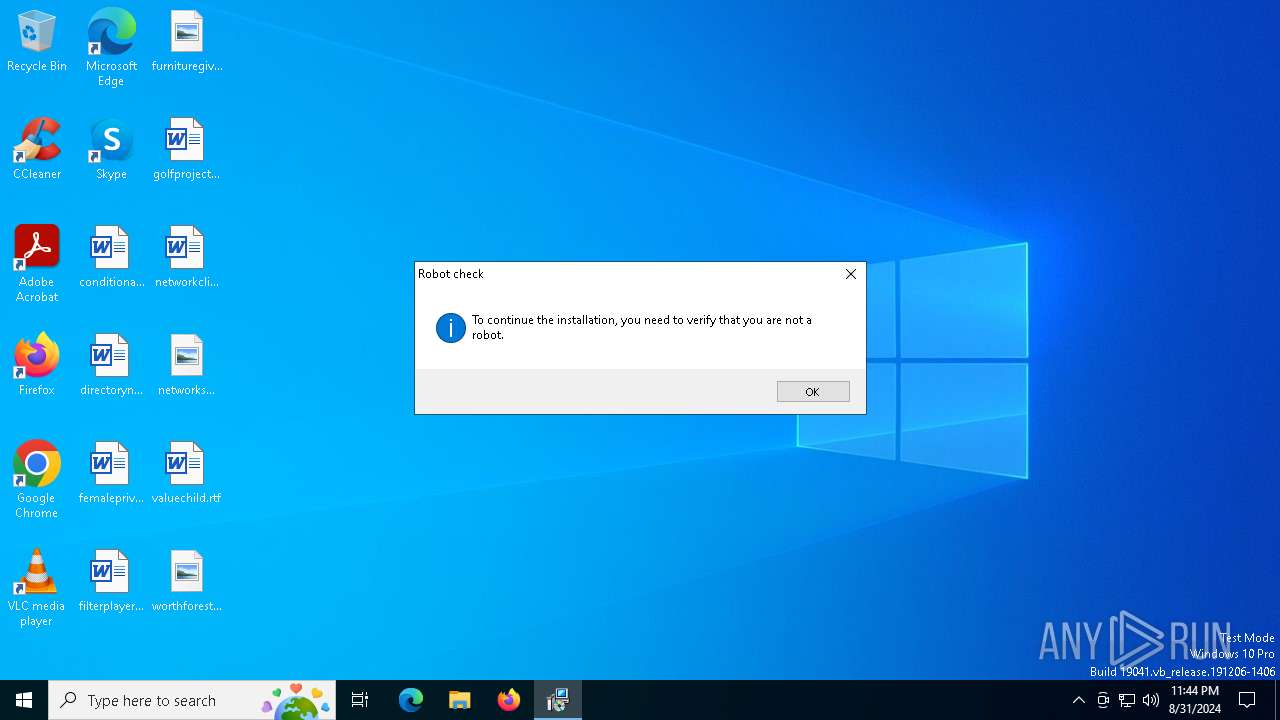
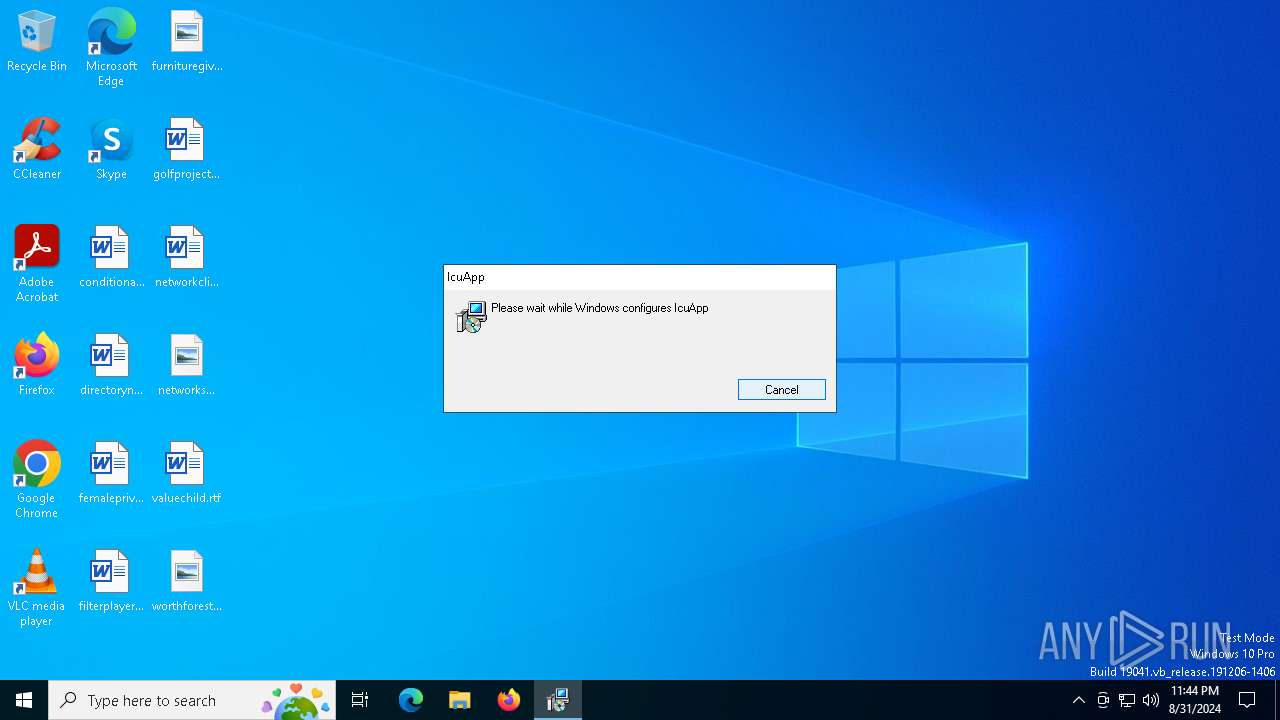
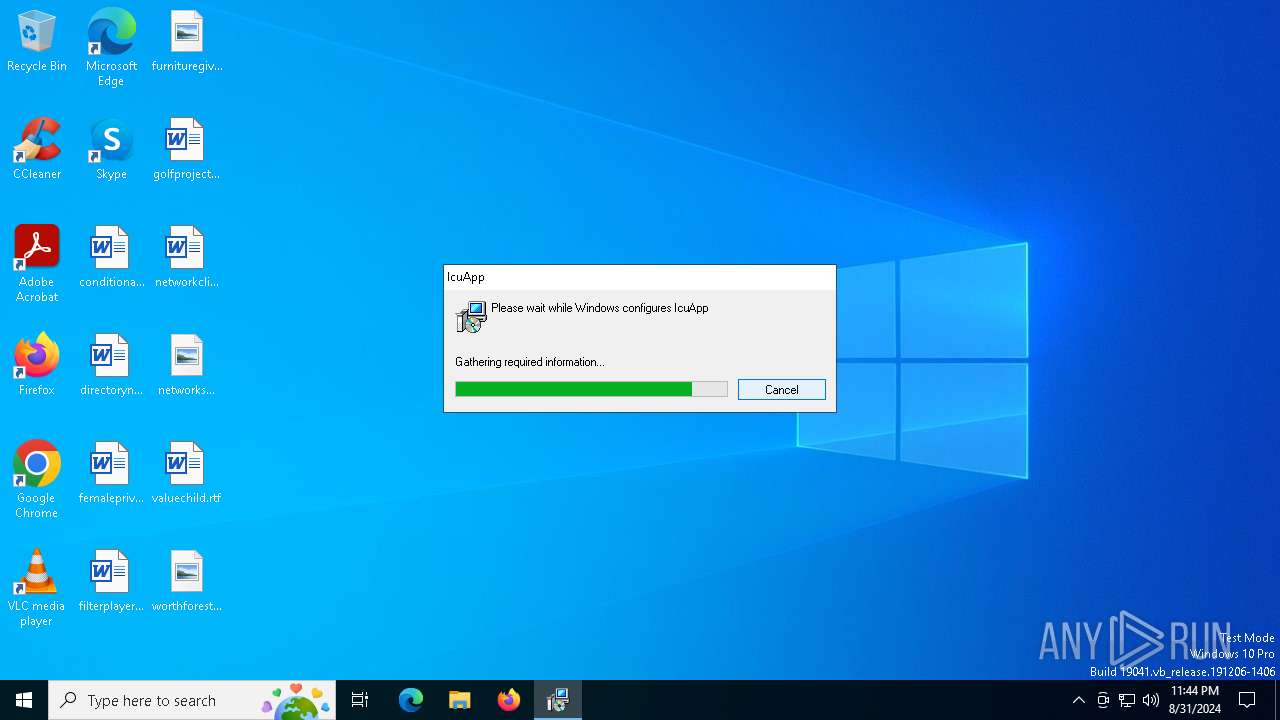
ROBOTDROPPER has been detected
- msiexec.exe (PID: 7052)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7052)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 780)
Checks Windows Trust Settings
- msiexec.exe (PID: 780)
Drops the executable file immediately after the start
- msiexec.exe (PID: 7052)
Process drops legitimate windows executable
- msiexec.exe (PID: 7052)
INFO
An automatically generated document
- msiexec.exe (PID: 6156)
Checks supported languages
- msiexec.exe (PID: 7052)
- msiexec.exe (PID: 780)
Reads the computer name
- msiexec.exe (PID: 780)
- msiexec.exe (PID: 7052)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7052)
Reads Environment values
- msiexec.exe (PID: 780)
Checks proxy server information
- msiexec.exe (PID: 780)
Reads the software policy settings
- msiexec.exe (PID: 780)
Creates files or folders in the user directory
- msiexec.exe (PID: 780)
- msiexec.exe (PID: 7052)
Creates a software uninstall entry
- msiexec.exe (PID: 7052)
Reads the machine GUID from the registry
- msiexec.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {45BF3423-4EAA-4A0C-8D2E-F452ACEBFA1D} |
| Words: | 10 |
| Subject: | IcuApp |
| Author: | Icuuq Cmpq |
| LastModifiedBy: | - |
| Software: | IcuApp |
| Template: | x64;2057 |
| Comments: | This installer database contains the logic and data required to install IcuApp. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:08:31 11:59:39 |
| ModifyDate: | 2024:08:31 11:59:39 |
