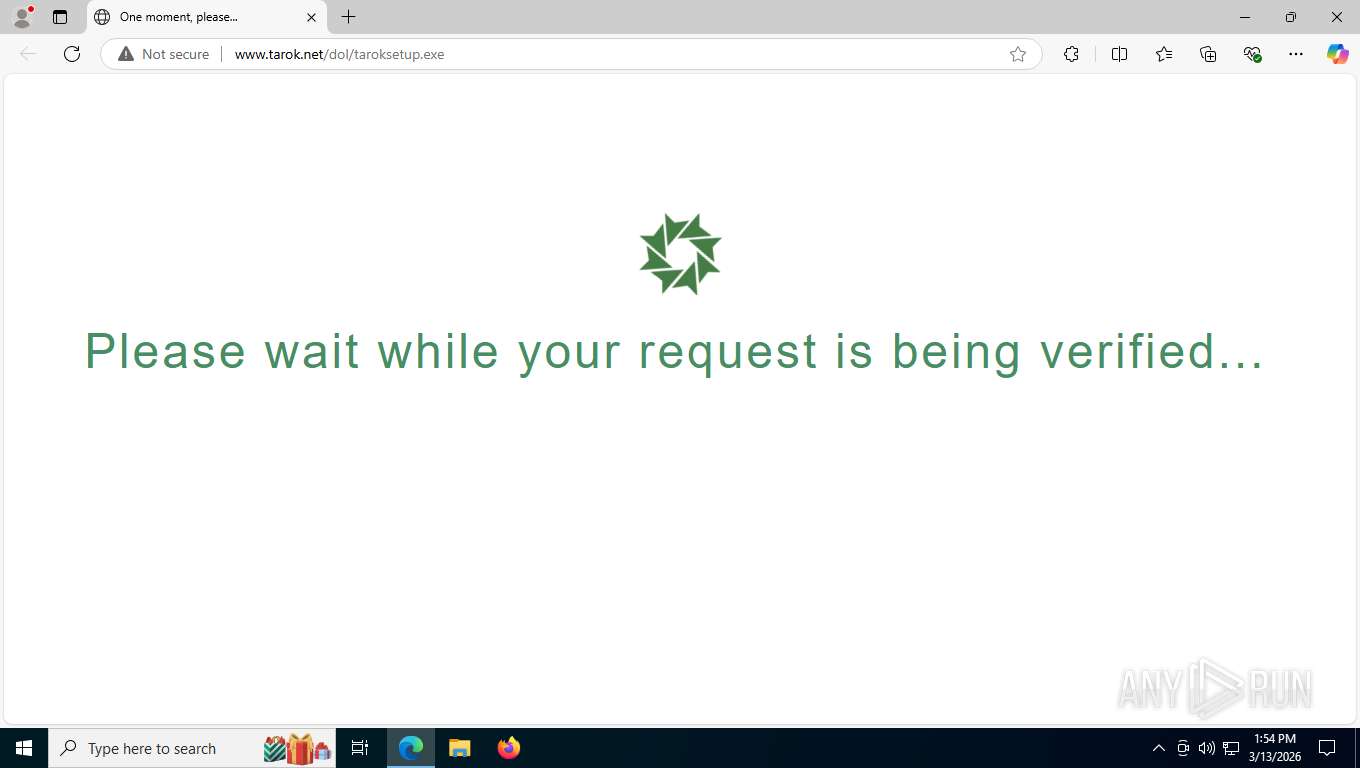
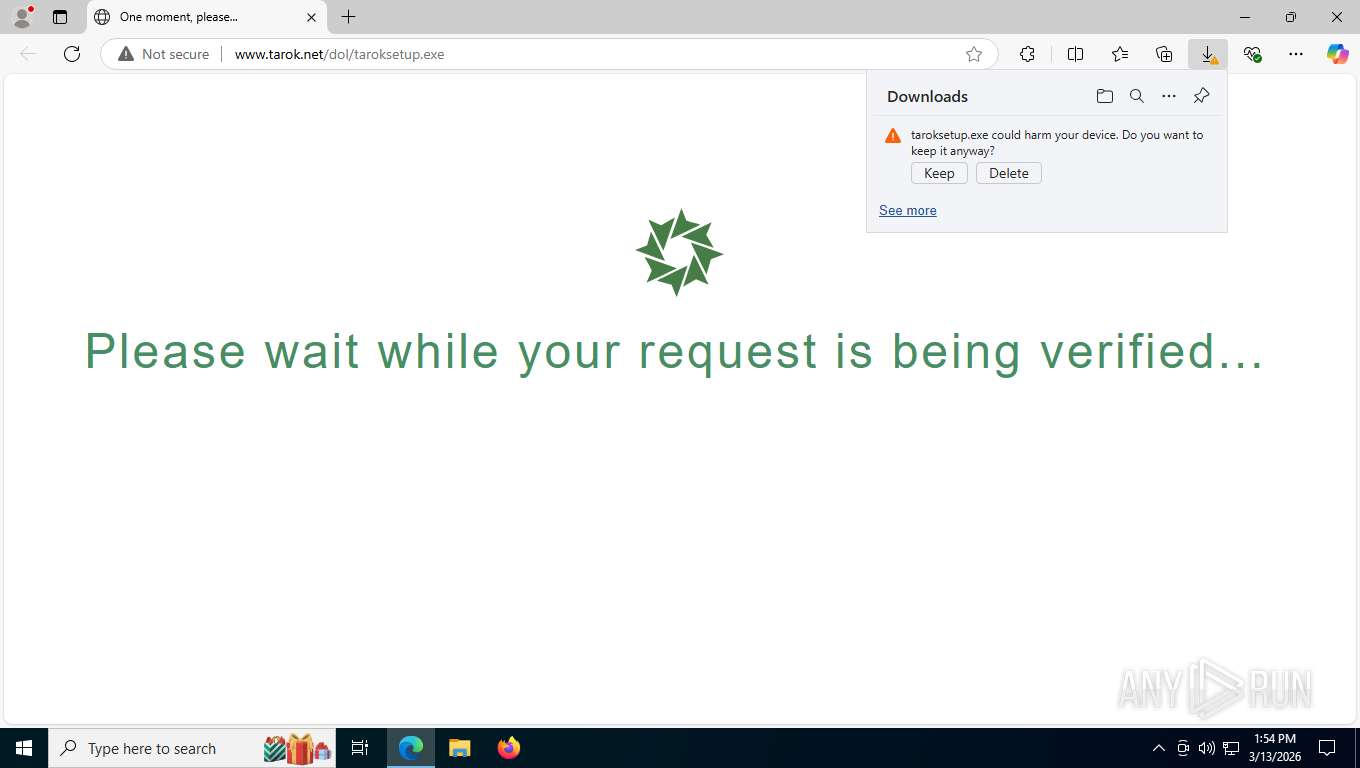
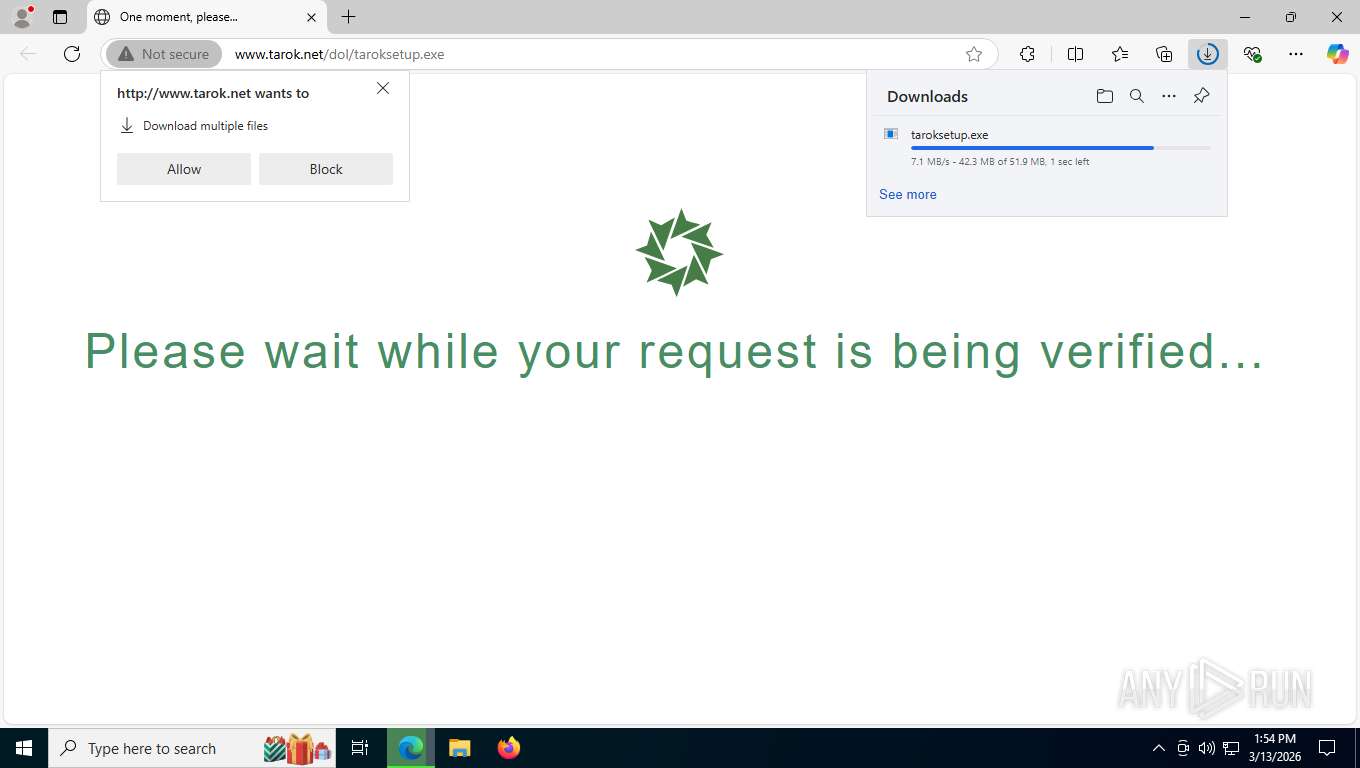
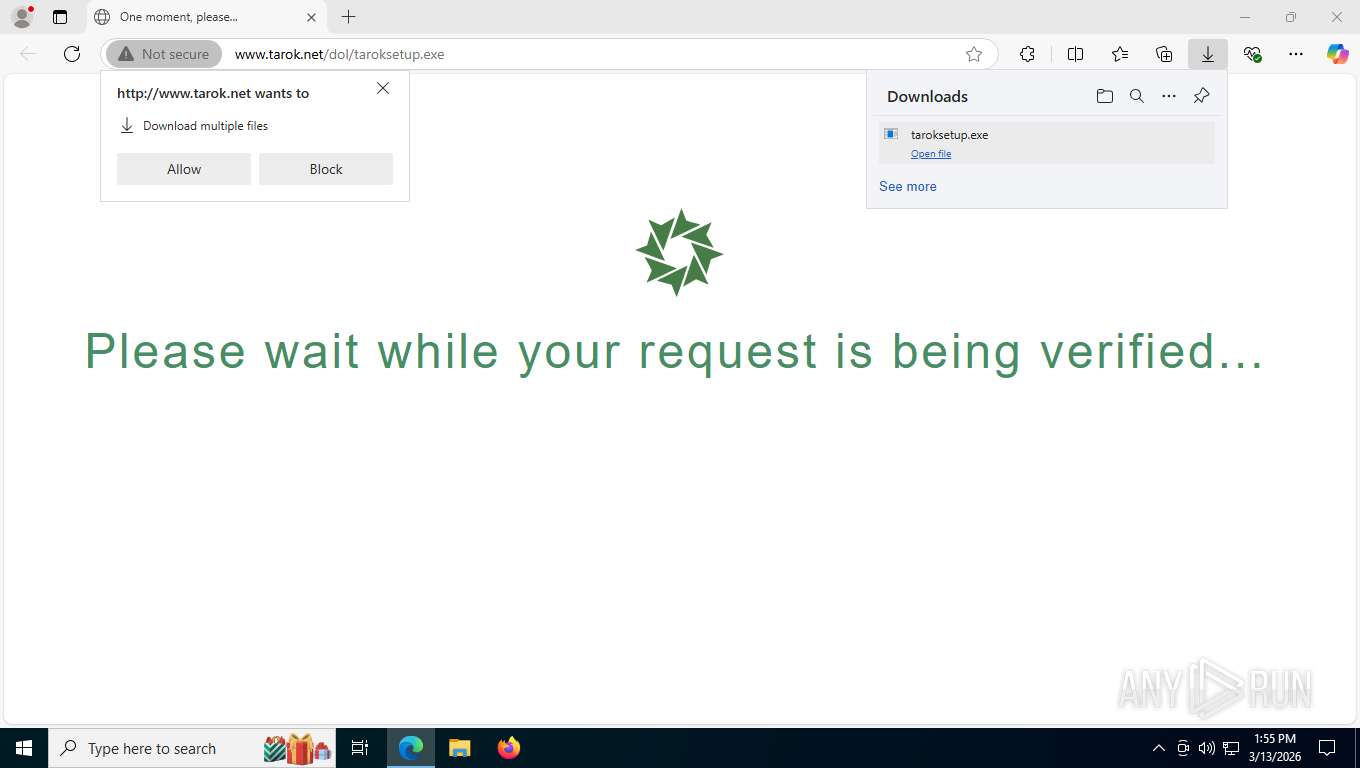
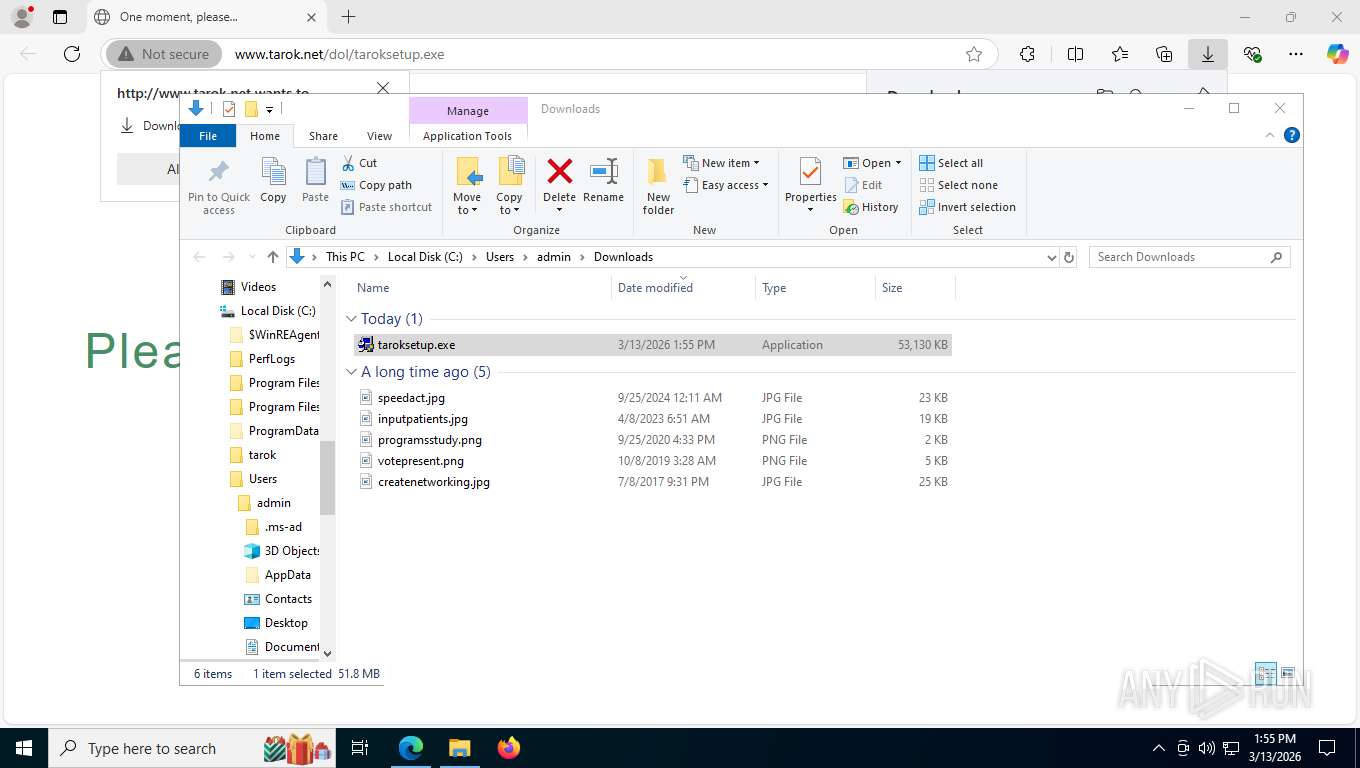
| URL: | http://www.tarok.net/dol/taroksetup.exe |
| Full analysis: | https://app.any.run/tasks/5ac8d4cb-f8b4-4271-8486-6d812f7baaf1 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2026, 17:54:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | AFD626474B0D916207637C56C5EECF14 |
| SHA1: | 1D0743A0BDFB87AB37BD3AD385EF6201DAB78142 |
| SHA256: | 65A714F7FA59F8D192EE6881FED852B5E5B2EA923DA7FC6E099056A6BBA214B6 |
| SSDEEP: | 3:N1KJS4i/0aKJXQL4A:Cc4igJXQL4A |
MALICIOUS
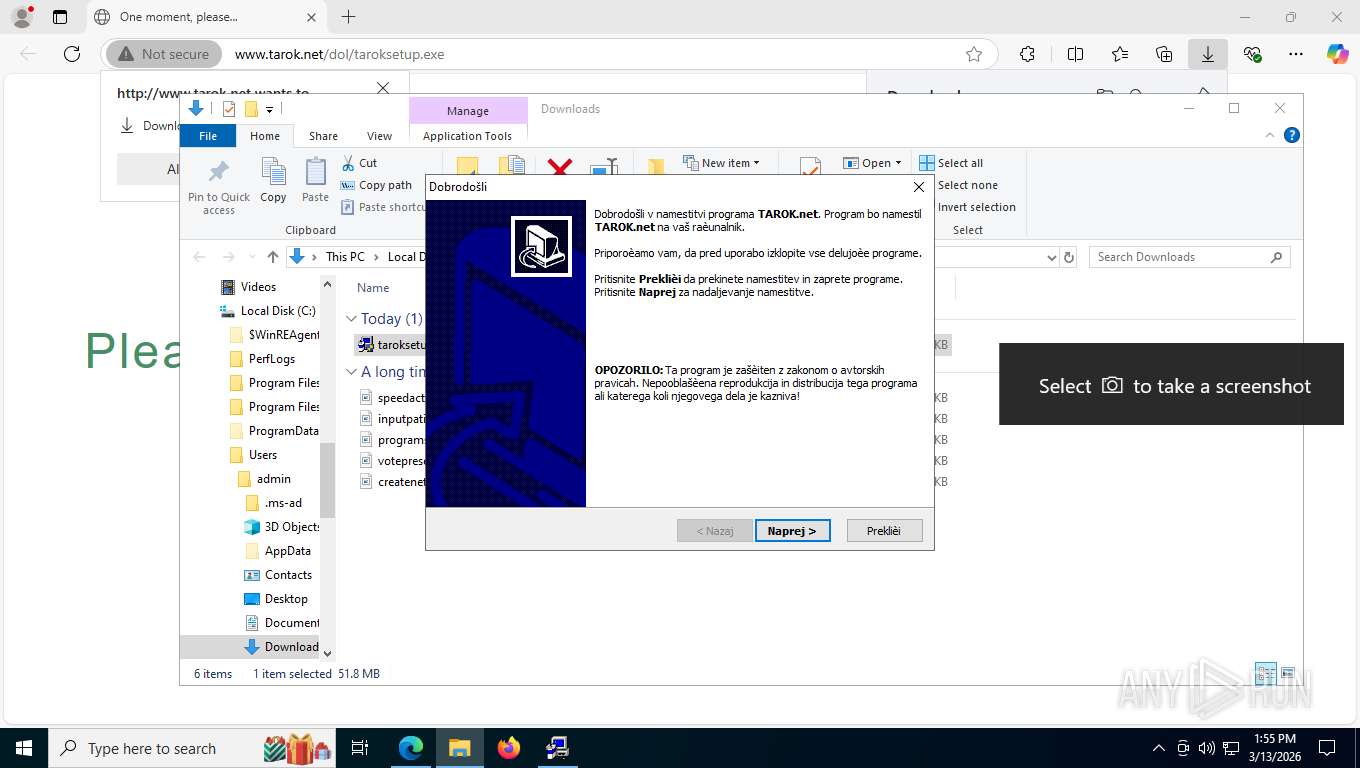
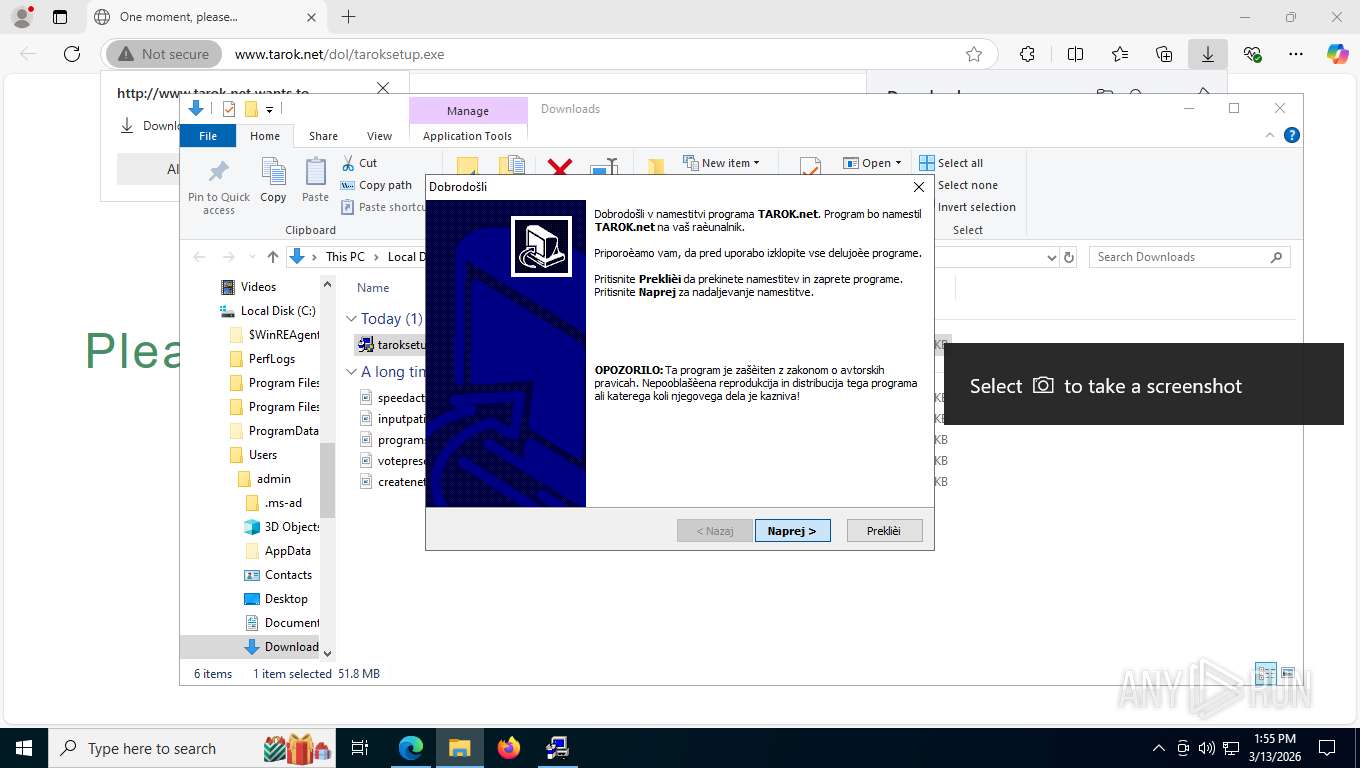
Executing a file with an untrusted certificate
- Engine.exe (PID: 8836)
SUSPICIOUS
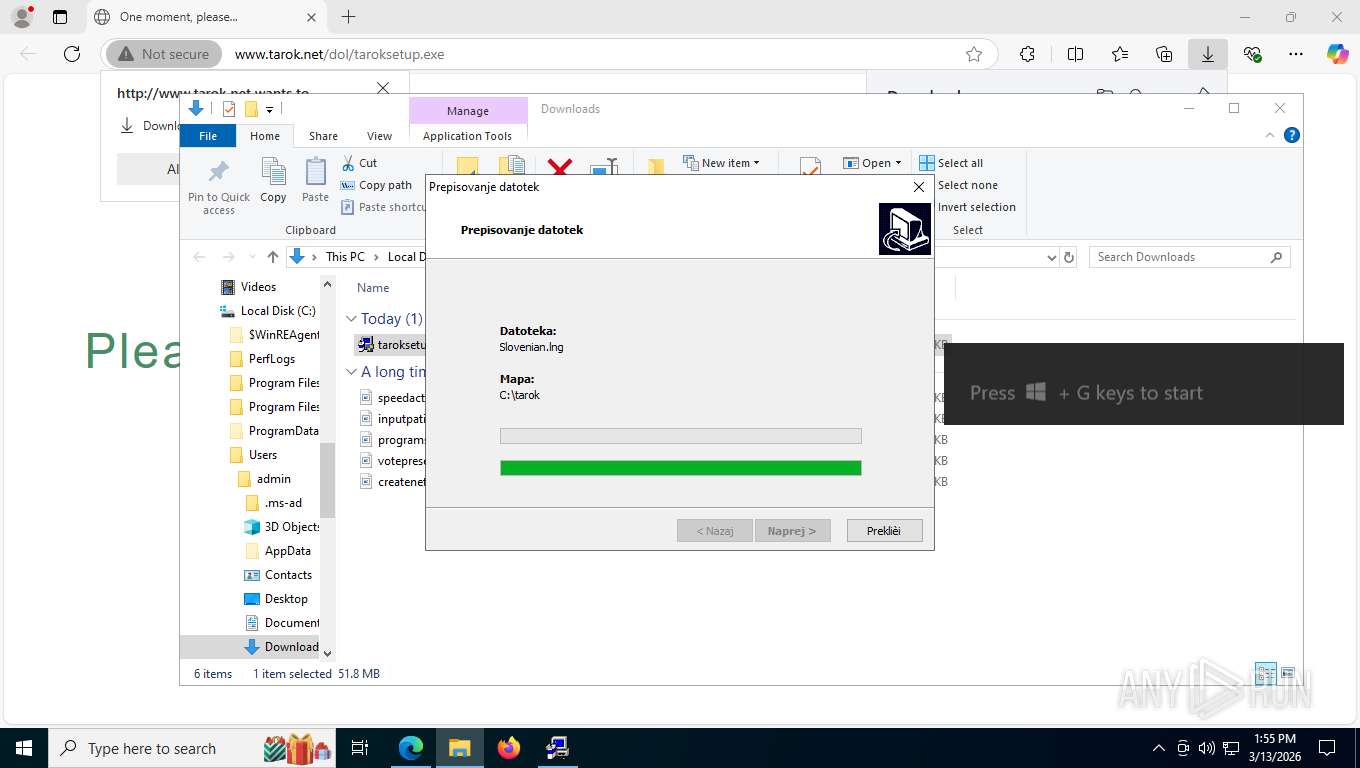
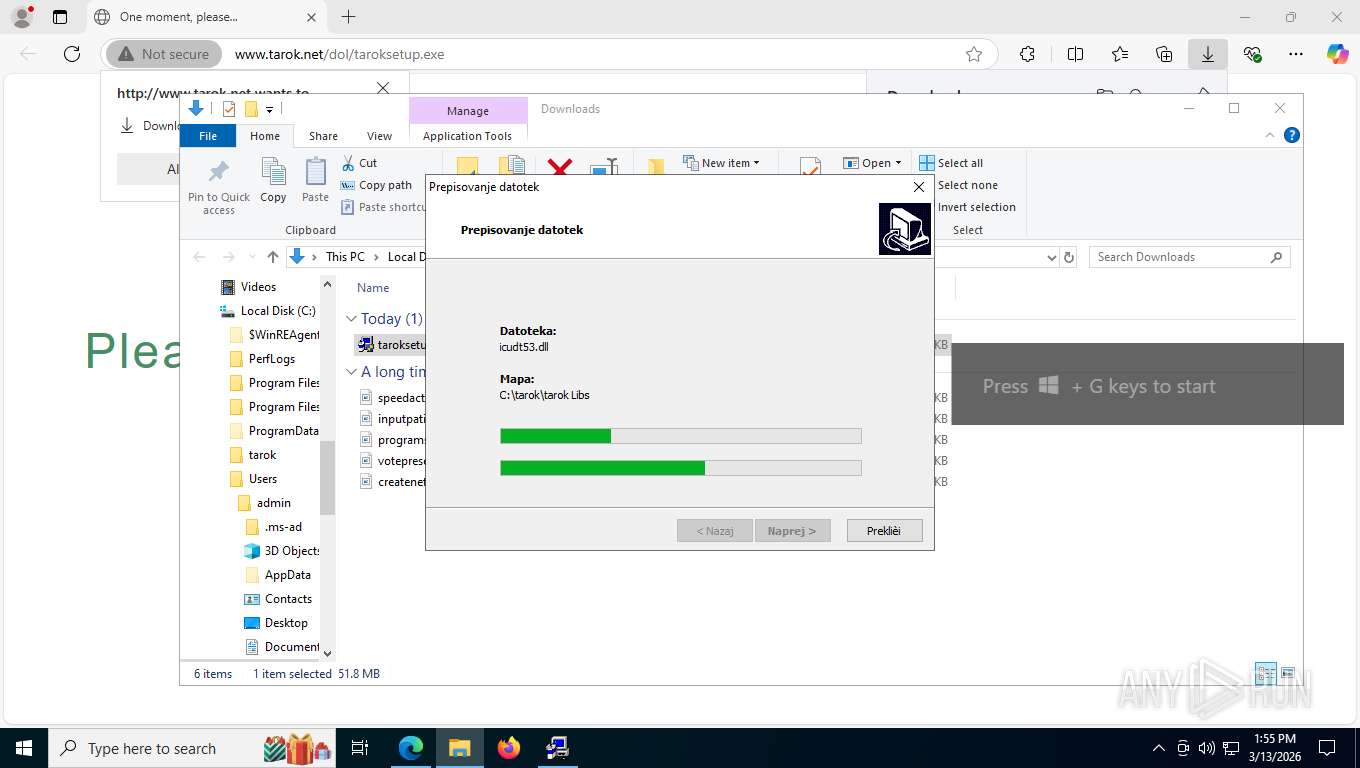
The process drops C-runtime libraries
- taroksetup.exe (PID: 4796)
- Engine.exe (PID: 8836)
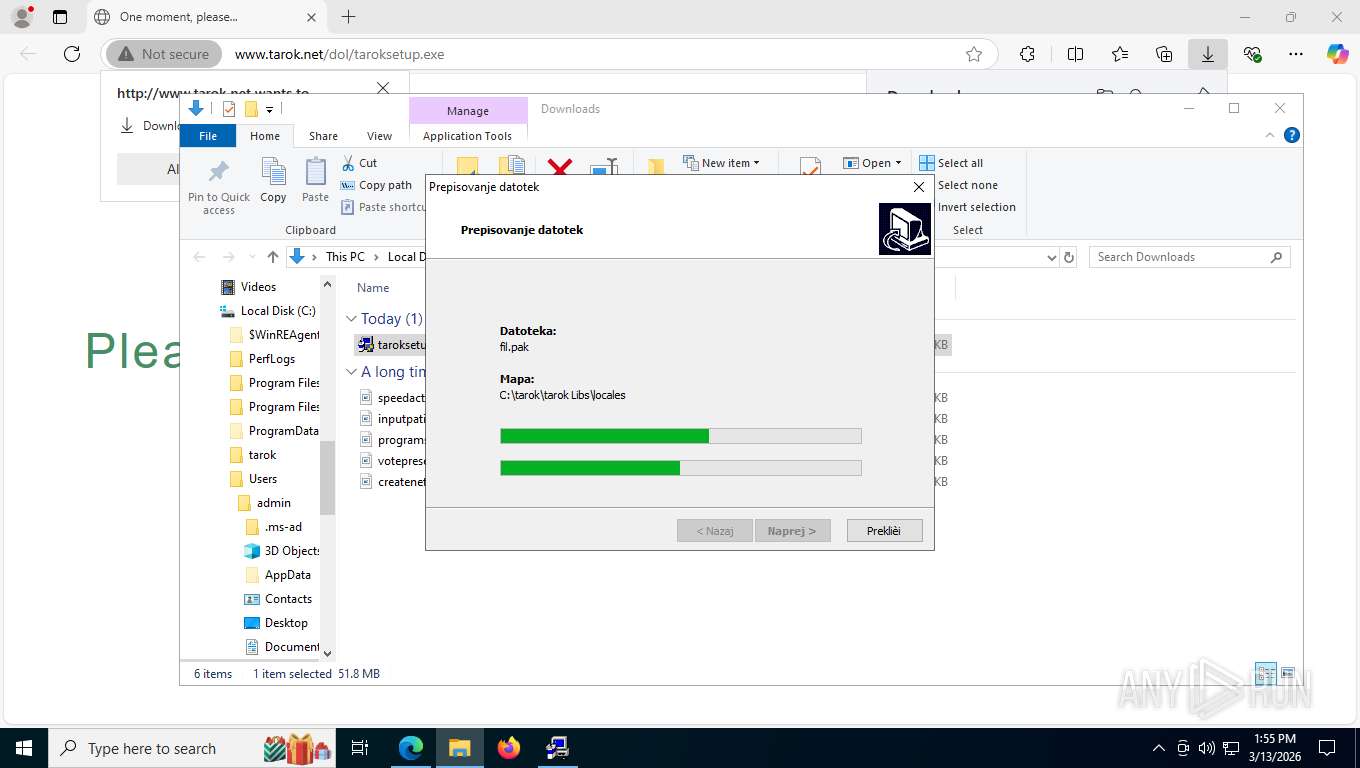
Executable content was dropped or overwritten
- taroksetup.exe (PID: 4796)
- Engine.exe (PID: 8836)
The process creates files with name similar to system file names
- taroksetup.exe (PID: 4796)
Reads the Windows owner or organization settings
- Engine.exe (PID: 8836)
Uses ICACLS.EXE to modify access control lists
- Engine.exe (PID: 8836)
INFO
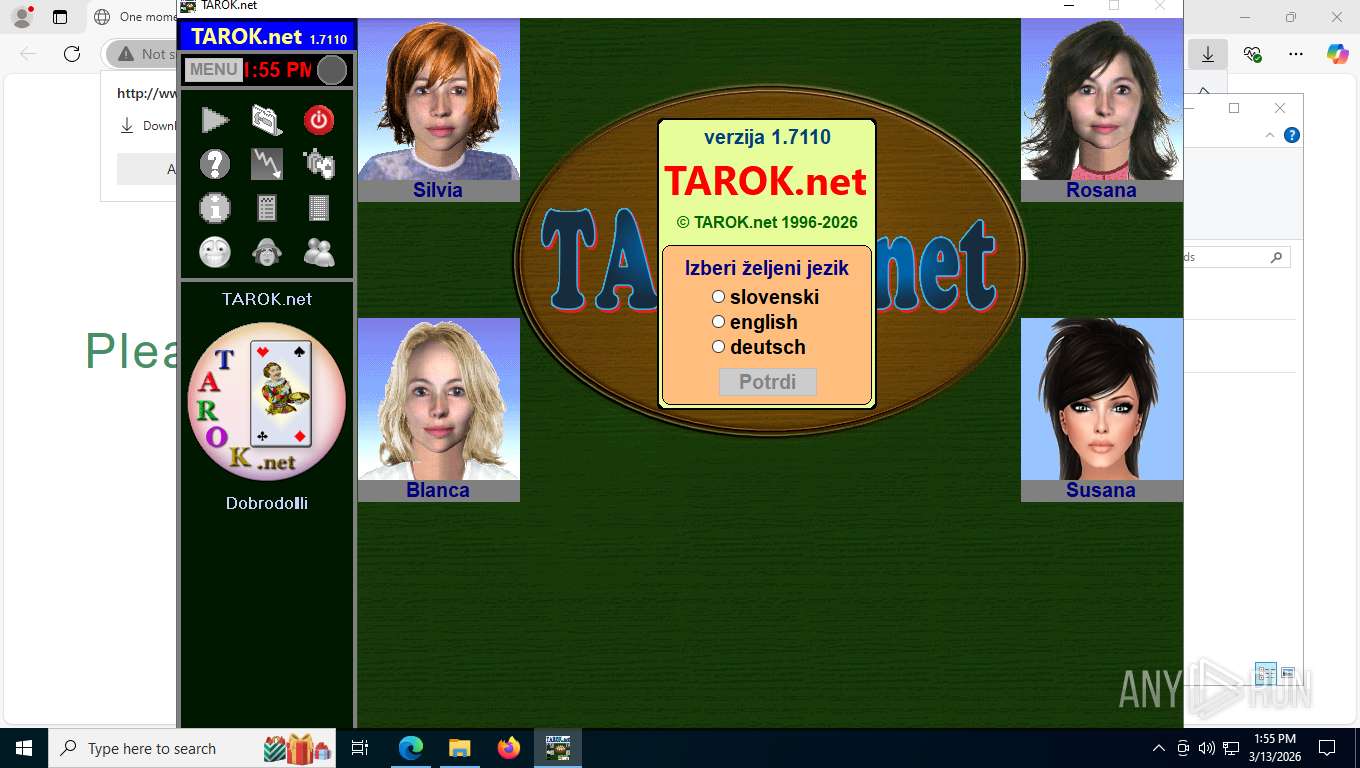
The sample compiled with english language support
- taroksetup.exe (PID: 4796)
- Engine.exe (PID: 8836)
Reads the computer name
- taroksetup.exe (PID: 4796)
- identity_helper.exe (PID: 6704)
- Engine.exe (PID: 8836)
- GameBar.exe (PID: 9032)
- tarok.exe (PID: 7672)
Checks supported languages
- identity_helper.exe (PID: 6704)
- taroksetup.exe (PID: 4796)
- Engine.exe (PID: 8836)
- tarok.exe (PID: 7672)
- GameBar.exe (PID: 9032)
Reads Environment values
- identity_helper.exe (PID: 6704)
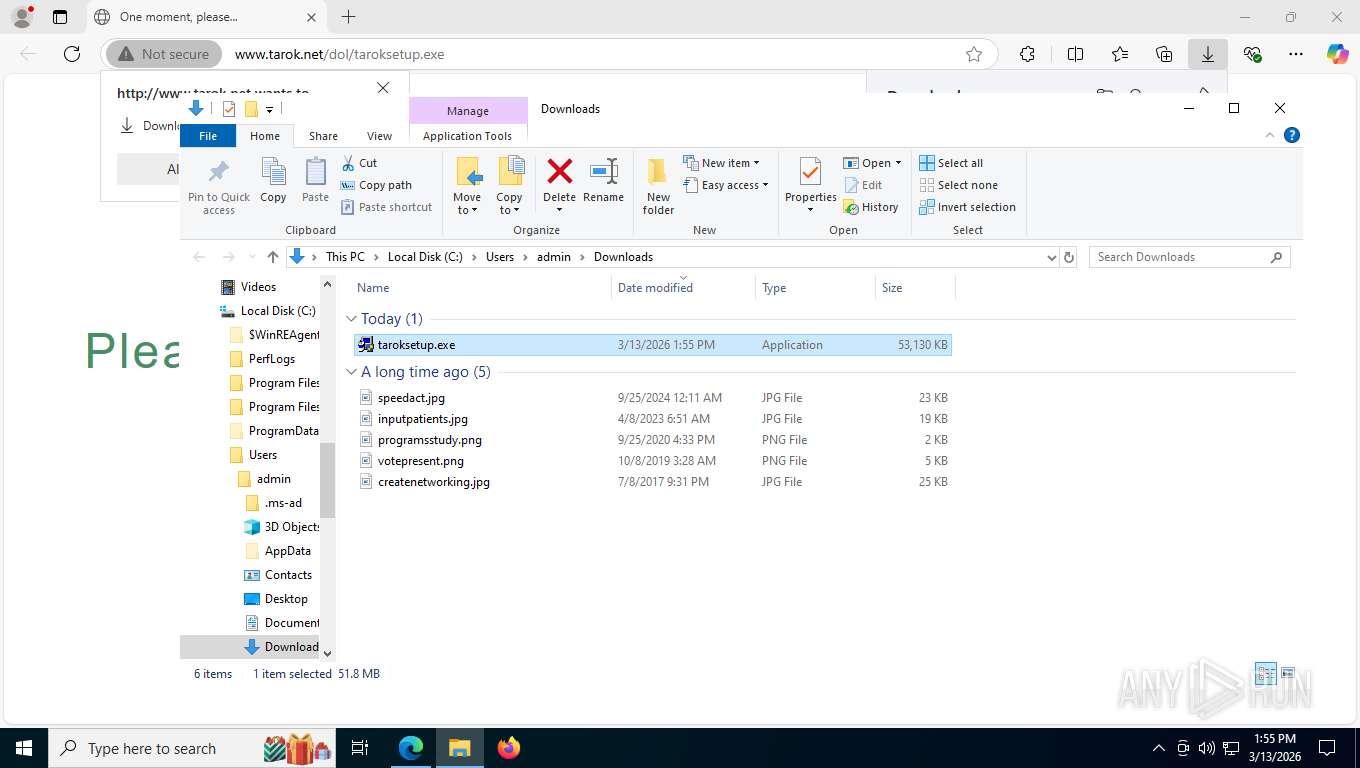
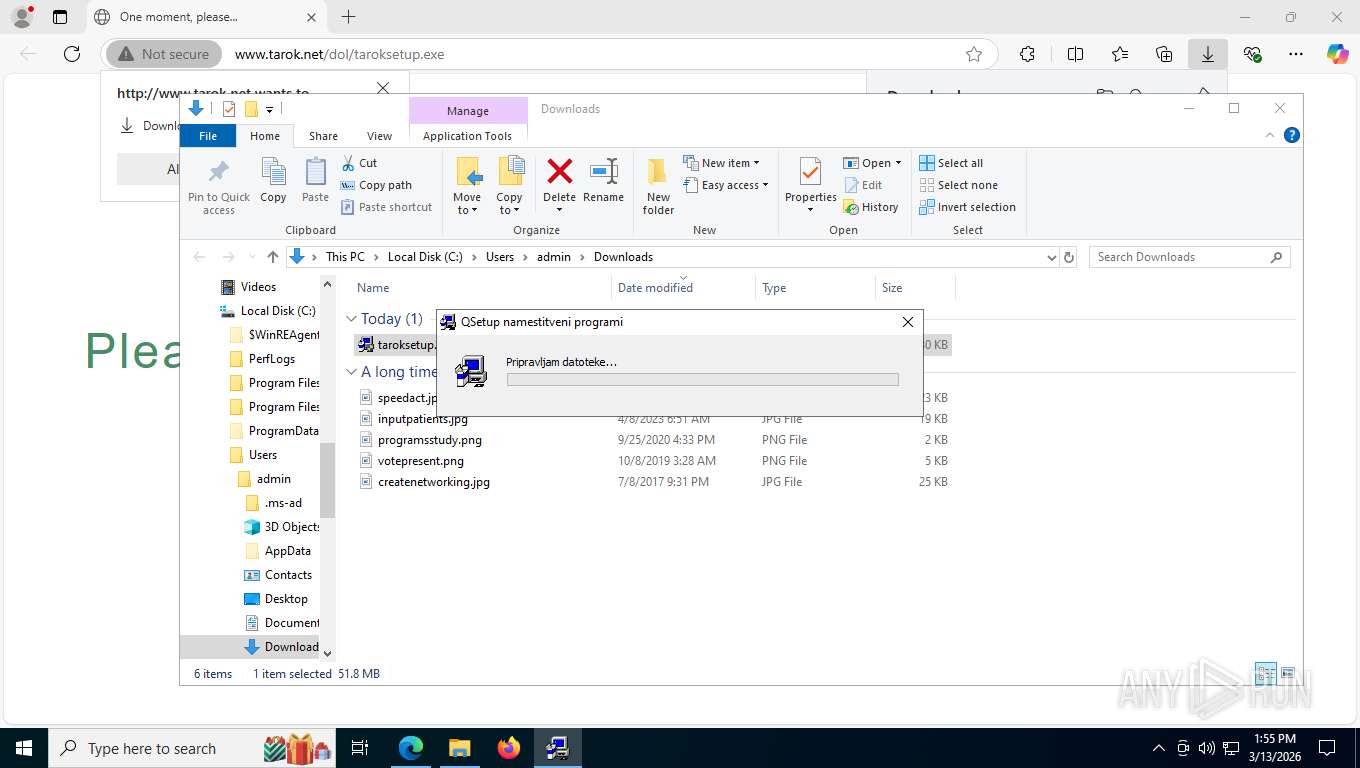
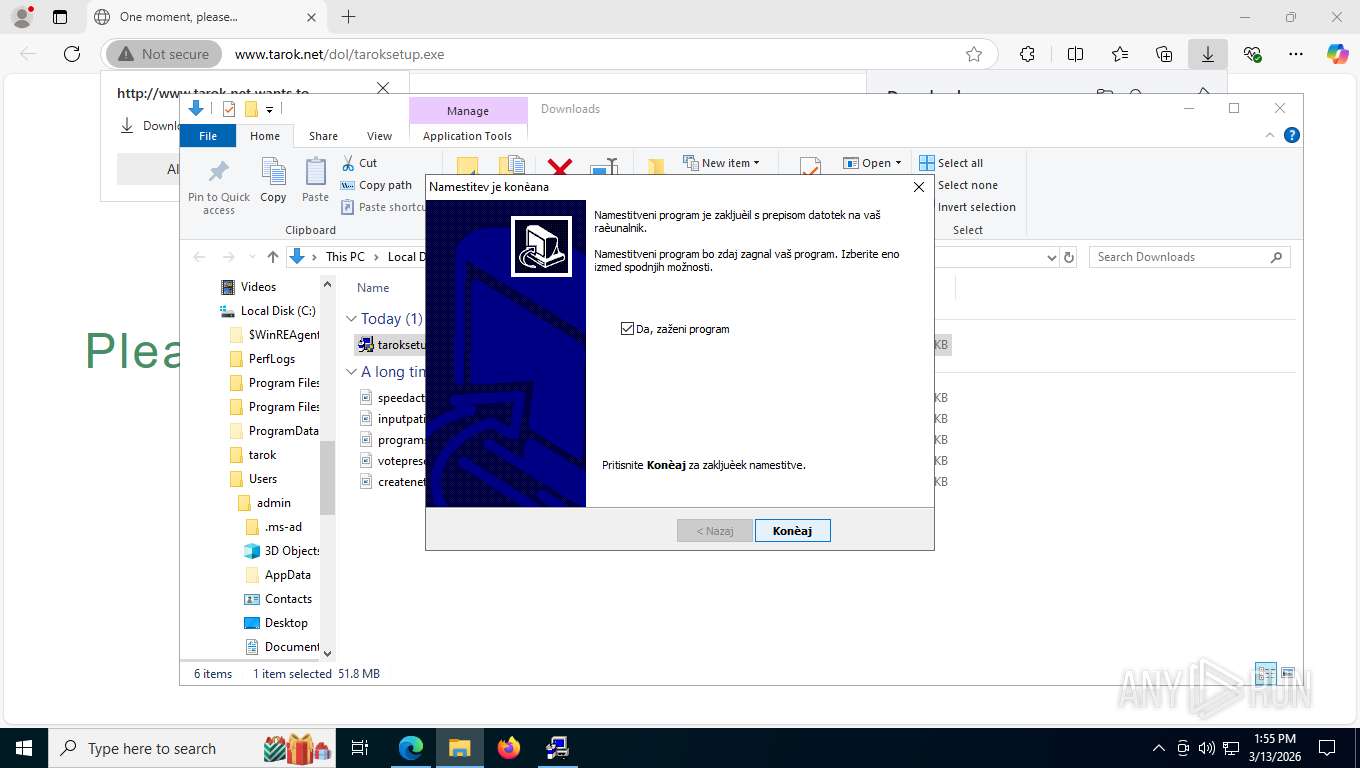
Manual execution by a user
