| File name: | nasm-2.16.03-installer-x64.exe |
| Full analysis: | https://app.any.run/tasks/0e3007ab-d402-4a38-8c5a-38c80fd039de |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 18:17:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive, 7 sections |
| MD5: | 4205B5973D293543E89C2069635117E3 |
| SHA1: | 1A67E9FE7605777A78096007600BFA1492AD0E9C |
| SHA256: | 657E1252676CFB26A008835C20A760F731C8E0414469A4ED0F83F0FB059CDD35 |
| SSDEEP: | 49152:wZWSBJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJJR:wZWNwaT7lyT6mlLgBEJZIuoO2pS4BNWv |
MALICIOUS
No malicious indicators.SUSPICIOUS
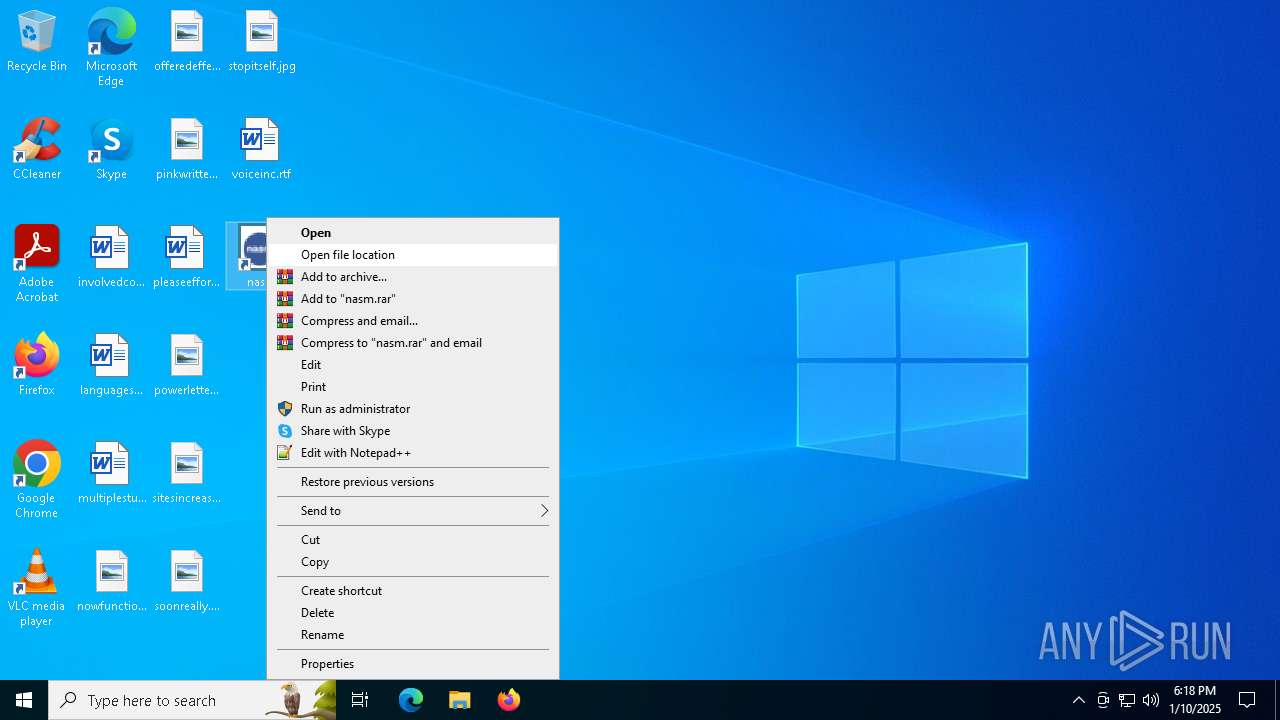
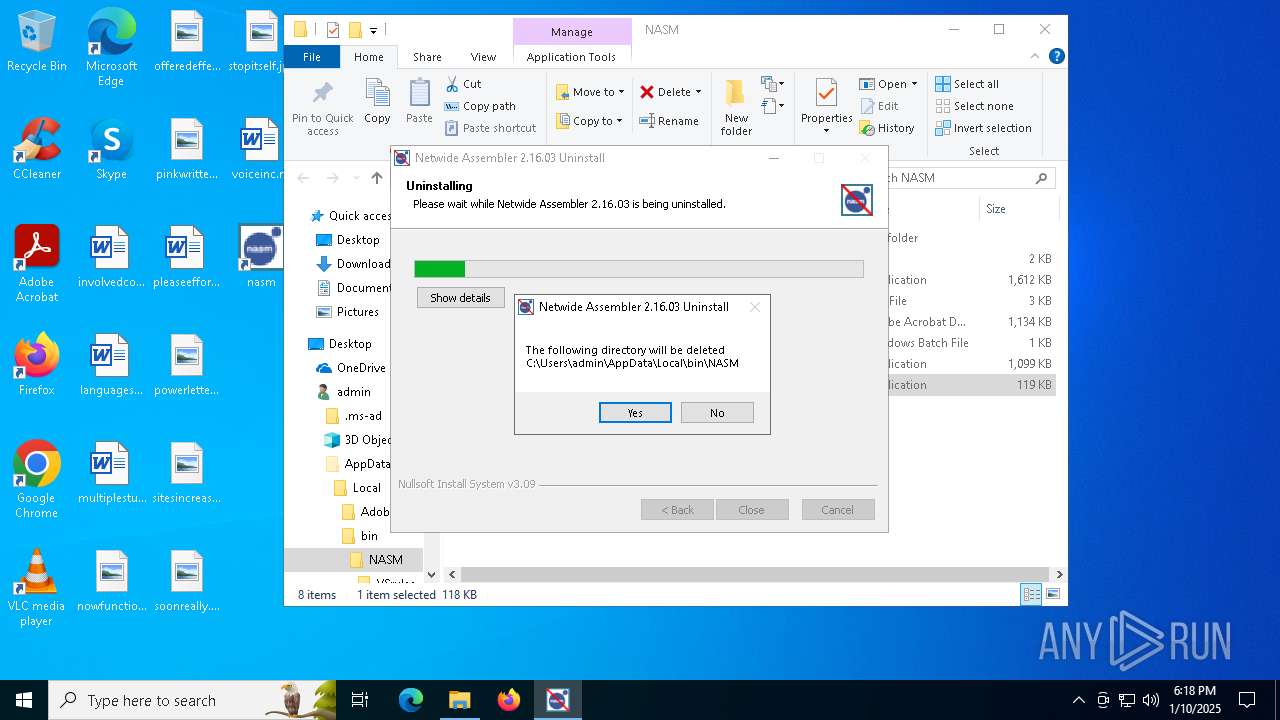
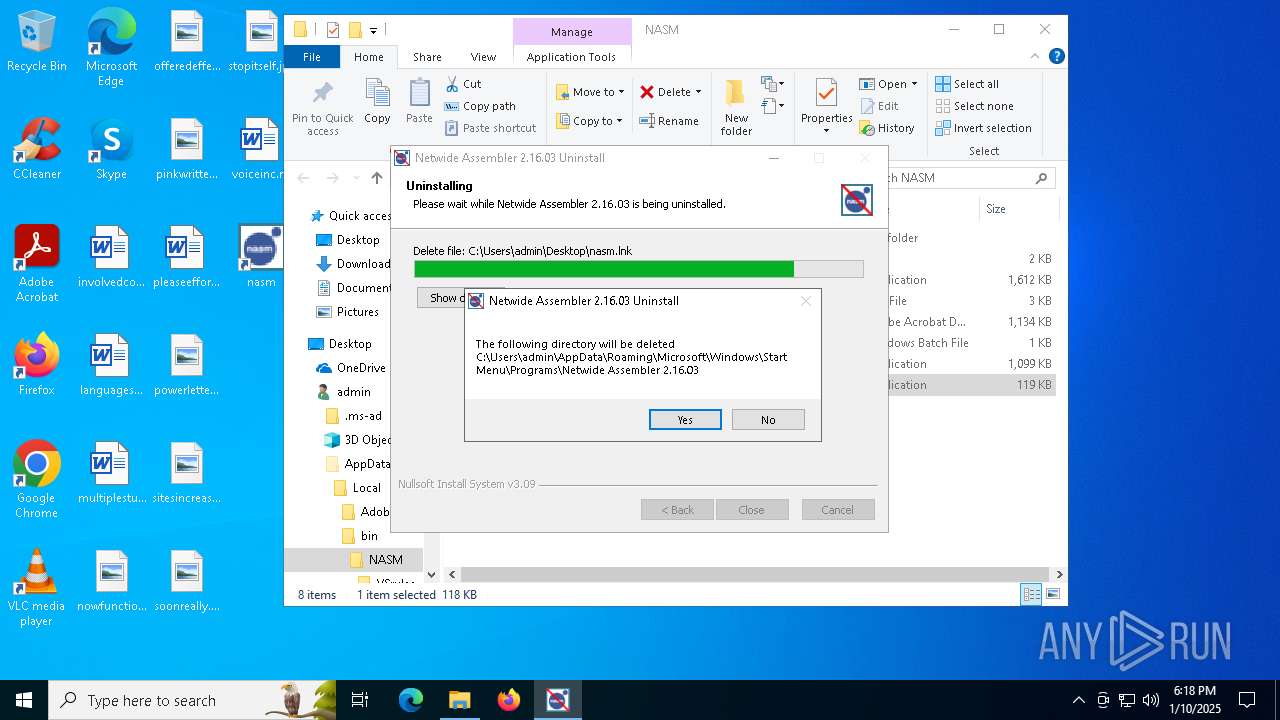
Executable content was dropped or overwritten
- Un.exe (PID: 6928)
- nasm-2.16.03-installer-x64.exe (PID: 6276)
- Uninstall.exe (PID: 6772)