| LastPrinted: | 2024:08:31 11:59:39 |
| Pages: | 450 |
Total processes
131
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | C:\Windows\syswow64\MsiExec.exe -Embedding 2A4061D0B0D88149C8518D5FC8FED629 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\x64__installer___v4.7.5.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7052 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 373
Read events
4 157
Write events
207
Delete events
9
Modification events
| (PID) Process: | (7052) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 8C1B0000D1D0BDBEFFFBDA01 | |||
| (PID) Process: | (7052) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 27F727C9B79DBCE3CC484C7EFBF32561F238A410357C034B6681815A1D6E0B62 | |||
| (PID) Process: | (7052) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (780) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
69
Suspicious files
31
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7052 | msiexec.exe | C:\Windows\Installer\12ba5f.msi | — | |
MD5:— | SHA256:— | |||
| 7052 | msiexec.exe | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\jmods\java.base.jmod | — | |
MD5:— | SHA256:— | |||
| 7052 | msiexec.exe | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\srv\classes.jsa | — | |
MD5:— | SHA256:— | |||
| 7052 | msiexec.exe | C:\Users\admin\AppData\Roaming\Icuuq Cmpq\IcuApp\srv\classes_nocoops.jsa | — | |
MD5:— | SHA256:— | |||
| 780 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:971C514F84BBA0785F80AA1C23EDFD79 | SHA256:F157ED17FCAF8837FA82F8B69973848C9B10A02636848F995698212A08F31895 | |||
| 7052 | msiexec.exe | C:\Windows\Installer\MSIBD22.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 780 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:61C0A21A61E81BEA2F1EEE3C20E824D5 | SHA256:A34301BB58700D59939DB1735746FE493C681E129EFD82A88A415DE6A0F93816 | |||
| 7052 | msiexec.exe | C:\Windows\Installer\MSICCB4.tmp | executable | |
MD5:54D74546C6AFE67B3D118C3C477C159A | SHA256:F9956417AF079E428631A6C921B79716D960C3B4917C6B7D17FF3CB945F18611 | |||
| 7052 | msiexec.exe | C:\Windows\Temp\~DF4146D4A7EF2CCD35.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 780 | msiexec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\licenseUser[1].htm | text | |
MD5:E99BB33727D338314912E86FBDEC87AF | SHA256:6856C5A3A26B5A3F2EAD70CA56870769D1FEE88F9C457F4360812F2203565824 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
31
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
780 | msiexec.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
780 | msiexec.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
5624 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5624 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6652 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1356 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
780 | msiexec.exe | 172.67.130.97:443 | get-license12.com | CLOUDFLARENET | US | unknown |
780 | msiexec.exe | 142.250.186.131:80 | c.pki.goog | GOOGLE | US | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2028 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
get-license12.com |
| unknown |
c.pki.goog |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |