| File name: | test-for-virus-total-compucare-Agent_Install.exe |
| Full analysis: | https://app.any.run/tasks/2572f57f-c7be-453d-a79c-00ea9dd29247 |
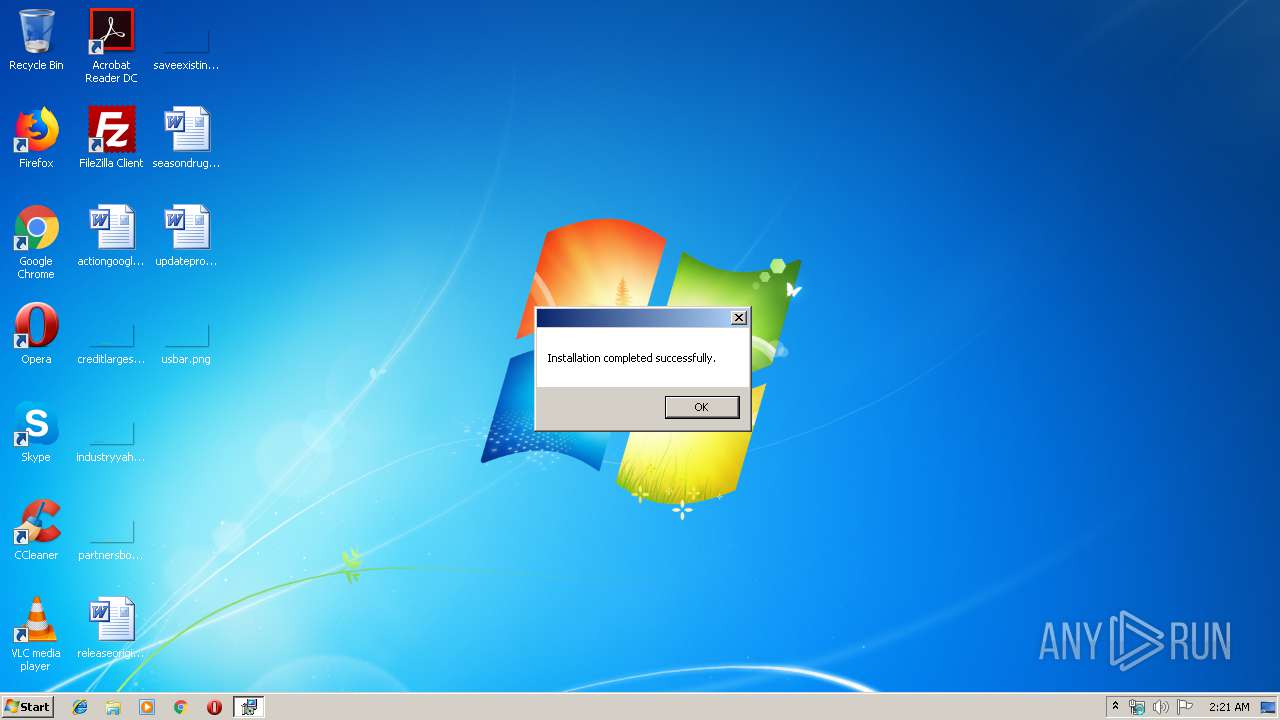
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 01:20:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D8247031A30E5DCFA61005EF3AAA2475 |
| SHA1: | 2453FD3E421329AAAFC54A50BD3066CD5639FF7D |
| SHA256: | 6579E2E4D3A3C5A184447738661C2FC25574224D507241E524190CDC098931E1 |
| SSDEEP: | 98304:VsiIeoDADHKTsgbCKZFBubH4b9ylxeyhjXZGvVuwbCv7p6Qk42fjFAEZl:Vsi1DBgbCKZFsbHxxPhjX0vVuwbkQeAx |
MALICIOUS
Loads dropped or rewritten executable
- test-for-virus-total-compucare-Agent_Install.exe (PID: 924)
- LTSvcMon.exe (PID: 3780)
- LTSVC.exe (PID: 3936)
Application was dropped or rewritten from another process
- test-for-virus-total-compucare-Agent_Install.exe (PID: 924)
- LabTechRemoteAgent.exe (PID: 1724)
- LTSvcMon.exe (PID: 3780)
- LTSVC.exe (PID: 3936)
Changes the autorun value in the registry
- LabTechRemoteAgent.exe (PID: 1724)
Changes settings of System certificates
- msiexec.exe (PID: 1848)
Starts NET.EXE for service management
- MsiExec.exe (PID: 2840)
SUSPICIOUS
Executable content was dropped or overwritten
- test-for-virus-total-compucare-Agent_Install.exe (PID: 3720)
- test-for-virus-total-compucare-Agent_Install.exe (PID: 924)
- LabTechRemoteAgent.exe (PID: 1724)
- msiexec.exe (PID: 1848)
- LTSVC.exe (PID: 3936)
Starts itself from another location
- test-for-virus-total-compucare-Agent_Install.exe (PID: 924)
Executed as Windows Service
- vssvc.exe (PID: 3156)
- LTSVC.exe (PID: 3936)
- LTSvcMon.exe (PID: 3780)
Searches for installed software
- LabTechRemoteAgent.exe (PID: 1724)
Executed via COM
- DrvInst.exe (PID: 876)
Creates a software uninstall entry
- LabTechRemoteAgent.exe (PID: 1724)
Adds / modifies Windows certificates
- msiexec.exe (PID: 1848)
Creates files in the program directory
- LabTechRemoteAgent.exe (PID: 1724)
Creates files in the Windows directory
- msiexec.exe (PID: 1848)
- MsiExec.exe (PID: 2840)
- LTSvcMon.exe (PID: 3780)
- LTSVC.exe (PID: 3936)
Reads Environment values
- LTSVC.exe (PID: 3936)
- LTSvcMon.exe (PID: 3780)
Removes files from Windows directory
- LTSVC.exe (PID: 3936)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3156)
Application launched itself
- msiexec.exe (PID: 1848)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2840)
- MsiExec.exe (PID: 3432)
Creates a software uninstall entry
- msiexec.exe (PID: 1848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:28 19:25:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 301568 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e0c1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.161.0 |
| ProductVersionNumber: | 19.0.161.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ConnectWise, Inc. |
| FileDescription: | ConnectWise Automate Remote Agent |
| FileVersion: | 19.0.161 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ConnectWise, Inc.. All rights reserved. |
| OriginalFileName: | LabTechRemoteAgent.exe |
| ProductName: | ConnectWise Automate Remote Agent |
| ProductVersion: | 19.0.161 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Feb-2018 18:25:32 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ConnectWise, Inc. |
| FileDescription: | ConnectWise Automate Remote Agent |
| FileVersion: | 19.0.161 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) ConnectWise, Inc.. All rights reserved. |
| OriginalFilename: | LabTechRemoteAgent.exe |
| ProductName: | ConnectWise Automate Remote Agent |
| ProductVersion: | 19.0.161 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 28-Feb-2018 18:25:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049827 | 0x00049A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55956 |
.rdata | 0x0004B000 | 0x0001EB34 | 0x0001EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11602 |
.data | 0x0006A000 | 0x00001740 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12305 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.739068 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gfids | 0x0006E000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.01067 |
.rsrc | 0x0006F000 | 0x00003A80 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52825 |
.reloc | 0x00073000 | 0x00003D8C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.7698 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
70
Monitored processes
26
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | C:\Windows\system32\net1 stop LTSvcMon | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 876 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot21" "" "" "6f9bf5bcb" "00000000" "000005C8" "000002BC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | "C:\Windows\System32\net.exe" stop LTService | C:\Windows\System32\net.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | "C:\Users\admin\AppData\Local\Temp\{A46BC3A7-D42C-4A32-B41B-2DEBC765524D}\.cr\test-for-virus-total-compucare-Agent_Install.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\test-for-virus-total-compucare-Agent_Install.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{A46BC3A7-D42C-4A32-B41B-2DEBC765524D}\.cr\test-for-virus-total-compucare-Agent_Install.exe | test-for-virus-total-compucare-Agent_Install.exe | ||||||||||||
User: admin Company: ConnectWise, Inc. Integrity Level: MEDIUM Description: ConnectWise Automate Remote Agent Exit code: 0 Version: 19.0.161 Modules
| |||||||||||||||
| 996 | "C:\Windows\System32\net.exe" stop LTSvcMon | C:\Windows\System32\net.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1588 | "C:\Windows\System32\net.exe" stop LTService | C:\Windows\System32\net.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.be\LabTechRemoteAgent.exe" -q -burn.elevated BurnPipe.{5122041C-E101-41AA-BDCF-6A4571A0294B} {CB543D38-693C-435A-903B-B6E2DF1F3D3D} 924 | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.be\LabTechRemoteAgent.exe | test-for-virus-total-compucare-Agent_Install.exe | ||||||||||||
User: admin Company: ConnectWise, Inc. Integrity Level: HIGH Description: ConnectWise Automate Remote Agent Exit code: 0 Version: 19.0.161 Modules
| |||||||||||||||
| 1848 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | "C:\Windows\System32\net.exe" stop LTSvcMon | C:\Windows\System32\net.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | C:\Windows\system32\net1 stop LTSvcMon | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 152
Read events
733
Write events
402
Delete events
17
Modification events
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (924) test-for-virus-total-compucare-Agent_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test-for-virus-total-compucare-Agent_Install_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
53
Suspicious files
16
Text files
142
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{A46BC3A7-D42C-4A32-B41B-2DEBC765524D}\.cr\test-for-virus-total-compucare-Agent_Install.exe | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\Microsoft.Deployment.Compression.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\RemoteAgentBootstrapper.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\Janus.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\winterop.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\wix.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\Microsoft.Deployment.Resources.dll | executable | |
MD5:— | SHA256:— | |||
| 924 | test-for-virus-total-compucare-Agent_Install.exe | C:\Users\admin\AppData\Local\Temp\{4CB04919-B2D8-46E3-AE67-47DC1845CAB4}\.ba\BootstrapperCore.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3936 | LTSVC.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkgbagepQkweqv7zzfEP | US | der | 1.48 Kb | whitelisted |
3936 | LTSVC.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/gsextendcodesignsha2g3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQ3DAV9N6WelMGCzSTdNIqjdmfHiAQU3CxYLCpvNS2feZWoSF3EbT5Tv7kCDBWcvWHUaDWCegib0A%3D%3D | US | der | 1.55 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3936 | LTSVC.exe | 151.101.2.133:80 | ocsp2.globalsign.com | Fastly | US | malicious |
924 | test-for-virus-total-compucare-Agent_Install.exe | 3.81.51.111:443 | compucaresystems.hostedrmm.com | — | US | suspicious |
3936 | LTSVC.exe | 3.81.51.111:443 | compucaresystems.hostedrmm.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
compucaresystems.hostedrmm.com |
| suspicious |
ocsp2.globalsign.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report