Starts itself from another location
- Uninstall.exe (PID: 6772)
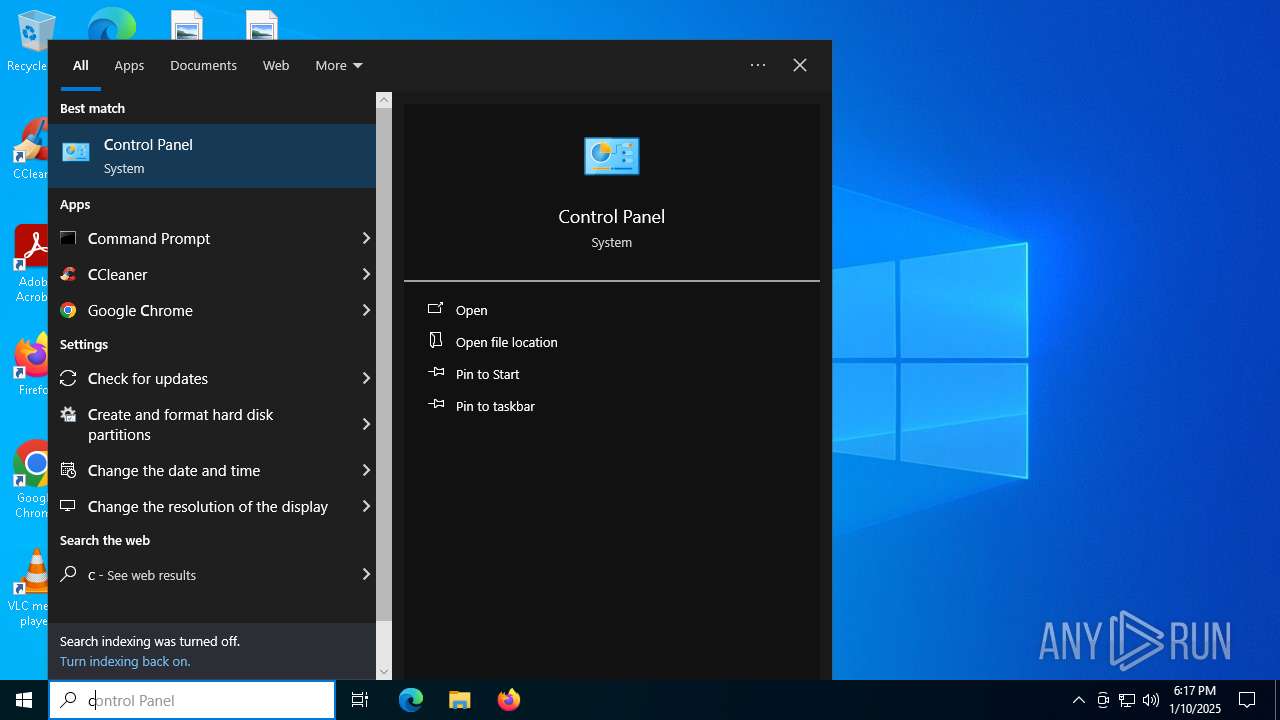
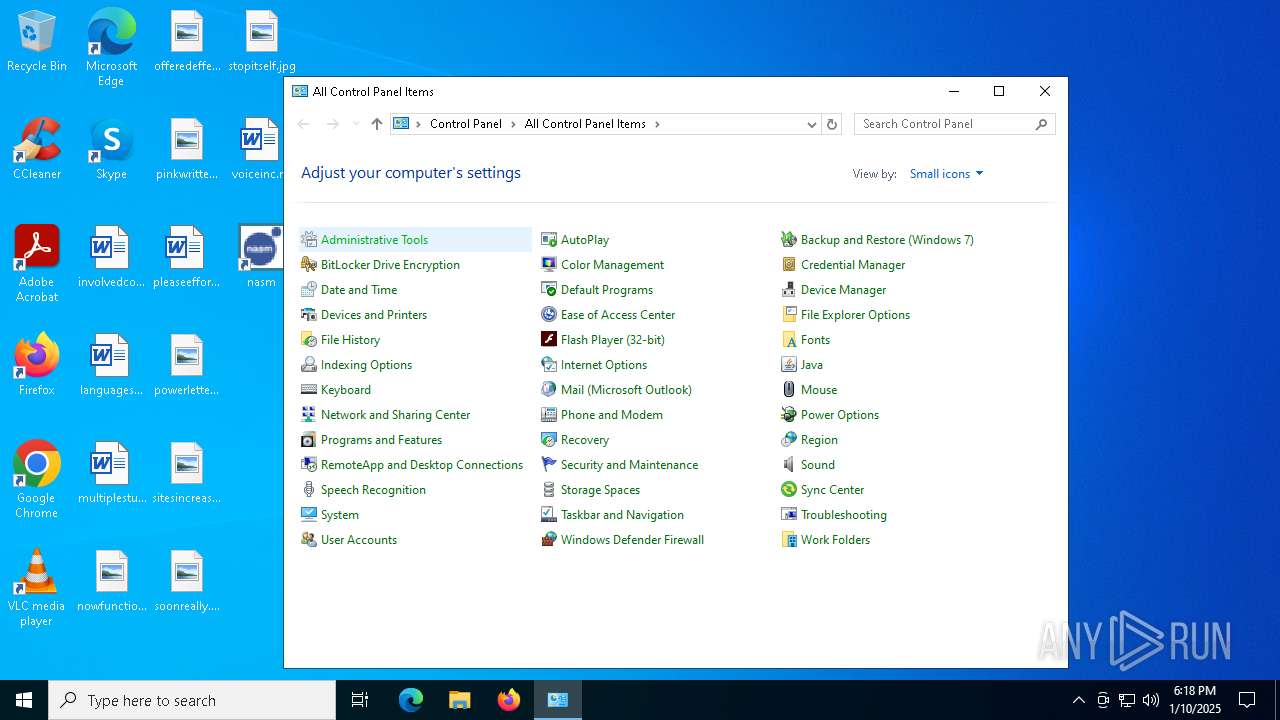
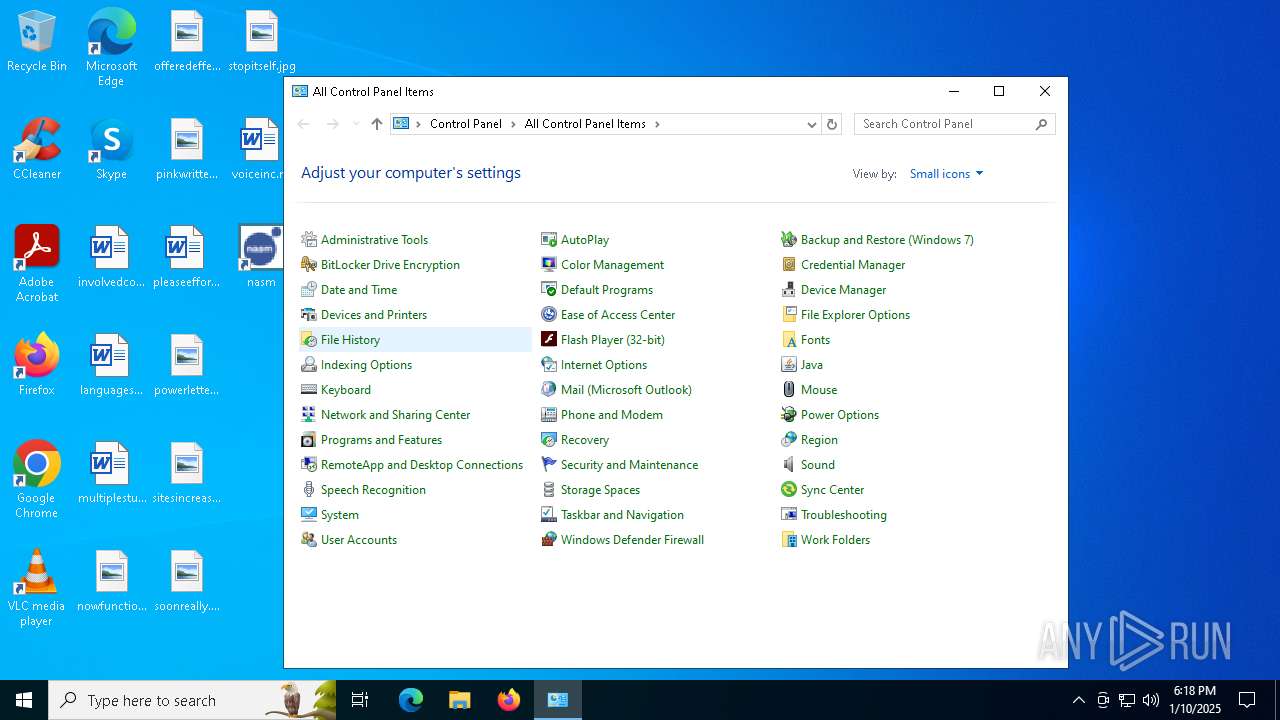
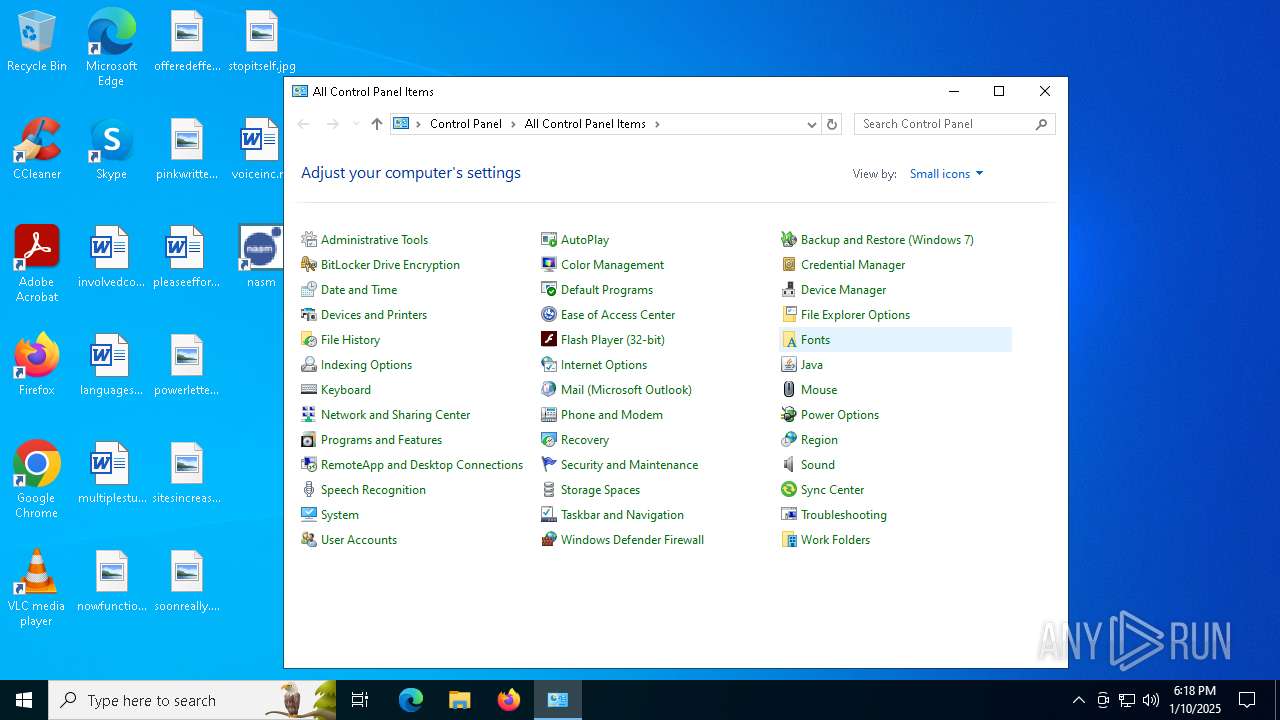
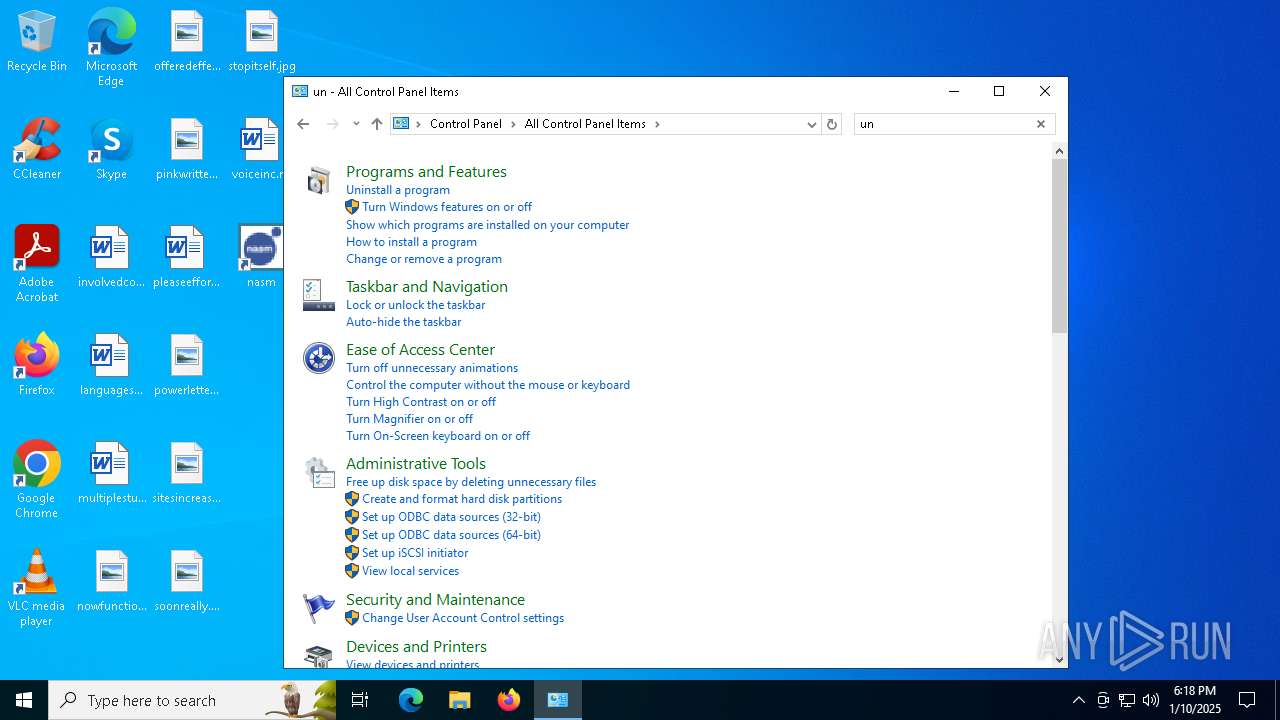
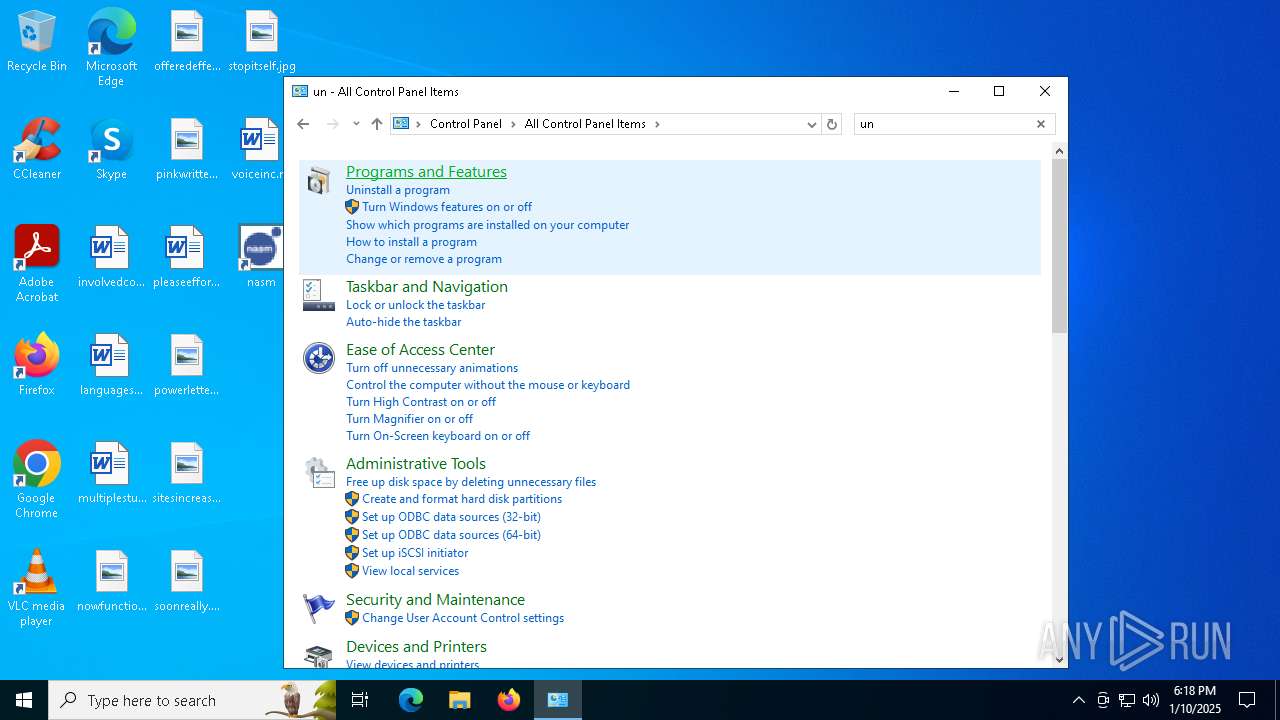
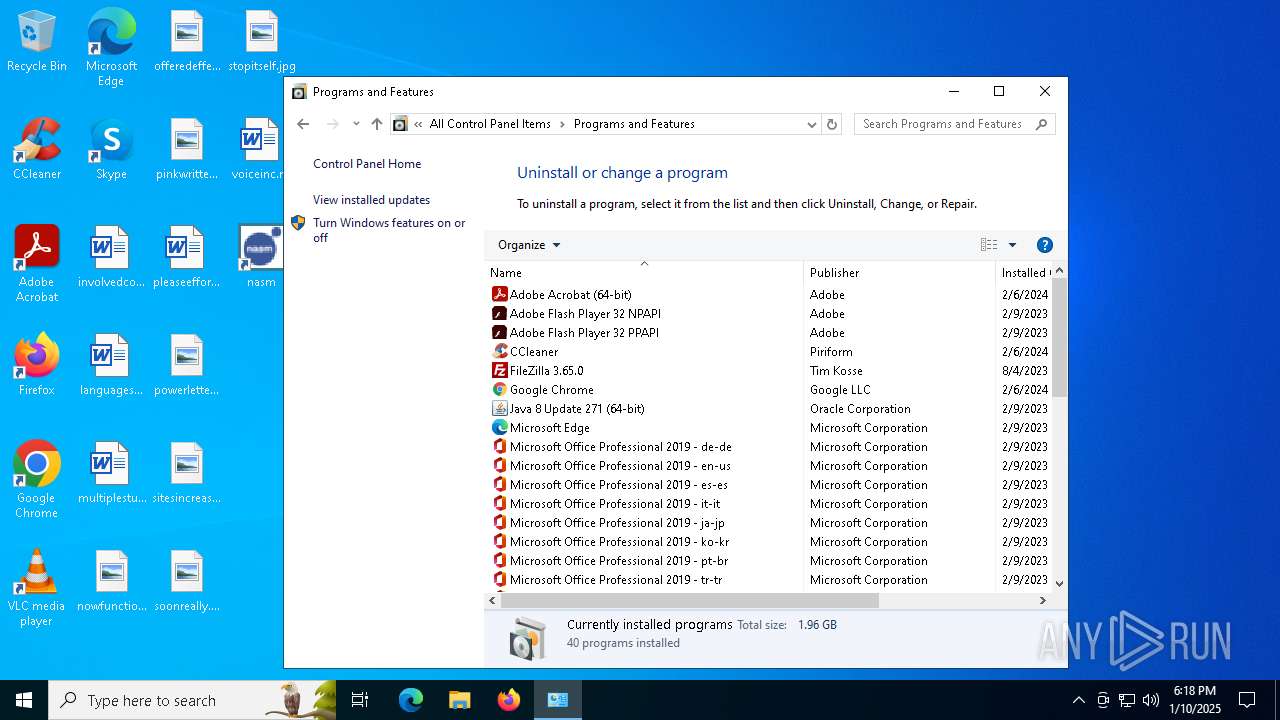
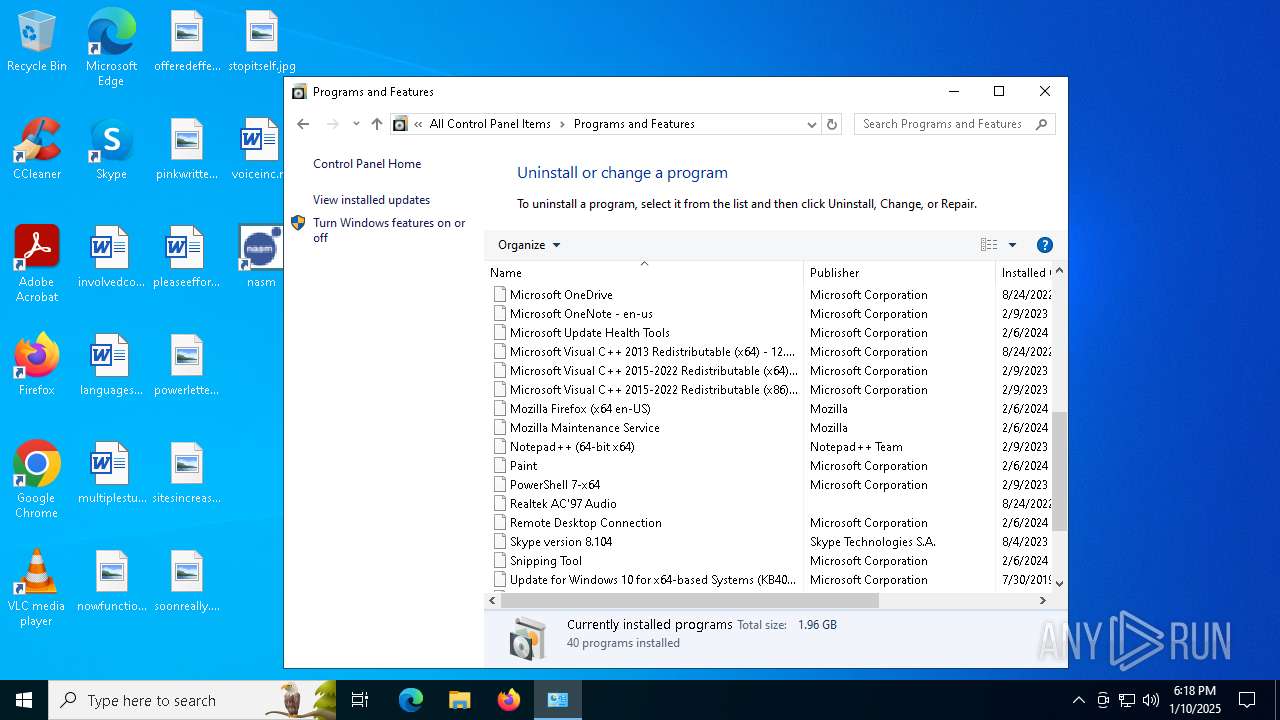
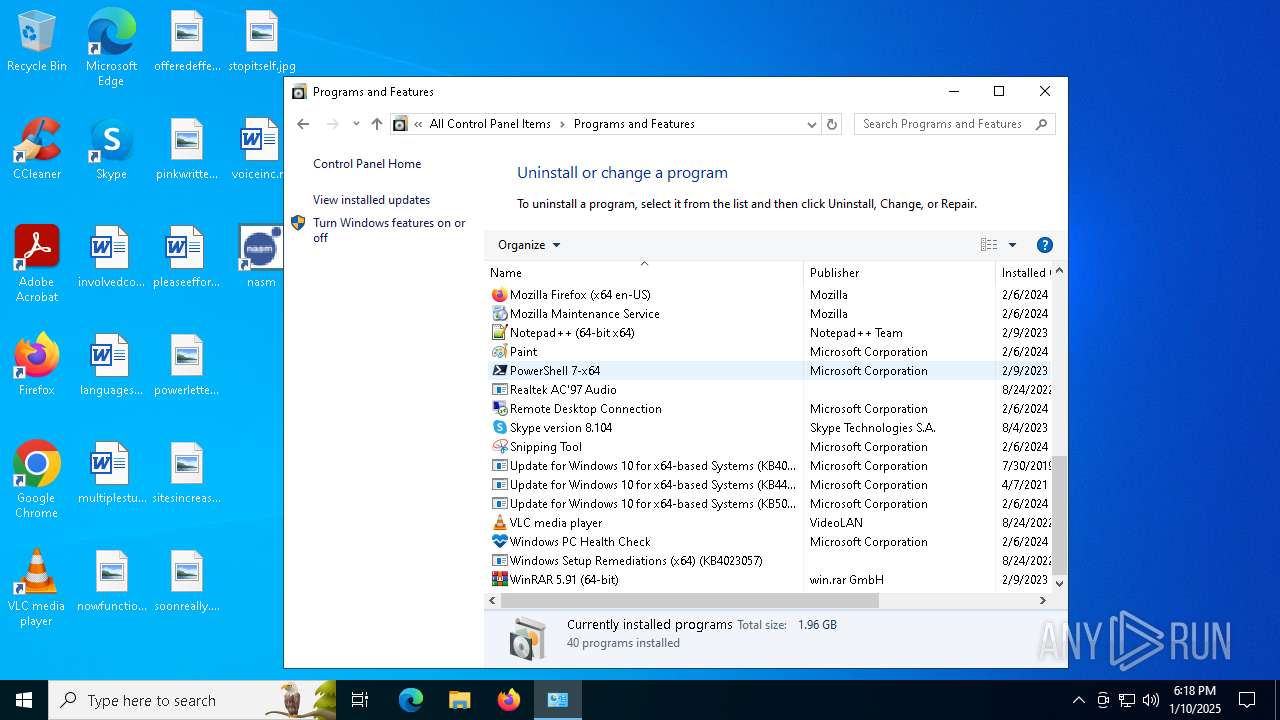
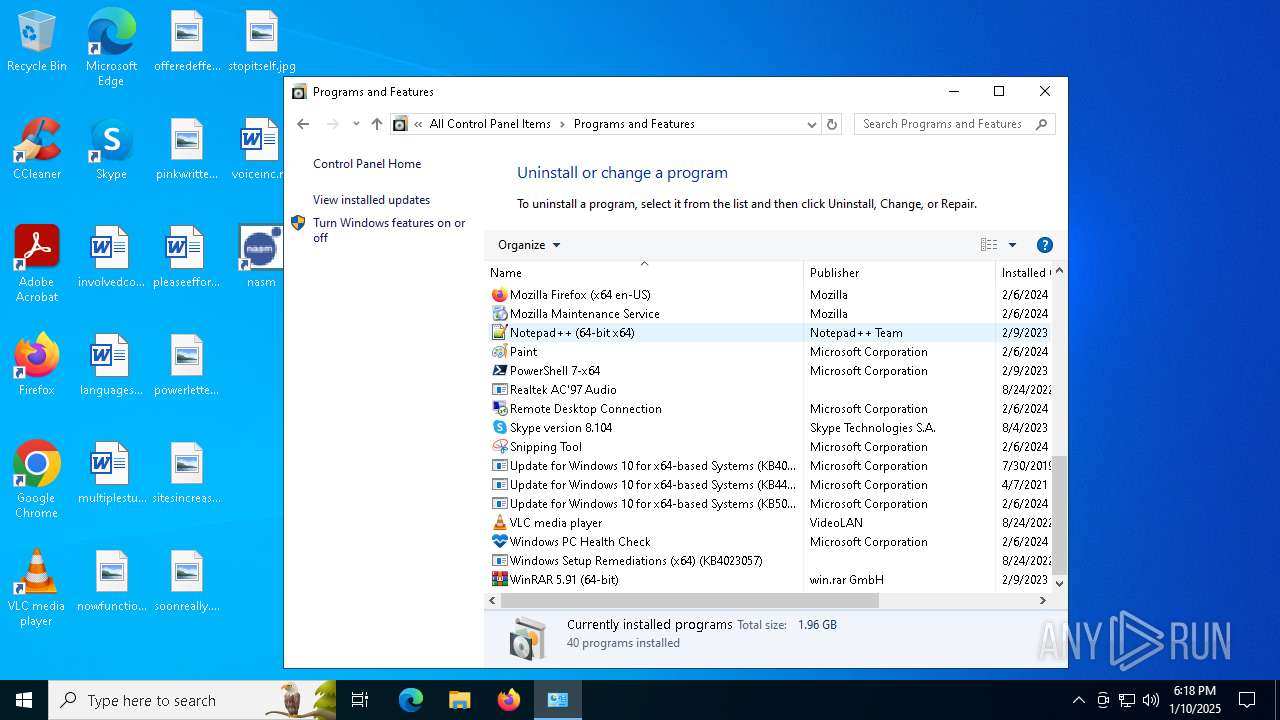
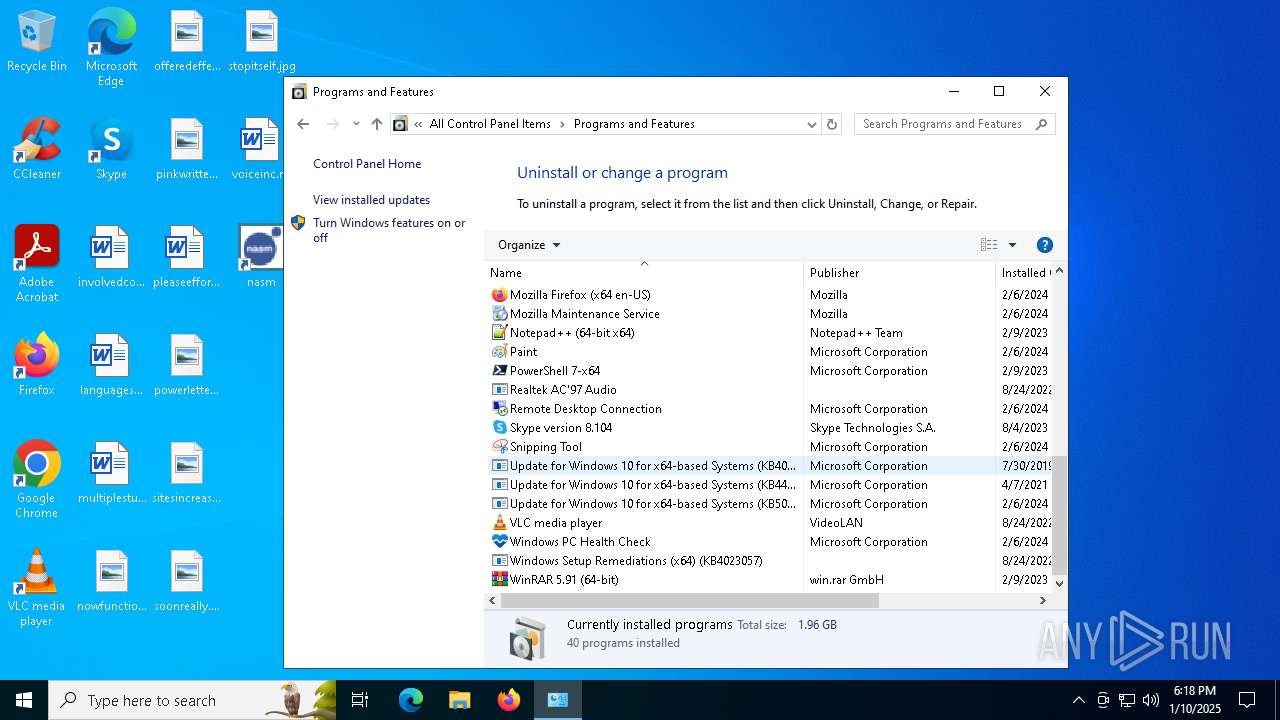
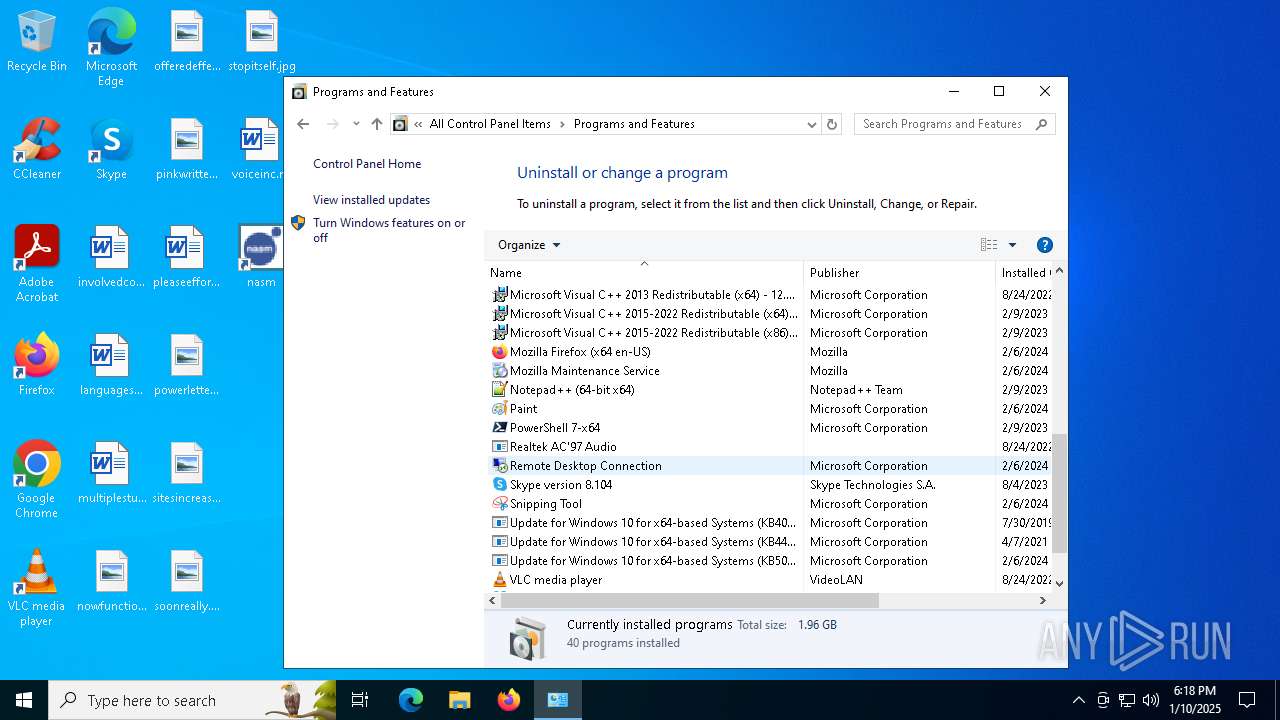
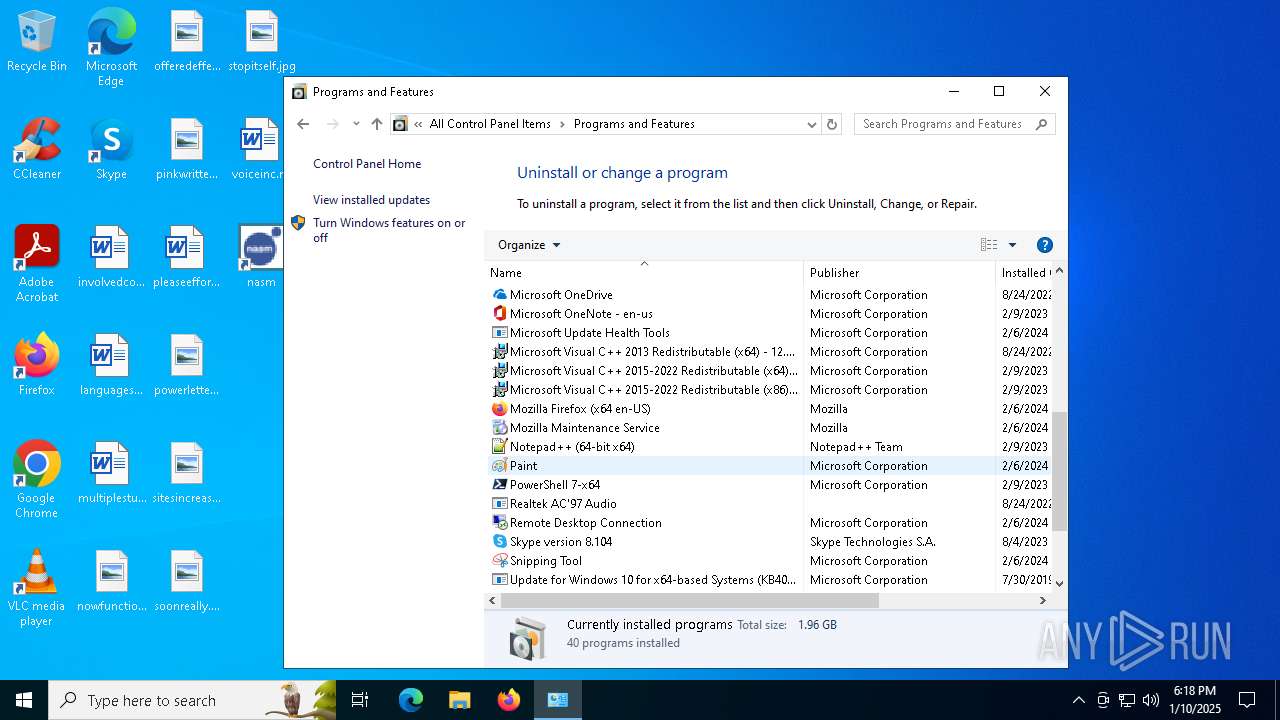
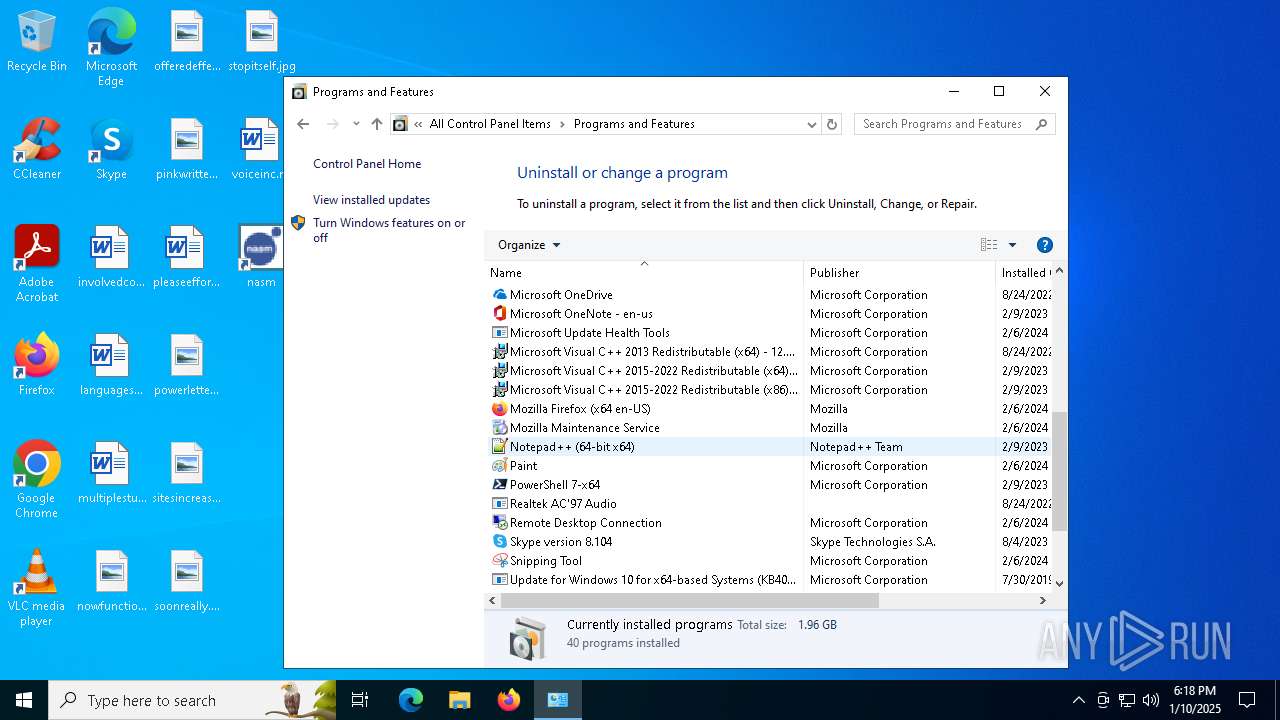
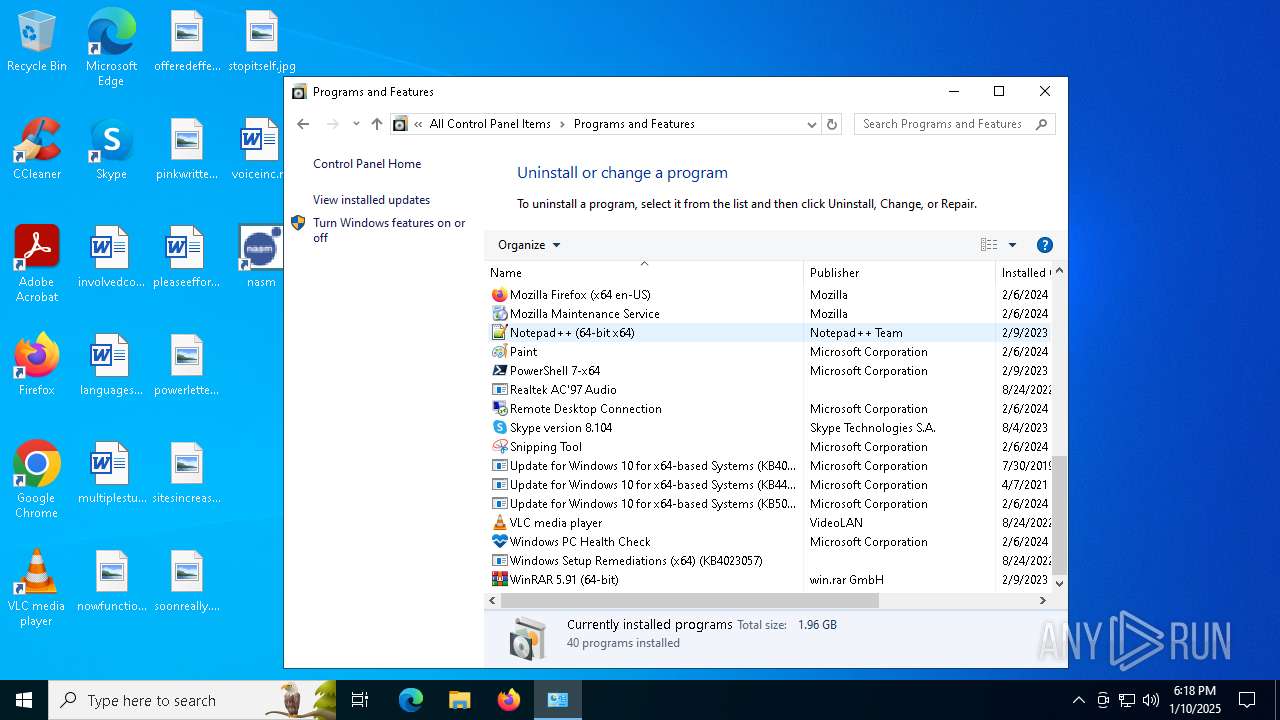
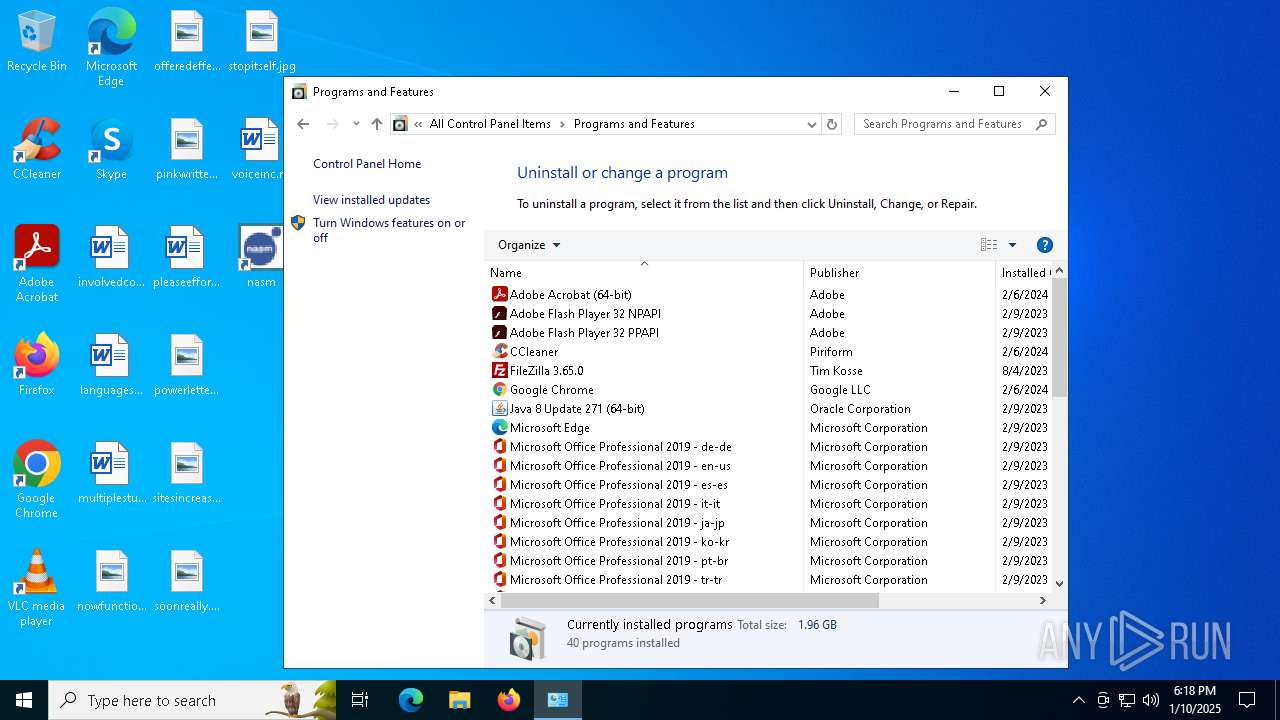
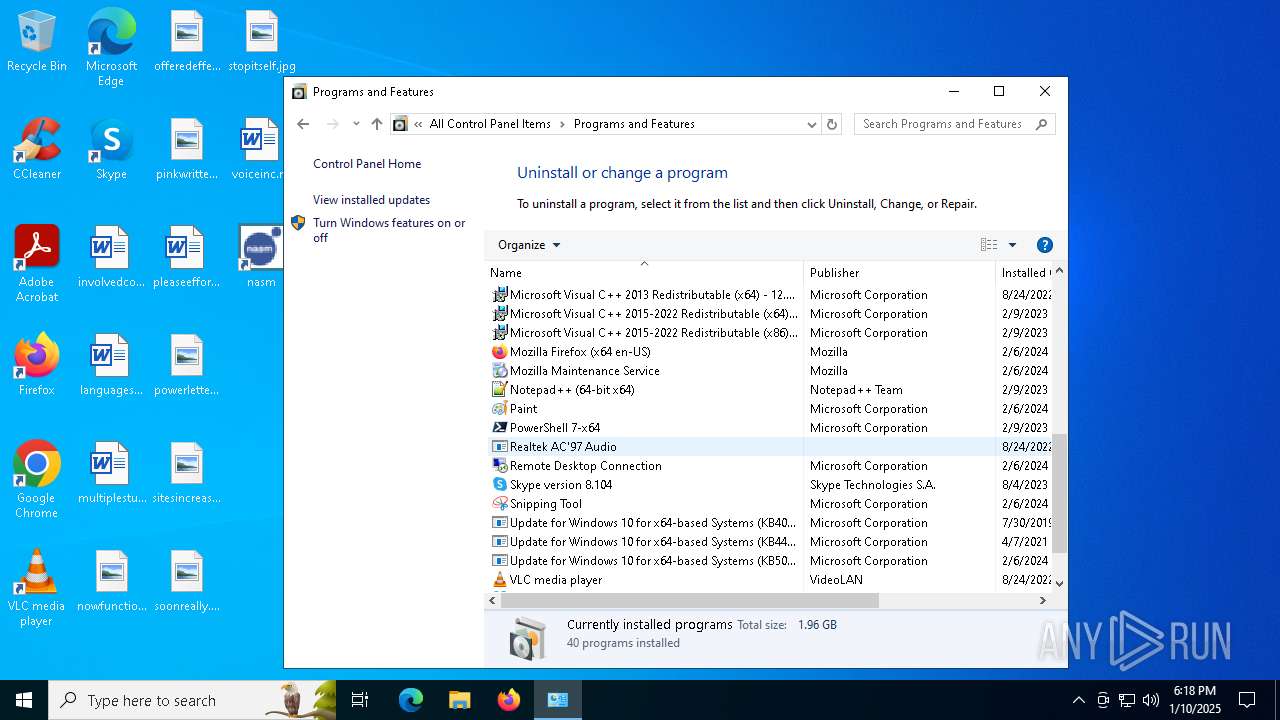
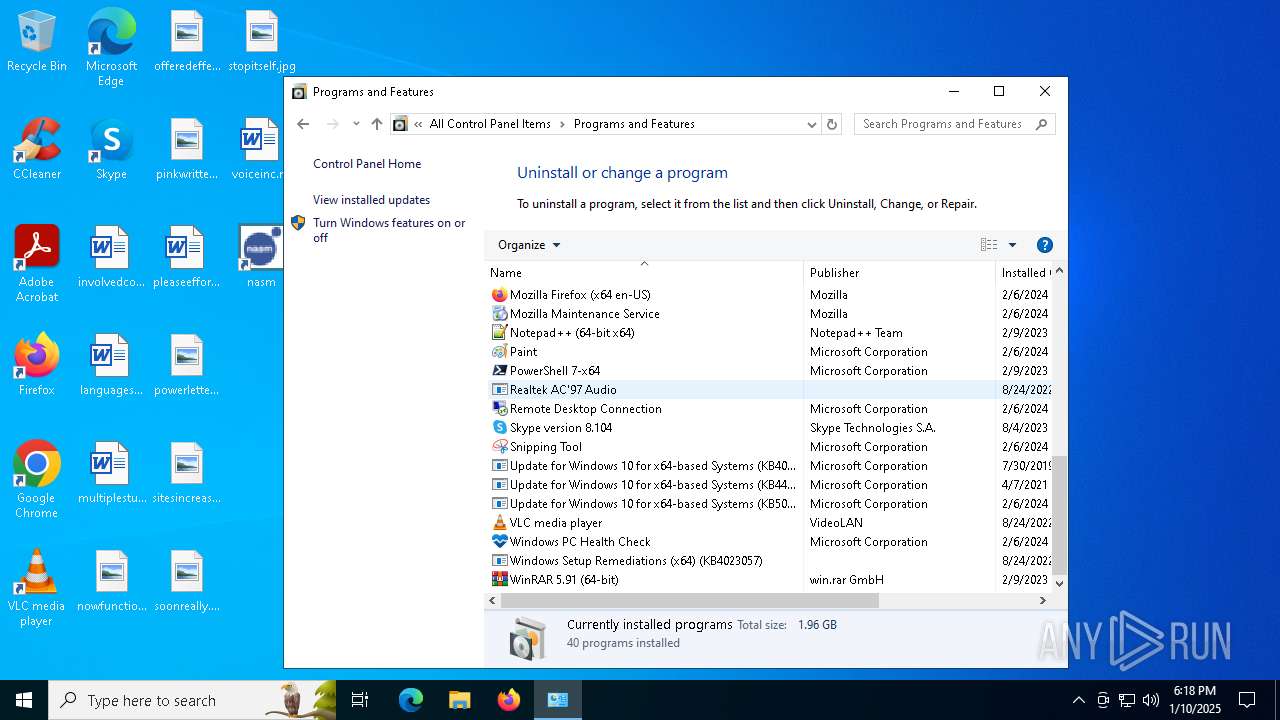
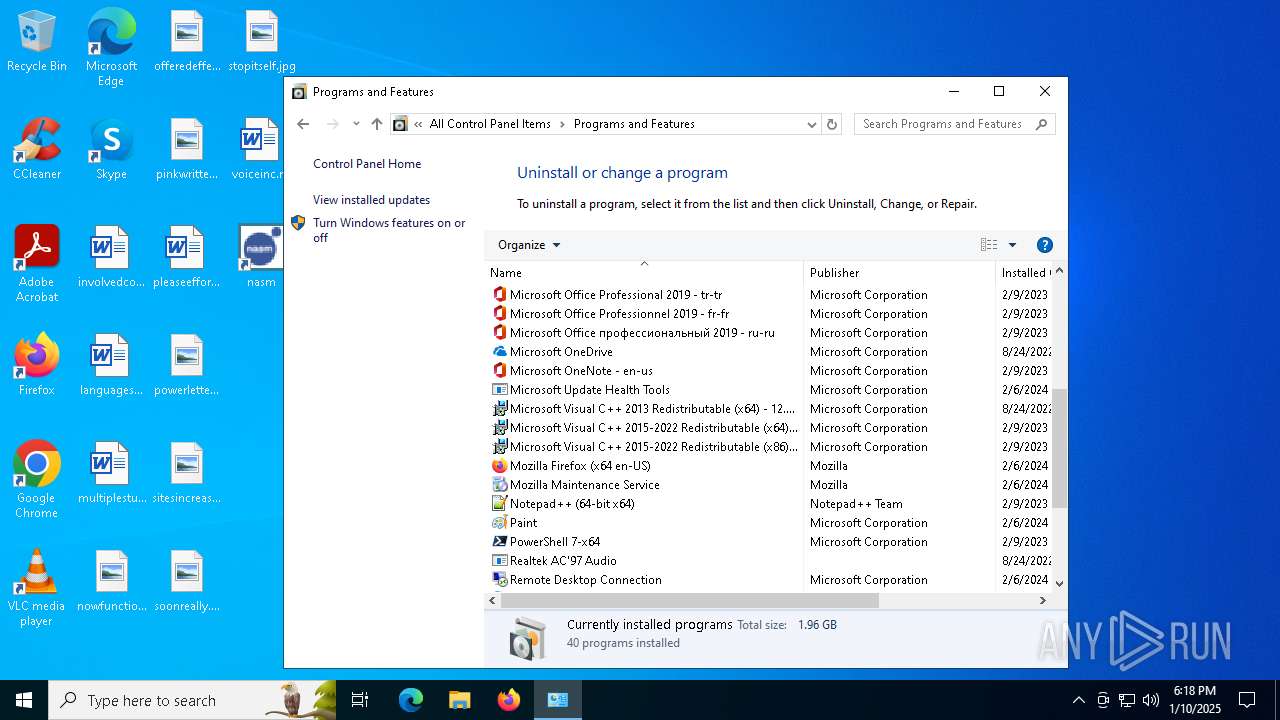
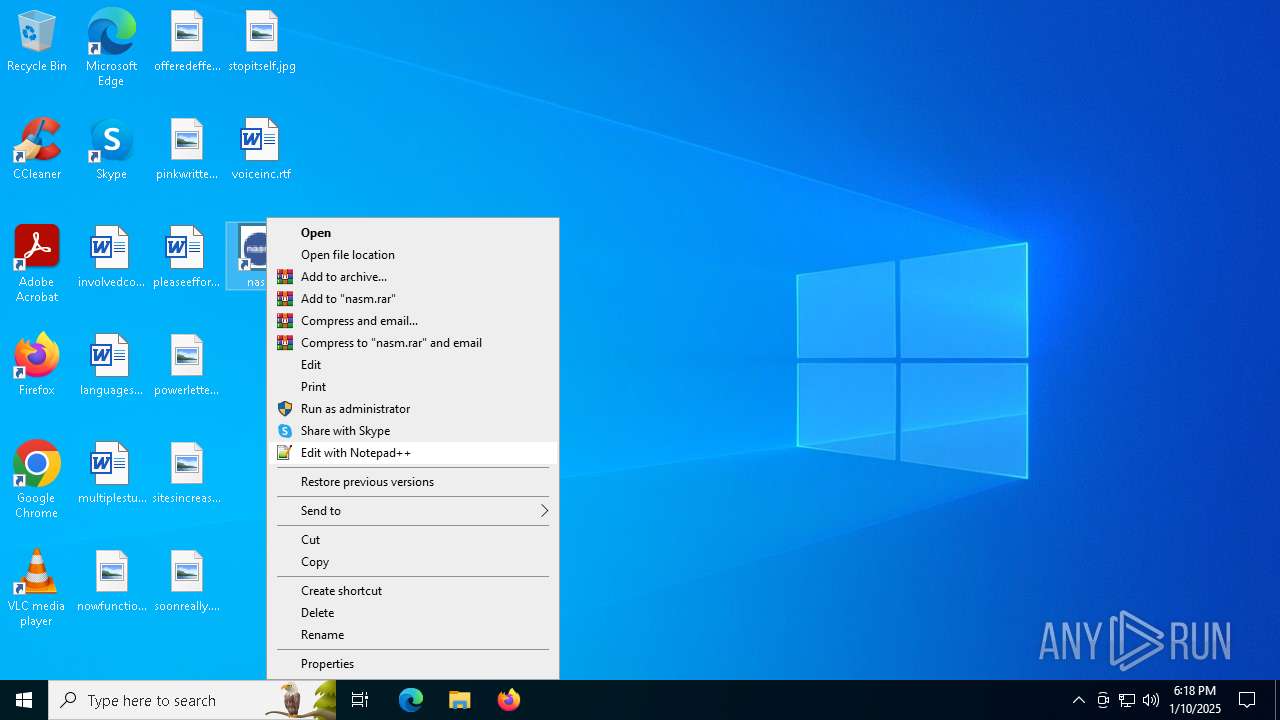
