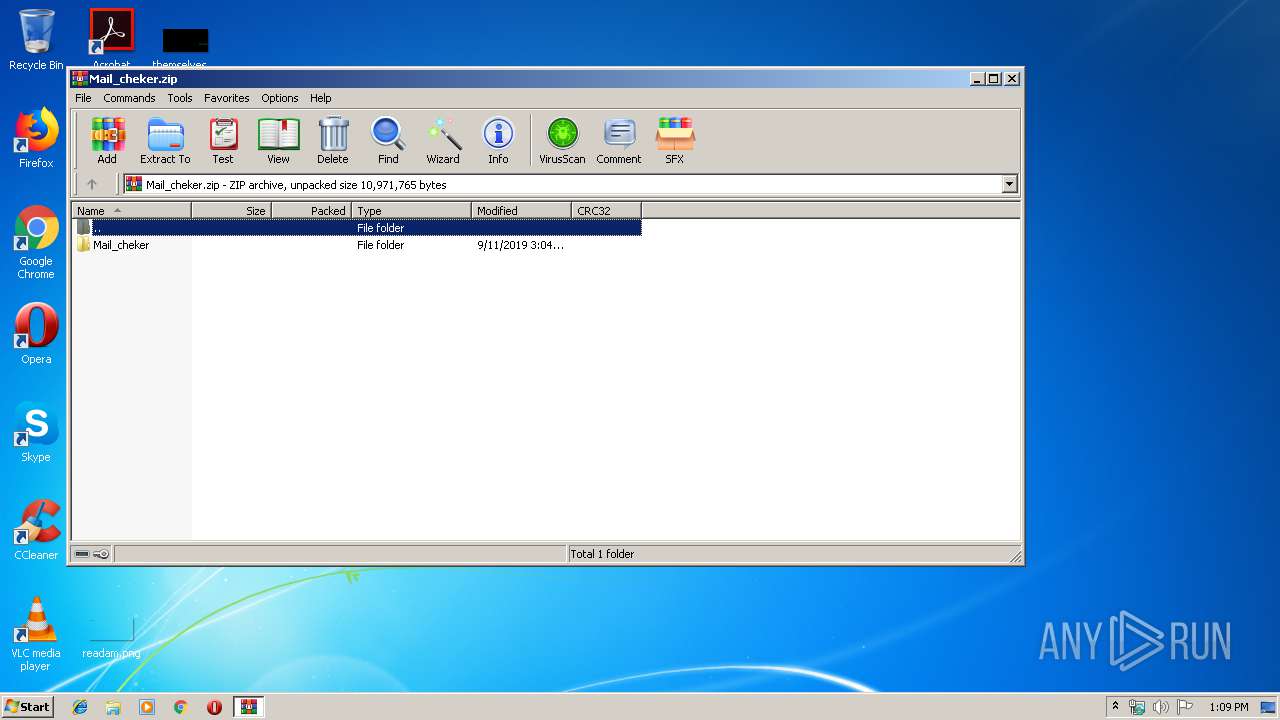
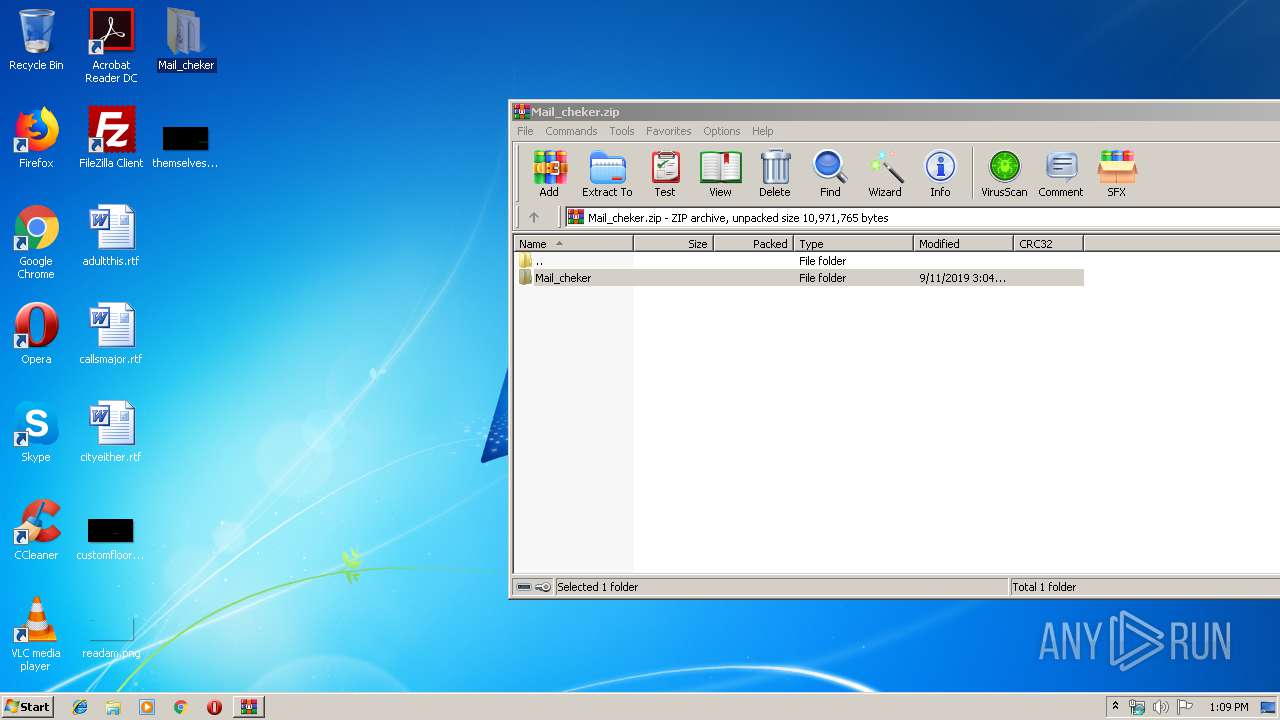
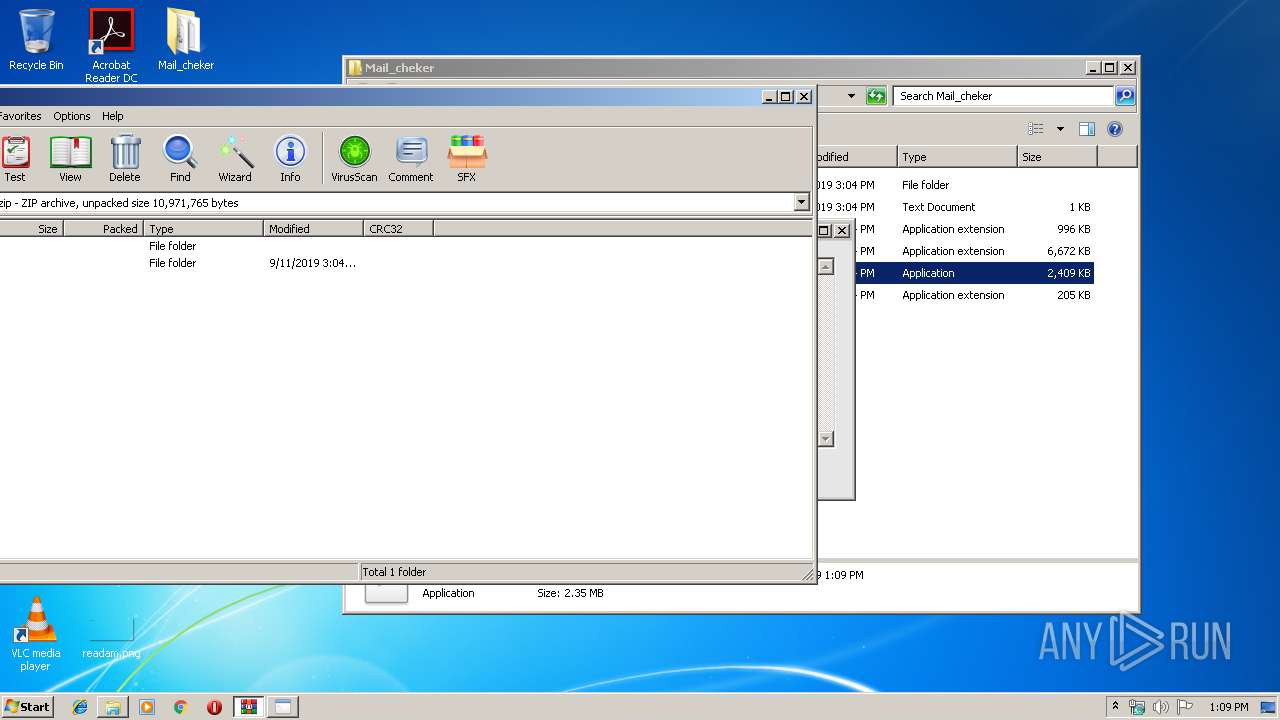
| File name: | Mail_cheker.zip |
| Full analysis: | https://app.any.run/tasks/7c9a5a02-7991-482b-b495-451b836f8fc6 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 12:09:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BE0845562A8360E5793AD3D4F0C7B2F4 |
| SHA1: | 7AE778DBCDC6FBBC750DF479B605FFDBBF8E7A4E |
| SHA256: | 658FC6D70CE0C71329589B917B4B28E3B51FB85D02B156A40546F17DE7C3CD8D |
| SSDEEP: | 98304:GDMWKVLFzW22KqJJwMyTx5VbeweiAK3mPIIxcZ5VugtM+HrnhJ:Gw52LJJwMyNe/iZmnu5ta+LhJ |
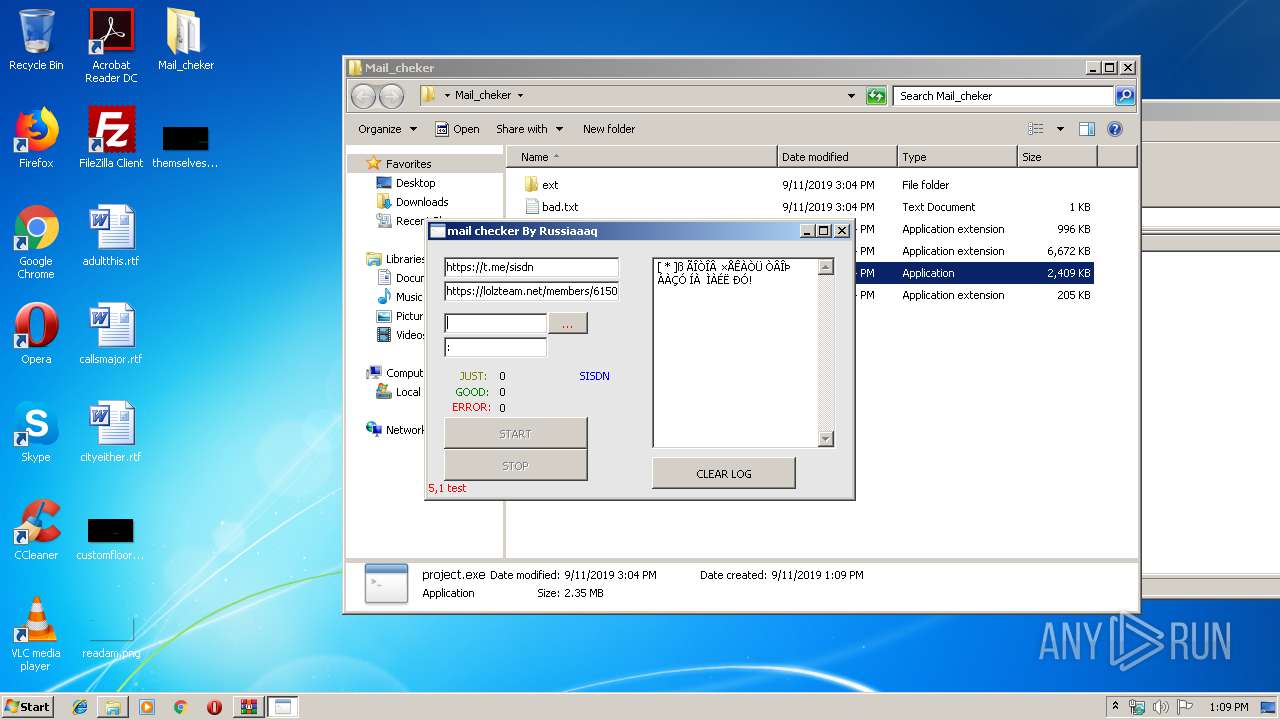
MALICIOUS
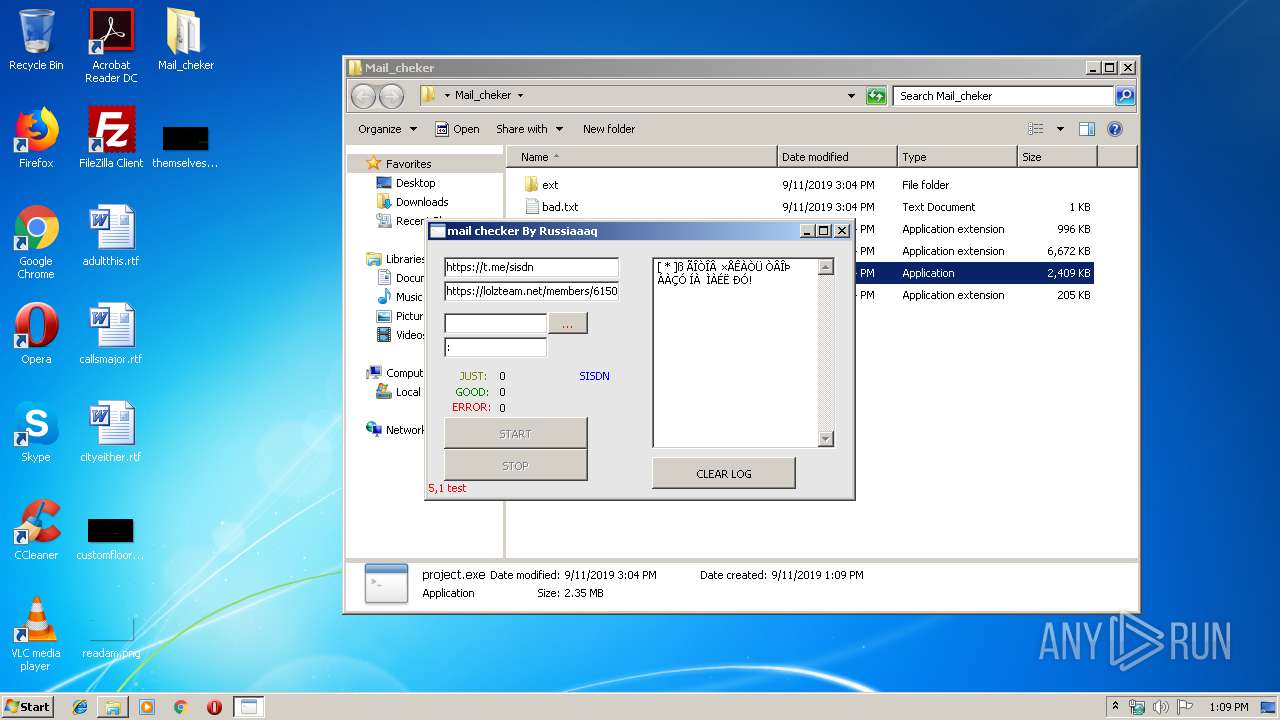
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1732)
- project.exe (PID: 3640)
SUSPICIOUS
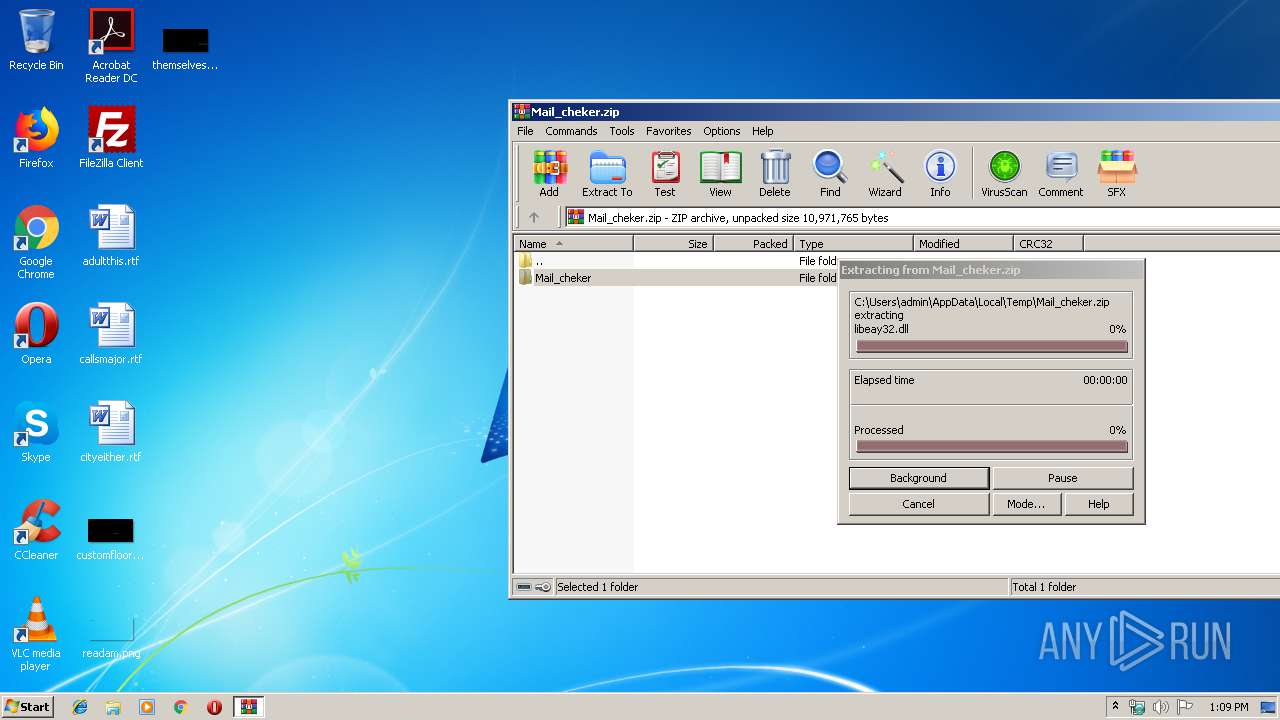
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3664)
INFO
Manual execution by user
- project.exe (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:11 15:04:28 |
| ZipCRC: | 0x09ef2e31 |
| ZipCompressedSize: | 98 |
| ZipUncompressedSize: | 130 |
| ZipFileName: | Mail_cheker/bad.txt |
Total processes
34
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1732 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\Desktop\Mail_cheker\project.exe" | C:\Users\admin\Desktop\Mail_cheker\project.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
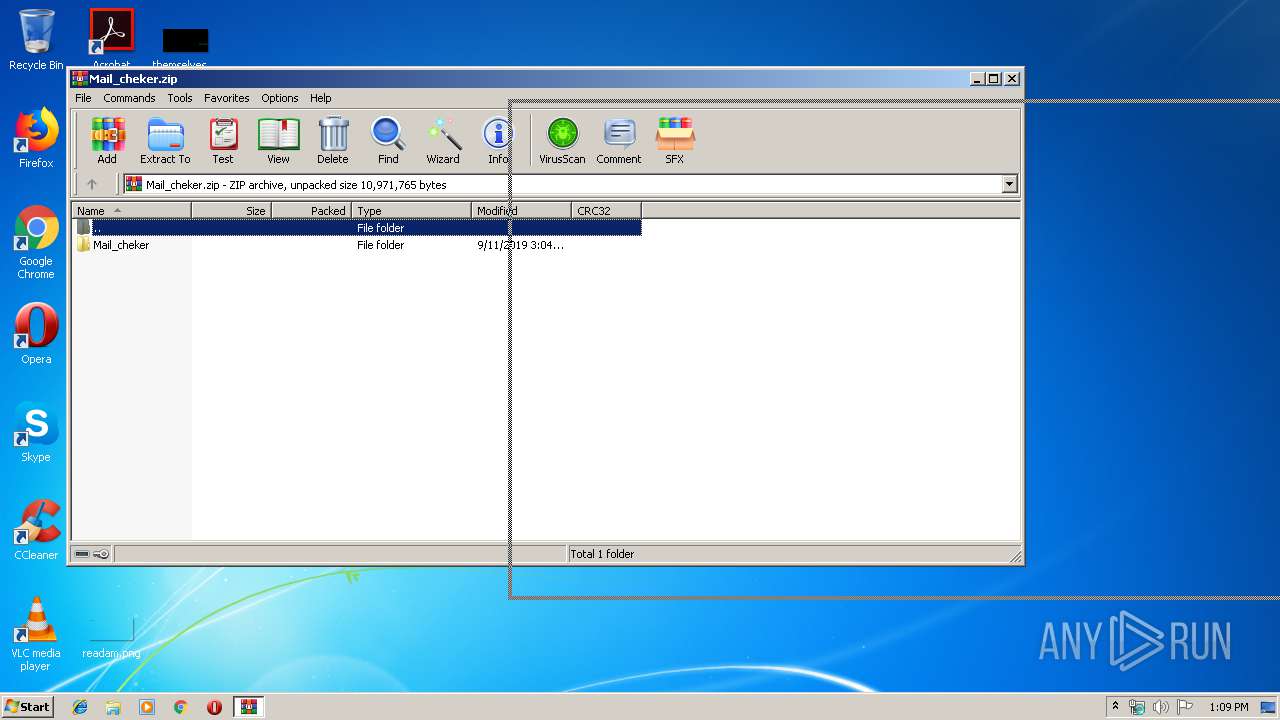
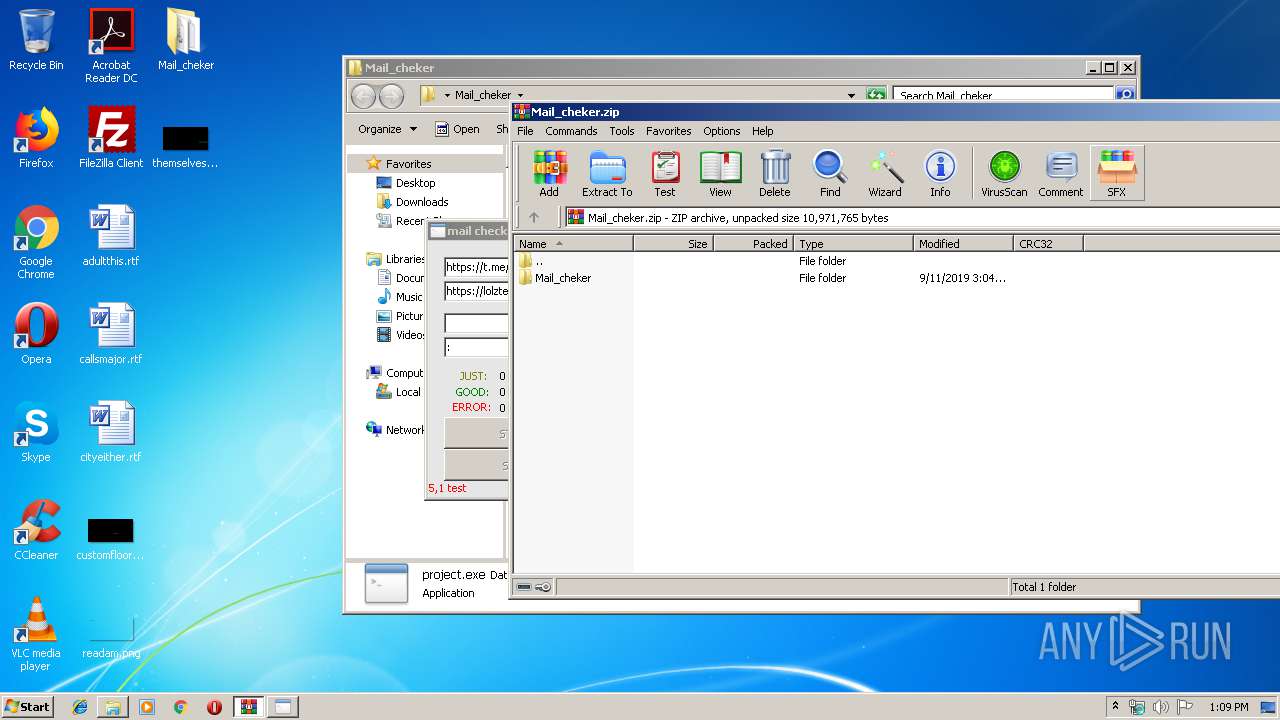
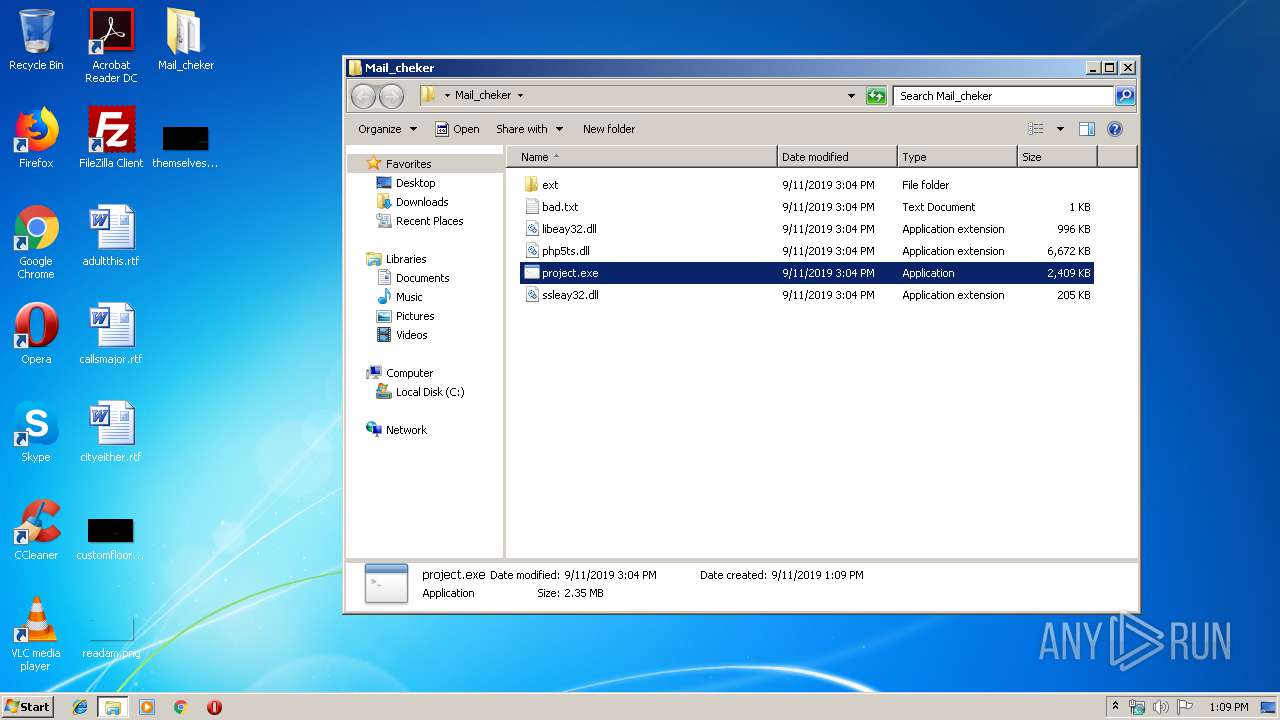
| 3664 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Mail_cheker.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
810
Read events
789
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Mail_cheker.zip | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1732) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1732) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
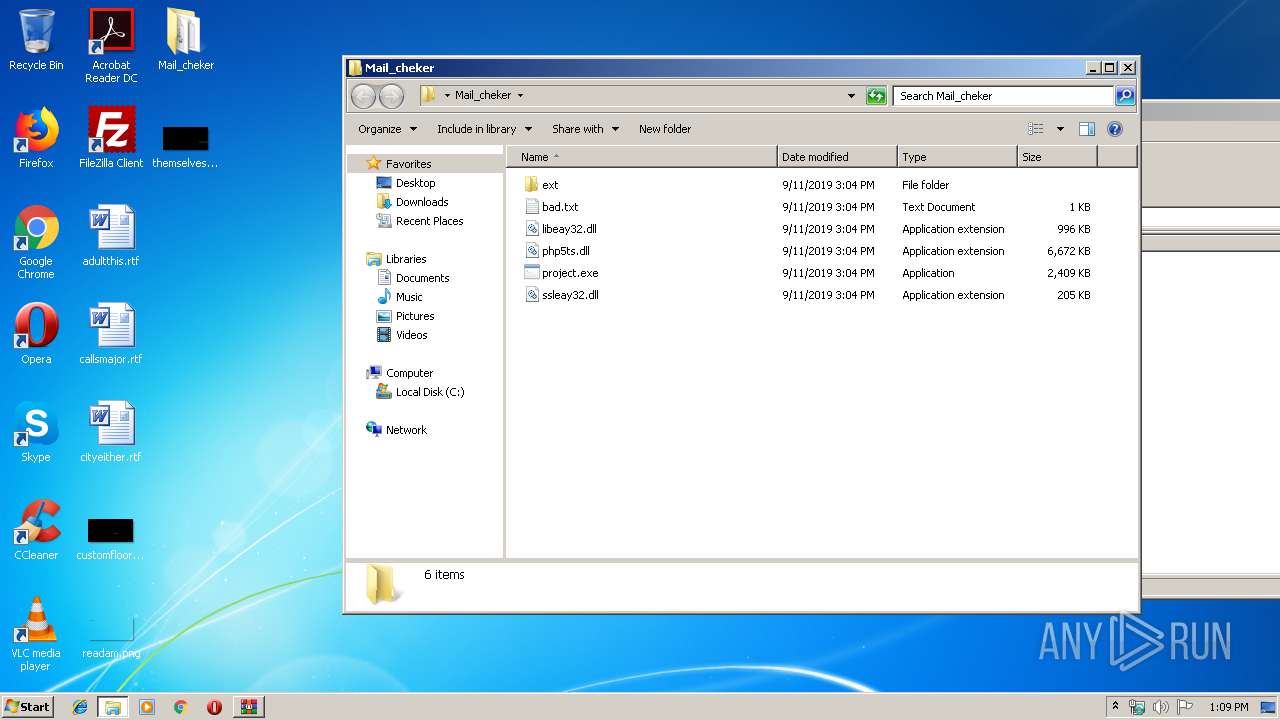
Executable files
3
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3664.26996\Mail_cheker\project.exe | — | |
MD5:— | SHA256:— | |||
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3664.26996\Mail_cheker\ssleay32.dll | — | |
MD5:— | SHA256:— | |||
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3664.26996\Mail_cheker\bad.txt | text | |
MD5:— | SHA256:— | |||
| 3640 | project.exe | C:\Users\admin\AppData\Local\Temp\PSE20\dfb43eeded00bf4989f4c306b92d82fc\php.ini | text | |
MD5:— | SHA256:— | |||
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3664.26996\Mail_cheker\ext\php_curl.dll | executable | |
MD5:— | SHA256:— | |||
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3664.26996\Mail_cheker\php5ts.dll | executable | |
MD5:C9AFF68F6673FAE7580527E8C76805B6 | SHA256:9B2C8B8C4CEC301C4303F58CA4E8B261D516F10FEB24573B092DFCCC263BAEA4 | |||
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3664.26996\Mail_cheker\libeay32.dll | executable | |
MD5:A5B591CF17429EE27B4F2C8D19656AAA | SHA256:375B4CB49CE113498D94C78EFAC16A8A1EAFB508F559DF25F8233B7C4EA8DB2A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report