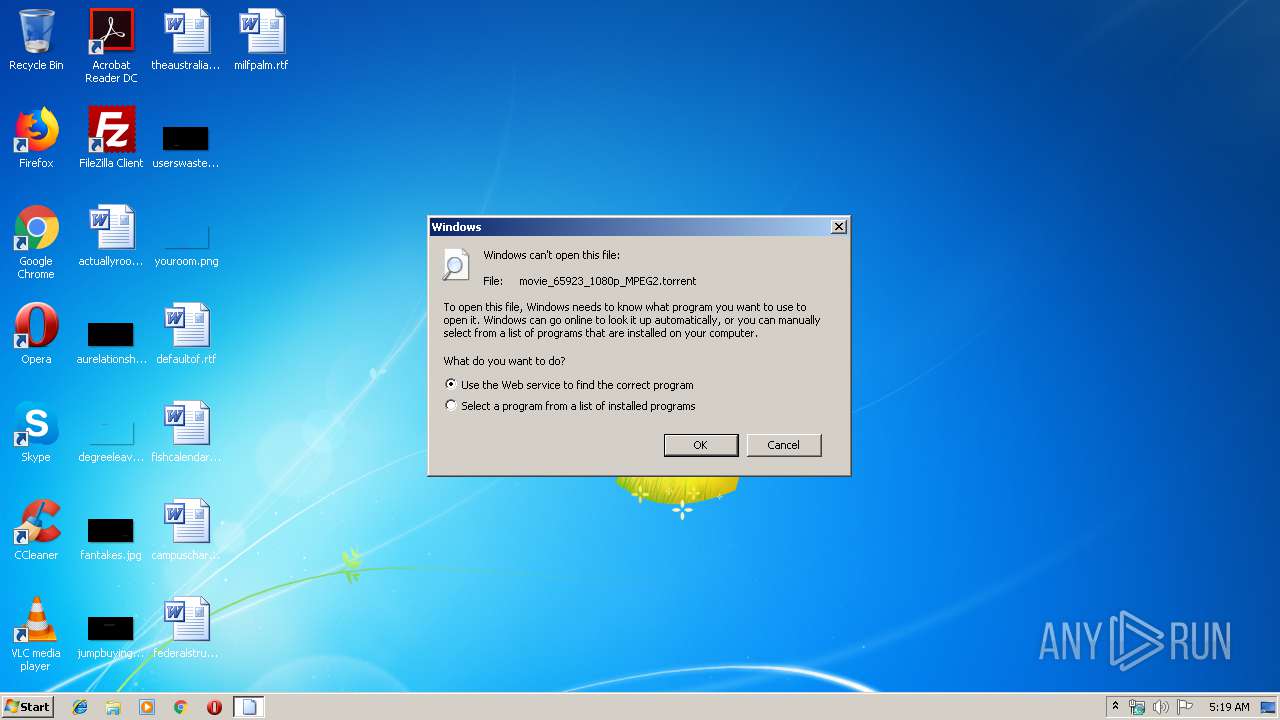
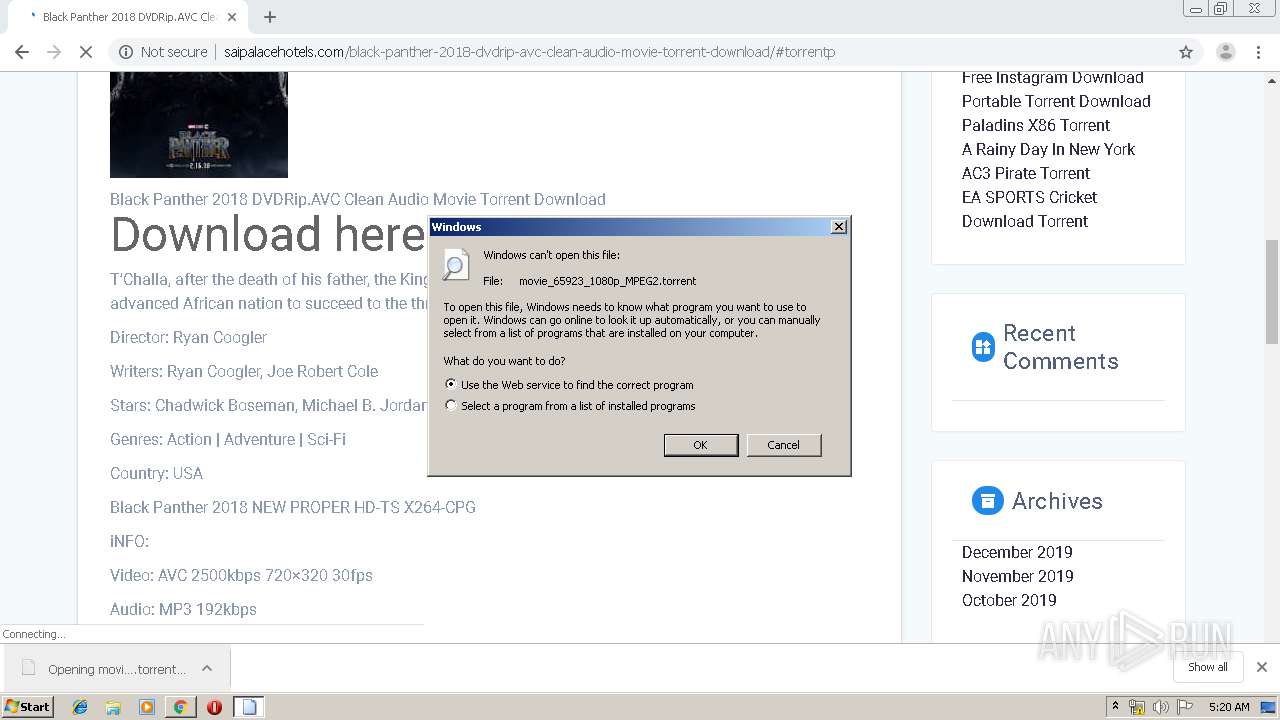
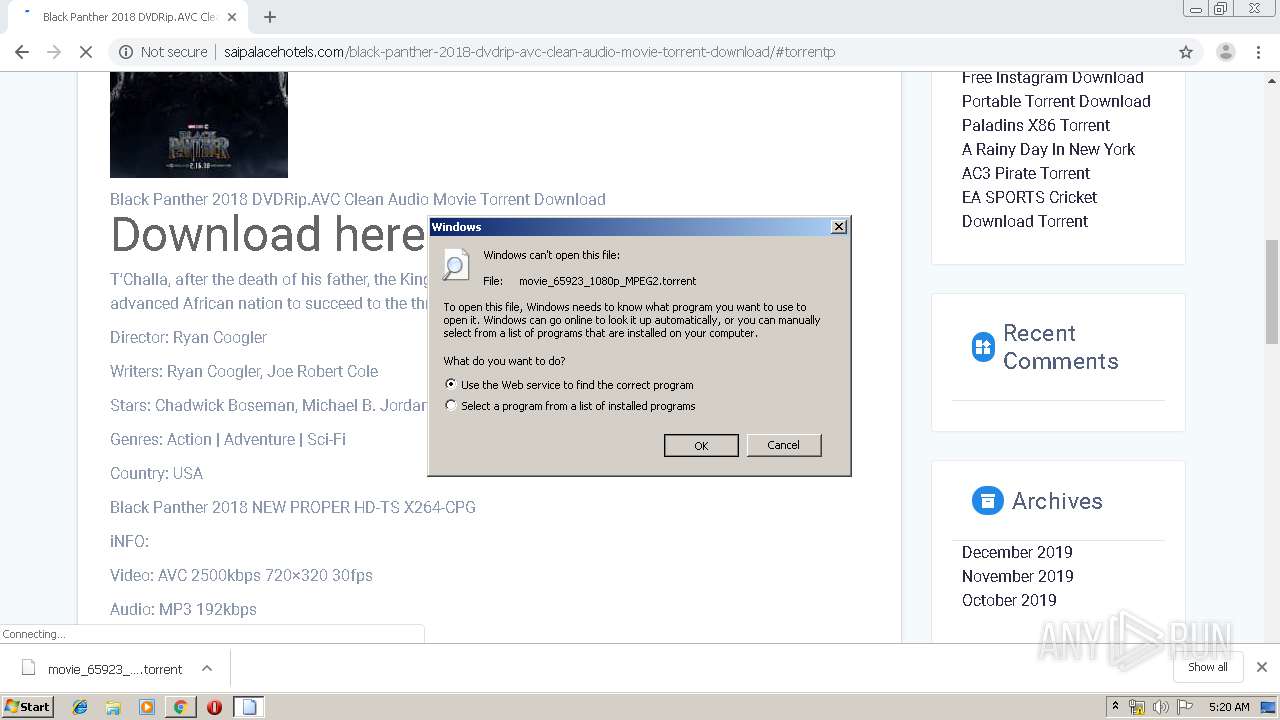
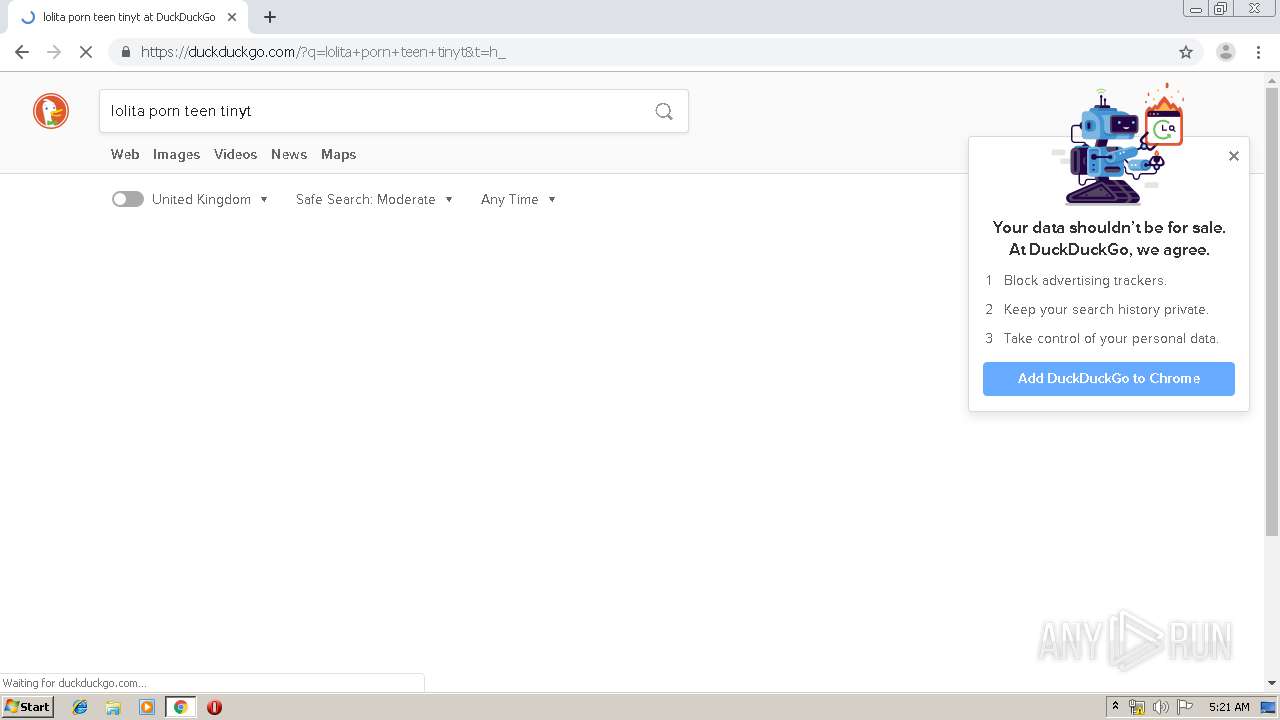
| File name: | movie_65923_1080p_MPEG2.torrent |
| Full analysis: | https://app.any.run/tasks/26241658-27e9-4f28-9035-13da5a5a4241 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2020, 05:18:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-bittorrent |
| File info: | BitTorrent file |
| MD5: | BEF2718D97268ECC19C7504DE860A9B5 |
| SHA1: | CB41FA50B86D729ED077CD626D8374AE65B761E2 |
| SHA256: | 65696D9A19DF63162131B06D4A7EA77FB4CC362CB9264698D0242F8EC680B8CD |
| SSDEEP: | 192:KtGfhB+VxNhDOFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFG:KtGfeVZN |
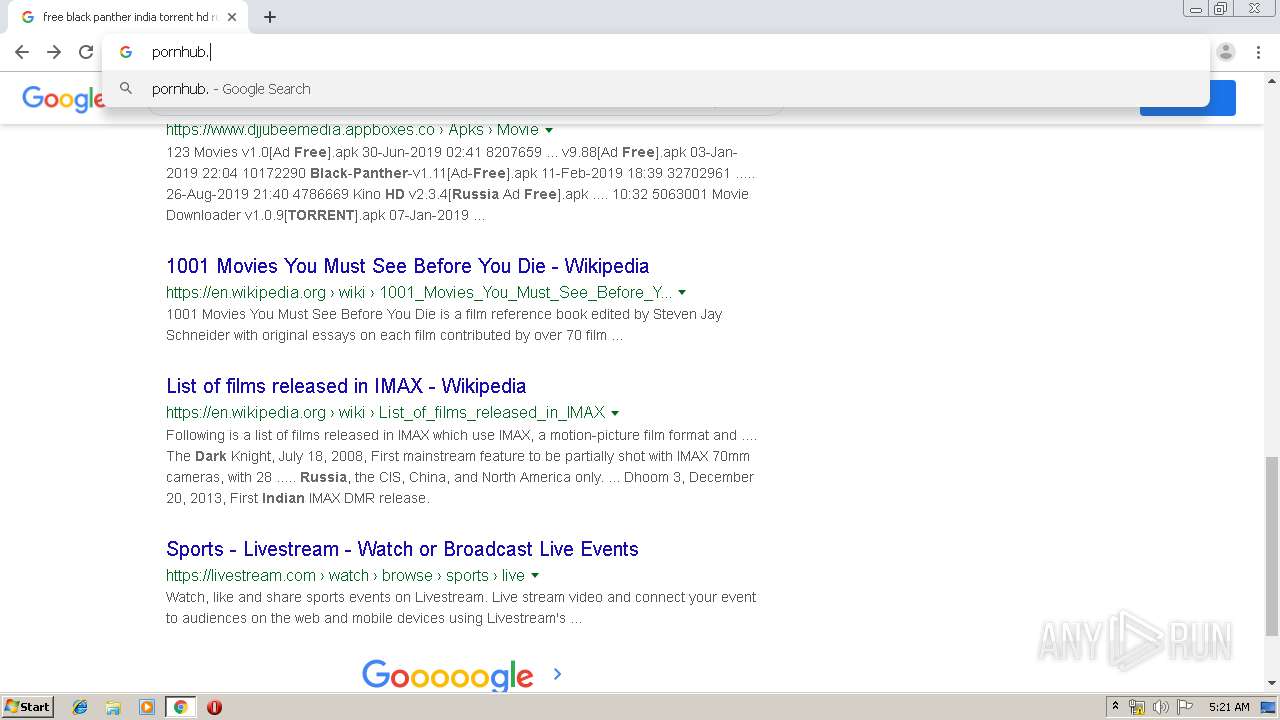
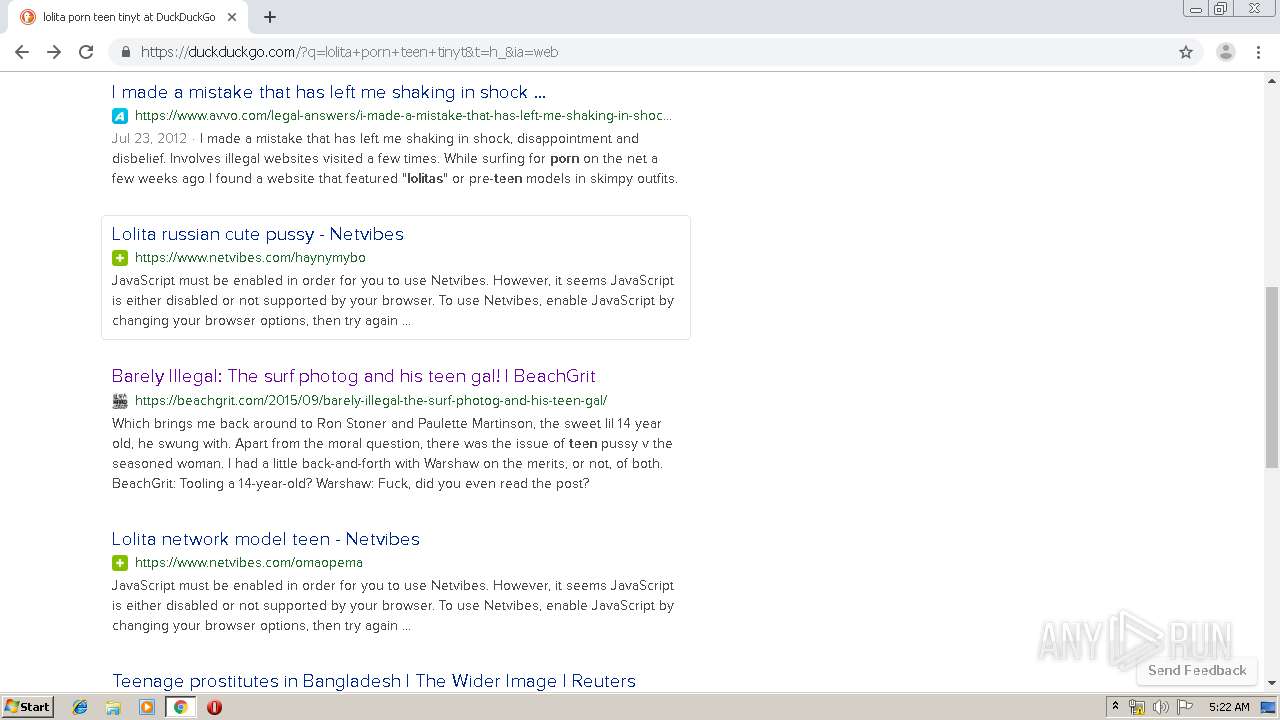
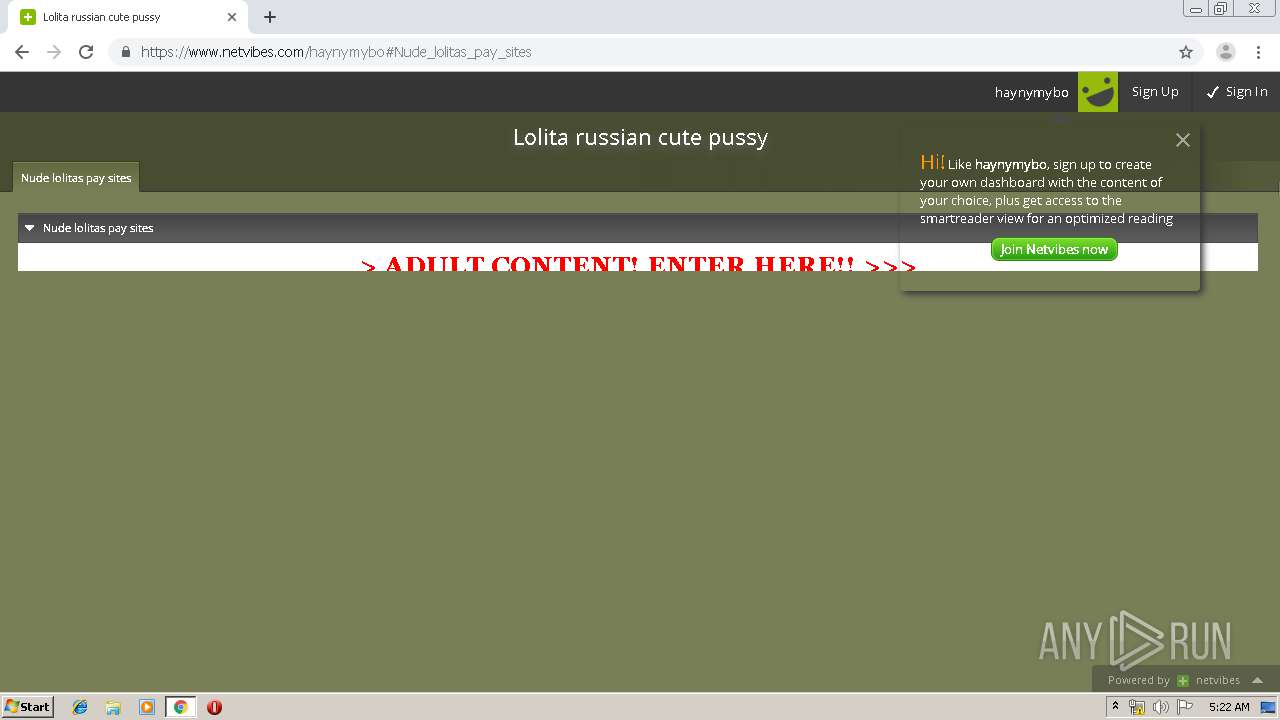
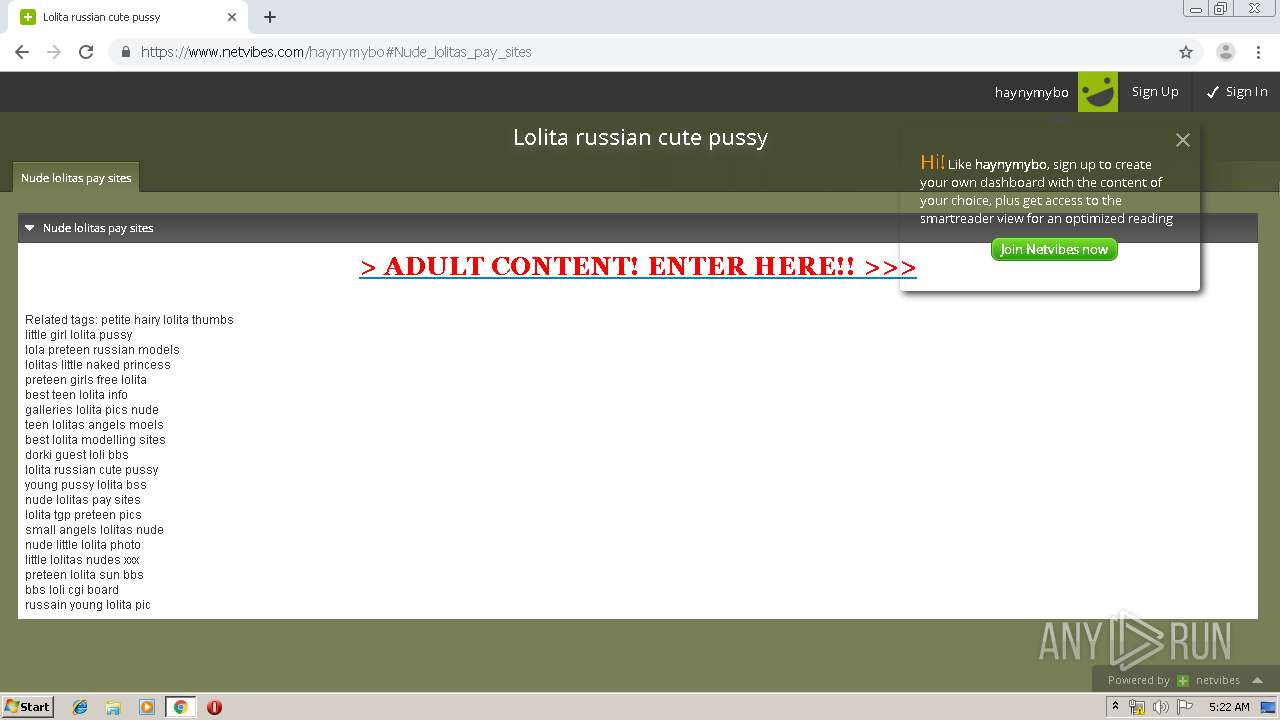
MALICIOUS
No malicious indicators.SUSPICIOUS
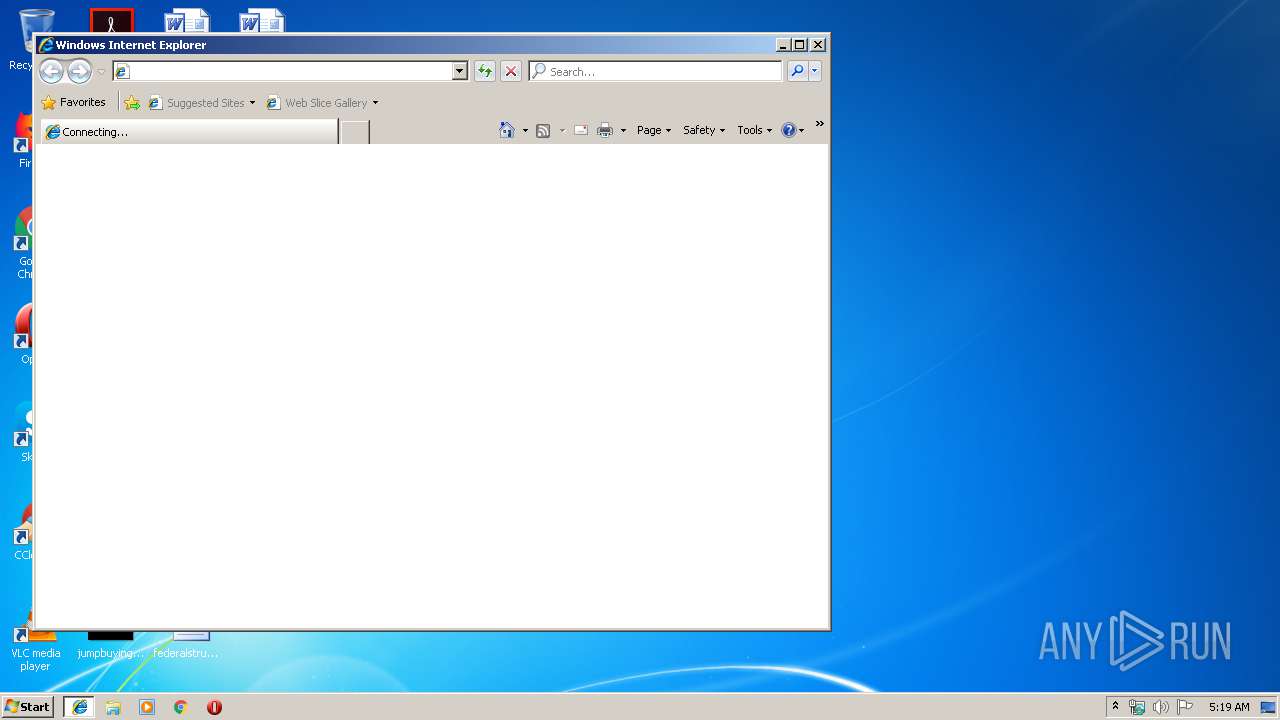
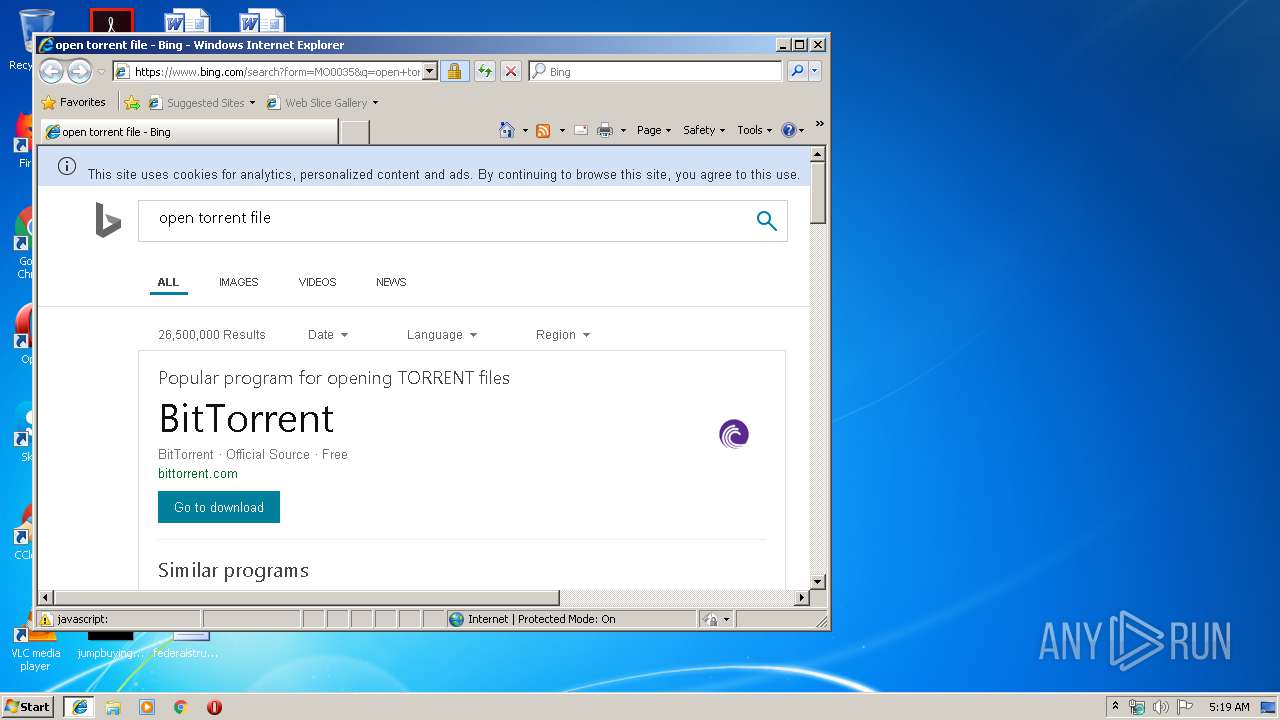
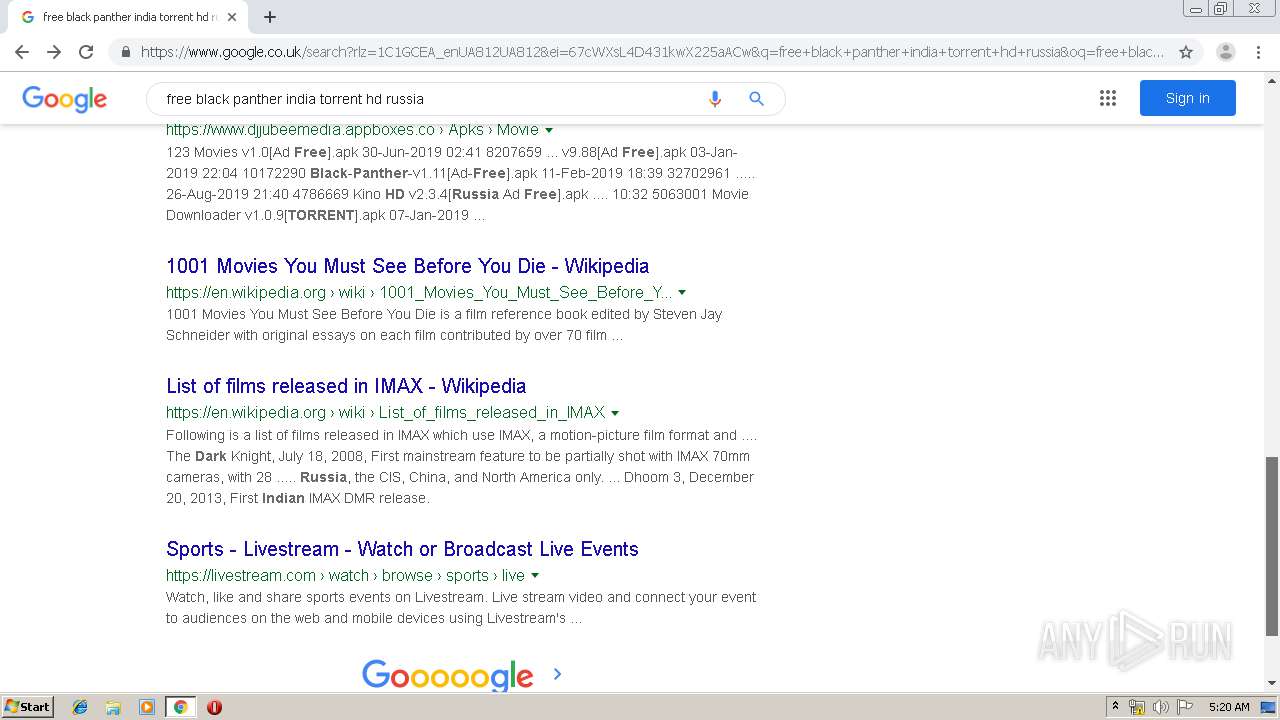
Starts Internet Explorer
- rundll32.exe (PID: 2864)
- rundll32.exe (PID: 1888)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1596)
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 2500)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2500)
INFO
Changes internet zones settings
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 736)
Application launched itself
- iexplore.exe (PID: 4040)
- chrome.exe (PID: 2500)
- iexplore.exe (PID: 736)
Reads internet explorer settings
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 564)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 736)
Reads Internet Cache Settings
- iexplore.exe (PID: 2108)
- chrome.exe (PID: 2500)
- iexplore.exe (PID: 564)
Creates files in the user directory
- iexplore.exe (PID: 2108)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1596)
- iexplore.exe (PID: 564)
- chrome.exe (PID: 2500)
Manual execution by user
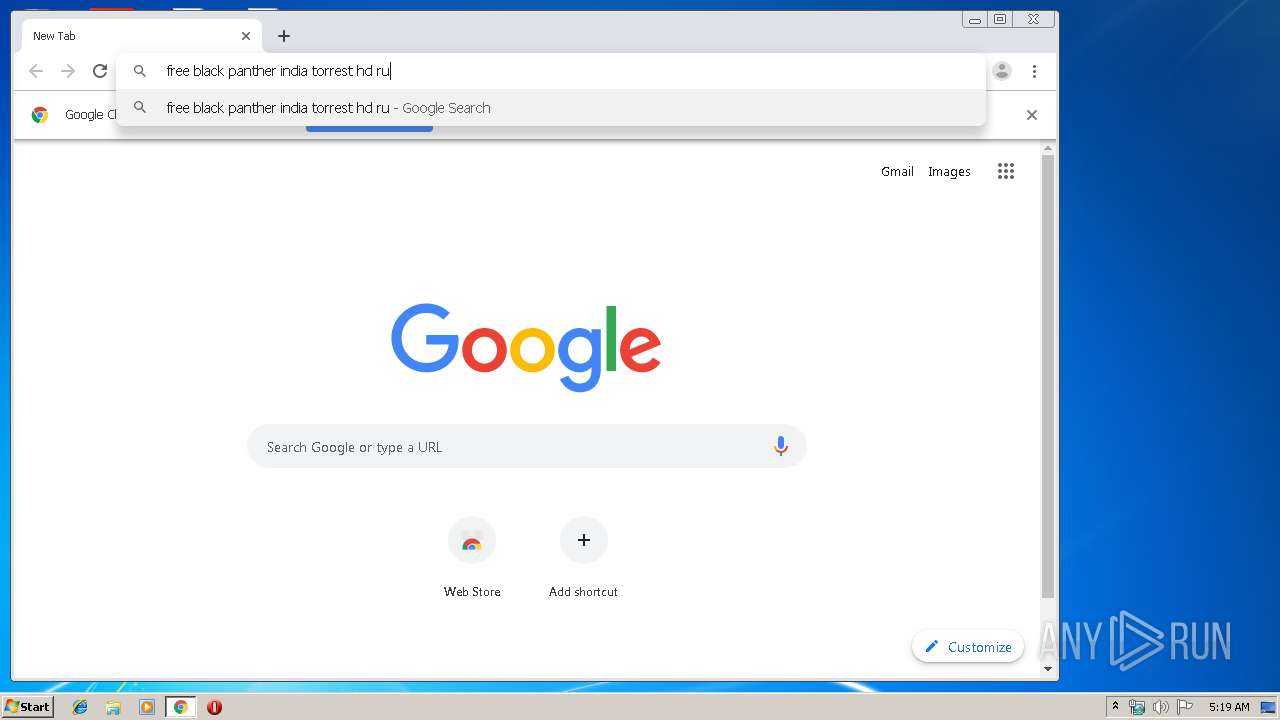
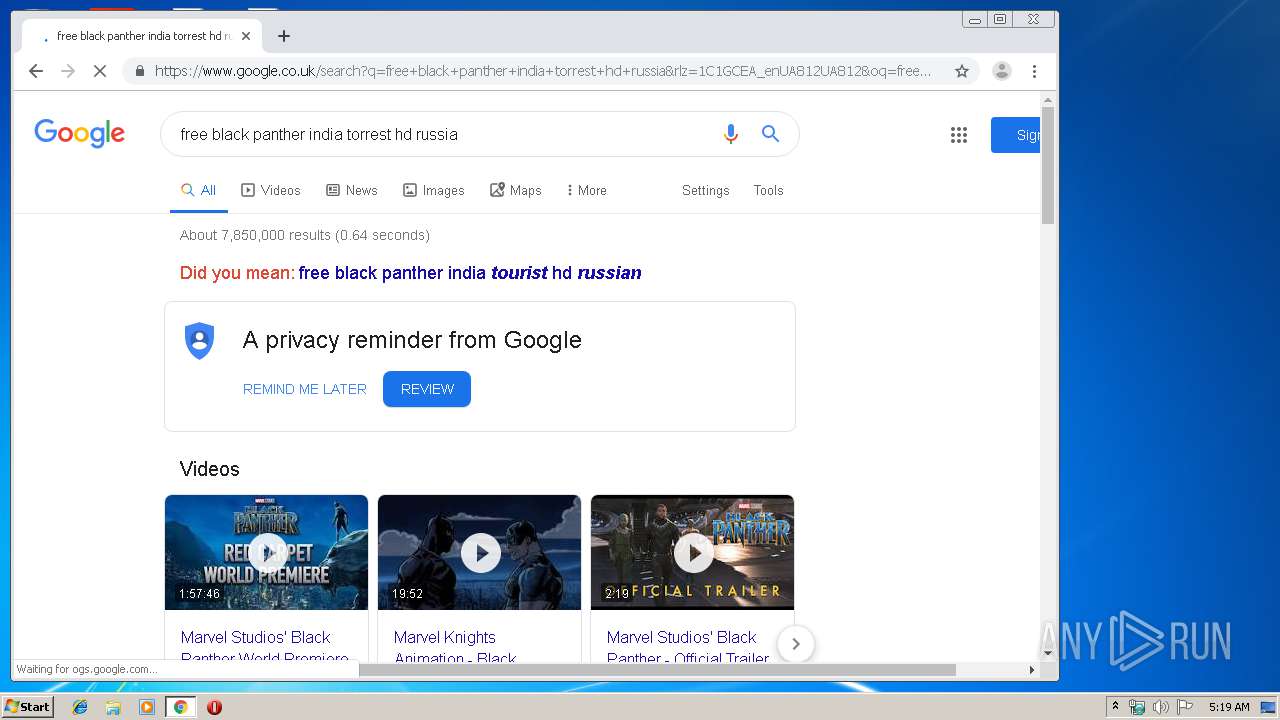
- chrome.exe (PID: 2500)
Changes settings of System certificates
- iexplore.exe (PID: 4040)
- chrome.exe (PID: 932)
- iexplore.exe (PID: 736)
Reads settings of System Certificates
- iexplore.exe (PID: 4040)
- chrome.exe (PID: 932)
Reads the hosts file
- chrome.exe (PID: 2500)
- chrome.exe (PID: 932)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 564)
- chrome.exe (PID: 2500)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .torrent | | | Torrent (trackerless) (57.6) |
|---|---|---|
| .torrent | | | Torrent (42.3) |
EXIF
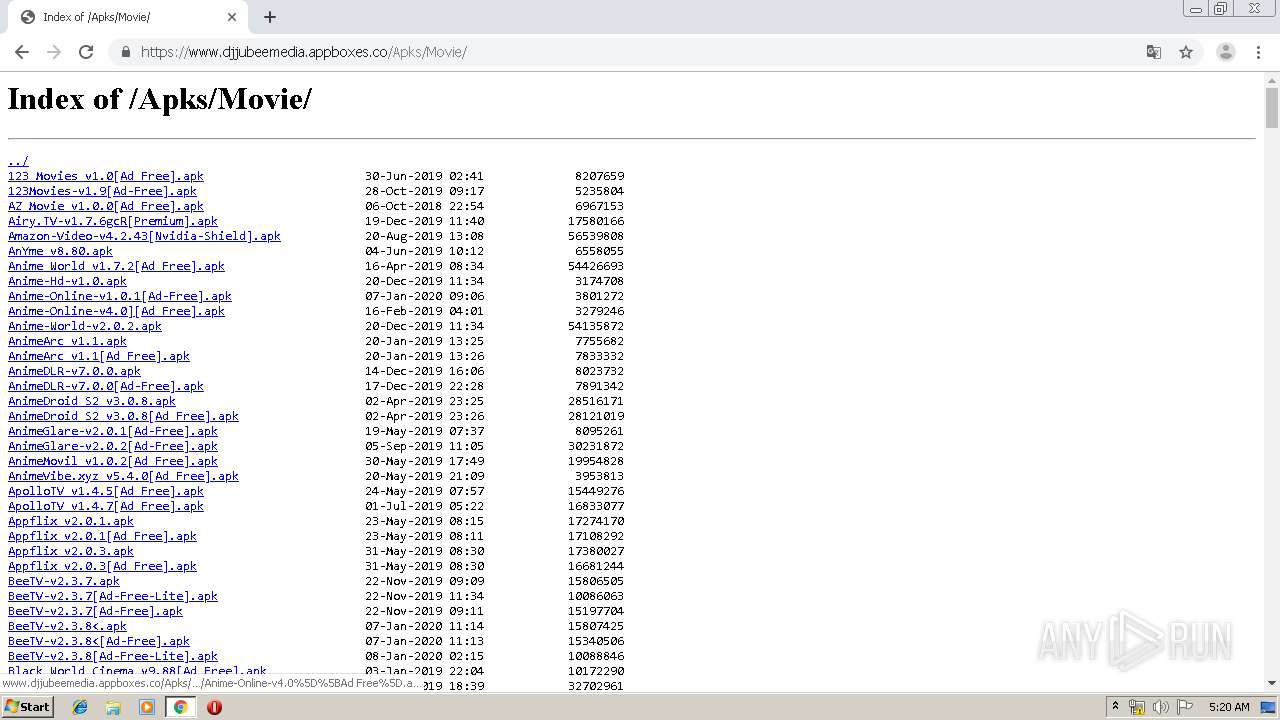
Torrent
| Announce: | udp://62.138.0.158:6969/announce |
|---|---|
| AnnounceList1: | udp://62.138.0.158:6969/announce |
| AnnounceList2: | udp://151.80.120.114:2710/announce |
| AnnounceList3: | udp://open.stealth.si:80/announce |
| AnnounceList4: | http://explodie.org:6969/announce |
| Creator: | mktorrent 1.1 |
| CreateDate: | 2020:01:09 06:15:34+01:00 |
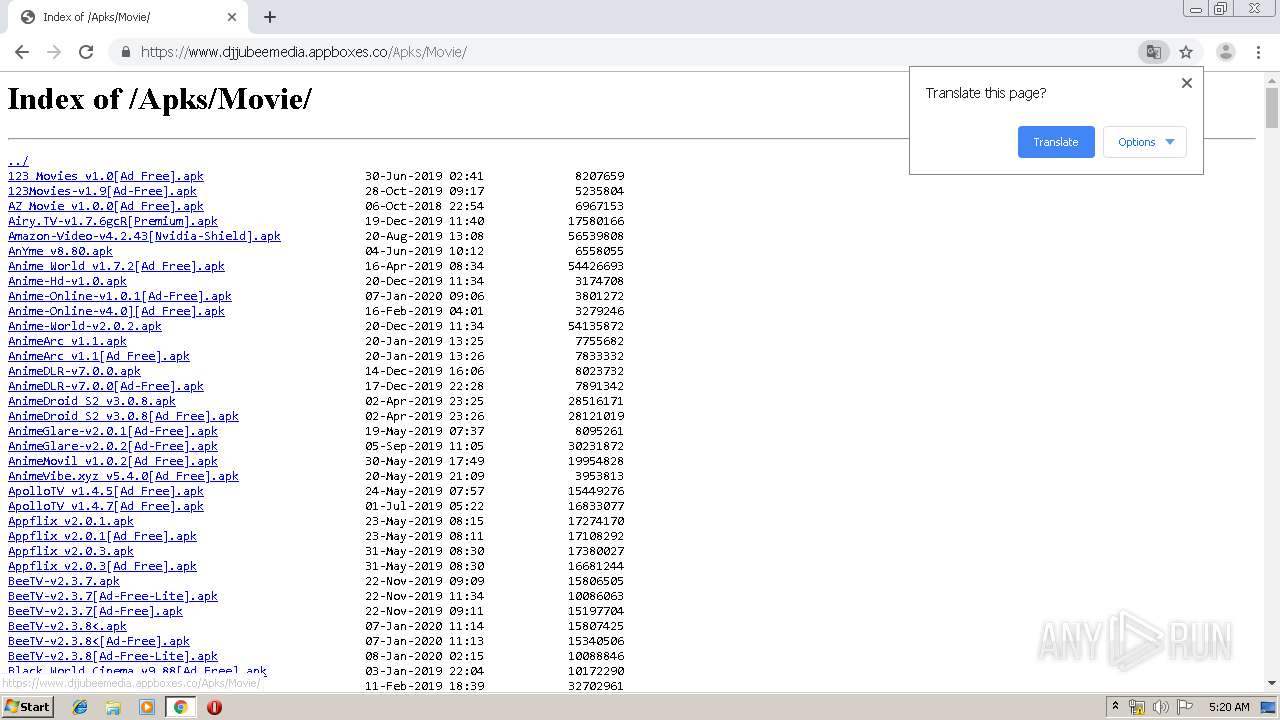
| File1Length: | 6.7 MB |
| File1Path: | 75095_VTS.vob |
| File2Length: | 326 kB |
| File2Path: | K-Lite Mega Codec Pack.exe |
| File3Length: | 852 MB |
| File3Path: | movie_75095_1080p_MPEG2.mpg |
| Name: | movie_75095_1080p_MPEG2 |
| PieceLength: | 262144 |
| Pieces: | (Binary data 68740 bytes, use -b option to extract) |
Total processes
132
Monitored processes
95
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17867533575917275168 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8148749739875183062 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16030082883374113077 --renderer-client-id=65 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3686718370166067099 --mojo-platform-channel-handle=3368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:736 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7988480183751851956 --renderer-client-id=76 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4719708855084622295 --mojo-platform-channel-handle=3716 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6122165411885867533 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,11517536753972723069,18101298981402300507,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12882626912948084743 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 056
Read events
1 742
Write events
298
Delete events
16
Modification events
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8F727BDB-329F-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (4040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E407010004000900050013000800B503 | |||
Executable files
0
Suspicious files
458
Text files
550
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\TC9EB7BJ\search[1].txt | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012020010920200110\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
345
DNS requests
223
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
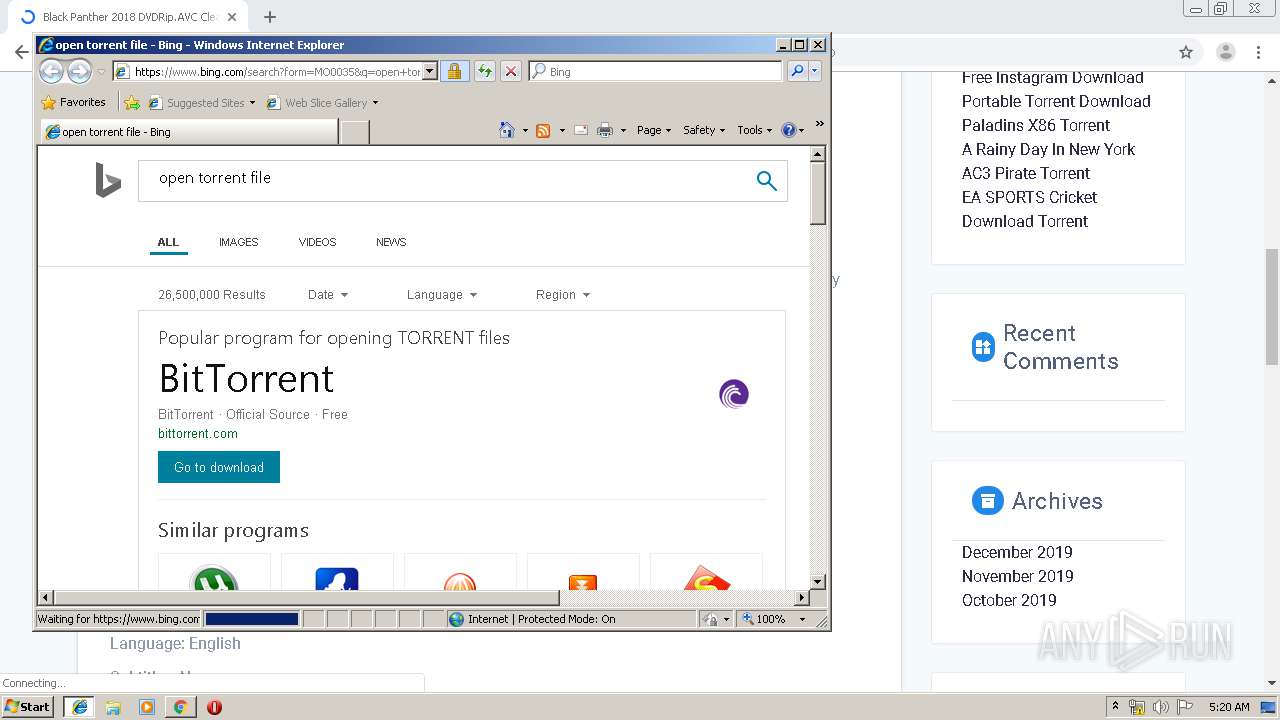
2108 | iexplore.exe | GET | 302 | 104.111.238.86:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=torrent | NL | — | — | whitelisted |
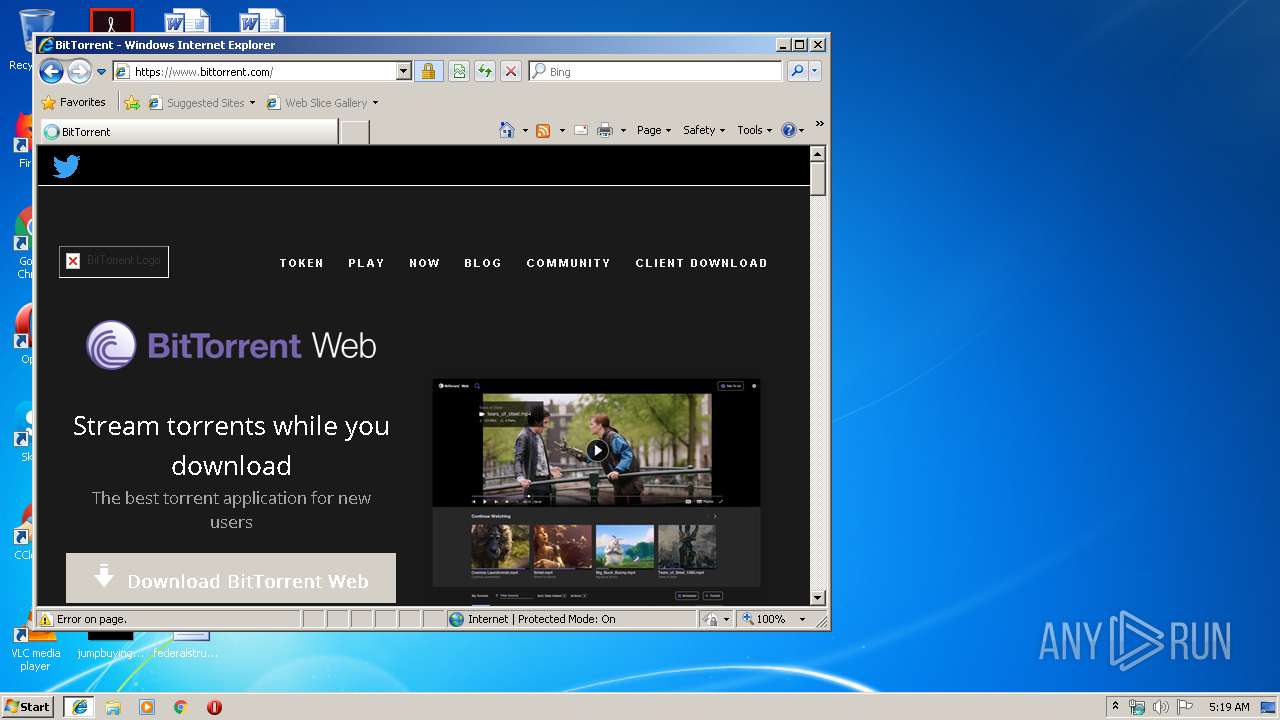
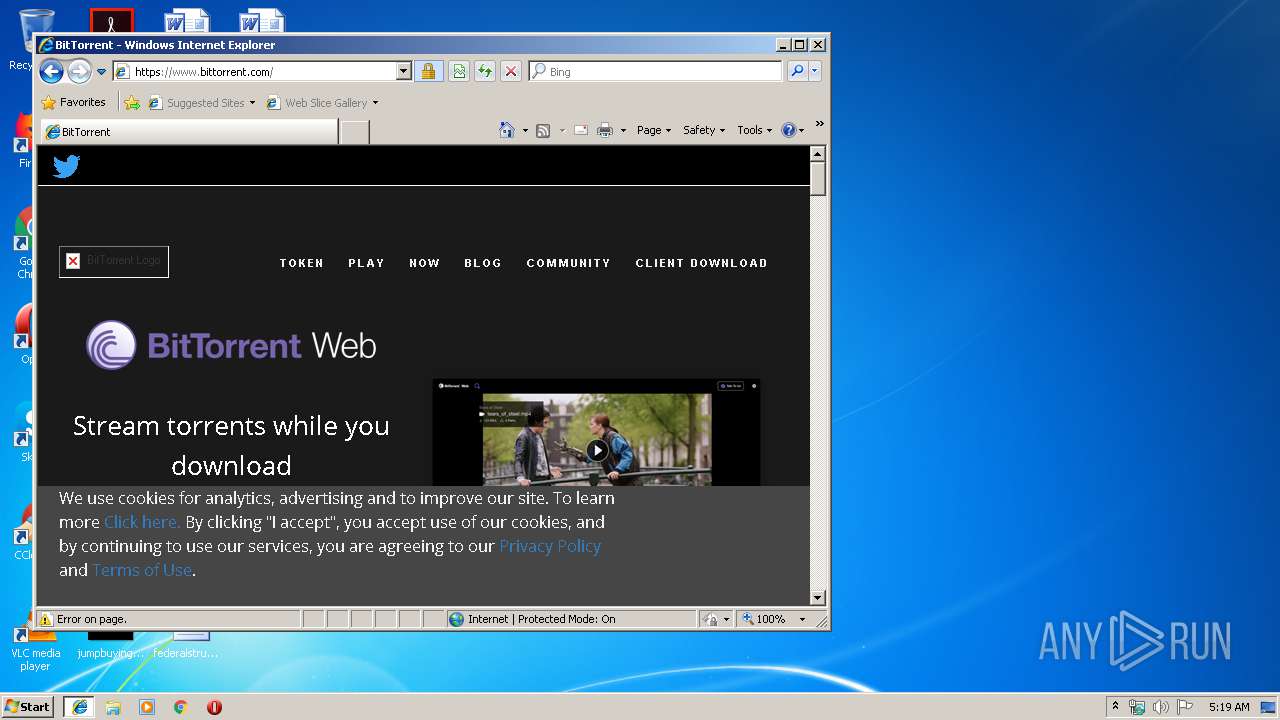
2108 | iexplore.exe | GET | 301 | 178.79.242.147:80 | http://www.bittorrent.com/ | DE | — | — | shared |
2108 | iexplore.exe | GET | 301 | 2.16.186.24:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=torrent | unknown | — | — | whitelisted |
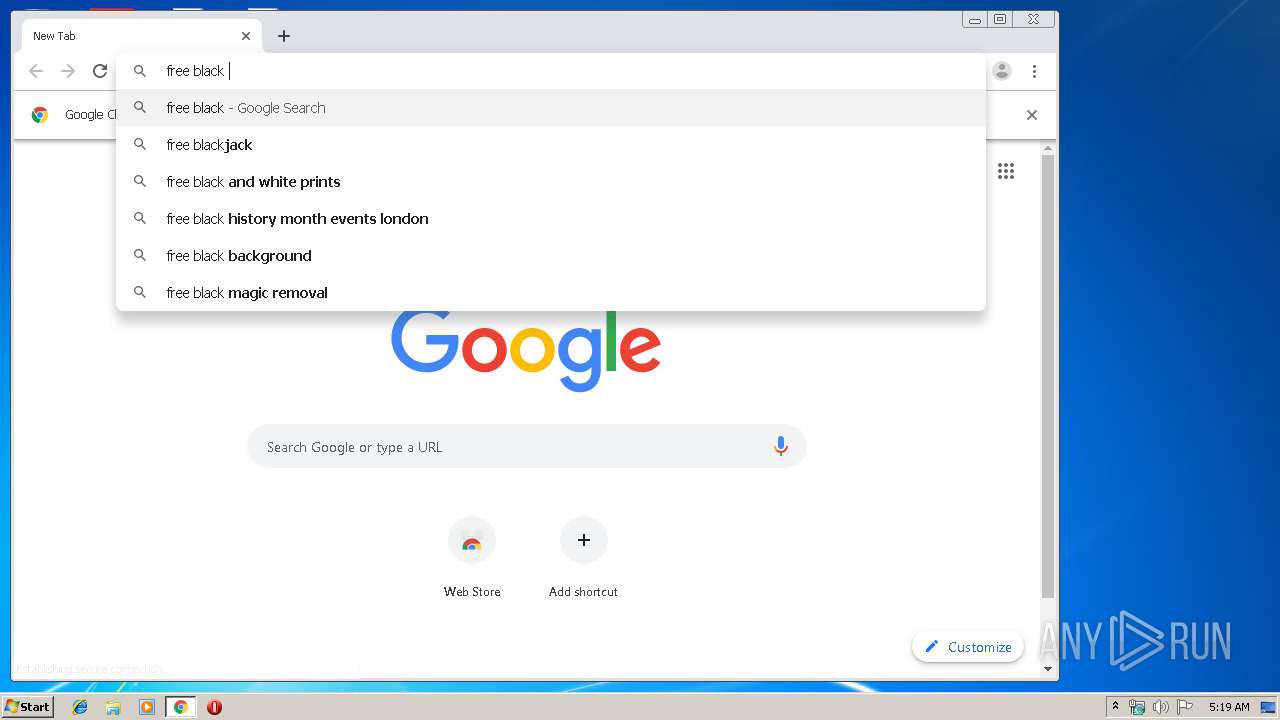
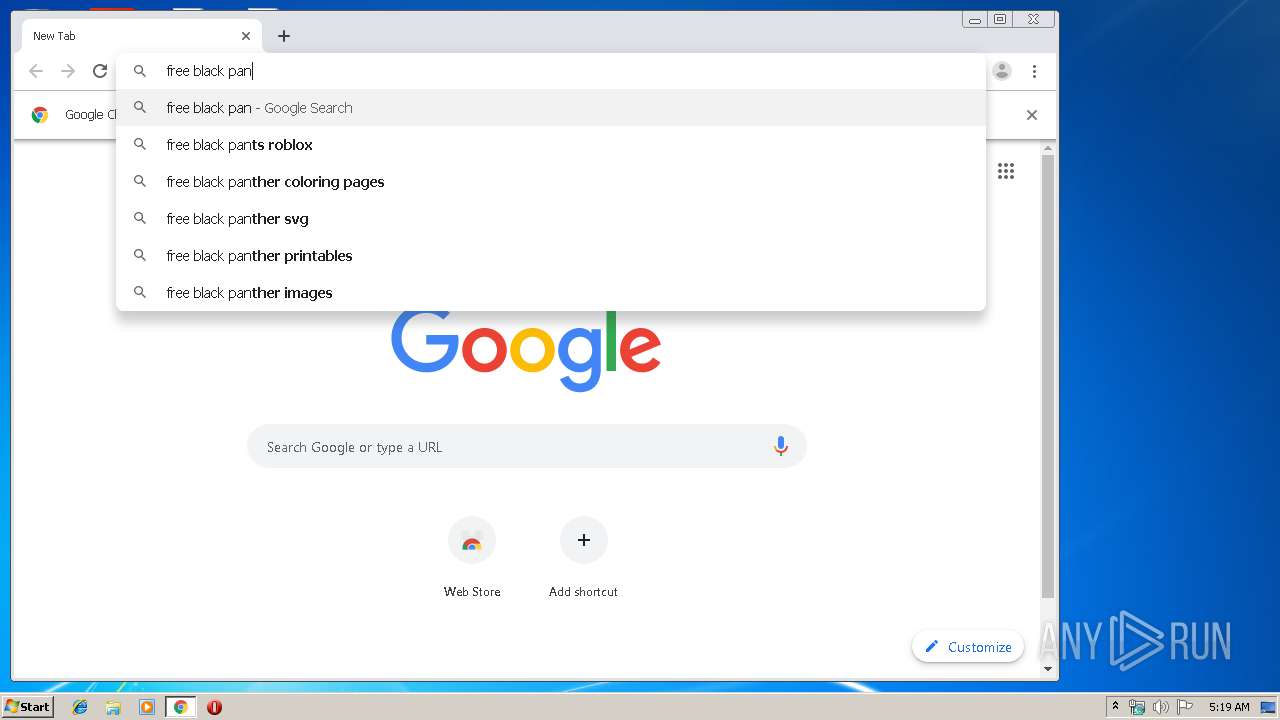
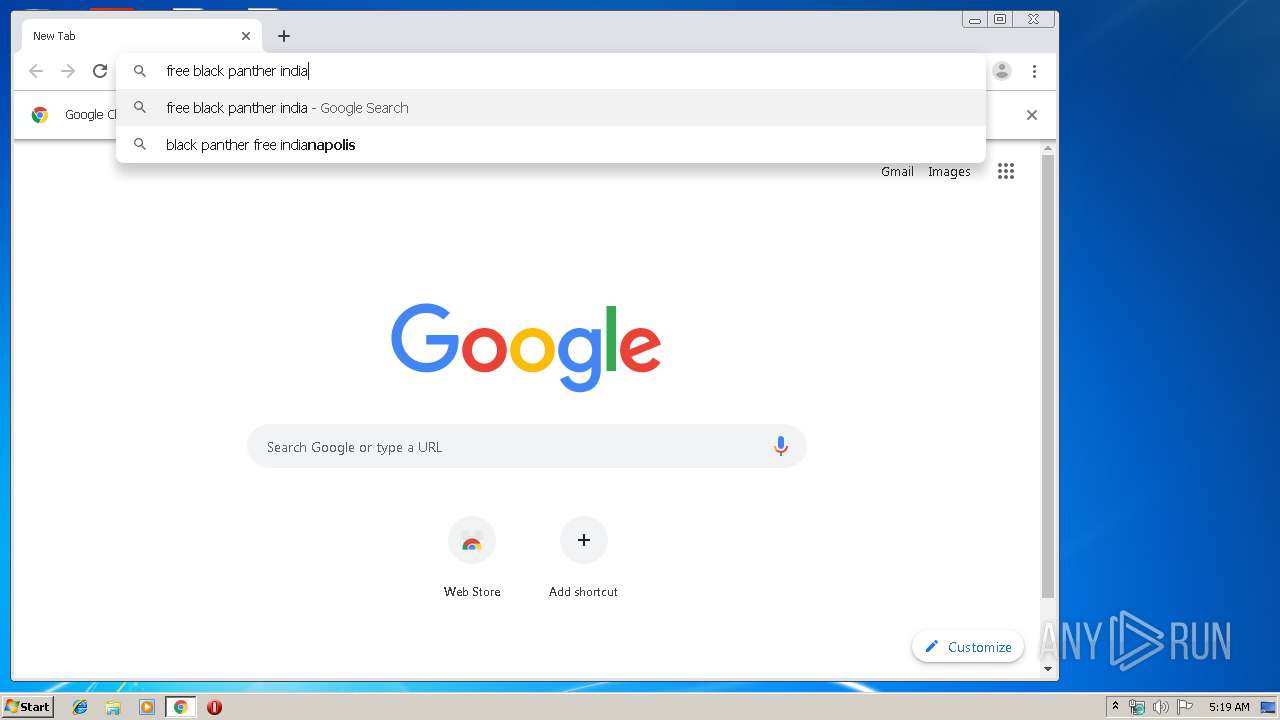
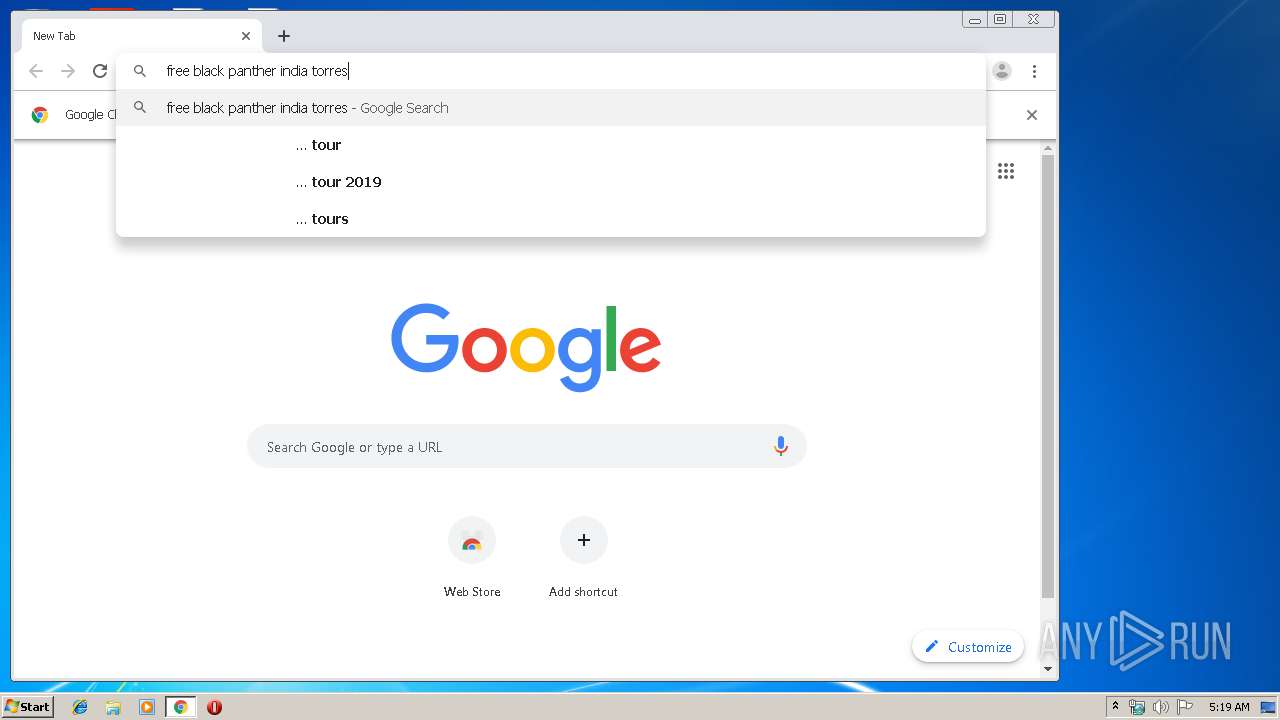
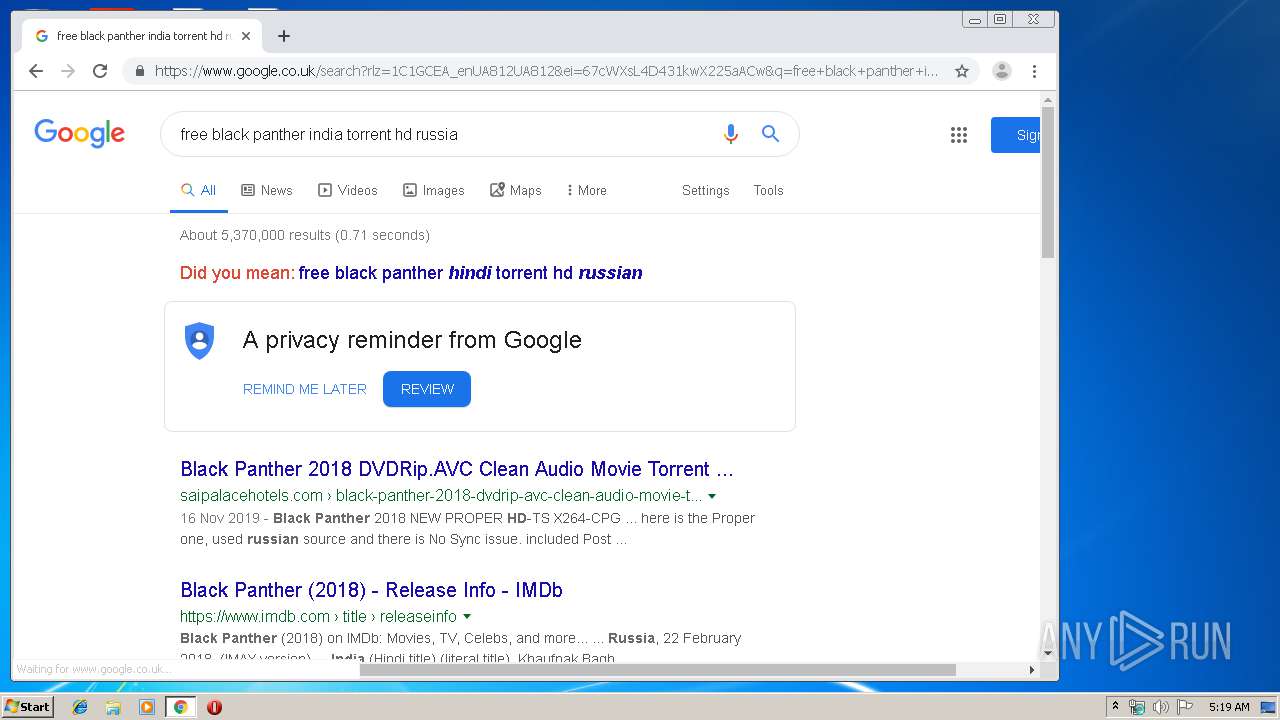
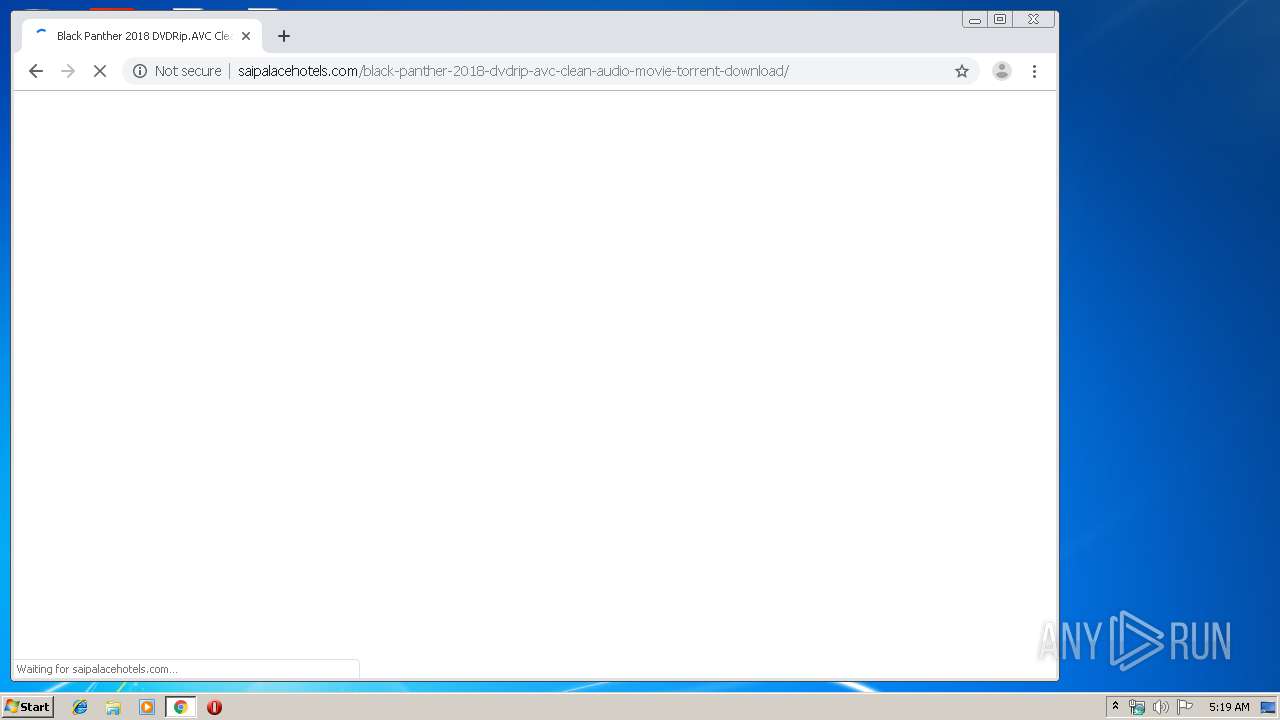
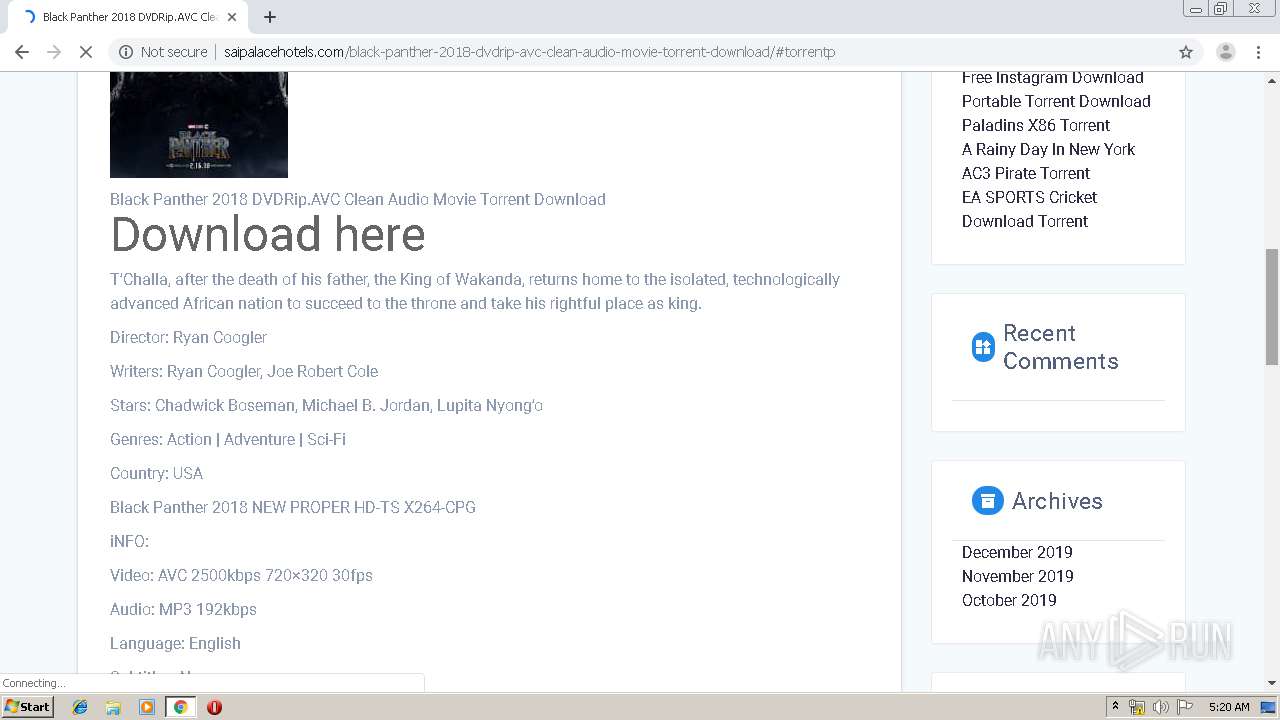
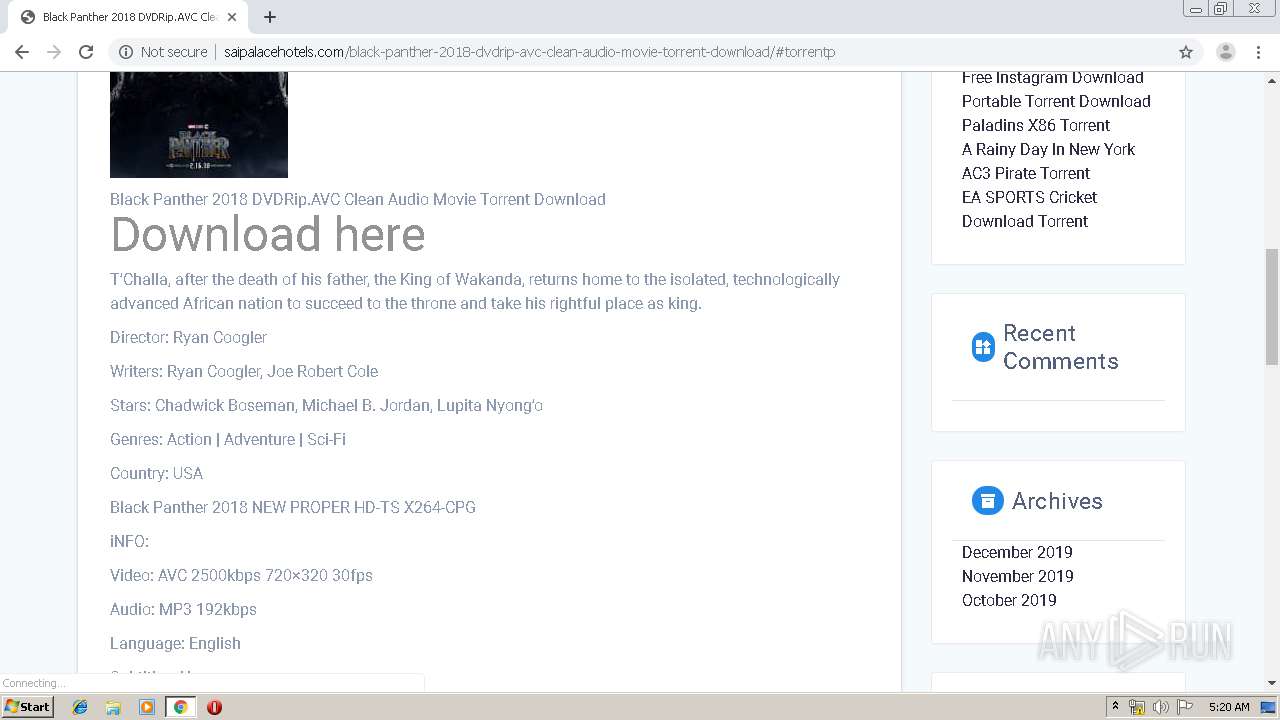
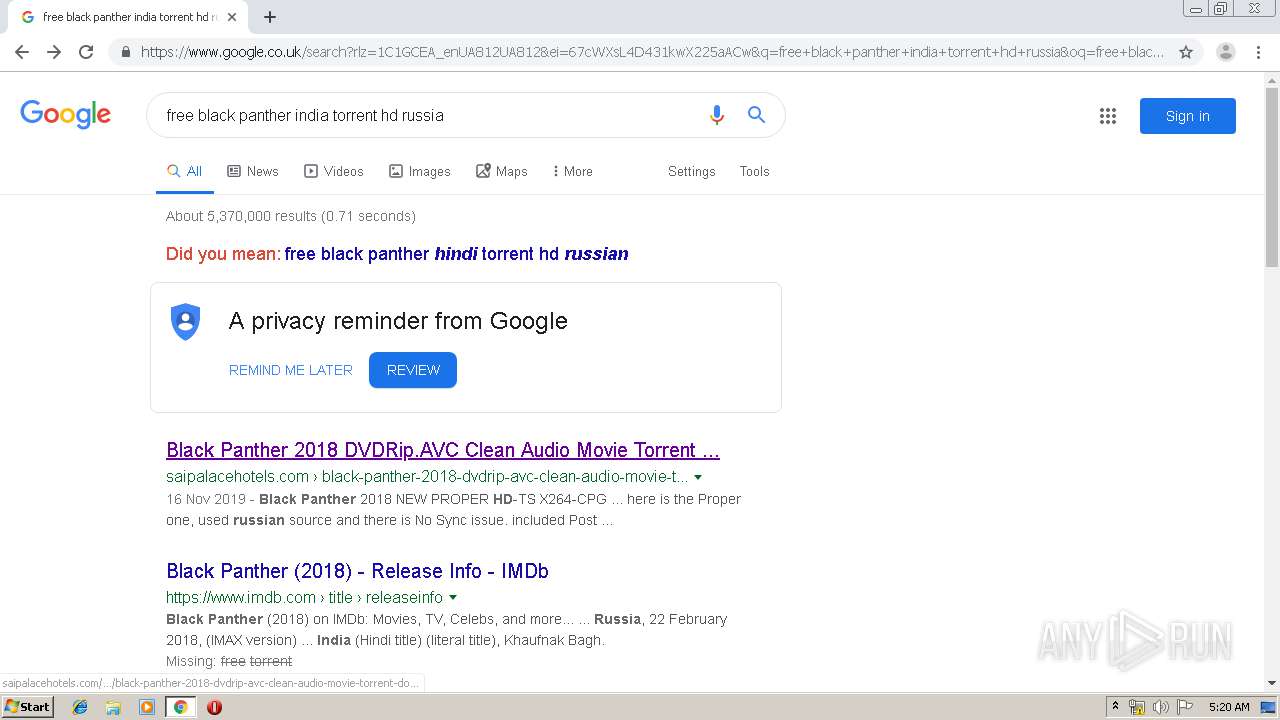
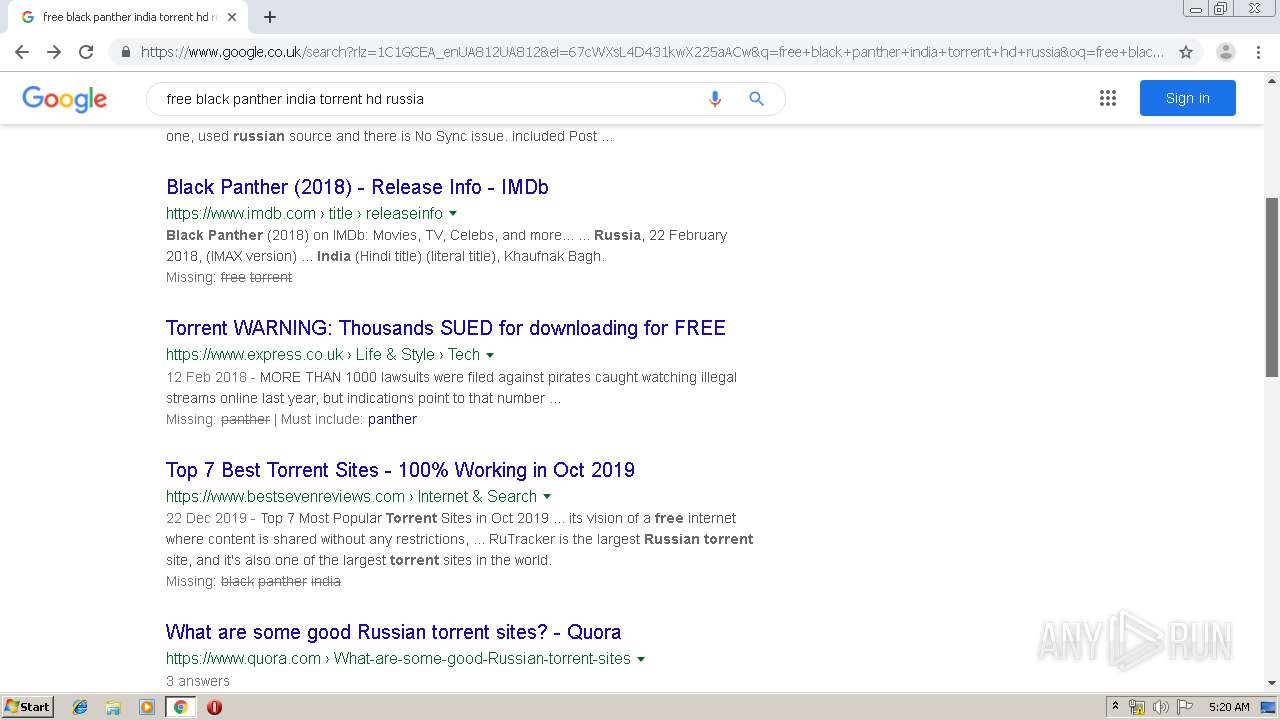
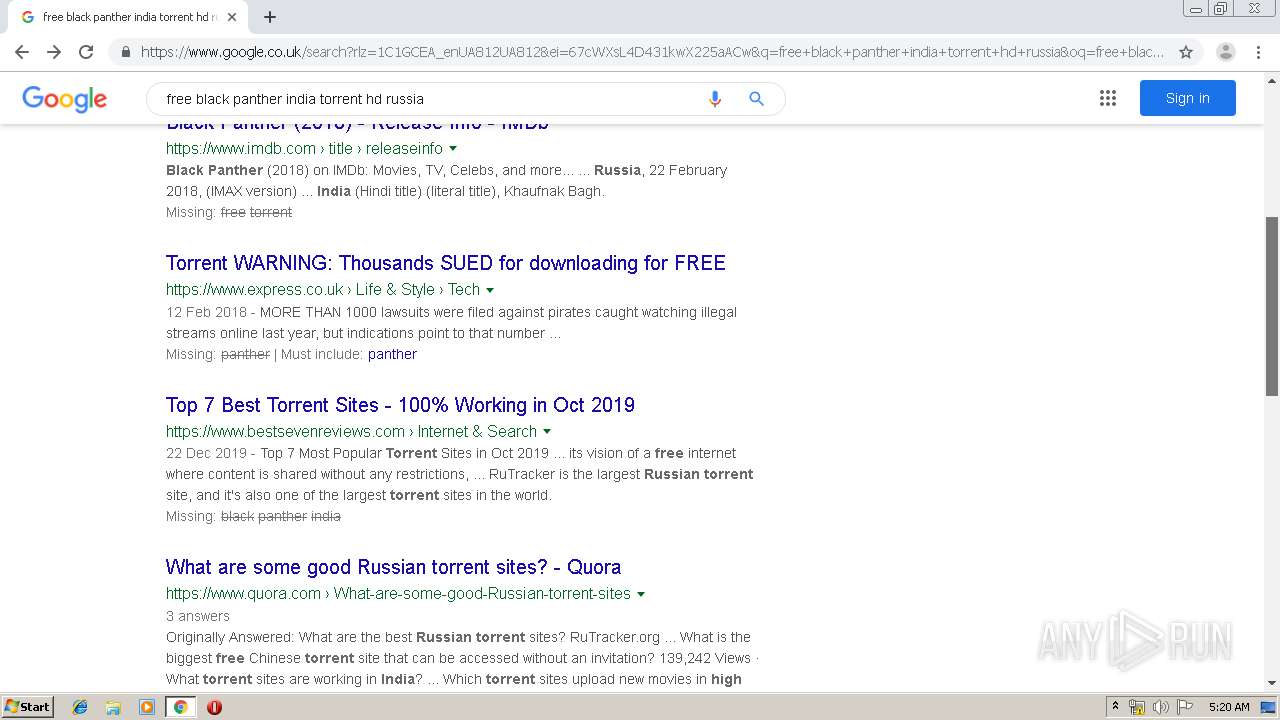
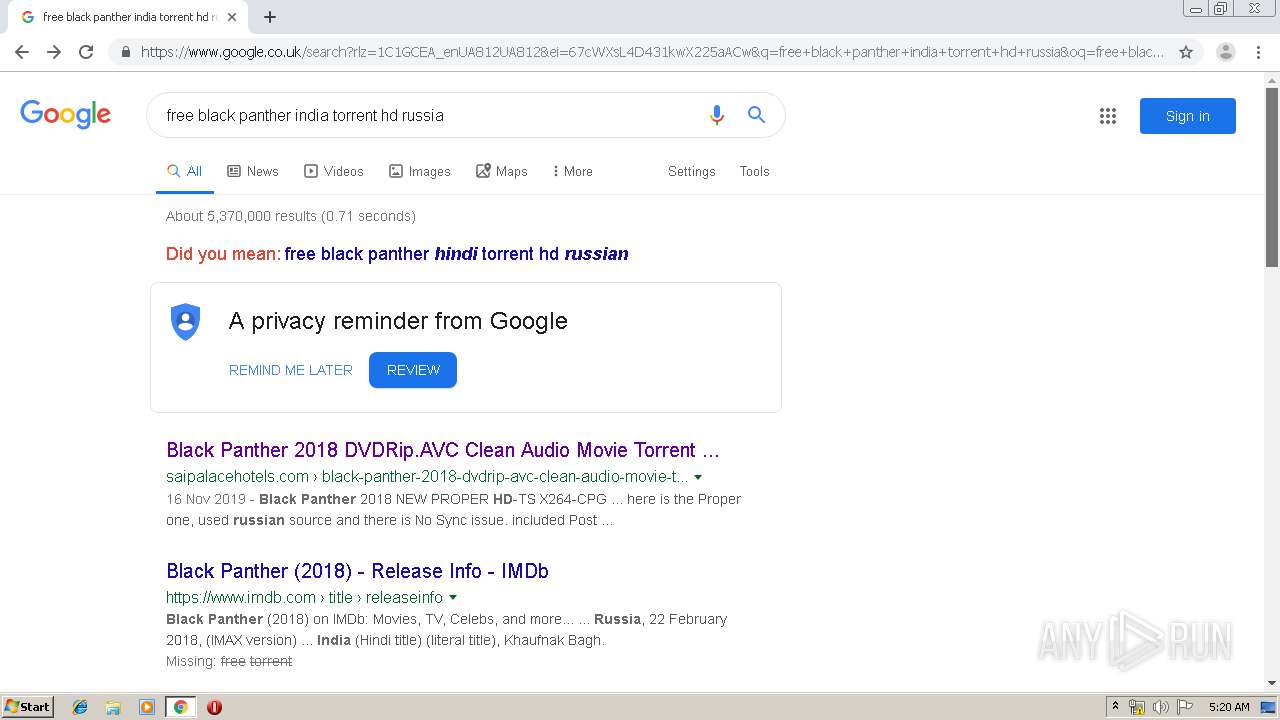
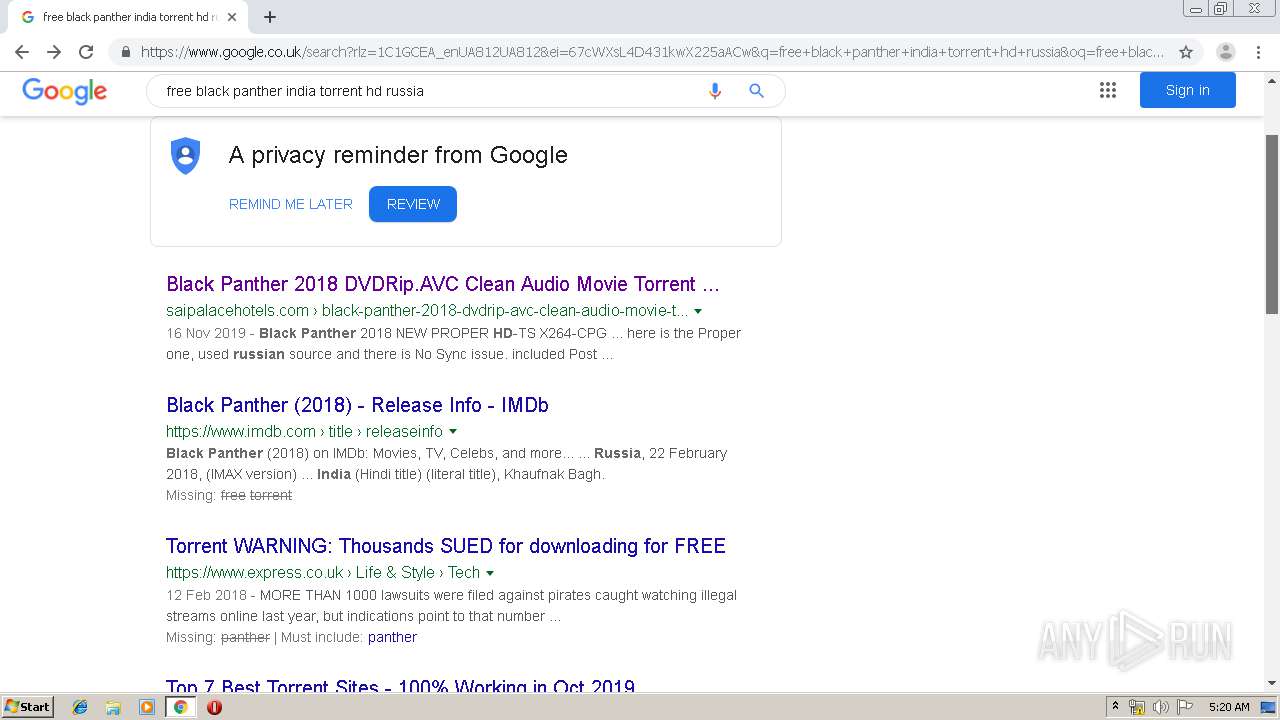
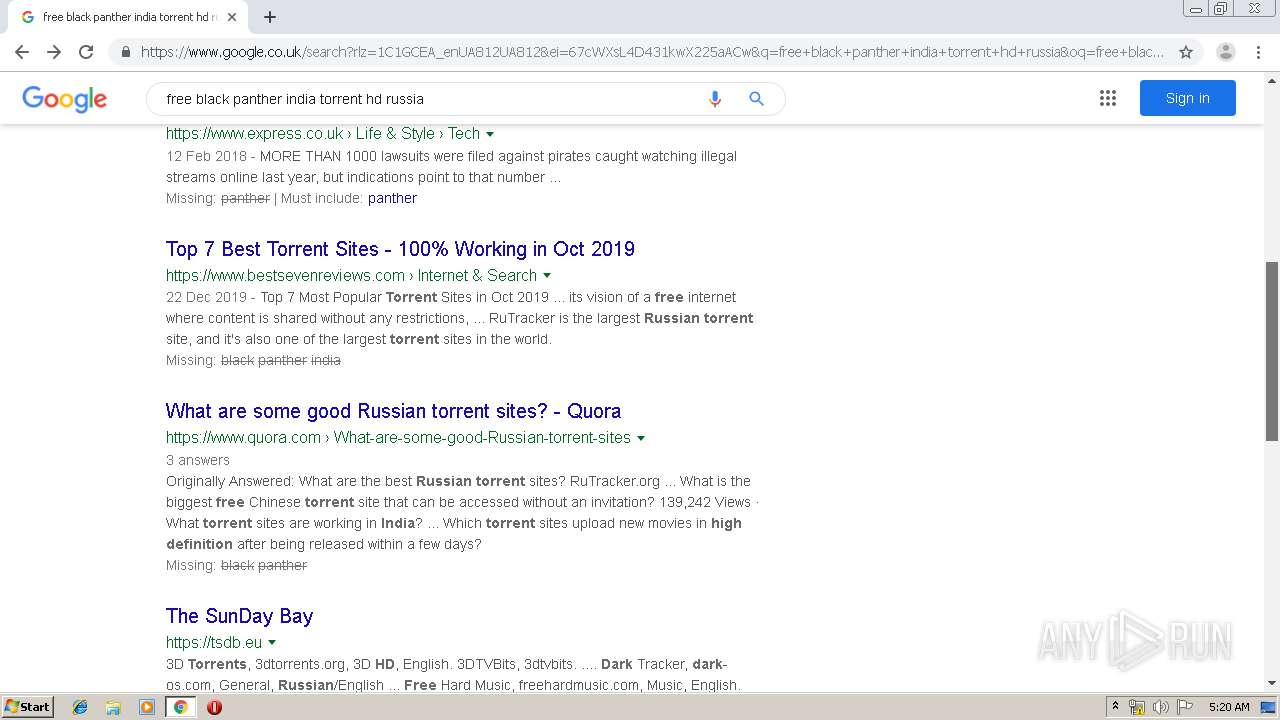
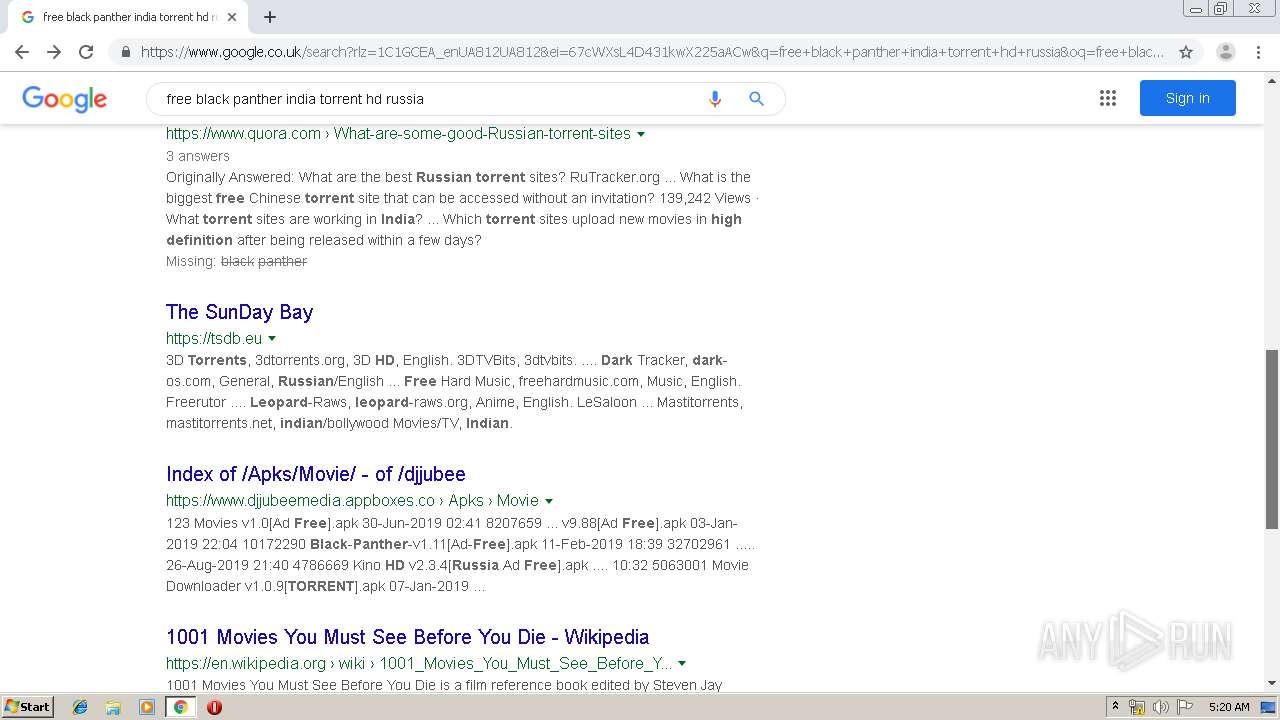
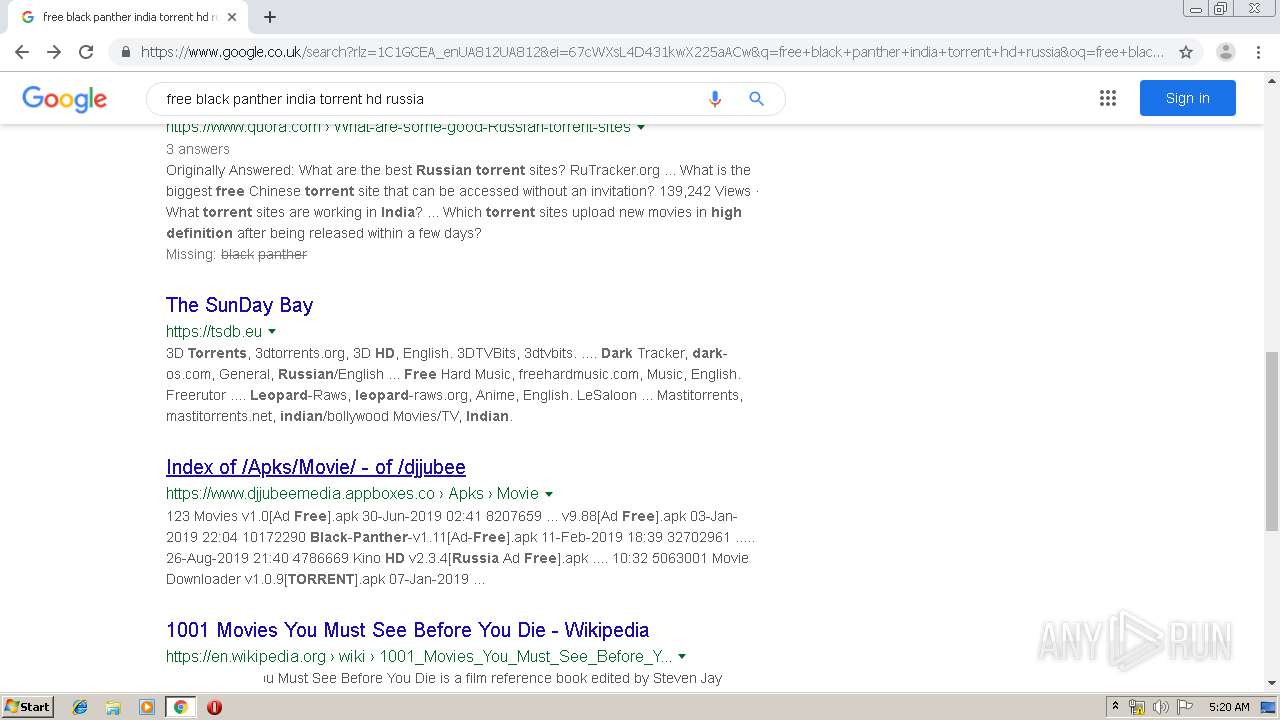
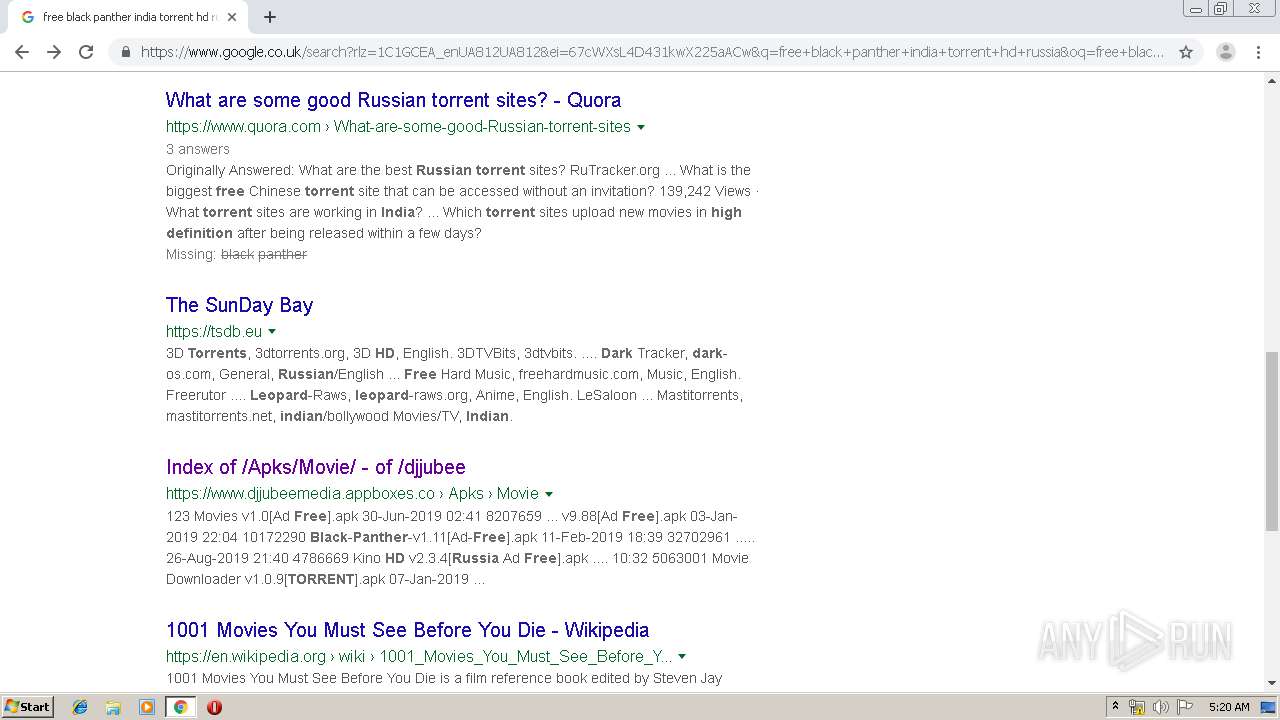
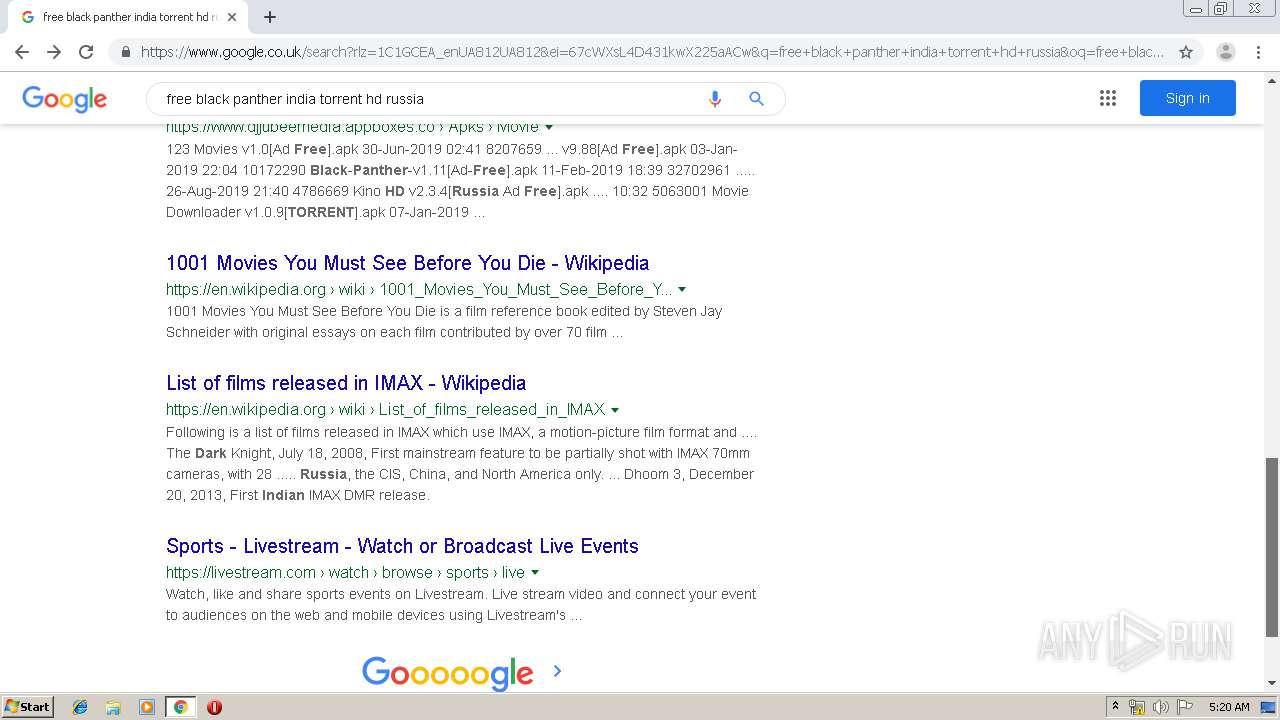
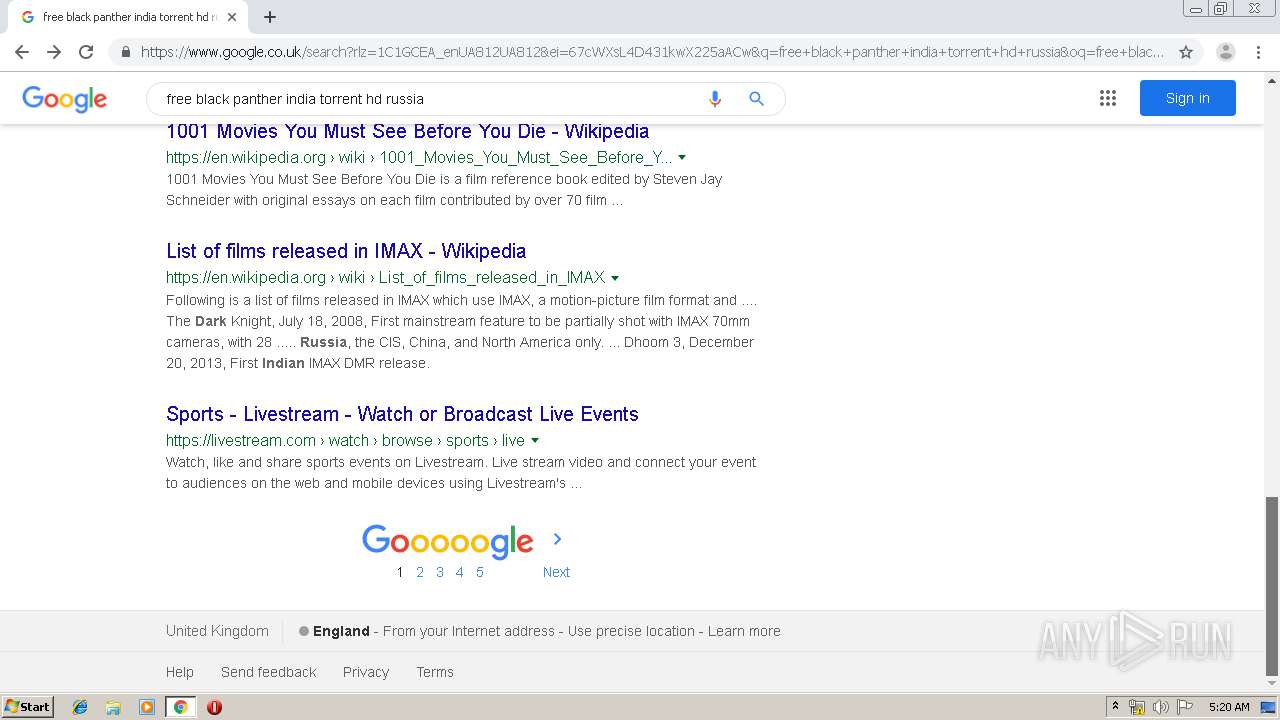
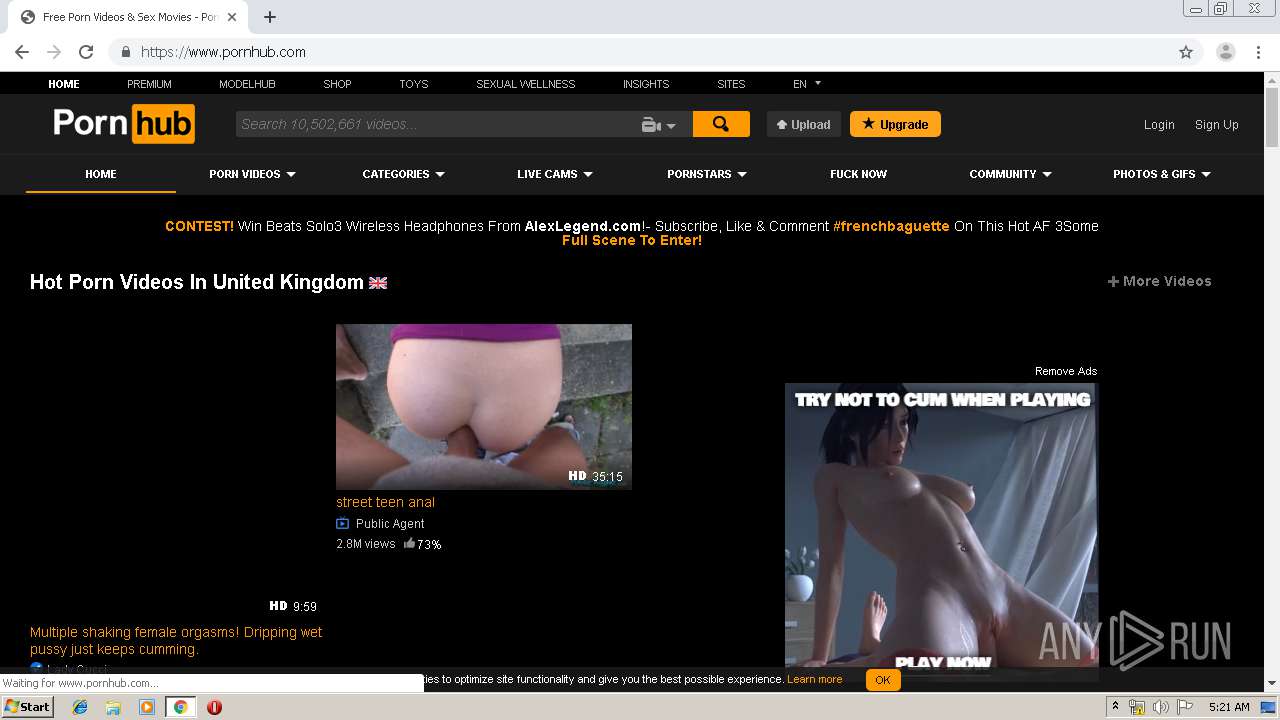
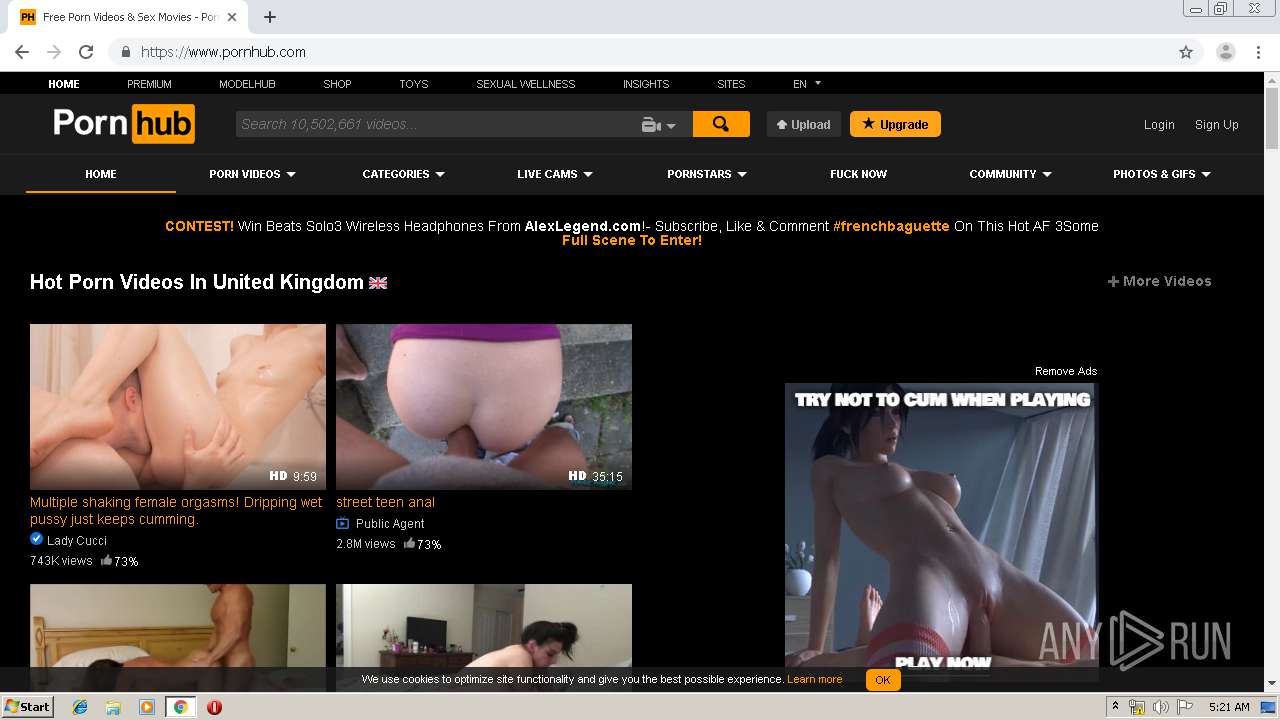
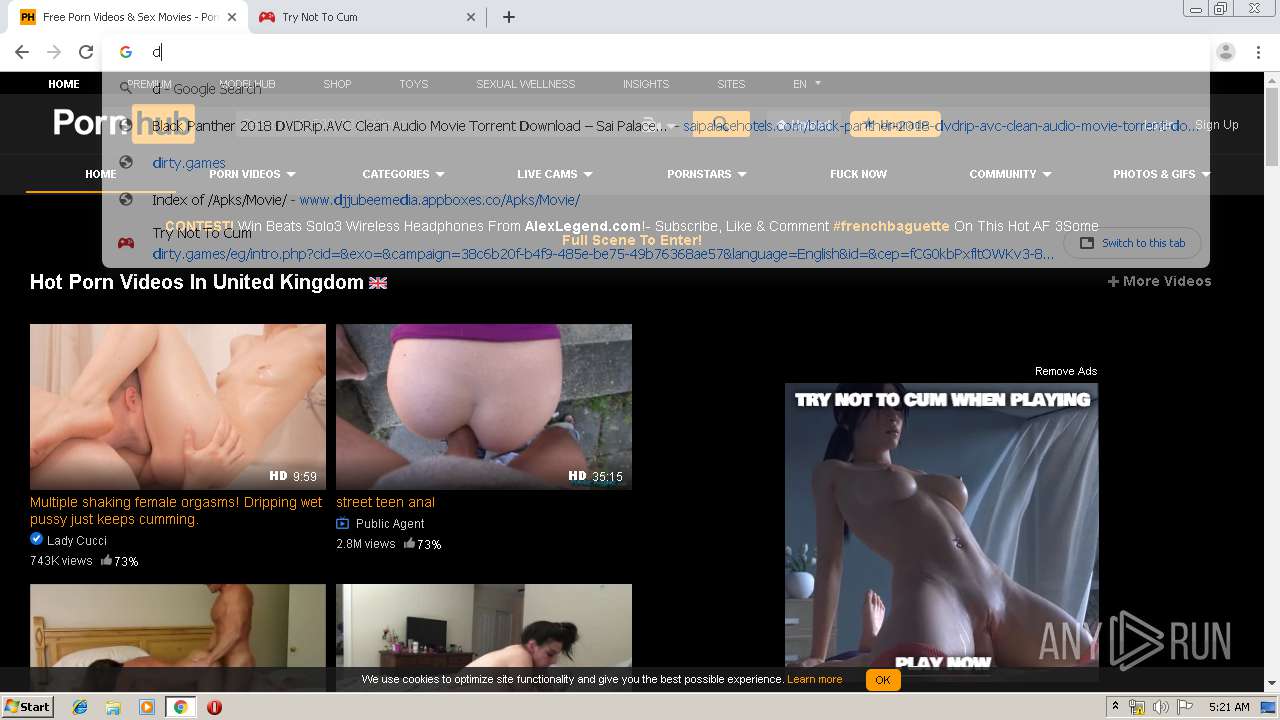
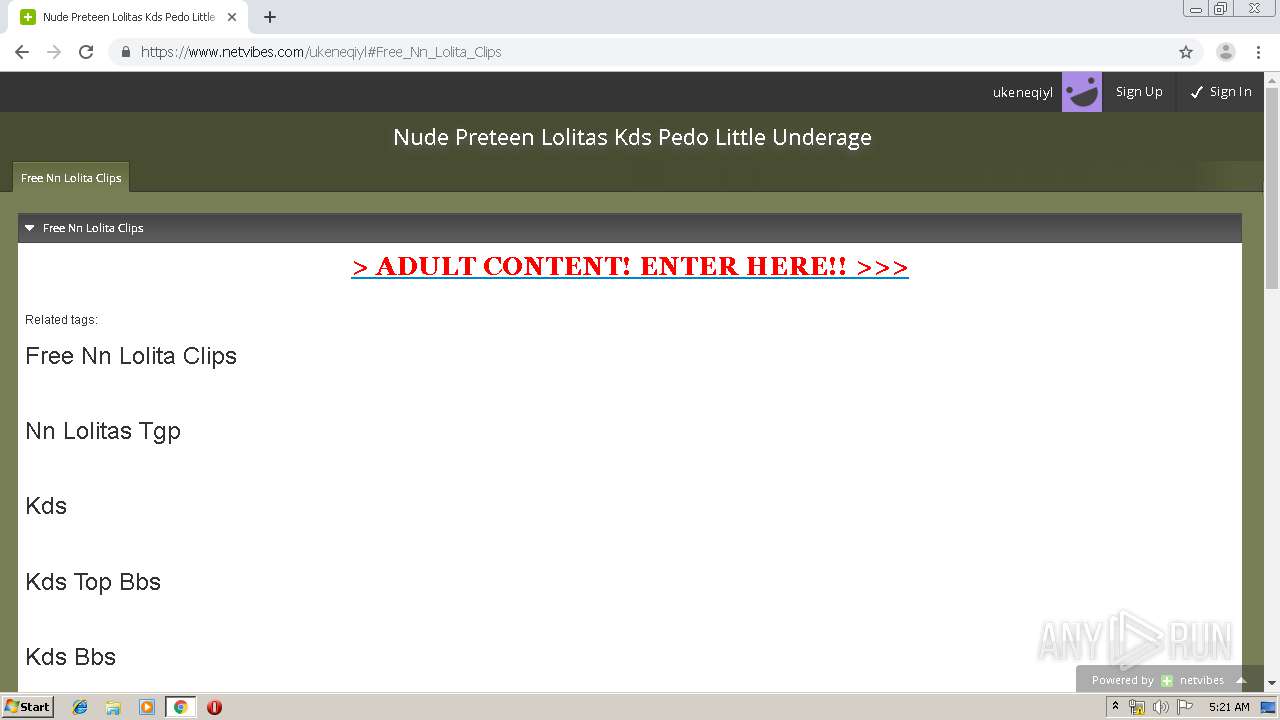
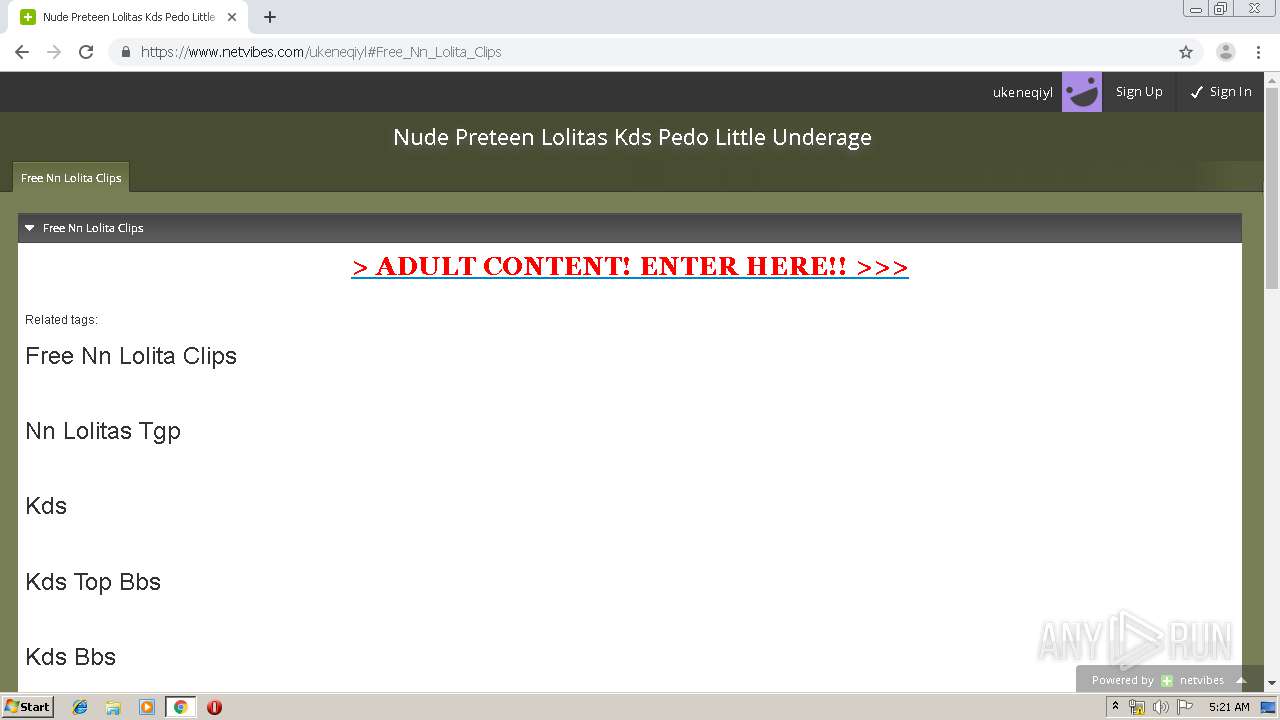
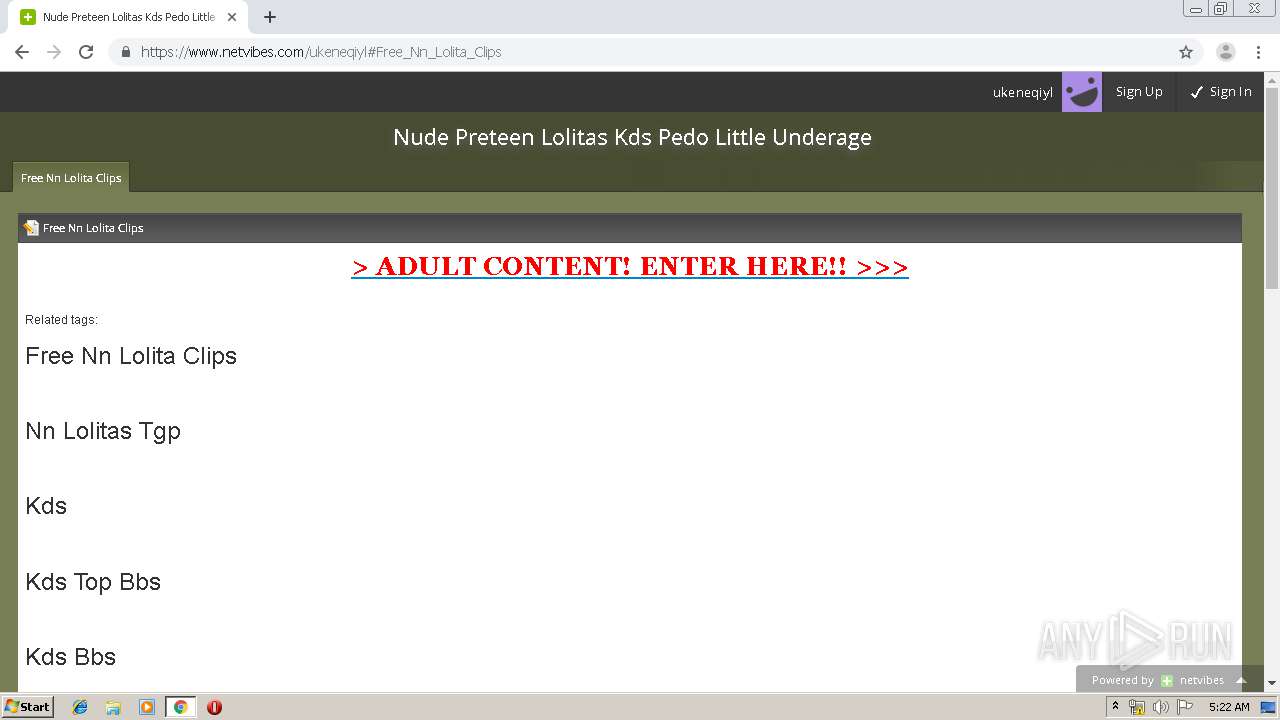
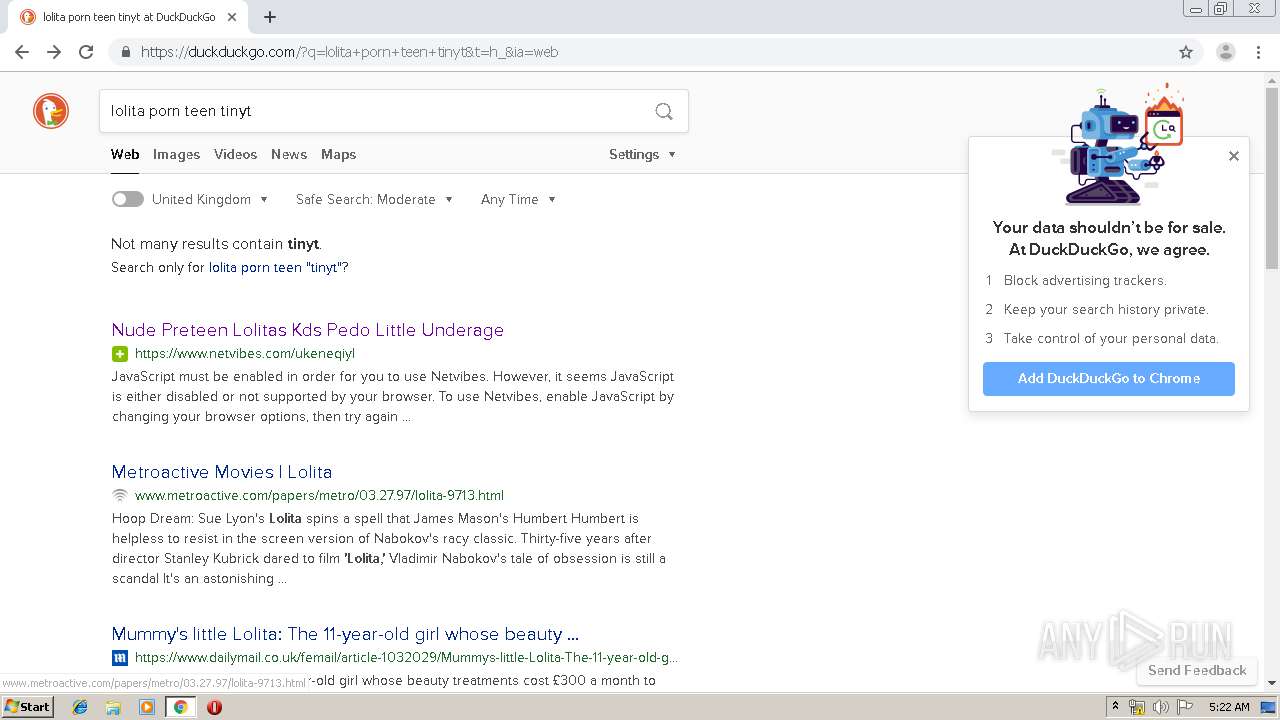
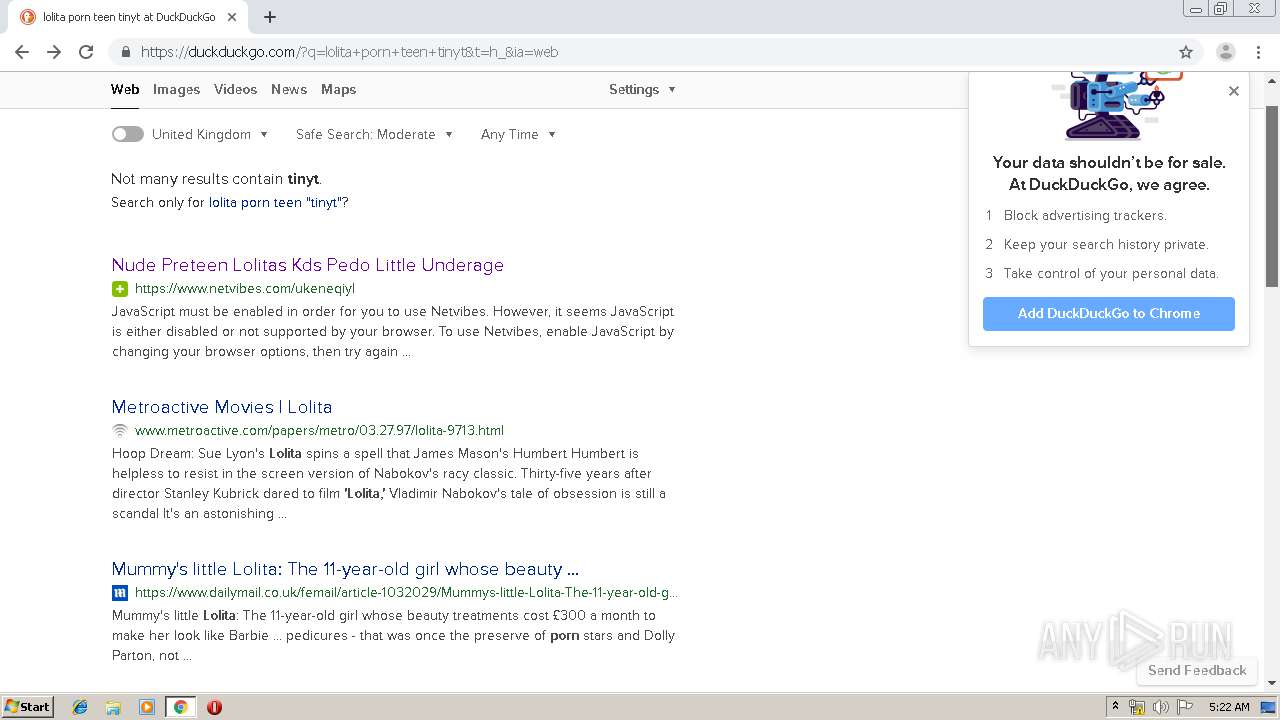
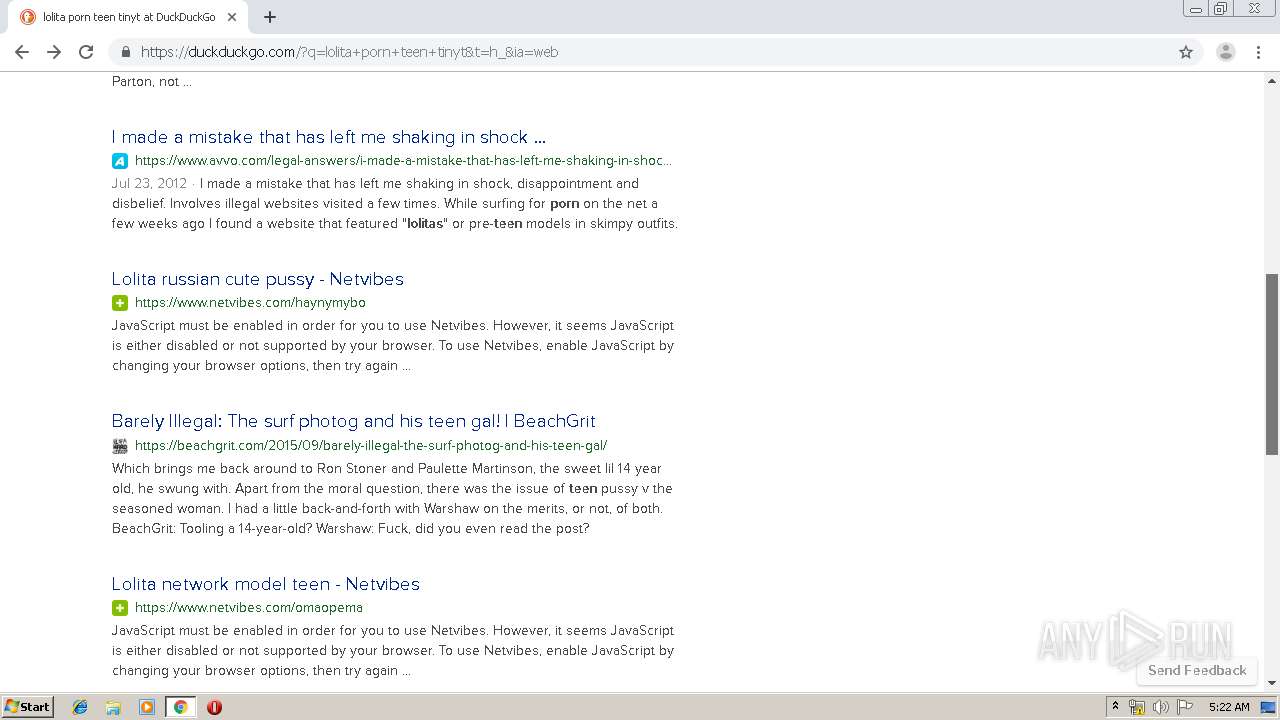
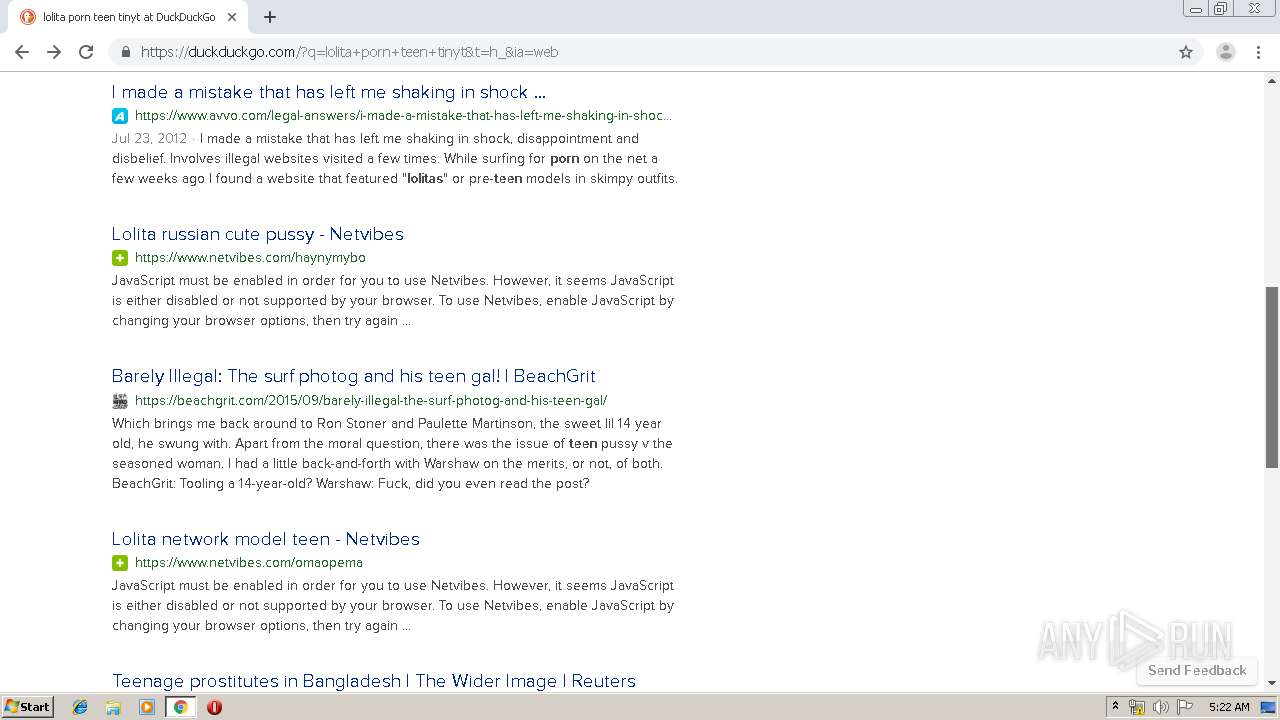
932 | chrome.exe | GET | 200 | 67.55.118.171:80 | http://saipalacehotels.com/black-panther-2018-dvdrip-avc-clean-audio-movie-torrent-download/ | US | html | 55.3 Kb | suspicious |
932 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
932 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
932 | chrome.exe | GET | 200 | 67.55.118.171:80 | http://saipalacehotels.com/wp-content/themes/materialis/style.min.css?ver=1.0.104 | US | text | 374 Kb | suspicious |
932 | chrome.exe | GET | — | 67.55.118.171:80 | http://saipalacehotels.com/wp-includes/js/jquery/jquery-migrate.min.js?ver=1.4.1 | US | — | — | suspicious |
932 | chrome.exe | GET | 200 | 67.55.118.171:80 | http://saipalacehotels.com/wp-content/plugins/contact-form-7/includes/css/styles.css?ver=5.1.1 | US | text | 1.65 Kb | suspicious |
932 | chrome.exe | GET | 200 | 173.194.183.103:80 | http://r2---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.117.25&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1578547096&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | iexplore.exe | 104.111.238.86:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
4040 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2108 | iexplore.exe | 2.16.186.24:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
2108 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4040 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2108 | iexplore.exe | 40.90.22.185:443 | login.live.com | Microsoft Corporation | US | unknown |
2108 | iexplore.exe | 178.79.242.147:80 | www.bittorrent.com | Limelight Networks, Inc. | DE | suspicious |
2108 | iexplore.exe | 178.79.242.147:443 | www.bittorrent.com | Limelight Networks, Inc. | DE | suspicious |
2108 | iexplore.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 209.197.3.15:443 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
shell.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bittorrent.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
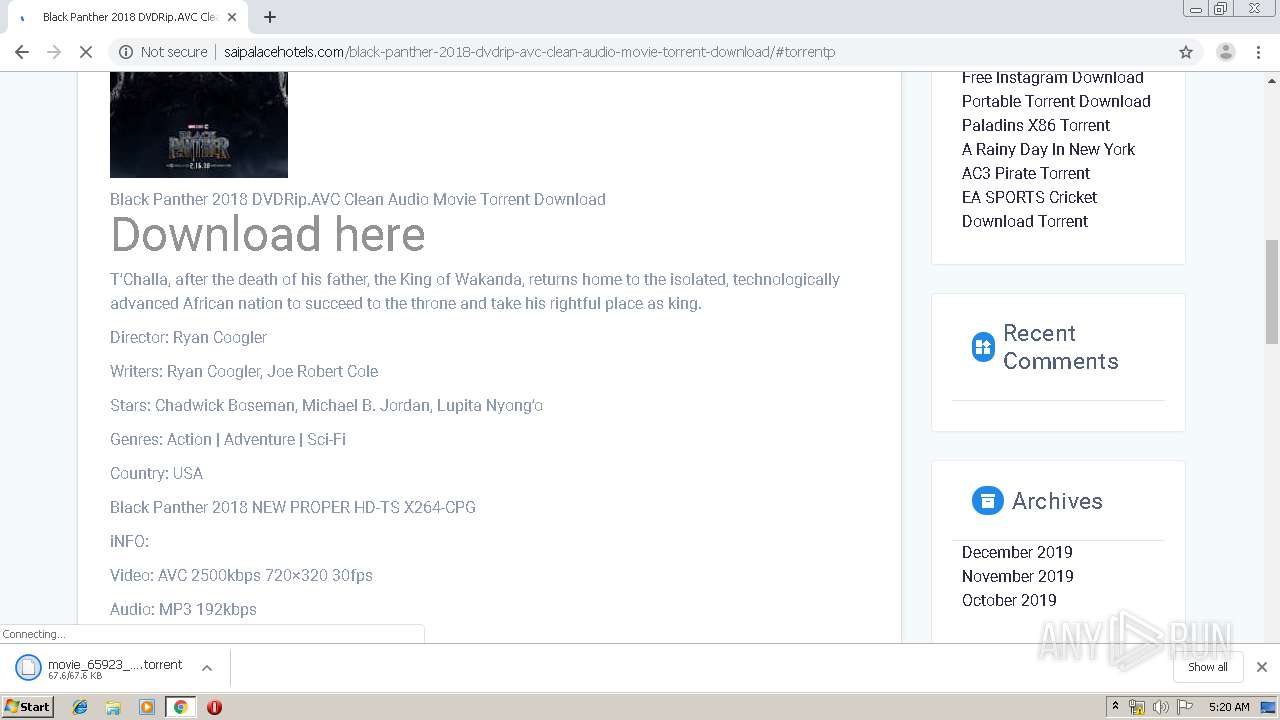
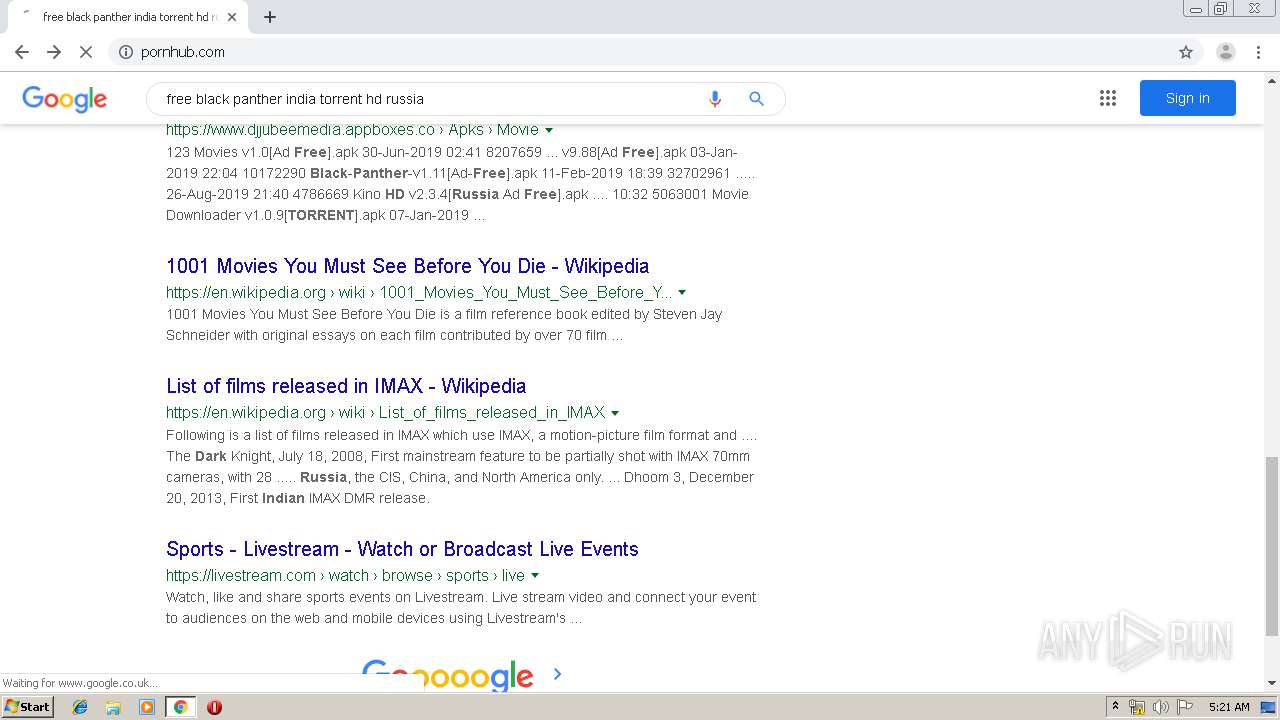
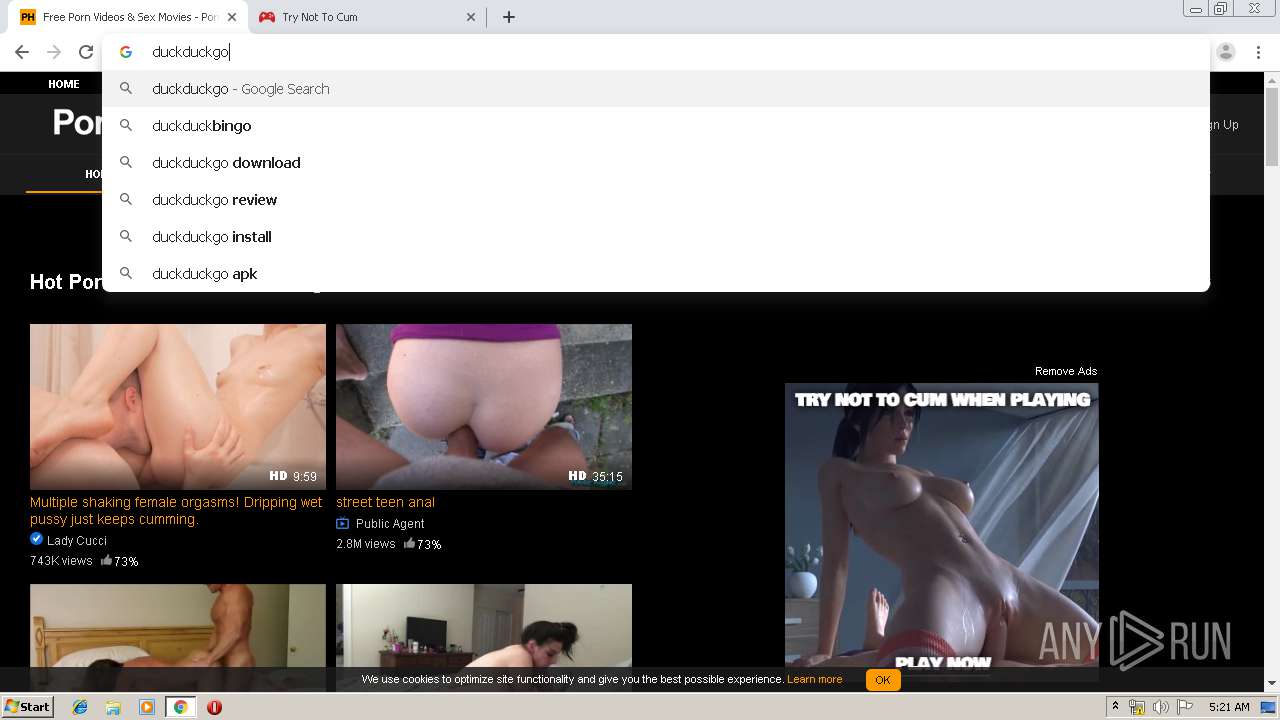
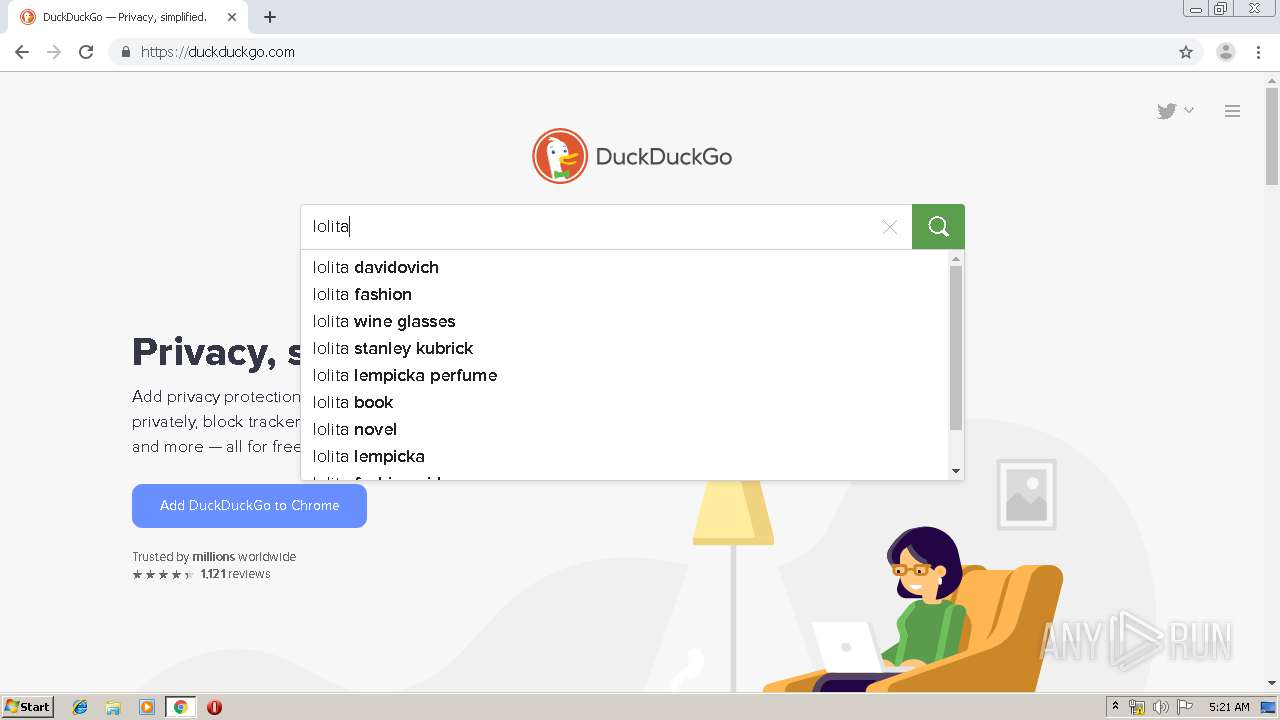
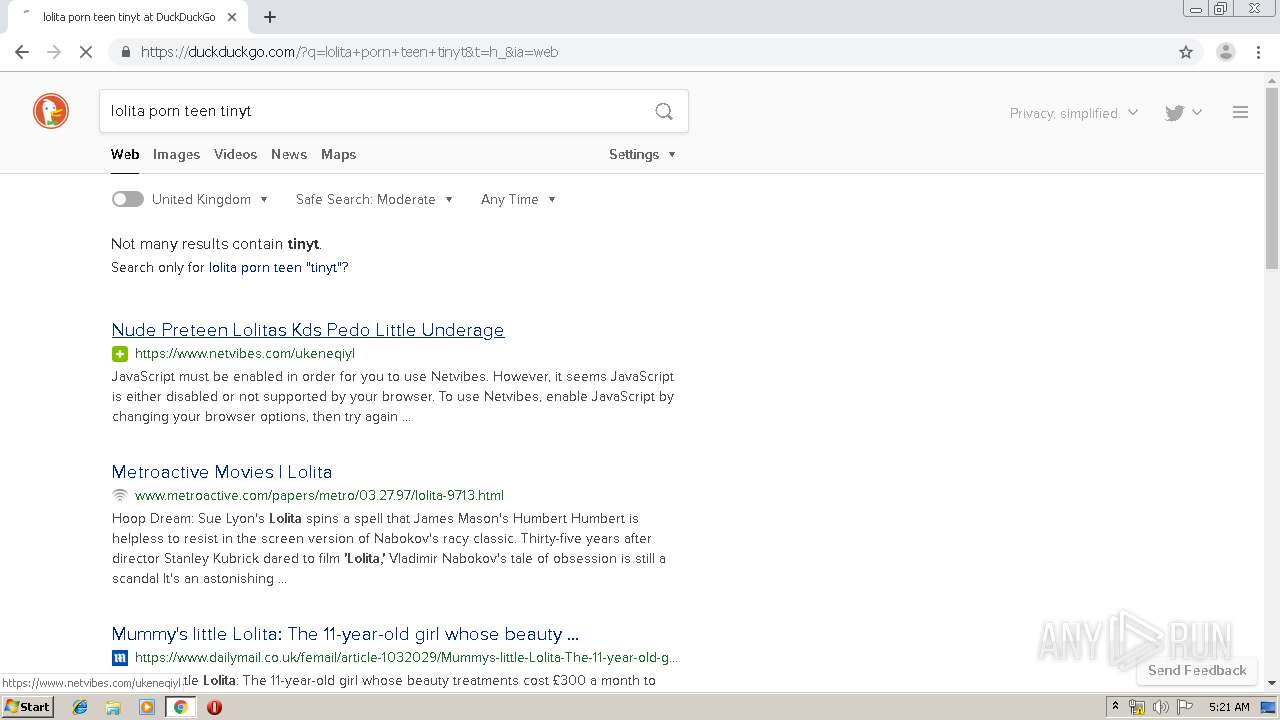
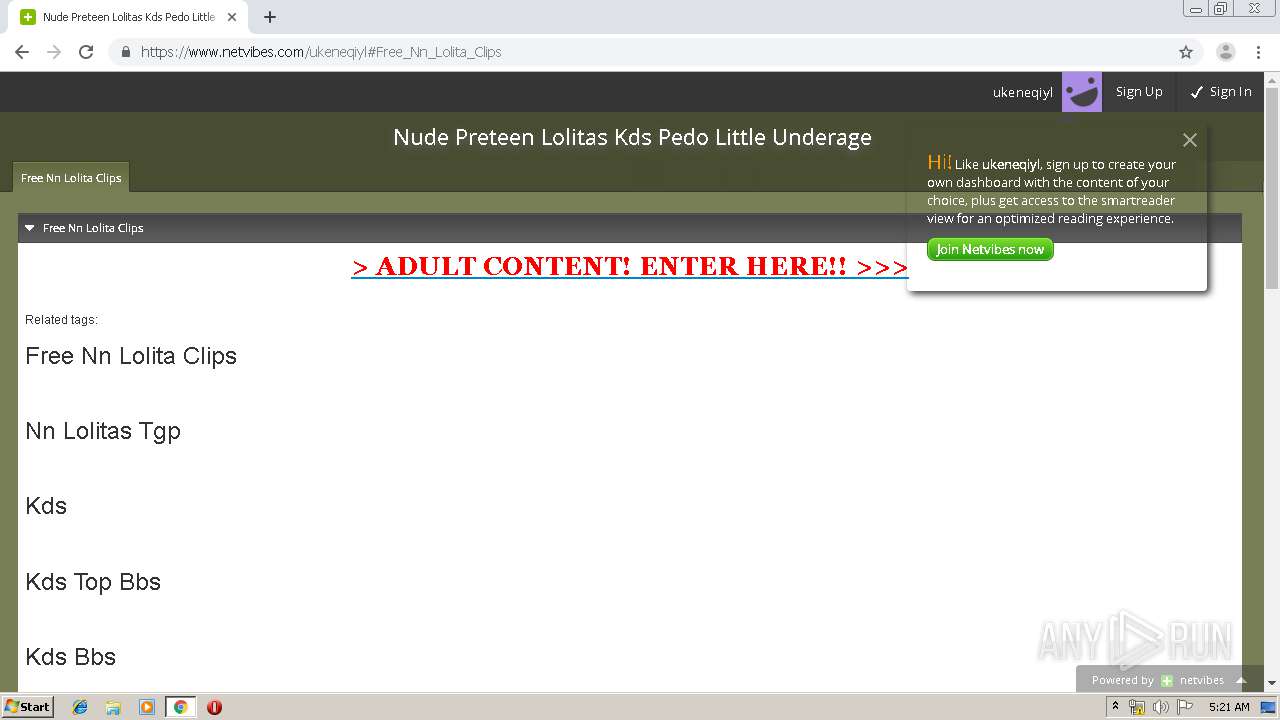
932 | chrome.exe | Potential Corporate Privacy Violation | ET P2P possible torrent download |
932 | chrome.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent - Torrent File Downloaded |
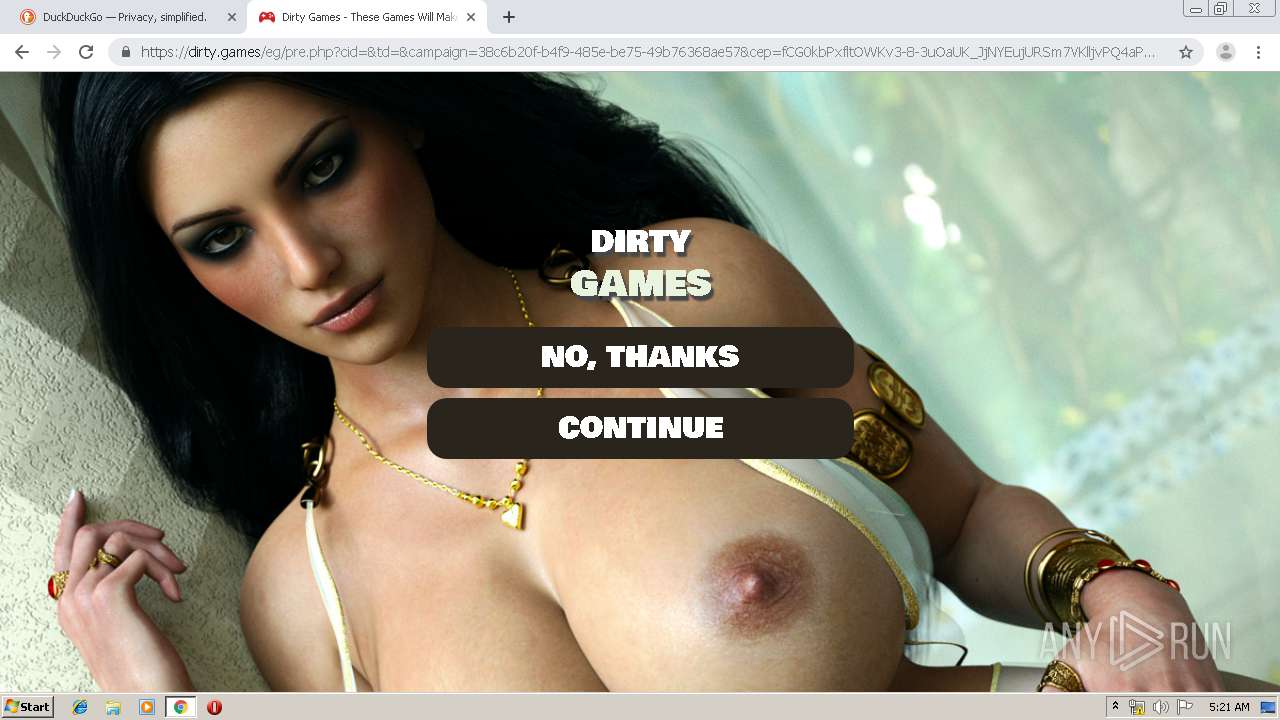
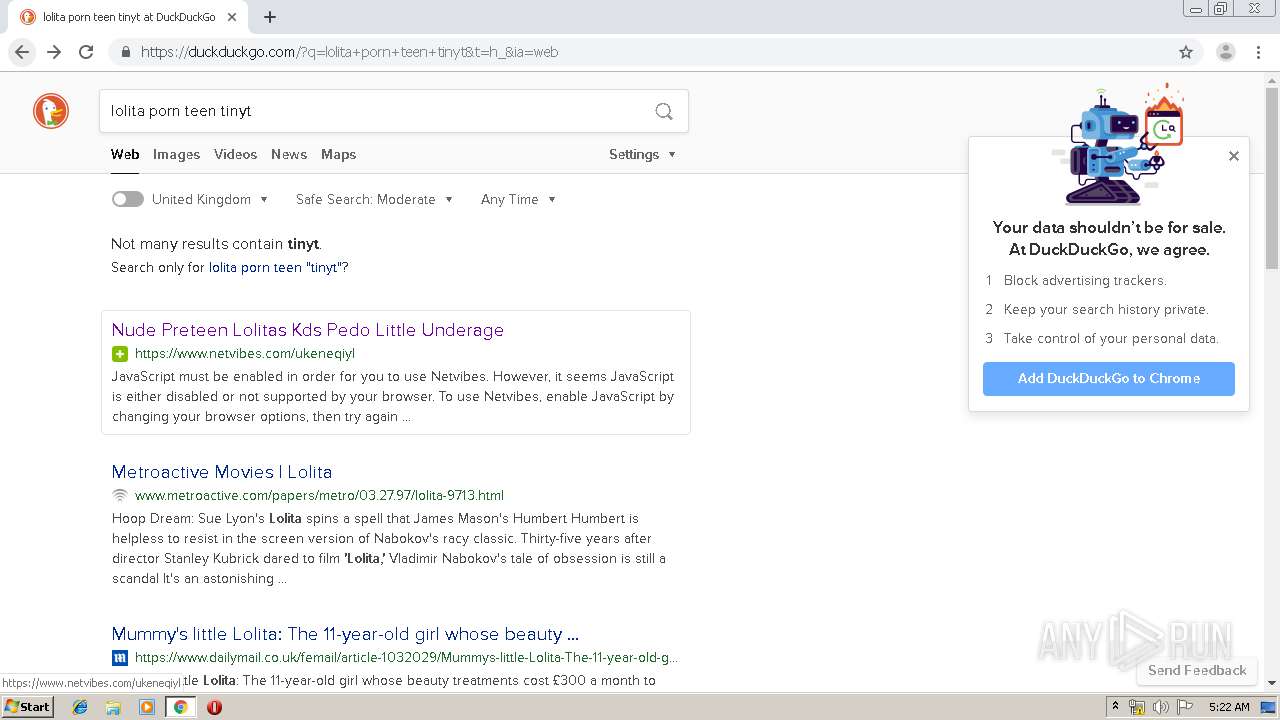
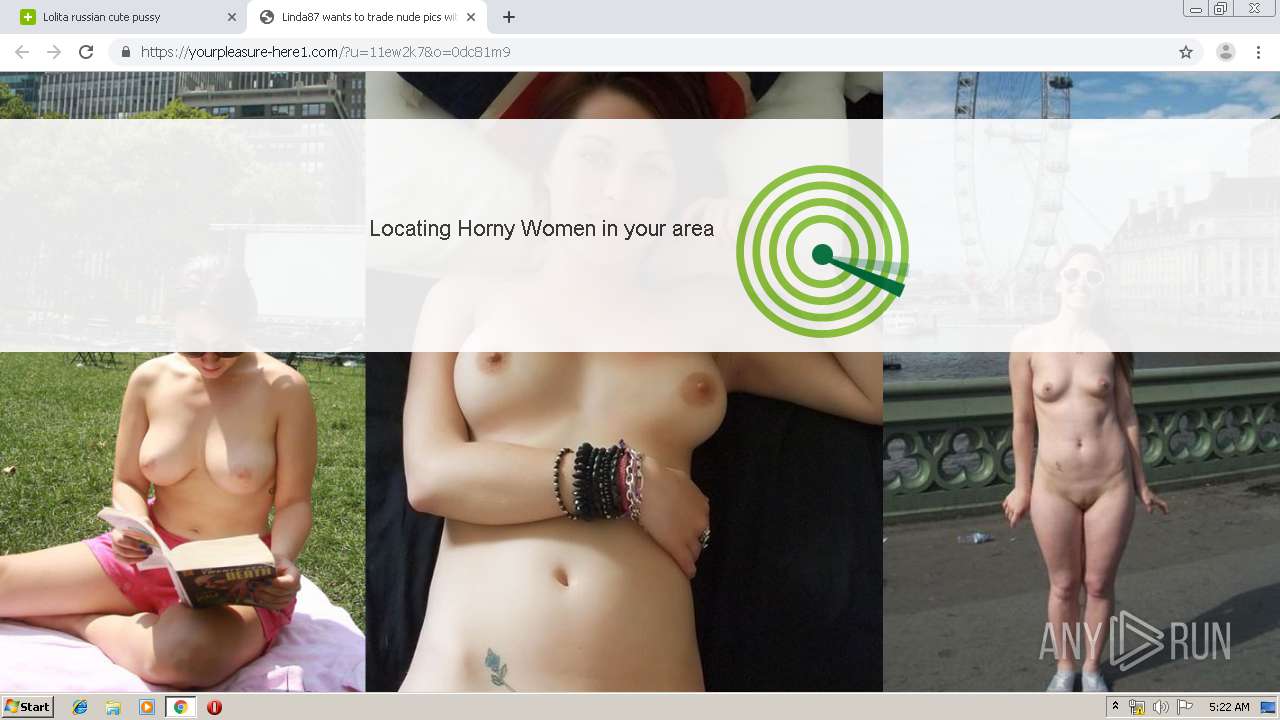
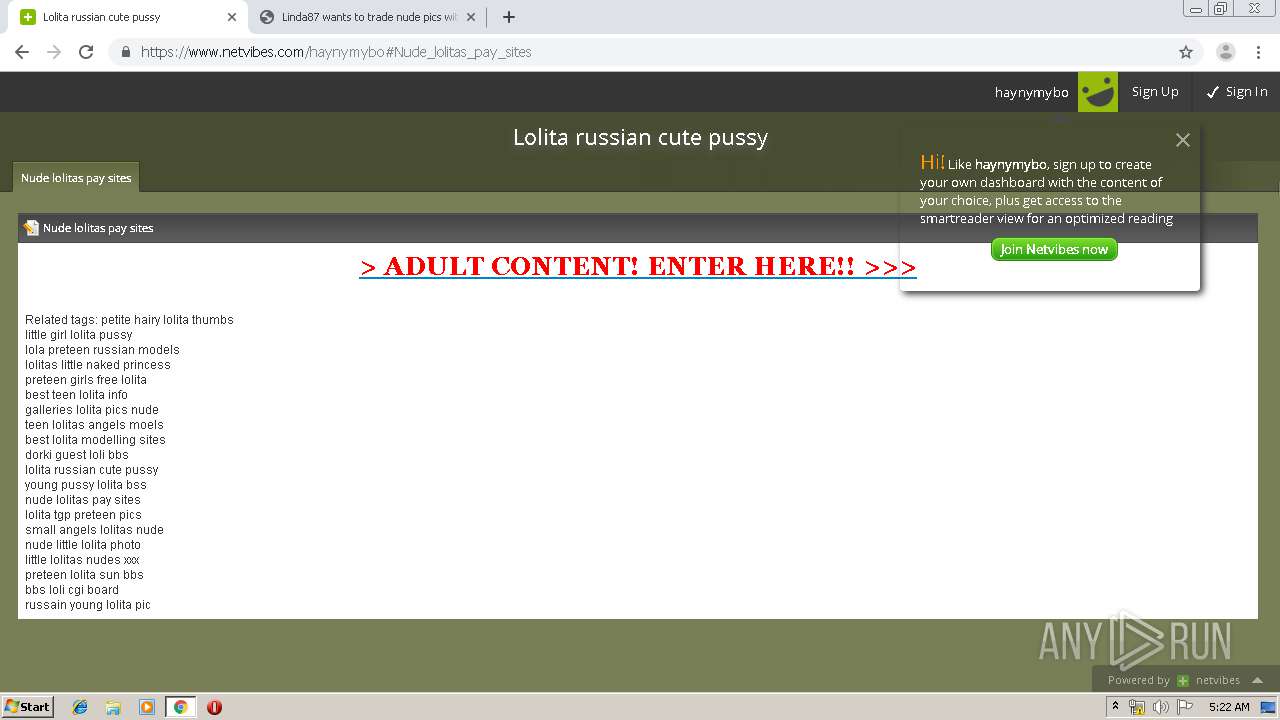
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - page redirecting to a SutraTDS |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - HTTP header redirecting to a SutraTDS |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - request in.cgi |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - page redirecting to a SutraTDS |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - redirect received |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - HTTP header redirecting to a SutraTDS |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - request in.cgi |
932 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - redirect received |