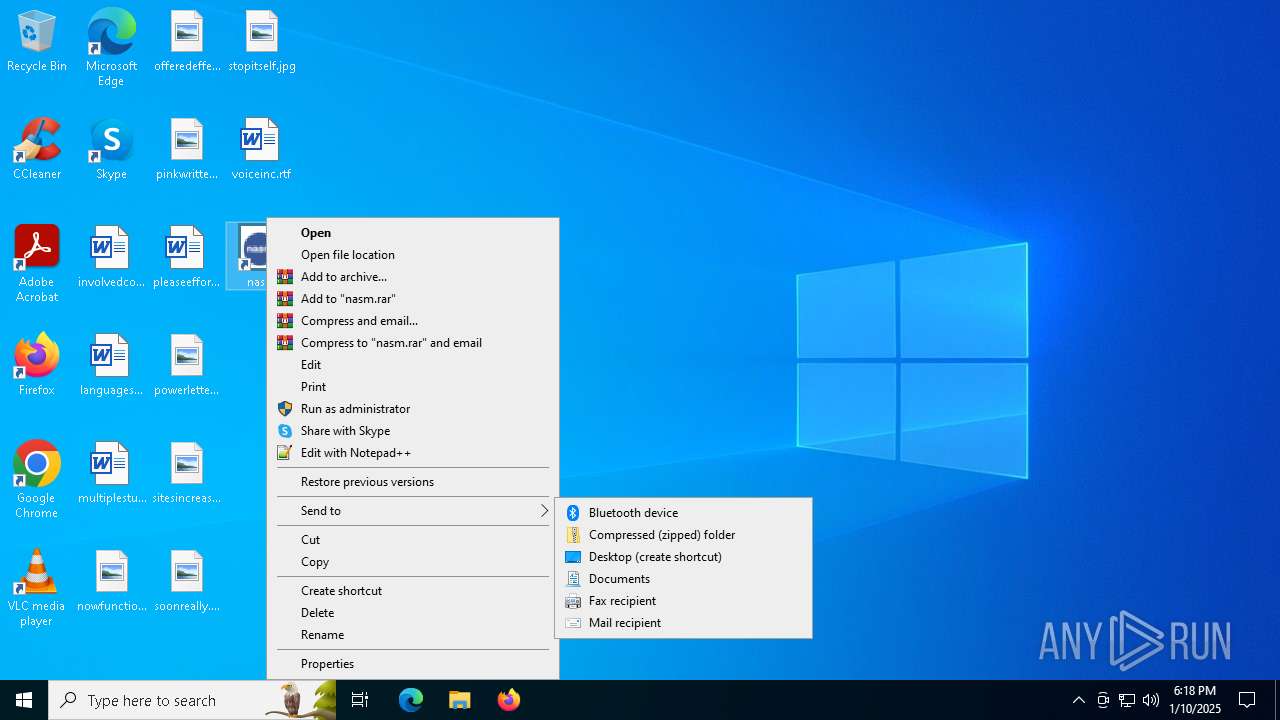
Searches for installed software
- explorer.exe (PID: 6316)
INFO
Create files in a temporary directory
- nasm-2.16.03-installer-x64.exe (PID: 6276)
Checks supported languages
- nasm-2.16.03-installer-x64.exe (PID: 6276)
Creates files or folders in the user directory
- nasm-2.16.03-installer-x64.exe (PID: 6276)
Reads the computer name
- nasm-2.16.03-installer-x64.exe (PID: 6276)
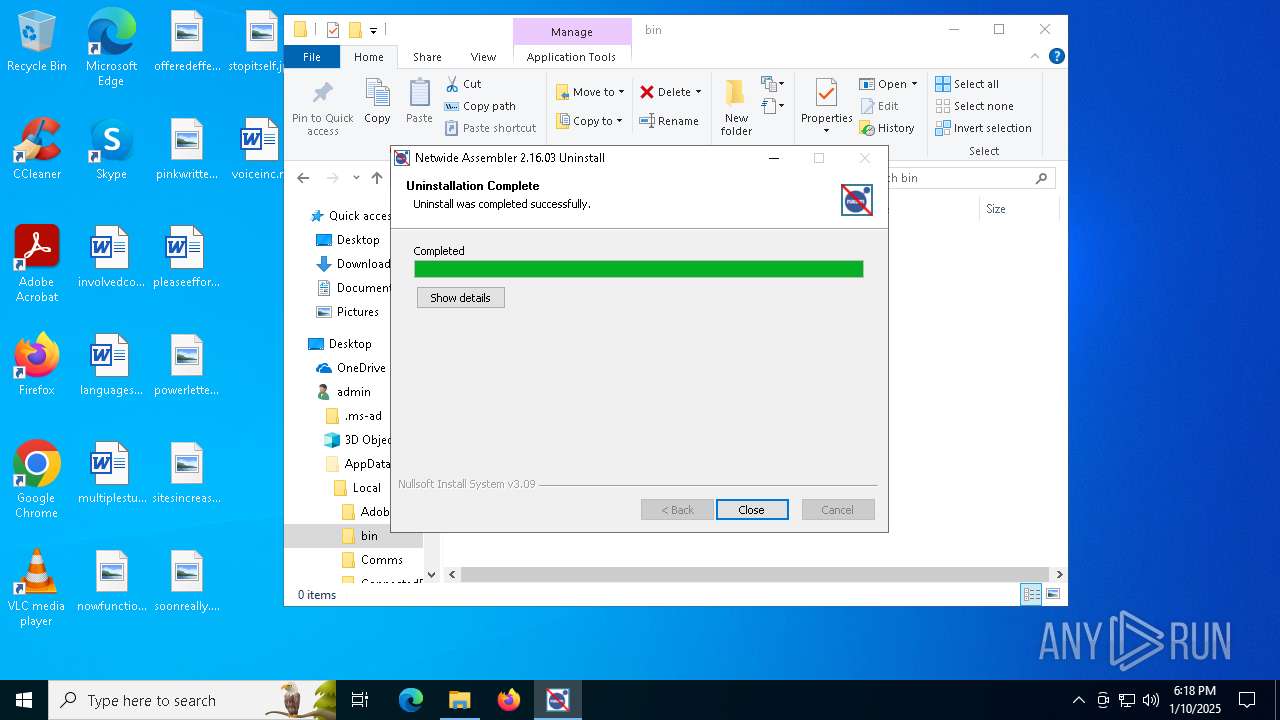
Manual execution by a user
- Uninstall.exe (PID: 6772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:20 00:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.4 |
| CodeSize: | 40960 |
| InitializedDataSize: | 67584 |
| UninitializedDataSize: | 407552 |
| EntryPoint: | 0x4c30 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2380 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5732 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6276 | "C:\Users\admin\AppData\Local\Temp\nasm-2.16.03-installer-x64.exe" | C:\Users\admin\AppData\Local\Temp\nasm-2.16.03-installer-x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6316 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
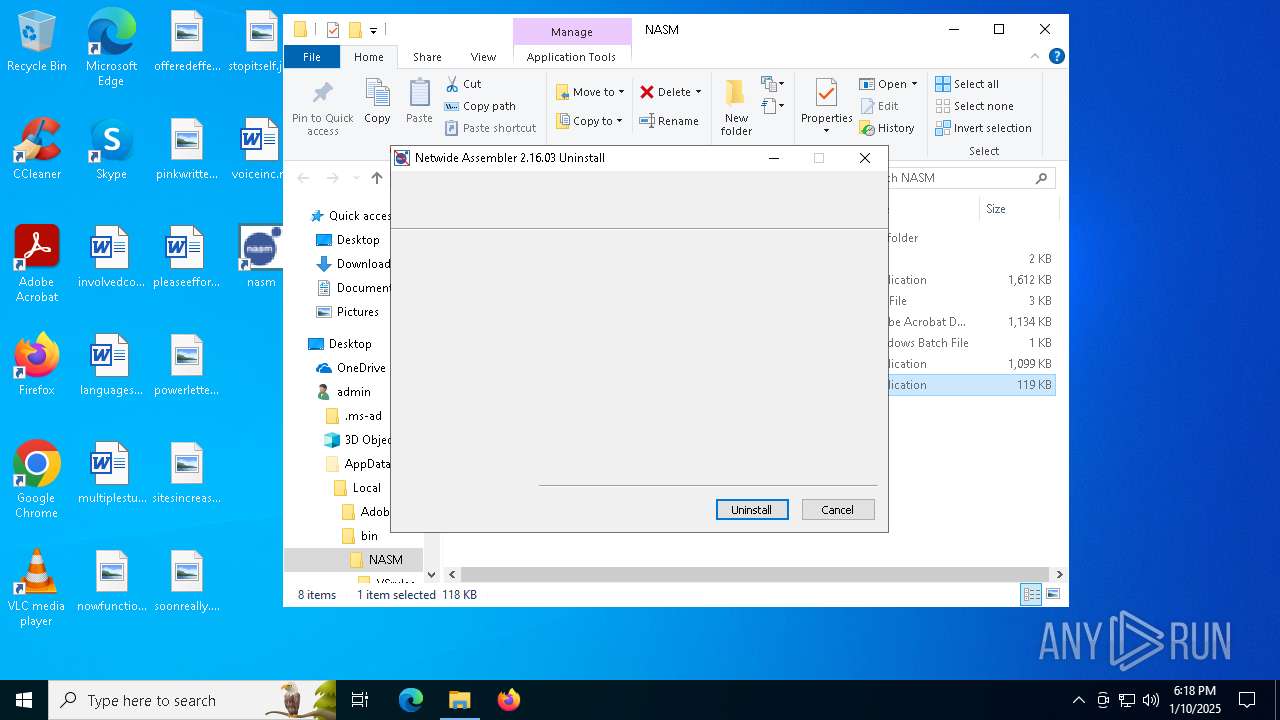
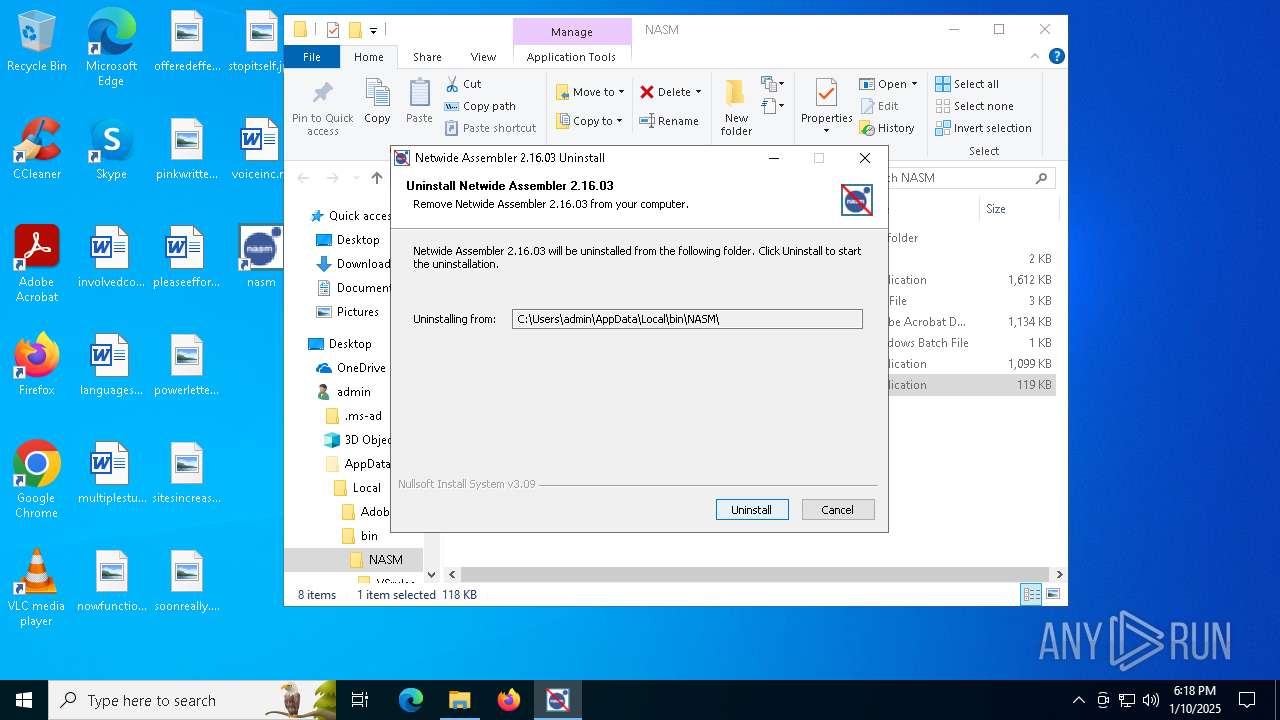
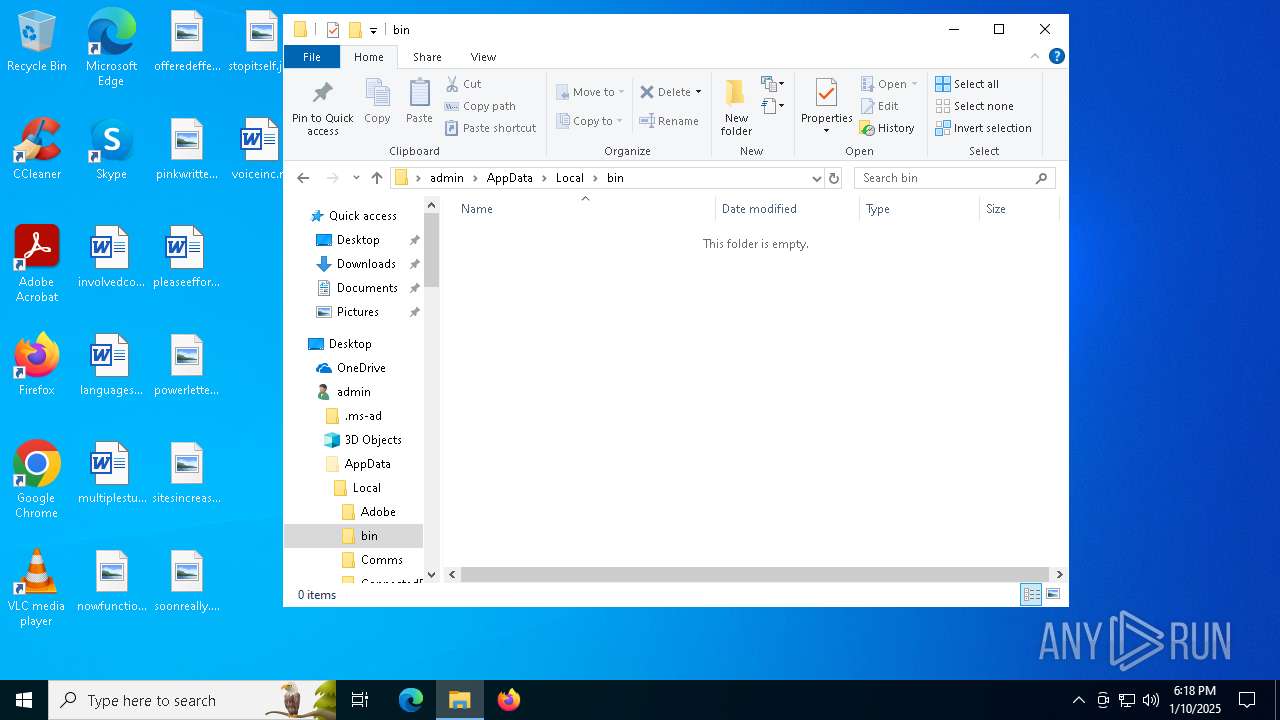
| 6772 | "C:\Users\admin\AppData\Local\bin\NASM\Uninstall.exe" | C:\Users\admin\AppData\Local\bin\NASM\Uninstall.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6928 | "C:\Users\admin\AppData\Local\Temp\~nsu1.tmp\Un.exe" _?=C:\Users\admin\AppData\Local\bin\NASM\ | C:\Users\admin\AppData\Local\Temp\~nsu1.tmp\Un.exe | Uninstall.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
18 459
Read events
18 403
Write events
54
Delete events
2
Modification events
| (PID) Process: | (6276) nasm-2.16.03-installer-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\nasm |
| Operation: | write | Name: | nasm |
Value: Netwide Assembler 2.16.03 | |||
| (PID) Process: | (6276) nasm-2.16.03-installer-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\nasm |
| Operation: | write | Name: | lnk |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Netwide Assembler 2.16.03 | |||
| (PID) Process: | (6276) nasm-2.16.03-installer-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\nasm |
| Operation: | write | Name: | bat-lnk |
Value: C:\Users\admin\Desktop\nasm.lnk | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 00000000040000000E00000003000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | Rev |
Value: 0 | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | FFlags |
Value: 18874369 | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | Vid |
Value: {137E7700-3573-11CF-AE69-08002B2E1262} | |||
| (PID) Process: | (6316) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
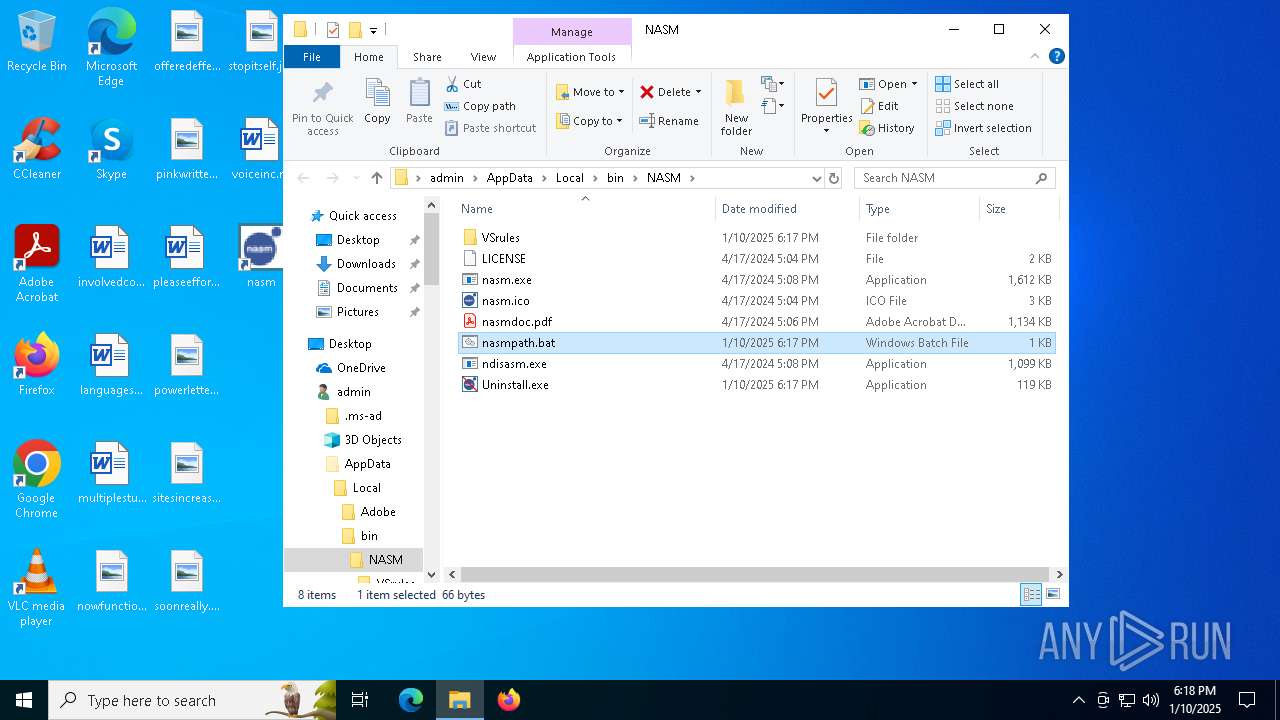
Executable files
7
Suspicious files
9
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Local\bin\NASM\ndisasm.exe | executable | |
MD5:43544DF799C5C503DC1D4D35F388825A | SHA256:CD57BE890F2D3D87189E67EB1C2537DE6B85DFC843461D7C0FDD437DC0F1270D | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Local\bin\NASM\nasm.ico | image | |
MD5:E4017E050E3A359A898AA0E01364C6B9 | SHA256:C2FAB8B5C7CF43FB7E381AB39FBF625A30267646D9B6795034BFE3E610066C8D | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Local\Temp\nsi51EE.tmp\UserInfo.dll | executable | |
MD5:14526F5953A85912872802AE286A787A | SHA256:C224F7DA273EE3815E462BE08FFF79B1435EB6E7733E3D4FEA5BD95C9F4B1D26 | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Local\bin\NASM\LICENSE | text | |
MD5:90904486F8FBF1861CF42752E1A39EFE | SHA256:1563996C52E220E15EF2418E67D39488255AA8C28C89E617074D3AFE3EE329E0 | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Netwide Assembler 2.16.03\nasm.lnk | binary | |
MD5:4D45C9292C0C0661E9211B2CEED93D65 | SHA256:D6371EA89B06B75FF1E5D1D7554FE444ABAD6ED0C66498811092FDA598CE0443 | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\Desktop\nasm.lnk | binary | |
MD5:498EAD2740D49AF0F3F4BF5B3B608322 | SHA256:93E242A1256D46AB48A4CAE8C21F6E68CDF5A054D47A1F7E775491D499ED0A98 | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Netwide Assembler 2.16.03\Manual.lnk | binary | |
MD5:541DBEF748C6AB4E4C3AE6DB012D6EDD | SHA256:686FDFAB4ACE805DA456E0FD8A919F3FDF411962A7DEA777AC8079BF41E598C7 | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Netwide Assembler 2.16.03\nasm-shell.lnk | binary | |
MD5:8A5529F772D9CA8A7882F14CD4E383C1 | SHA256:76D8E2133C402B4C62D85242609778B96A166ADFD5190CA90A3ABBBDFA42B96F | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Local\bin\NASM\nasmdoc.pdf | ||
MD5:2322E3E634FDB0904E5A758D58D0C09C | SHA256:1B6CF21AAE13988F4190D007853F126D702A24B3EC9AA2E01E1C75D8BB437185 | |||
| 6276 | nasm-2.16.03-installer-x64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Netwide Assembler 2.16.03\Uninstall.lnk | binary | |
MD5:4A9E7B67E17B3872DF5BC80BCBFE5905 | SHA256:4C63A4A813A4A5DB8E8788BDBF719892D102B8DB35EBE974E938F948E974ABDF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
40
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4548 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4548 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2456 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |