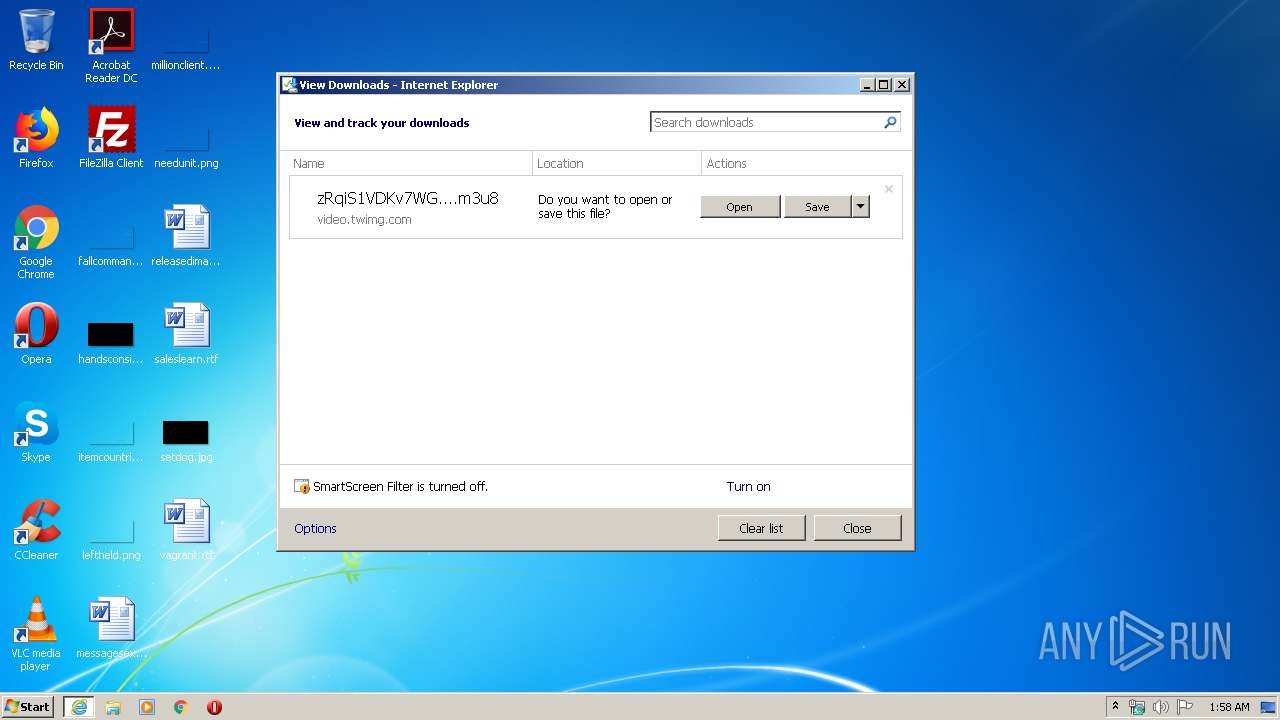
| URL: | https://video.twimg.com/ext_tw_video/884493155273461760/pu/pl/zRqiS1VDKv7WGk9E.m3u8 |
| Full analysis: | https://app.any.run/tasks/592dfeb8-c133-4937-93d8-35b73f91a523 |
| Verdict: | No threats detected |
| Analysis date: | April 28, 2020, 00:58:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 74D8411FB7D6D0F7D65871691632C993 |
| SHA1: | 35A1BCA7A8D37BEC4BAAD727380C75FE8AD1E559 |
| SHA256: | 6585A18BBA2851FBD0552B706A842605B46CD7EE4CD2D9CE84D2FDCE7E5F9B5B |
| SSDEEP: | 3:N8OAQ0KKKAT54fdd3cWUFCULTVKhVQVWBizgHI:24Ubm1d3eCAZCVQGuN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 2228)
INFO
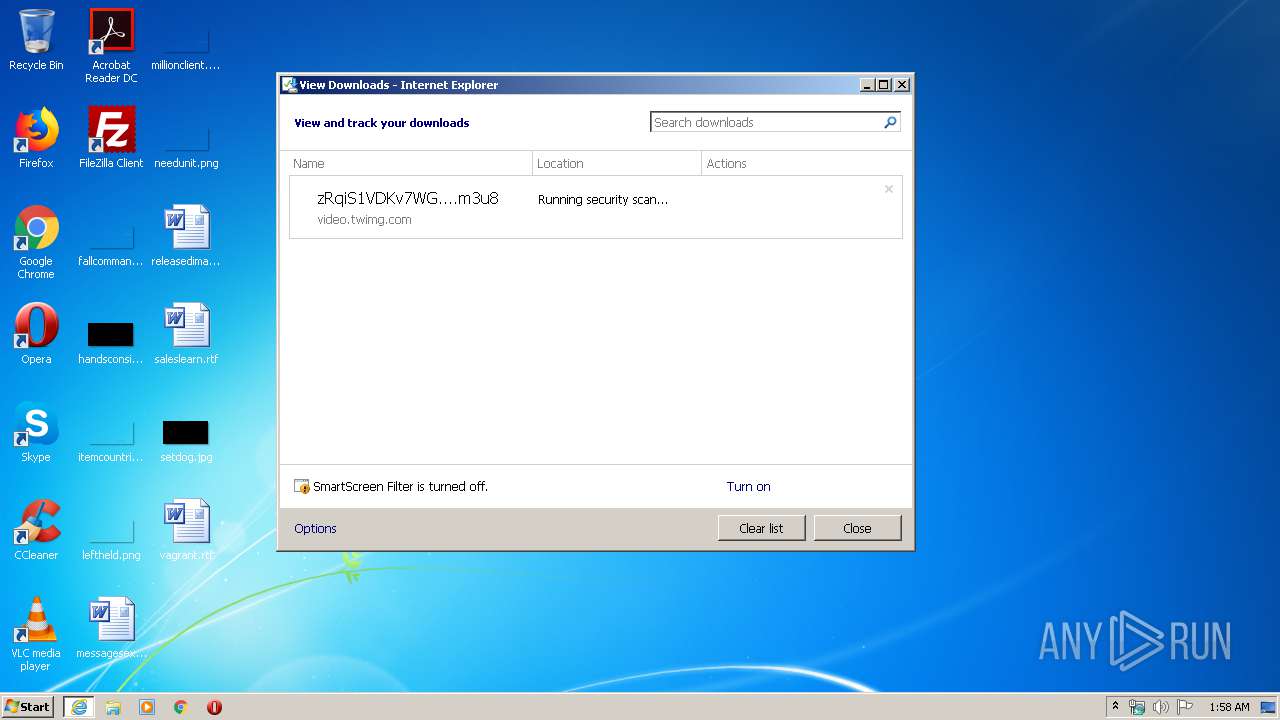
Reads Internet Cache Settings
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 2740)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3896)
Changes internet zones settings
- iexplore.exe (PID: 3896)
Reads settings of System Certificates
- iexplore.exe (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
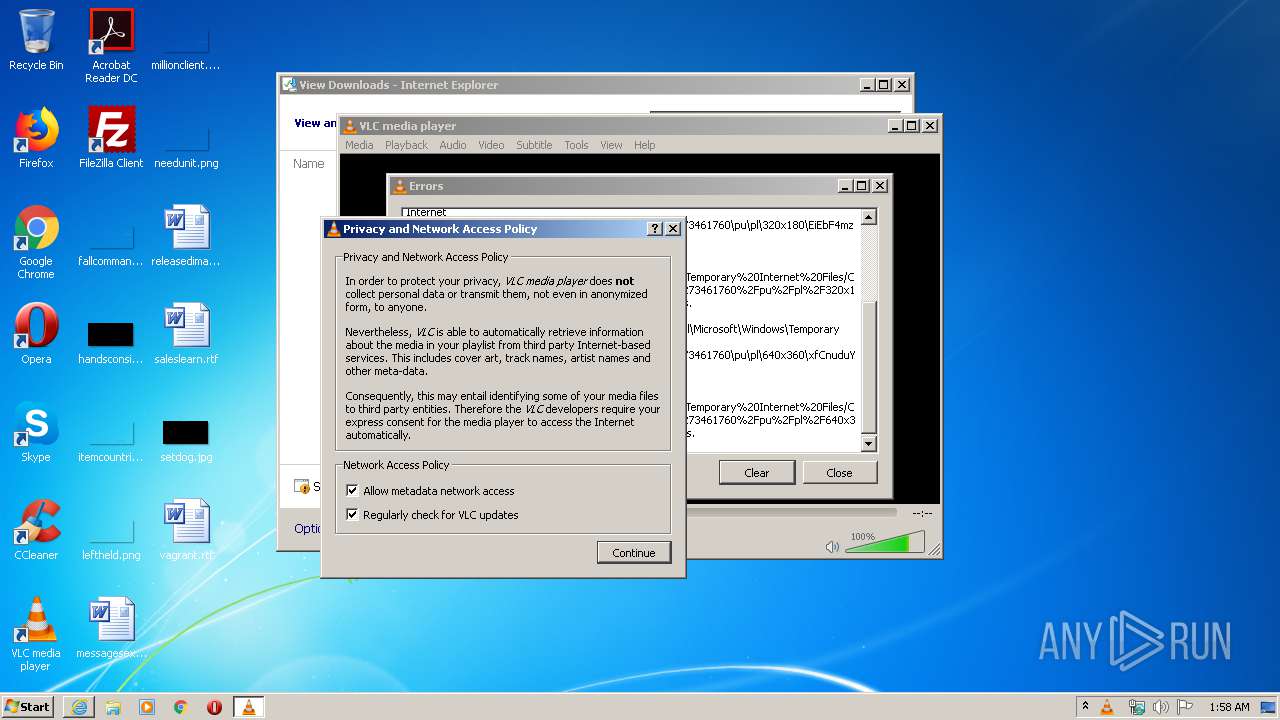
| 2228 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\zRqiS1VDKv7WGk9E.m3u8" | C:\Program Files\VideoLAN\VLC\vlc.exe | iexplore.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3896 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Internet Explorer\iexplore.exe" https://video.twimg.com/ext_tw_video/884493155273461760/pu/pl/zRqiS1VDKv7WGk9E.m3u8 | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 203
Read events
1 159
Write events
44
Delete events
0
Modification events
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 801122044 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30809336 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
5
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD5D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2740 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD5D7.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6DBD38470D2D9857.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\zRqiS1VDKv7WGk9E.m3u8.gb9ay00.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2228 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC200E.tmp | — | |
MD5:— | SHA256:— | |||
| 2228 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlcrc.2228 | — | |
MD5:— | SHA256:— | |||
| 2228 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC5875.tmp | — | |
MD5:— | SHA256:— | |||
| 2740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\zRqiS1VDKv7WGk9E.m3u8 | text | |
MD5:— | SHA256:— | |||
| 2740 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\zRqiS1VDKv7WGk9E[1].m3u8 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2740 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2740 | iexplore.exe | 68.232.34.217:443 | video.twimg.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
2740 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 68.232.34.217:443 | video.twimg.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
video.twimg.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
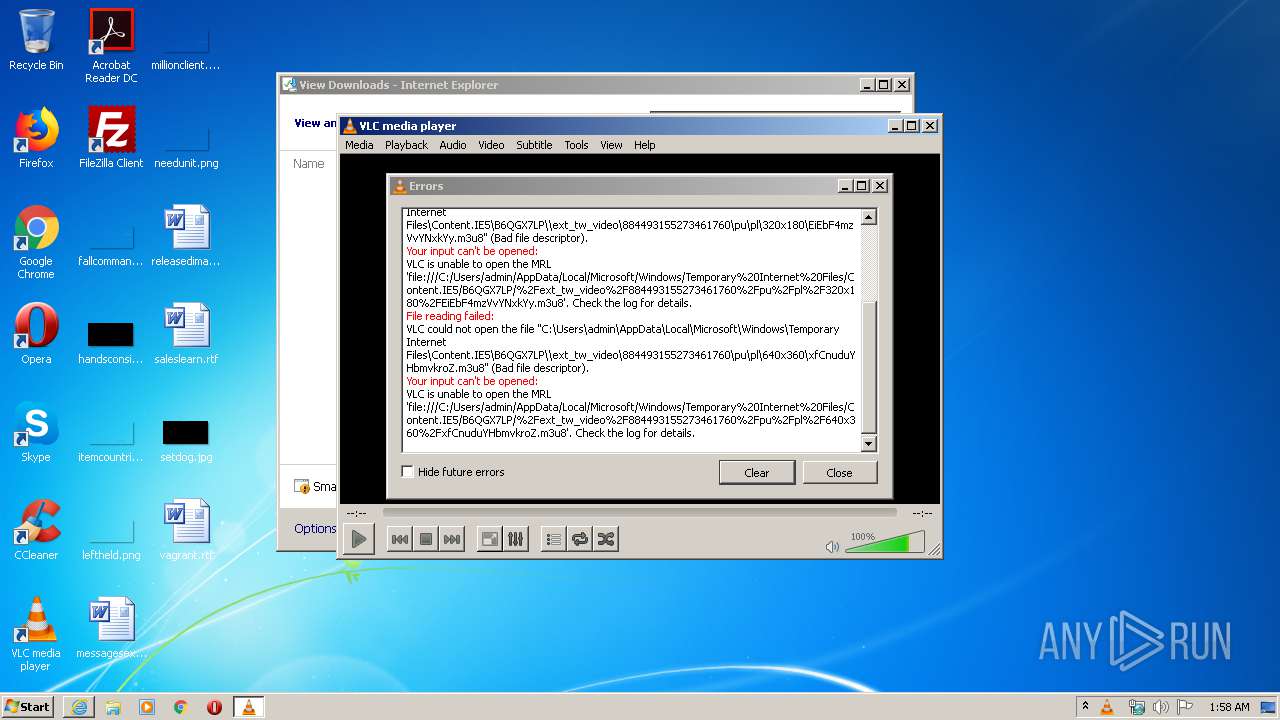
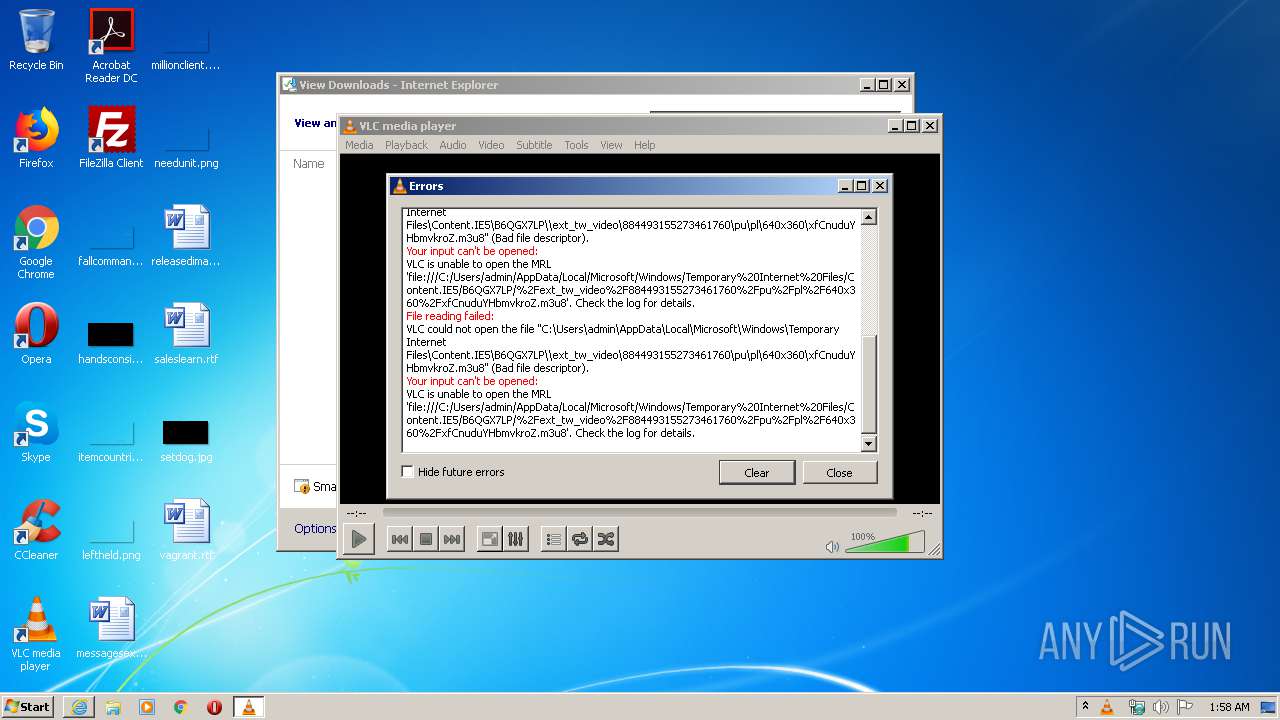
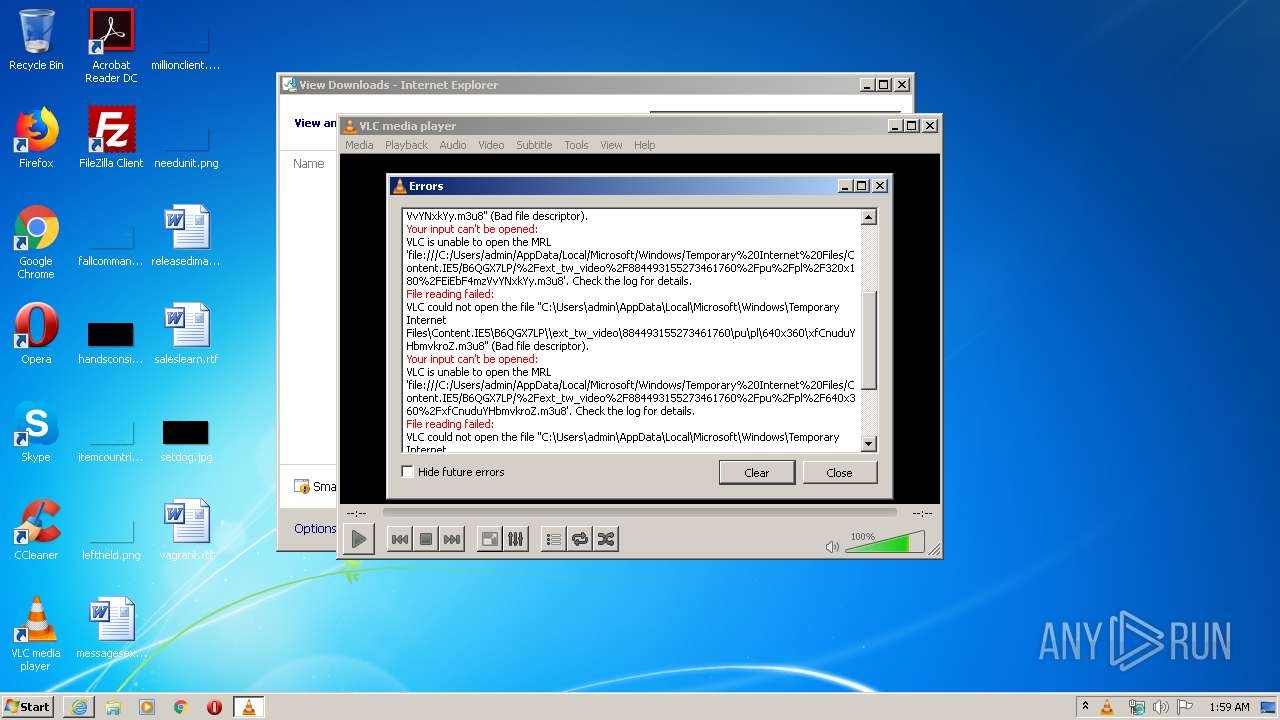
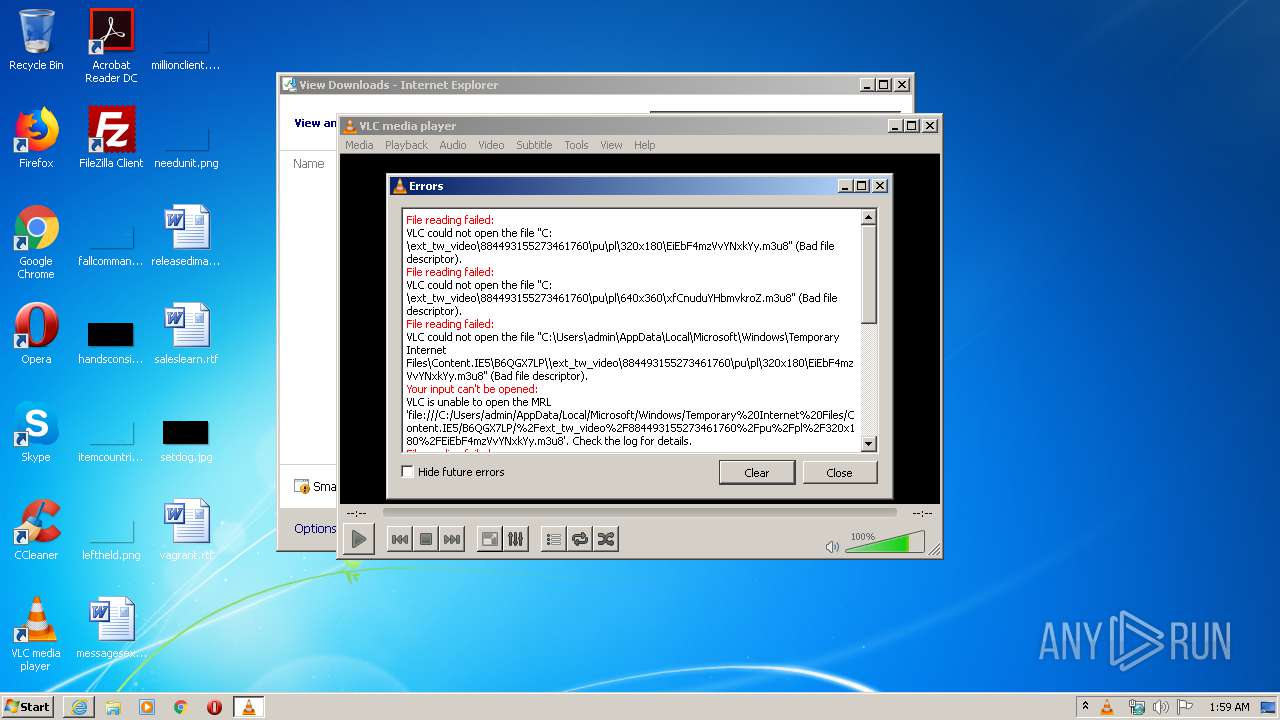
vlc.exe | core stream error: no suitable access module for `file:///C:/ext_tw_video/884493155273461760/pu/pl/320x180/EiEbF4mzVvYNxkYy.m3u8'
|
vlc.exe | filesystem access error: cannot open file C:\ext_tw_video\884493155273461760\pu\pl\640x360\xfCnuduYHbmvkroZ.m3u8 (No such file or directory)
|
vlc.exe | filesystem access error: cannot open file C:\ext_tw_video\884493155273461760\pu\pl\320x180\EiEbF4mzVvYNxkYy.m3u8 (No such file or directory)
|
vlc.exe | httplive stream error: No playable streams found in Meta playlist
|
vlc.exe | httplive stream: HTTP Live Streaming (/C:/Users/admin/AppData/Local/Microsoft/Windows/Temporary%20Internet%20Files/Content.IE5/B6QGX7LP/zRqiS1VDKv7WGk9E.m3u8)
|
vlc.exe | core stream error: no suitable access module for `file:///C:/ext_tw_video/884493155273461760/pu/pl/640x360/xfCnuduYHbmvkroZ.m3u8'
|
vlc.exe | es demux error: cannot peek
|
vlc.exe | es demux error: cannot peek
|