- taroksetup.exe (PID: 4796)
- taroksetup.exe (PID: 7104)
Create files in a temporary directory
- taroksetup.exe (PID: 4796)
Executable content was dropped or overwritten
- msedge.exe (PID: 5752)
Application launched itself
- msedge.exe (PID: 5752)
Reads security settings of Internet Explorer
- GameBar.exe (PID: 9032)
- Engine.exe (PID: 8836)
- tarok.exe (PID: 7672)
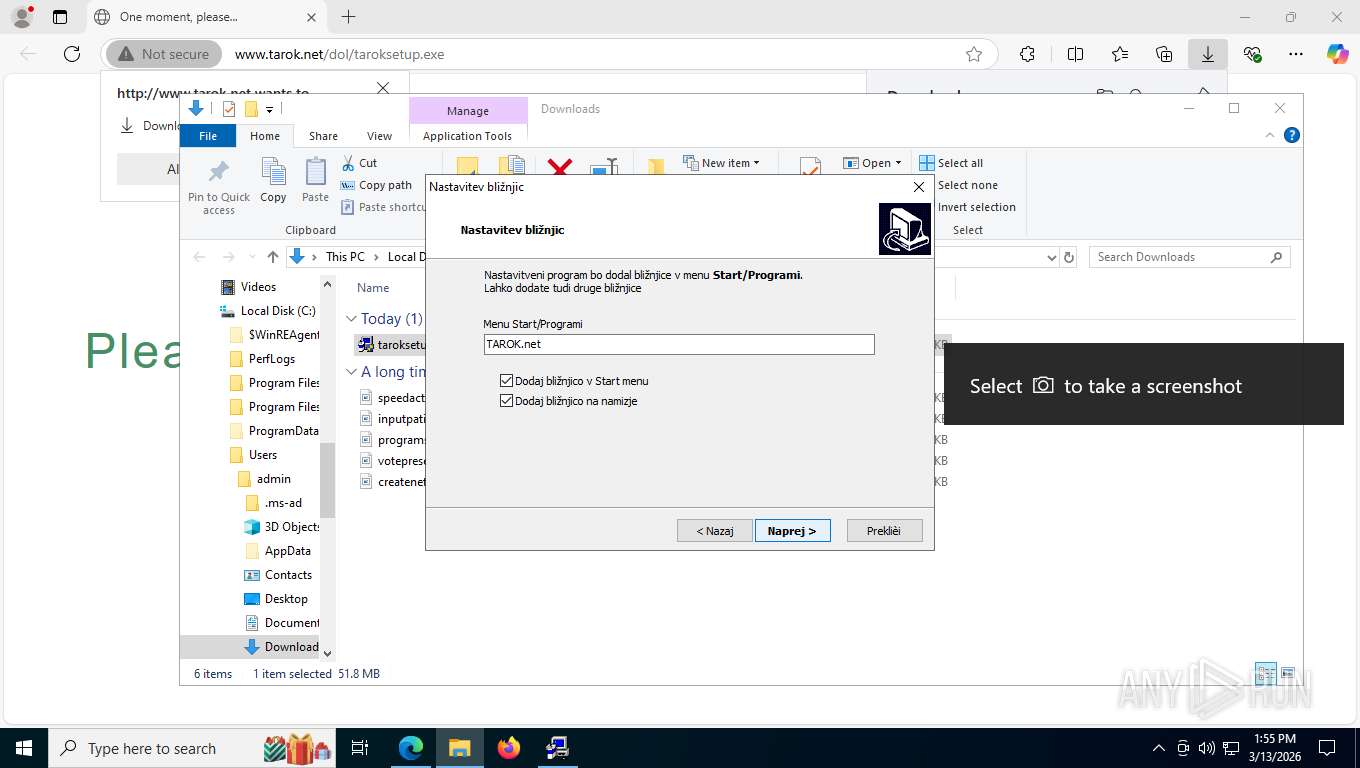
Creates files in the program directory
- Engine.exe (PID: 8836)
Creates a software uninstall entry
- Engine.exe (PID: 8836)
Process checks computer location settings
- Engine.exe (PID: 8836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
181
Monitored processes
32
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5448,i,9298247283906319395,10399926909942730831,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5472 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7776,i,9298247283906319395,10399926909942730831,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7688 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2944 | C:\WINDOWS\system32\cacls.exe "C:\tarok\Slovenian.lng" /E /C /G Everyone:F | C:\Windows\SysWOW64\cacls.exe | — | Engine.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6180,i,9298247283906319395,10399926909942730831,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6236 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4312,i,9298247283906319395,10399926909942730831,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4328 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7784,i,9298247283906319395,10399926909942730831,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7320 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4608 | C:\WINDOWS\system32\cacls.exe "C:\tarok" /T /E /C /G Everyone:F | C:\Windows\SysWOW64\cacls.exe | — | Engine.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4796 | "C:\Users\admin\Downloads\taroksetup.exe" | C:\Users\admin\Downloads\taroksetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.245 Modules
| |||||||||||||||
| 5472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6200,i,9298247283906319395,10399926909942730831,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6620 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 100
Read events
3 074
Write events
26
Delete events
0
Modification events
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | CurrentDisplayMonitor |
Value: 670061006D006500000076CB288A12B3DC01 | |||
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | StartupTipIndex |
Value: 0100000000000000032D2B8A12B3DC01 | |||
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | InstalledVersionMajor |
Value: 02008906248A12B3DC01 | |||
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | InstalledVersionMinor |
Value: 22000169268A12B3DC01 | |||
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | InstalledVersionBuild |
Value: 616D0169268A12B3DC01 | |||
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | InstalledVersionRevision |
Value: 00000169268A12B3DC01 | |||
| (PID) Process: | (9032) GameBar.exe | Key: | \REGISTRY\A\{2aa8bde4-17d8-3036-8d4f-3b1dee186d34}\LocalState |
| Operation: | write | Name: | PreviousAppTerminationFromSuspended |
Value: 000169268A12B3DC01 | |||
| (PID) Process: | (8836) Engine.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\App Management\ARPCache\TAROK.net |
| Operation: | write | Name: | Changed |
Value: 0 | |||
| (PID) Process: | (8836) Engine.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\App Management\ARPCache\TAROK.net |
| Operation: | write | Name: | SlowInfoCache |
Value: 280200000100000000B4380700000000D0391B8C12B3DC010500000043003A005C007400610072006F006B005C007400610072006F006B002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8836) Engine.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\tarok\tarok_uninstall.exe |
Value: RUNASADMIN | |||
Executable files
72
Suspicious files
141
Text files
114
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5457.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5467.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e5477.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5467.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1e5486.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
57
DNS requests
42
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8892 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:krjPrSuuaCeppr13SNr54fwbYfl3pnOYhHIcmgI6K_g&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
8892 | msedge.exe | GET | 200 | 52.123.243.67:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.55 Kb | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
8892 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
— | — | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 314 b | whitelisted |
8892 | msedge.exe | GET | 200 | 152.89.234.25:80 | http://www.tarok.net/dol/taroksetup.exe | SI | html | 11.5 Kb | unknown |
8892 | msedge.exe | GET | 200 | 152.89.234.25:80 | http://www.tarok.net/dol/taroksetup.exe | SI | binary | 51.8 Mb | unknown |
8892 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
8892 | msedge.exe | GET | 302 | 152.89.234.25:80 | http://www.tarok.net/z0f76a1d14fd21a8fb5fd0d03e0fdc3d3cedae52f?wsidchk=9661295&pdata=http%253A%252F%252Fwww.tarok.net%252Fdol%252Ftaroksetup.exe&id=7fa3b767c460b54a2be4d49030b349c7&ts=1773424491 | SI | — | — | unknown |
8892 | msedge.exe | GET | 200 | 23.3.89.90:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | — | 665 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8400 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7208 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.222:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.3.89.90:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 23.3.89.90:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.tarok.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8892 | msedge.exe | Misc activity | HUNTING [ANY.RUN] Green Spinner browser checking page often used in phishing campaigns |
8892 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
8892 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
8400 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |